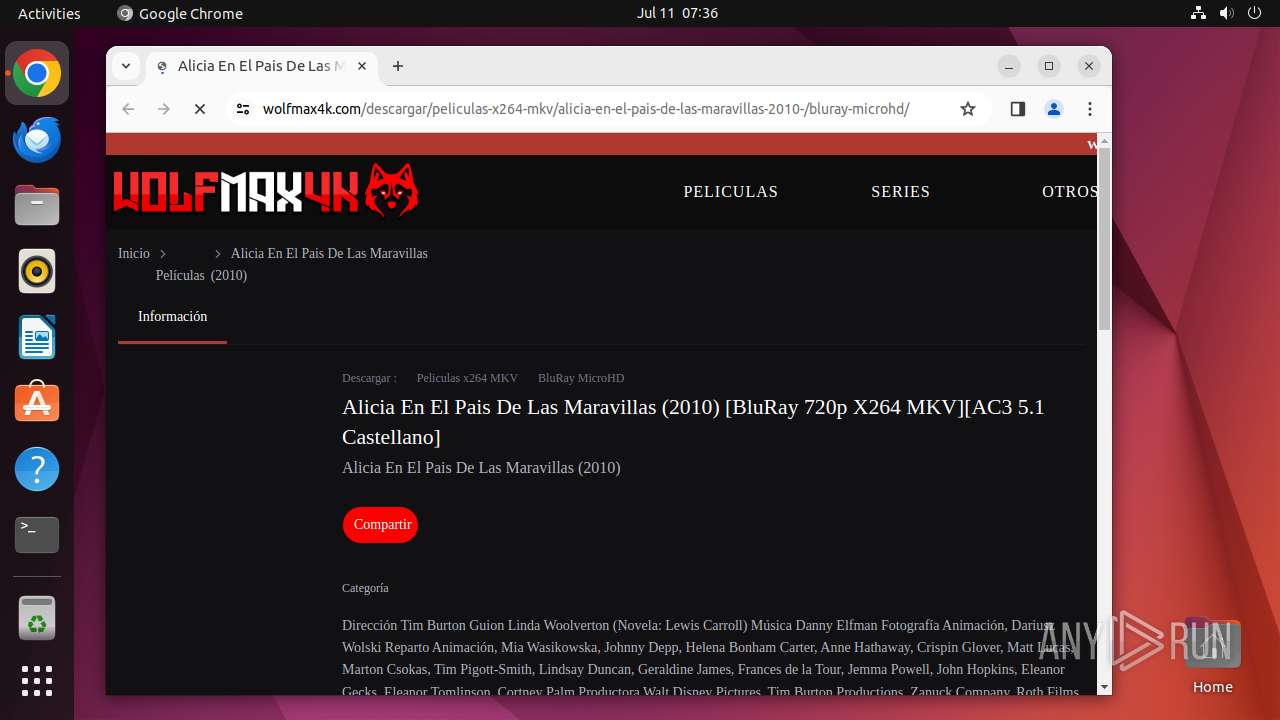
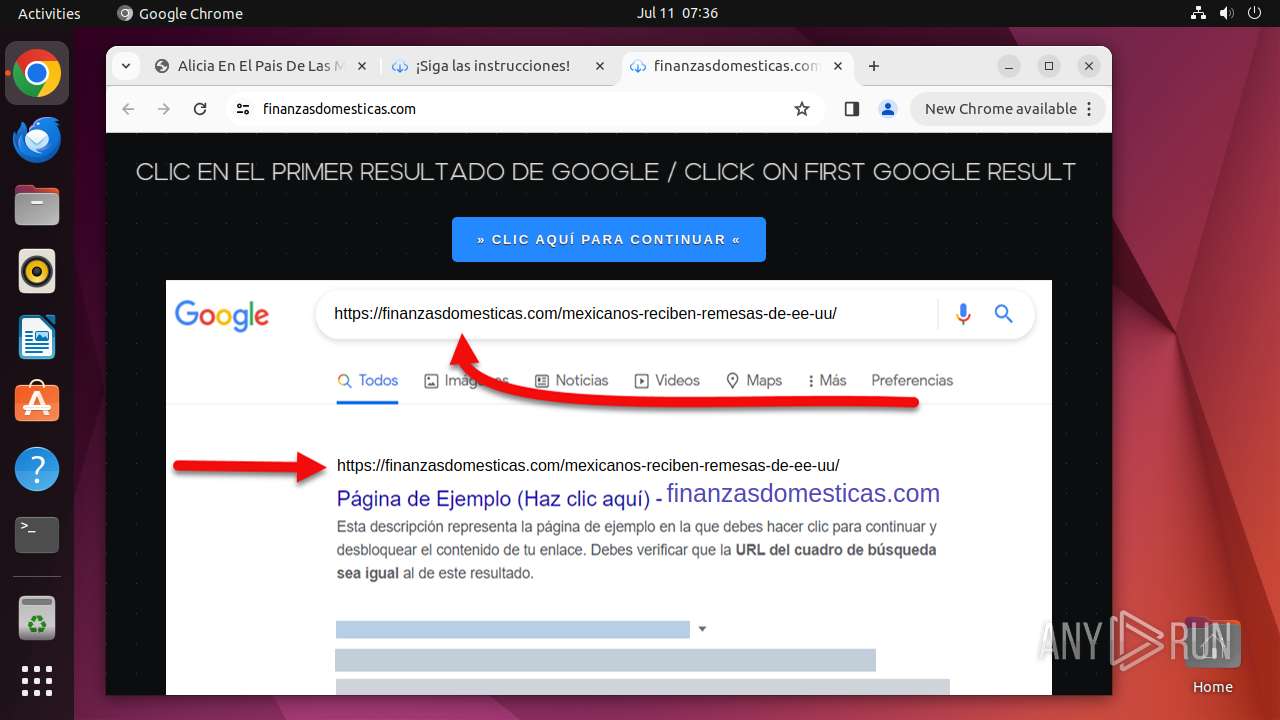
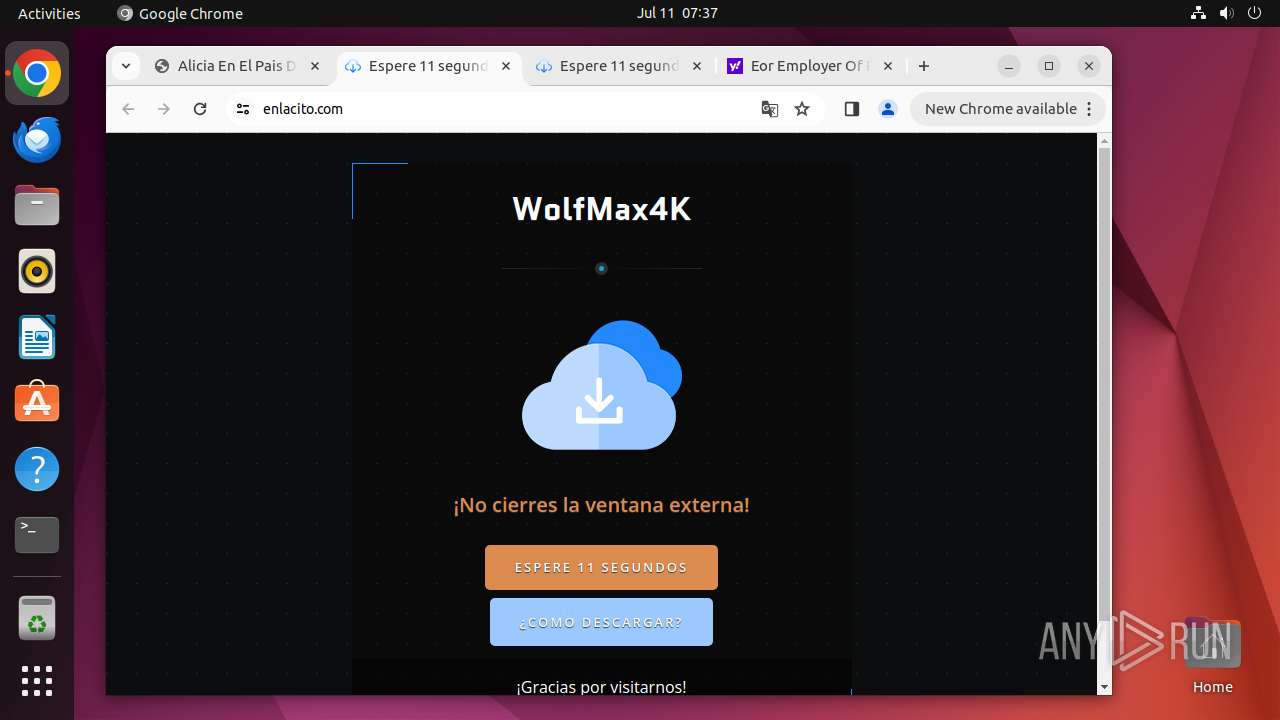
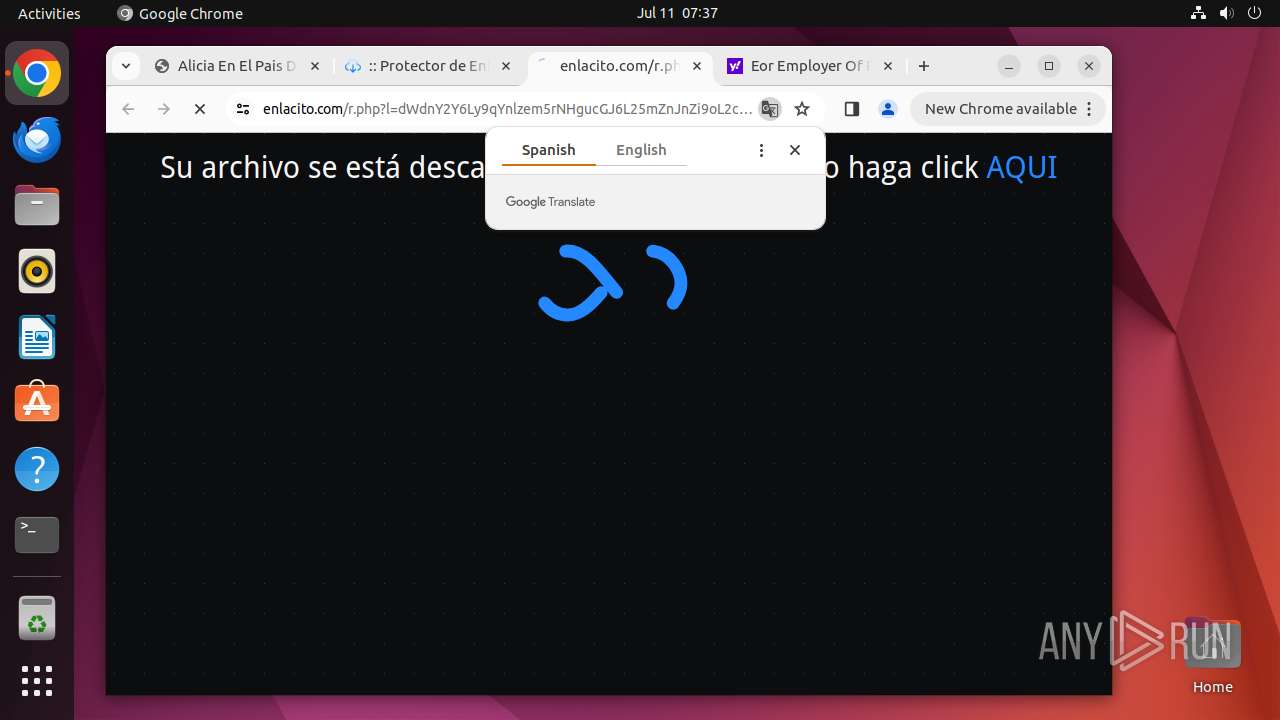
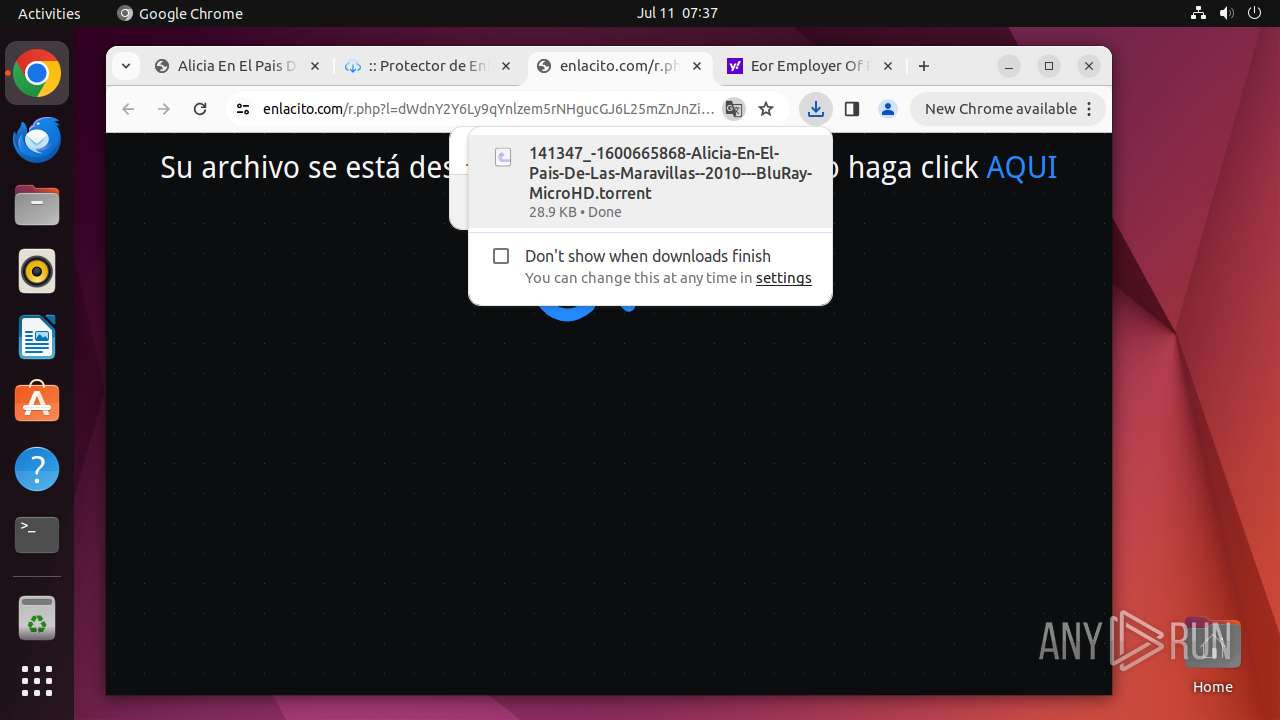
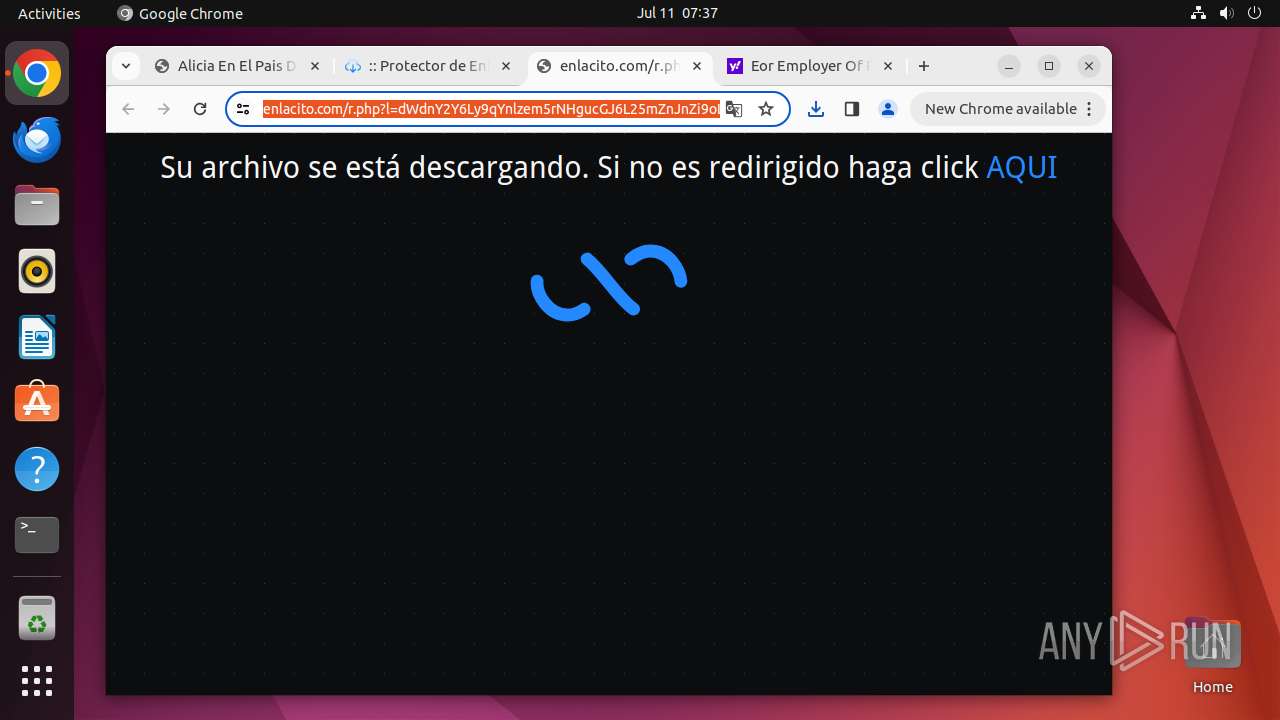
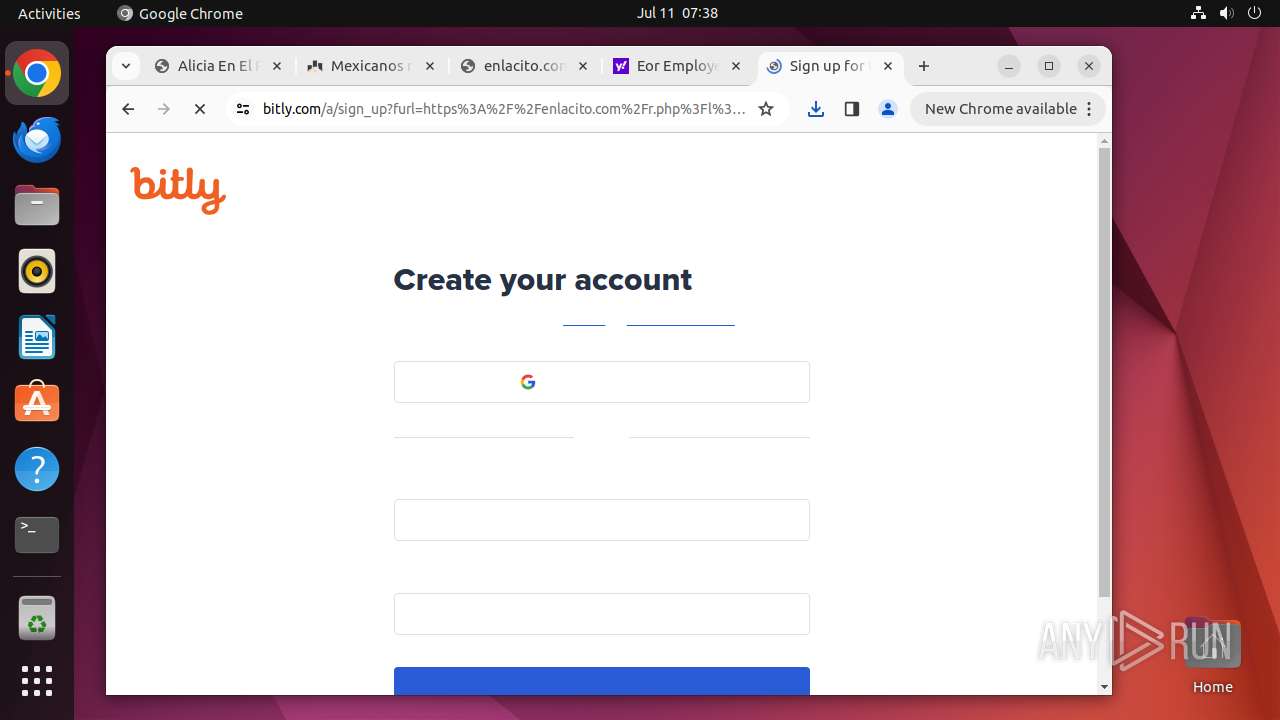
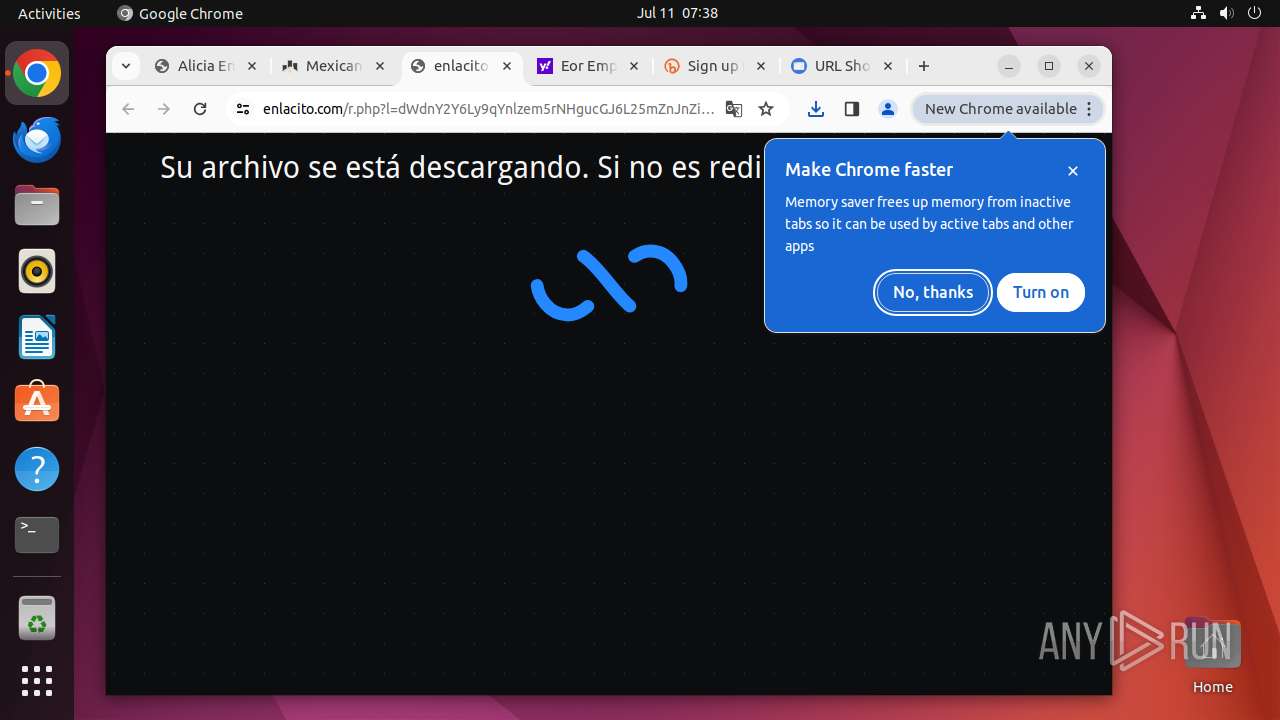
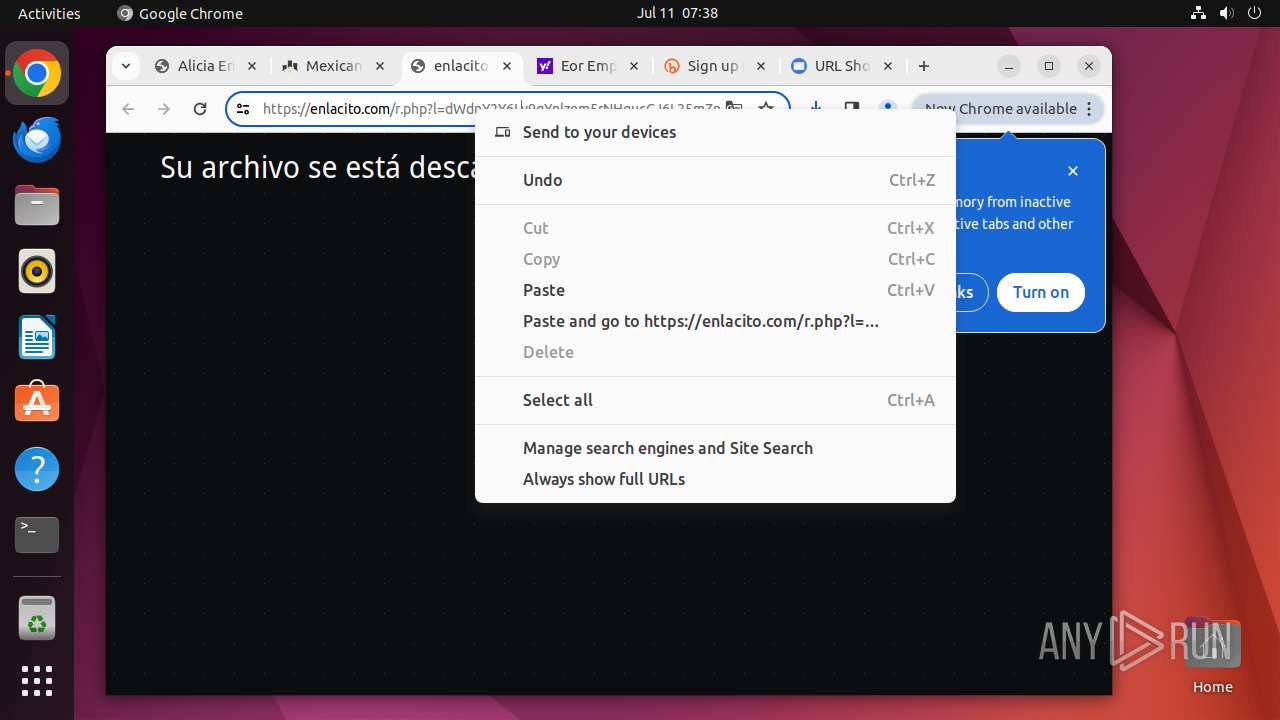
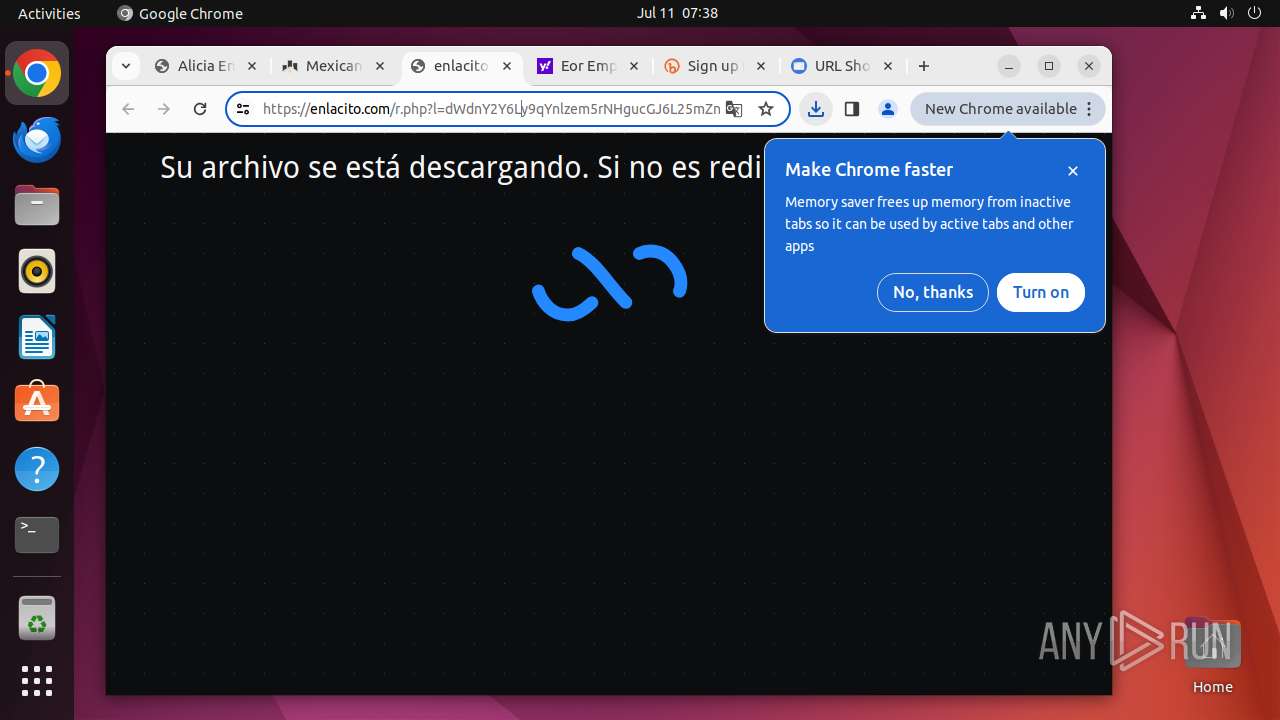
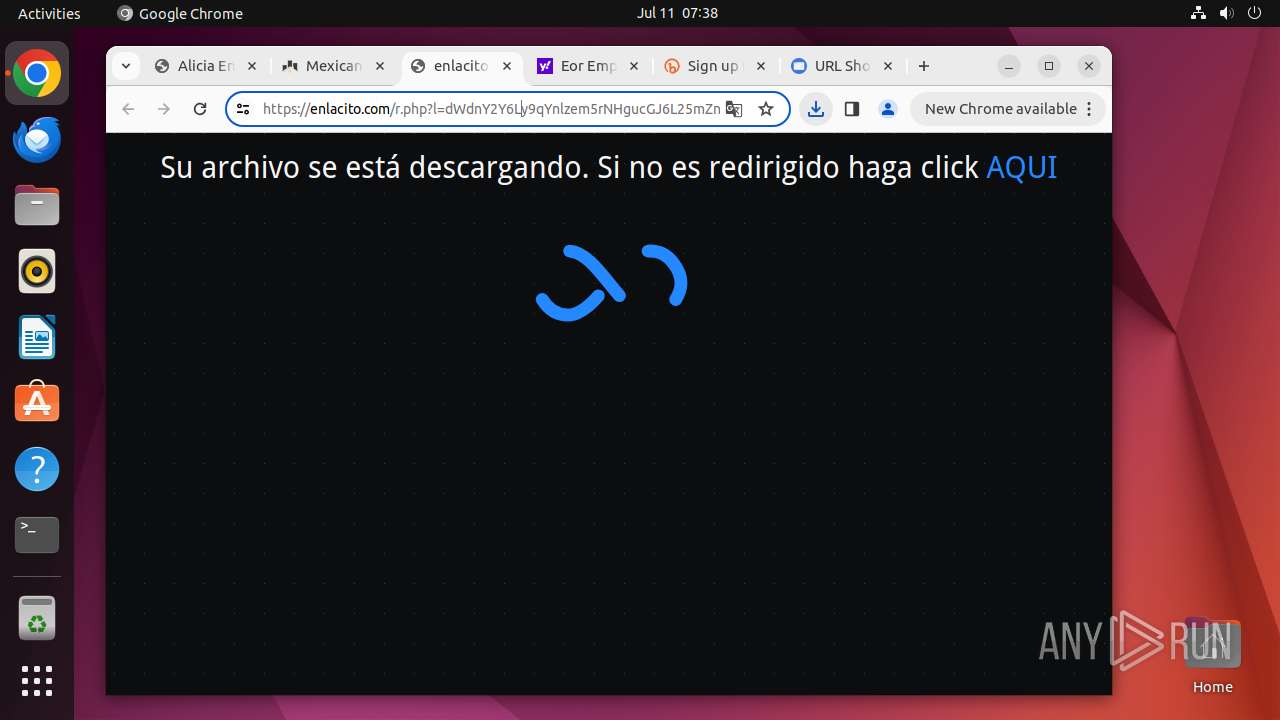
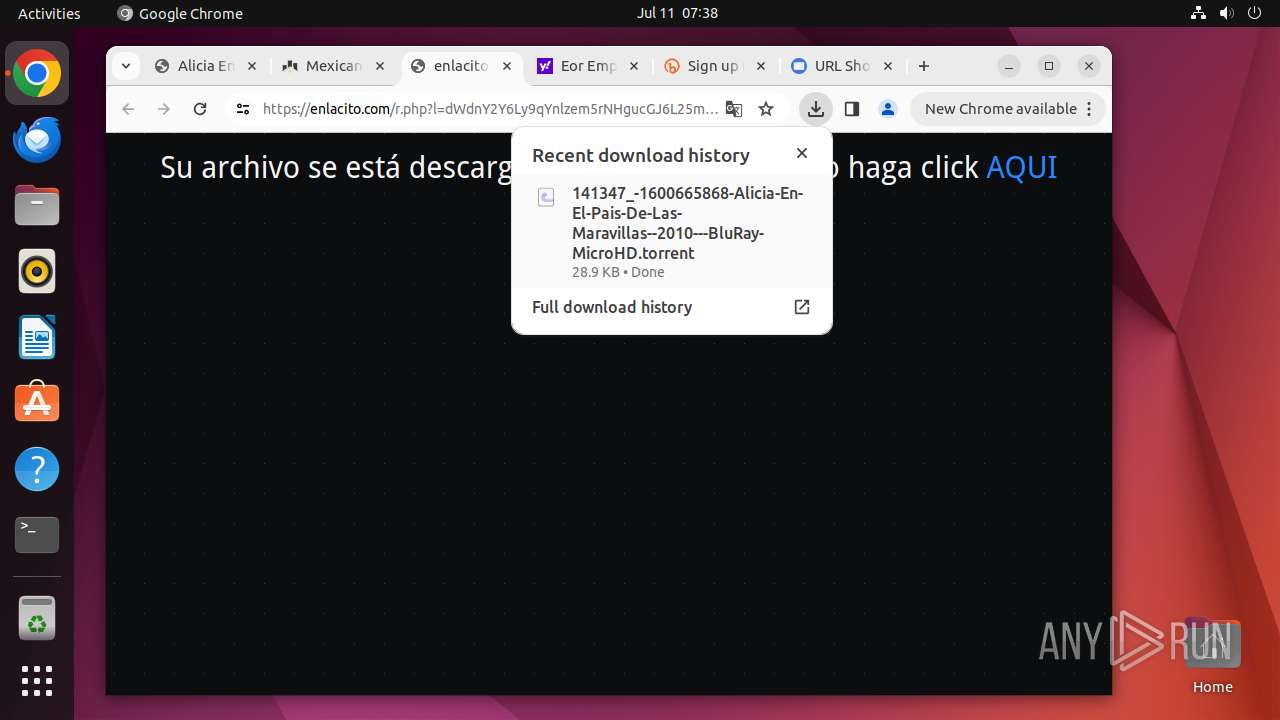
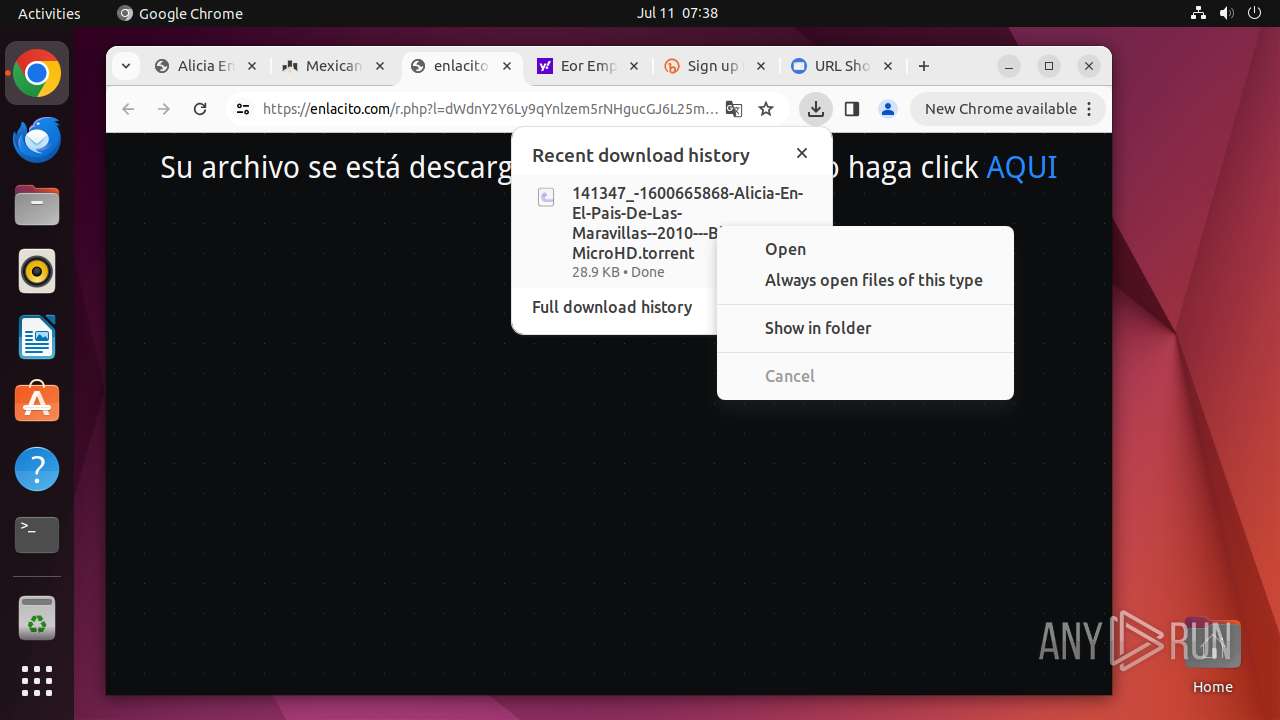
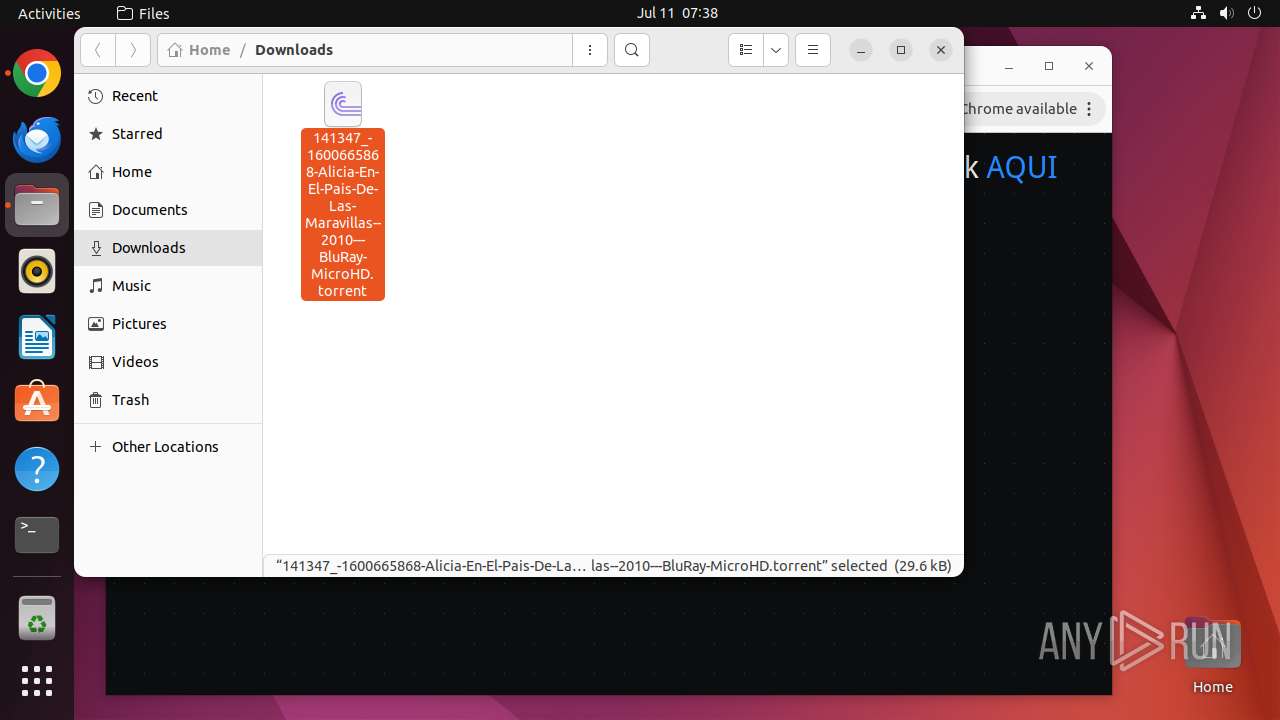
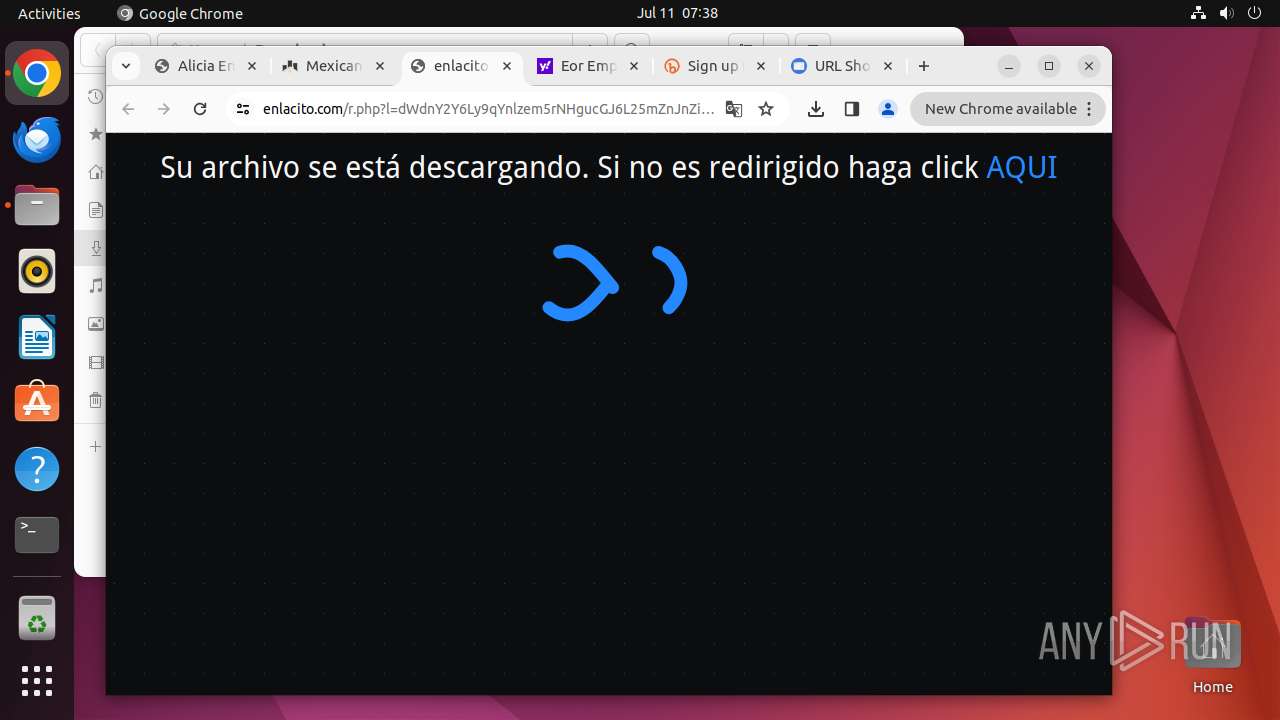
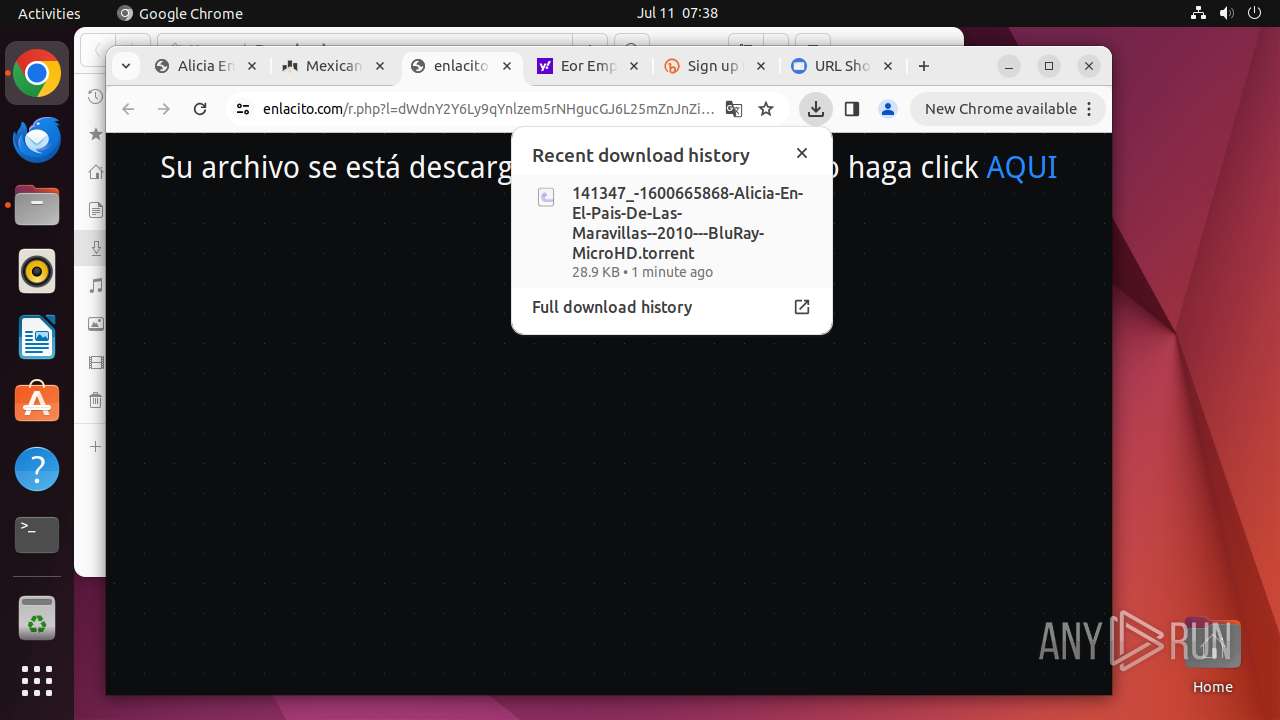
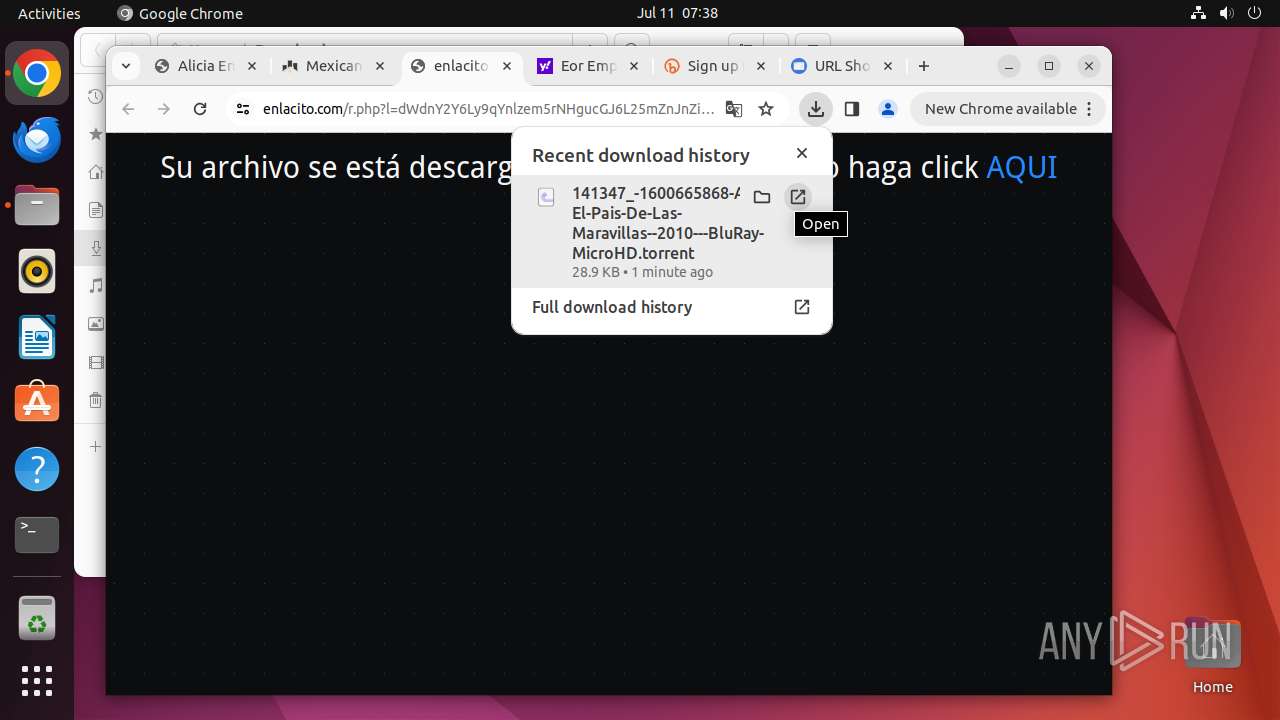
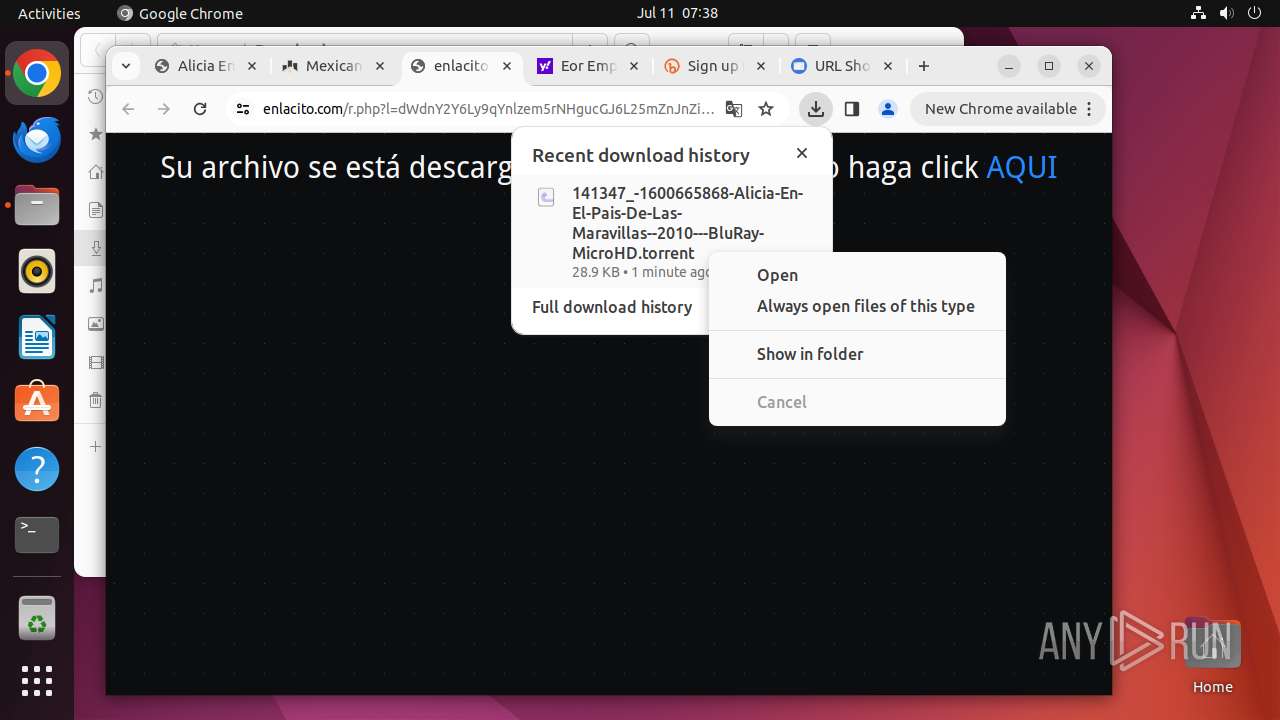
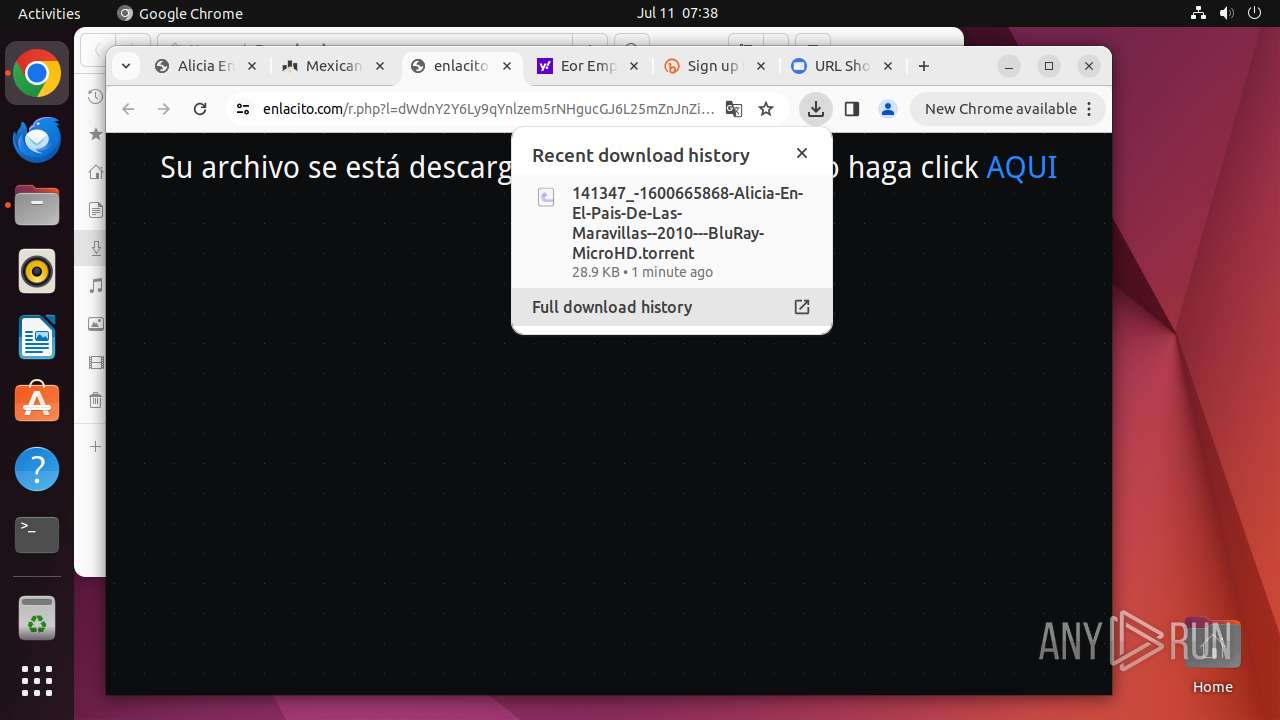
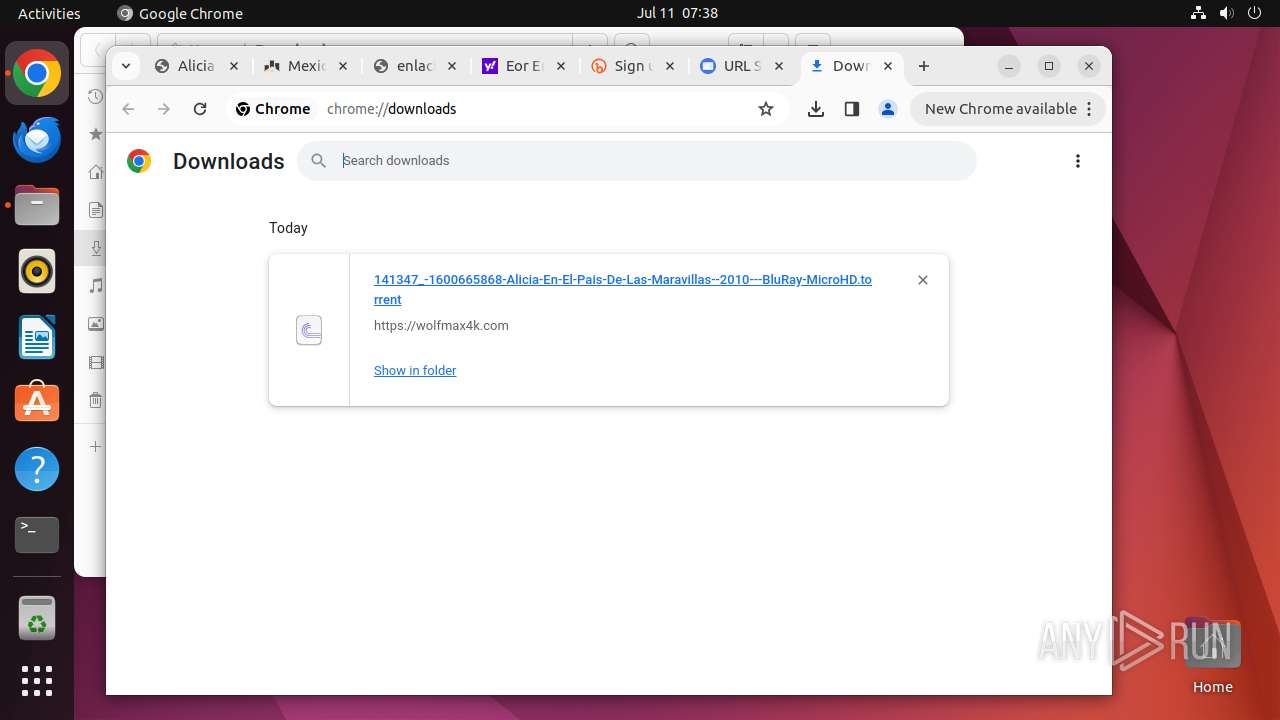
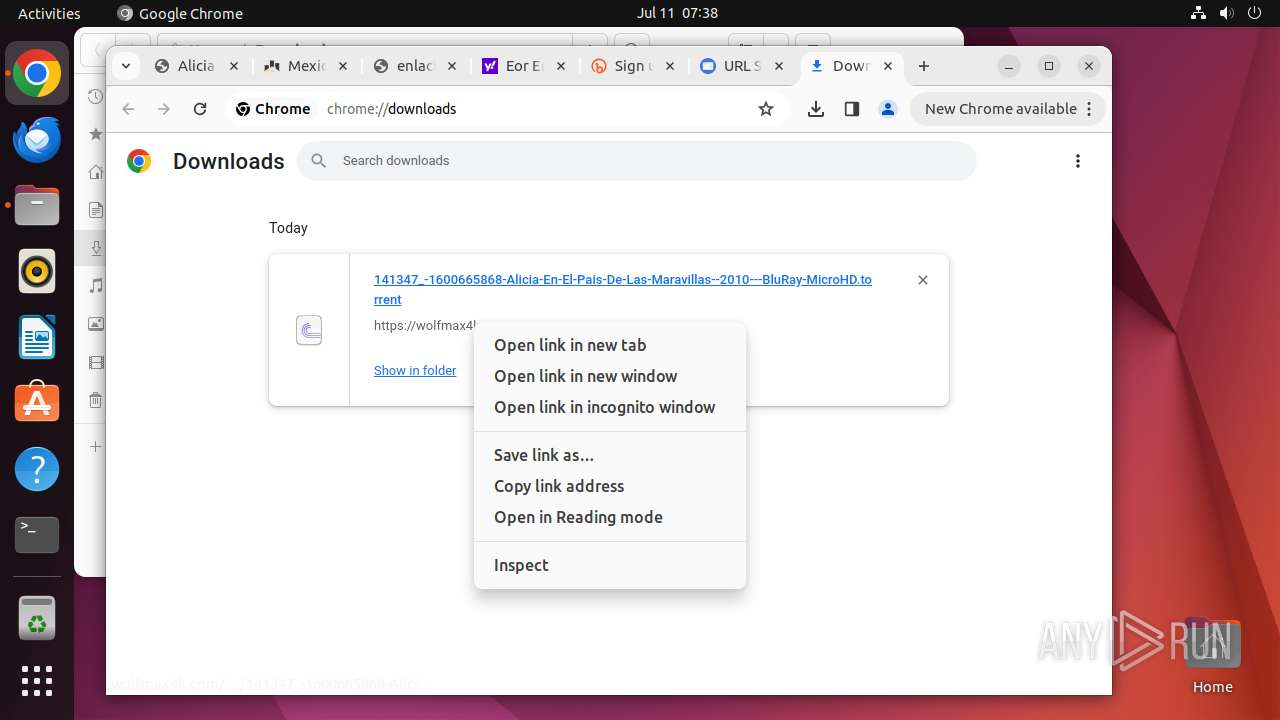
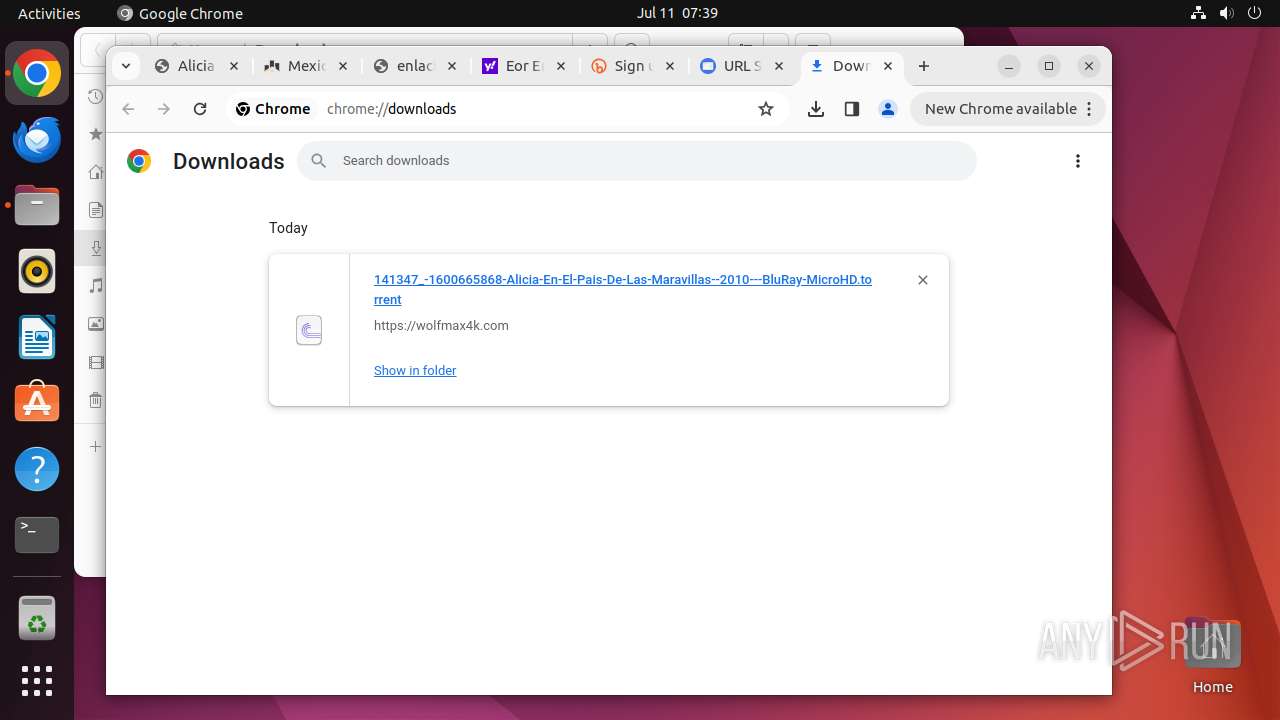
