| File name: | r1z.dll |
| Full analysis: | https://app.any.run/tasks/a9fc092a-530b-4dca-9d27-8fc91ce18f11 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2024, 20:39:10 |
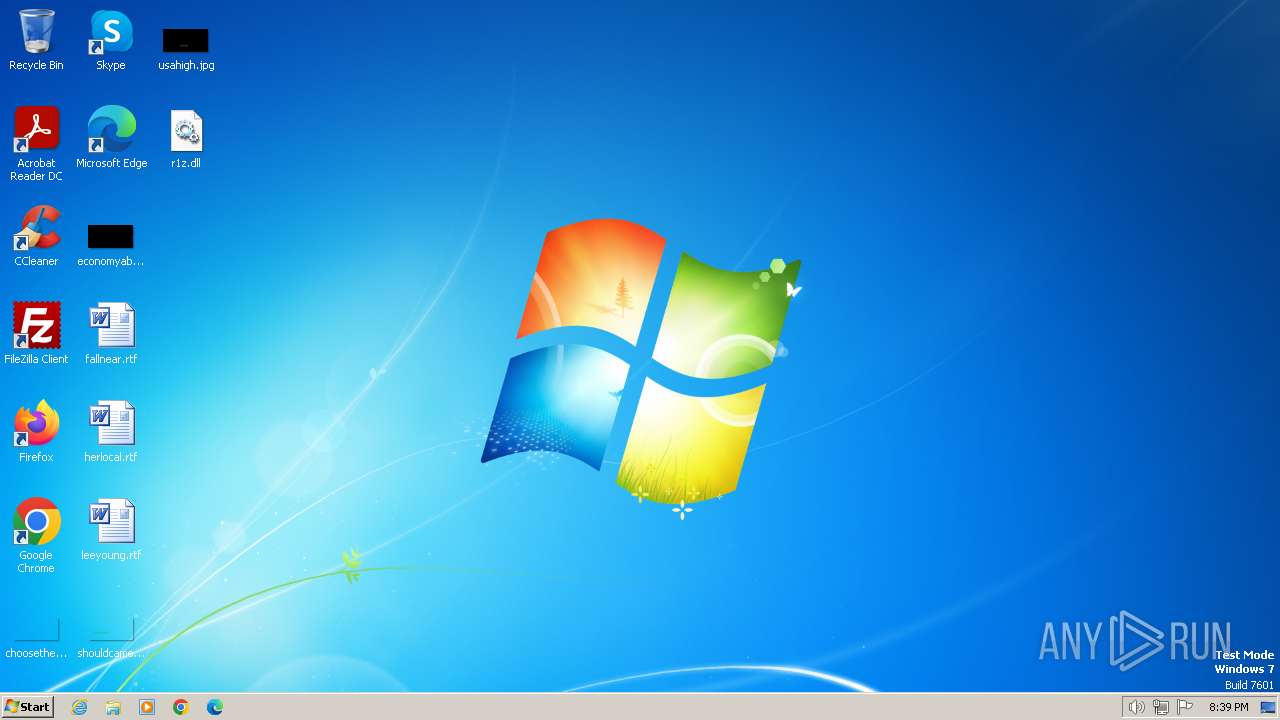
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (console) x86-64 (stripped to external PDB), for MS Windows |
| MD5: | 74020B034BDB2B250242EB28C02B1D91 |
| SHA1: | 7B8A50FE97F9B40513D4371E596ABCFD74CB0F65 |
| SHA256: | 5671B6D4BAA9A483F66774EF06743713F662B1DE3A6E6E23C95CBAD803CE4D43 |
