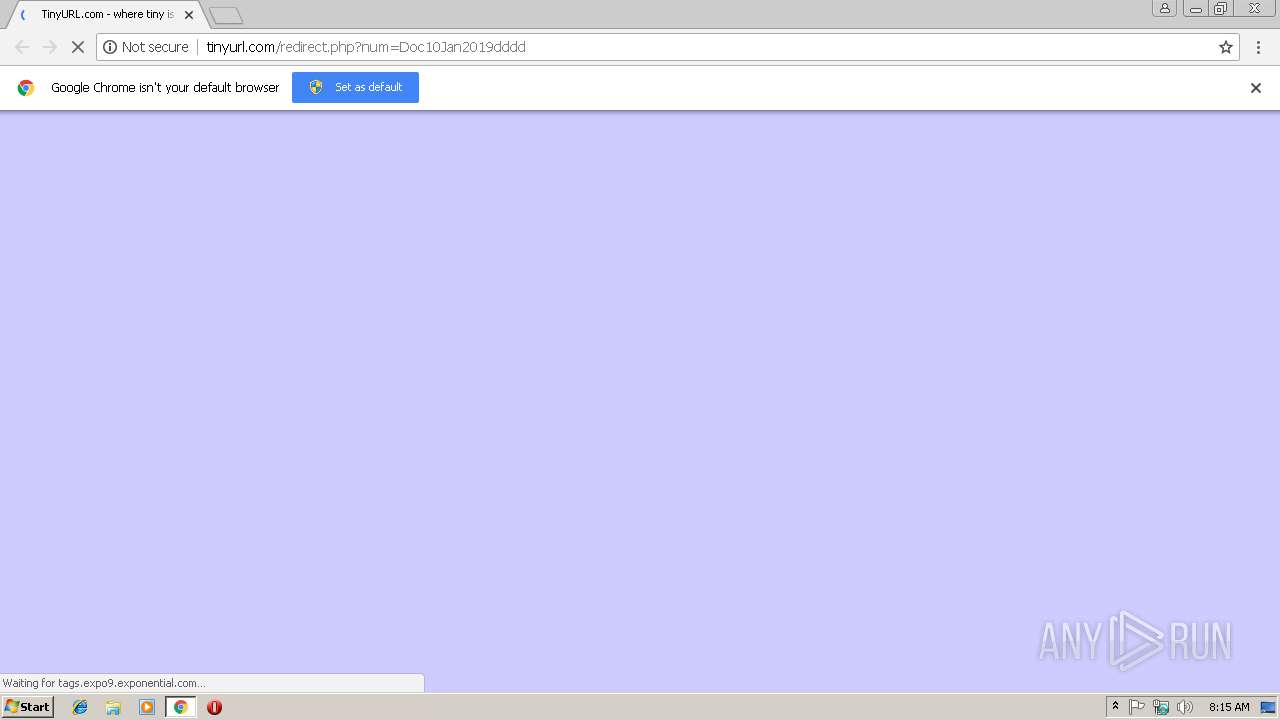
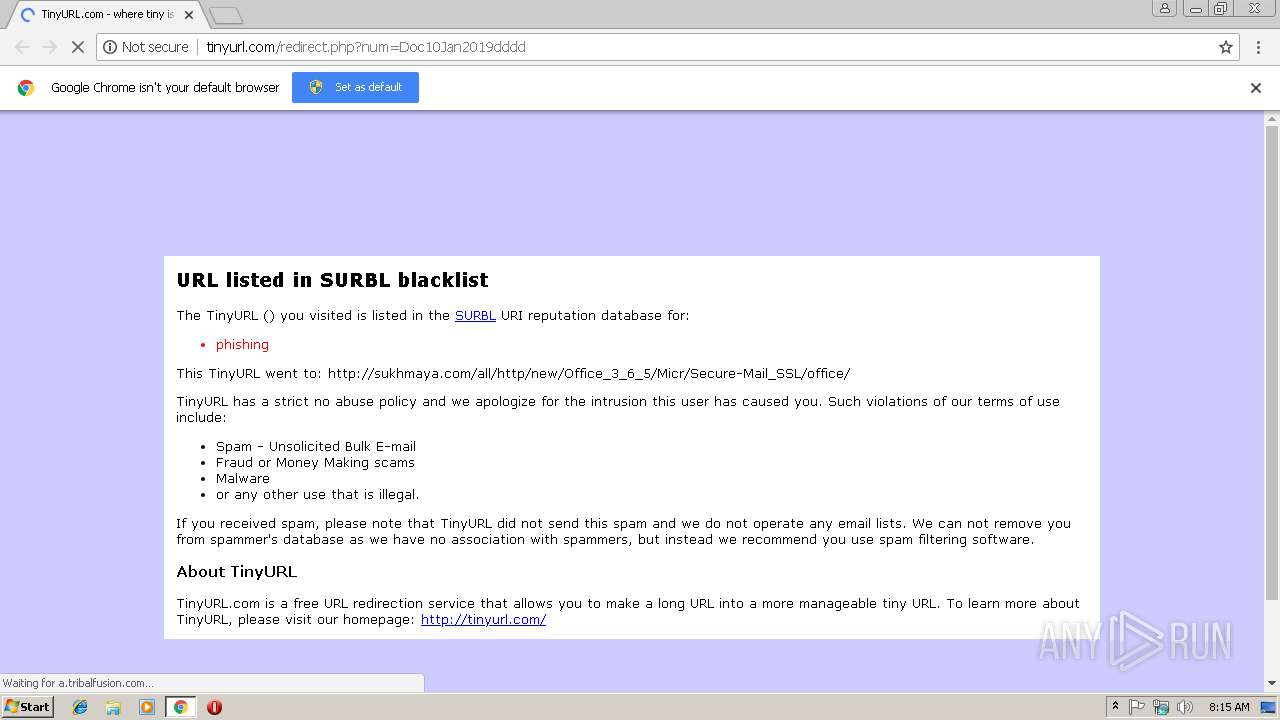
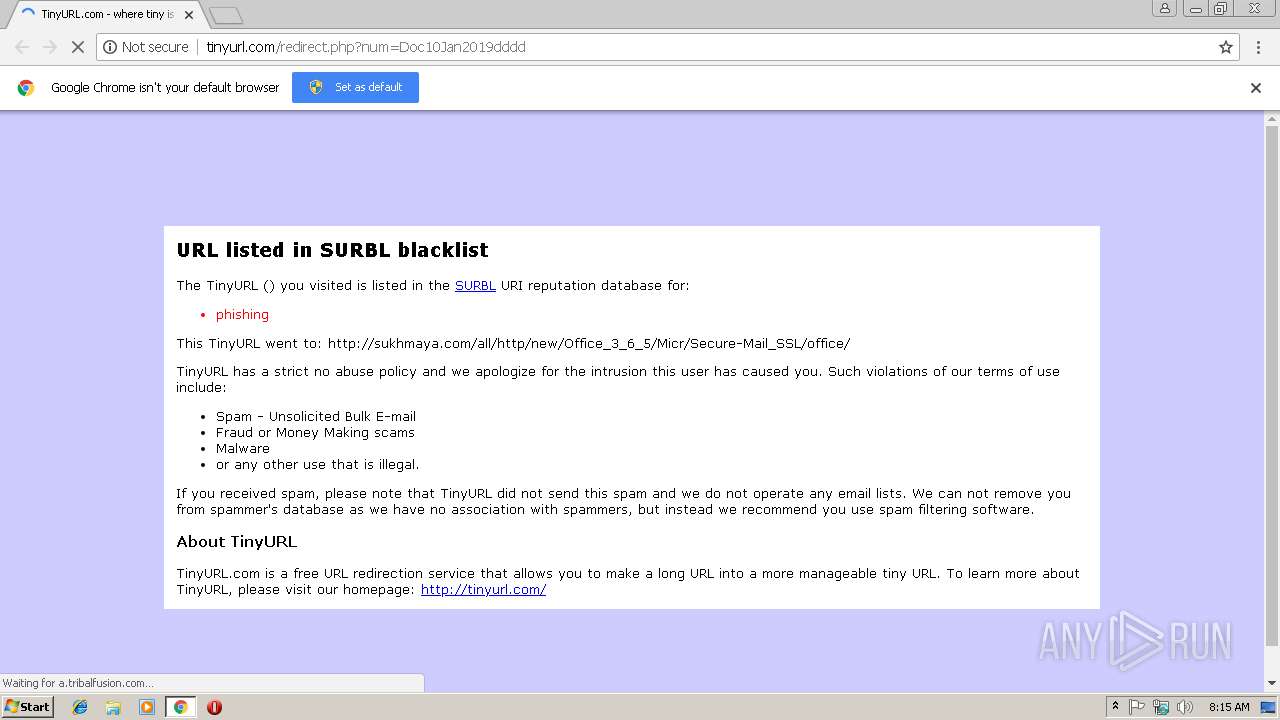
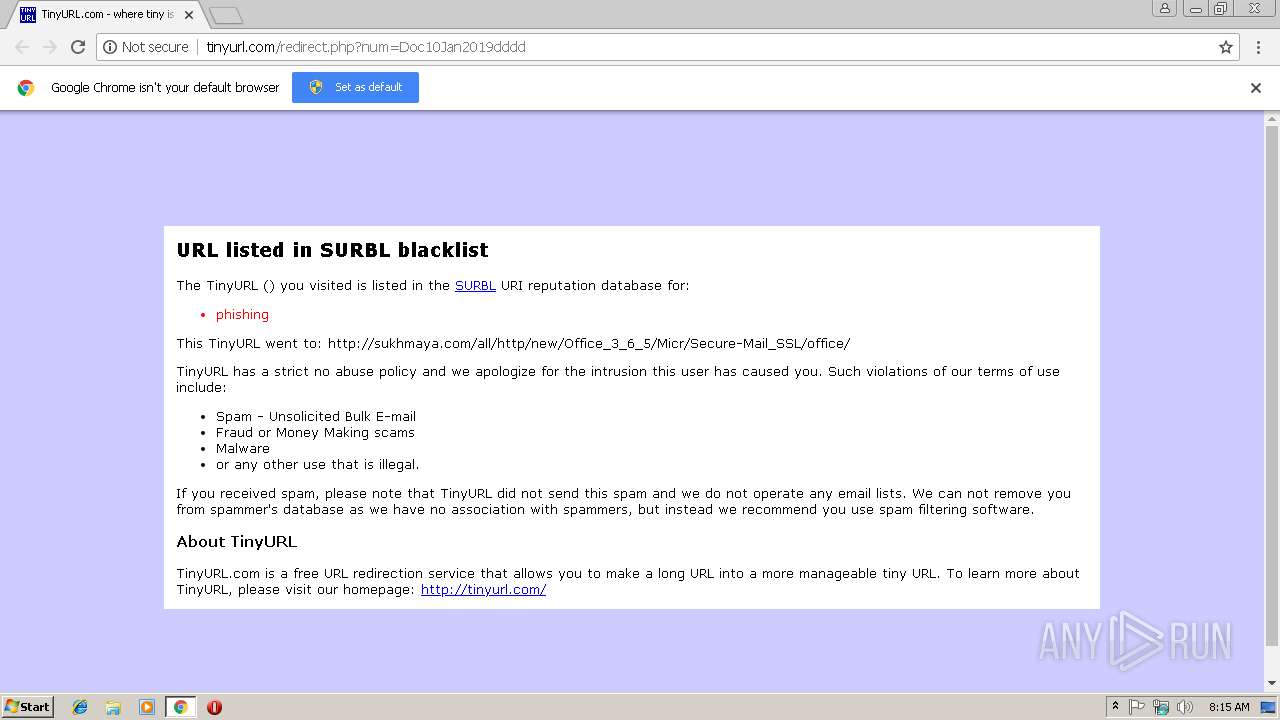
| URL: | https://www.tinyurl.com/Doc10Jan2019dddd |
| Full analysis: | https://app.any.run/tasks/d99af152-5b9c-42ab-89dc-cb13430d2fdd |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 08:14:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C4DD51FF298485E966A913509AFCA4DE |
| SHA1: | AAAC0E1FAE67AB89684BD75D23A8D646F199C4C5 |
| SHA256: | 5660CF6A3731E0261A82E5C1DA7167F98C1E891A25C1A862878B9E21D3B4C395 |
| SSDEEP: | 3:N8DSL+ZLdIQUFiT33:2OL+1dUFW33 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2852)
Reads settings of System Certificates
- chrome.exe (PID: 2852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=852,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=587870EDE714DF2DF9DDF8B0C0206D68 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=587870EDE714DF2DF9DDF8B0C0206D68 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.tinyurl.com/Doc10Jan2019dddd | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2856 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=DC90CB3CE07C5A03967FC8D644DDACD3 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DC90CB3CE07C5A03967FC8D644DDACD3 --renderer-client-id=5 --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=852,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=F4B63269BD6E203505565838A05B2088 --mojo-platform-channel-handle=2360 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=852,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=9219ECD7232D6D48318B7D9669D9667E --mojo-platform-channel-handle=3940 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=852,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=8FC767577AF1E7C24CB24E9688133455 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8FC767577AF1E7C24CB24E9688133455 --renderer-client-id=3 --mojo-platform-channel-handle=1528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
508
Read events
463
Write events
42
Delete events
3
Modification events
| (PID) Process: | (2944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2852-13191668115246000 |
Value: 259 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2852-13191668115246000 |
Value: 259 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
9
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\74802bb0-60c3-48cc-b75f-0942b928756a.tmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\071866ef-44b3-4c3b-80f0-b8c040dde142.tmp | — | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old | text | |
MD5:8CA4BA2B95D7089861A48ED69FDE6561 | SHA256:AA64C14D0C68B62BBAB62A6D6FA4662FF89E1FBC7B337C926AC213C191D6406C | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF198999.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
48
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2852 | chrome.exe | GET | 302 | 52.58.79.83:80 | http://pixel.advertising.com/ups/57628/sync?uid=18072662434940820237&_origin=1&redir=true&verify=true | DE | — | — | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/p.media?clickID=aWmRwQXWnAntIm56nS4VvgVVQ6VVbjSAFmWtJUUFM05U6qUarvWTr7Pq3ZcSGQLRbmpRWniWsj34UupodipYaPN3H3APGBZa26rHpWXnUHQ70bUcYbbi0EIMRUJGWUQ0THQWmUjsQFvNYqFo3Eji5E3RmaMC1rZbfUWMSoAbBpsMomWQE2aZbe5t6o56BKnb3GYcMTXGFVVrbKgsv1Eg&mediaDataID=8039566&mediaName=frame.html | US | html | 262 b | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/p.media?clickID=aQmRwQR6ZbK2HQoXH3InHIo4AM14cMbUsJlUsngR6FuWWvQWbbP2b6sVTnoVaJcSEJZdSGBCPUmxRWvaUVMS5UXsnHZamYT6p4tYZdPsrB56JZbmdINUWFbXFUkYbYeXaaqPUQZbUrM4WdFWmFQrRFZbsXavy5aUk2avRmEMD1rYfTdjWnAnJmc7pmHvF3arj3dIy46jImUbETrr78ZbeUNZd&mediaDataID=6347136&mediaName=frame.html | US | html | 188 b | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.78:80 | http://tags.expo9.exponential.com/tags/TinyURLcom/ROS/tags.js | US | html | 2.25 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/p.media?clickID=a3mRwQ36nY5cneTs3bWcf8SmnNTH3QTbMR5rPmWEjpTar9SEYFRVjZaQUaoRW7bUGjU4UmxmHyMXamx4dMDPVZbB5PnImWZayVHjhYUf9XFYfXaIsRr3CTUMSVHJ2orBoRbjNYavn4EYa4T72oEFAXUffUtMRoAnBnV7nmHbJ2arf3Hus46vZdprrIXcQVYsMT1cjOmqv4QcYdaxQ6sg&mediaDataID=6530936&mediaName=frame.html | US | html | 234 b | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/j.ad?flashVer=0&ver=1.28&th=7428607684&tagKey=2665270249&loaderVer=0.1&site=tinyurlcom&adSpace=ros¢er=1&json=1&callback=e9Manager.setSingleAdResponse&env=display&size=728x90,468x60&busted=1&url=http%3A%2F%2Ftinyurl.com%2Fredirect.php%3Fnum%3DDoc10Jan2019dddd&f=0&p=14449584&tKey=aMmneMmdEsYaXv3tjCQcZbBRDUyRNjXJK&a=3&adContainerId=richmedia_4&rnd=14450405 | US | text | 2.10 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 104.20.218.42:80 | http://tinyurl.com/redirect.php?num=Doc10Jan2019dddd | US | html | 1.95 Kb | shared |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/j.ad?flashVer=0&ver=1.28&th=7428607684&tagKey=2665270249&loaderVer=0.1&site=tinyurlcom&adSpace=ros¢er=1&json=1&callback=e9Manager.setSingleAdResponse&env=display&size=728x90,468x60&busted=1&url=http%3A%2F%2Ftinyurl.com%2Fredirect.php%3Fnum%3DDoc10Jan2019dddd&f=0&p=14449584&tKey=aMmneMmdEsYaXv3tjCQcZbBRDUyRNjXJK&a=1&adContainerId=richmedia_2&rnd=14451502 | US | text | 3.36 Kb | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/p.media?clickID=a1mRwQ3AJGnbvZaXVbYXGQV1sfumTnR2FF4TUMGWm74RqY3SsUMPtfx0WbpVPbw4cJ5XF3DTPau4AU6R6bG3Hro1tvZdpWAo3mMY4GjdUsJdUcjhSAZbuTHv3UFM15bZanUErvVqr8PEZbFScQZaRbAnSd3iWcbU2Fuxmtqq0qap3WvBPcbZc5PJZcmdImTtfdXrQiXrZbj1EqM4VUsbtUPLP&mediaDataID=4056396&mediaName=frame.html | US | html | 195 b | whitelisted |
2852 | chrome.exe | GET | 200 | 204.11.109.68:80 | http://a.tribalfusion.com/p.media?clickID=aYmRwQ2mvHotArUtZbdYrMkXrQiXqetSrJZdWFZb1VHJ3oFjtRFjNXEvo4qJl4T71oErCYbFfUdr0mPnJpGvspWQE2ark2tuN3PFGmFbJYVfP1cv31GfymaF43bFWTF7HUmvTPaY2PsBMQHUxYdBmWAYp2GB50UUDT6in2PBeQAnB3Wno1tBJpdZaN5AvU5cUeUG39VGM849YJetYvje&mediaDataID=6807466&mediaName=frame.html | US | html | 254 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2852 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 104.20.219.42:443 | www.tinyurl.com | Cloudflare Inc | US | shared |
2852 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 204.11.109.78:80 | tags.expo9.exponential.com | Exponential Interactive, Inc. | US | unknown |
2852 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2852 | chrome.exe | 204.11.109.68:80 | a.tribalfusion.com | Exponential Interactive, Inc. | US | unknown |
2852 | chrome.exe | 52.222.161.55:80 | rules.quantcount.com | Amazon.com, Inc. | US | unknown |
2852 | chrome.exe | 52.58.79.83:80 | pixel.advertising.com | Amazon.com, Inc. | DE | unknown |
2852 | chrome.exe | 104.111.241.32:80 | tags.bluekai.com | Akamai International B.V. | NL | whitelisted |
2852 | chrome.exe | 172.217.18.98:80 | cm.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.tinyurl.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
tinyurl.com |
| shared |
tags.expo9.exponential.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
connect.facebook.net |
| whitelisted |
www.facebook.com |
| whitelisted |
edge.quantserve.com |
| whitelisted |