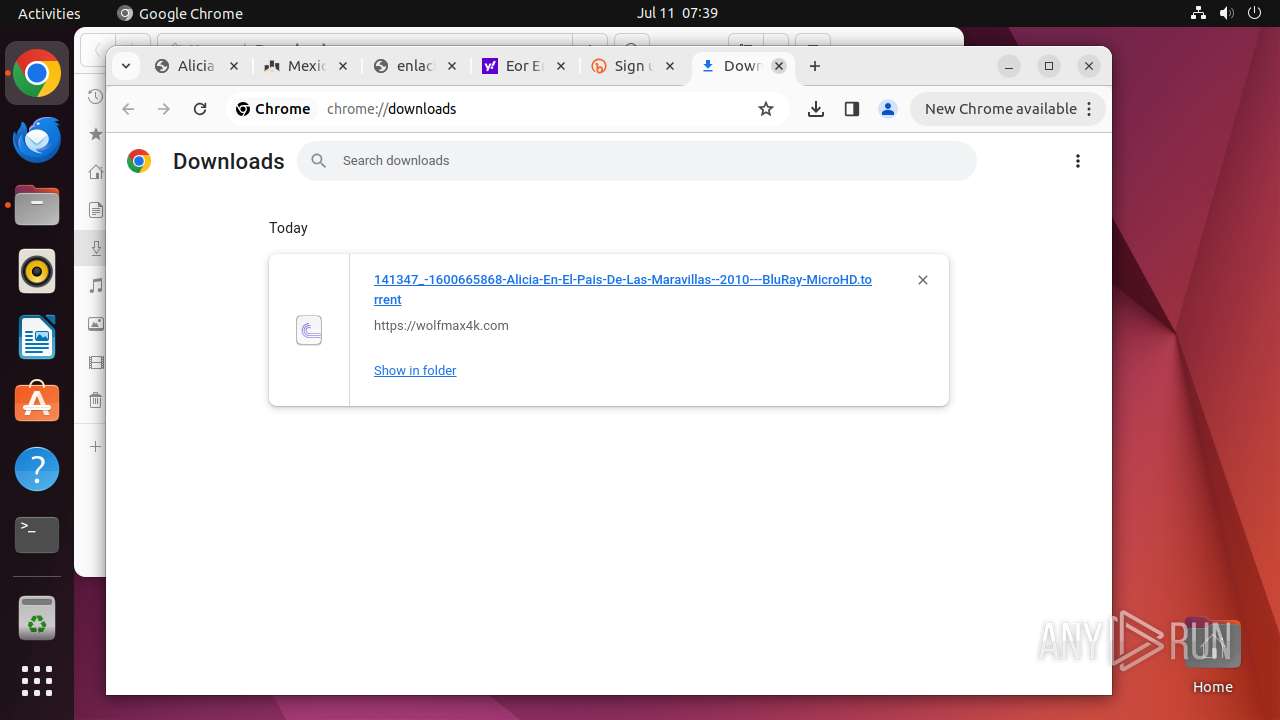
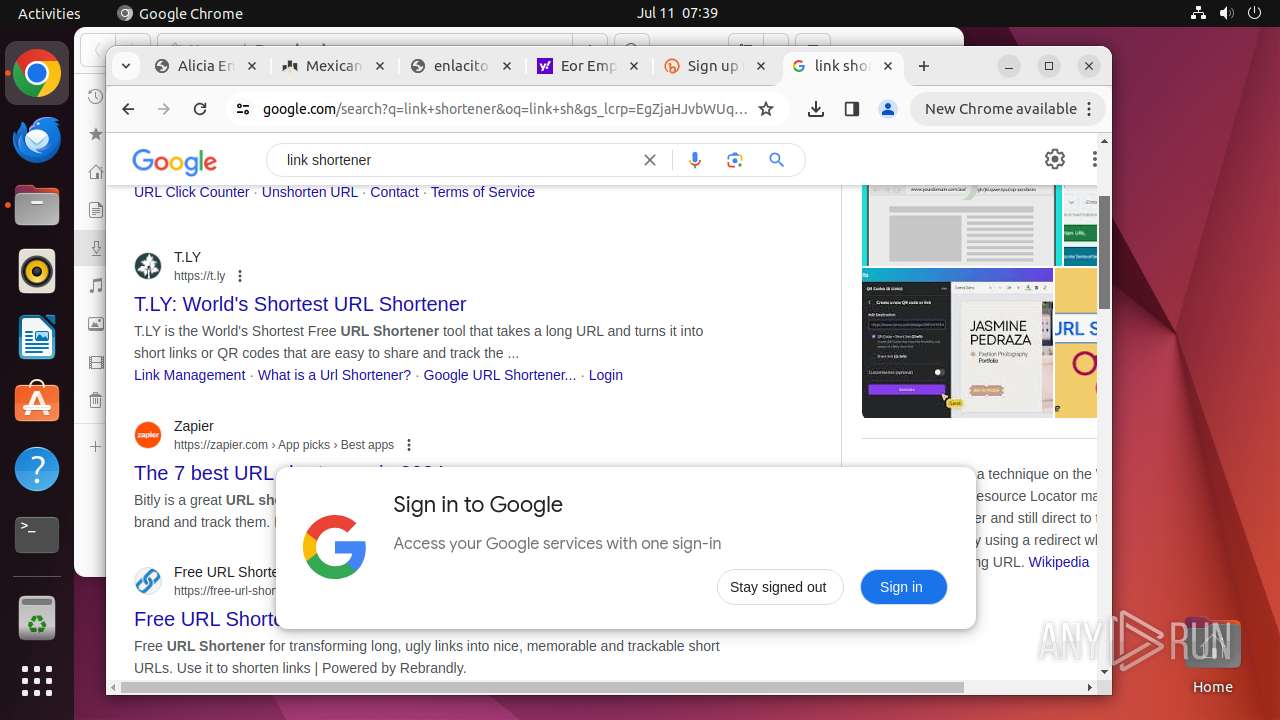
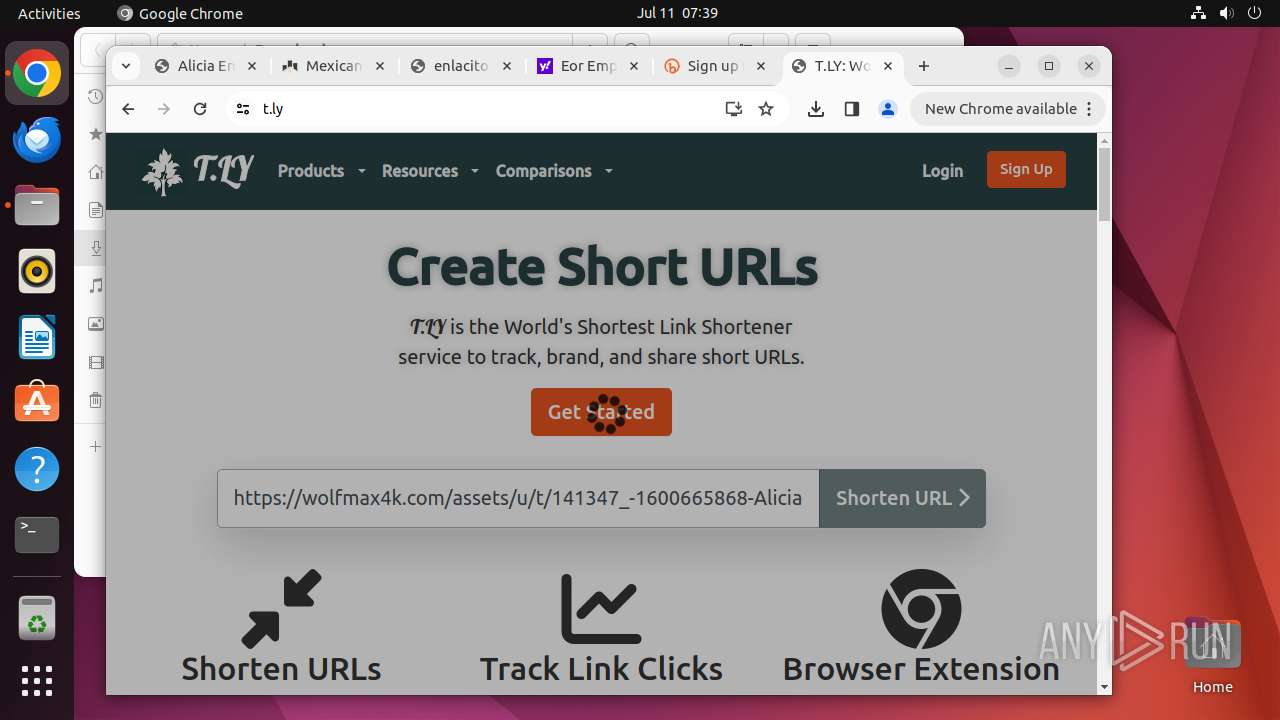
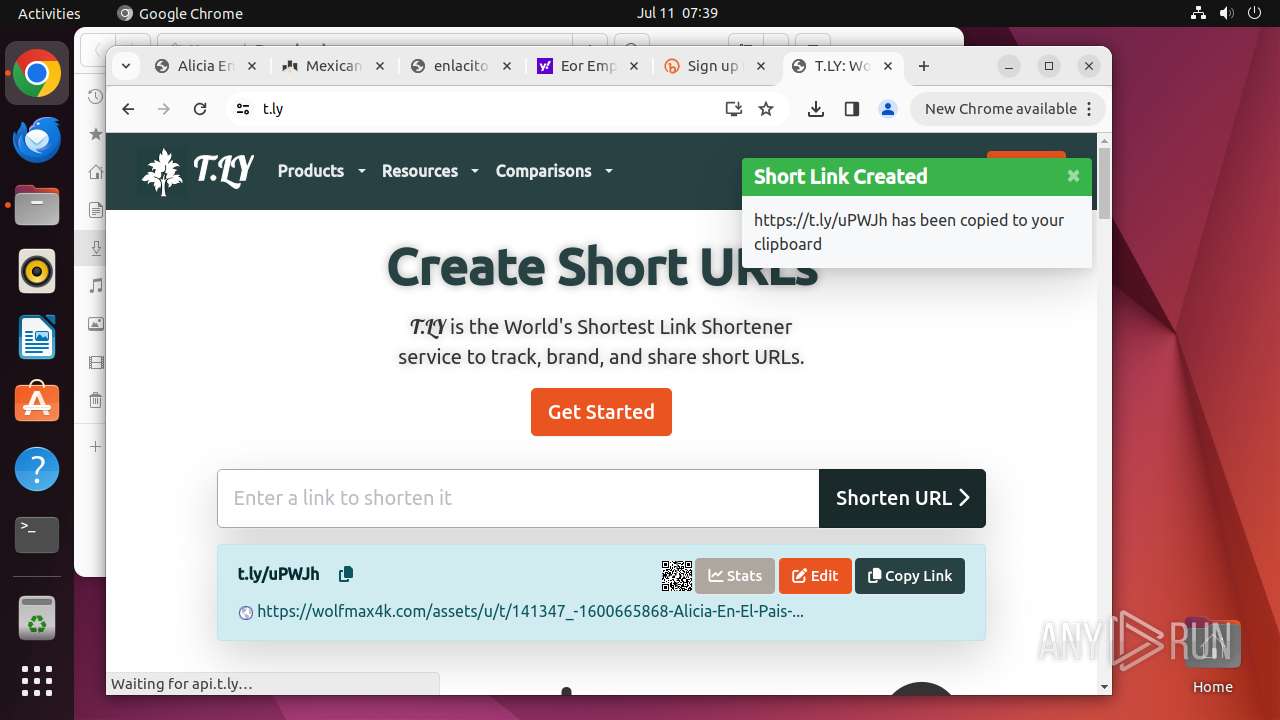
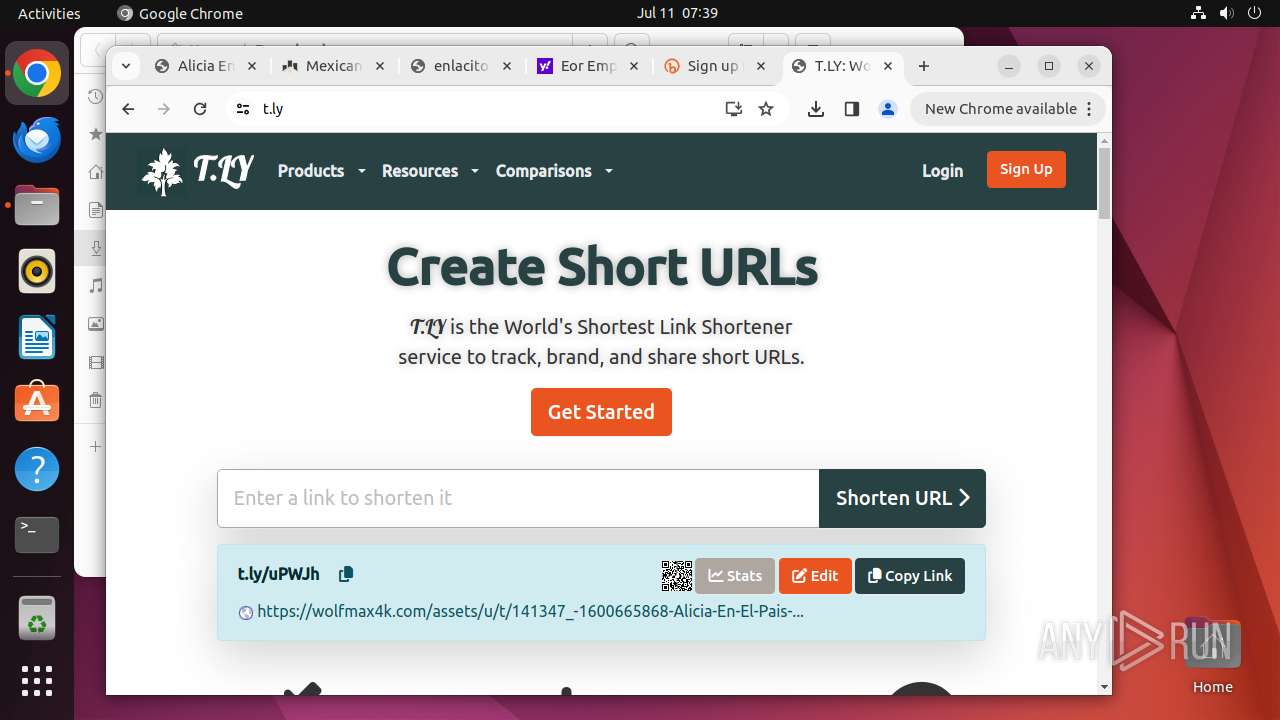
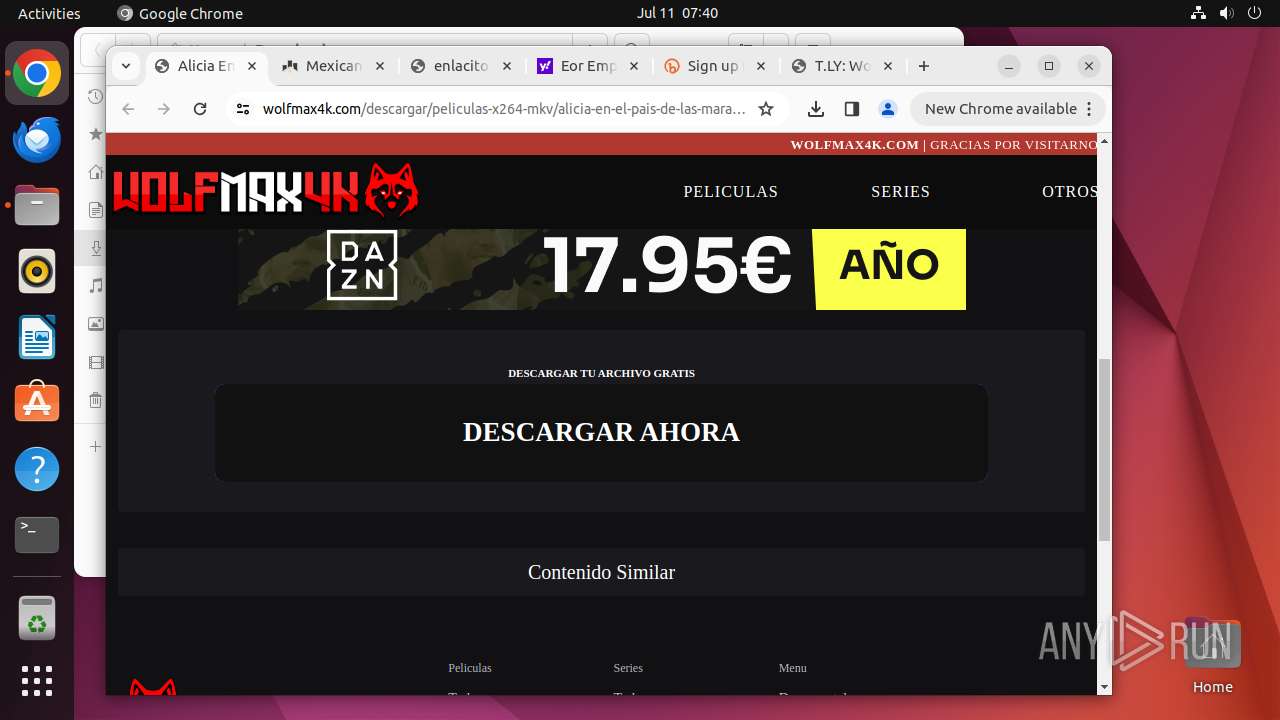
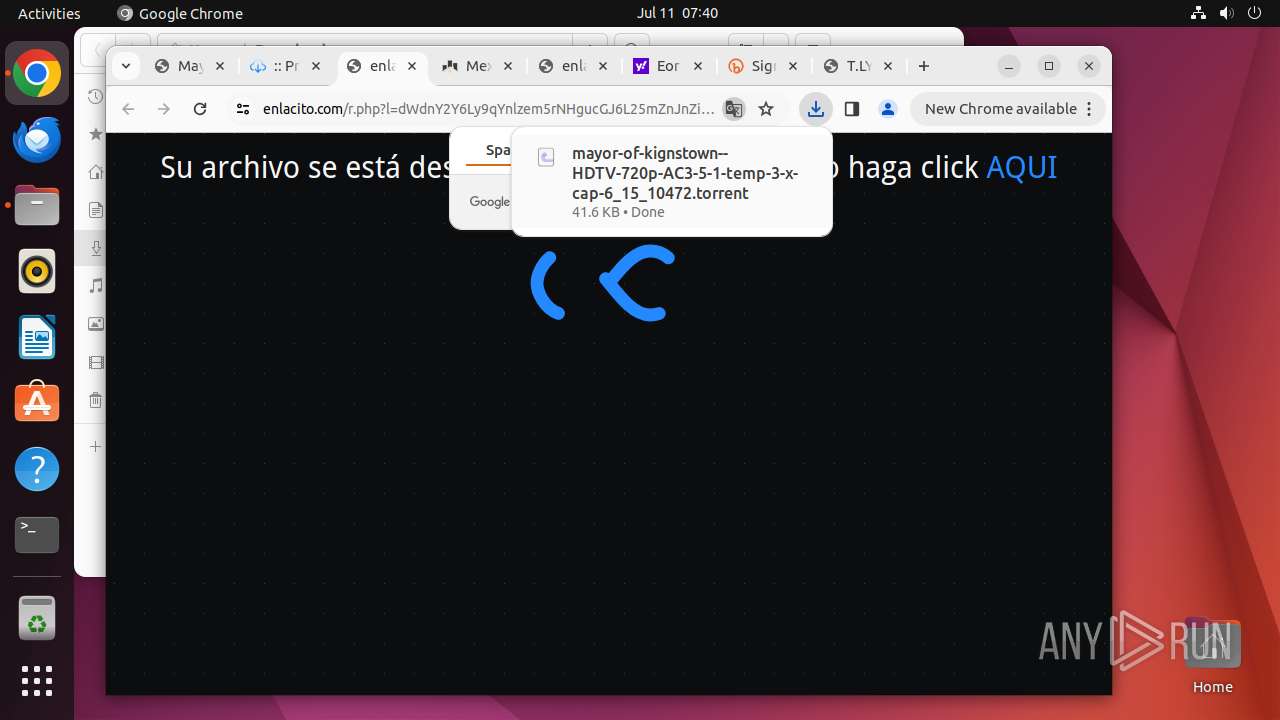
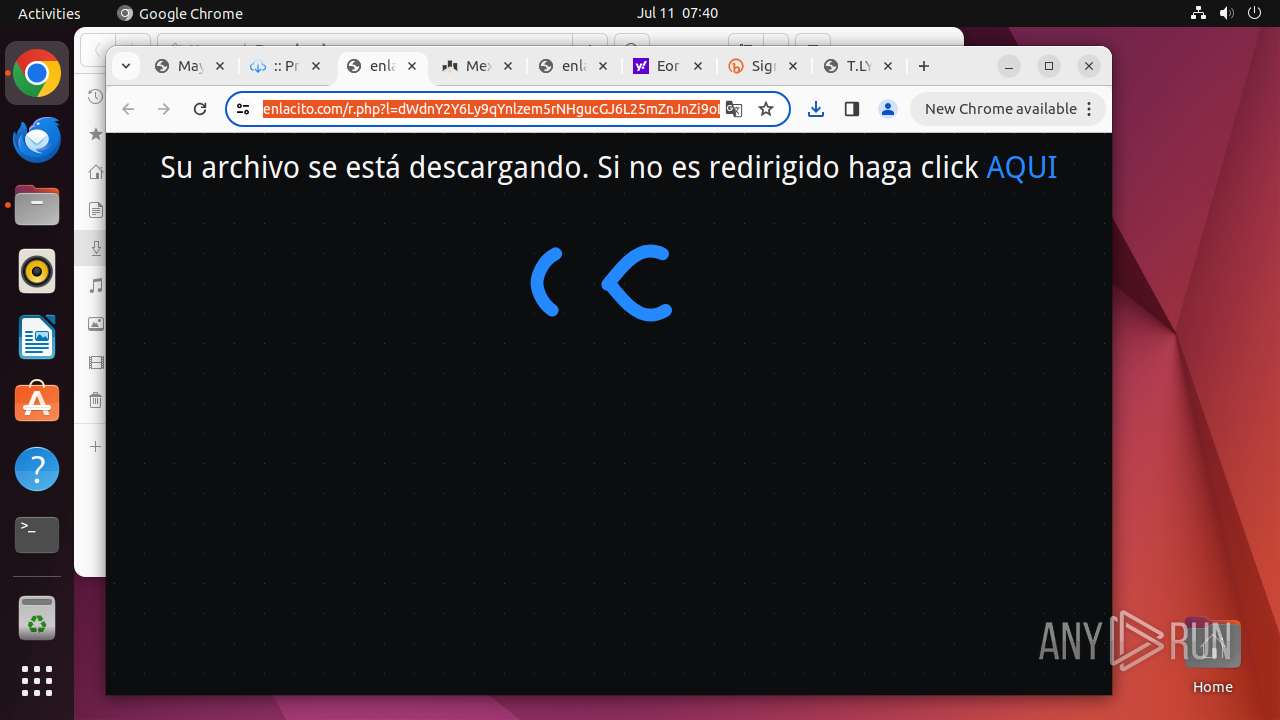
| URL: | https://wolfmax4k.com/descargar/peliculas-x264-mkv/alicia-en-el-pais-de-las-maravillas-2010-/bluray-microhd/ |
| Full analysis: | https://app.any.run/tasks/475236bb-1fa8-4ae4-b4b4-b18a3575e7ab |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2024, 06:35:58 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 8824C7EC0D3D4EE6B39DFB33F1B88E02 |
| SHA1: | 3209B6824B377F6B2BE686E0604F8EE29555E397 |
| SHA256: | 56539CCA9BB8F24C3C087B74C39A17F5985618BB91692703FECDBDB7C1275087 |
| SSDEEP: | 3:N8bJUHR2Wb/JH1nE2NAQVEhIY3EGiK+XE5IHN:2OgAxnNJSr0Gp8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