| SSDEEP: | 24576:KiTVNk/8xHBhxH3S2gtLDbpxUIDP8VbGEE:KiT/kEx3xHC2gtLDbpxUIDP8VbGE |
MALICIOUS
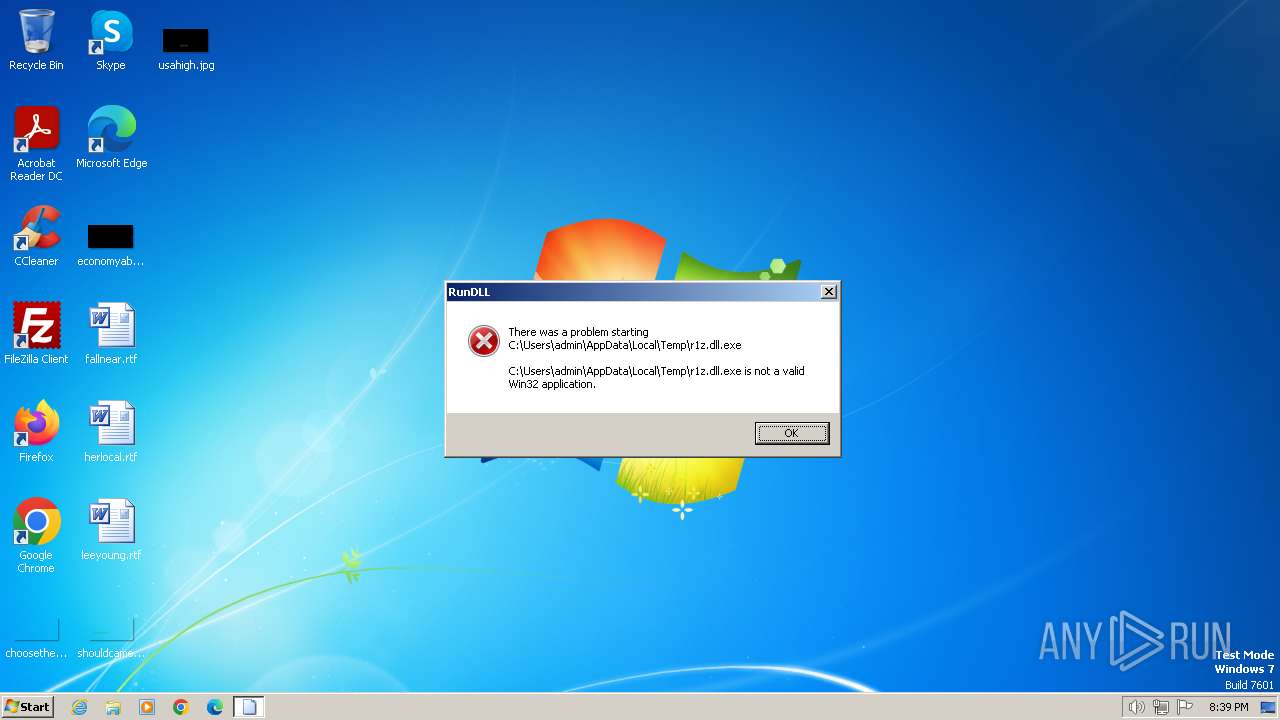
Drops the executable file immediately after the start
- rundll32.exe (PID: 2044)
SUSPICIOUS
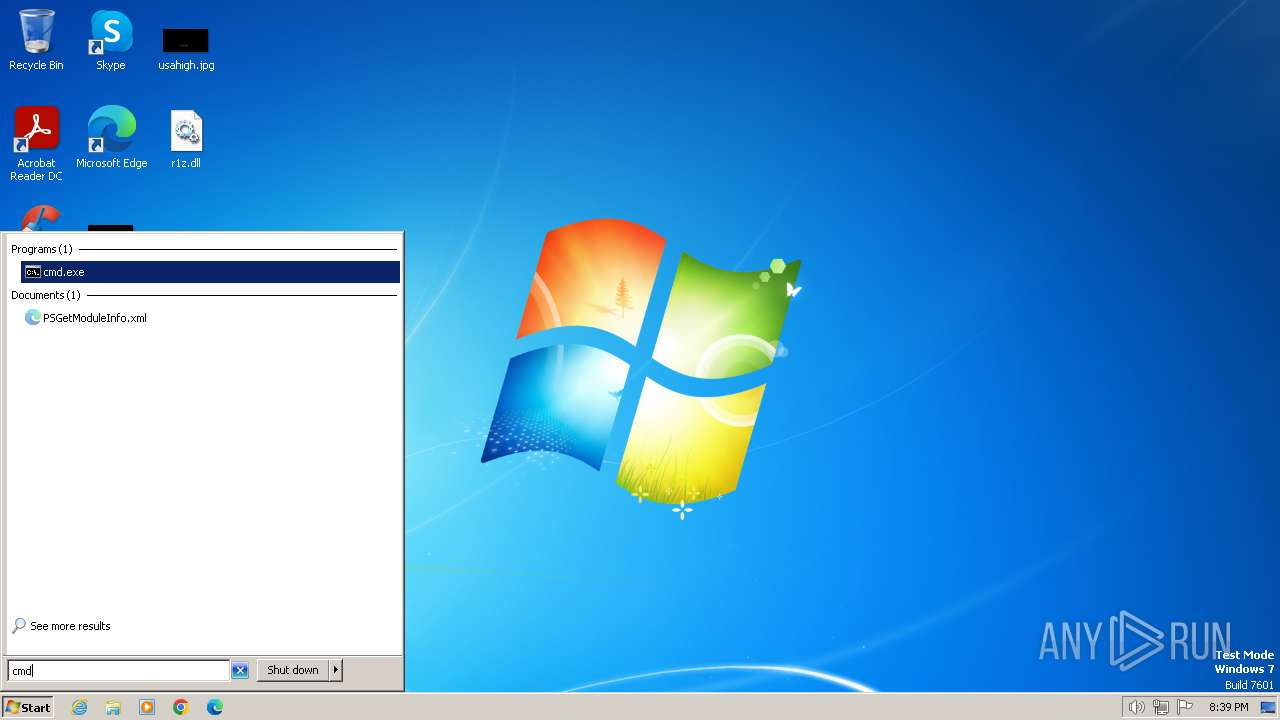
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1936)
Reads the Internet Settings
- powershell.exe (PID: 1936)
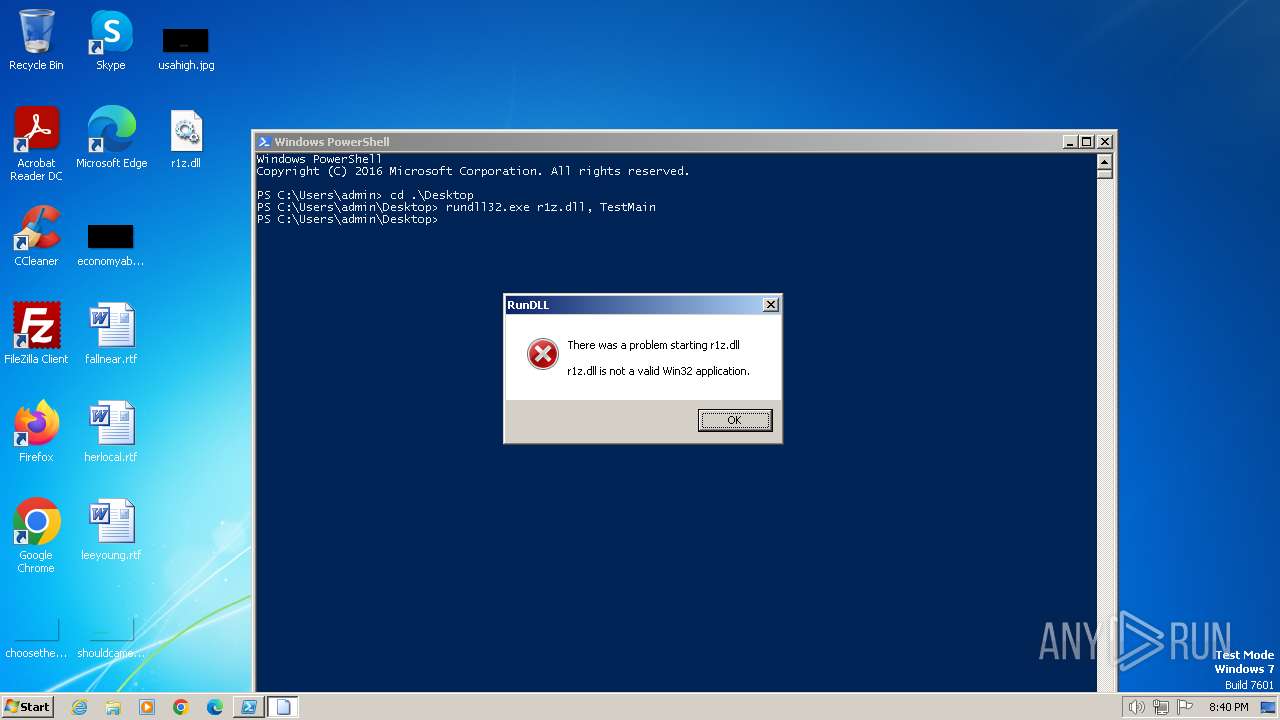
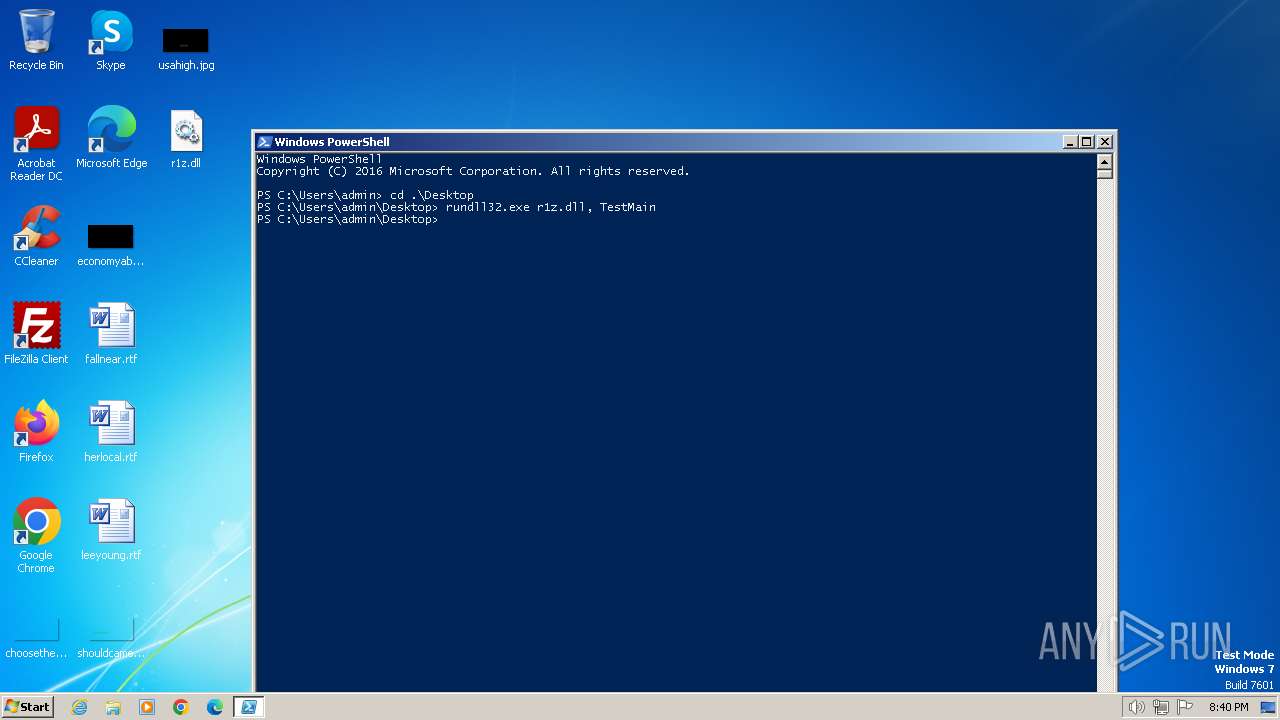
