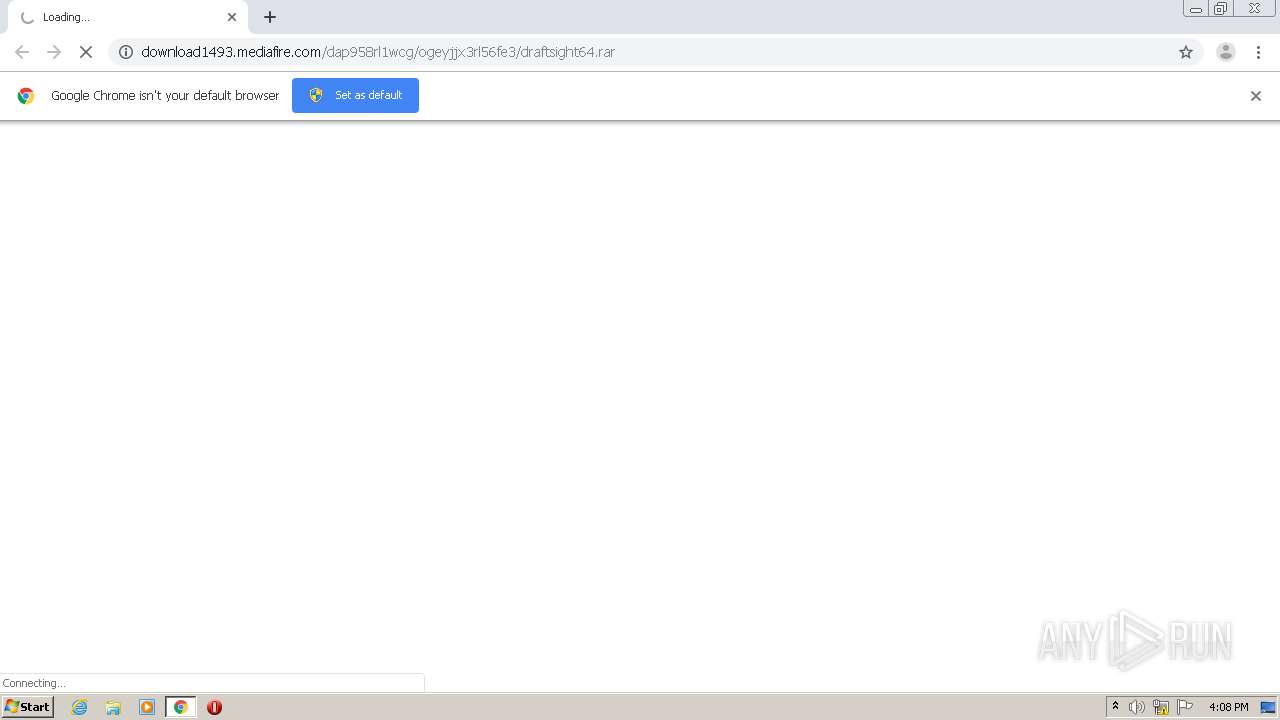
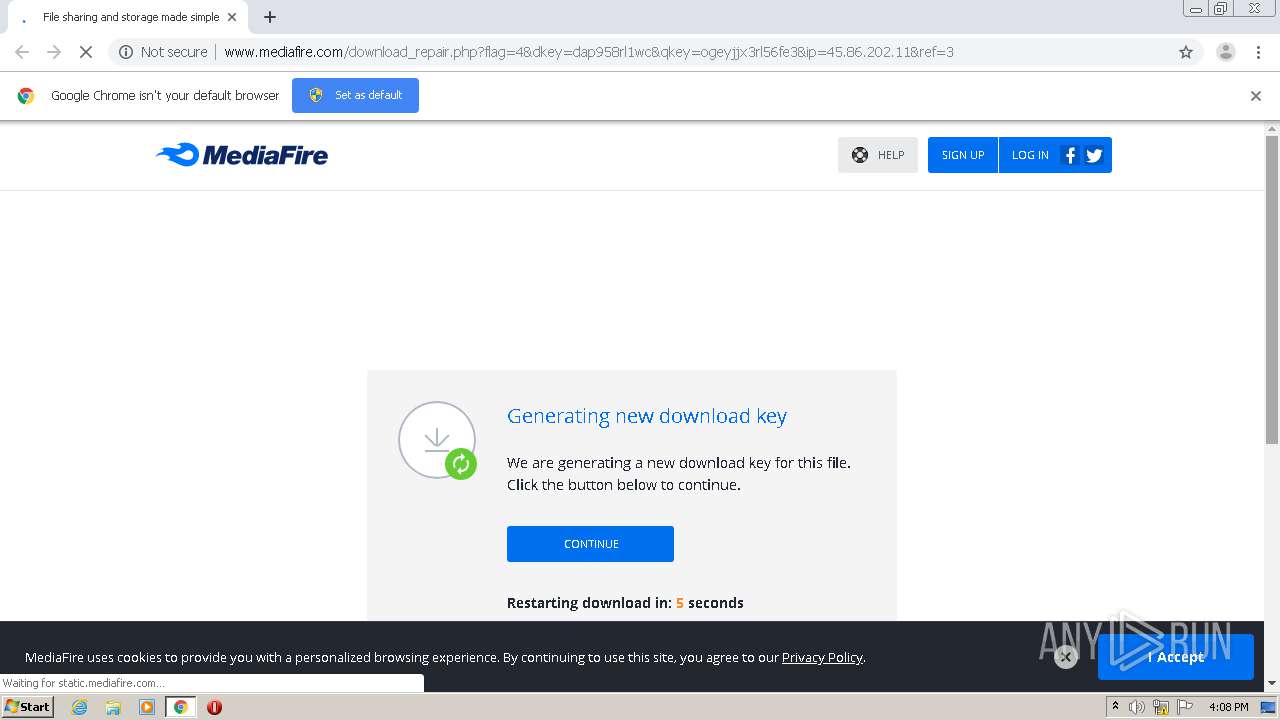
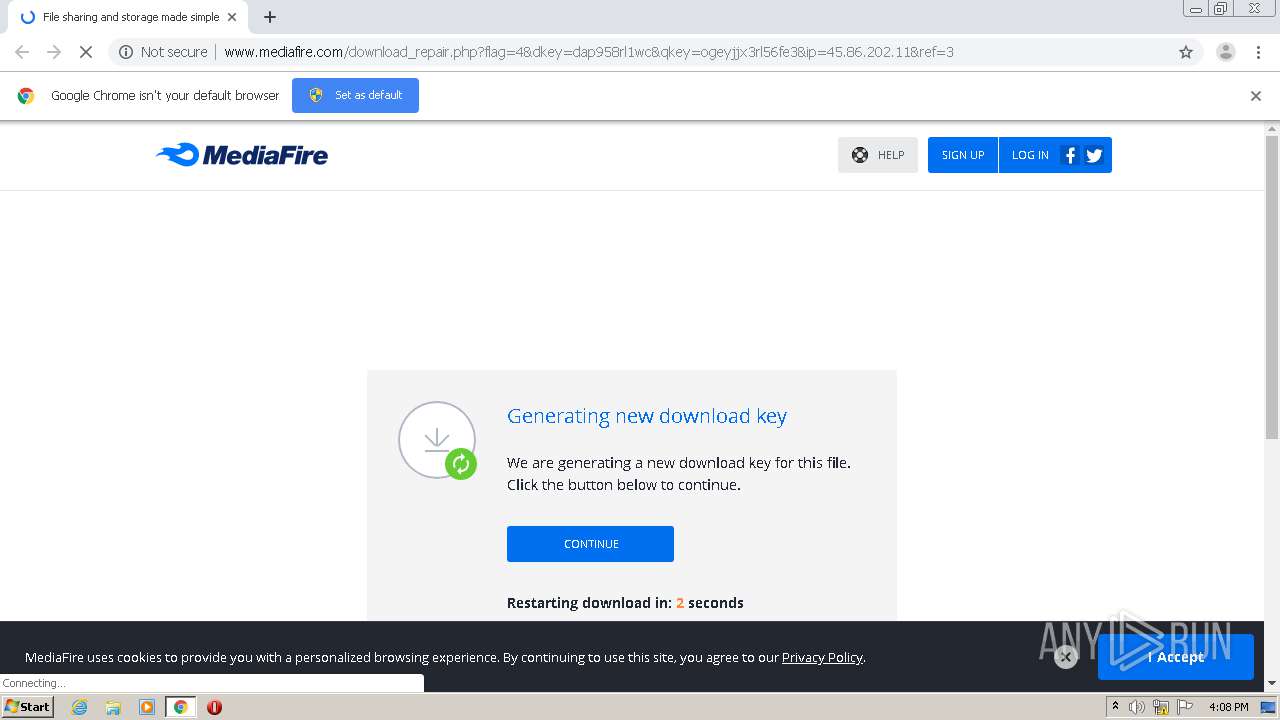
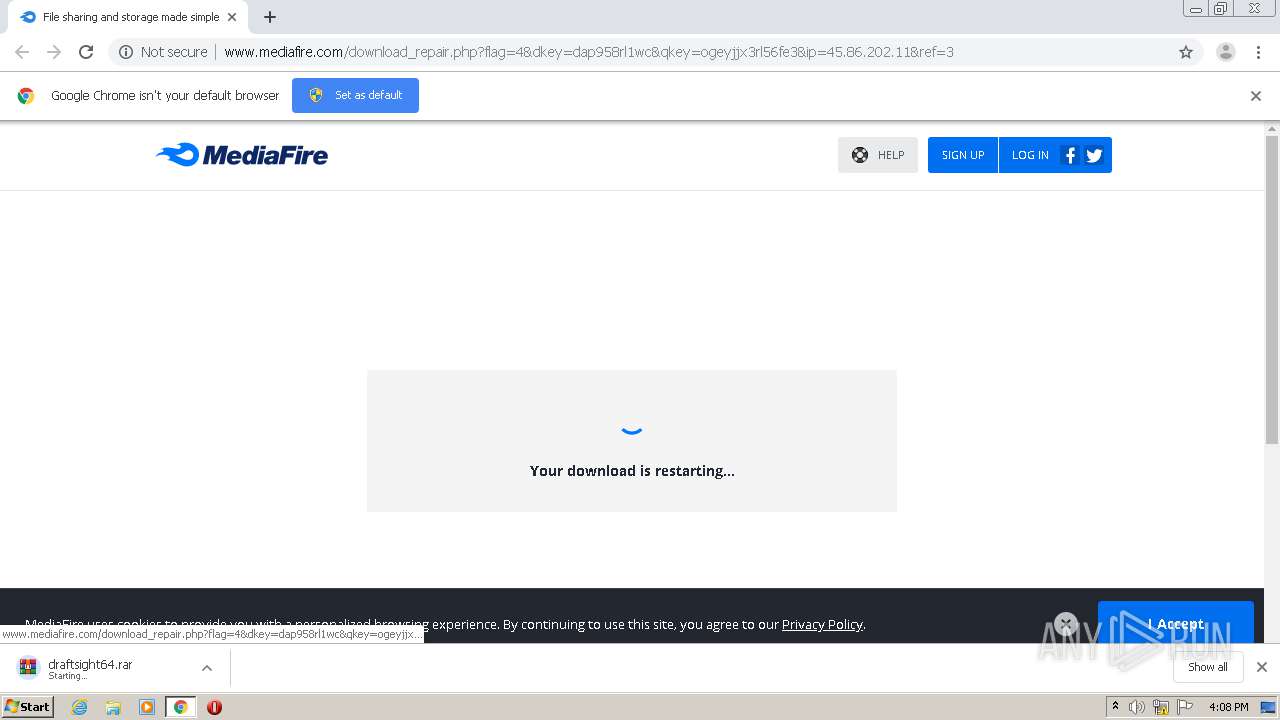
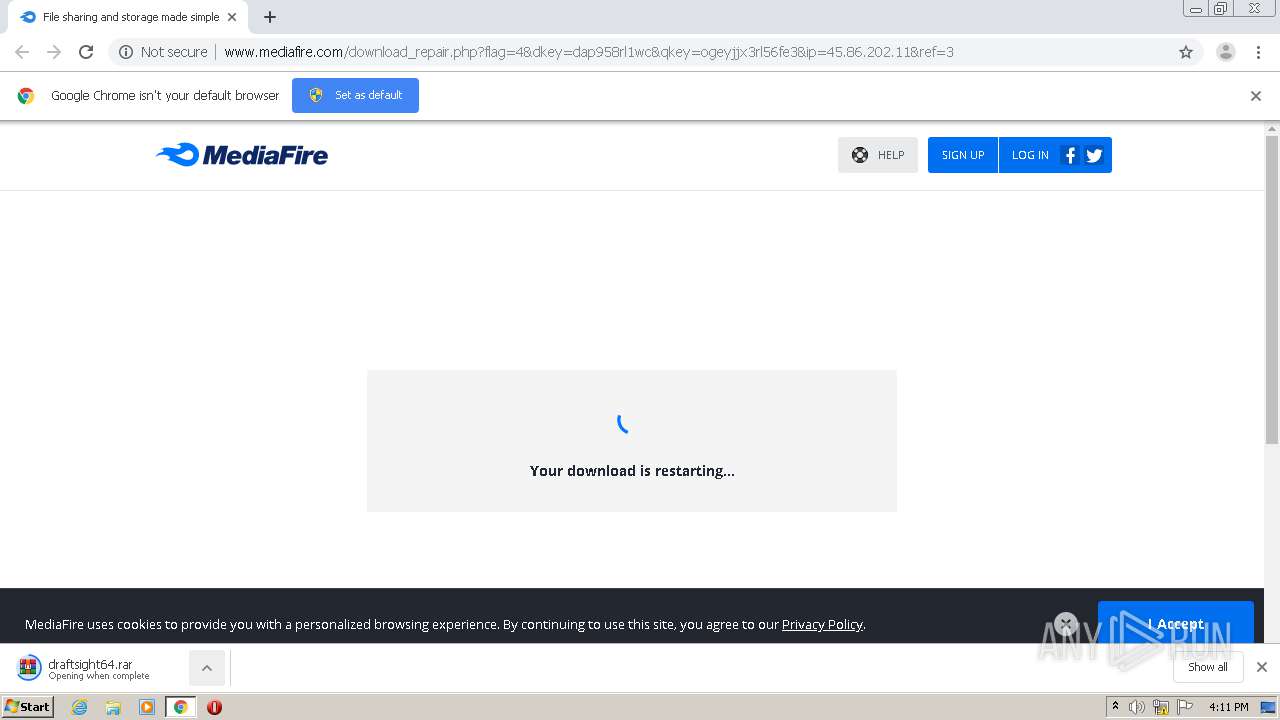
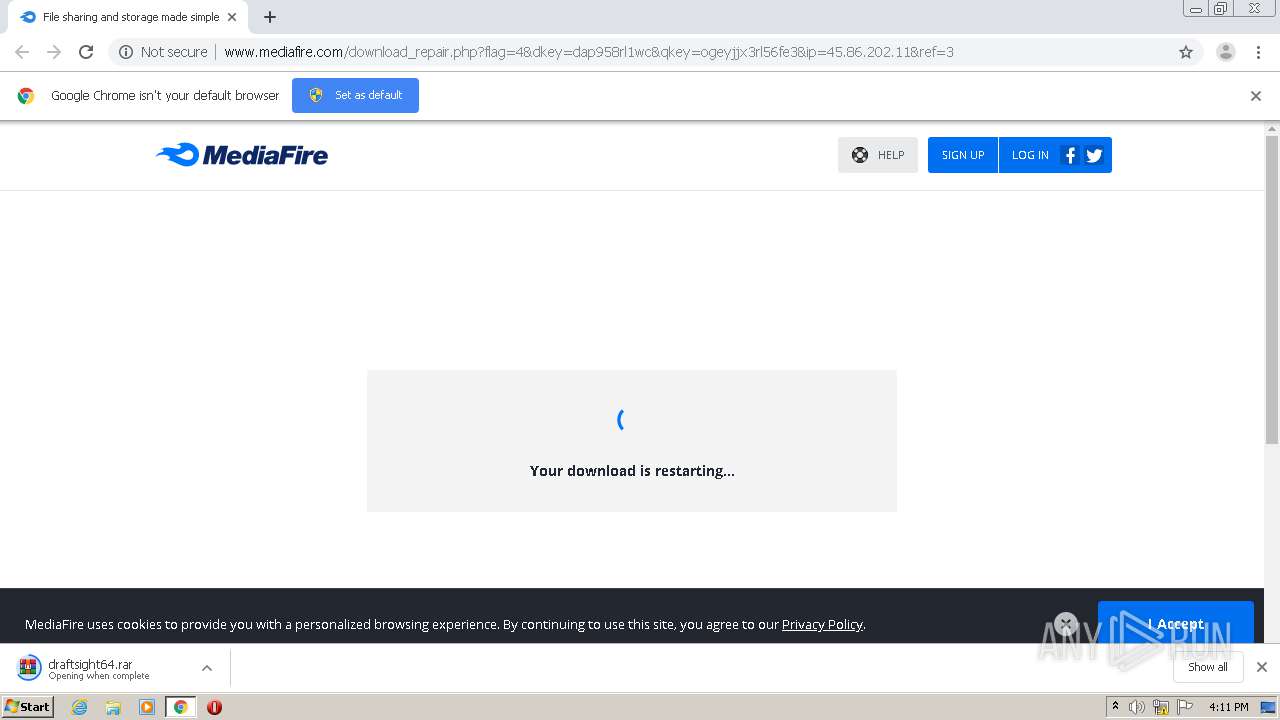
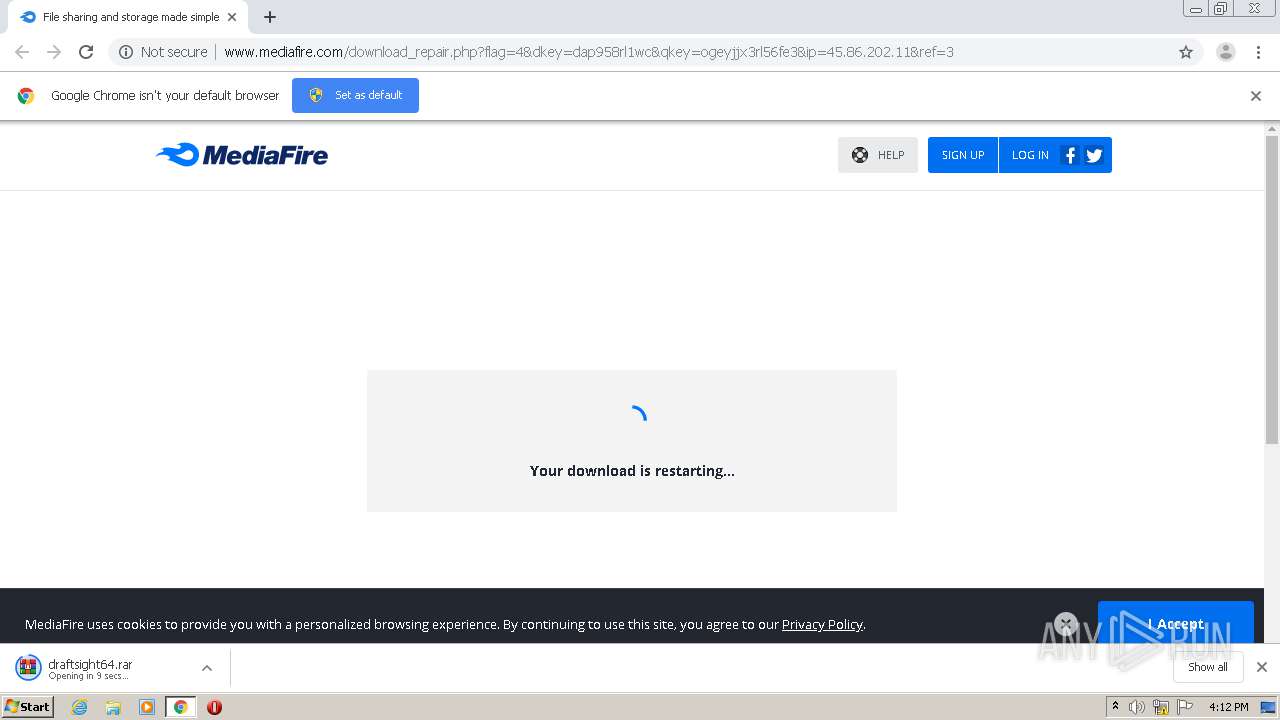
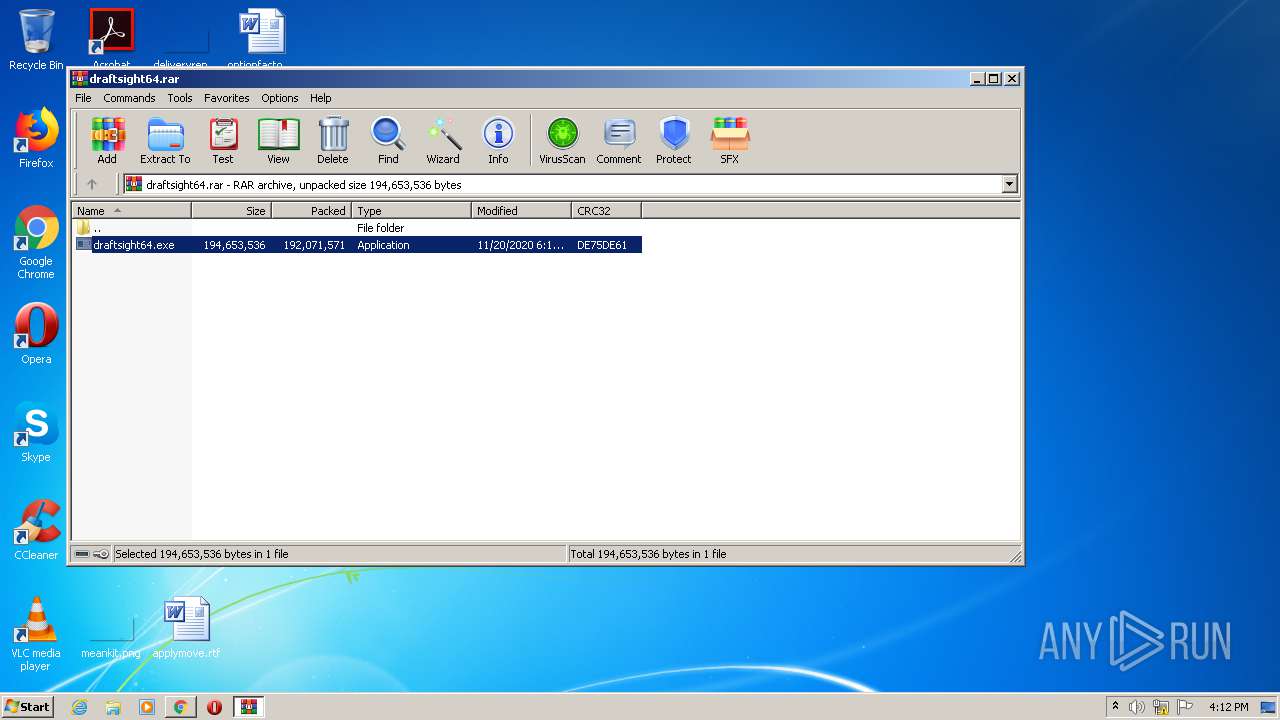
| URL: | http://download1493.mediafire.com/dap958rl1wcg/ogeyjjx3rl56fe3/draftsight64.rar |
| Full analysis: | https://app.any.run/tasks/a6a5ec15-8abe-4b99-8a48-43cbfd5a59ef |
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2021, 16:08:06 |
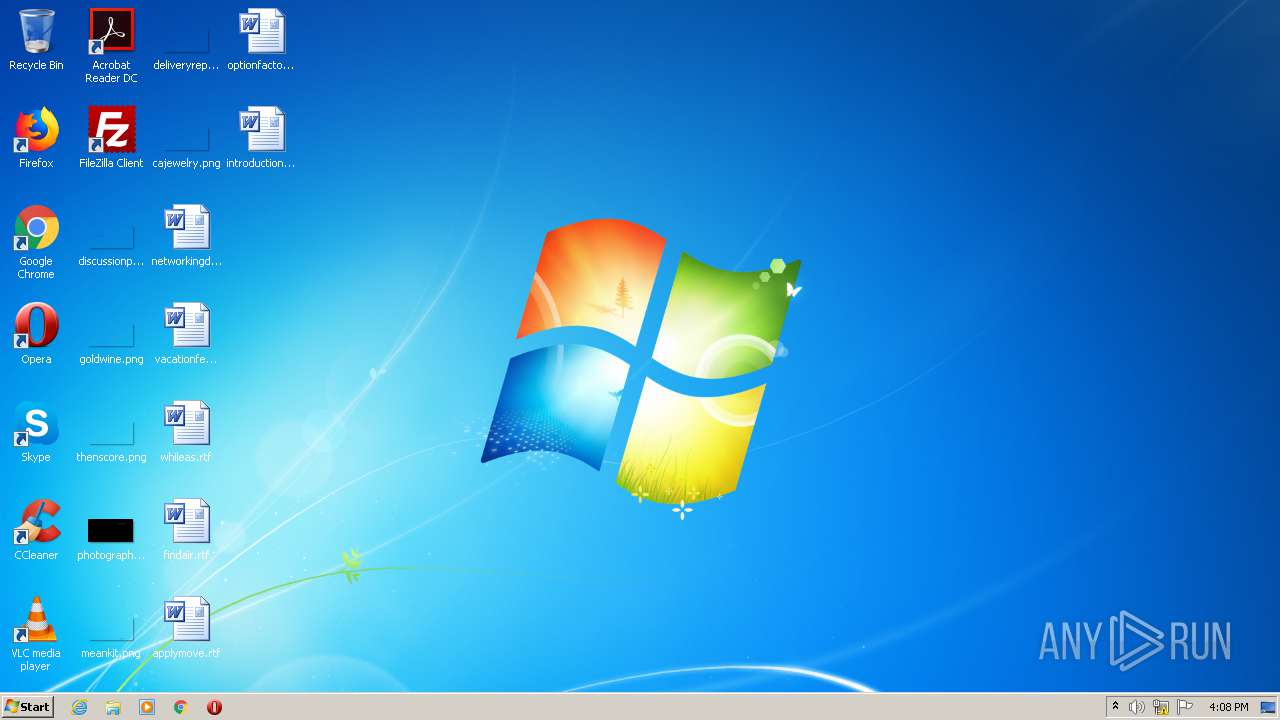
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
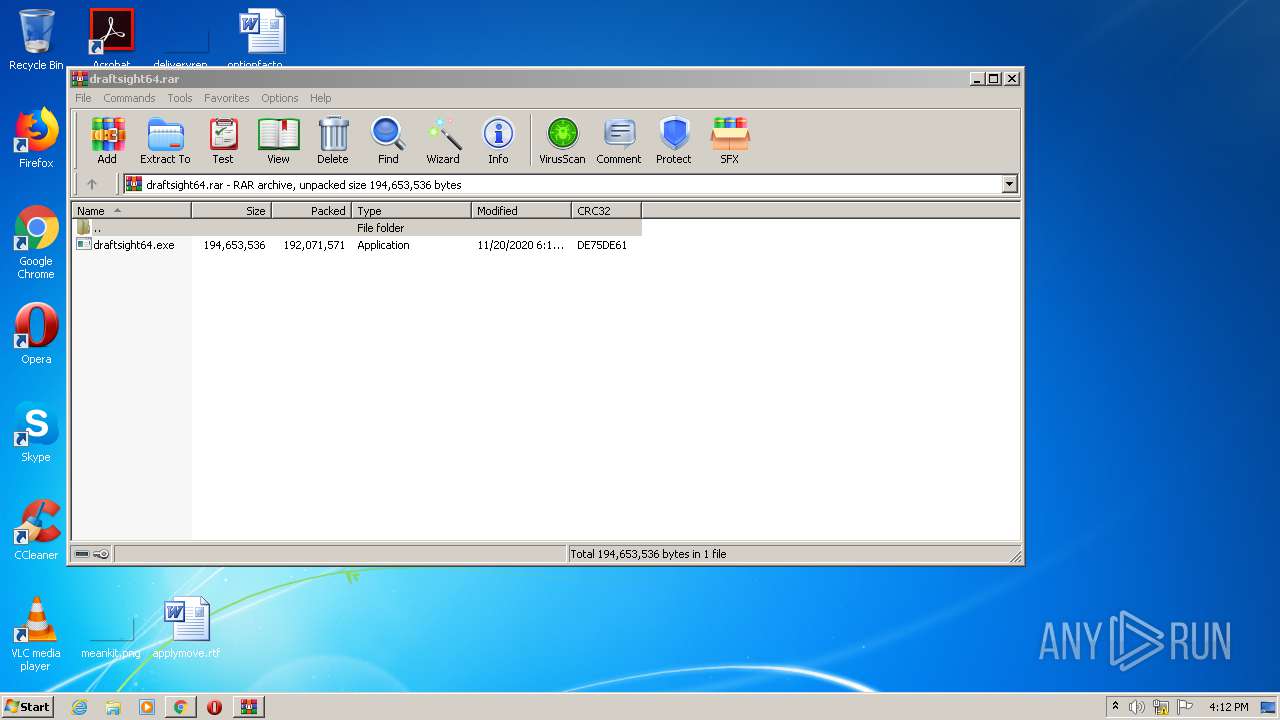
| MD5: | E91DCE7D7C65E5B4993A9844145636F1 |
| SHA1: | F9689E0934D9C042C1626F39227349D8E25EBF8C |
| SHA256: | 5640A8794A7F49073CF217A843E774844FB5071DE79D7F2D74A2D79D5865BE68 |
| SSDEEP: | 3:N1KaKE6RRBMEQeGWEVcyyJjth4WKBXqRqG:CaK6EQeGDV1s6hqt |
MALICIOUS
Application was dropped or rewritten from another process
- DraftSight.exe (PID: 3416)
- DraftSight.exe (PID: 2080)
Changes the autorun value in the registry
- draftsight64.exe (PID: 2856)
SUSPICIOUS
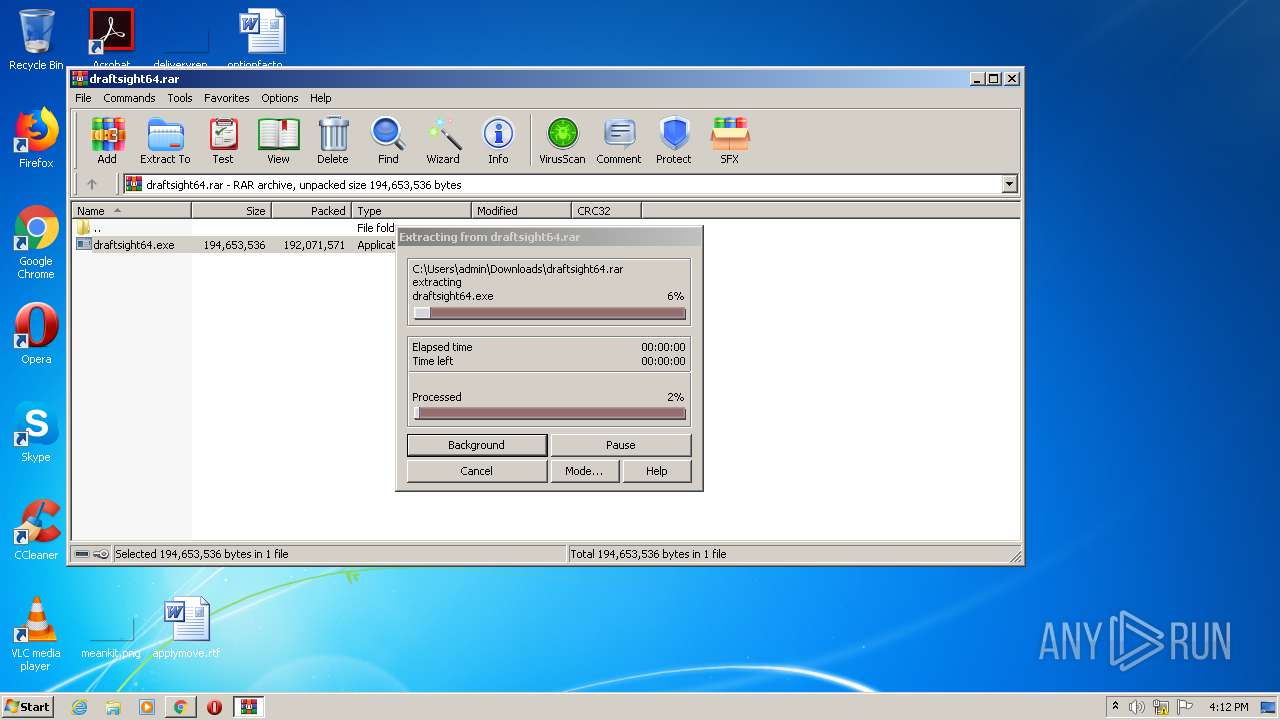
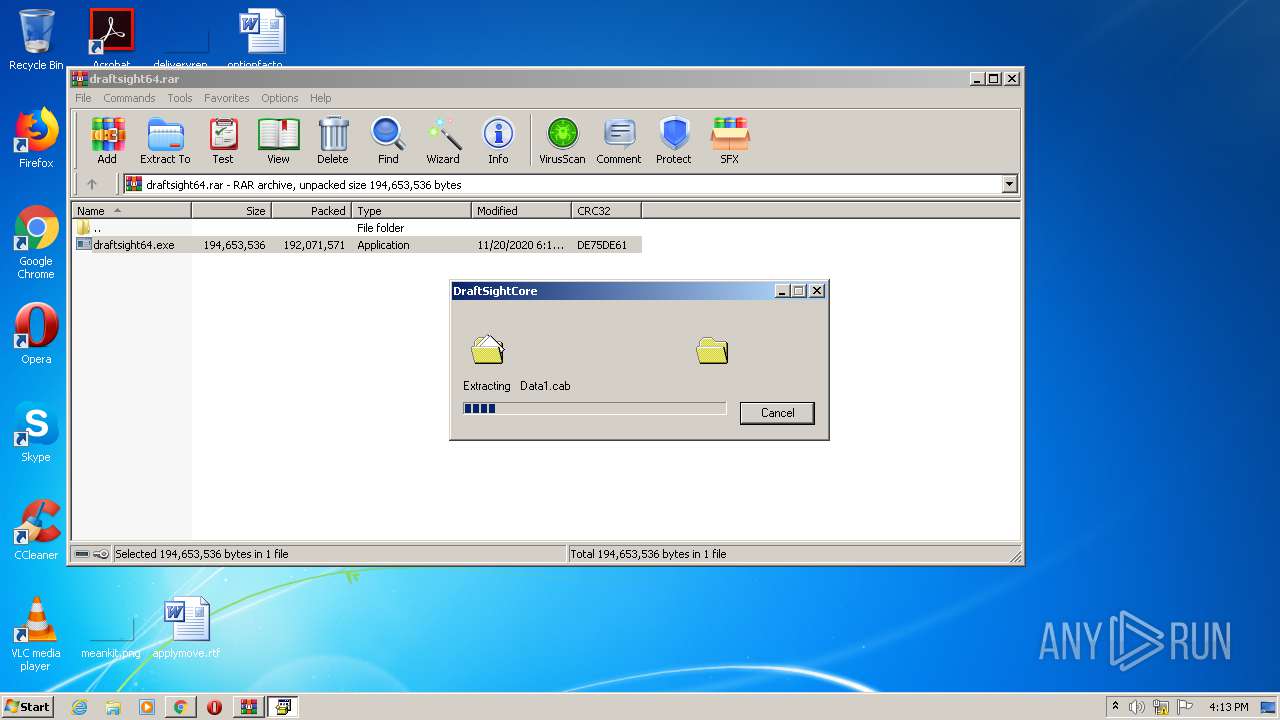
Executable content was dropped or overwritten
- draftsight64.exe (PID: 2856)
Drops a file that was compiled in debug mode
- draftsight64.exe (PID: 2856)
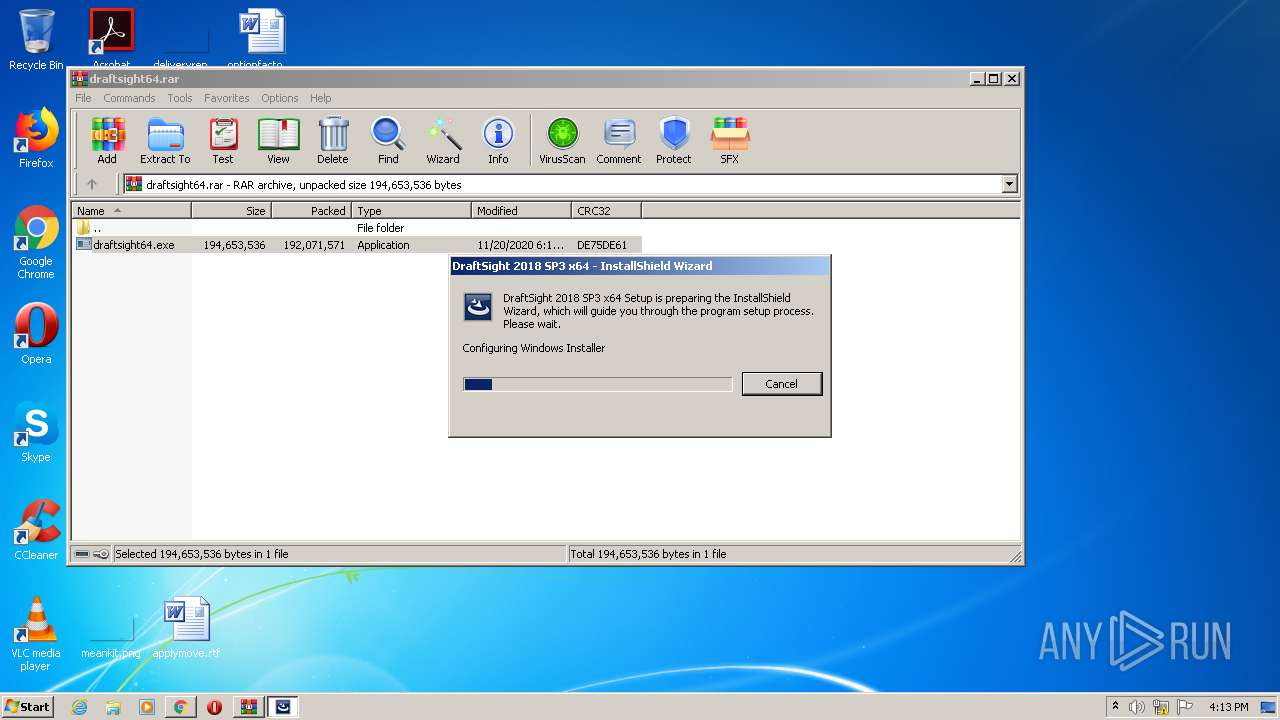
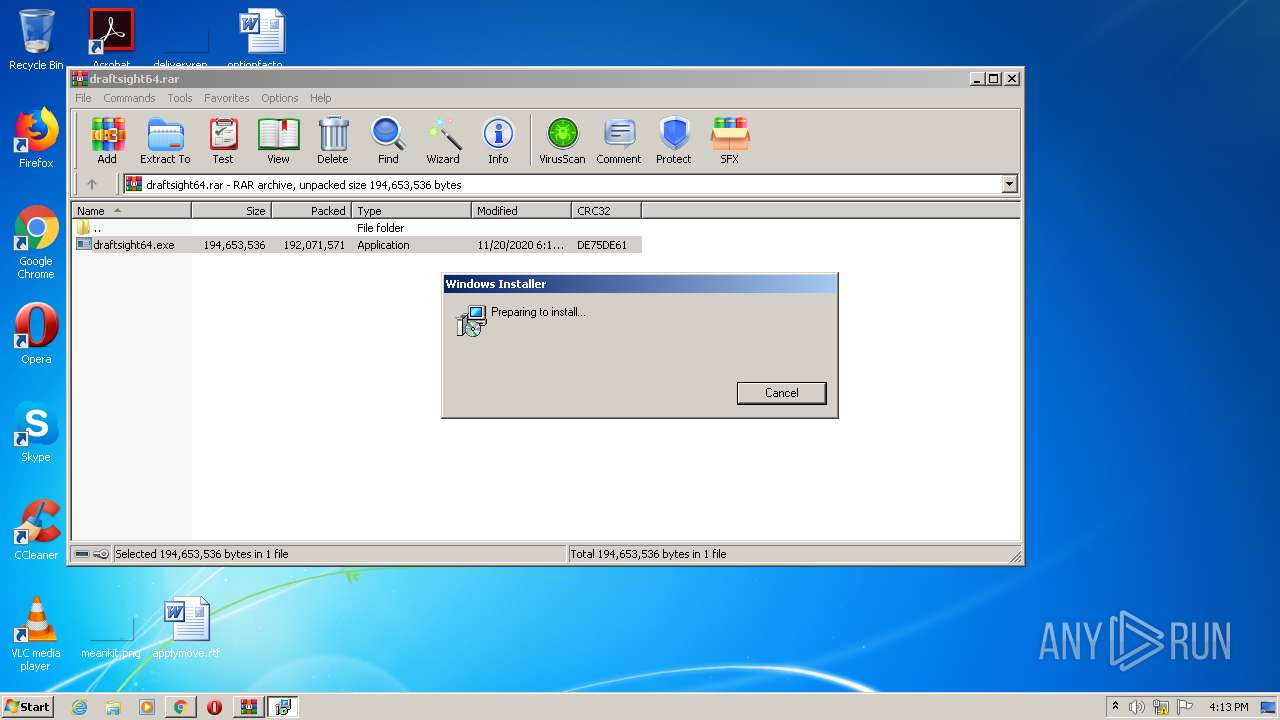
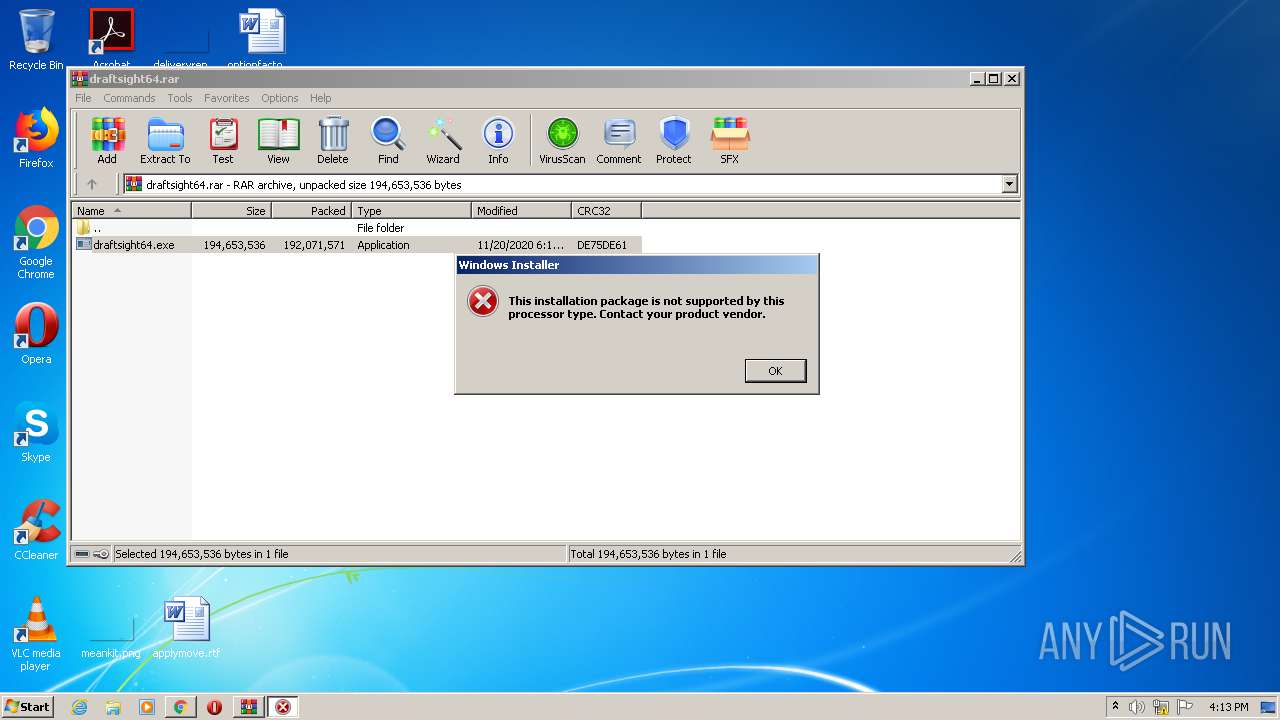
Starts Microsoft Installer
- DraftSight.exe (PID: 2080)
INFO
Reads the hosts file
- chrome.exe (PID: 2644)
- chrome.exe (PID: 1108)
Application launched itself
- chrome.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
18
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9492744490599119725 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11593670658954125291 --mojo-platform-channel-handle=1460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2560 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12617791169111301209 --mojo-platform-channel-handle=2976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11129802192047466209 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8815591602276686236 --mojo-platform-channel-handle=2988 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10479095555573903598 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\DraftSight.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\DraftSight.exe | draftsight64.exe | ||||||||||||
User: admin Company: Dassault Systemes Integrity Level: HIGH Description: Setup Launcher Unicode Exit code: 1633 Version: 18.3.0105 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,3395392056345131932,8644365857272137139,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10217646127021363463 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://download1493.mediafire.com/dap958rl1wcg/ogeyjjx3rl56fe3/draftsight64.rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 369
Read events
1 294
Write events
72
Delete events
3
Modification events
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2644-13255027710279250 |
Value: 259 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
43
Text files
124
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FFF1AFF-A54.pma | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d89728cd-e491-4146-ba00-42a2533f4b32.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF128370.TMP | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF12839f.TMP | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1283ed.TMP | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1286bc.TMP | — | |
MD5:— | SHA256:— | |||
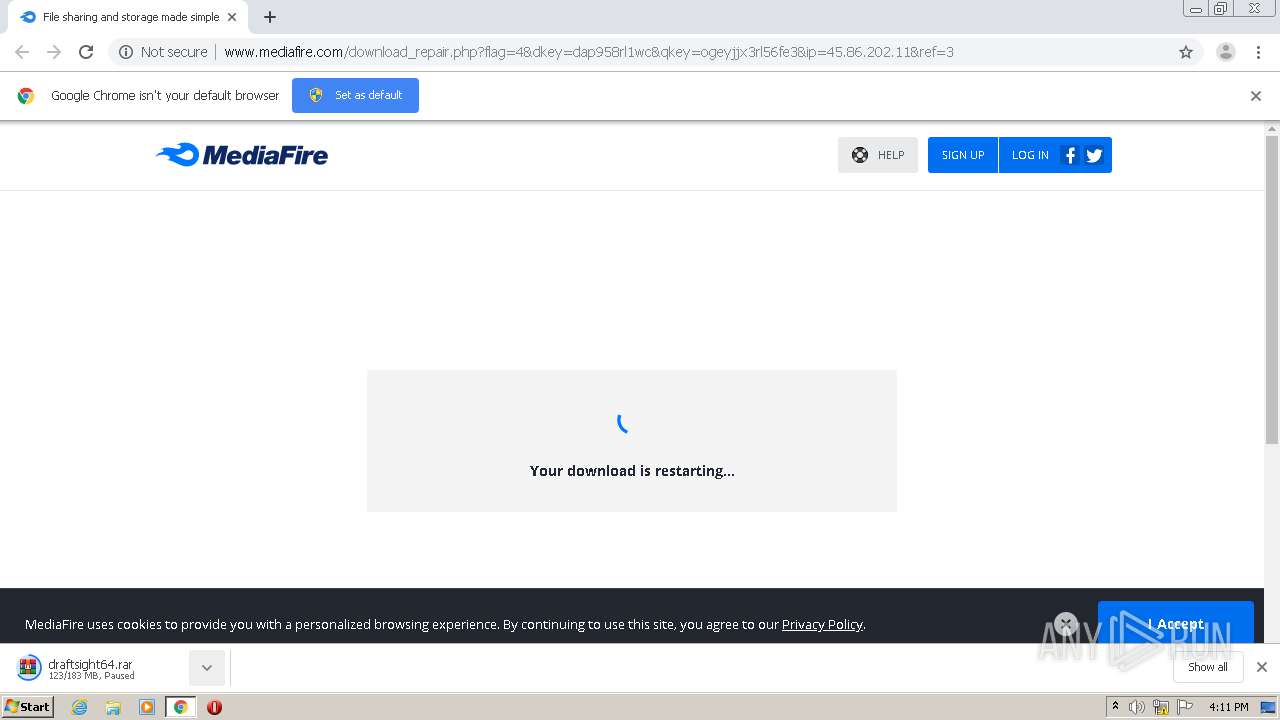
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
52
DNS requests
30
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
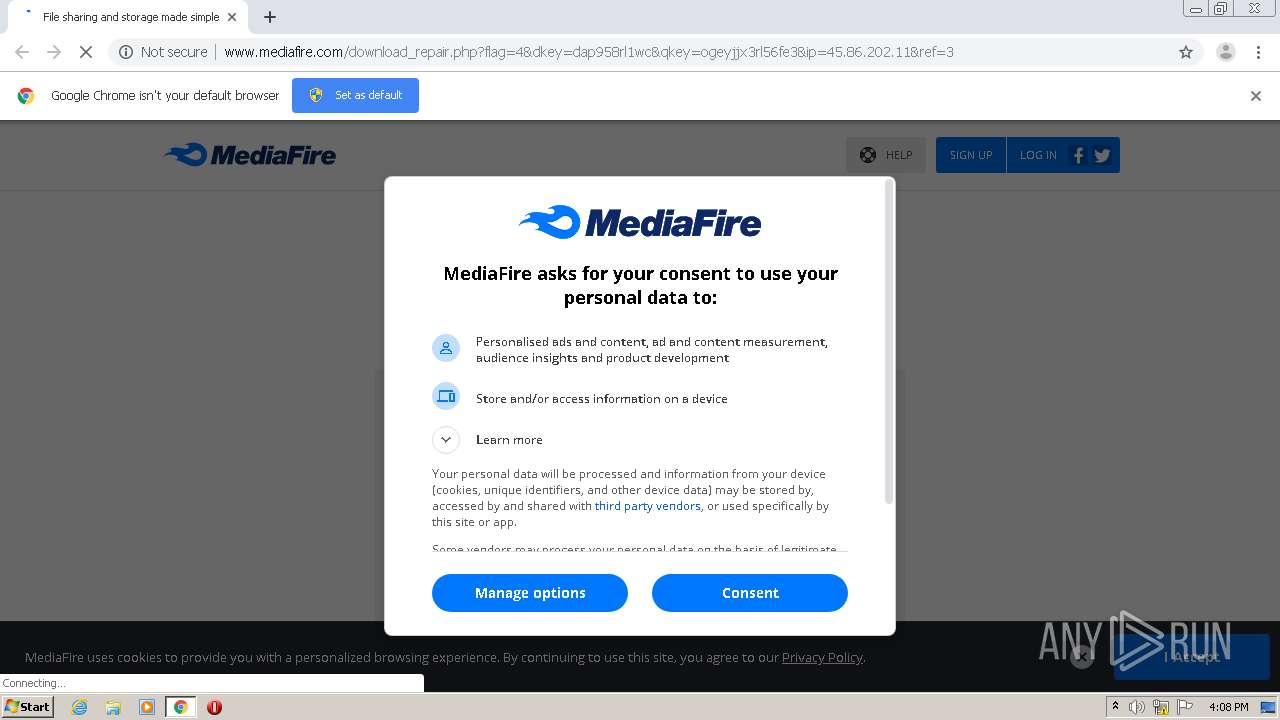
1108 | chrome.exe | GET | 302 | 205.196.123.181:80 | http://download1493.mediafire.com/dap958rl1wcg/ogeyjjx3rl56fe3/draftsight64.rar | US | — | — | whitelisted |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/js/master_121718.js | US | text | 150 Kb | shared |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/css/mfv3_121718.php?ver=nonssl | US | text | 51.7 Kb | shared |
1108 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://www.mediafire.com/blank.html | US | html | 157 b | shared |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/css/mfv4_121718.php?ver=nonssl&date=2021-01-13 | US | text | 56.9 Kb | shared |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_u1_full_color.svg | US | image | 2.04 Kb | shared |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_u1_full_color_reversed.svg | US | image | 2.02 Kb | shared |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/icons/svg_light/facebook.svg | US | image | 298 b | shared |
1108 | chrome.exe | GET | 200 | 172.217.168.74:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.7.2/jquery.min.js | US | html | 33.0 Kb | whitelisted |
1108 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://static.mediafire.com/images/icons/ico30/ico30-v9.png | US | image | 11.1 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1108 | chrome.exe | 172.217.169.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1108 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1108 | chrome.exe | 205.196.123.181:80 | download1493.mediafire.com | MediaFire, LLC | US | unknown |
1108 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1108 | chrome.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
1108 | chrome.exe | 172.217.169.100:443 | www.google.com | Google Inc. | US | whitelisted |
1108 | chrome.exe | 142.250.184.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1108 | chrome.exe | 172.217.168.74:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1108 | chrome.exe | 216.58.214.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1108 | chrome.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download1493.mediafire.com |
| unknown |
accounts.google.com |
| shared |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1108 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |