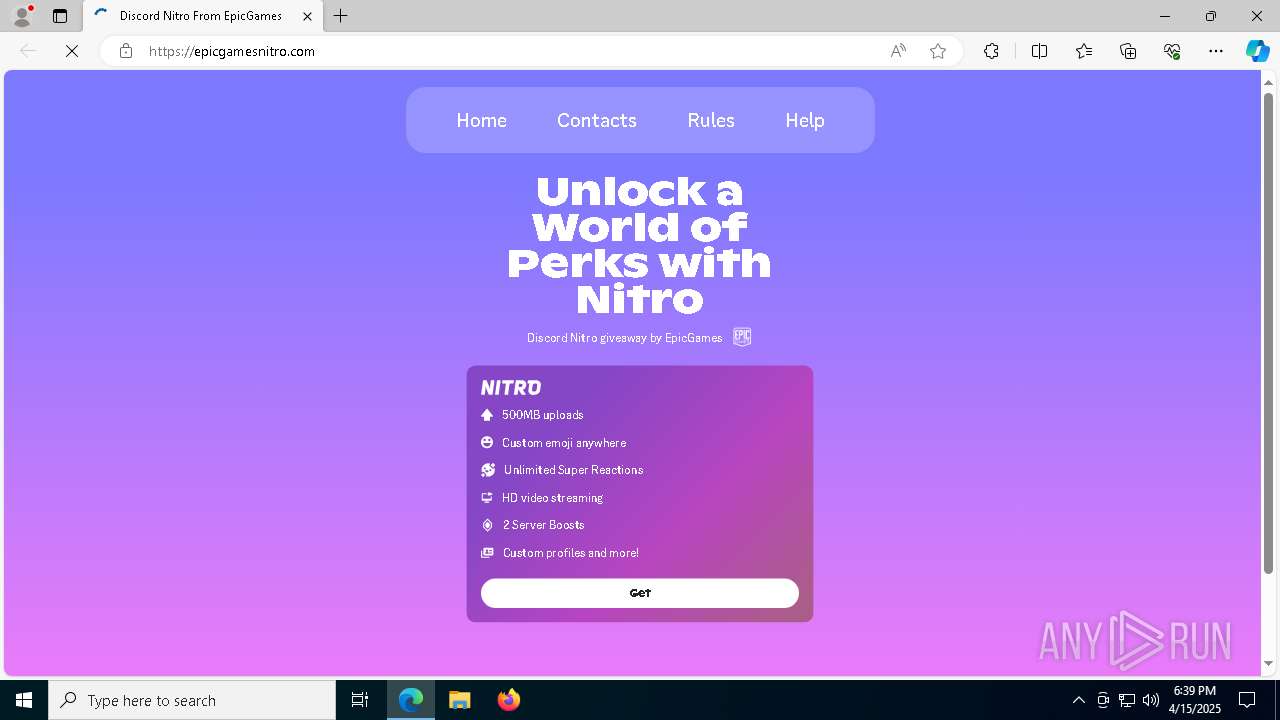
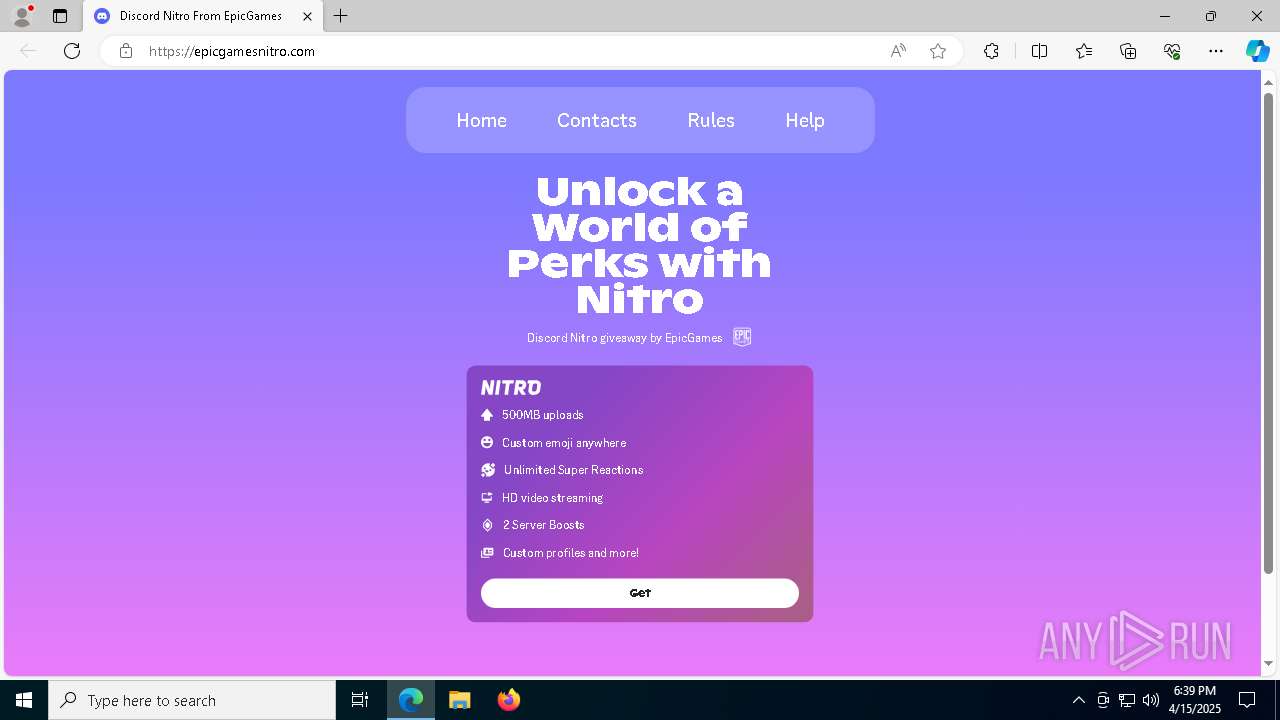
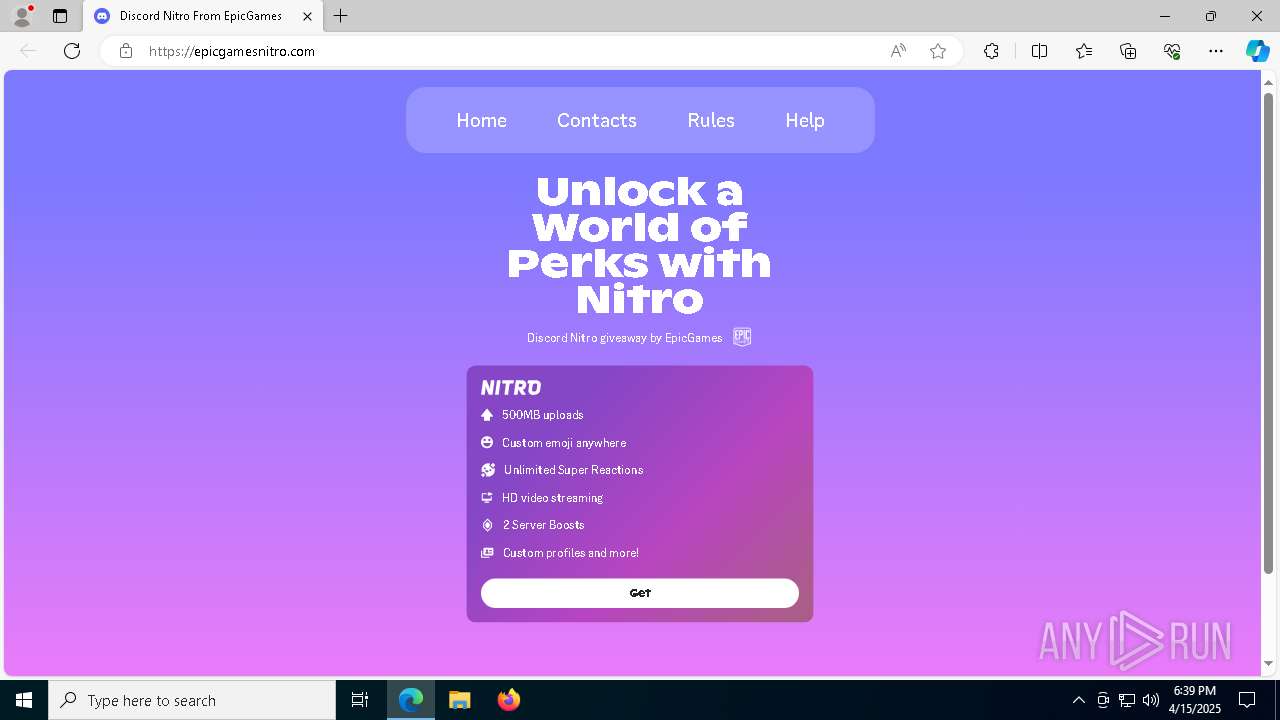
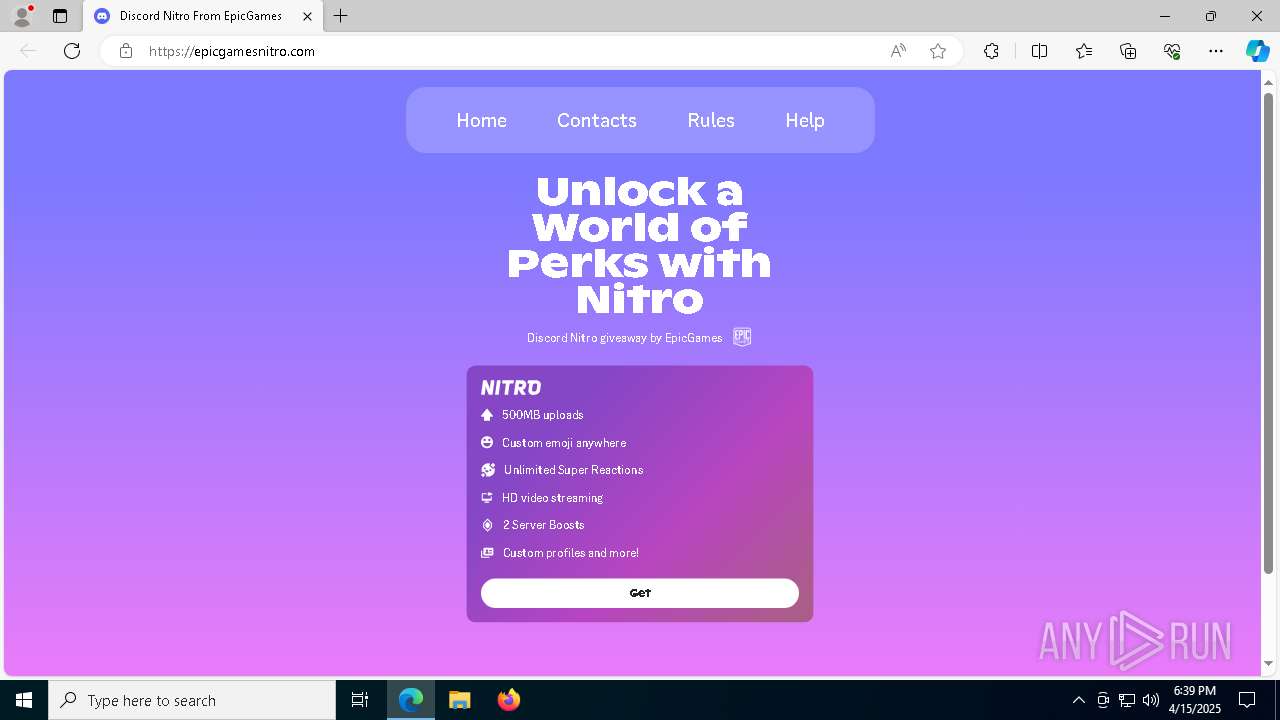
| URL: | https://u.to/TUc6Ig |
| Full analysis: | https://app.any.run/tasks/c7933bf0-e753-480c-a77d-eb1a434cf203 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 18:38:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 3B4746EE552792DAADE32BC36579E2DD |
| SHA1: | 2E37B5C86EDE681AE86472925BDFA53D0D3ECEFB |
| SHA256: | 5667B25E41607437C3DEDD7692064B82FA9ACC54DEECF55005A98D65836833A8 |
| SSDEEP: | 3:N8oXkC:2oUC |
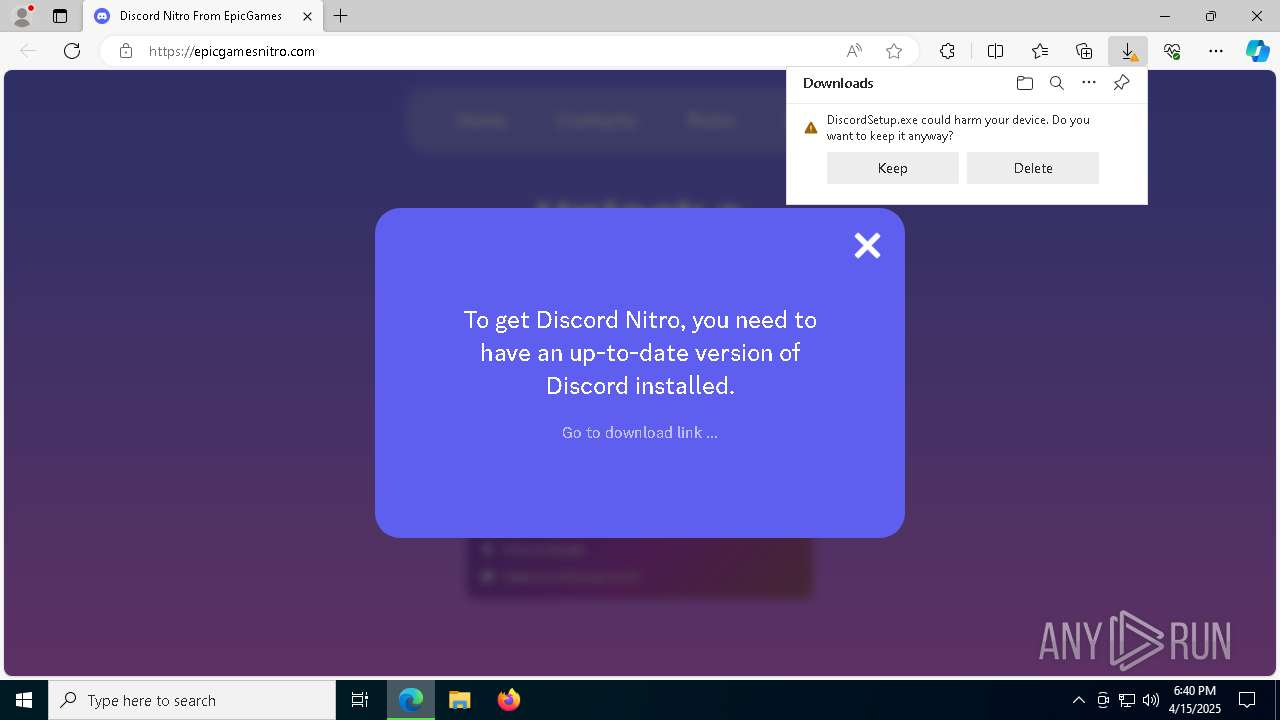
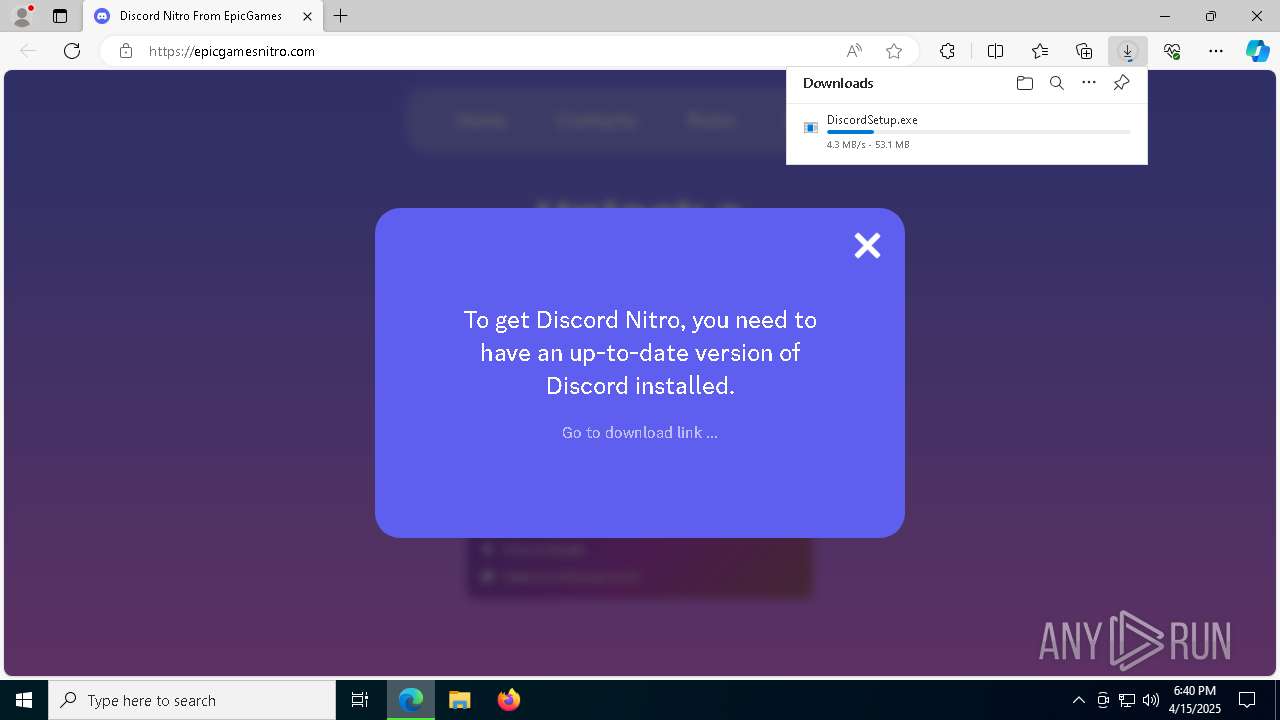
MALICIOUS
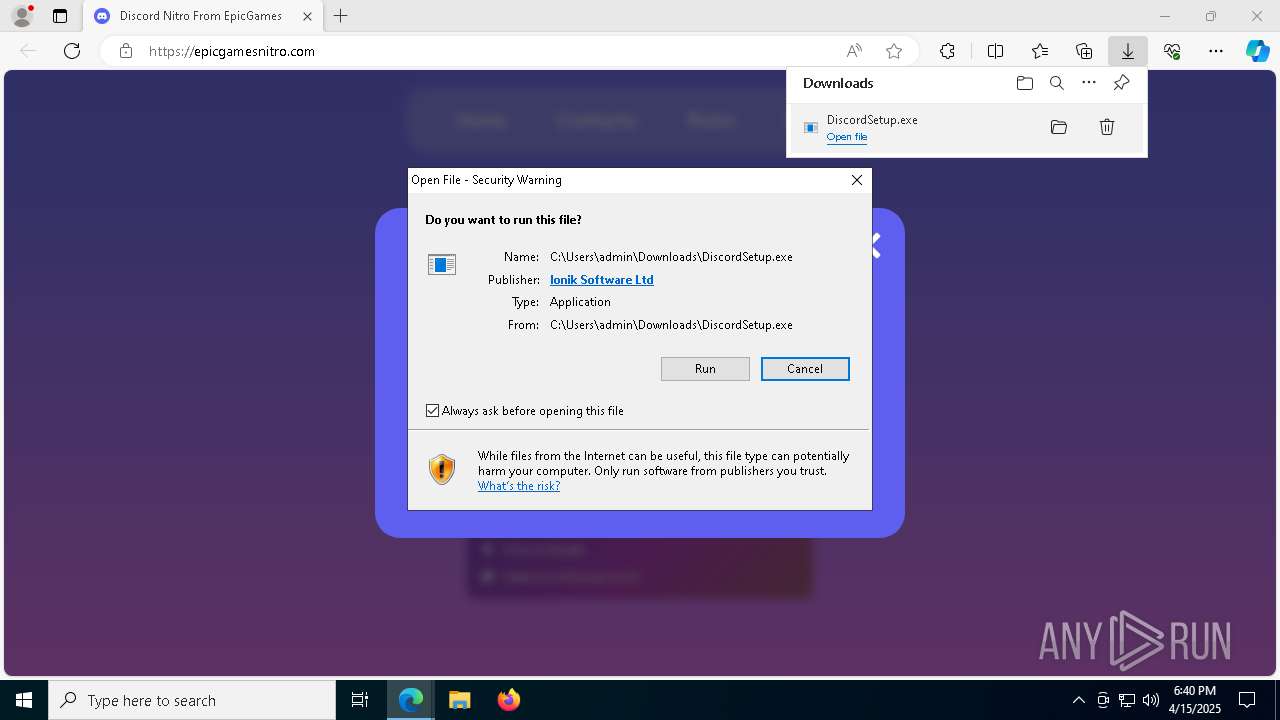
Executing a file with an untrusted certificate
- DiscordSetup.exe (PID: 8172)
Opens an HTTP connection (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Sends HTTP request (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Creates internet connection object (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Creates a new folder (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 2800)
Accesses environment variables (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Gets %appdata% folder path (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Checks whether a specified folder exists (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Gets path to any of the special folders (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Uses base64 encoding (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Bypass execution policy to execute commands
- powershell.exe (PID: 3124)
- powershell.exe (PID: 5576)
Changes powershell execution policy (Bypass)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Uses sleep, probably for evasion detection (SCRIPT)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- CfgHelper.exe (PID: 5324)
Accesses the network adapter (Win32_NetworkAdapter) via WMI (SCRIPT)
- CfgHelper.exe (PID: 5324)
Deletes a file (SCRIPT)
- setup_helper.exe (PID: 2800)
Uses Task Scheduler to run other applications
- setup_helper.exe (PID: 2800)
Gets username (SCRIPT)
- setup_helper.exe (PID: 2800)
SUSPICIOUS
Adds, changes, or deletes HTTP request header (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Runs shell command (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- wscript.exe (PID: 7644)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Reads security settings of Internet Explorer
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Executable content was dropped or overwritten
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 2800)
The process executes VB scripts
- DiscordSetup.exe (PID: 8172)
Reads the date of Windows installation
- DiscordSetup.exe (PID: 8172)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7644)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Writes binary data to a Stream object (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Saves data to a binary file (SCRIPT)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 2800)
Executes WMI query (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Gets full path of the running script (SCRIPT)
- setup_helper.exe (PID: 7500)
- CfgHelper.exe (PID: 5324)
Accesses product unique identifier via WMI (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Checks whether a specific file exists (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Changes charset (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Reads data from a binary Stream object (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Sets XML DOM element text (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Base64-obfuscated command line is found
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
BASE64 encoded PowerShell command has been detected
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Starts POWERSHELL.EXE for commands execution
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Creates XML DOM element (SCRIPT)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Adds/modifies Windows certificates
- setup_helper.exe (PID: 2800)
Creates a Folder object (SCRIPT)
- setup_helper.exe (PID: 2800)
Accesses current user name via WMI (SCRIPT)
- setup_helper.exe (PID: 2800)
Gets computer name (SCRIPT)
- CfgHelper.exe (PID: 5324)
Accesses computer name via WMI (SCRIPT)
- CfgHelper.exe (PID: 5324)
INFO
Checks supported languages
- identity_helper.exe (PID: 5864)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Reads Environment values
- identity_helper.exe (PID: 5864)
- DiscordSetup.exe (PID: 8172)
Reads the computer name
- identity_helper.exe (PID: 5864)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Application launched itself