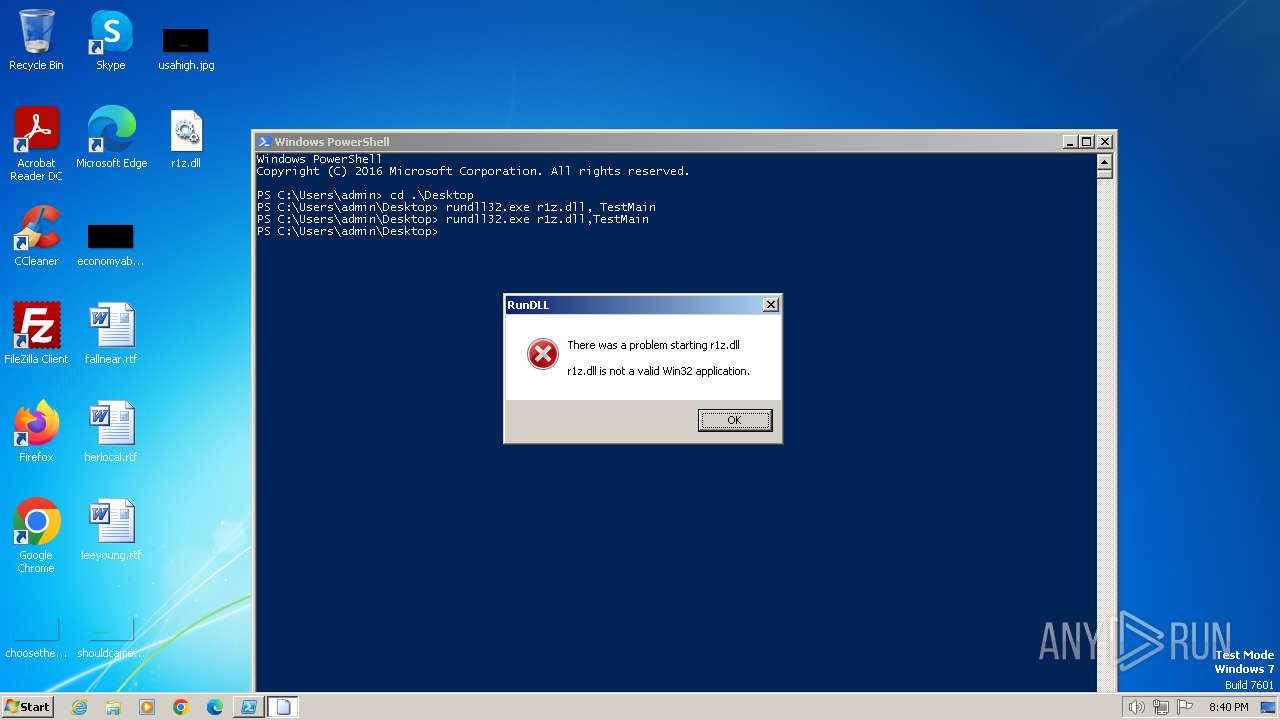
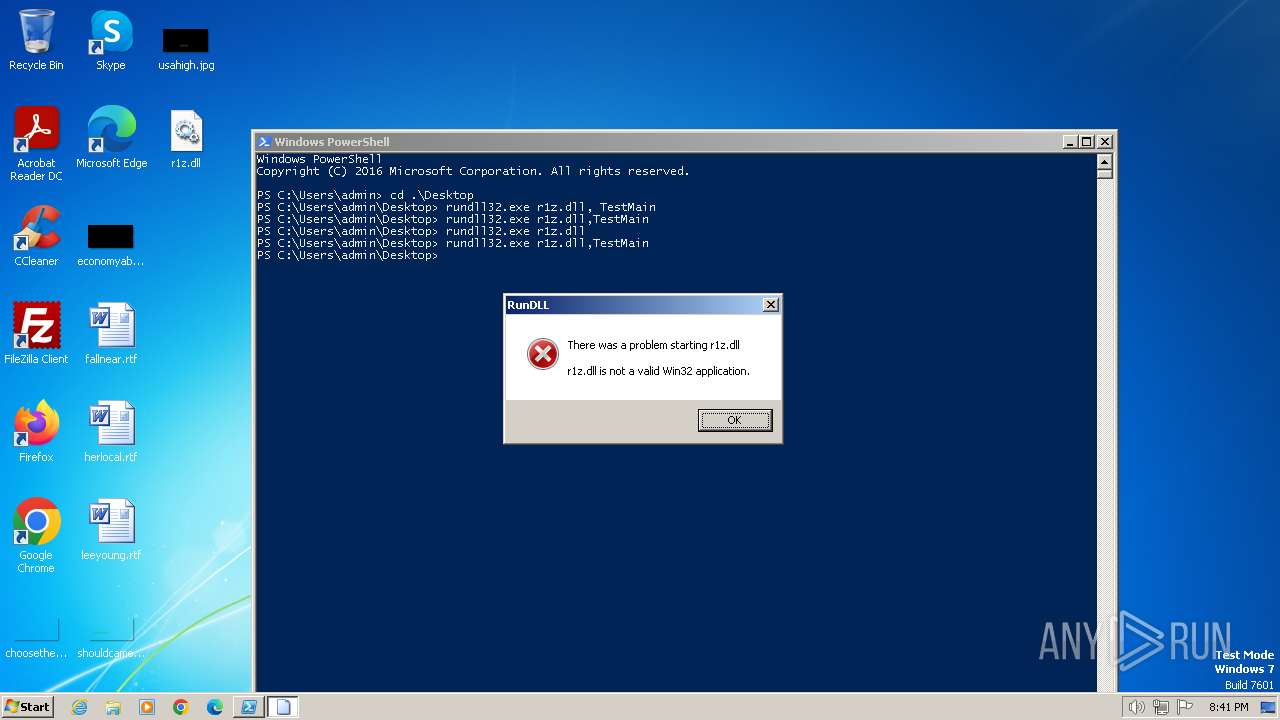
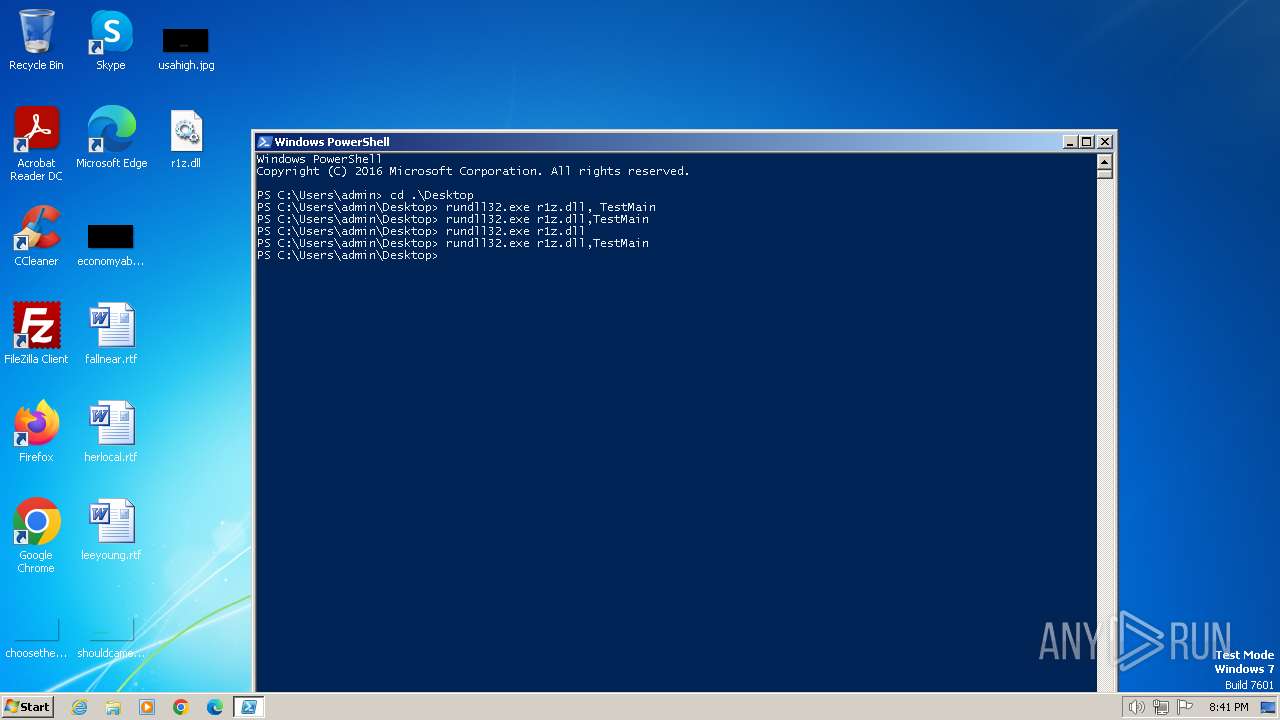
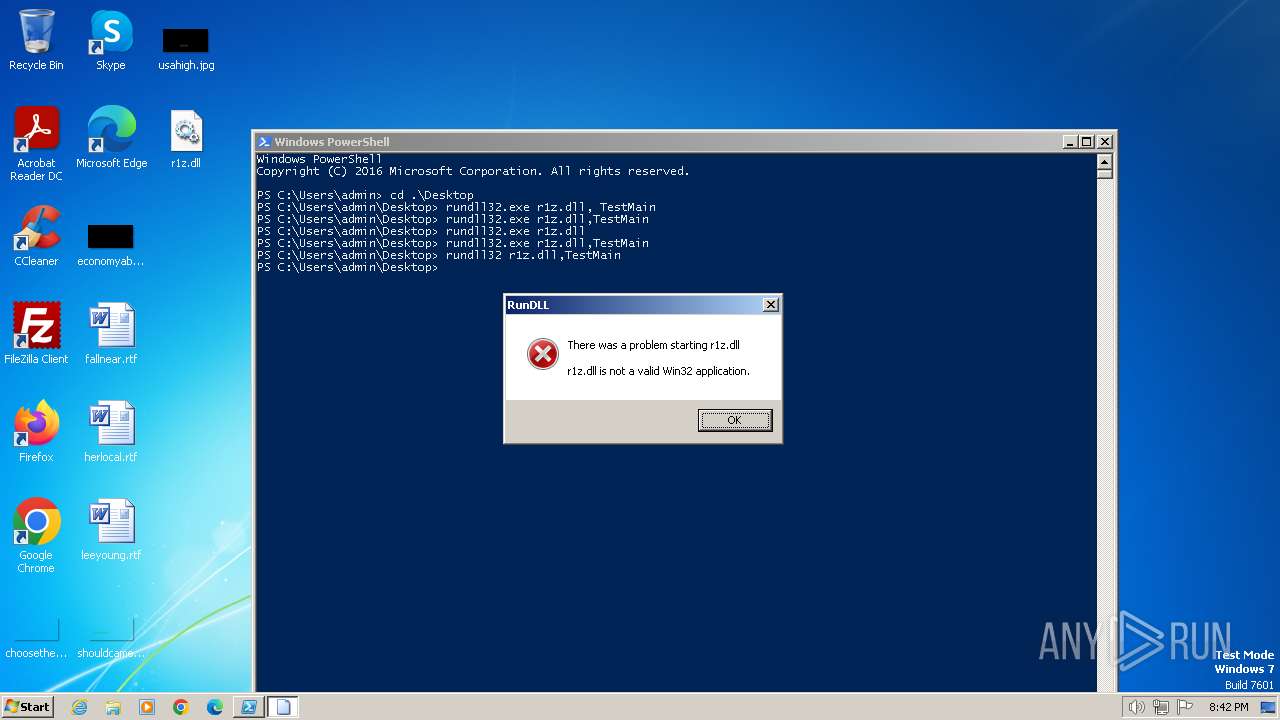
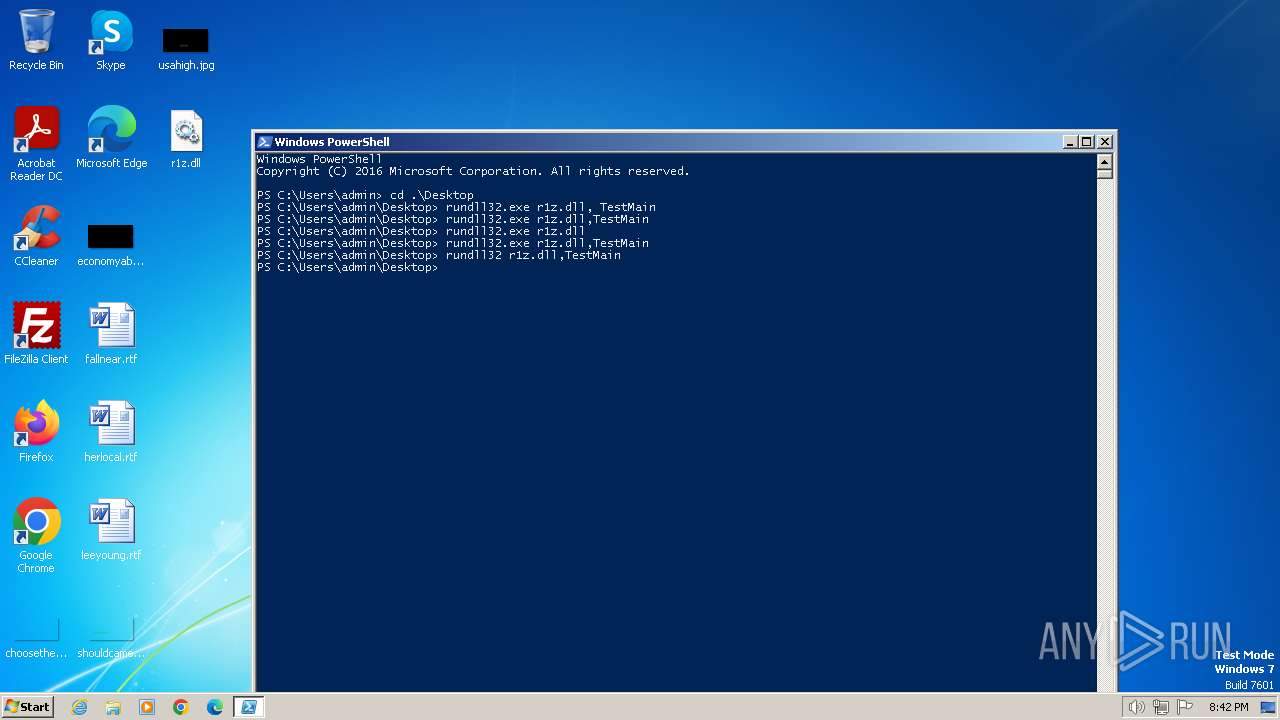
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 1936)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 124)
Reads the computer name
- wmpnscfg.exe (PID: 124)
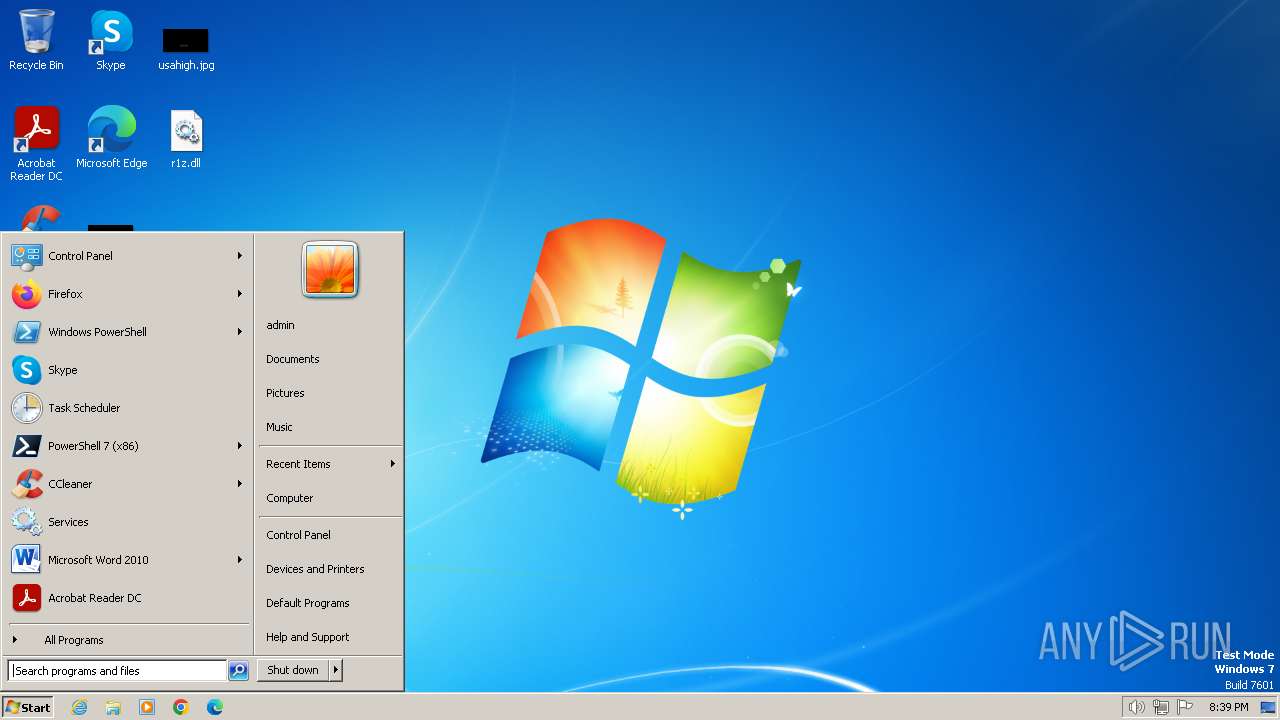
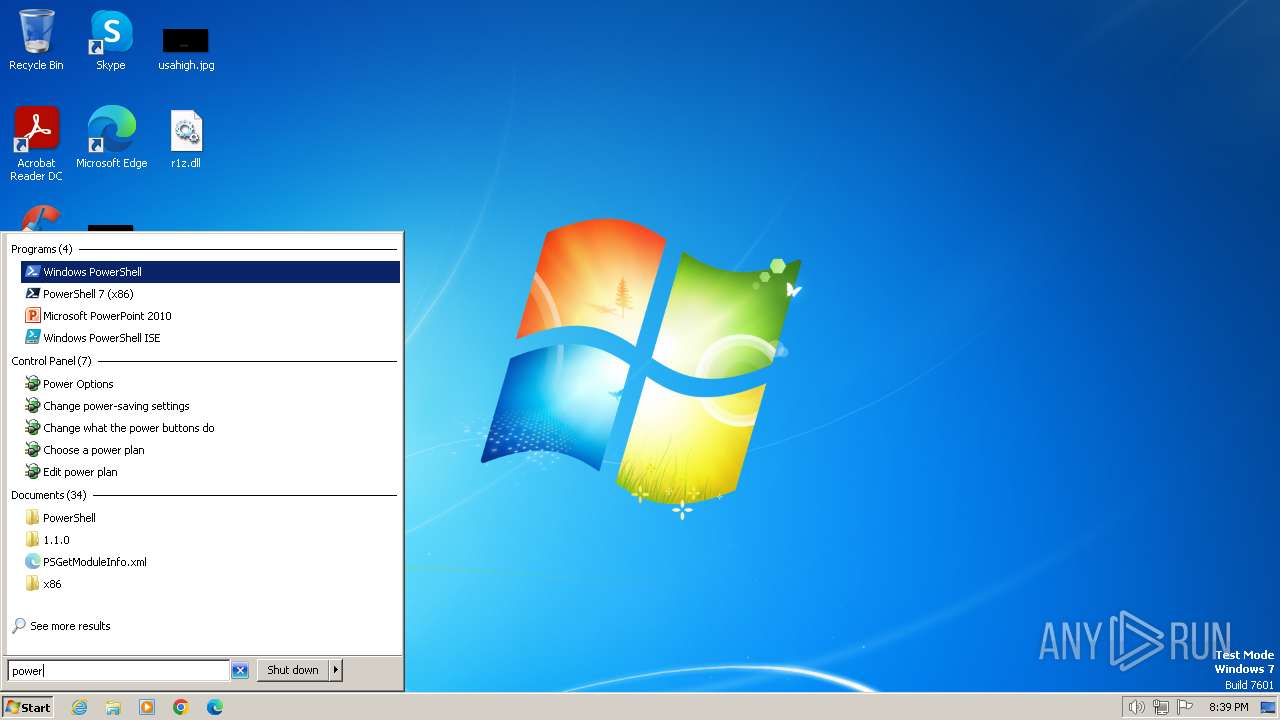
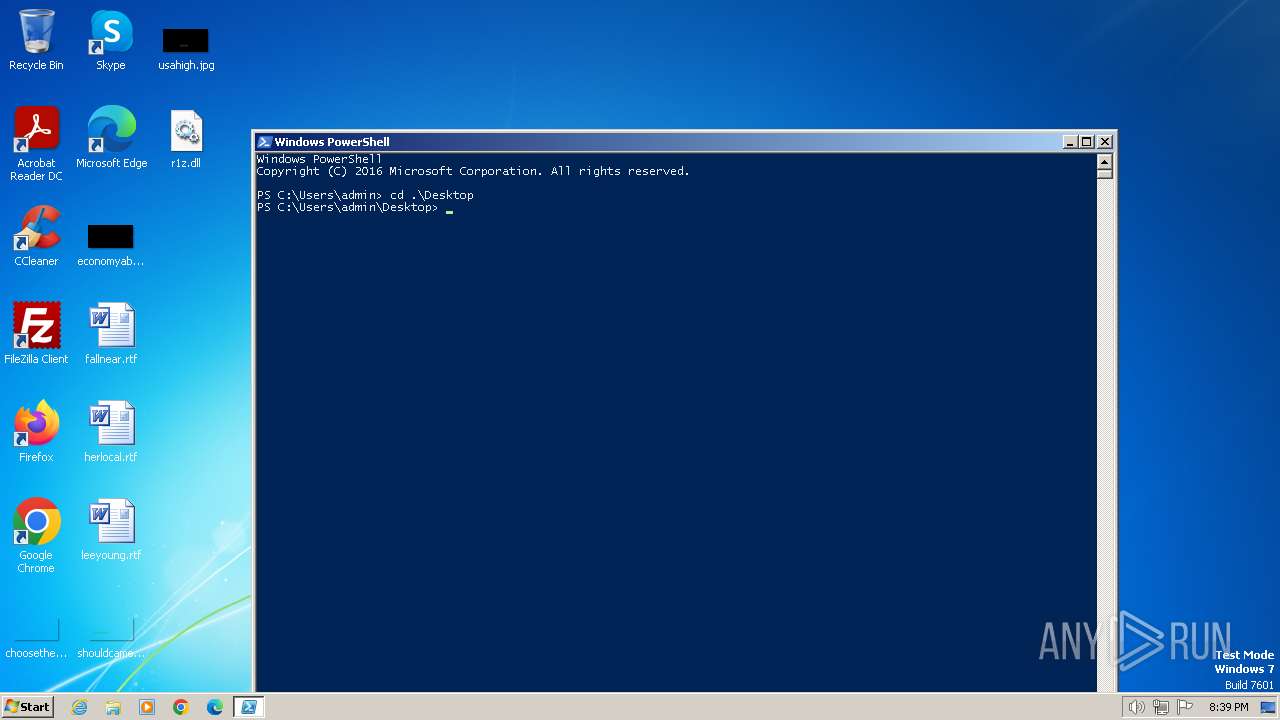
Manual execution by a user
- wmpnscfg.exe (PID: 124)
- explorer.exe (PID: 2088)
- powershell.exe (PID: 1936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:11:22 23:33:29+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug, DLL |
| PEType: | PE32+ |
| LinkerVersion: | 2.4 |
| CodeSize: | 455680 |
| InitializedDataSize: | 950272 |
| UninitializedDataSize: | 90112 |
| EntryPoint: | 0x1320 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
43
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1536 | "C:\Windows\system32\rundll32.exe" r1z.dll TestMain | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
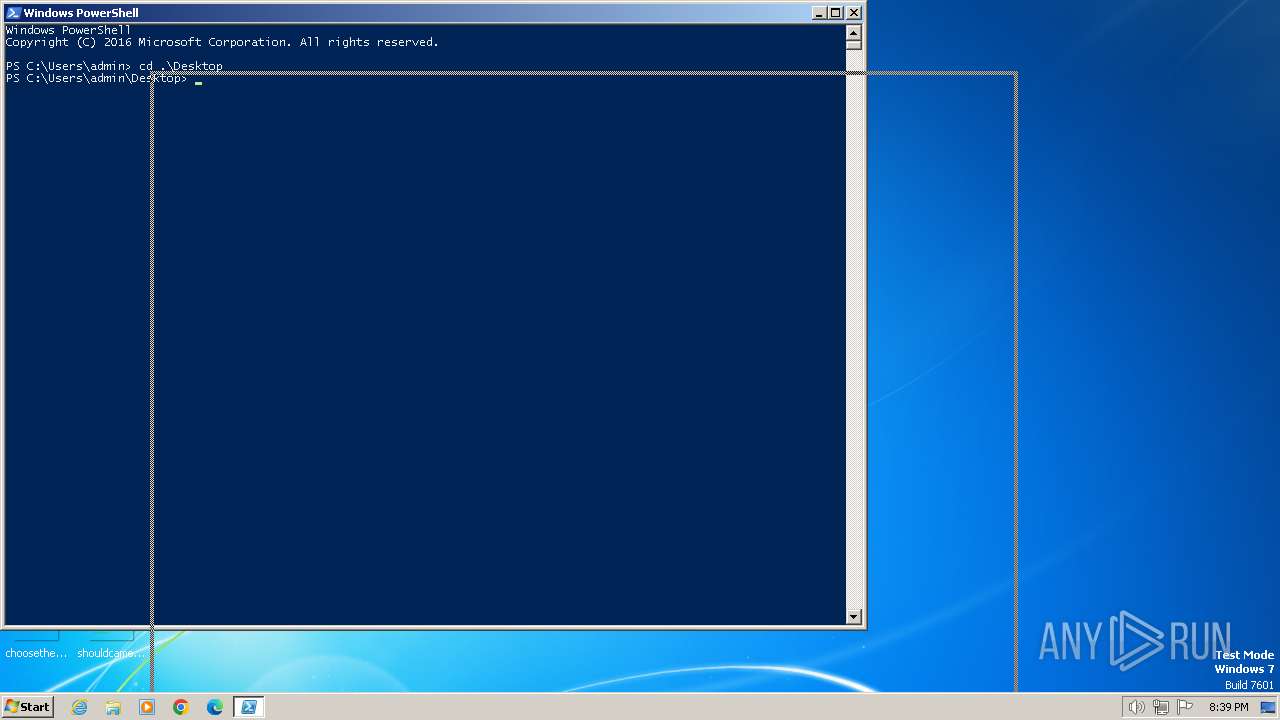
| 1936 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2044 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\r1z.dll.exe", #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Windows\system32\rundll32.exe" r1z.dll | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Windows\system32\rundll32.exe" r1z.dll,TestMain | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Windows\system32\rundll32.exe" r1z.dll,TestMain | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2668 | "C:\Windows\system32\rundll32.exe" r1z.dll,TestMain | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 211
Read events
1 151
Write events
60
Delete events
0
Modification events
| (PID) Process: | (1936) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1936) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1936) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1936) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1936) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1936 | powershell.exe | C:\Users\admin\AppData\Local\Temp\j2bqy0lo.mue.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Local\Temp\2a1zhvsa.j54.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2JJ046X65IO090L0DS3D.temp | binary | |
MD5:08BD373ED63BA050A5503C1EE55B5FED | SHA256:4A1FCBACF0EA839481C30ABE5FA932761E893AF8175BC925D4071F4D1BBC896F | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:08BD373ED63BA050A5503C1EE55B5FED | SHA256:4A1FCBACF0EA839481C30ABE5FA932761E893AF8175BC925D4071F4D1BBC896F | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe686a.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:DE3E389E155C6845D43C07185A11ACF1 | SHA256:6761E2D1F087BBAA8A8DB8B1294E66088FDBE0B9B7FC6E43476D8B2ABDB79E56 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |