| File name: | .exe |
| Full analysis: | https://app.any.run/tasks/ba3272b0-a214-4930-9eda-55ded774e4eb |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 17:44:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 5 sections |
| MD5: | 7C9B7354279680E57E740BE0B8ABFF20 |
| SHA1: | 3781358A558E563FCD7A997A89A6BACF46641DAE |
| SHA256: | 567D56920D6C11920923CA11AD80E35A974B3001091155F67299A7A231335A73 |
| SSDEEP: | 24576:HaJ9QdPsHWYWz+xwoVFOhQOH5NYvB6hO9V8aE02:HppGWYWz+xwo2hQOH5NYvB6hO9V8aj2 |
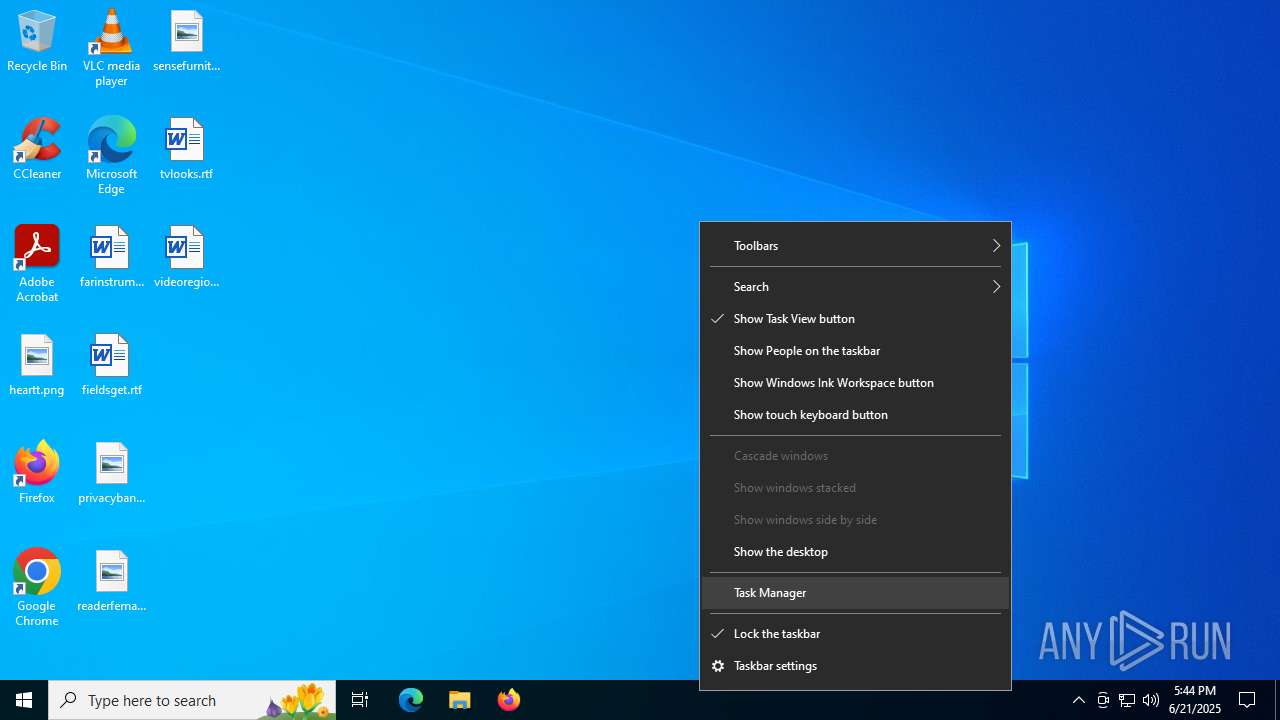
MALICIOUS
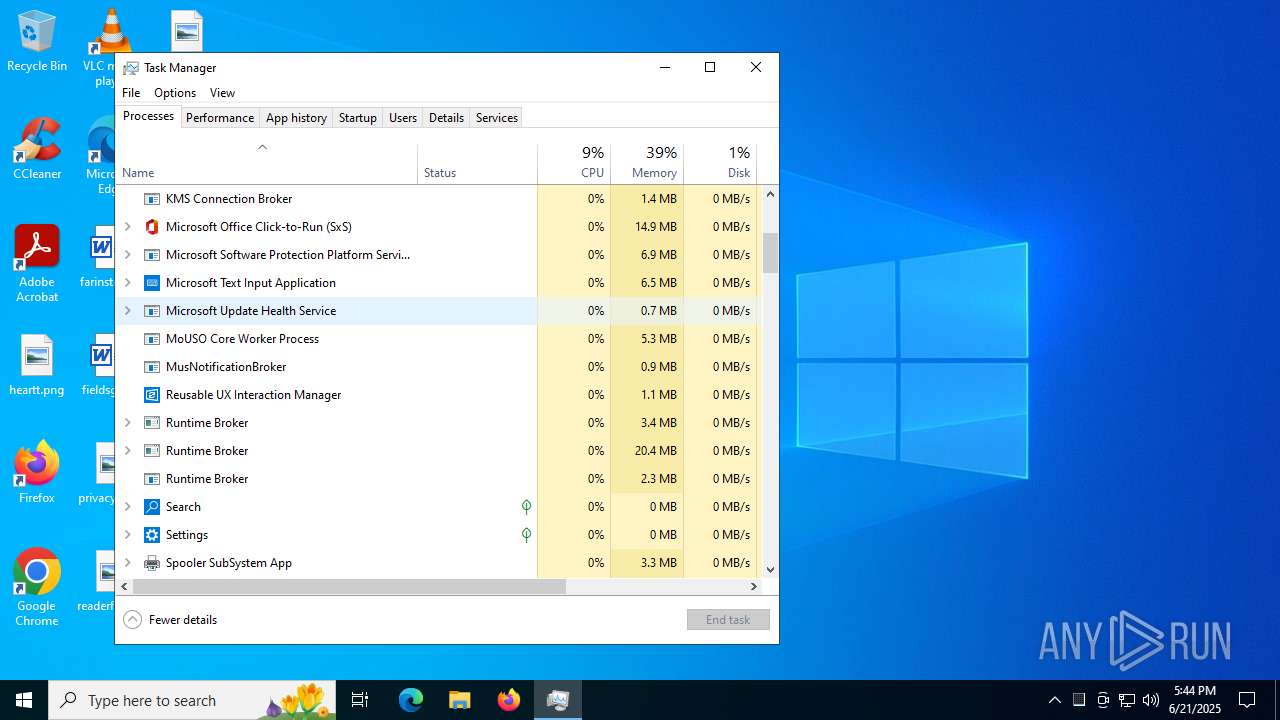
Application was injected by another process
- svchost.exe (PID: 4204)
- sihost.exe (PID: 4180)
- svchost.exe (PID: 4248)
- explorer.exe (PID: 4772)
- svchost.exe (PID: 5048)
- RuntimeBroker.exe (PID: 5224)
- StartMenuExperienceHost.exe (PID: 5160)
- SearchApp.exe (PID: 5328)
- RuntimeBroker.exe (PID: 5448)
- dllhost.exe (PID: 5604)
- ApplicationFrameHost.exe (PID: 5096)
- RuntimeBroker.exe (PID: 4376)
- UserOOBEBroker.exe (PID: 5936)
- dllhost.exe (PID: 2484)
- TextInputHost.exe (PID: 2772)
- RuntimeBroker.exe (PID: 7092)
- firefox.exe (PID: 3388)
- default-browser-agent.exe (PID: 5172)
- firefox.exe (PID: 984)
- taskhostw.exe (PID: 420)
- svchost.exe (PID: 6984)
Changes the autorun value in the registry
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
- explorer.exe (PID: 4772)
DIAMOTRIX has been detected (SURICATA)
- explorer.exe (PID: 4772)
Runs injected code in another process
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
SUSPICIOUS
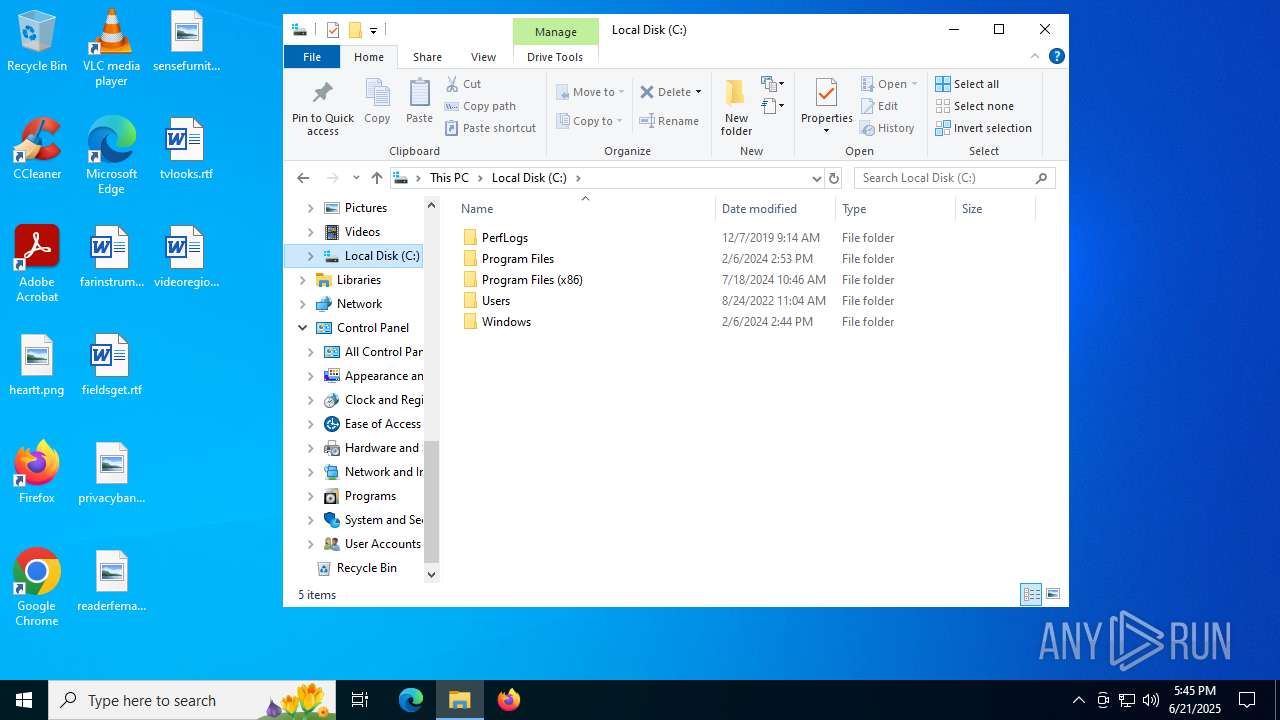
Executable content was dropped or overwritten
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
Connects to the server without a host name
- explorer.exe (PID: 4772)
Creates file in the systems drive root
- explorer.exe (PID: 4772)
INFO
Reads security settings of Internet Explorer
- taskhostw.exe (PID: 420)
- Taskmgr.exe (PID: 4944)
- explorer.exe (PID: 4772)
Checks supported languages
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
- default-browser-agent.exe (PID: 5172)
Local mutex for internet shortcut management
- taskhostw.exe (PID: 420)
Reads the computer name
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
Reads the machine GUID from the registry
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
- StartMenuExperienceHost.exe (PID: 5160)
- TextInputHost.exe (PID: 2772)
- default-browser-agent.exe (PID: 5172)
Creates files in the program directory
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
Launching a file from a Registry key
- ba3272b0-a214-4930-9eda-55ded774e4eb.exe (PID: 2760)
- explorer.exe (PID: 4772)
Checks proxy server information
- explorer.exe (PID: 4772)
Application launched itself
- chrome.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33) |
| .exe | | | DOS Executable Generic (33) |
| .vxd | | | VXD Driver (0.5) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:21 17:45:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 23040 |
| InitializedDataSize: | 227840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2468 |
| OSVersion: | 5.2 |
| ImageVersion: | 1 |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
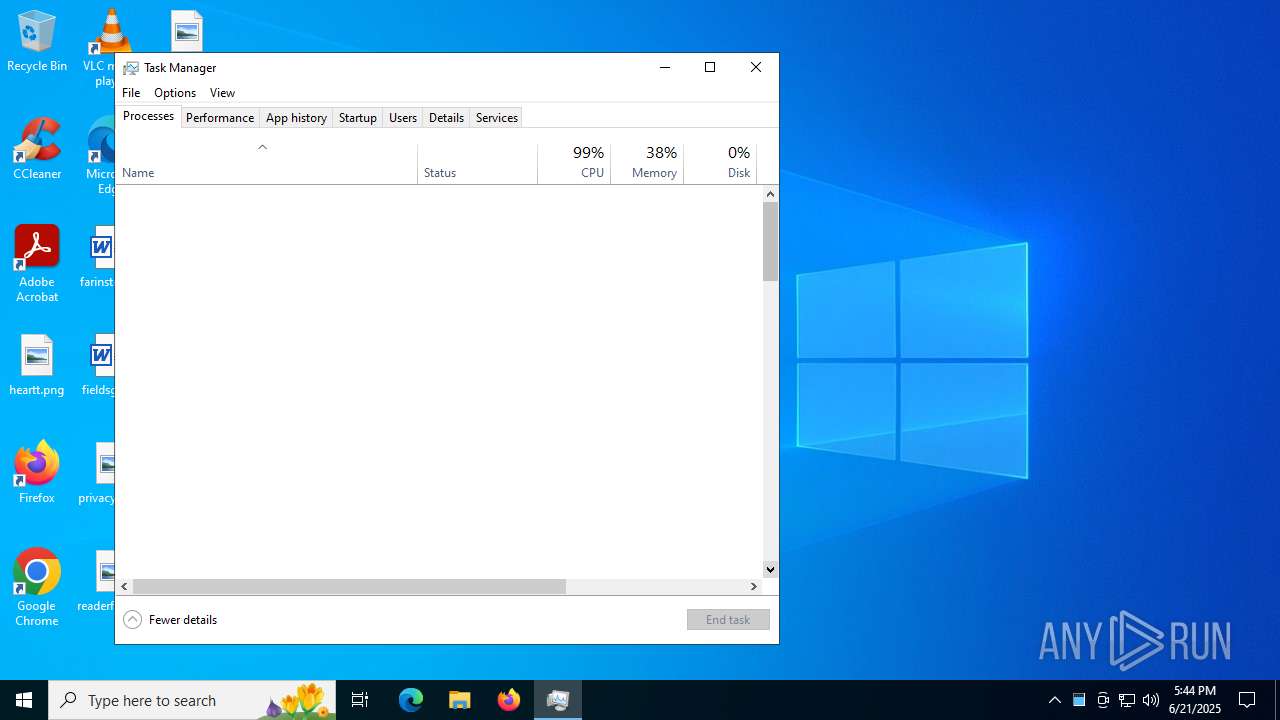
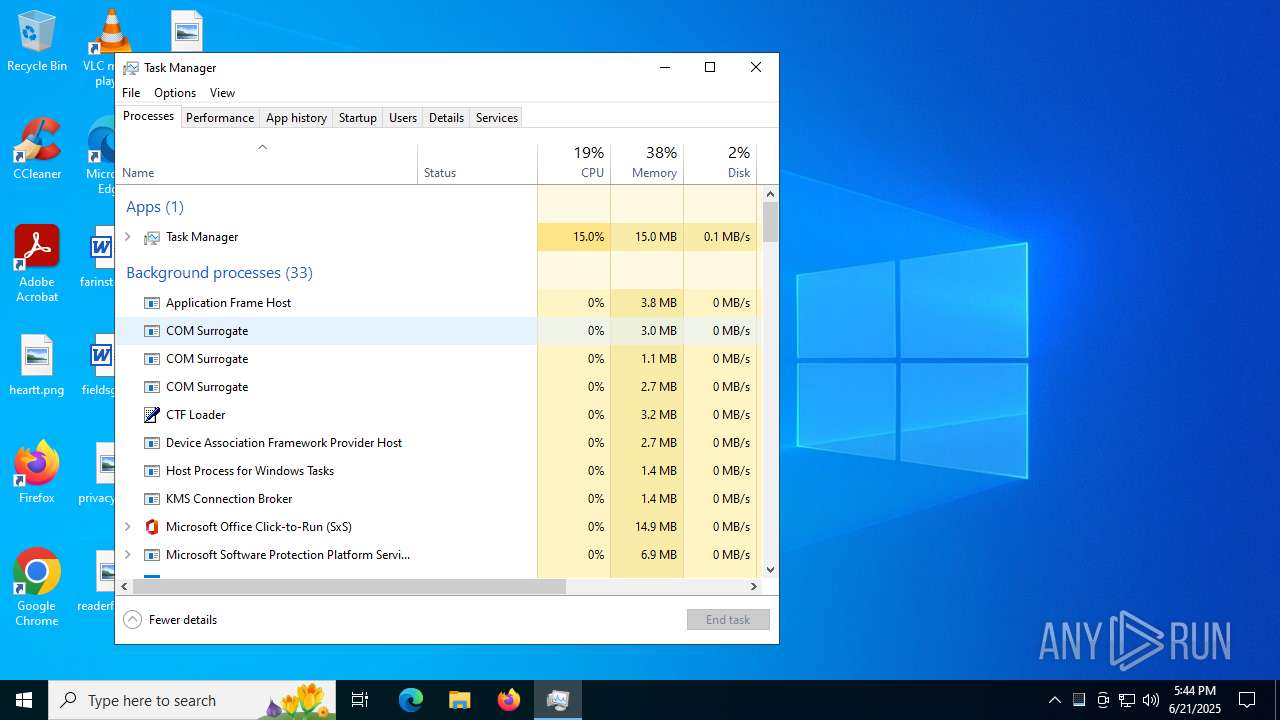
Total processes
149
Monitored processes
33
Malicious processes
3
Suspicious processes
19
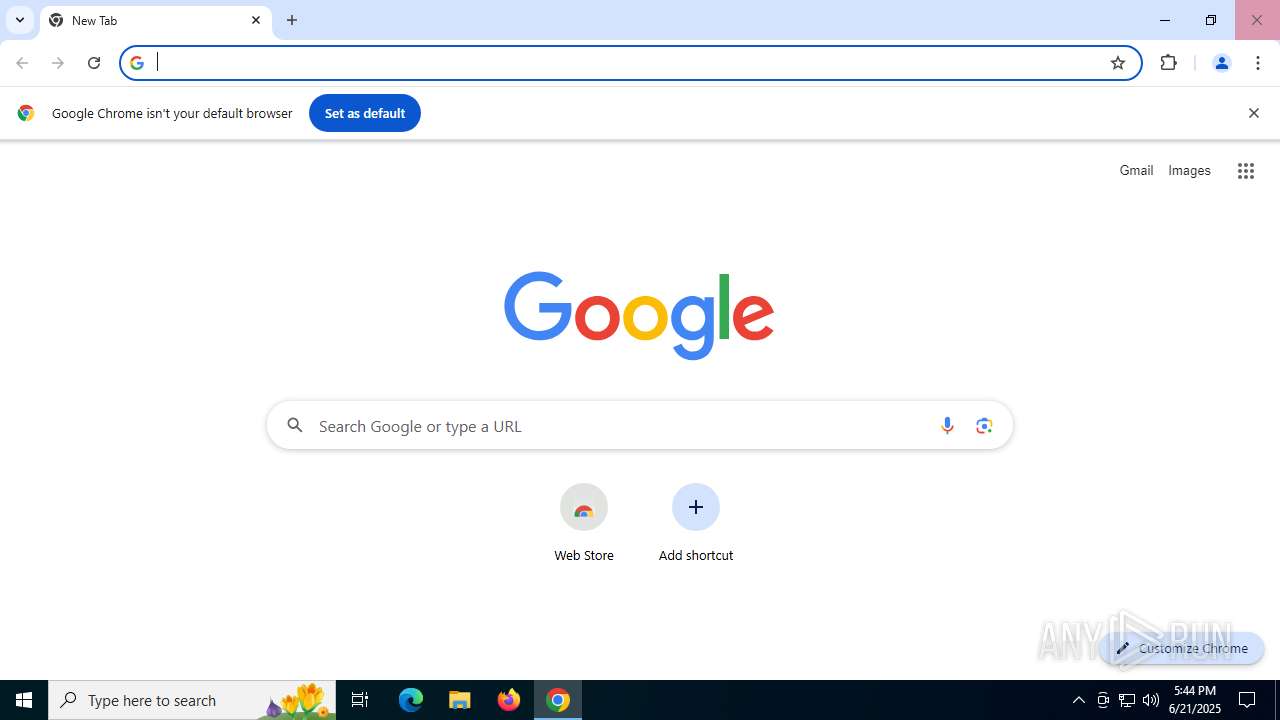
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3248,i,17942081897811176403,13112613349236254720,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 420 | taskhostw.exe | C:\Windows\System32\taskhostw.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | "C:\Program Files\Mozilla Firefox\firefox.exe" --backgroundtask defaultagent do-task 308046B0AF4A39CB | C:\Program Files\Mozilla Firefox\firefox.exe | default-browser-agent.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --disable-http2 --string-annotations --field-trial-handle=2208,i,17942081897811176403,13112613349236254720,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2240 