| File name: | 네이버tv_동영상.js |
| Full analysis: | https://app.any.run/tasks/5e4bdf18-e228-4215-a314-d220552a6853 |
| Verdict: | Malicious activity |
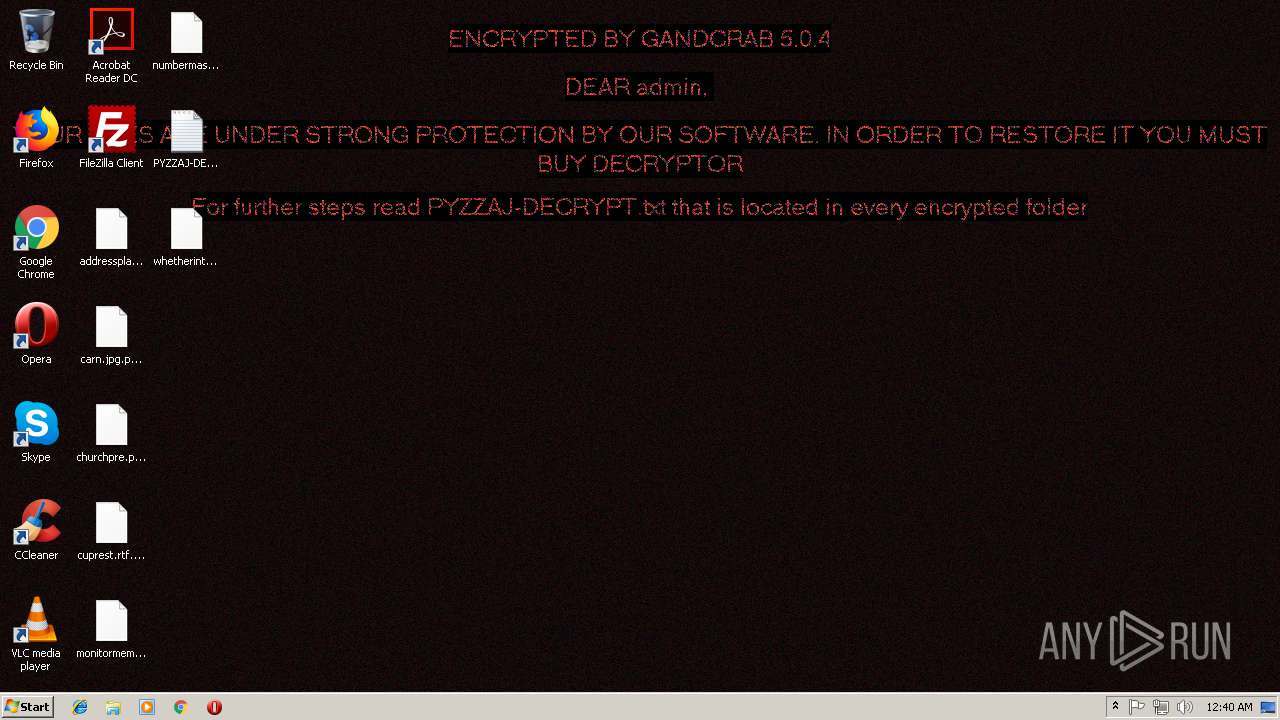
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | November 16, 2018, 00:39:38 |
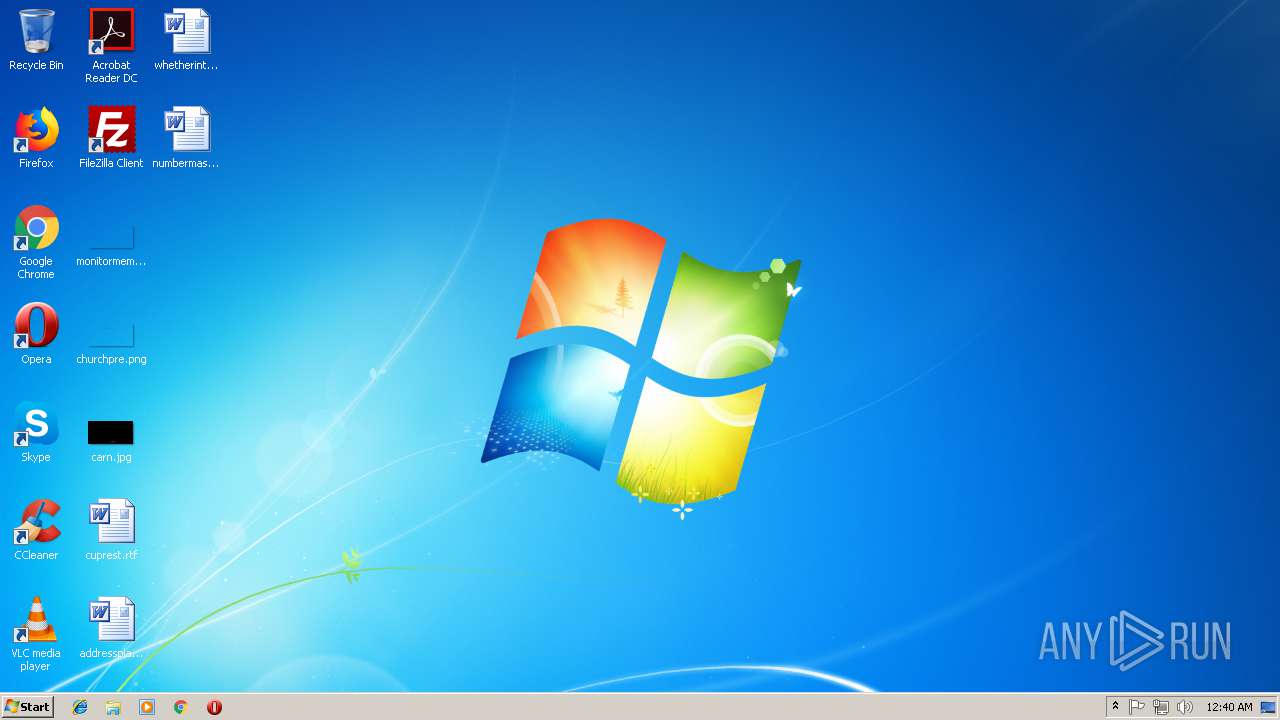
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | E7CBFA441ED6A65D7F9F41A5B3669E8A |
| SHA1: | 3CF08C328E184B98AD05216FDE2BB362200A1EFF |
| SHA256: | 566CFCA87B8B490E0F61F4E828F5493F42E4AEB632F8A660A3CA2FDED4824A23 |
| SSDEEP: | 3072:KmQUqR/sJoovLCq9VpJefws7DBQc2ki41UnS0wFF4hkUpYh6uW8WFMKuLEQmd6M7:KmsmecXMw27jOSVUpYW+fLEQmd6k |
MALICIOUS
Application was dropped or rewritten from another process
- tdmrmaxv.exe (PID: 2900)
GandCrab keys found
- tdmrmaxv.exe (PID: 2900)
Writes file to Word startup folder
- tdmrmaxv.exe (PID: 2900)
Dropped file may contain instructions of ransomware
- tdmrmaxv.exe (PID: 2900)
Actions looks like stealing of personal data
- tdmrmaxv.exe (PID: 2900)
Changes settings of System certificates
- tdmrmaxv.exe (PID: 2900)
Renames files like Ransomware
- tdmrmaxv.exe (PID: 2900)
Deletes shadow copies
- tdmrmaxv.exe (PID: 2900)
Connects to CnC server
- tdmrmaxv.exe (PID: 2900)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 3112)
Reads the cookies of Mozilla Firefox
- tdmrmaxv.exe (PID: 2900)
Creates files in the program directory
- tdmrmaxv.exe (PID: 2900)
Creates files like Ransomware instruction
- tdmrmaxv.exe (PID: 2900)
Adds / modifies Windows certificates
- tdmrmaxv.exe (PID: 2900)
Creates files in the user directory
- tdmrmaxv.exe (PID: 2900)
INFO
Dropped object may contain TOR URL's
- tdmrmaxv.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1416 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | tdmrmaxv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\tdmrmaxv.exe" | C:\Users\admin\tdmrmaxv.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3112 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\네이버tv_동영상.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
523
Read events
473
Write events
45
Delete events
5
Modification events
| (PID) Process: | (3112) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3112) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00700079007A007A0061006A000000 | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A4000052534131000800000100010081D62A7DD33E4DC830F48B30F5C52773409100653E978D667B70DE9D537CCC5E7AB8DAEDC4ABF5B8F389303380643DDE3E2F59BB1EB09CFCFB54282B69D37A56E5F0E587139E169EEC885F85A1A98F289CBCD10AC202A9961D17DC242689E89C03BD2D84F18F177126F18FF91809E21D851B8010BCBDF94F1861AF27F94E25EB8AAB191F44D466B450C60A7482DB62402B06B4D85C2D7CD747F0F4B653B178C6219DC081CE2362670E93843E9D74E5560A779021F5E775A1E5E648BC4BA3E36F906831637F1069C1B148AB788E45E9C89CF7E7839C943A7CF5A78FC4CD2E3F20D4BCBF2B46AB4A002C0BAEF6C0AF5948C257672EBF134DF69CAAB959275B30BA | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 9404000059628DC8DFD87BC89273C847A75E6356904D7E742CF7197C8F044ACFDBD0FF966607C438E829C288CE05503151980306BD4979D231E4808607F71E5F9D9C9C2FF77914980FF387CADF35183FB0B82B00C7BDDF9920E3FFD245C298C37E13A288044622EF546368919BD811DE5320914990AB0AE4EE7F01BC5A31FA7FFD5E2ED2BE9C31A3BACEC6890BF65D893ABF28838281966E5F2328452EDB4047B2E40FC77417E8BDF922CAF4ADED24C97C0F7147676DA3B2C60974F2438E6A1EF83EAF2F63F6521BDCA6E1BE7414F8502CF64439C8F6173566F94CBD60AAF55CBD874B0E49ECACE904B90BE216EBFF77D2B7E3B9B65EE2B0AFEA07F75C0B3EEF14C3D43D89D83F812D69A83C792965835032EAFD89C18FA3F67473CEF2B30310C8527BBD8D61B4E1FADCA45F0F13C14567CE7932600B5B8B31CD24B8EB7E6DE554B43F90A72BD4B331F6C41005F3C02DE41A77A4D31AD78FA123A01E085F0EDE97E9B36C466CBC11AB57635507C592708AB6841A999A1FBBABDED28DB995EF13326EA2455DA0C86B75CFCFF6C68B4A39E1AD37BB6A90F83E09DB2C7A86EDFC817CA16F4230C7A85E8A5F010B613528E1DED38D128EE40277B7EFCFF255A352F5CE7D970A0D53CC8AB7BCA9EFE6DE78A336743570B6B4EAE52DCC6483869873001FC89C682AE879E775C363DAA17CA381ACE4143F0548FF51A575BDA4CA82F3B6219D4E38C16E1D17C40FA4431761DACC05A9CEADAD1B9B3EAA29766E5D644FEFDADAA543E48BF0E83A10BD03D4064A45D77473773597818C08F21319933BA1C36BFD5EDCAF34372CB4DE33C1F509E543C7A0012F37B9A9E516F5DA0F05322ACA39872BA62CC4537B95CB8E6A210AB597DAC334040D6CFBC1C095D7C0880CC412F551F408BE41736B574266DF1455470AA6FFCCFFFCB5CC6081B89E69857E61AC301A562579FF4C6EB65DA7E730F8CB373F224D6300F190938C4D7C24BFDAB1225A79DEAE9C4800367FA1AA4218370B7D45FA1BD3774DD05258BE8A1E5D33829DA13DF7EEEE659040470306F6F2B91FF69269388924FF54A86A44D5B4E77415980CB552EF4ED72B65C06B2AE685AF32B6C3389EA2A47D7291BA69BF170B53B1AFC45B49AA078988DA57C5ABAF396FAA1CBEA885E727B5A7997D4B270F7E3D62682DFA6B567DD963A2433DEE0C29A5233CD112E6B8C80393AE47D89AA6626323FE4C713E650D67C62A661398F6F8A656599371F3EB6EE75C942AB1CA2FF1DB3D1845315535BEB23DC70B5F31E60133E8D0C95348050BBCB5D3A398B0B6A42F15234C6DE192BAA16FC8E8B2AD92A2775A35E80929EDD4CF877111262C9AB344E8E4F71681E075554DD1CA6010A7C09C3C05E5DBFF80506184B4B144EADF9A4072EBDB775972EF38D4261235CA3719EEB84DBC285A8E257096B75B40A08782AF43826545C74E07E1911075714815B228D2A19AD94B47C0CAF8A9F3E7E7DD3DB76188E4A4A44735A309617E25845601F4290AFC489DC21A2AC10EBDC48450C65DE68A48862FD1CA0084FA29D8B51CD0339B659526A125F4A814595F999F71B315C36BFE4981AB07EEEF532B1B8233C74F23B4C94E957903377B5230E5F6252023D74D581CAA0A11E87C256C92C4F8DF807A5AFD1075B1A2D9A8AE8C59753203B8CB18FF8CCAE68E0670022CD7F2FF080B3494EAA3F0410737B58E1BB78DF402EC8A7A04ABE486C5CED854642860FD5F3F9A7F7362F940C81FC2DE710DE8339E92555F01B29D4C1AF8F2389C0A6A5C026A1F064694E238DD890F67C1BFD30190EA6CB13F2C5057A19B3A15FDEAE8B87C71078411CE36178F039507F23591955CCE79A91AD11E4399CC5A6607F59CCC097B10A94F55851C27479777D7642E28F3B79530C394B68C2DBDAF37D5A450E54ADFEDC3486C1FDFC4B8E854EADCA0F4917B7D7EE78284F6951E33176B393A38B378E40373735F1D55647E17A004A15827EBB7291E0014A08EDC64379FCAF0C6E044454EC4A135E4A67CAE1955B0DC0ECF00C3C88863086301866018A9AE8B0E80D86B152621DA5673BD4B98467C63784FEE2D95E5D128C6E88E1FEA6D0E2D74FAA31F7CD2E77AC375902B8A854B863FA924DE4C990A5E8A0A4B31349D8B3347C0B079509F9F3E086C4FB7DCFEAE9F69DD0598E65794CBE8895802CF4511F1CA577E929C88655F79B0E6F3BB24773A65E610D050373B54D5BE9043C819B1D70B4E1F003DC84BE8B498ECFDC9CFD89BC20ACDCCADFA35073235C2C3CB6BFD8DC312B4902F1ABA3685D54BC162083F8120E2EF2AA8E794BBF77F87A44F07F7EF7A102F445AF4F0F209AA3D6A8CFDA9821943B59C8CD1868C906132ABBAF16A62CC612890C04C29BEA2AC4D0AFF | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tdmrmaxv_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tdmrmaxv_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2900) tdmrmaxv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\tdmrmaxv_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
278
Text files
213
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | tdmrmaxv.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Local\VirtualStore\PYZZAJ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\PYZZAJ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\PYZZAJ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2900 | tdmrmaxv.exe | C:\Users\admin\AppData\PYZZAJ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
58
DNS requests
27
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | tdmrmaxv.exe | GET | — | 78.46.77.98:80 | http://www.2mmotorsport.biz/ | DE | — | — | suspicious |
2900 | tdmrmaxv.exe | GET | — | 212.59.186.61:80 | http://www.hotelweisshorn.com/ | CH | — | — | malicious |
2900 | tdmrmaxv.exe | GET | 301 | 104.24.22.22:80 | http://www.belvedere-locarno.com/ | US | — | — | shared |
2900 | tdmrmaxv.exe | GET | 301 | 83.138.82.107:80 | http://www.swisswellness.com/ | DE | — | — | whitelisted |
2900 | tdmrmaxv.exe | GET | 302 | 192.185.159.253:80 | http://www.pizcam.com/ | US | — | — | malicious |
2900 | tdmrmaxv.exe | GET | 301 | 80.244.187.247:80 | http://www.hotelfarinet.com/ | GB | — | — | malicious |
2900 | tdmrmaxv.exe | GET | — | 217.26.53.37:80 | http://www.hrk-ramoz.com/ | CH | — | — | malicious |
2900 | tdmrmaxv.exe | GET | 301 | 212.59.186.61:80 | http://www.morcote-residenza.com/ | CH | — | — | malicious |
2900 | tdmrmaxv.exe | GET | — | 69.16.175.10:80 | http://www.hardrockhoteldavos.com/ | US | — | — | whitelisted |
2900 | tdmrmaxv.exe | GET | 301 | 83.166.138.7:80 | http://www.whitepod.com/ | CH | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | tdmrmaxv.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
2900 | tdmrmaxv.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
2900 | tdmrmaxv.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
2900 | tdmrmaxv.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
2900 | tdmrmaxv.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
2900 | tdmrmaxv.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
2900 | tdmrmaxv.exe | 138.201.162.99:443 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
2900 | tdmrmaxv.exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
2900 | tdmrmaxv.exe | 192.185.159.253:443 | www.pizcam.com | CyrusOne LLC | US | malicious |
2900 | tdmrmaxv.exe | 83.138.82.107:80 | www.swisswellness.com | hostNET Medien GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
www.whitepod.com |
| whitelisted |
www.hardrockhoteldavos.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2900 | tdmrmaxv.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
2900 | tdmrmaxv.exe | A Network Trojan was detected | ET TROJAN [eSentire] Win32/GandCrab v4/5 Ransomware CnC Activity |
2900 | tdmrmaxv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2900 | tdmrmaxv.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (jpg) |
2900 | tdmrmaxv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2900 | tdmrmaxv.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
2900 | tdmrmaxv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2900 | tdmrmaxv.exe | A Network Trojan was detected | ET POLICY Data POST to an image file (gif) |
2900 | tdmrmaxv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |
2900 | tdmrmaxv.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/GandCrab Ransomware CnC Activity |