| File name: | file.ps1.ps1 |
| Full analysis: | https://app.any.run/tasks/bd14941d-ecf9-4c59-ab5a-64f6565d82d2 |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2024, 13:06:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 94960084387D2D9387C9076EAD2A0364 |
| SHA1: | 7CD1E6A70B93036E4F296AD7AAA0A52CB961A196 |
| SHA256: | 565A293E439602865756B8FE9C275C5FB4299C8E893904F80937B0BCAD73DB02 |
| SSDEEP: | 48:/A6kszmW4ivd/ckzRap9KLNaHw2ZEwO4kuAcGBX55PMbjHy4ApCWw:/FzzmW4ivd/c4LR2OgAcQJq/p |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 3732)
- powershell.exe (PID: 6012)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 3732)
SUSPICIOUS
The process executes Powershell scripts
- powershell.exe (PID: 3732)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 6012)
- powershell.exe (PID: 3732)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 3732)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3732)
Application launched itself
- powershell.exe (PID: 3732)
INFO
The process uses the downloaded file
- powershell.exe (PID: 3732)
- powershell.exe (PID: 6012)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6012)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6012)
Disables trace logs
- powershell.exe (PID: 6012)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6012)
Checks proxy server information
- powershell.exe (PID: 6012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
121
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3732 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\file.ps1.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5696 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6012 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -noexit -ExecutionPolicy Bypass -file "C:\Users\admin\Desktop\file.ps1.ps1" -elevated | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 489
Read events
10 488
Write events
1
Delete events
0
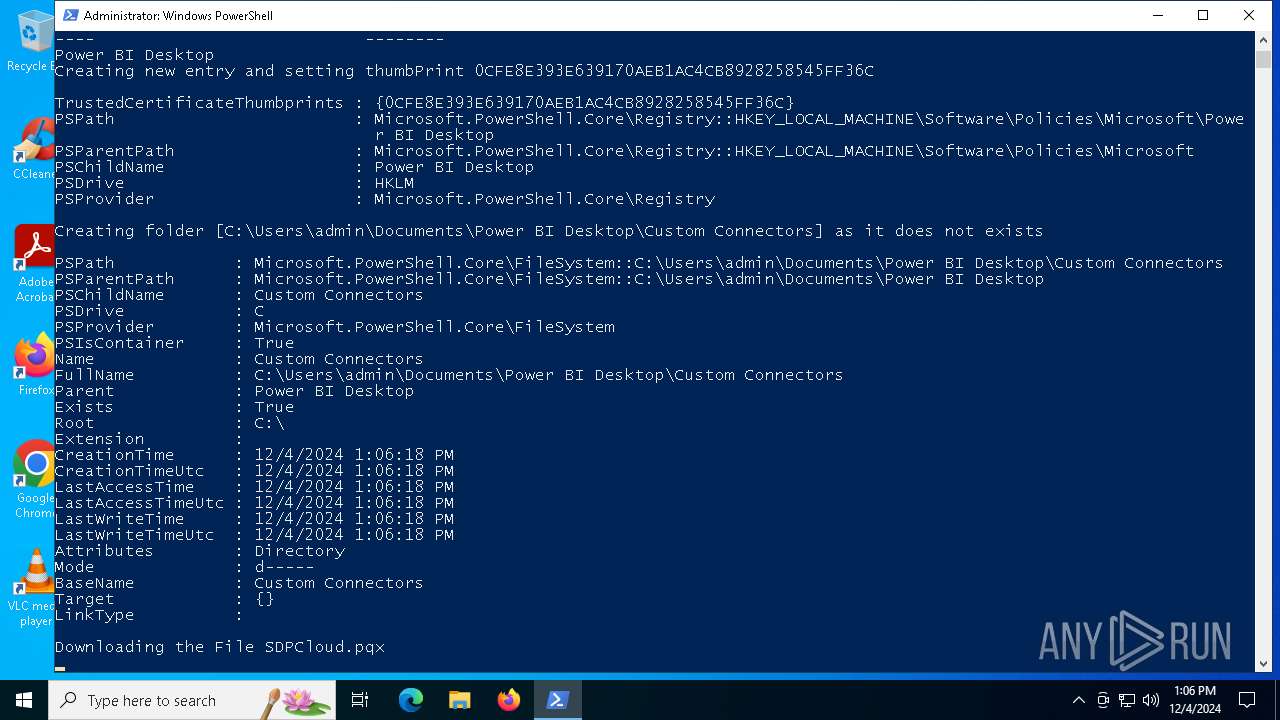
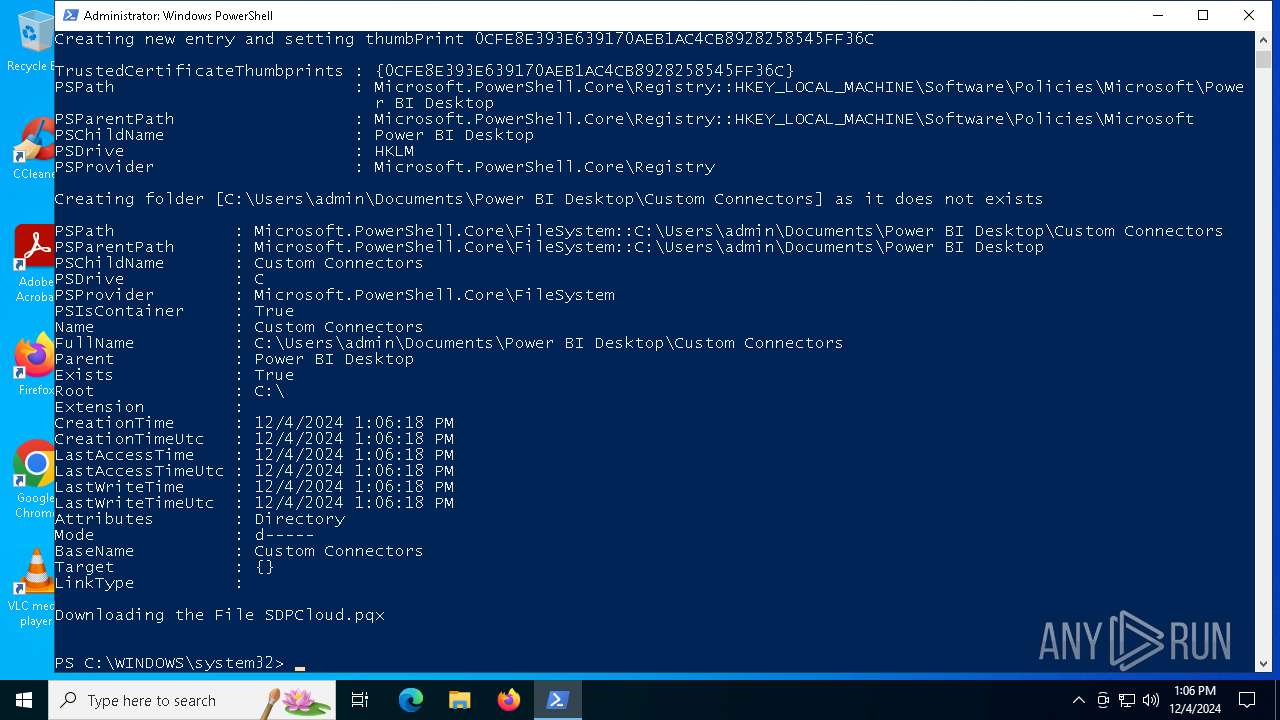
Modification events
| (PID) Process: | (6012) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Power BI Desktop |
| Operation: | write | Name: | TrustedCertificateThumbprints |
Value: 0CFE8E393E639170AEB1AC4CB8928258545FF36C | |||
Executable files
0
Suspicious files
8
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3732 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:240B68948069C9FFB2728131796915FC | SHA256:3ECC971A3AA460873CB266764364A7ABD95AED98506B5084B5CCF8C0940B23A1 | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L7IRJ2CXYGNAR3L178ZN.temp | binary | |
MD5:63D54EFB533C5366B3D4D4CFA6A0B3A9 | SHA256:D7BD78986D3B8BD8C9A6ED5D8A5423244635B13E40AE99662FD0431F10F3F73B | |||
| 6012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:D50C05FC4E9F871EA1ED933EBB872532 | SHA256:D184760E46B9E2EF3B769E4F0BC0DC302BD720B3BBF791E72328956A1420F1DF | |||
| 6012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4ATEX1YFM6X661CRJX75.temp | binary | |
MD5:D50C05FC4E9F871EA1ED933EBB872532 | SHA256:D184760E46B9E2EF3B769E4F0BC0DC302BD720B3BBF791E72328956A1420F1DF | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0b3h4sed.2qc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF135d75.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hczv1b0j.gj5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tid3q1oa.lw1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6012 | powershell.exe | C:\Users\admin\Documents\Power BI Desktop\Custom Connectors\SDPCloud.pqx | compressed | |
MD5:8C9673D8663FE5E4C27D997B2464CF93 | SHA256:EED1859D76D56A8A14CCEA88DE88F777BF186BF557DB204E8ADFDC28224DDD15 | |||
| 3732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qzhnkcvl.nnr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
372 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | GET | 200 | 204.141.42.100:443 | https://sdpondemand.manageengine.com/SDPCloud.pqx | unknown | compressed | 35.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
372 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
372 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
crl.microsoft.com |
| unknown |
www.microsoft.com |
| unknown |
sdpondemand.manageengine.com |
| unknown |
self.events.data.microsoft.com |
| unknown |