- msedge.exe (PID: 6476)
Reads the software policy settings
- slui.exe (PID: 7516)
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- powershell.exe (PID: 3124)
- setup_helper.exe (PID: 2800)
- powershell.exe (PID: 5576)
- slui.exe (PID: 720)
- CfgHelper.exe (PID: 5324)
Executable content was dropped or overwritten
- msedge.exe (PID: 6476)
- msedge.exe (PID: 7000)
Reads Microsoft Office registry keys
- DiscordSetup.exe (PID: 8172)
The sample compiled with english language support
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 2800)
- msedge.exe (PID: 7000)
Process checks computer location settings
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Creates files or folders in the user directory
- DiscordSetup.exe (PID: 8172)
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
Reads the machine GUID from the registry
- setup_helper.exe (PID: 7500)
- setup_helper.exe (PID: 2800)
- CfgHelper.exe (PID: 5324)
Create files in a temporary directory
- powershell.exe (PID: 3124)
- powershell.exe (PID: 5576)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3124)
- powershell.exe (PID: 5576)
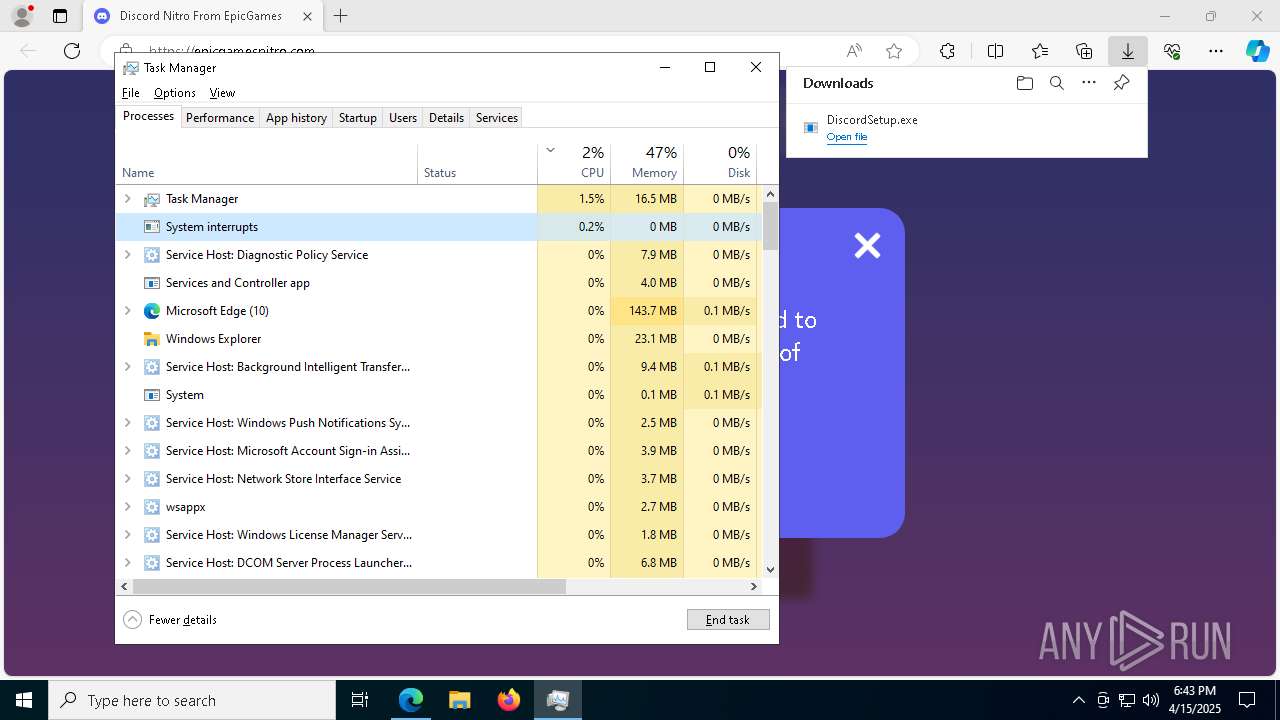
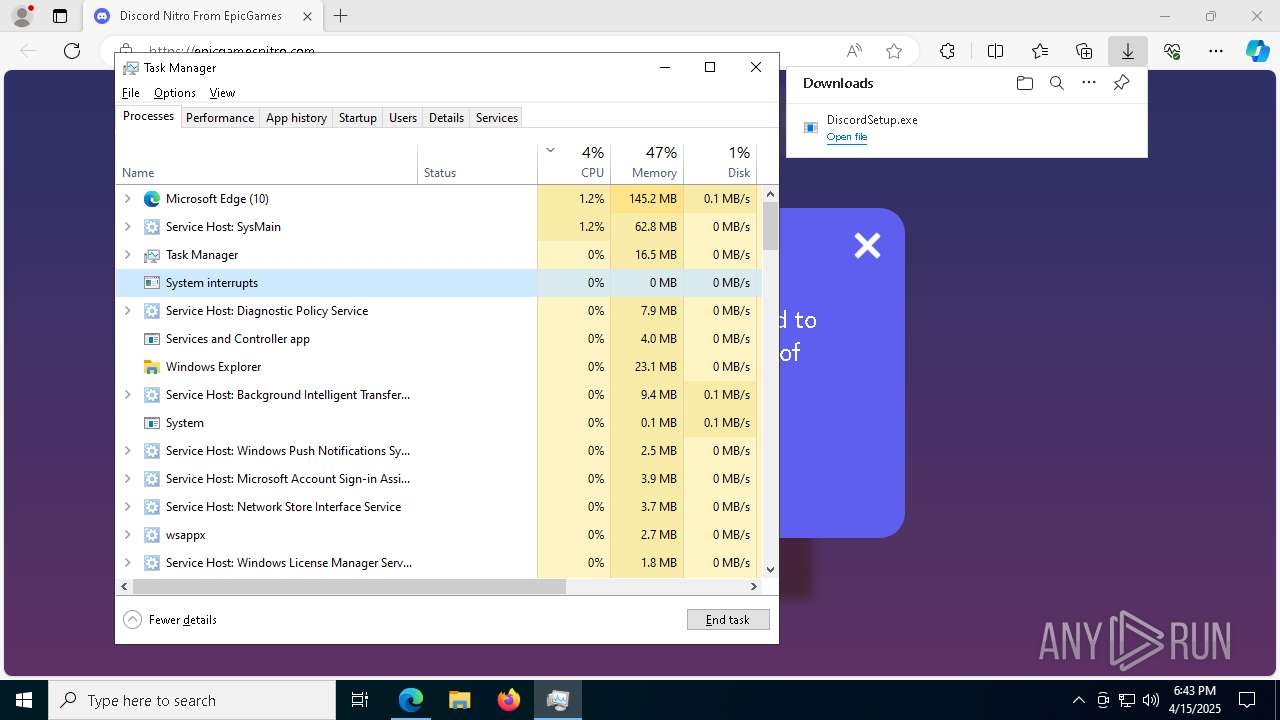
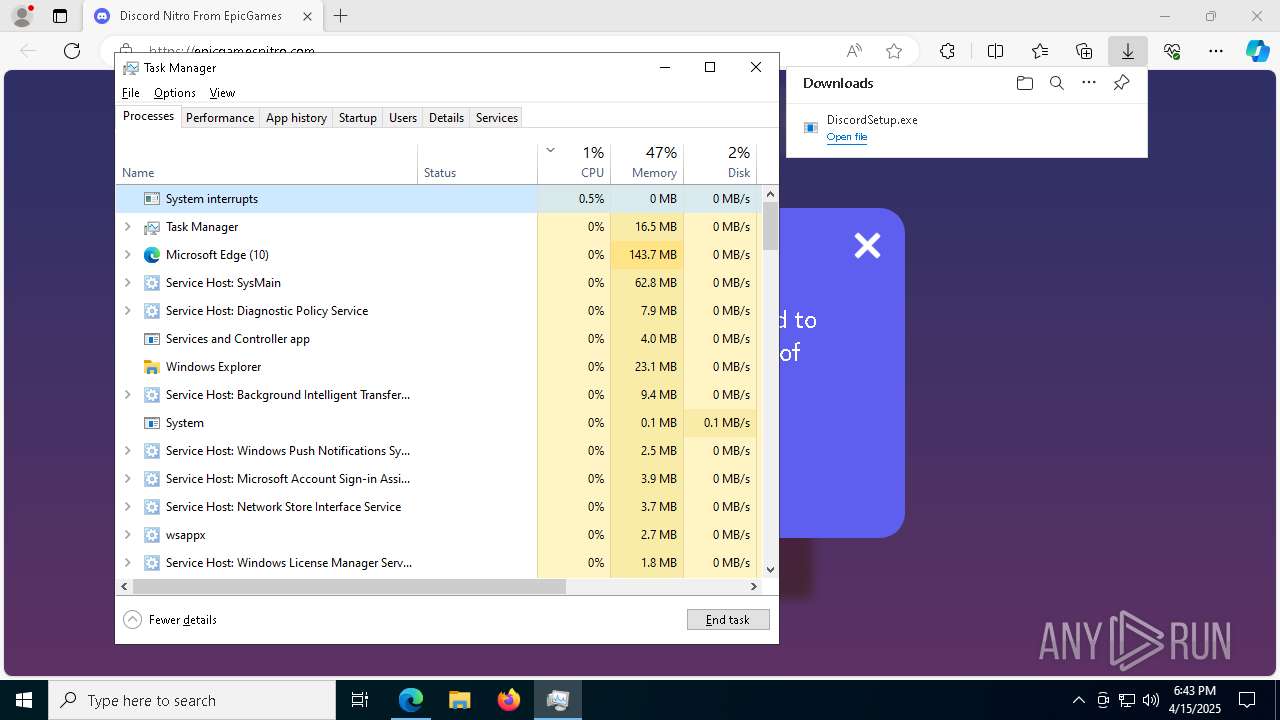
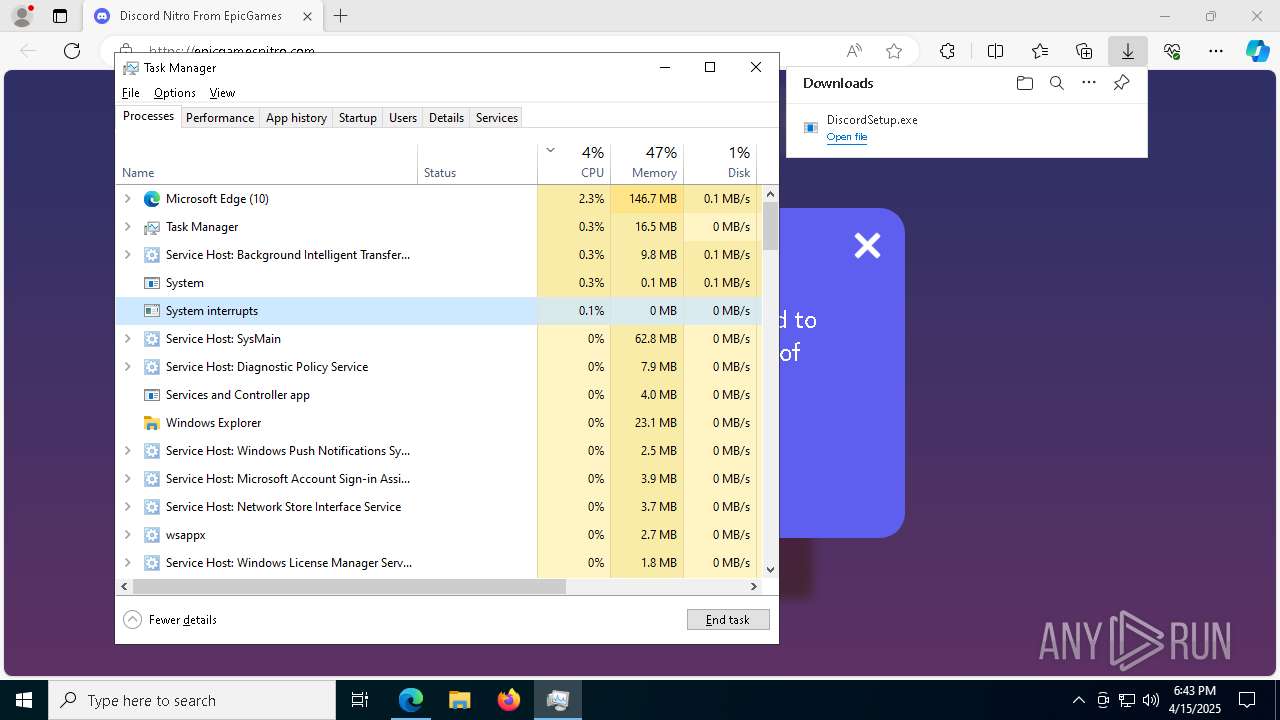
Reads security settings of Internet Explorer
- powershell.exe (PID: 3124)
- Taskmgr.exe (PID: 5164)
- powershell.exe (PID: 5576)
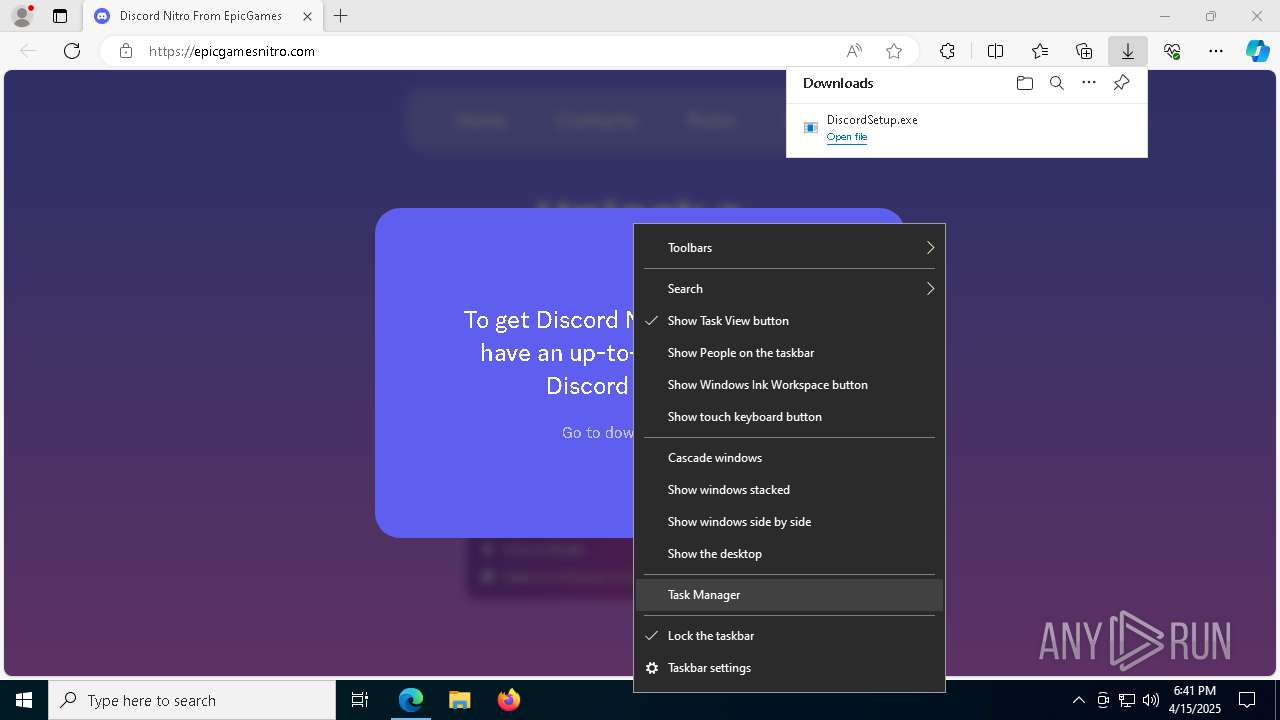
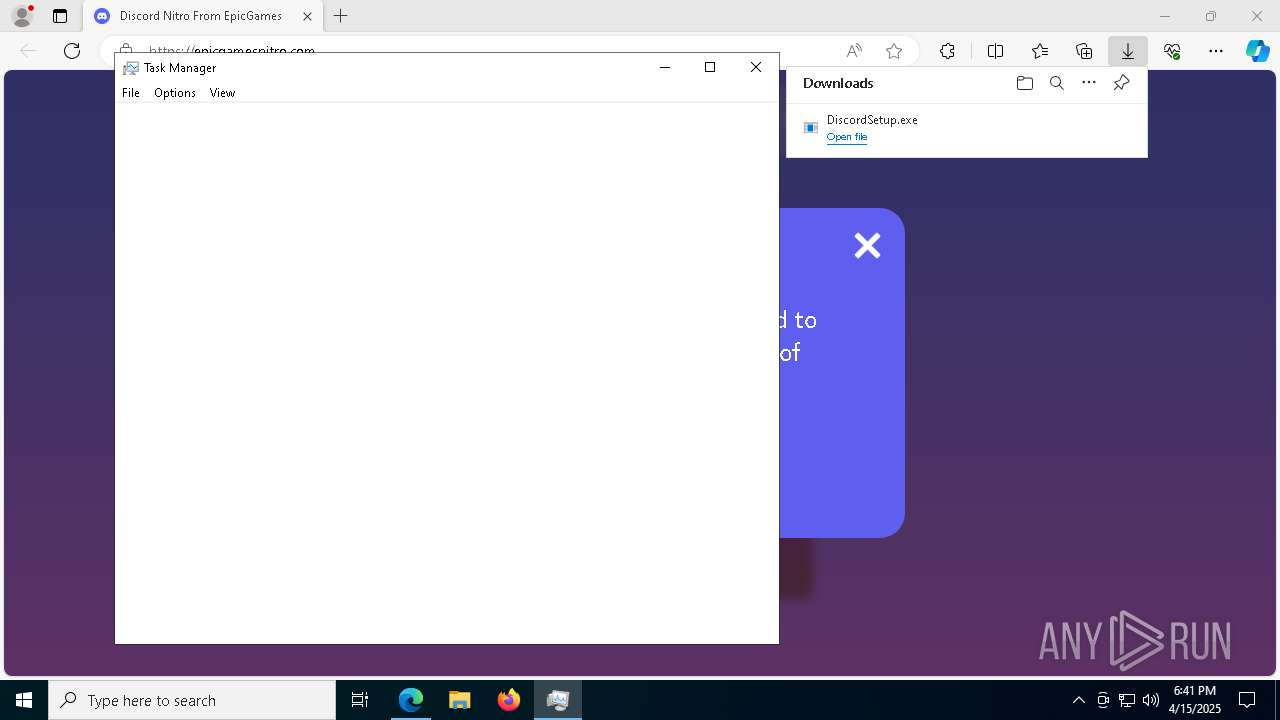
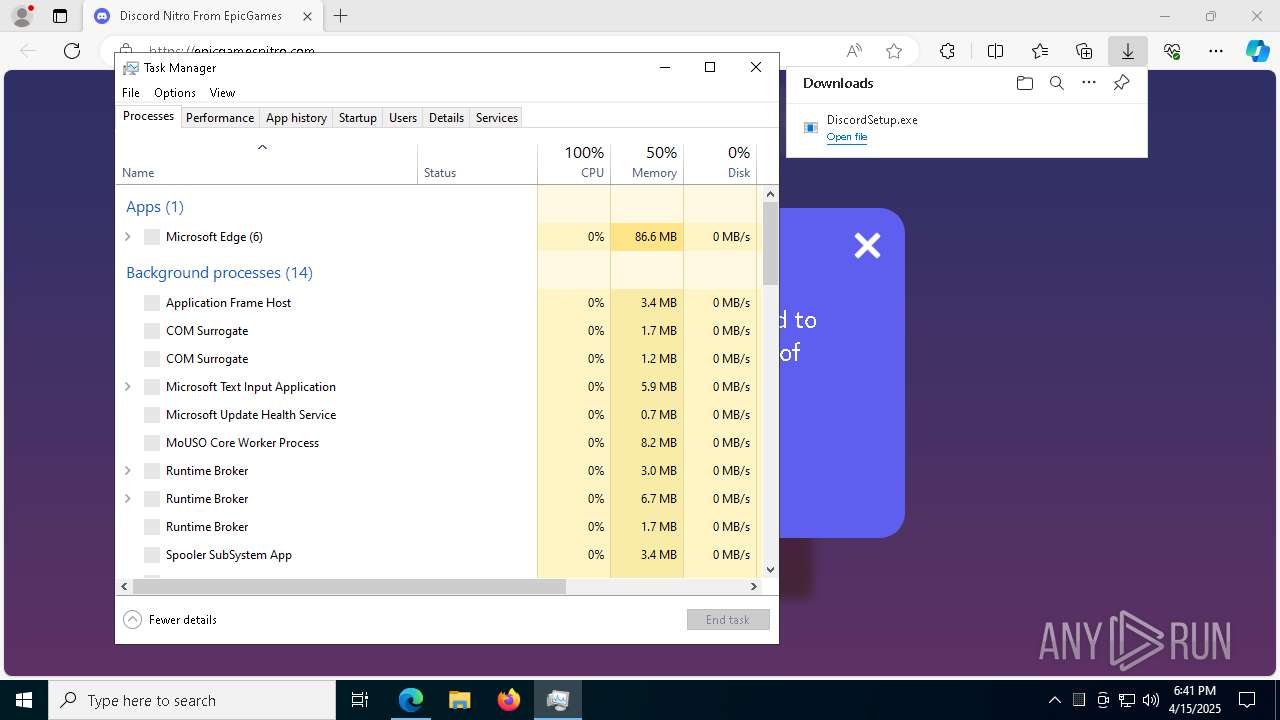
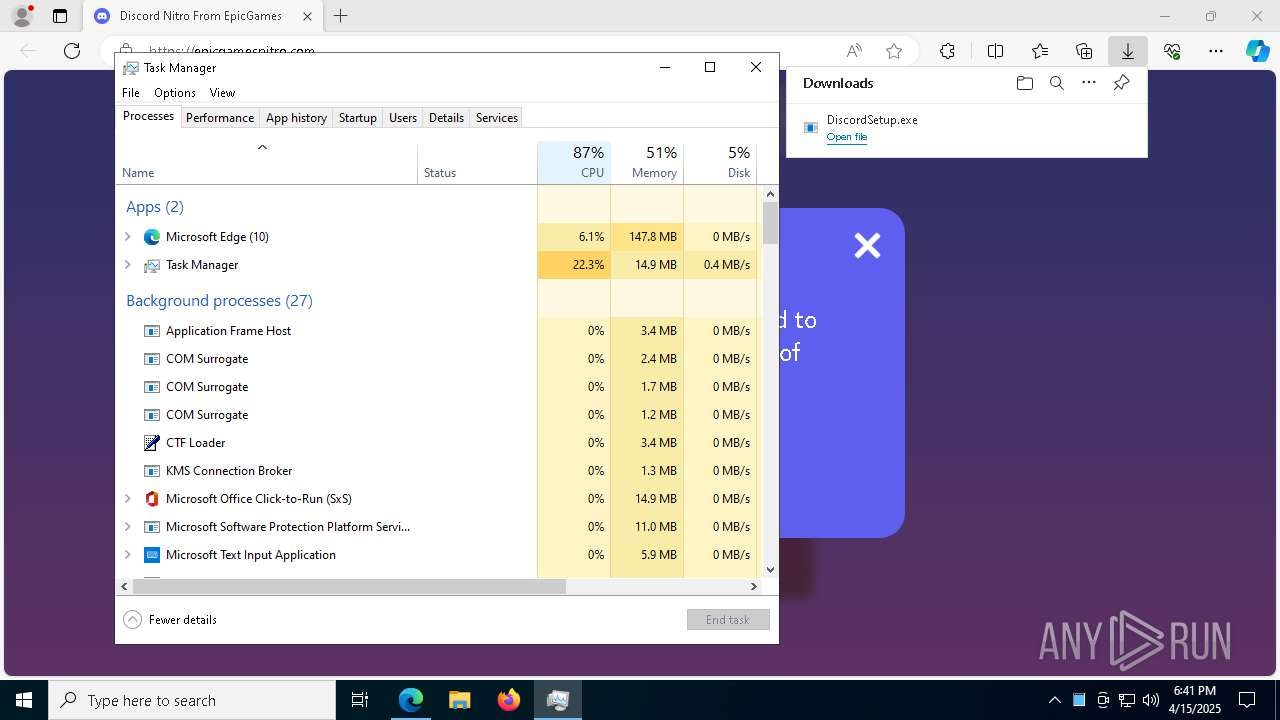
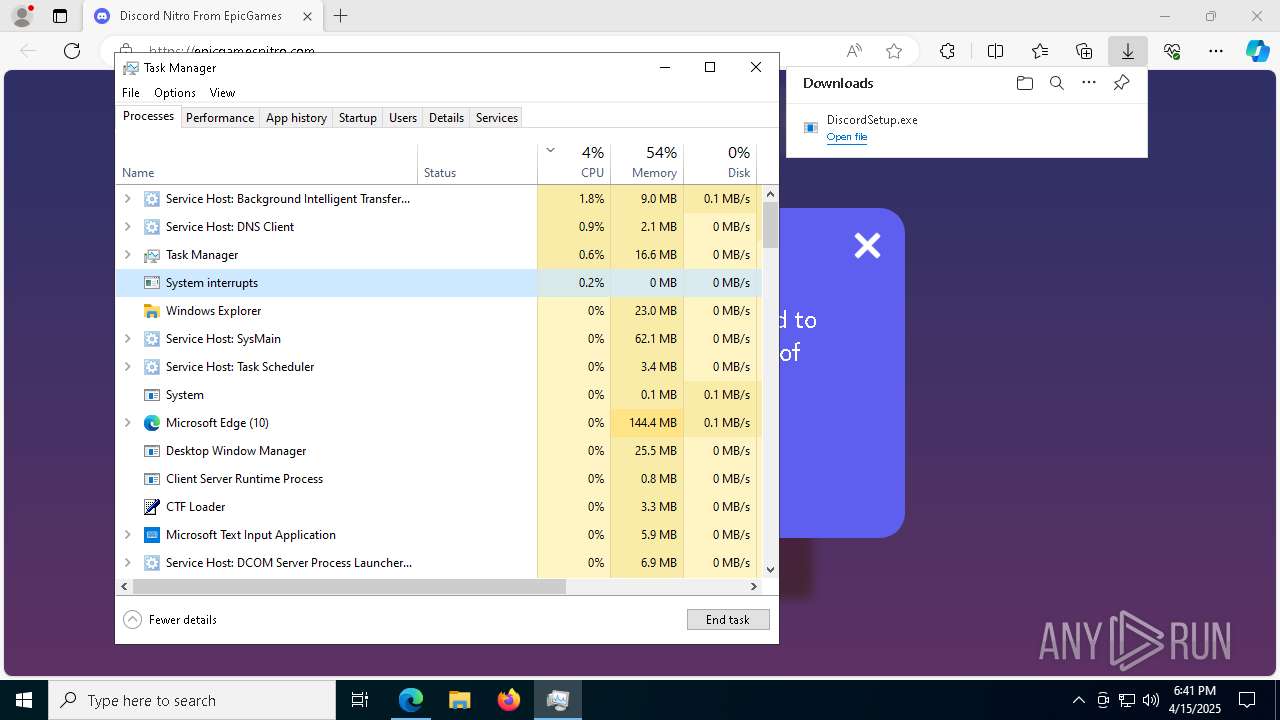
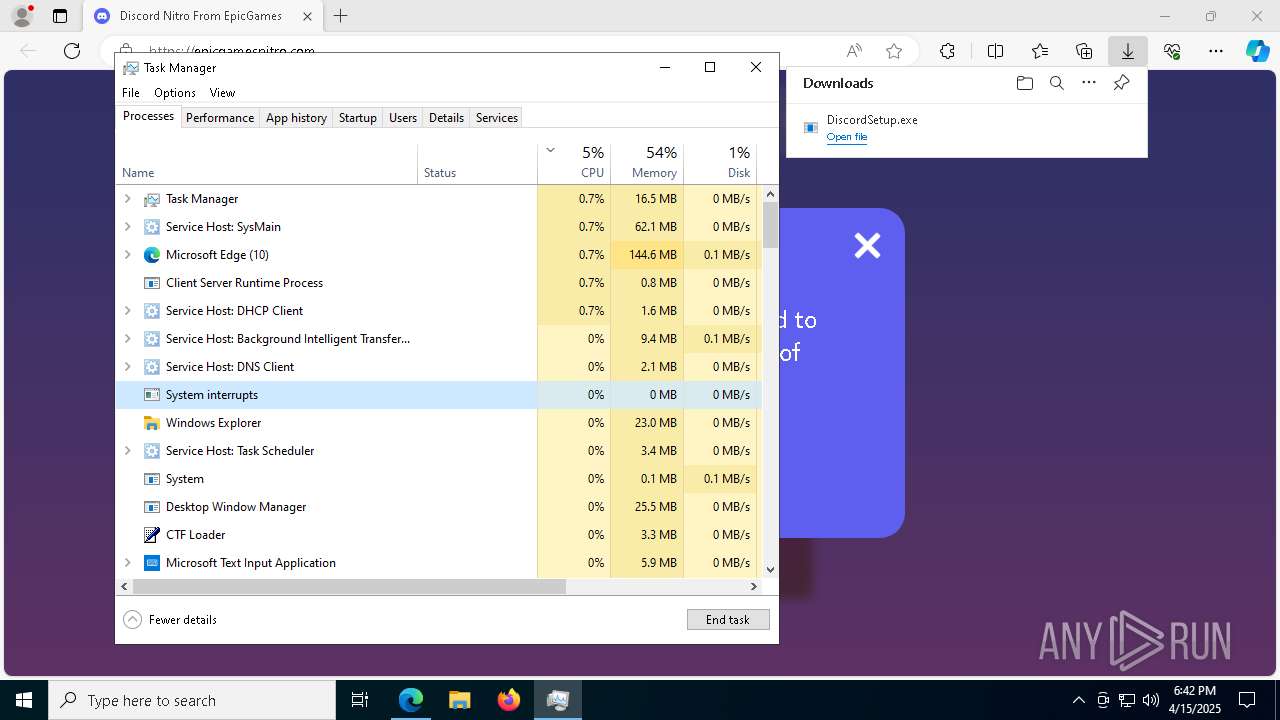
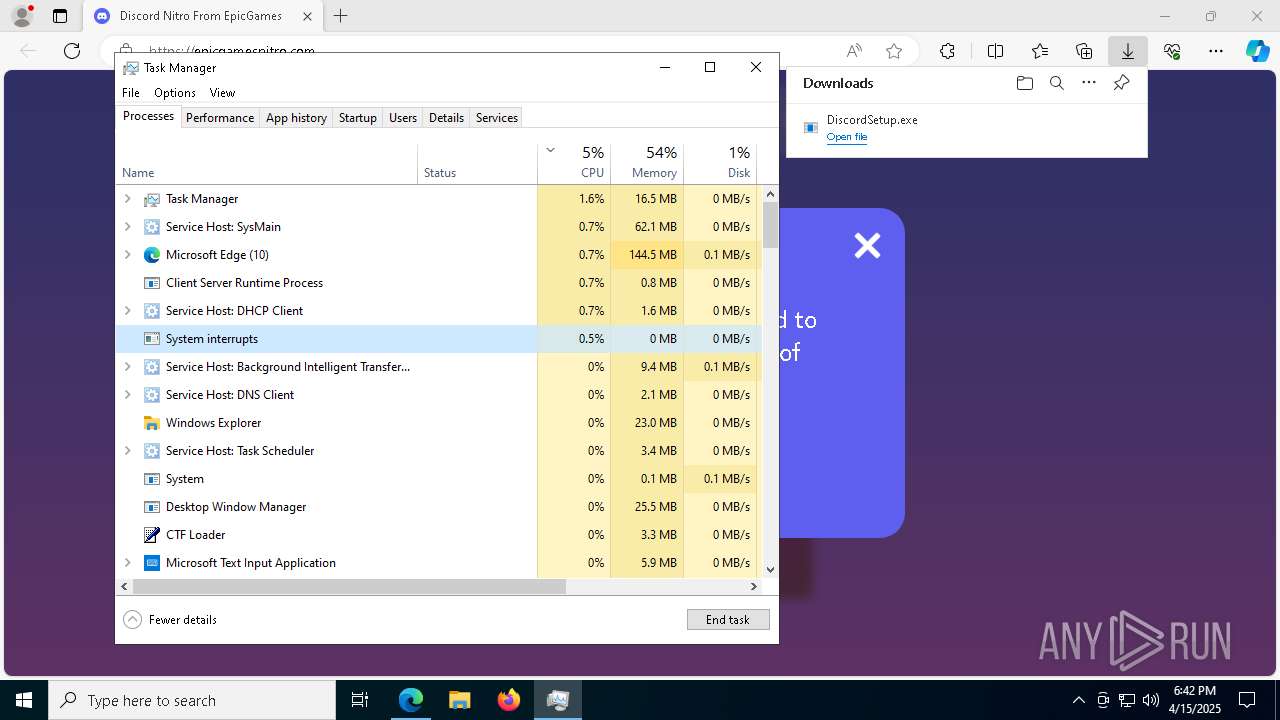
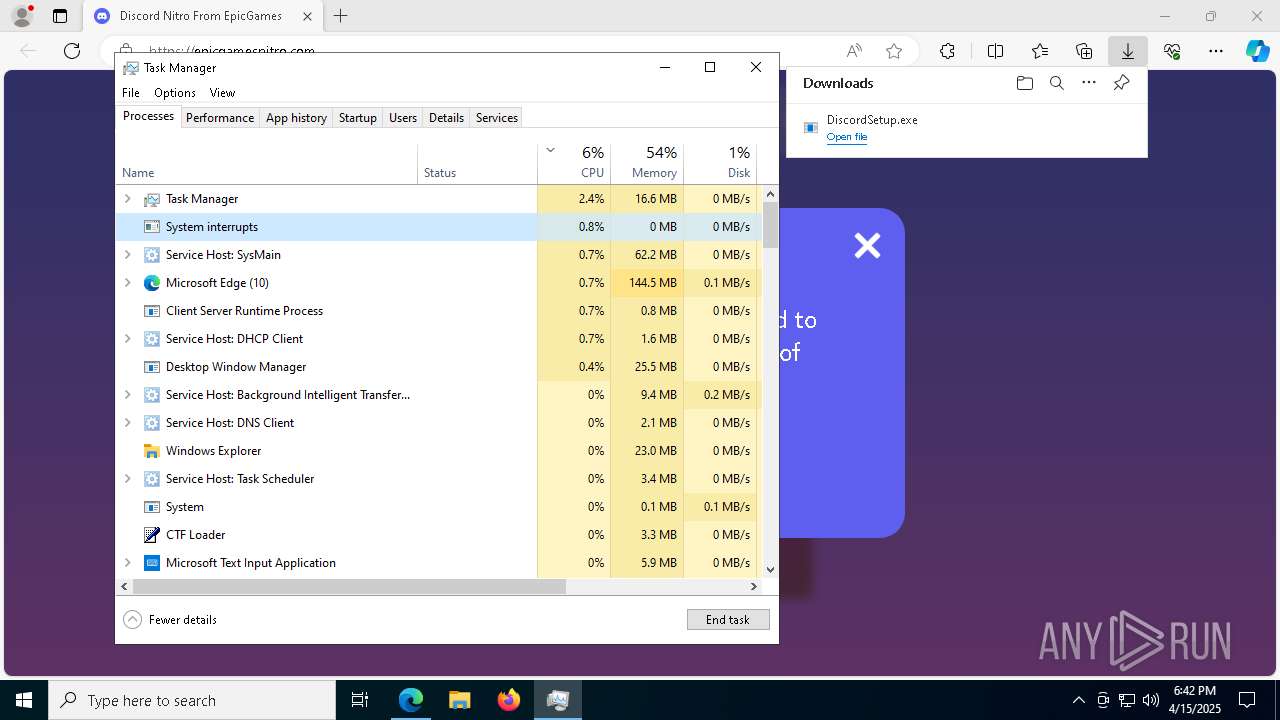
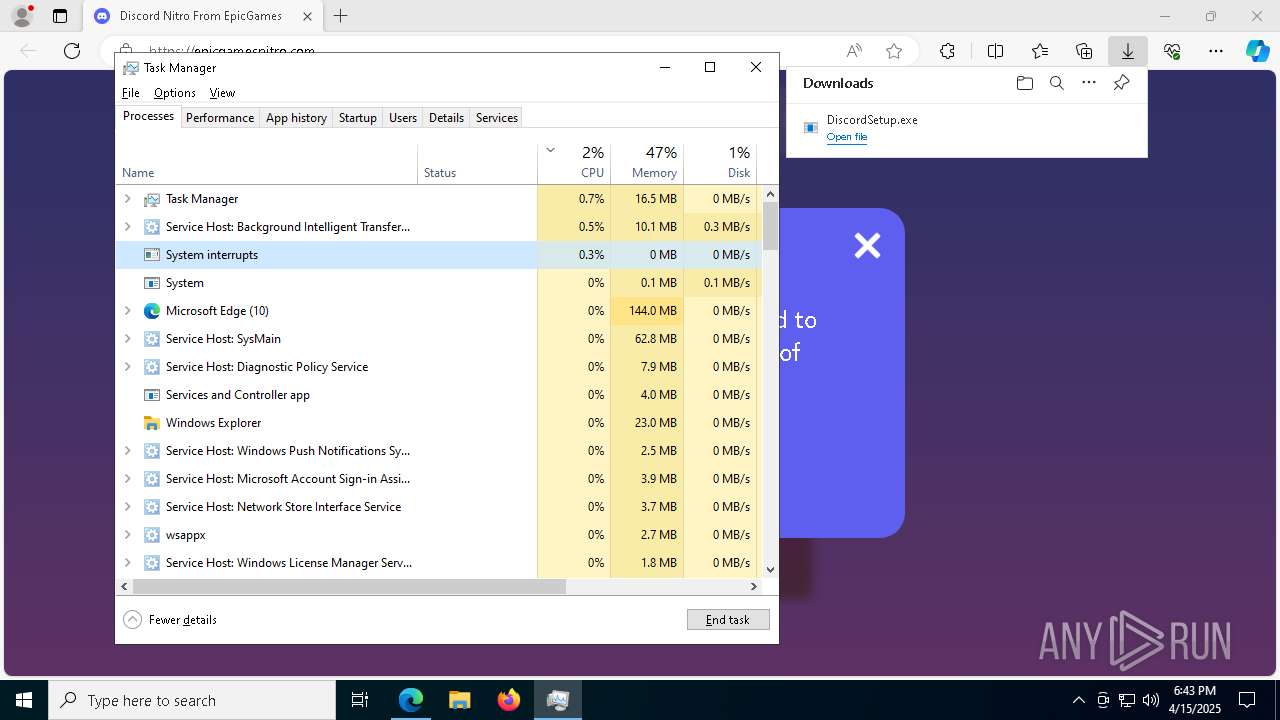
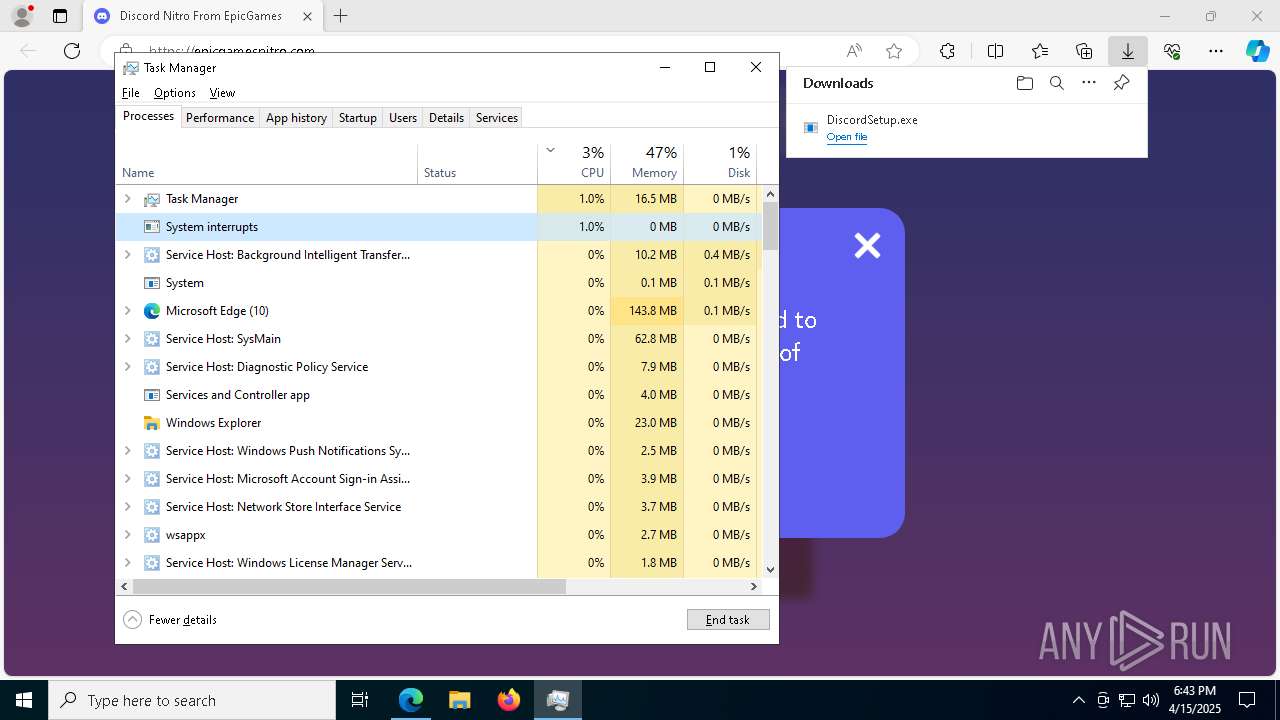
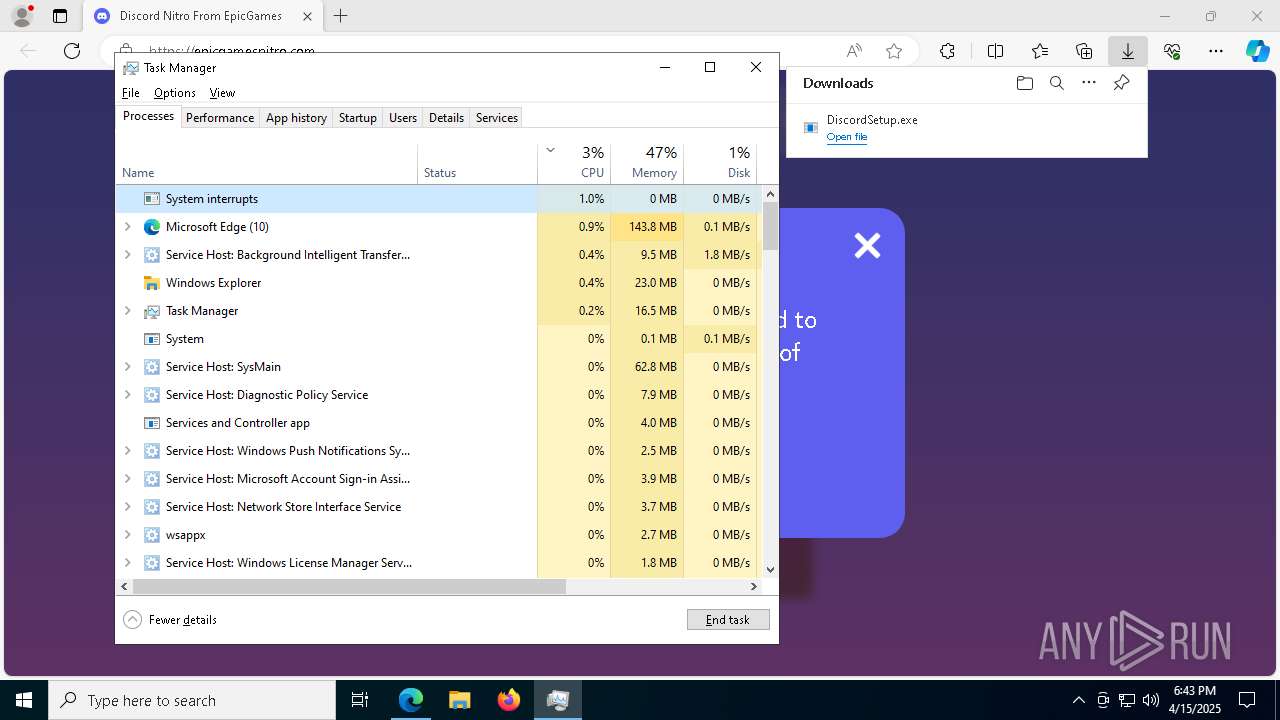
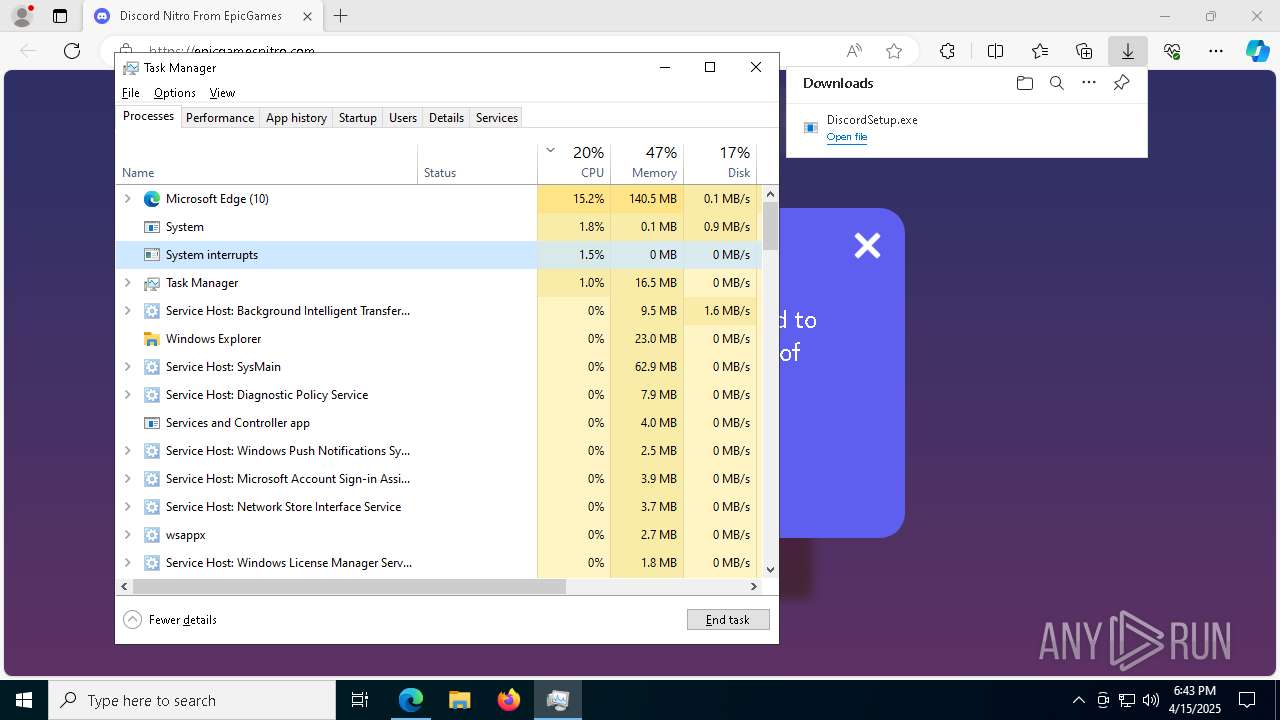
Manual execution by a user
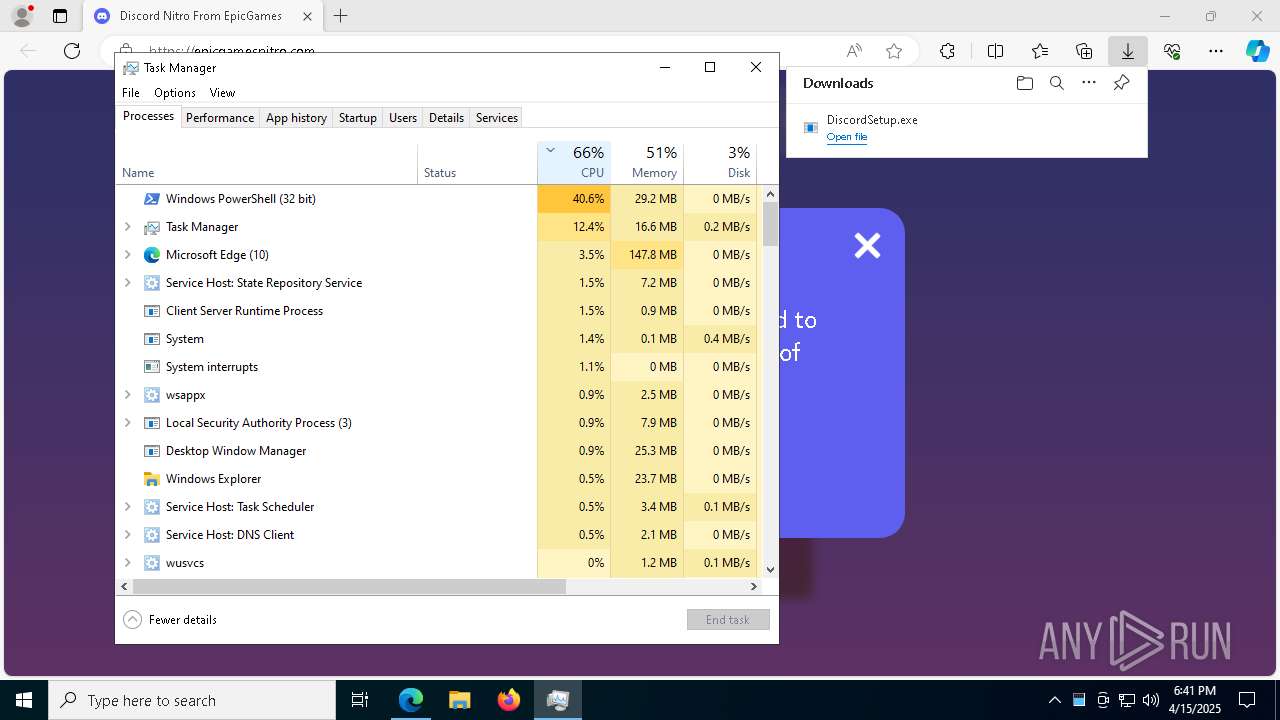
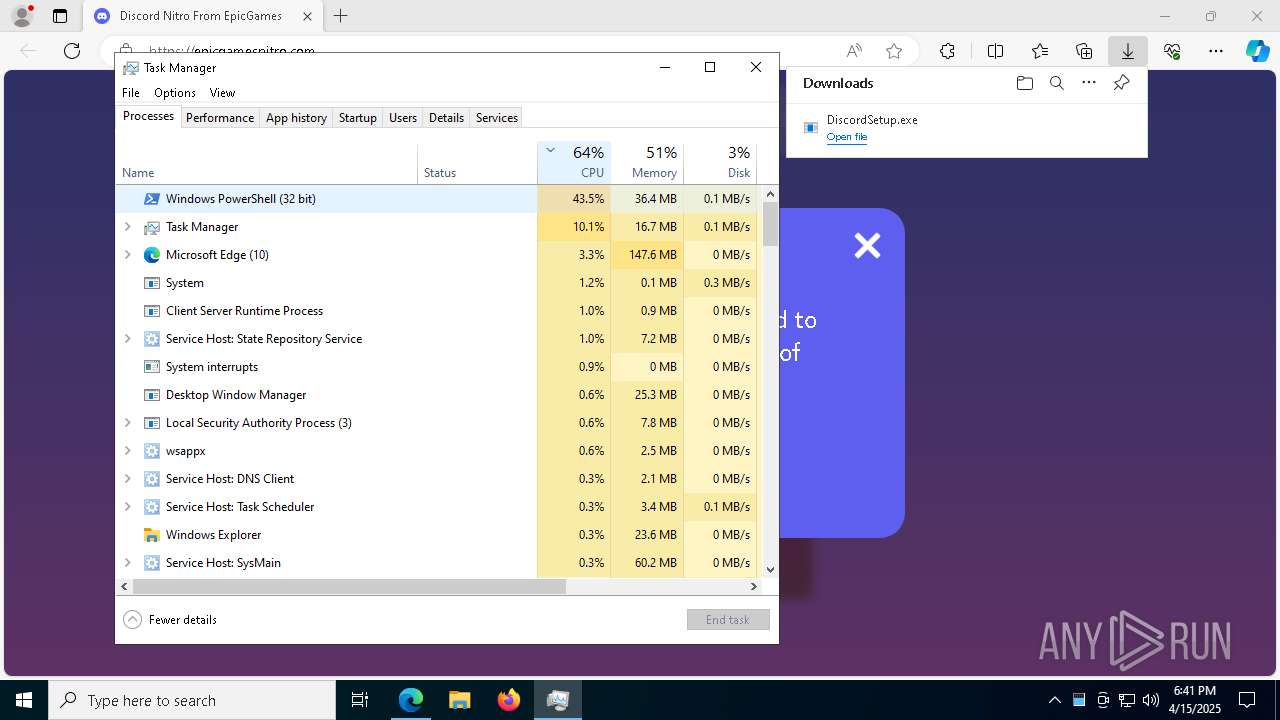
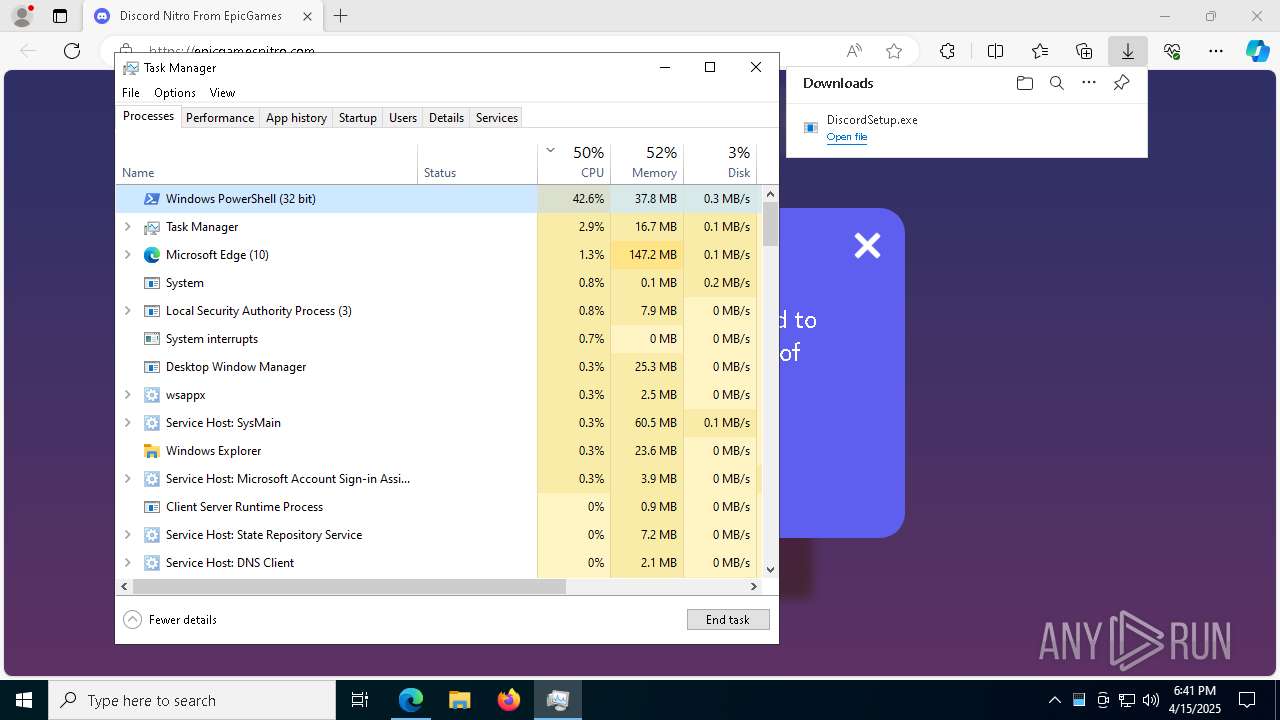
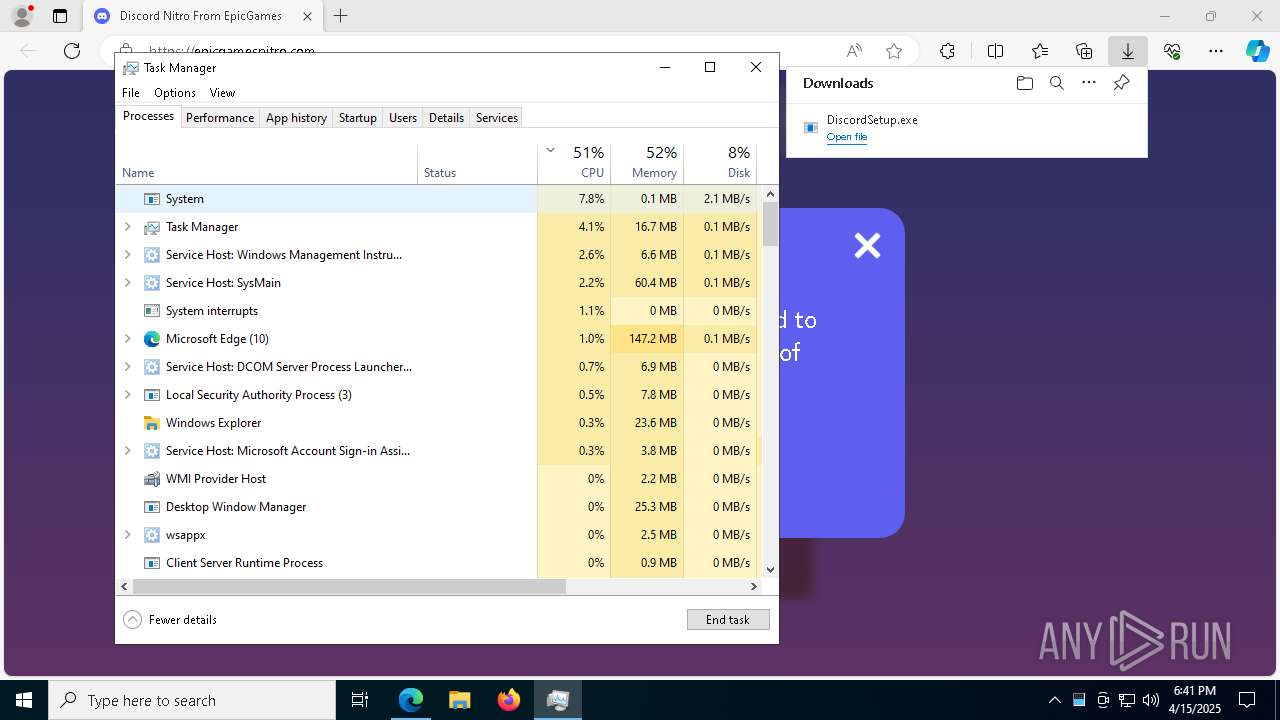
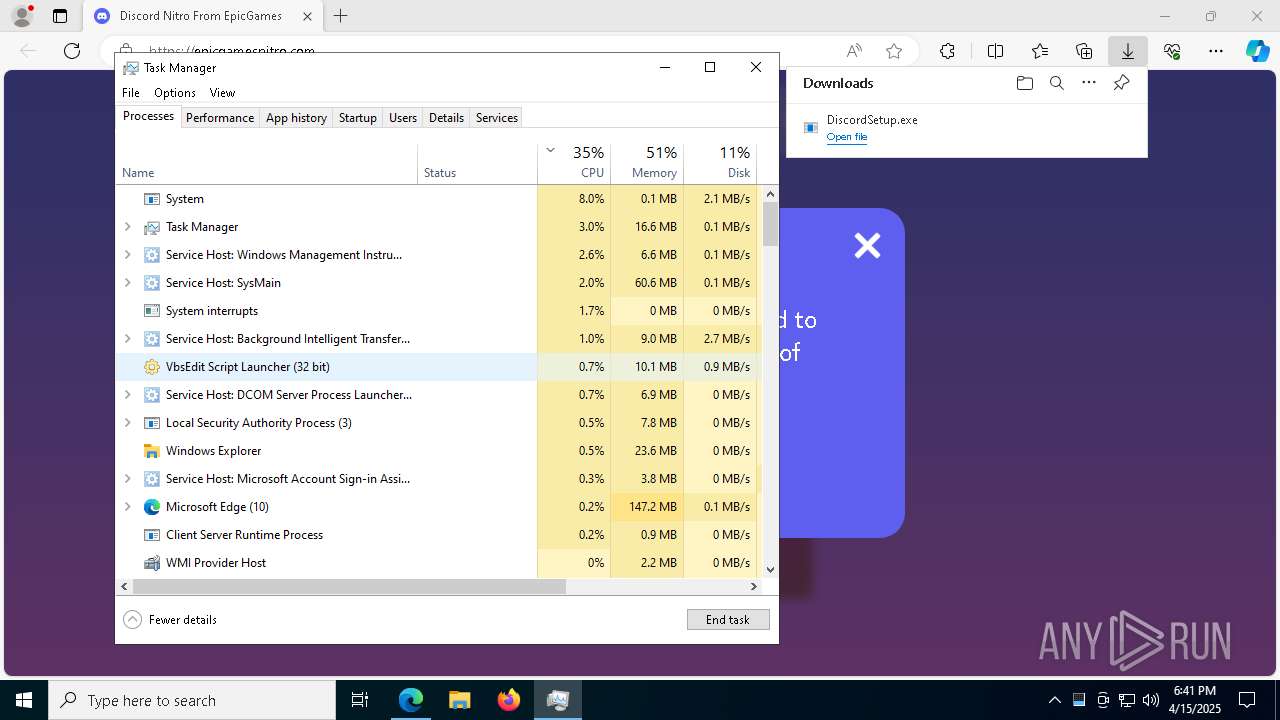
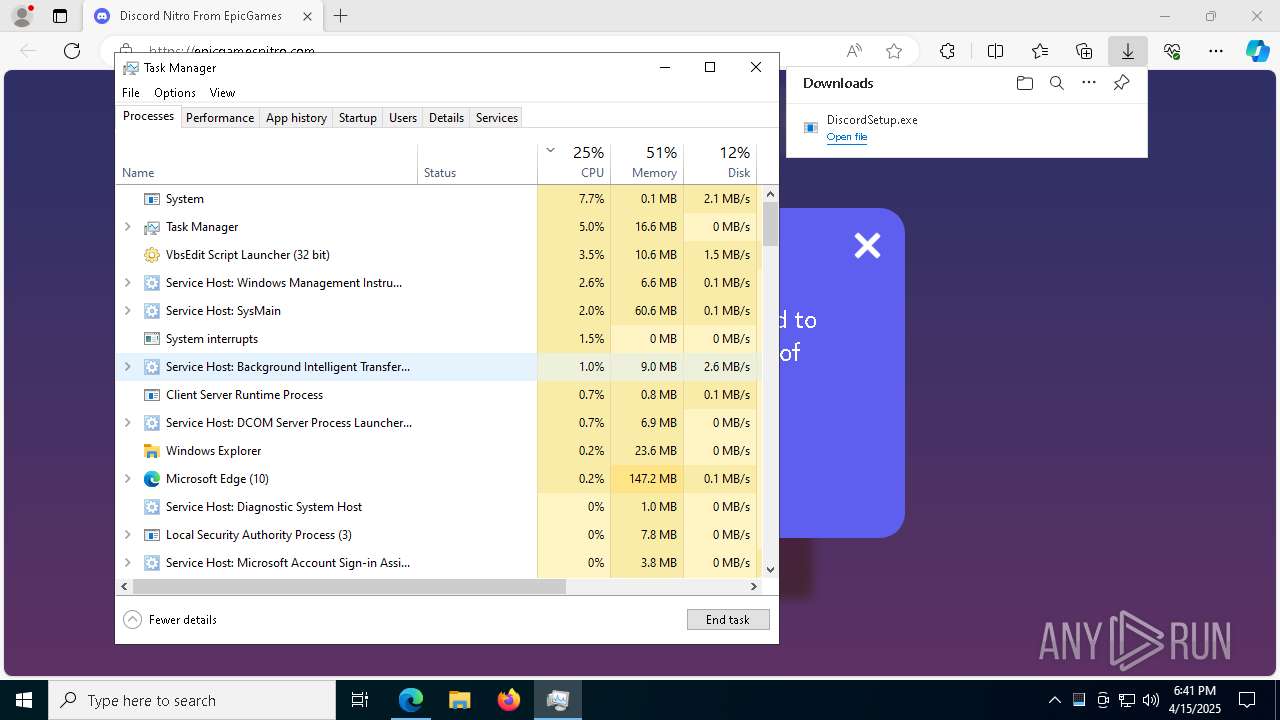
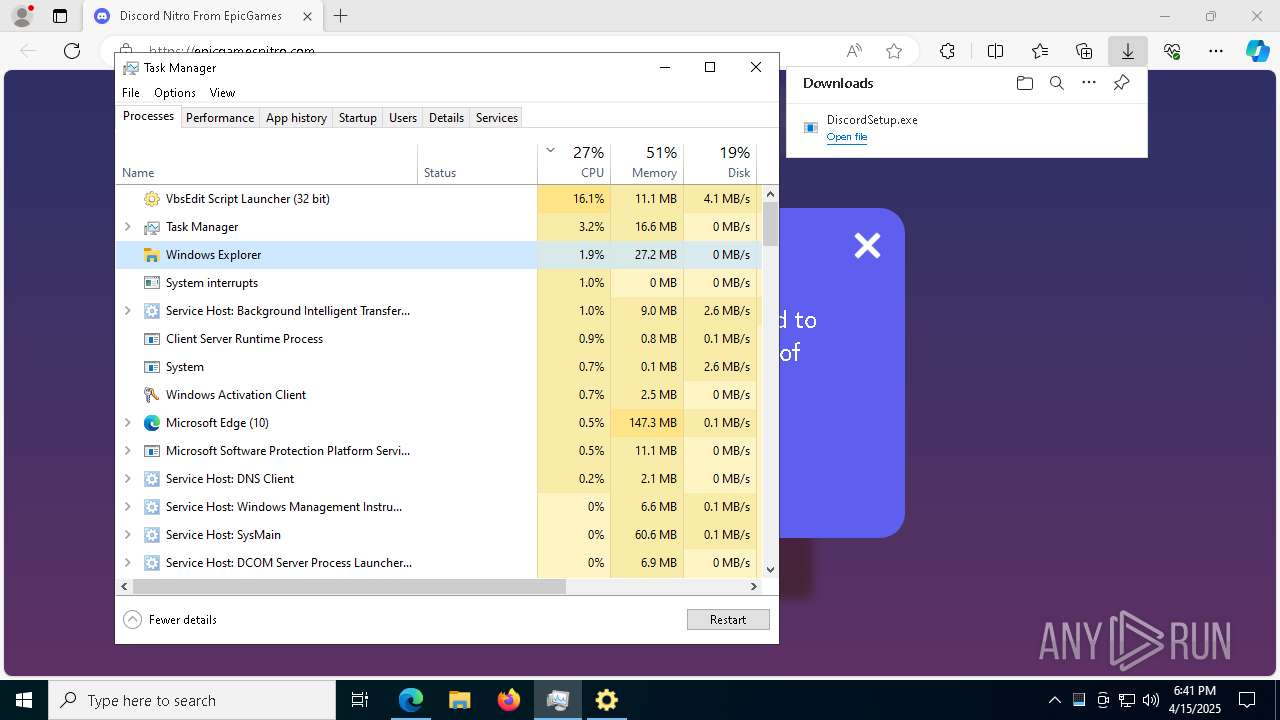
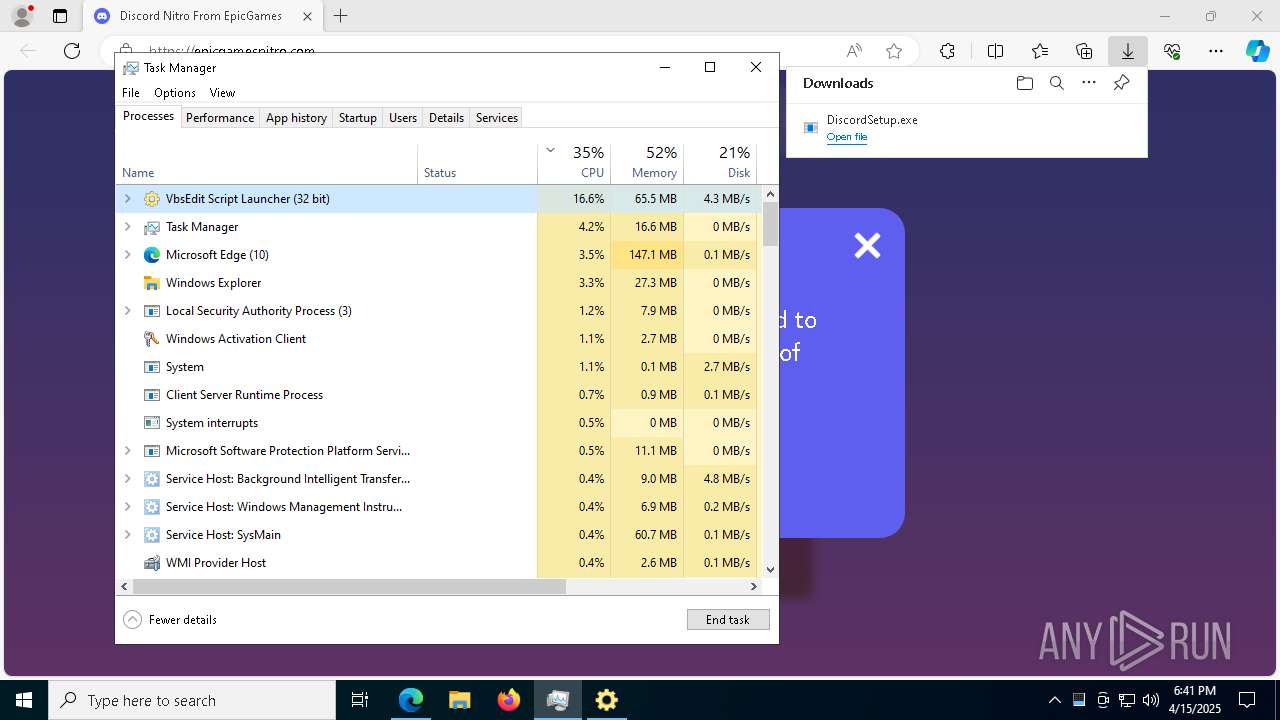
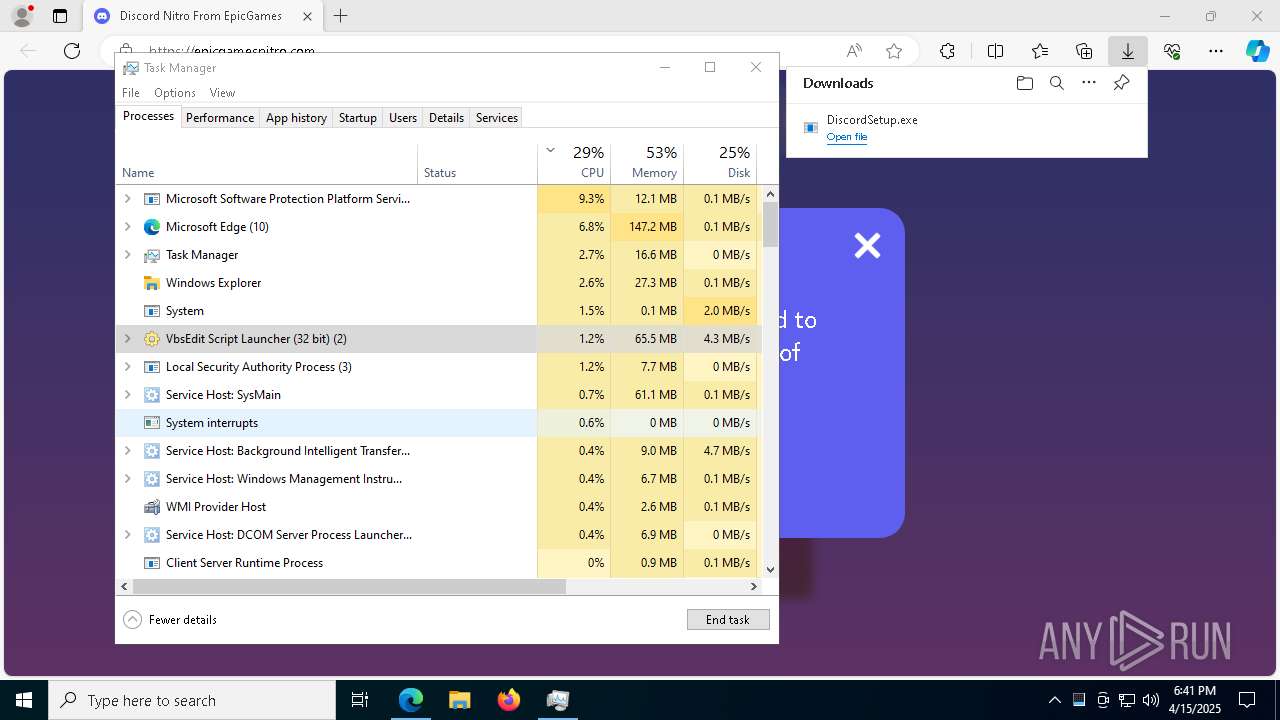
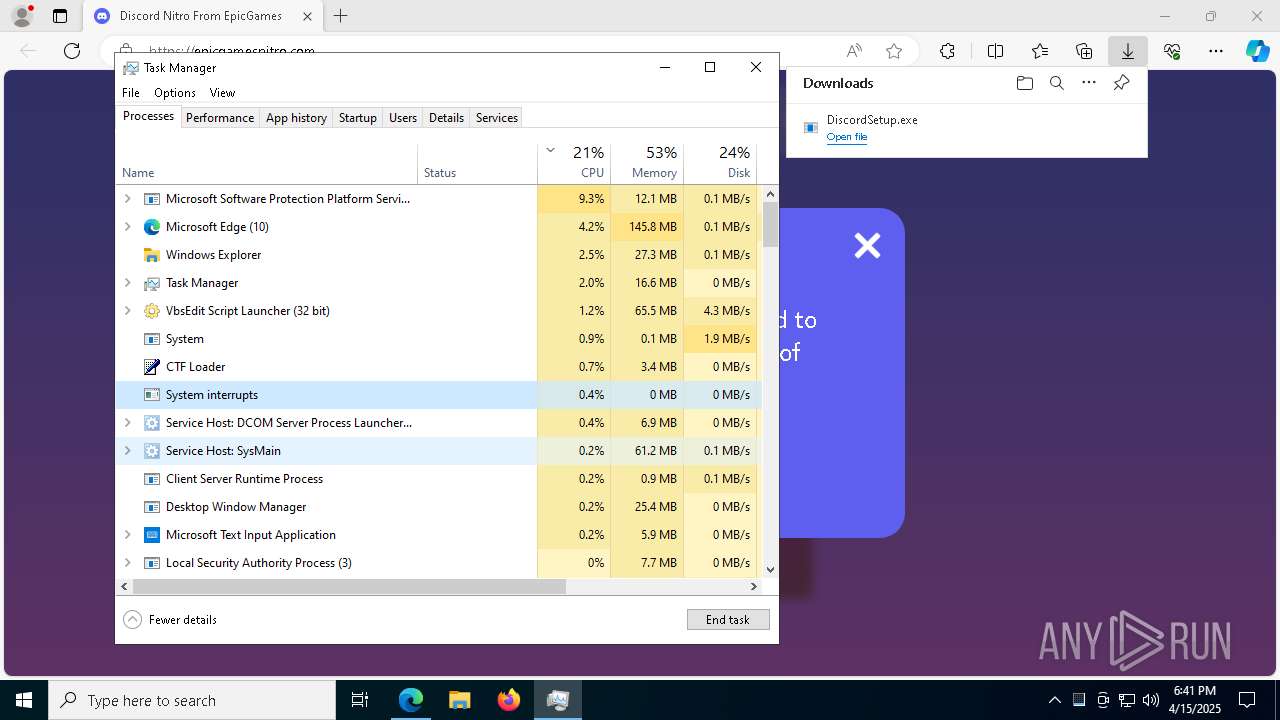
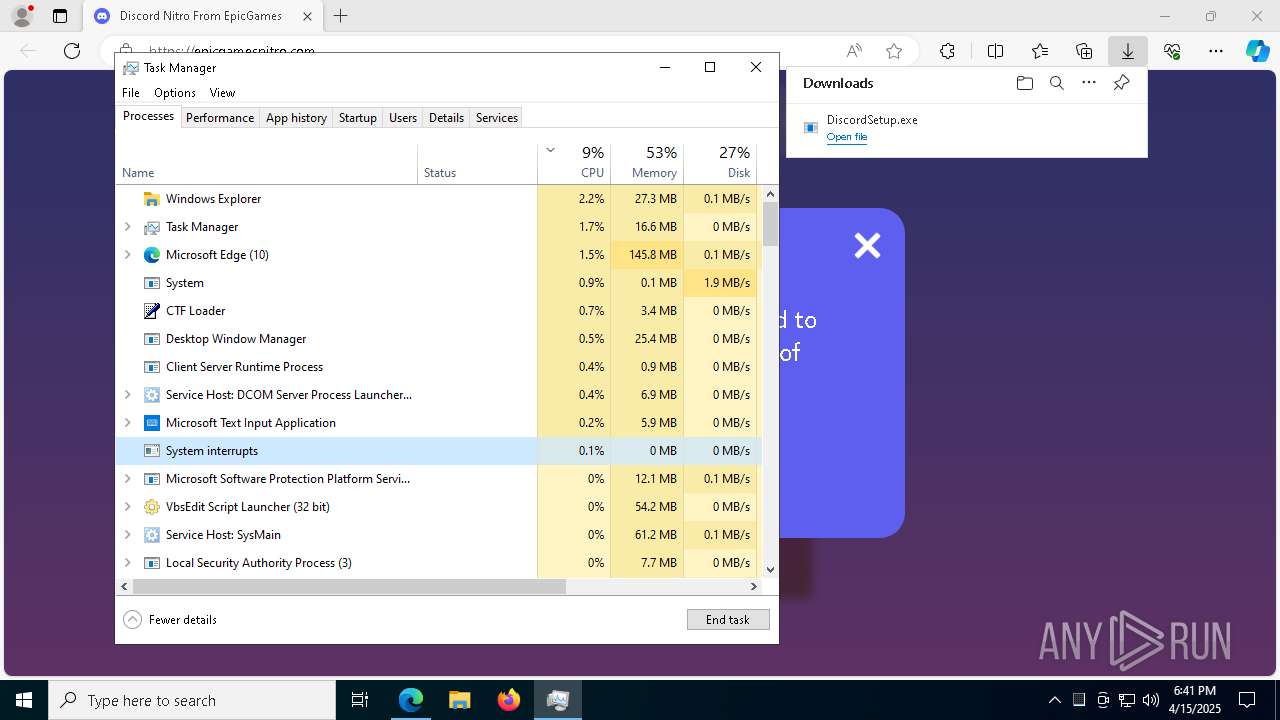
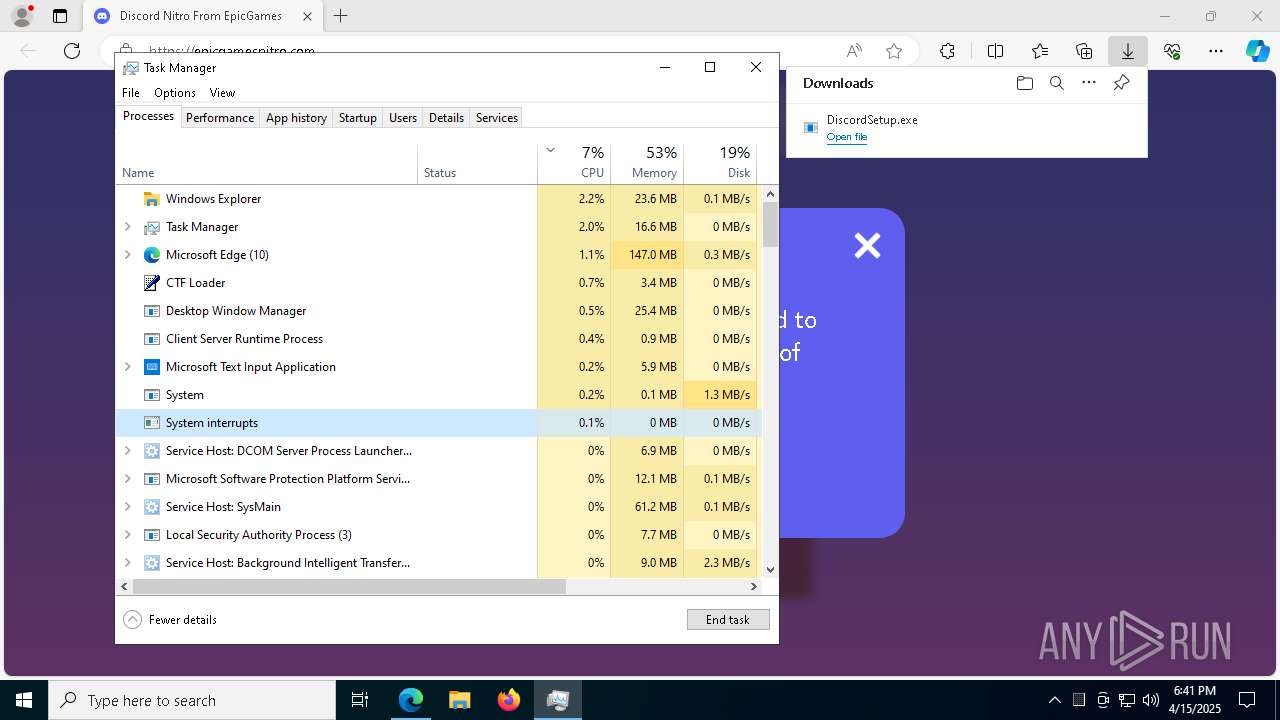
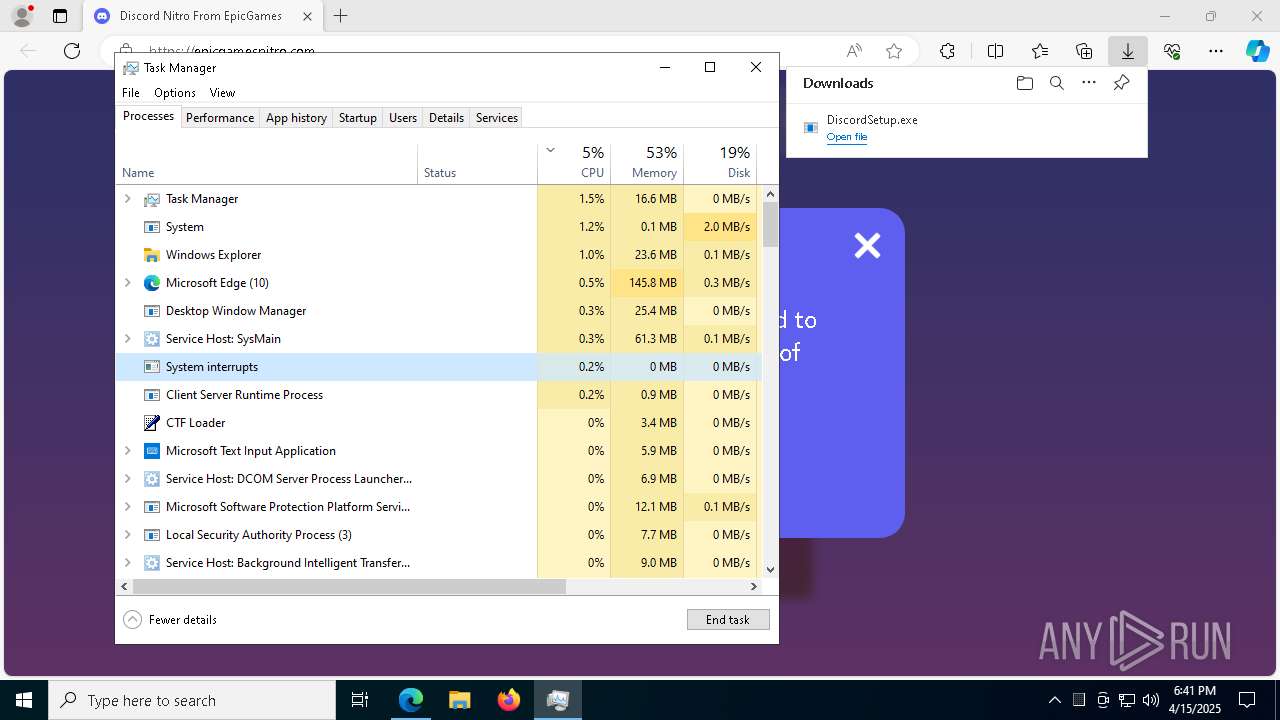
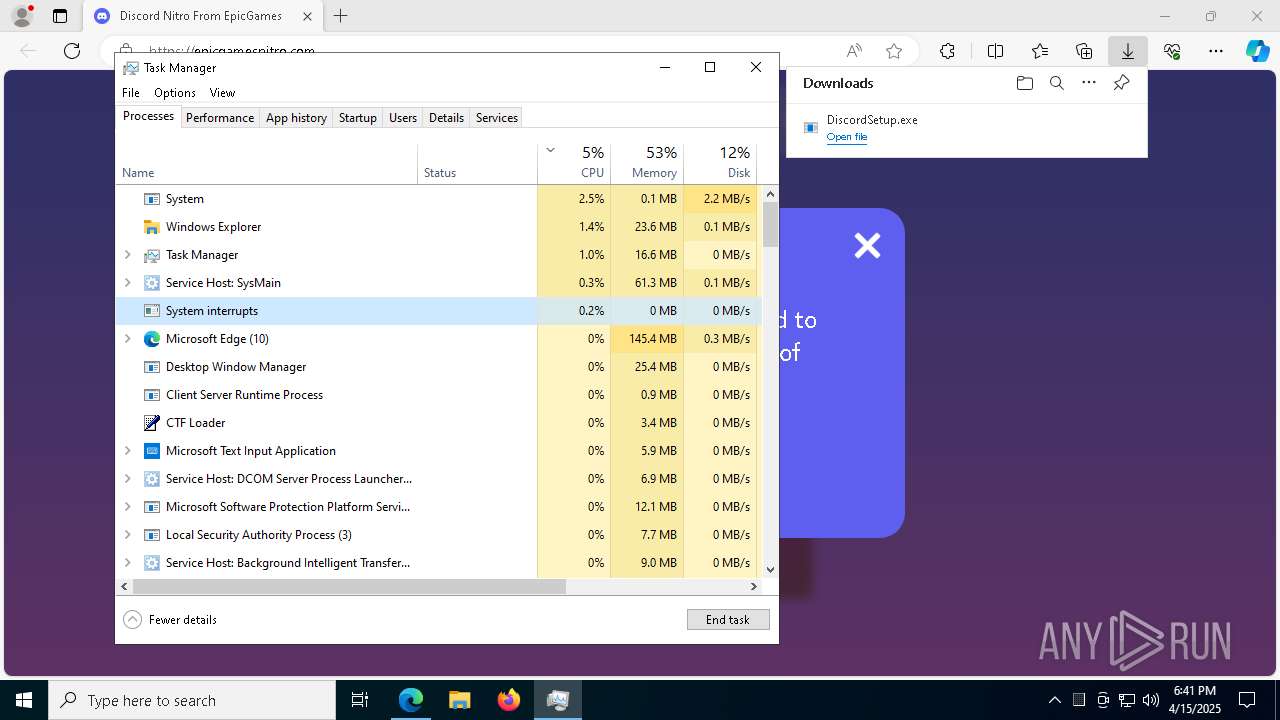
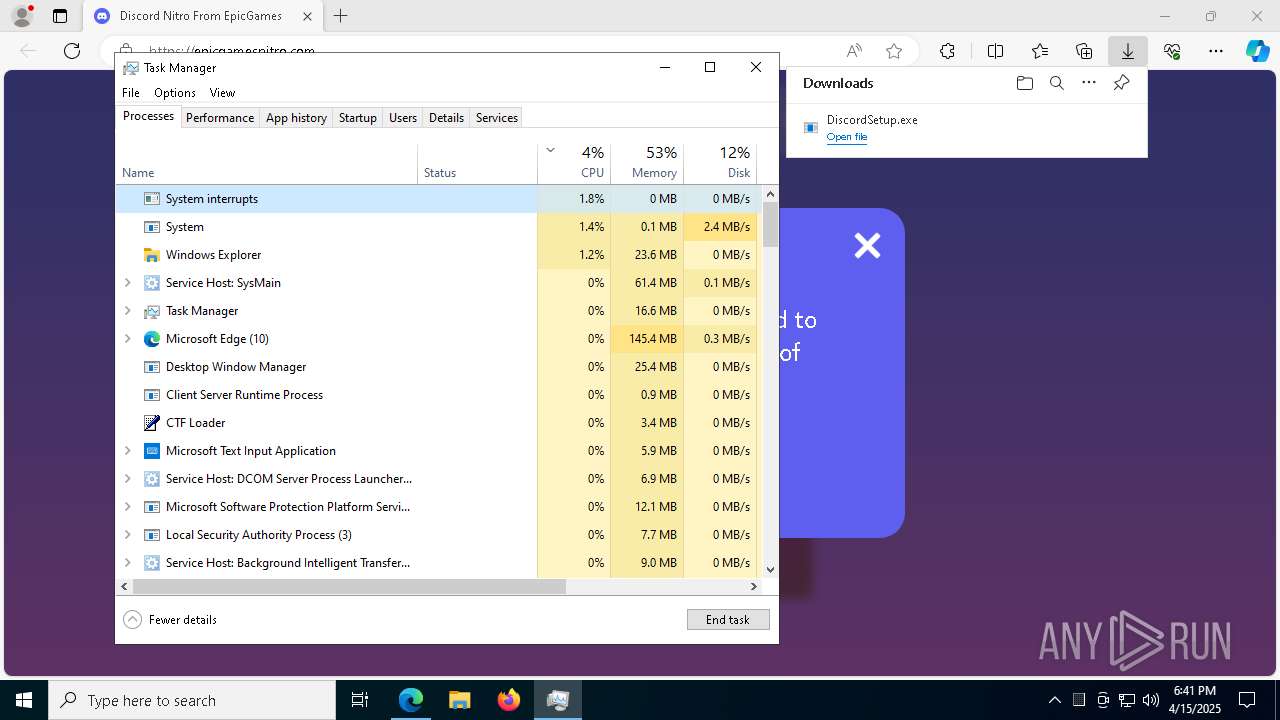
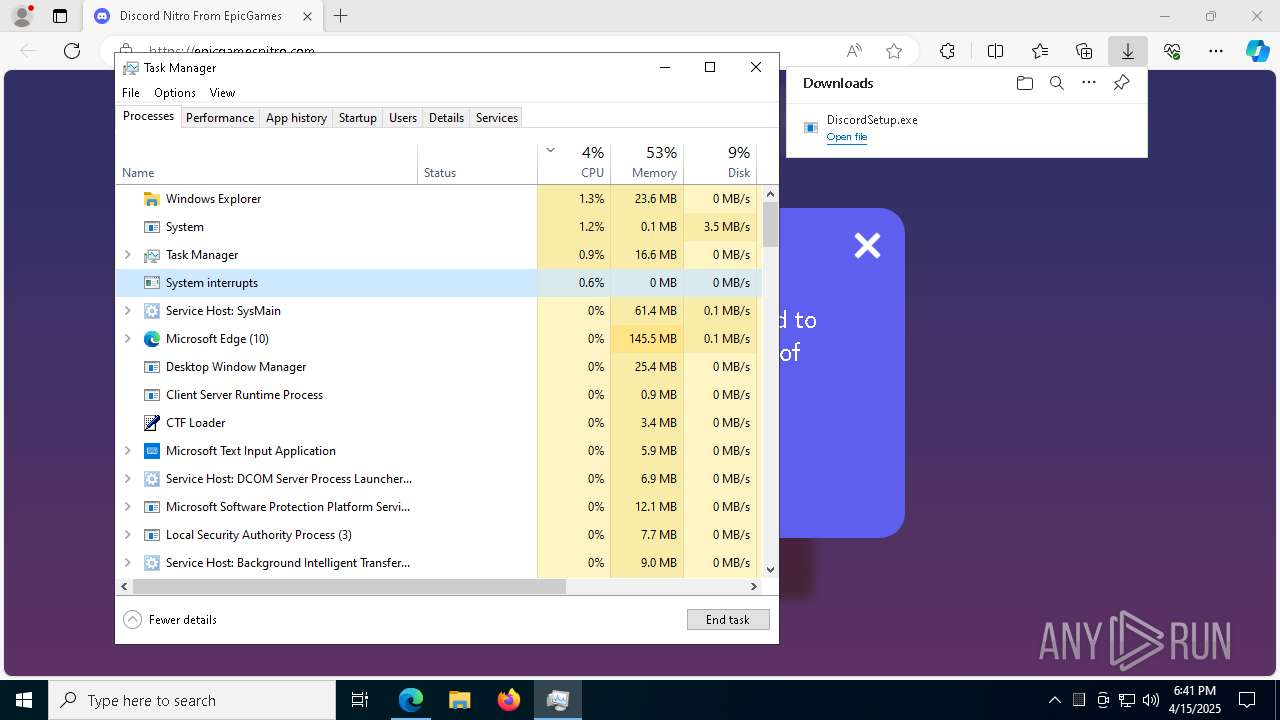
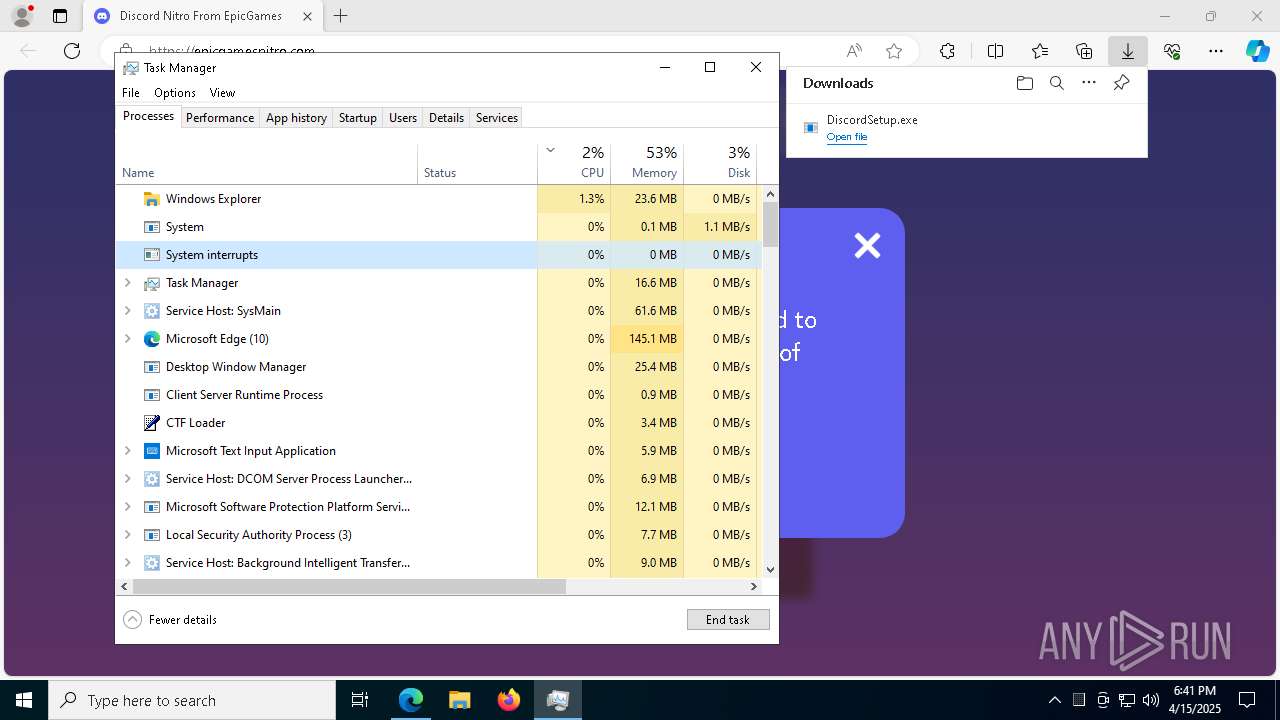
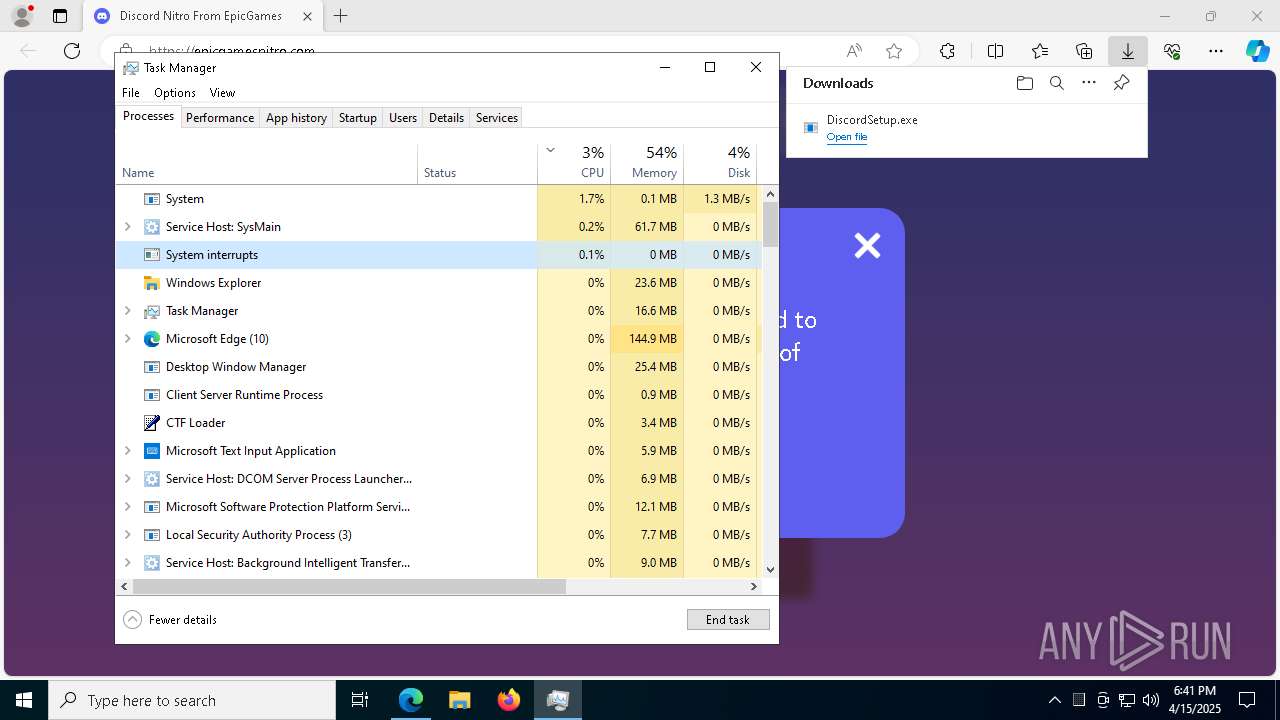
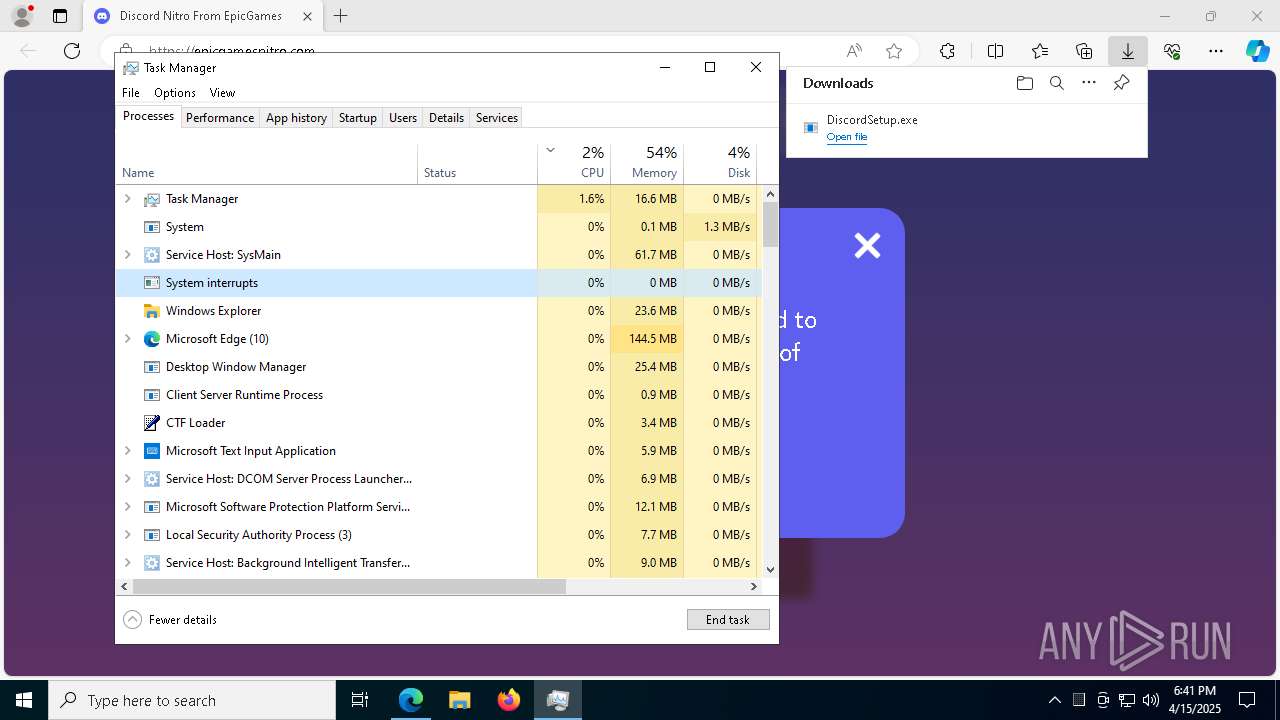
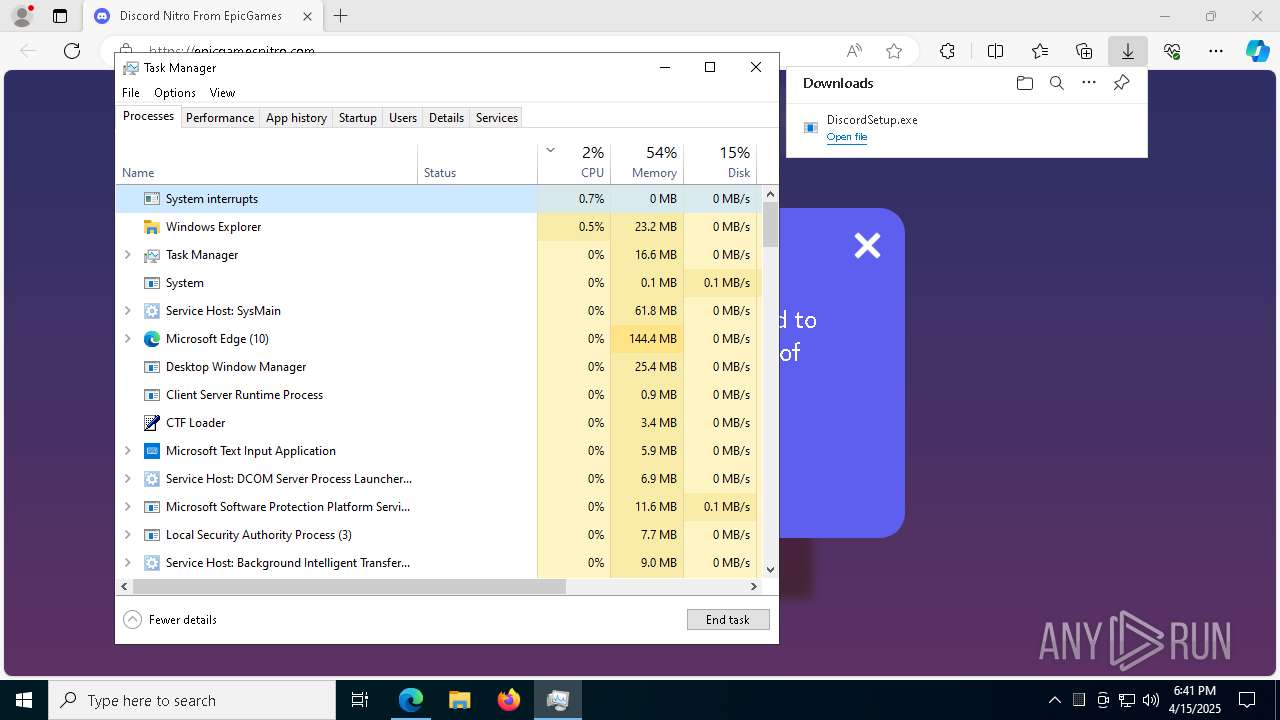
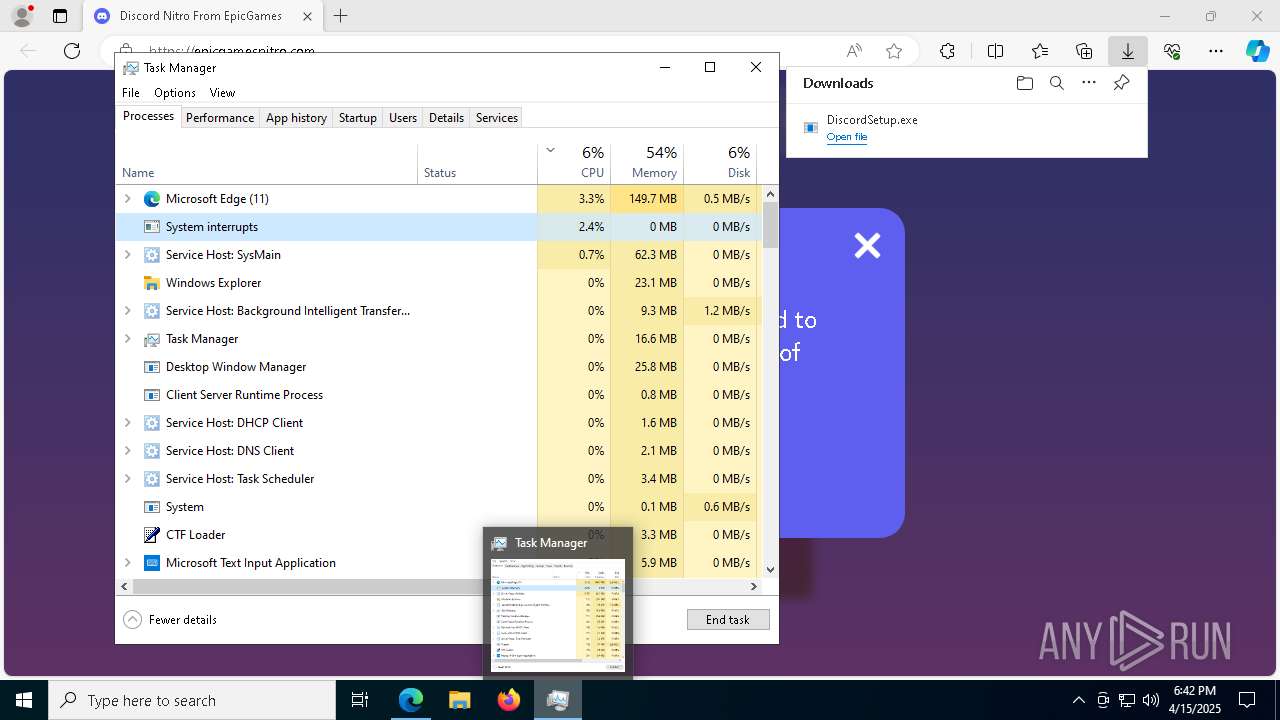
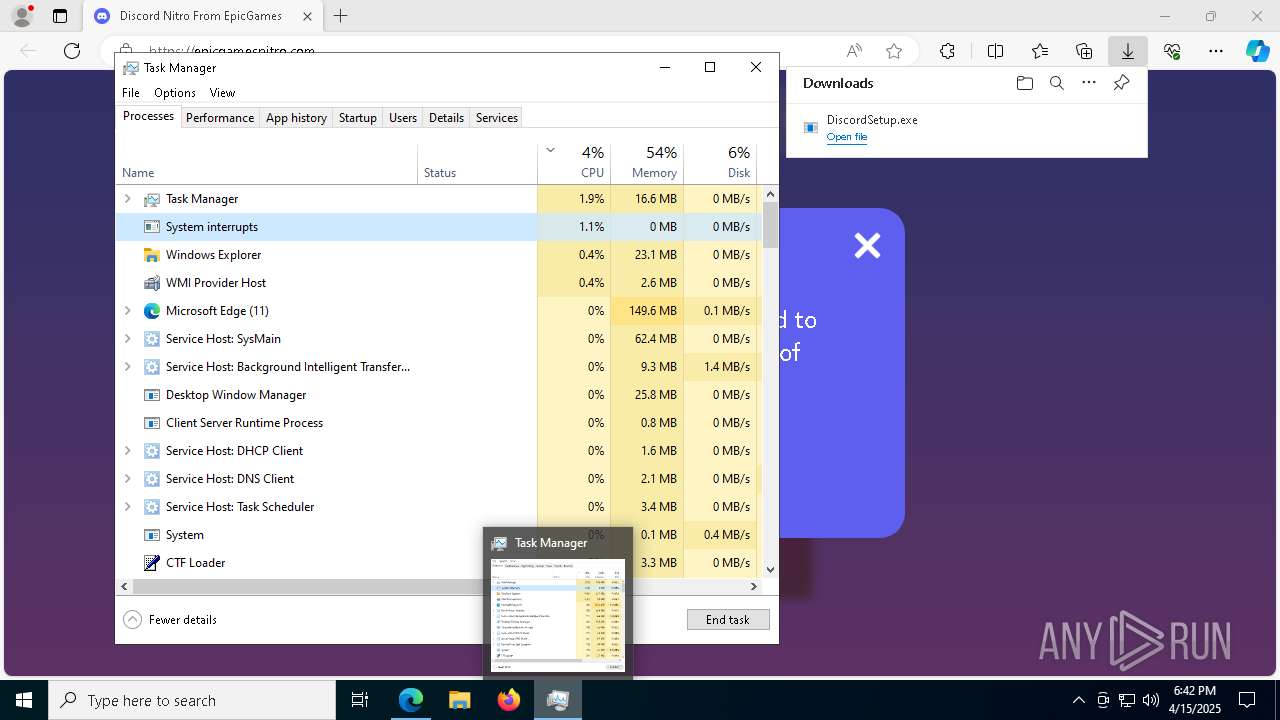
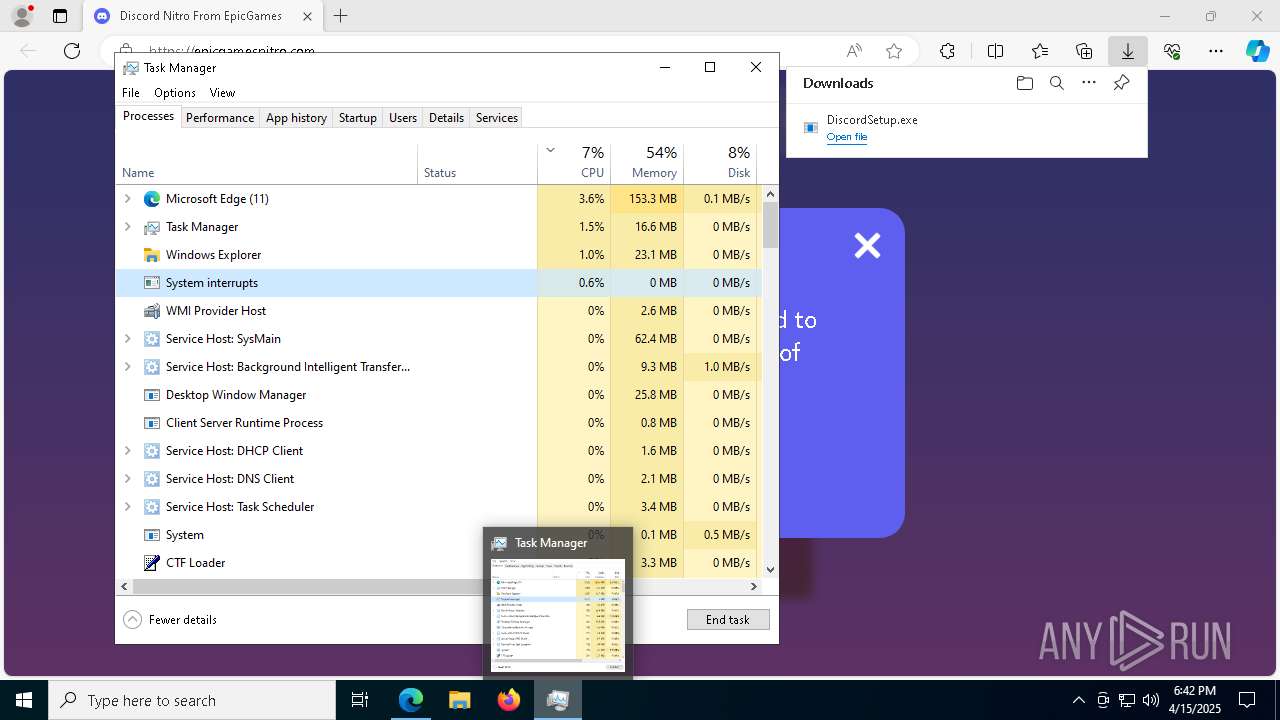
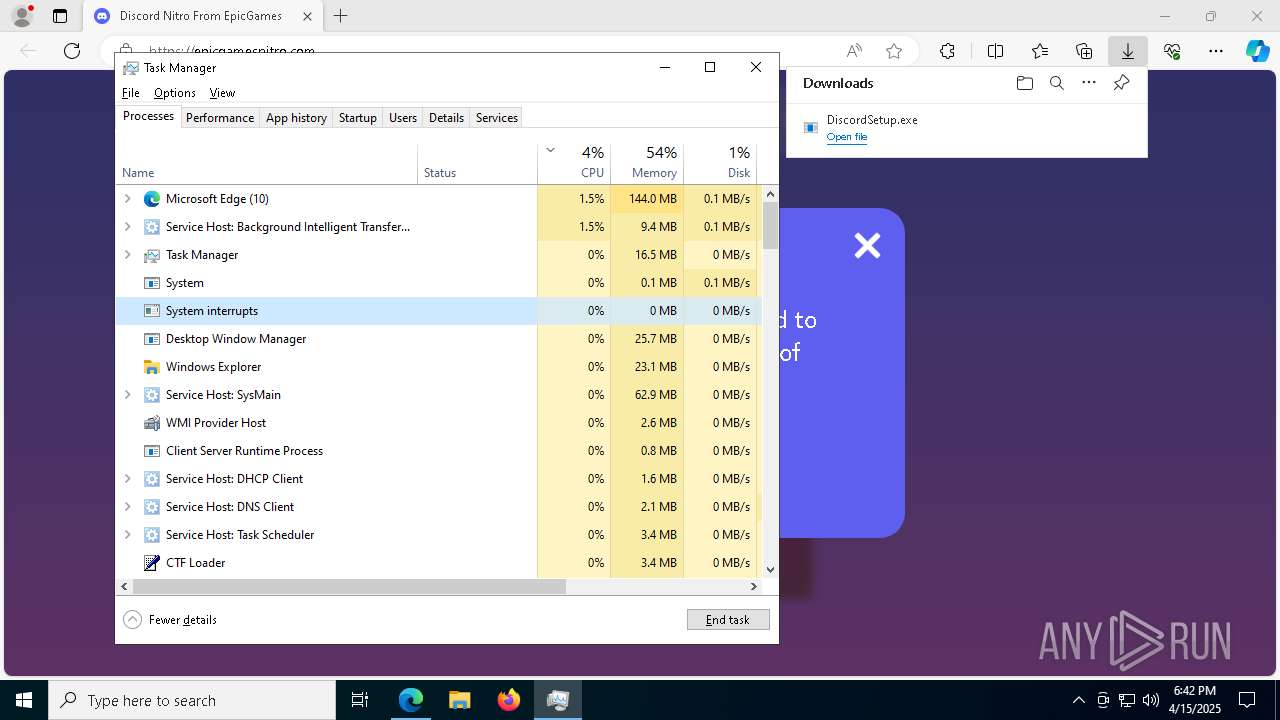
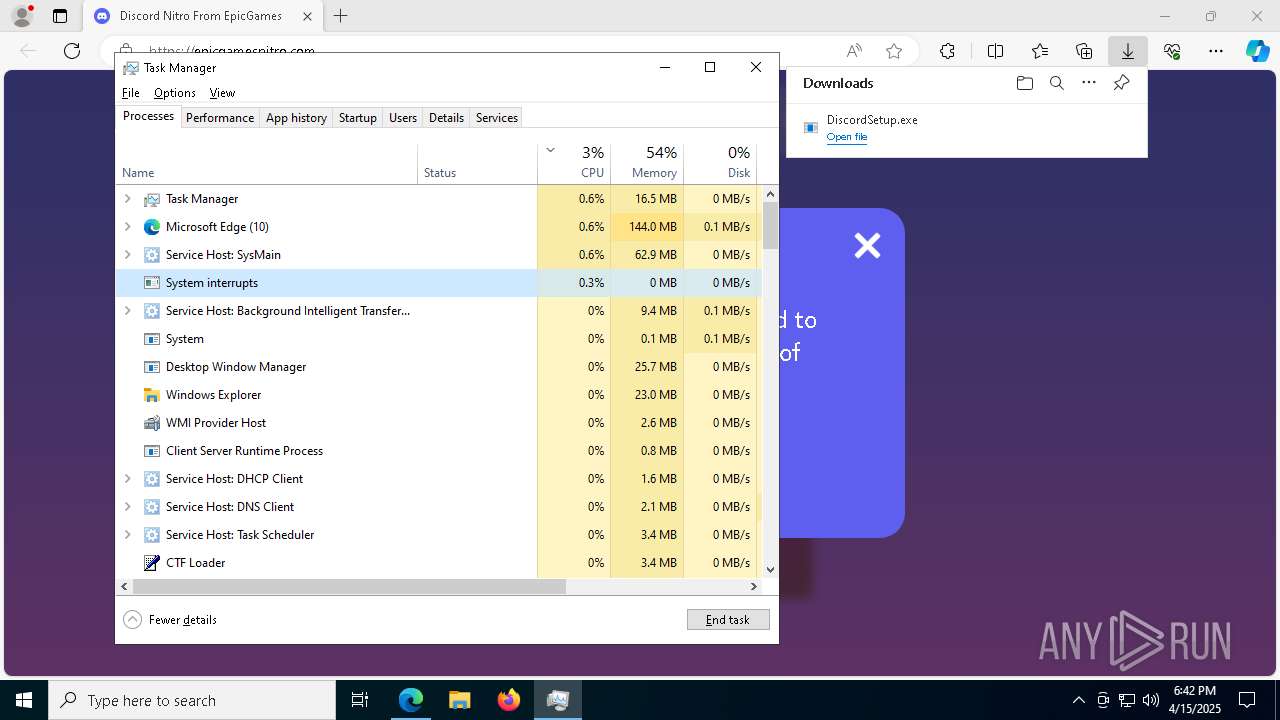
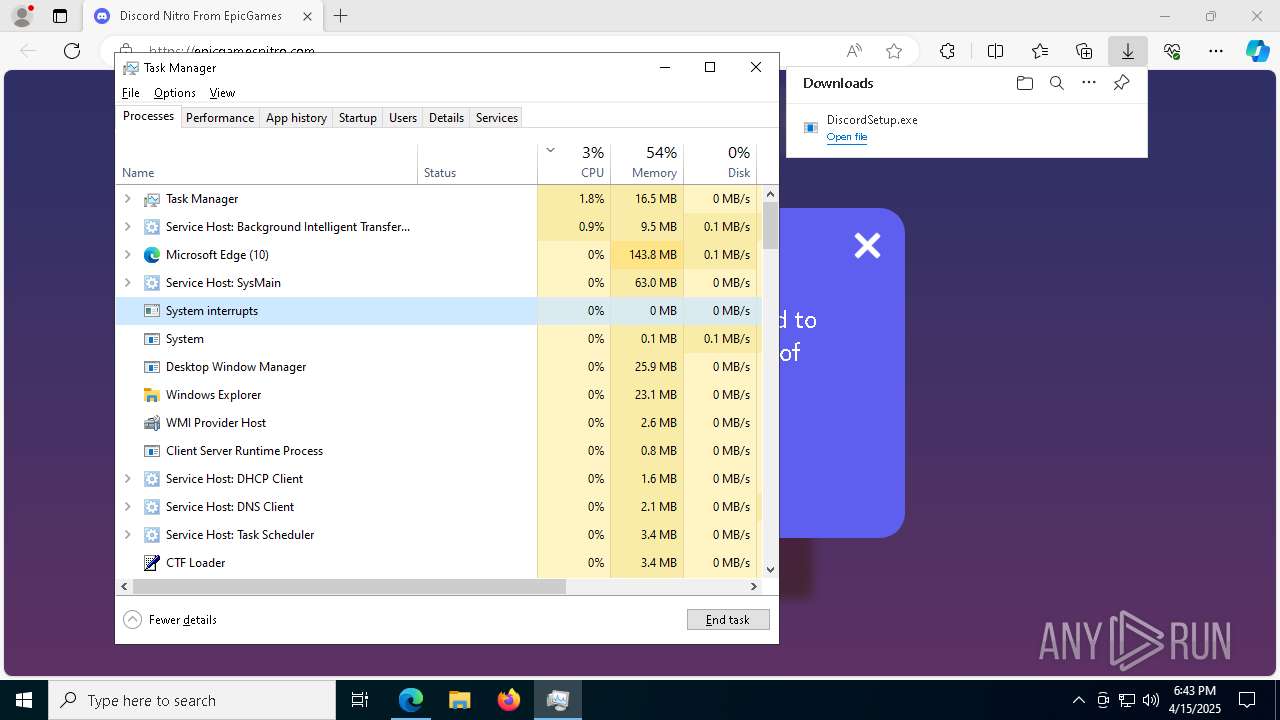
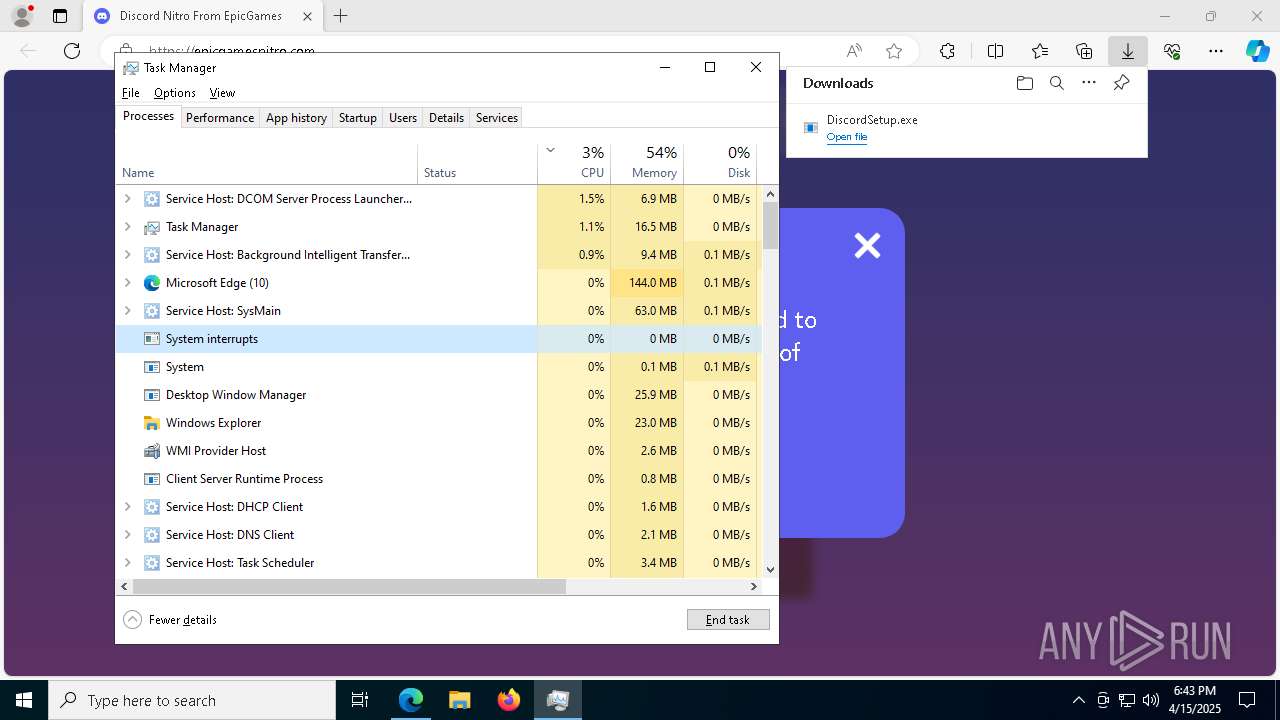
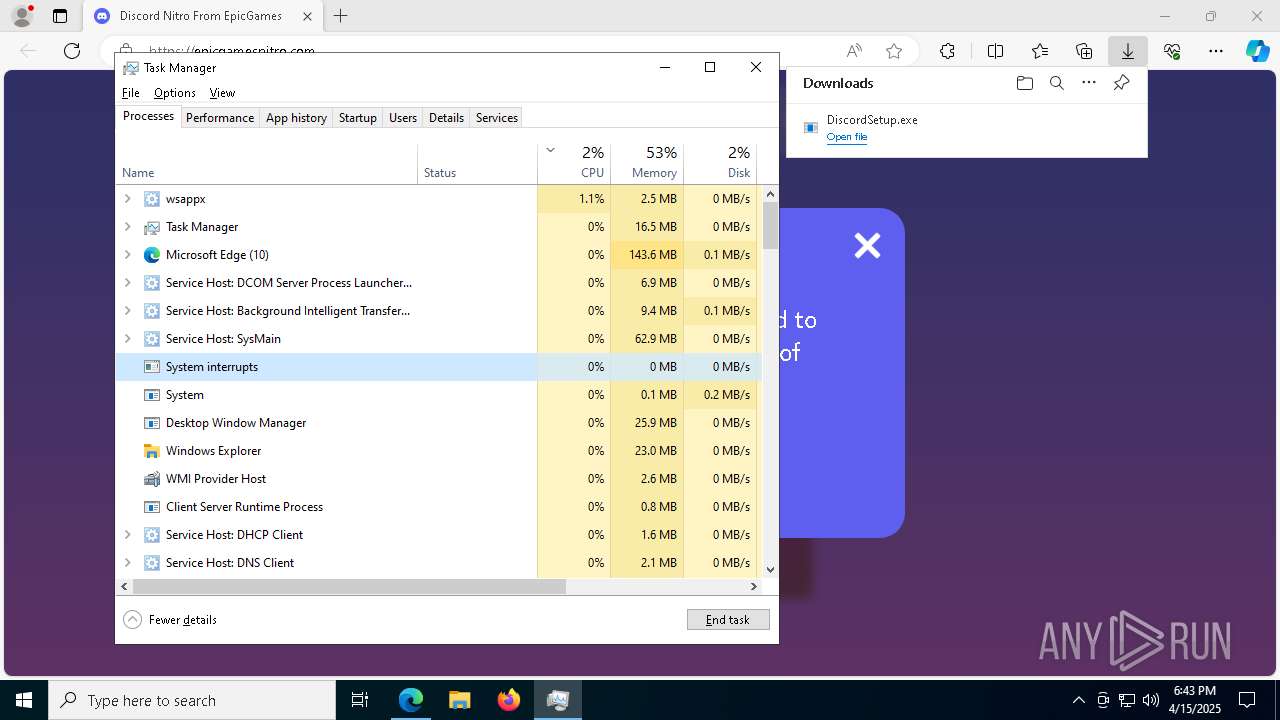
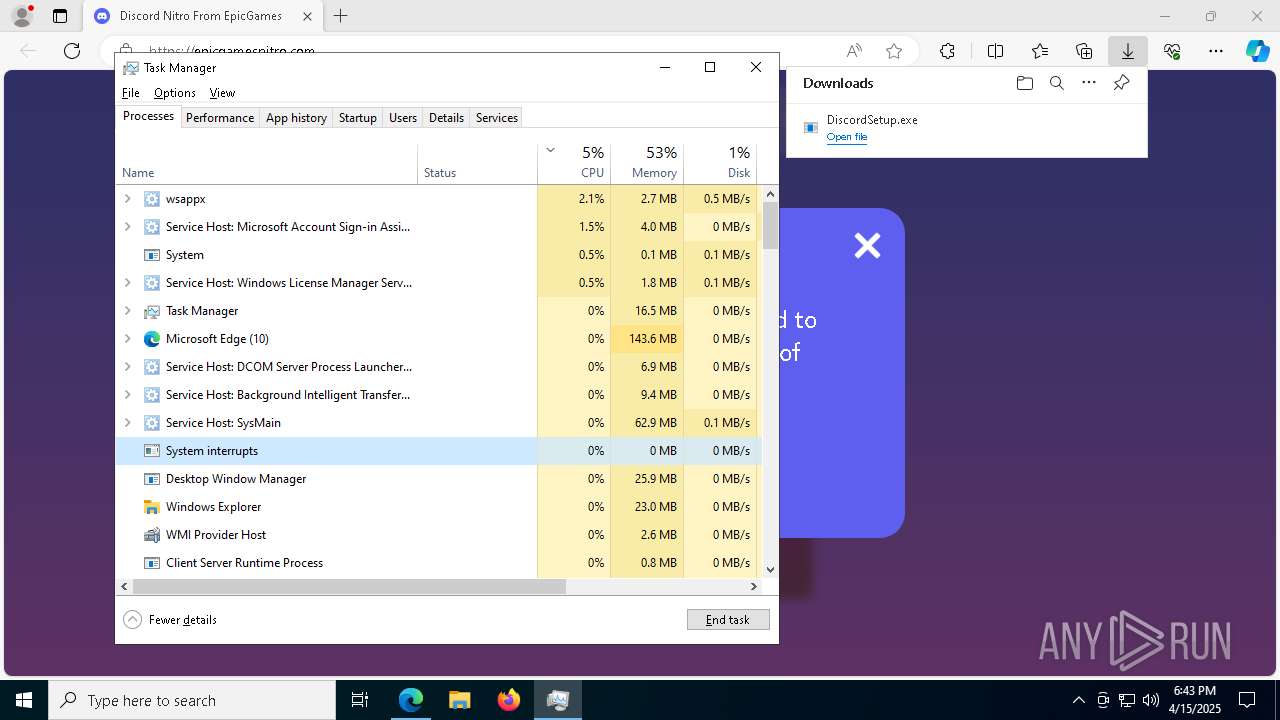
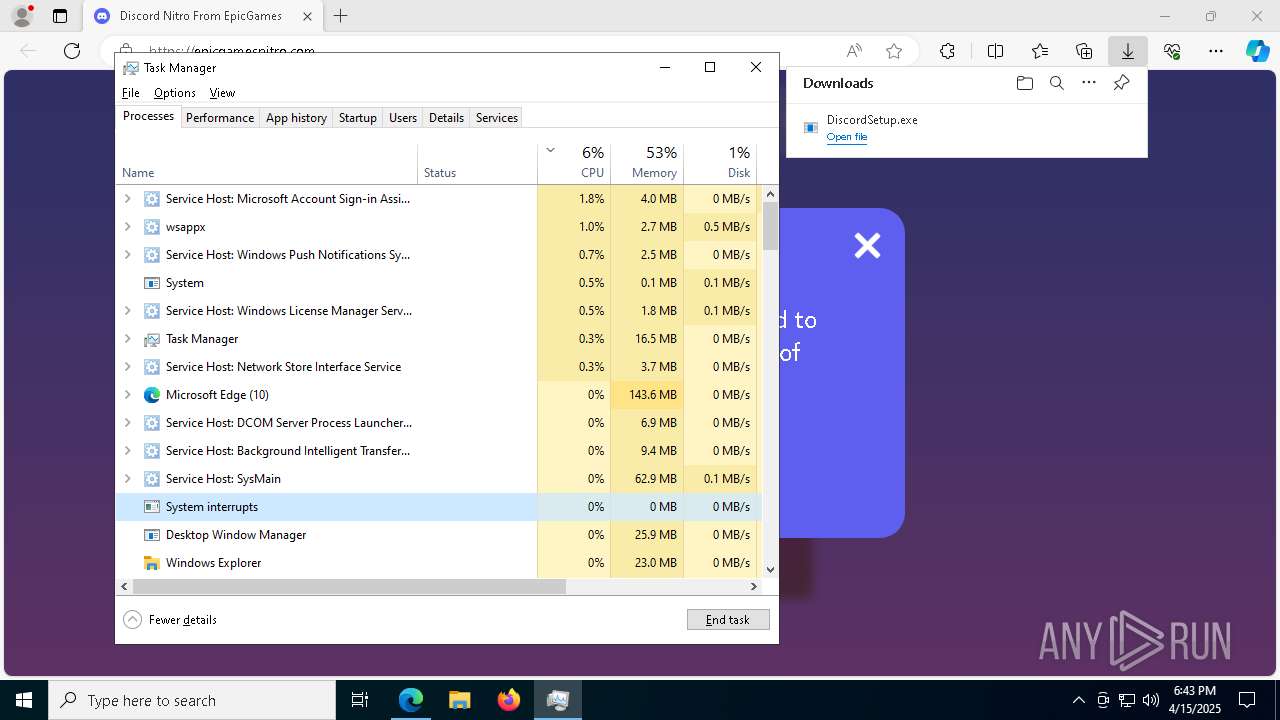
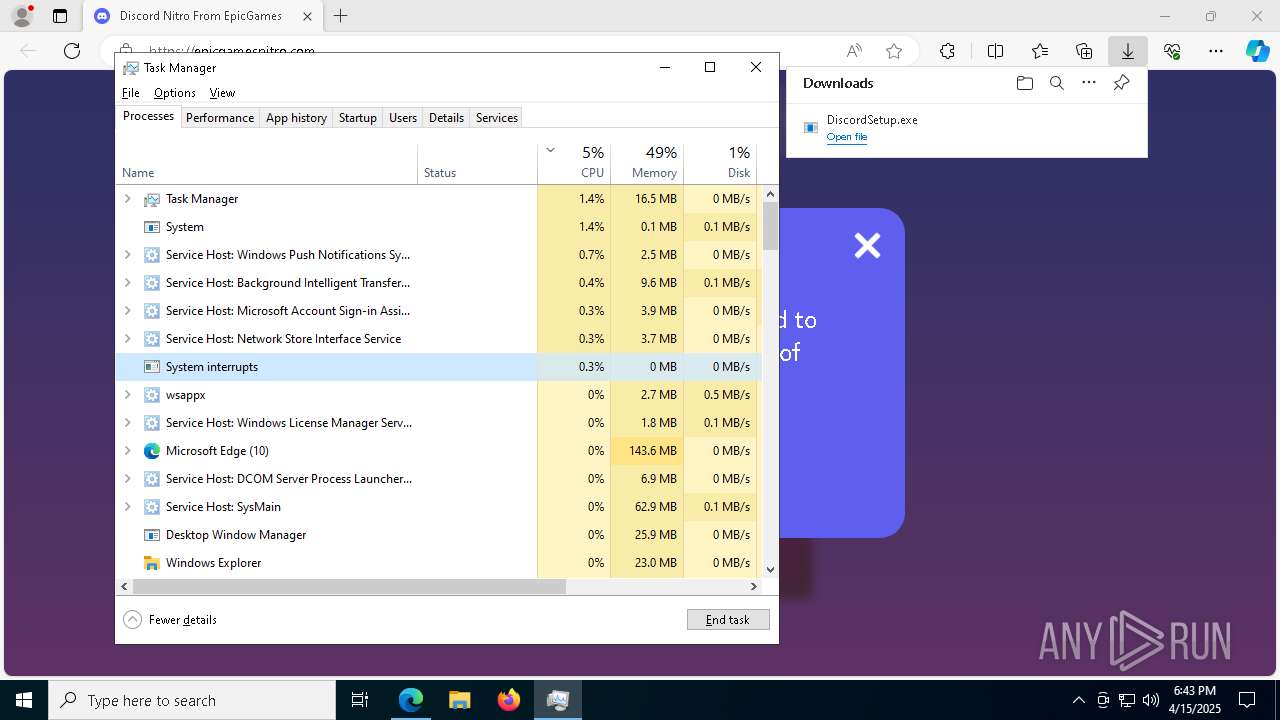
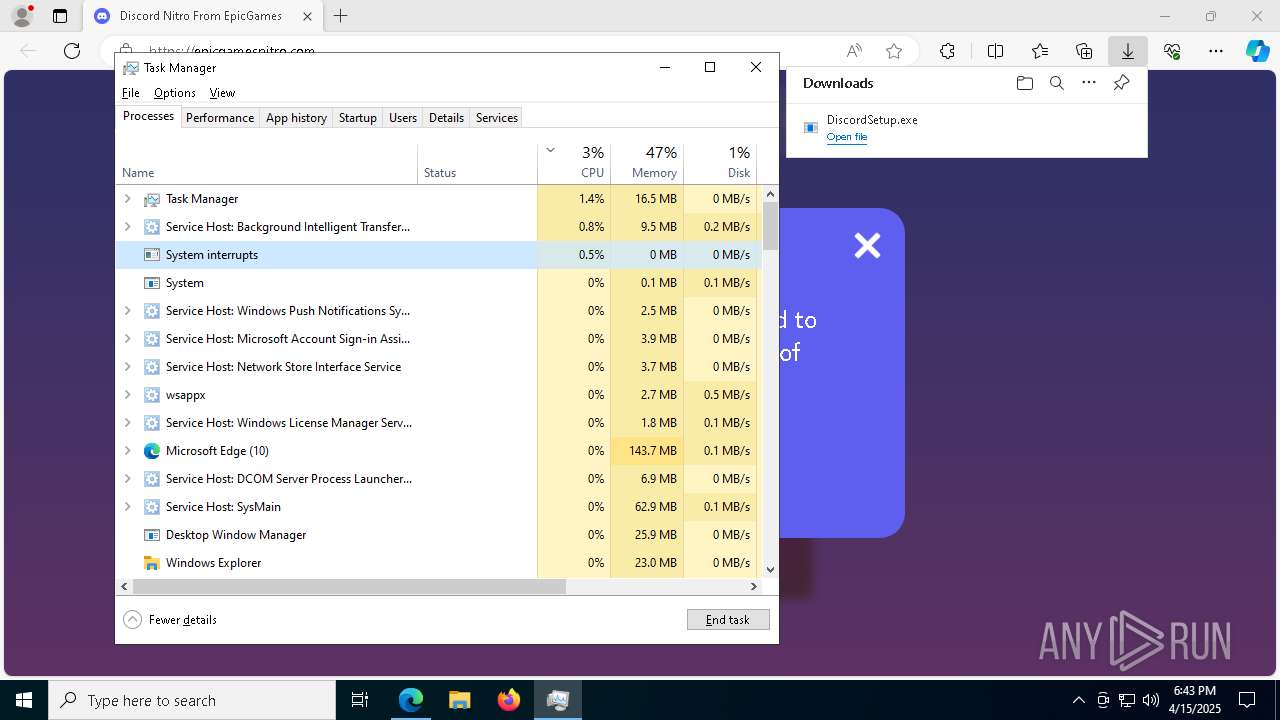
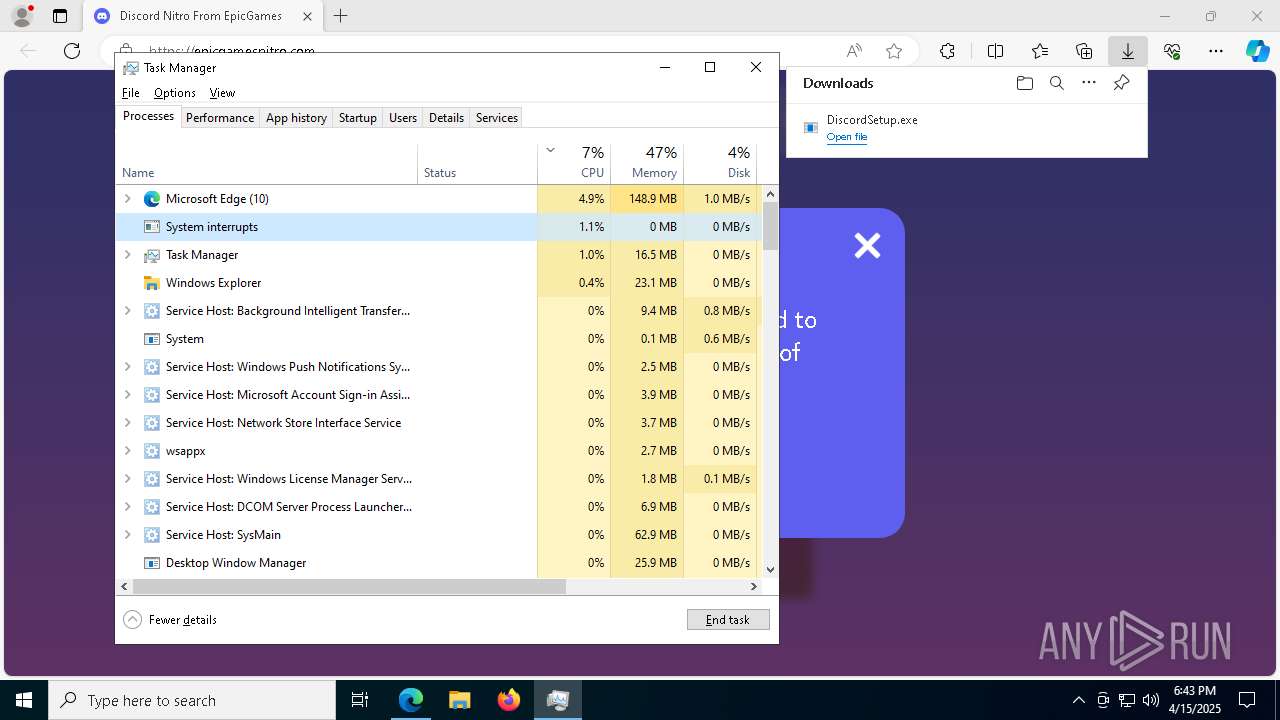
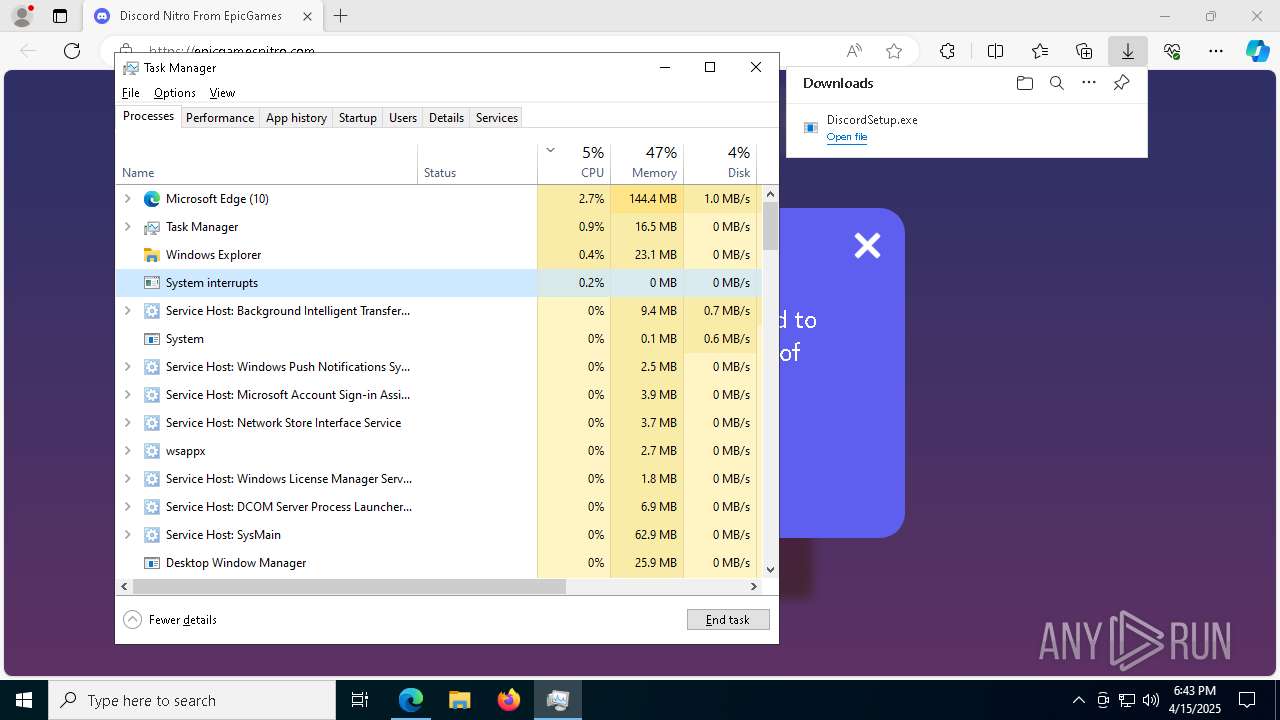
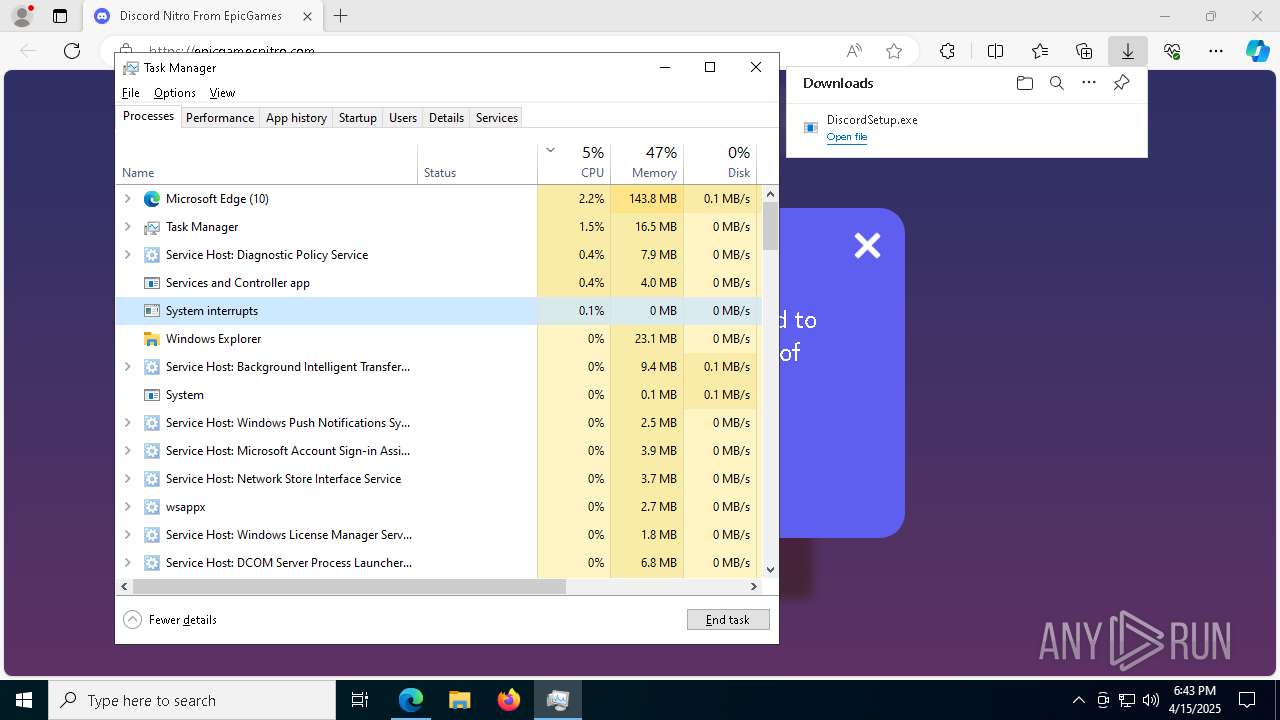
- Taskmgr.exe (PID: 456)
- Taskmgr.exe (PID: 5164)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5576)
Creates files in the program directory
- setup_helper.exe (PID: 2800)
Checks proxy server information
- slui.exe (PID: 720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
215
Monitored processes
77
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4784 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6672 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2712 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1532 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2408 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6200 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4184 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=6572 --field-trial-handle=2412,i,7489074762694055148,18080872448644959472,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
43 422
Read events
43 391
Write events
26
Delete events
5
Modification events
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2B4648C46B912F00 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8E7D5F8D-502A-4553-AB22-E40D843155B7} | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C4BD187-78D7-4663-AE01-3C57488DF942} | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C8BB01F9-3241-4D29-B568-9EAC6990BDDF} | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {124697AC-8D6B-42DC-BA52-48DE6AB00FFB} | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6476) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A8A440C46B912F00 | |||
Executable files
22
Suspicious files
465
Text files
97
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b836.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 6476 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
82
DNS requests
86
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1348 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744953271&P2=404&P3=2&P4=PkWBk5gHvbDI11I%2f%2fZsLlE%2bRRgX1%2b32ka0nQwDdBV48A17Ik6Rne5mXqbVn0%2bjRLoc8EZzc7j0NqvVvUnTeyfw%3d%3d | unknown | — | — | whitelisted |
7376 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7376 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1348 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744953271&P2=404&P3=2&P4=PkWBk5gHvbDI11I%2f%2fZsLlE%2bRRgX1%2b32ka0nQwDdBV48A17Ik6Rne5mXqbVn0%2bjRLoc8EZzc7j0NqvVvUnTeyfw%3d%3d | unknown | — | — | whitelisted |
1348 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744953271&P2=404&P3=2&P4=PkWBk5gHvbDI11I%2f%2fZsLlE%2bRRgX1%2b32ka0nQwDdBV48A17Ik6Rne5mXqbVn0%2bjRLoc8EZzc7j0NqvVvUnTeyfw%3d%3d | unknown | — | — | whitelisted |
1348 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744953271&P2=404&P3=2&P4=PkWBk5gHvbDI11I%2f%2fZsLlE%2bRRgX1%2b32ka0nQwDdBV48A17Ik6Rne5mXqbVn0%2bjRLoc8EZzc7j0NqvVvUnTeyfw%3d%3d | unknown | — | — | whitelisted |