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4744,i,17942081897811176403,13112613349236254720,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --disable-http2 --string-annotations --field-trial-handle=2428,i,17942081897811176403,13112613349236254720,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2720 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2484 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x244,0x248,0x24c,0x220,0x250,0x7ffc4511fff8,0x7ffc45120004,0x7ffc45120010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\AppData\Local\Temp\ba3272b0-a214-4930-9eda-55ded774e4eb.exe" | C:\Users\admin\AppData\Local\Temp\ba3272b0-a214-4930-9eda-55ded774e4eb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2772 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Version: 123.26505.0.0 Modules
| |||||||||||||||
Total events
11 801
Read events
11 647
Write events
139
Delete events
15
Modification events
| (PID) Process: | (420) taskhostw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\CloudStore\Store\DefaultAccount\Current\default$windows.data.apps.appleveltileinfo$appleveltilelist\windows.data.apps.appleveltileinfo$w~microsoft.skype.skypedesktop |
| Operation: | write | Name: | Data |
Value: 434201000A0201002A0693DFDBC2062A000000 | |||
| (PID) Process: | (420) taskhostw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\AppListBackup\ListOfTaskBackedUpTiles_2476180233 |
| Operation: | write | Name: | ListOfTaskBackedUpTiles_2476180233 |
Value: {"tileId":"W~Microsoft.Skype.SkypeDesktop", "appIconLightAssetId":"", "appIconDarkAssetId":"", "displayName":"", "sortName":"", "suiteName":"", "packageId":"", "action":"2", "shortcutArgs":"", "targetPath":""} | |||
| (PID) Process: | (420) taskhostw.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Software\Microsoft\TIP\AggregateResults |
| Operation: | write | Name: | data |
Value: 5F37110201000080856D77FF000000000100000001000000049434020100008086F11F11000000000200000039060000846C81020101008006D1ECE63A00000002000000D60100001CCF9A0201000300B5B9B1720000000055000000270000001CCF9A0201000300B5B9B1721008000018000000010000001CCF9A02017F00801EB4E8D5280000000100000002000000ABC39D02018003000285A591000000000100000001000000ABC39D02018003000285A591100800001800000019000000 | |||
| (PID) Process: | (2760) ba3272b0-a214-4930-9eda-55ded774e4eb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\bbeecafdaeec |
| Operation: | write | Name: | CurrentPath |
Value: C:\Users\admin\AppData\Local\Temp\ba3272b0-a214-4930-9eda-55ded774e4eb.exe | |||
| (PID) Process: | (2760) ba3272b0-a214-4930-9eda-55ded774e4eb.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | bbeecafdaeec |
Value: "C:\ProgramData\bbeecafdaeec.exe" | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 84EF566800000000 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
47
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17b14e.TMP | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF17b16e.TMP | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF17b16e.TMP | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF17b16e.TMP | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF17b16e.TMP | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3740 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
33
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4772 | explorer.exe | POST | 200 | 185.156.72.89:80 | http://185.156.72.89/nzcwzue/pqrfxn.php | unknown | — | — | unknown |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1488 | chrome.exe | GET | 200 | 172.217.16.142:80 | http://clients2.google.com/time/1/current?cup2key=8:mwbJ17WG5yMG__Y1tnA5LI6N5CSUFNyYEDs8LUXQ4yI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4236 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4236 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5720 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4772 | explorer.exe | 185.156.72.89:80 | — | Tov Vaiz Partner | RU | unknown |
6320 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6320 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4772 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix POST Request M3 |