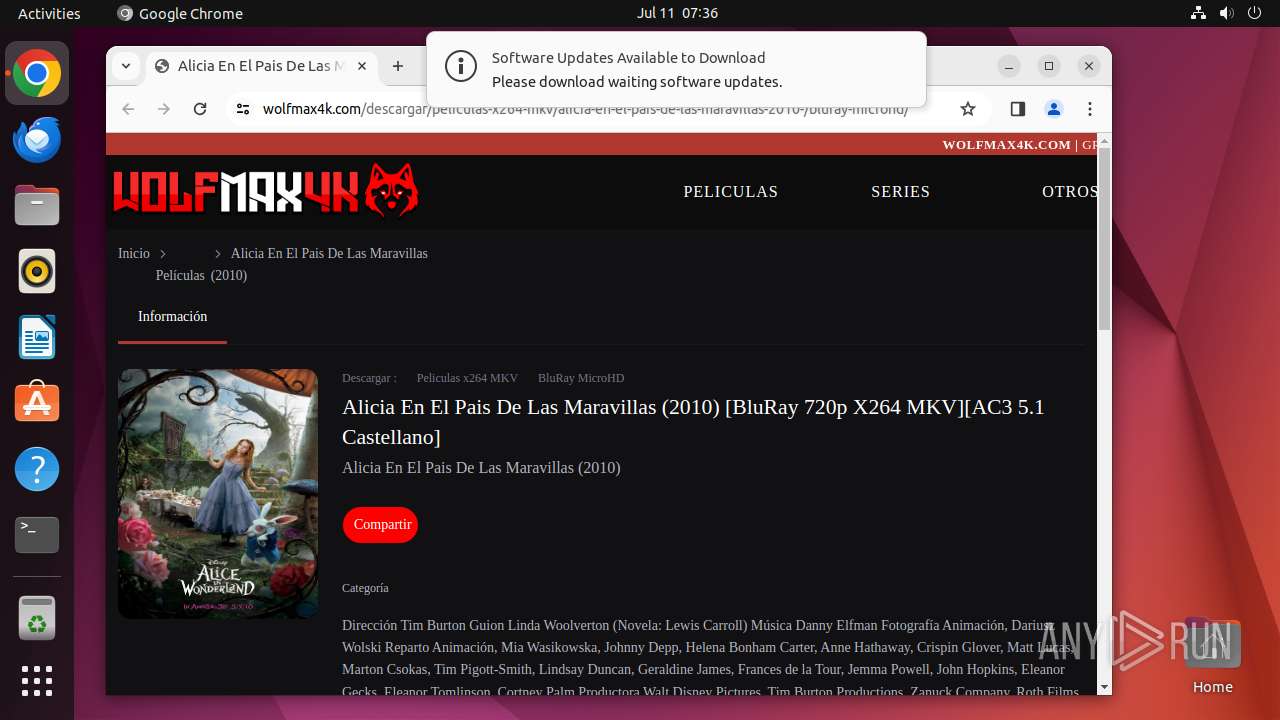
Executes commands using command-line interpreter
- update-notifier (PID: 14261)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 14294)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 14263)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
439
Monitored processes
224
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12931 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://wolfmax4k\.com/descargar/peliculas-x264-mkv/alicia-en-el-pais-de-las-maravillas-2010-/bluray-microhd/ " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 12932 | sudo -iu user google-chrome https://wolfmax4k.com/descargar/peliculas-x264-mkv/alicia-en-el-pais-de-las-maravillas-2010-/bluray-microhd/ | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 12933 | /usr/bin/google-chrome https://wolfmax4k.com/descargar/peliculas-x264-mkv/alicia-en-el-pais-de-las-maravillas-2010-/bluray-microhd/ | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12934 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12935 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12936 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12937 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12938 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12939 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12940 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
10
Suspicious files
498
Text files
37
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12933 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12933 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13036 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
692
DNS requests
892
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | US | binary | 1.98 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/n4jhhmkouwdq5a5pt3k6lmblae_456/lmelglejhemejginpboagddgdfbepgmp_456_all_ZZ_adatthpmxfx3v7y6geszldjbsq2a.crx3 | US | binary | 47.5 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/exukexv52szdyt6e333f4dka5q_8924/hfnkpimlhhgieaddgfemjhofmfblmnib_8924_all_ac3avscsh4o4ae24cadmf2kqlpoa.crx3 | US | binary | 579 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kiabhabjdbkjdpjbpigfodbdjmbglcoo/1.f6cc30e6a2d15e778f6701074d1f4b4505db1f516e06c9969160e0d6c62c5837/1.153e9301be7e862a33e2cab936a0a97e2f8bdf2dae1be516d6fe8a5f184ce028/abe599c5e7c450e0e3bfebef2d768b2903a8f50780214f1b81006d26589c3fc9.puff | US | binary | 3.03 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.e232391b105870e13719796efea3025cbd6ac95d2a97b88d4404c92eed8eb8c2/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/e14cfc1fc47e48a5521008562d65b5093e414f7b64b555abe6c2c4990f7c5179.puff | US | binary | 47.9 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.900410b03a2b6d9b98abb85833bbb2a557cbda8fe7df65fb688a9ca04a3f6d40/1.ff0e88cc4f10c87e09be229b861a5ce2909b22d830b3634c51e29b150342eee0/427368a661ed32d5b6002fd830e70c8056dcd40649a6bf5666360d93073e0362.puff | US | binary | 21.3 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/actgis4zukemrpucdmqy7zkouhiq_2024.7.9.2/jflhchccmppkfebkiaminageehmchikm_2024.07.09.02_all_adk66shklhaywu6w5bia4kjkis2q.crx3 | US | binary | 9.24 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gp5sujfha3uuuceulcjdrip7ga_20240628.649506826.14/obedbbhbpmojnkanicioggnmelmoomoc_20240628.649506826.14_all_ENGB500000_adhq4rfezapaqpsy653jepwymmeq.crx3 | US | binary | 5.13 Mb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | US | binary | 135 Kb | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://cacerts.rapidssl.com/RapidSSLTLSRSACAG1.crt | US | binary | 1.18 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 156.146.33.141:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
485 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 104.21.49.132:443 | wolfmax4k.com | — | — | unknown |
— | — | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
12933 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 142.250.185.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
— | — | 151.101.1.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
wolfmax4k.com |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
accounts.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Claudflare content delivery network (cdnjs .cloudflare .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
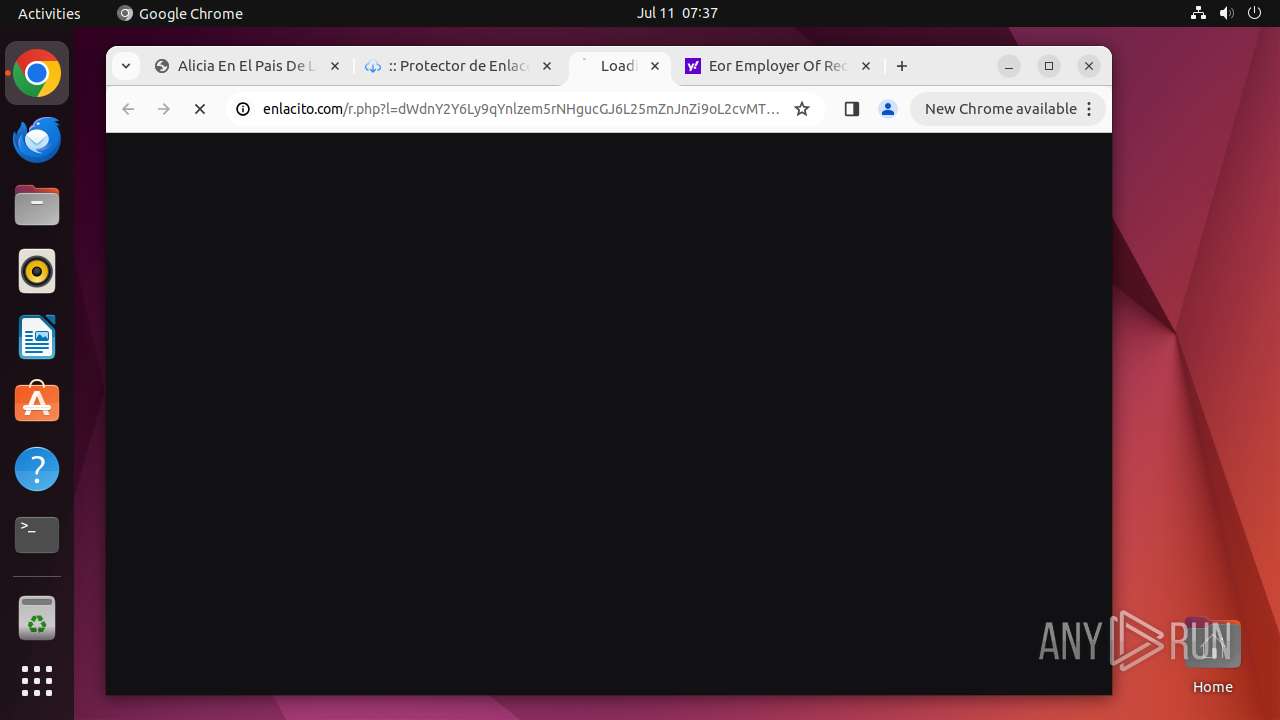
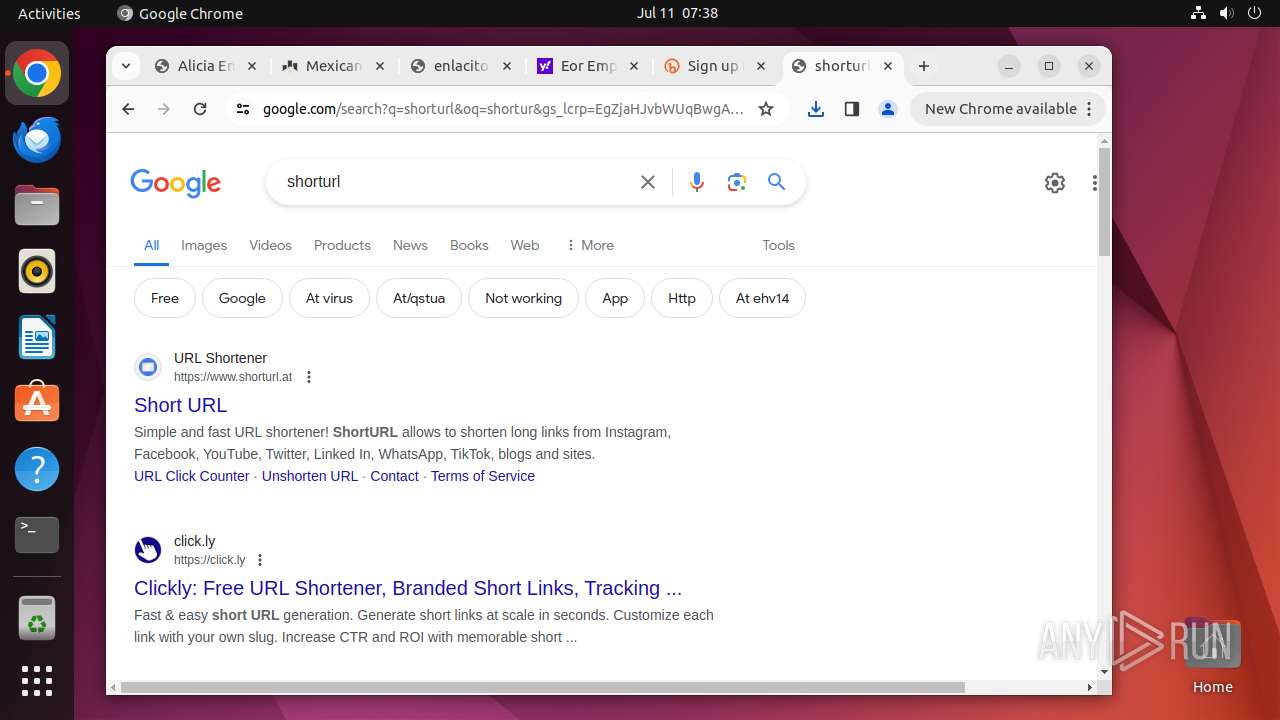
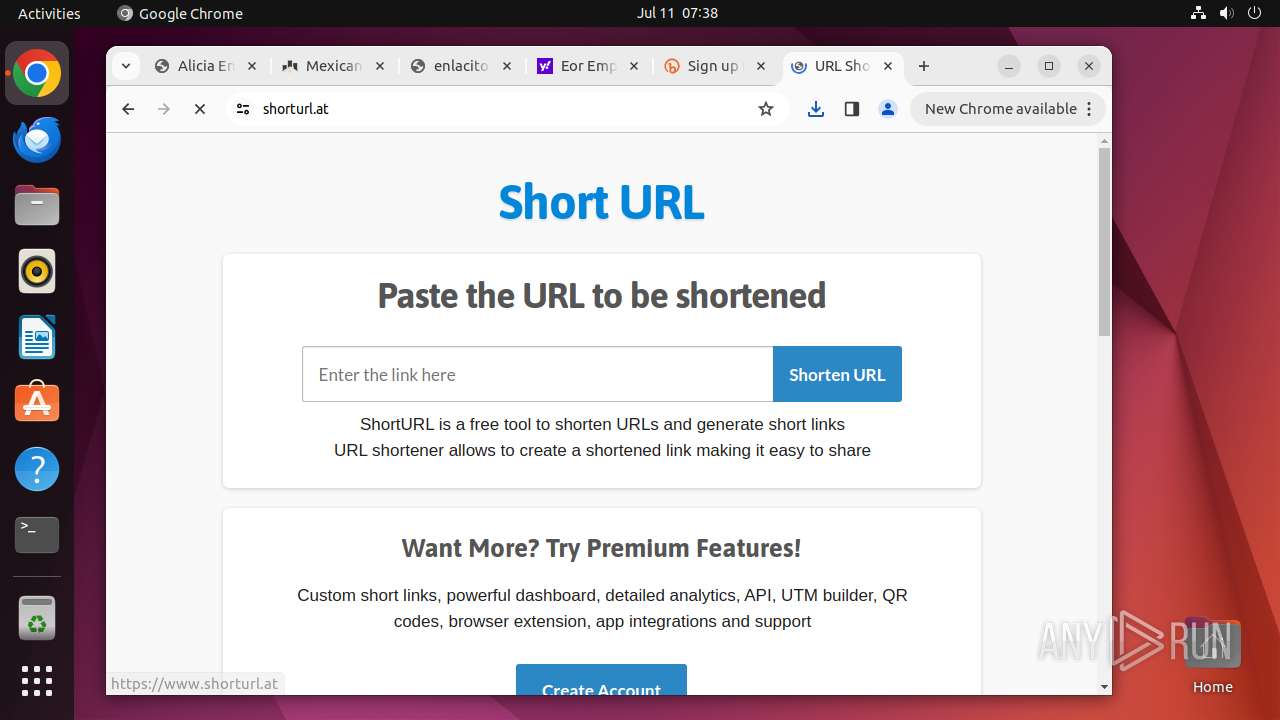
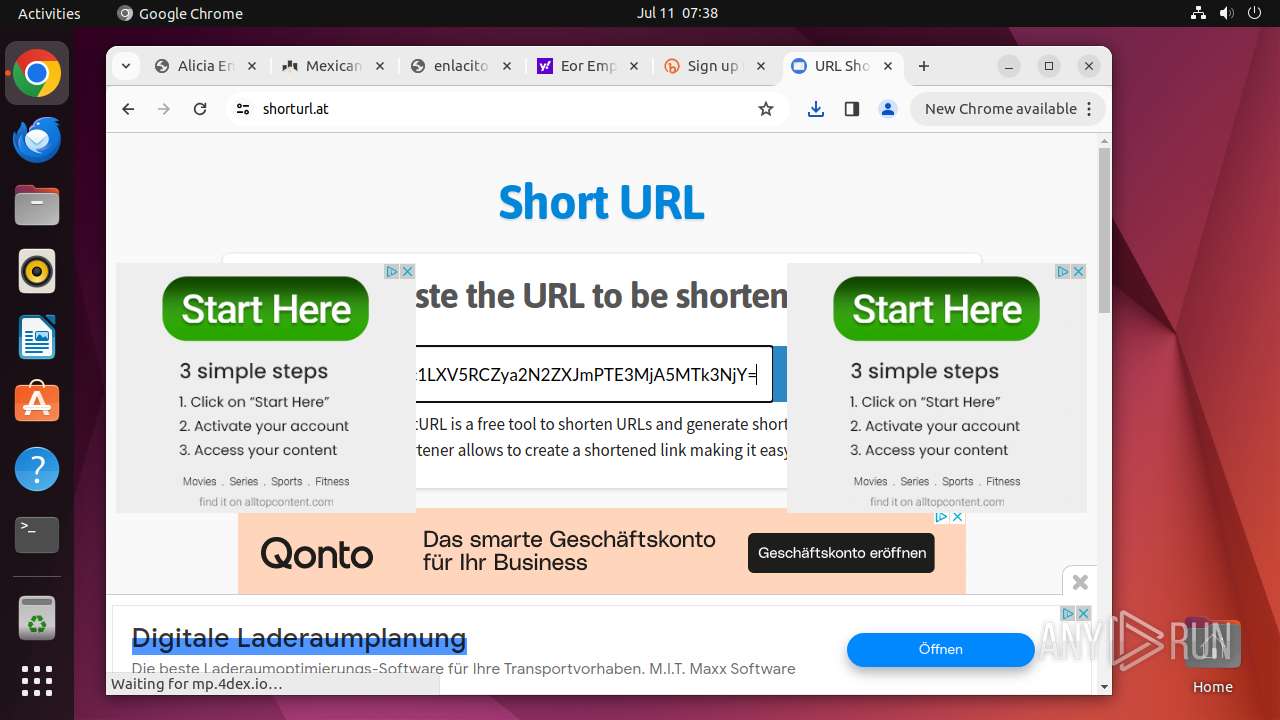
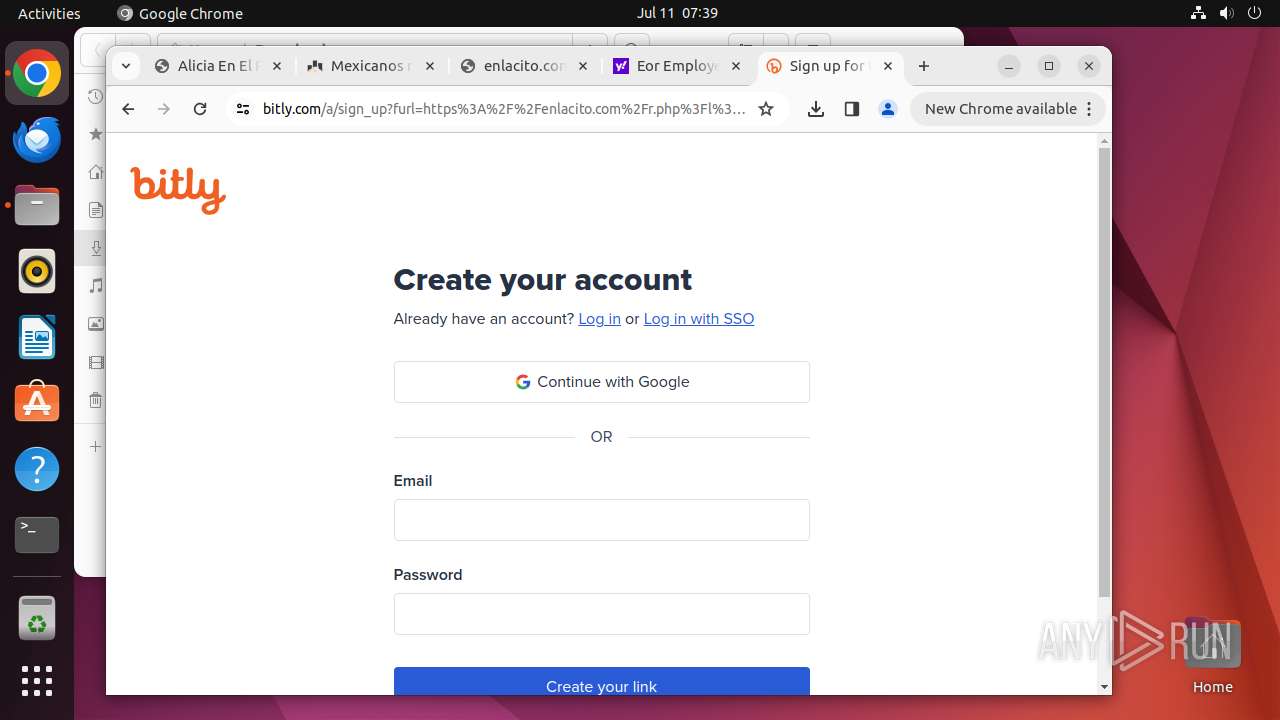
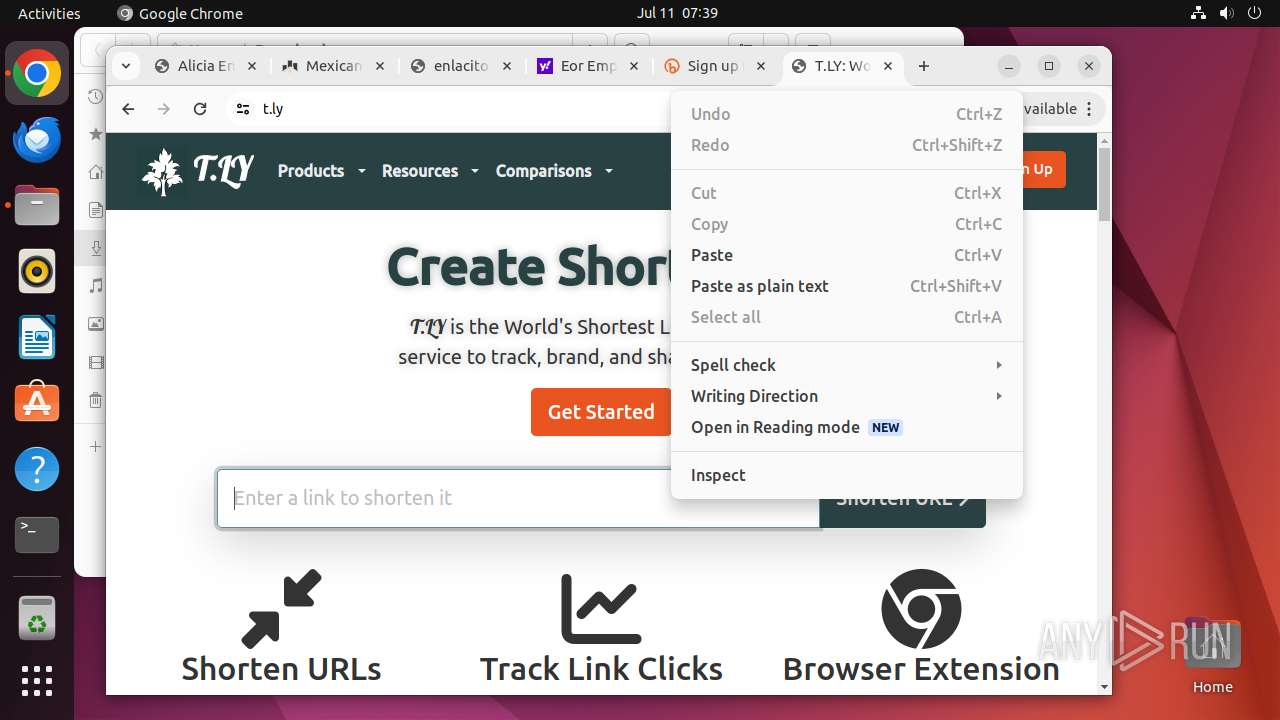
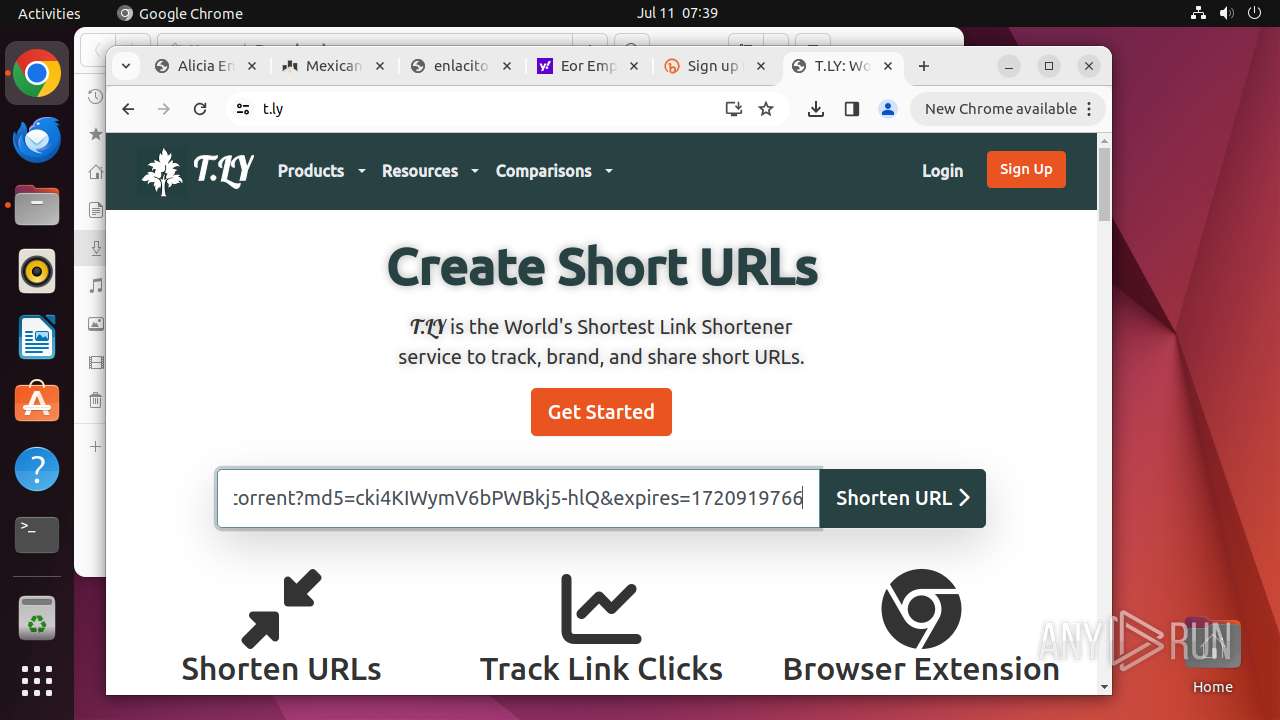
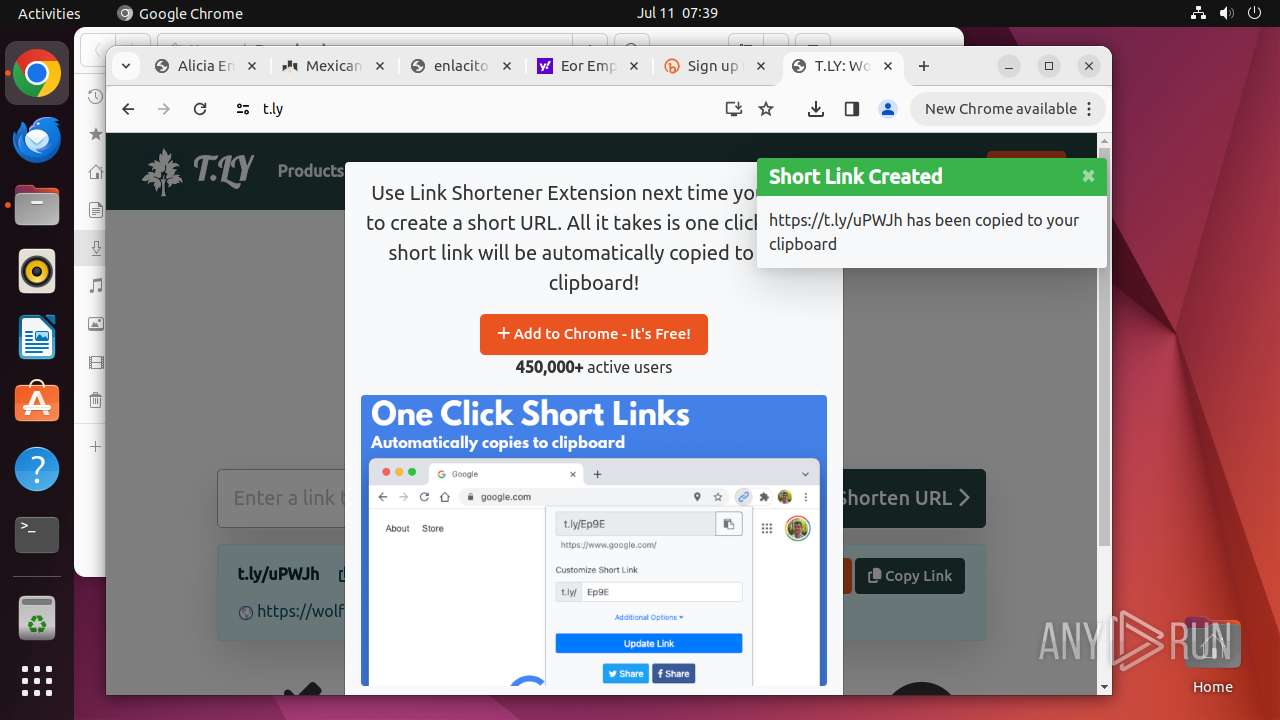
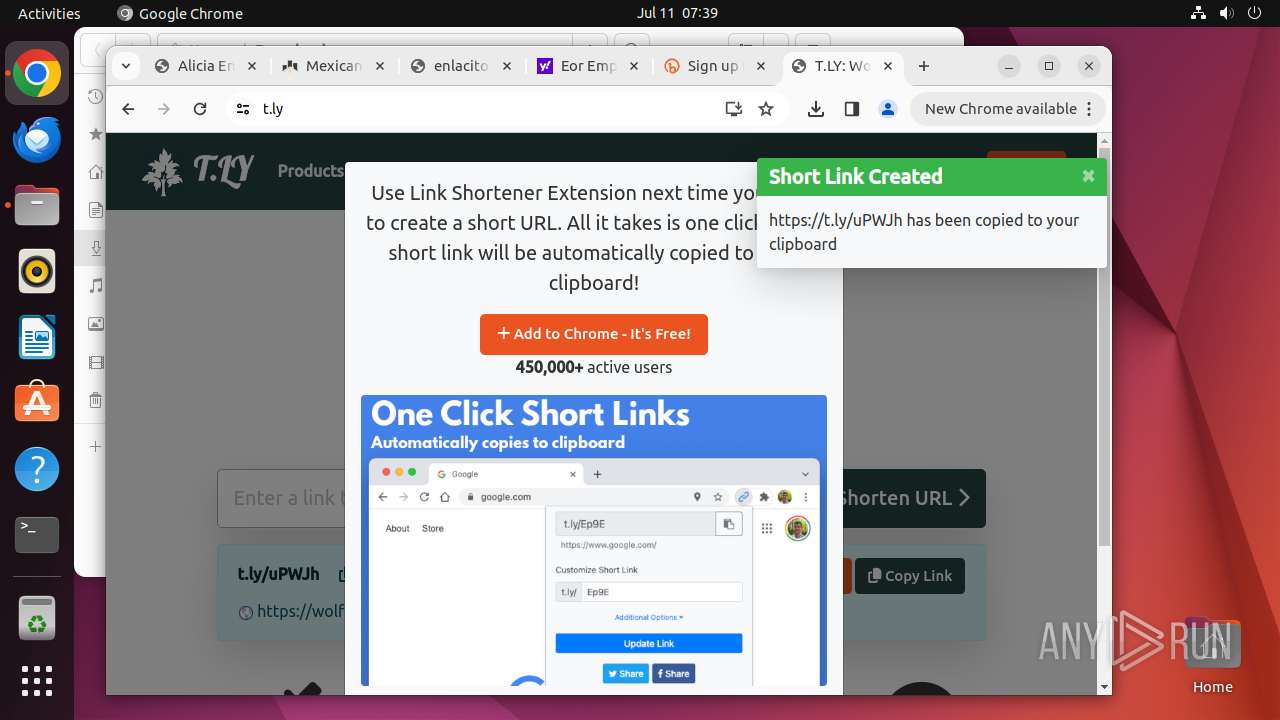
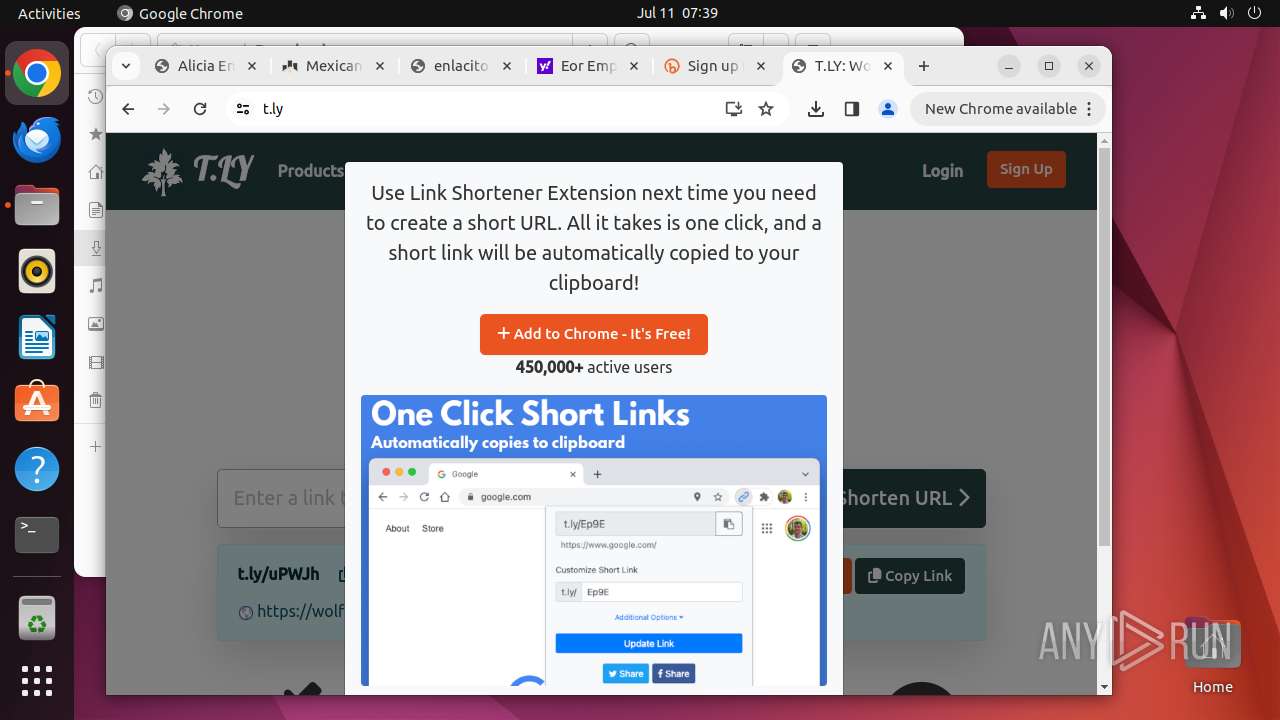
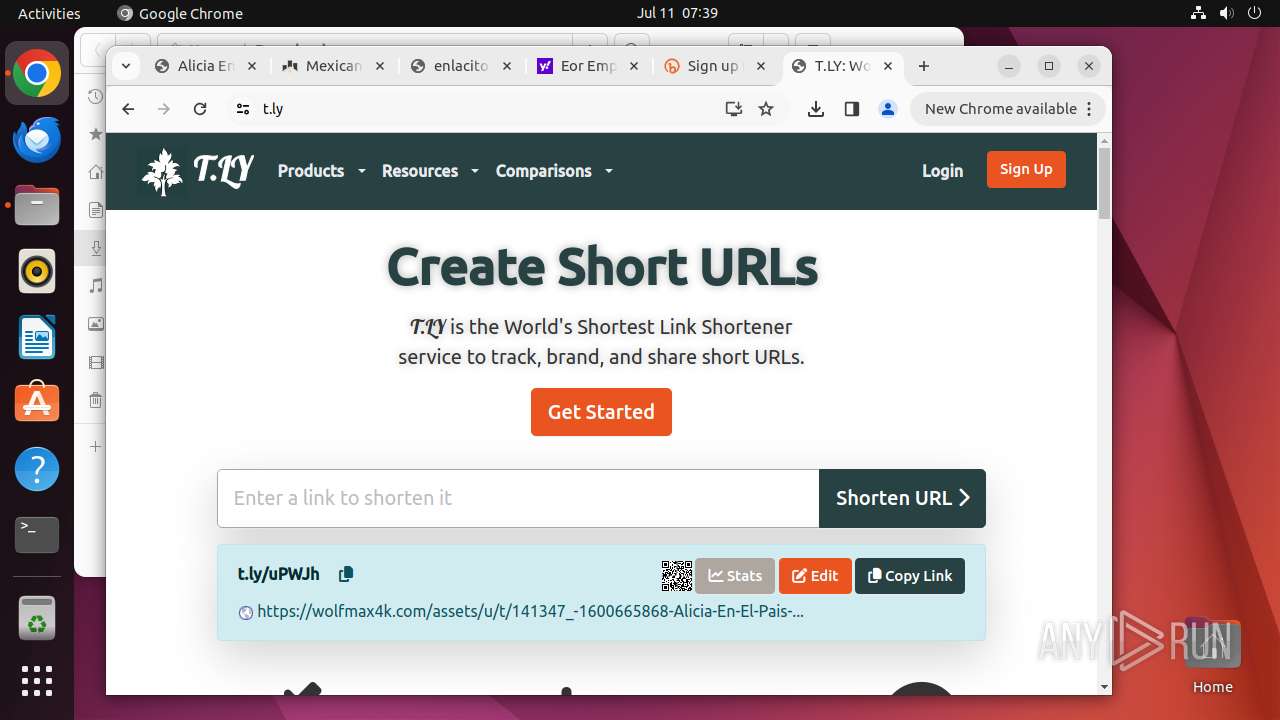
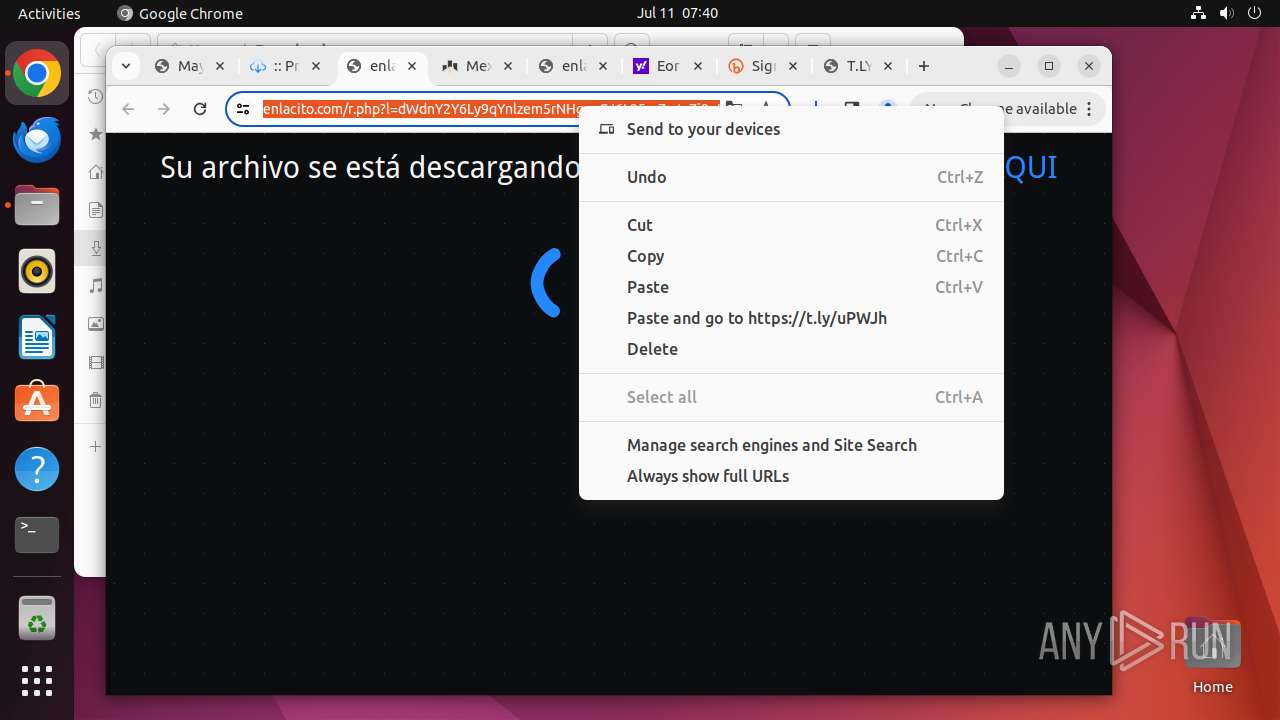
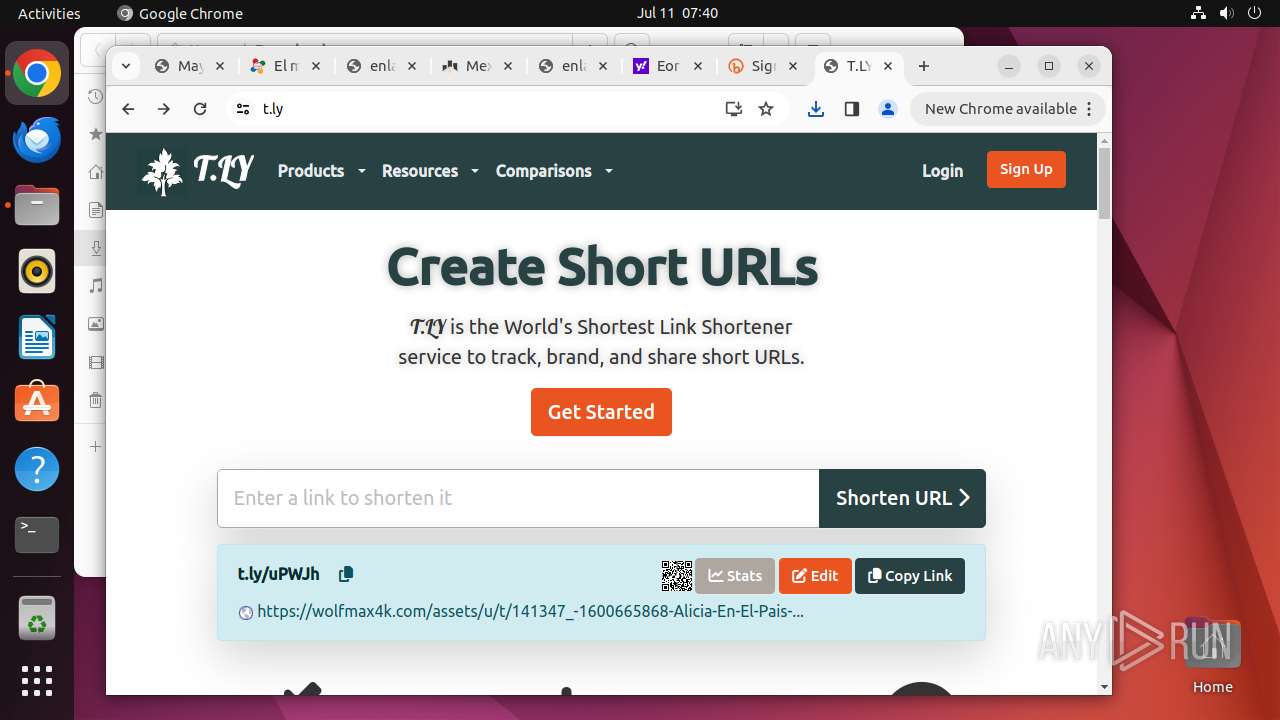
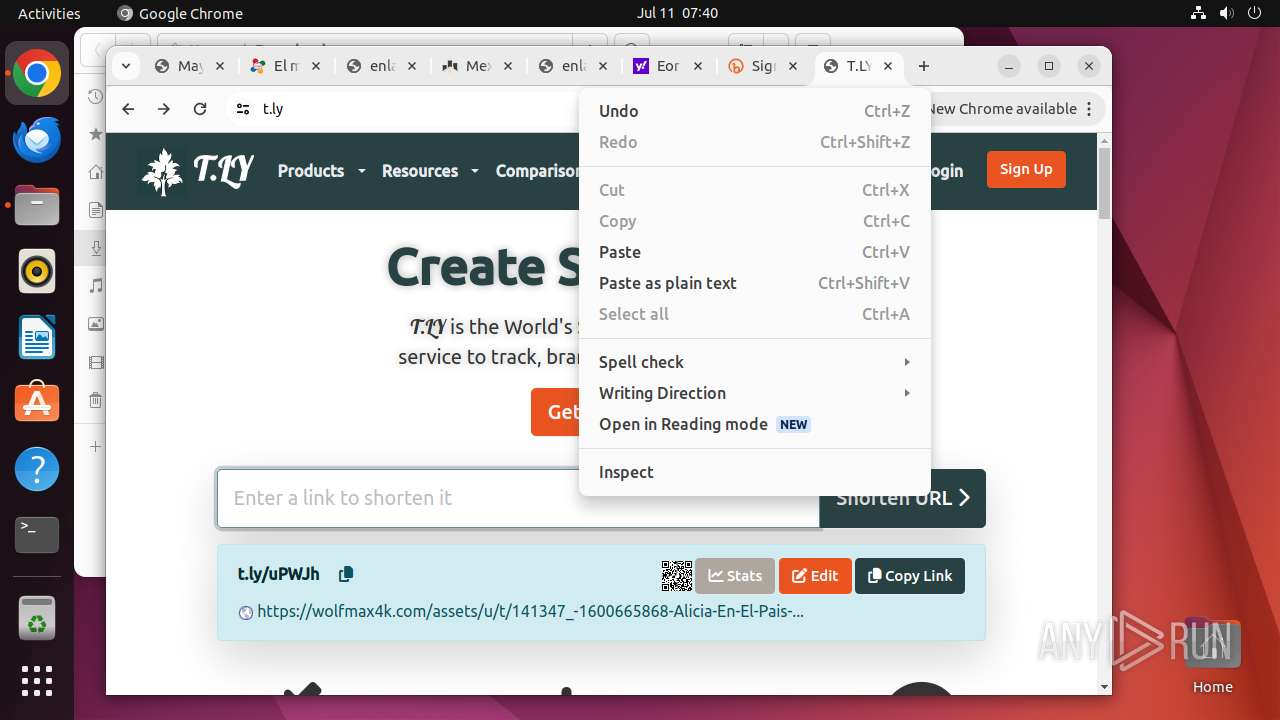
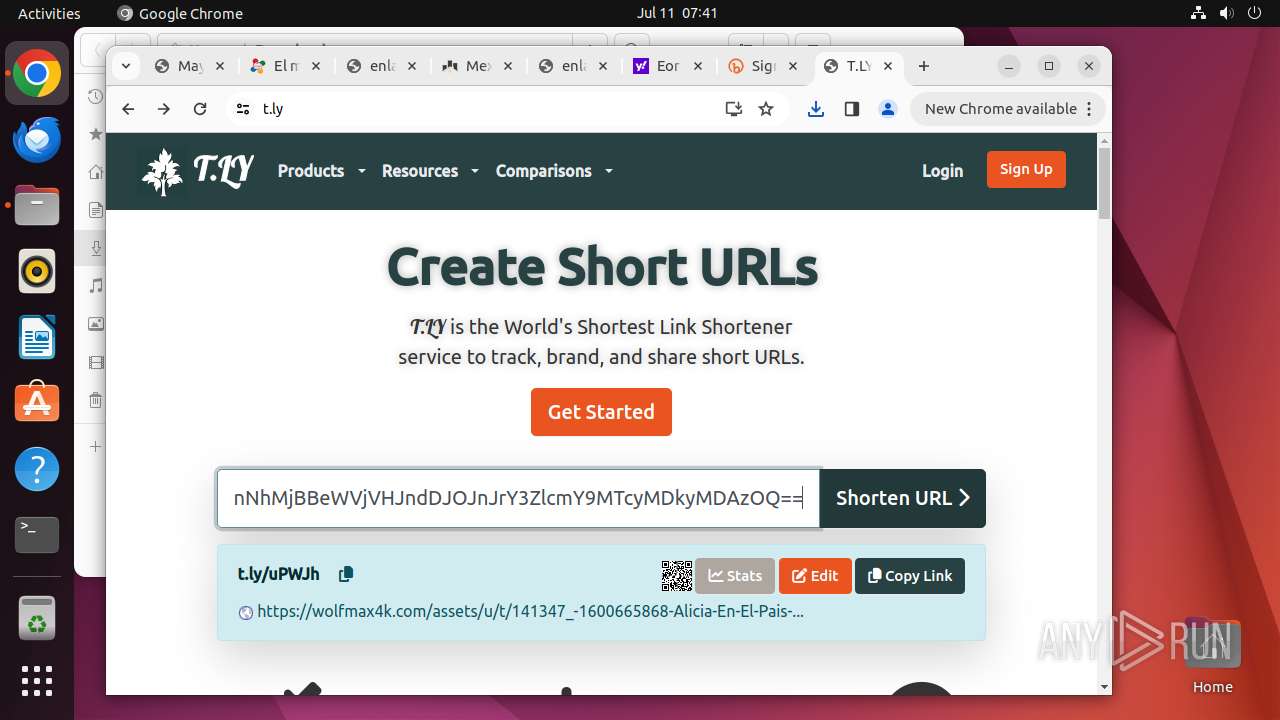
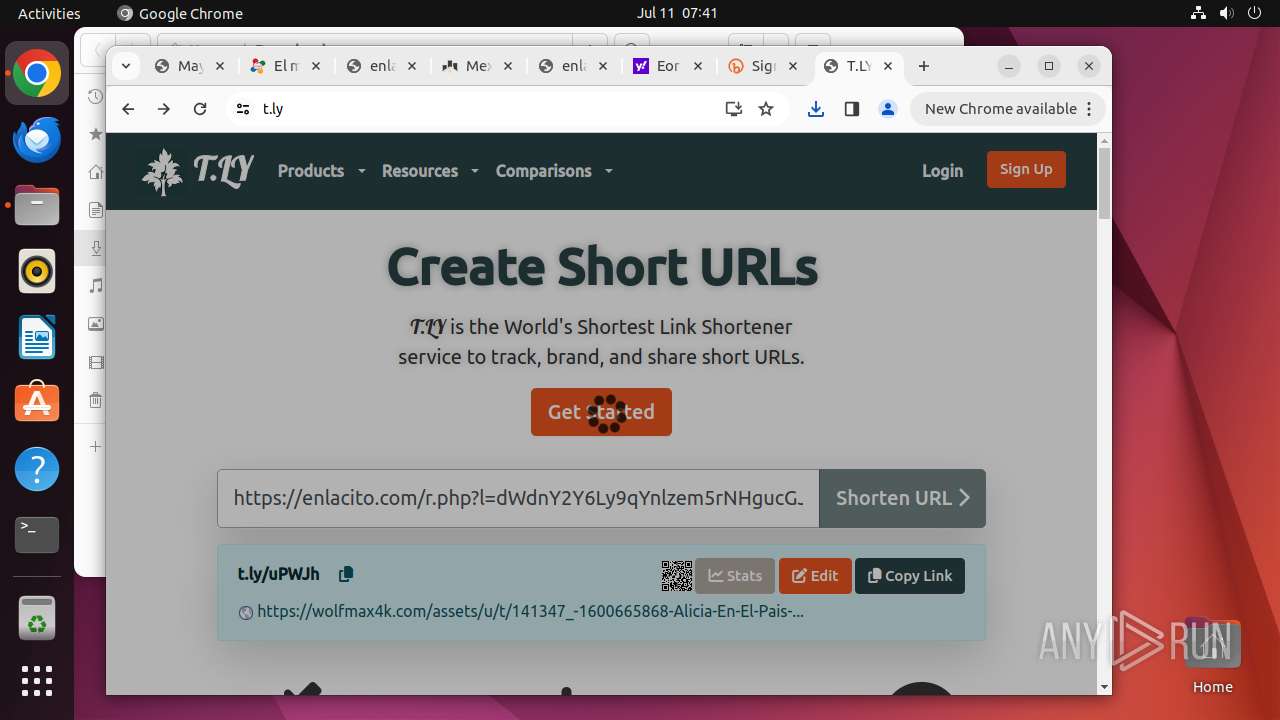
425 | systemd-resolved | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
425 | systemd-resolved | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (t .ly) |
— | — | Misc activity | ET INFO Observed URL Shortening Service Domain (t .ly in TLS SNI) |
— | — | Misc activity | ET INFO Observed URL Shortening Service Domain (t .ly in TLS SNI) |
— | — | Misc activity | ET INFO Observed URL Shortening Service Domain (t .ly in TLS SNI) |
— | — | Misc activity | ET INFO Observed URL Shortening Service Domain (t .ly in TLS SNI) |