1348 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744953271&P2=404&P3=2&P4=PkWBk5gHvbDI11I%2f%2fZsLlE%2bRRgX1%2b32ka0nQwDdBV48A17Ik6Rne5mXqbVn0%2bjRLoc8EZzc7j0NqvVvUnTeyfw%3d%3d | unknown | — | — | whitelisted |
1348 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744953271&P2=404&P3=2&P4=PkWBk5gHvbDI11I%2f%2fZsLlE%2bRRgX1%2b32ka0nQwDdBV48A17Ik6Rne5mXqbVn0%2bjRLoc8EZzc7j0NqvVvUnTeyfw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6476 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2108 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2108 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2108 | msedge.exe | 195.216.243.155:443 | u.to | Ddos-guard Ltd | RU | whitelisted |
2108 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2108 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
u.to |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
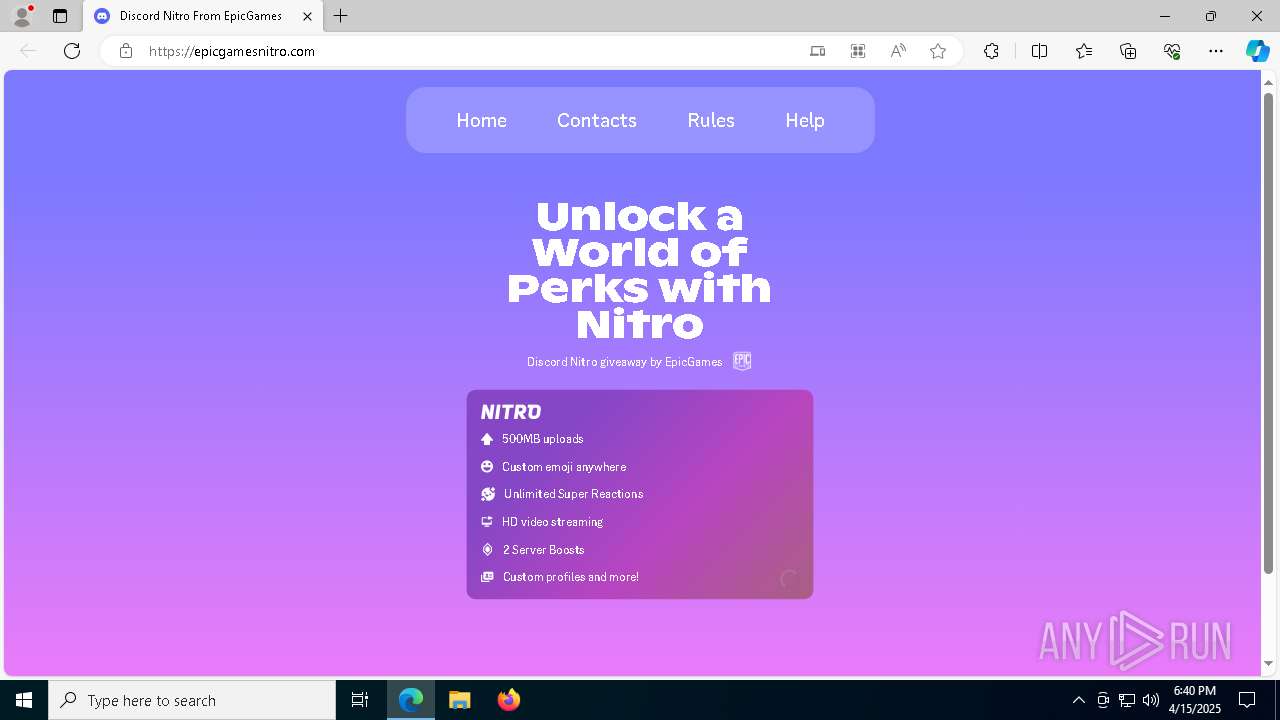
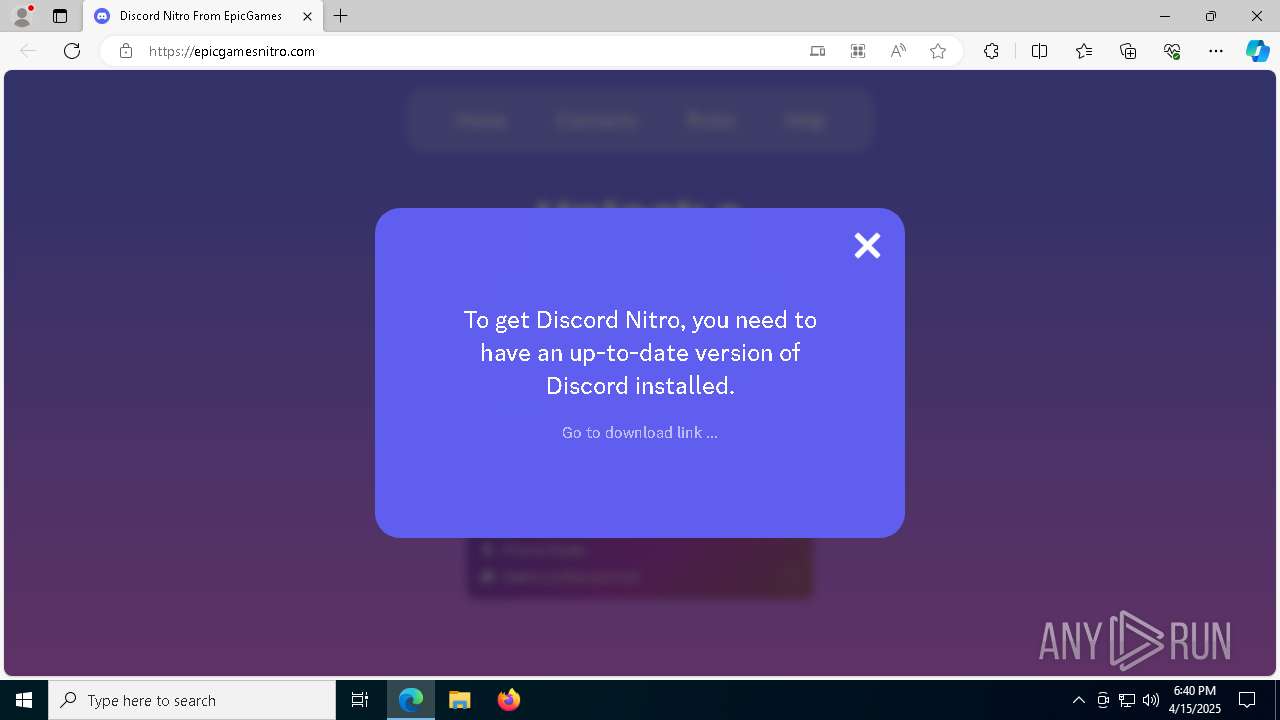
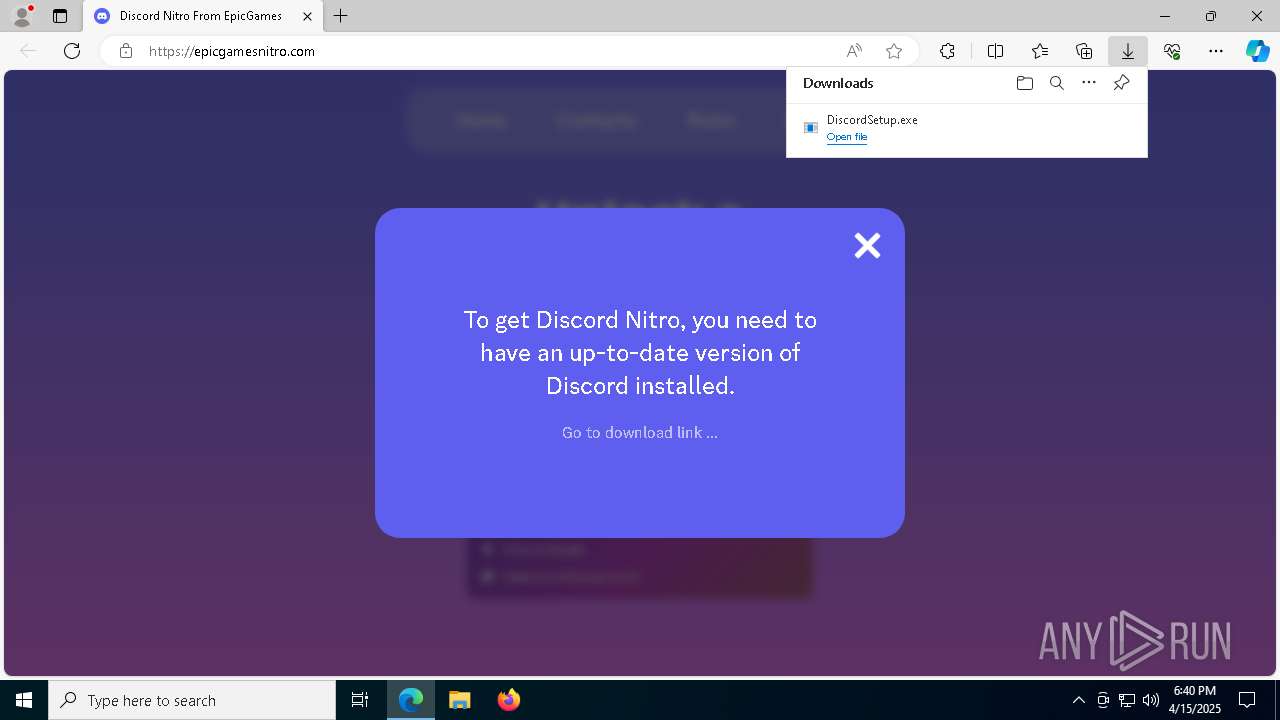
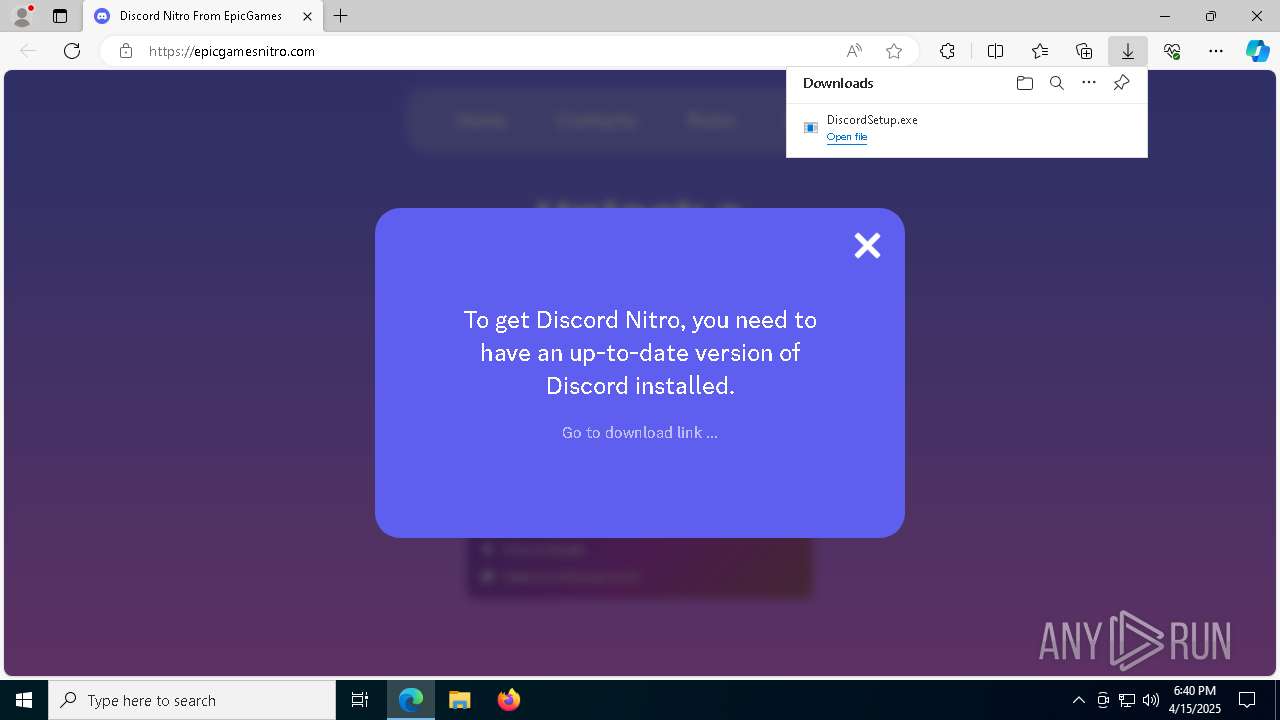
epicgamesnitro.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2108 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2108 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (u .to) |
2108 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (u .to) |
2108 | msedge.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (u .to) |
2108 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (u .to) |
2108 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
2108 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2108 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |