| File name: | bat2exe.exe |
| Full analysis: | https://app.any.run/tasks/4a781833-0e73-442f-827d-ecbb4f68c66f |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 11:28:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 645E34388858DA82C92DA32DED26A707 |
| SHA1: | C242788B4ACFE12EF88194C2EF1064AB4852CDE0 |
| SHA256: | 56341A3050A3561923378788BEBC81D739864CF199C43907B45E2CBBE1EBFE55 |
| SSDEEP: | 24576:B8FyepIfwNg+mhI1mEbxGkZVmFSEq7IGiz09AiVjgX2YByCSDupWREu:B8fpIyrmOkqcIEcJjgX2YiJD |
MALICIOUS
No malicious indicators.SUSPICIOUS
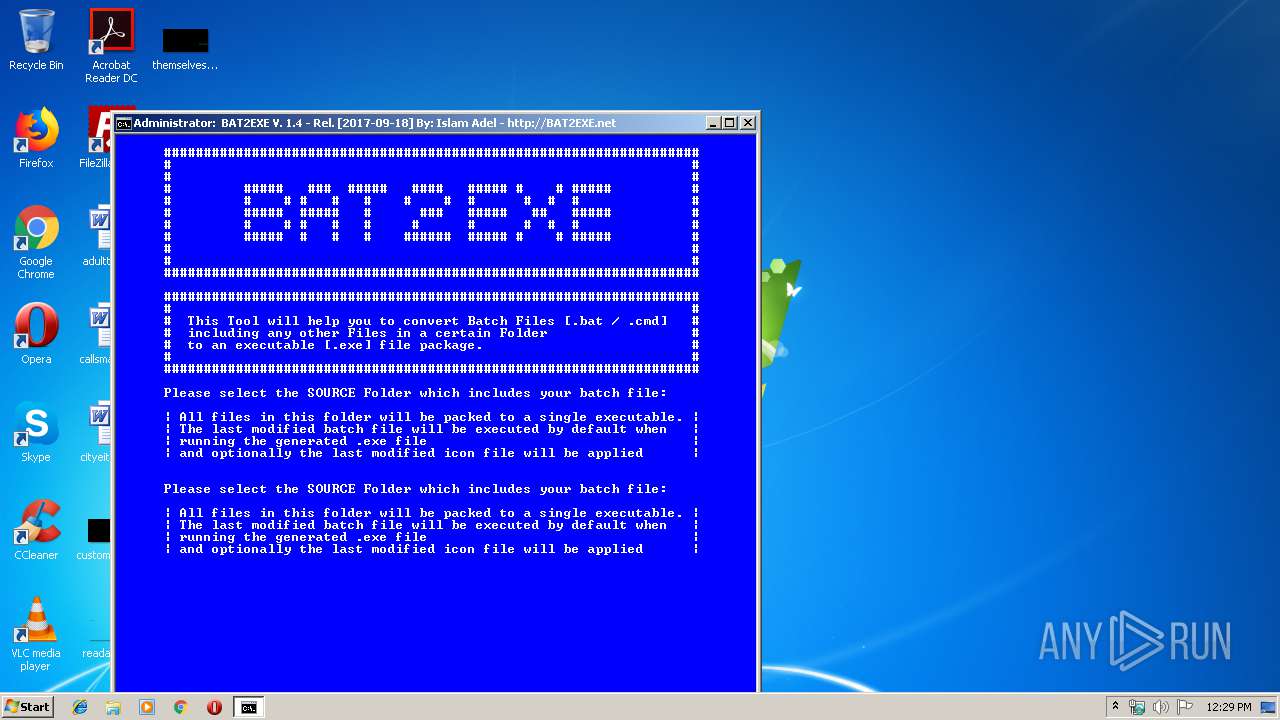
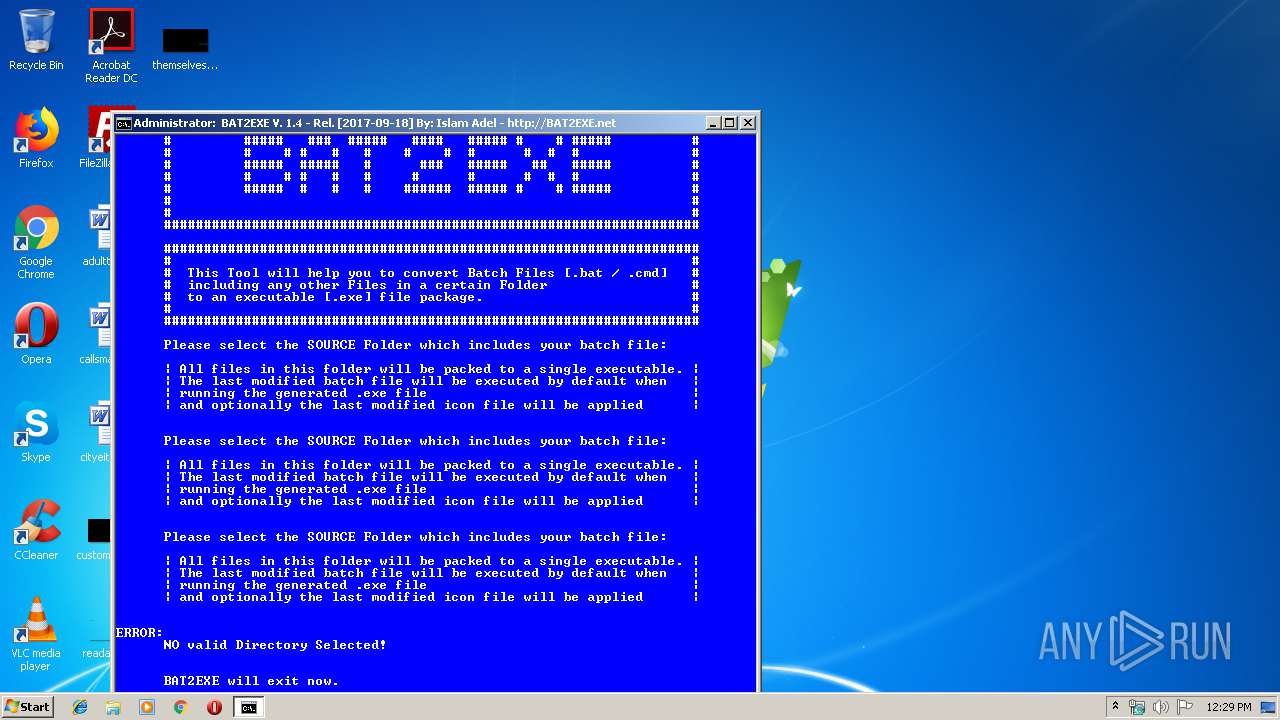
Starts CMD.EXE for commands execution
- bat2exe.exe (PID: 1920)
- cmd.exe (PID: 4072)
Executable content was dropped or overwritten
- bat2exe.exe (PID: 1920)
Executes scripts
- cmd.exe (PID: 2528)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 840)
Application launched itself
- cmd.exe (PID: 4072)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:04 17:12:31+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 93184 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x167d2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.4.0.0 |
| ProductVersionNumber: | 16.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 16.04 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2016 Igor Pavlov |
| OriginalFileName: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 16.04 |
| Comments: | Modified by an unpaid evaluation copy of Resource Tuner 2. http://www.heaventools.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Oct-2016 15:12:31 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX |
| FileVersion: | 16.04 |
| InternalName: | 7zS.sfx |
| LegalCopyright: | Copyright (c) 1999-2016 Igor Pavlov |
| OriginalFilename: | 7zS.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 16.04 |
| Comments: | Modified by an unpaid evaluation copy of Resource Tuner 2. http://www.heaventools.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Oct-2016 15:12:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00016BC5 | 0x00016C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63827 |
.rdata | 0x00018000 | 0x00003814 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.23725 |
.data | 0x0001C000 | 0x00002430 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.87468 |
.sxdata | 0x0001F000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00020000 | 0x00004248 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.74116 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50337 | 896 | UNKNOWN | English - United States | RT_VERSION |
2 | 6.01638 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.70086 | 1128 | Unicode (UTF 16LE) | English - United States | RT_ICON |
97 | 3.04857 | 184 | UNKNOWN | English - United States | RT_DIALOG |
188 | 2.17822 | 84 | UNKNOWN | English - United States | RT_STRING |
207 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
48
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | C:\Windows\system32\cmd.exe /c cscript //nologo bin\browse.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Temp\bat2exe.exe" | C:\Users\admin\AppData\Local\Temp\bat2exe.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 2304 | cscript //nologo bin\browse.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2448 | cscript //nologo bin\browse.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2528 | C:\Windows\system32\cmd.exe /c cscript //nologo bin\browse.vbs | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2728 | PING 127.0.0.1 -w 1 -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2768 | cscript //nologo bin\browse.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2880 | MODE 80,50 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3516 | PING 127.0.0.1 -w 1 -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\AppData\Local\Temp\bat2exe.exe" | C:\Users\admin\AppData\Local\Temp\bat2exe.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 16.04 Modules
| |||||||||||||||
Total events
1 404
Read events
1 381
Write events
23
Delete events
0
Modification events
| (PID) Process: | (1920) bat2exe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1920) bat2exe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2304) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
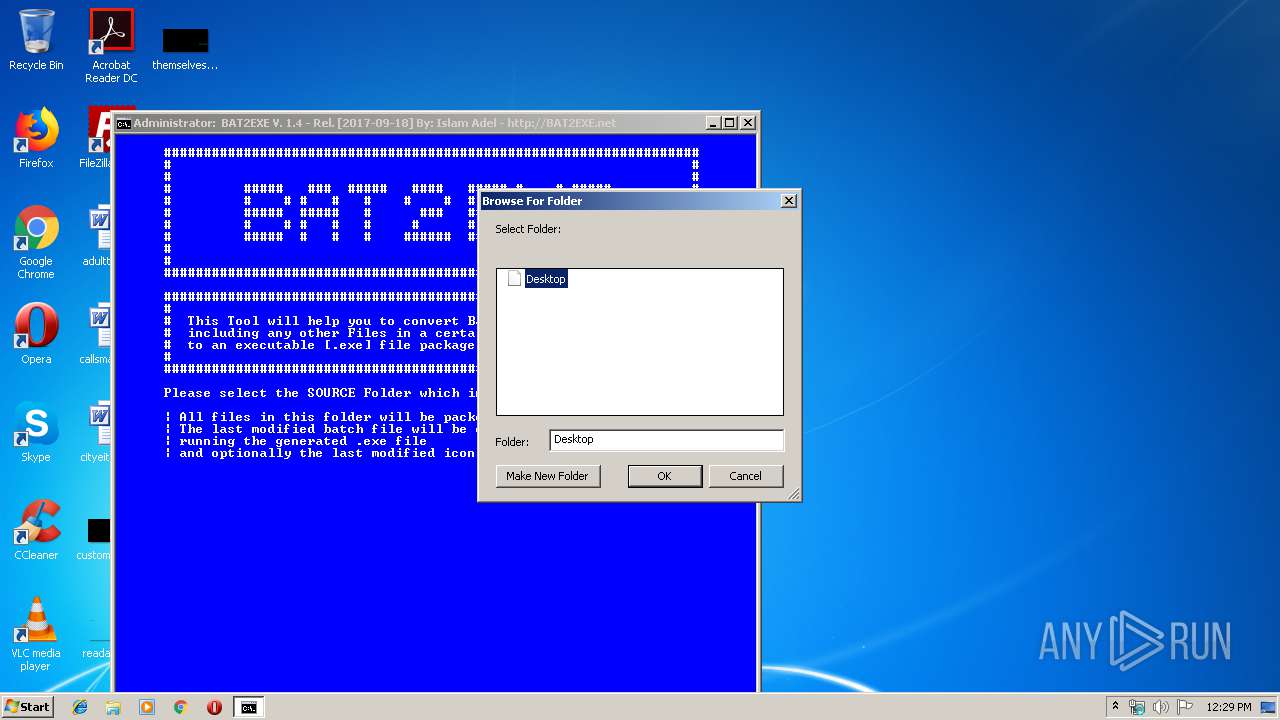
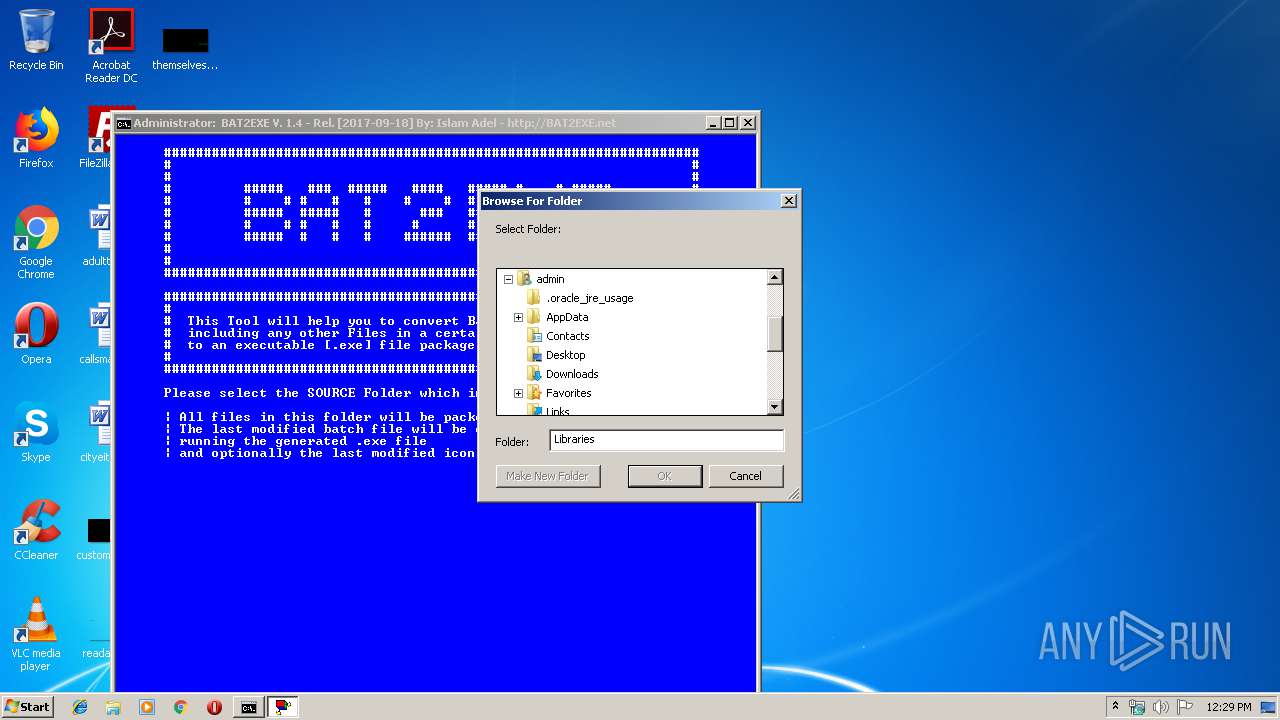
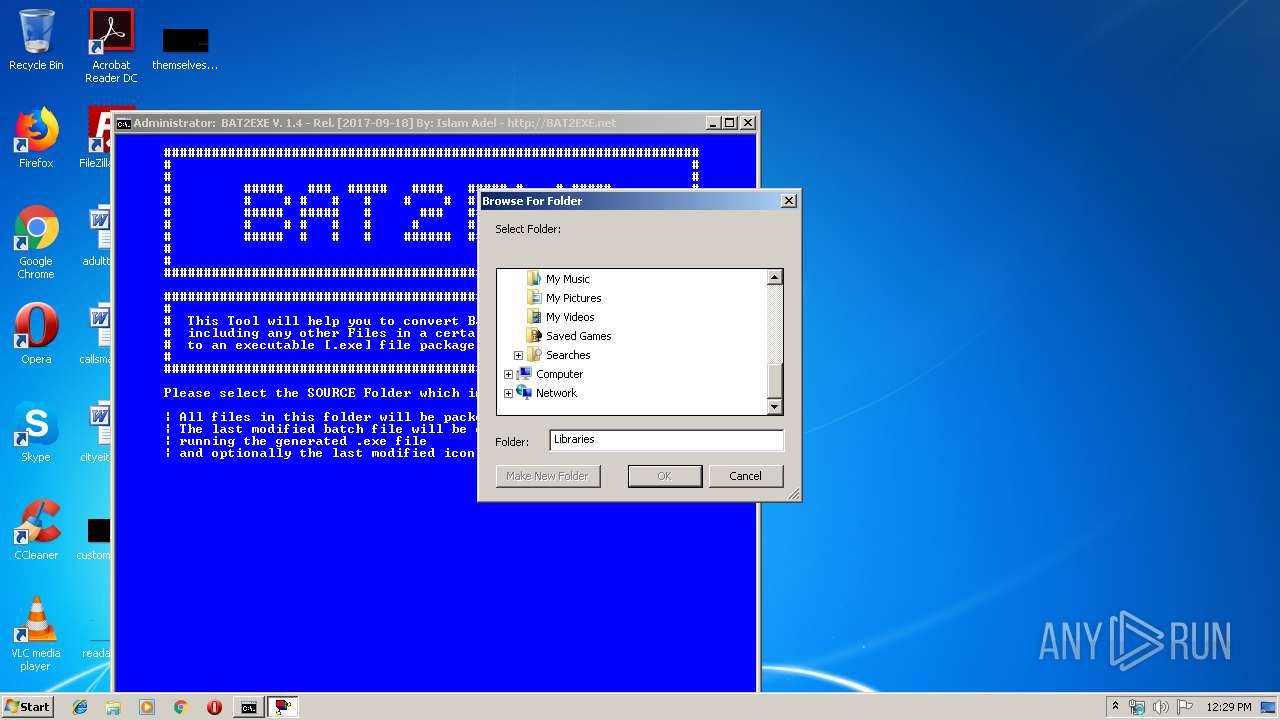
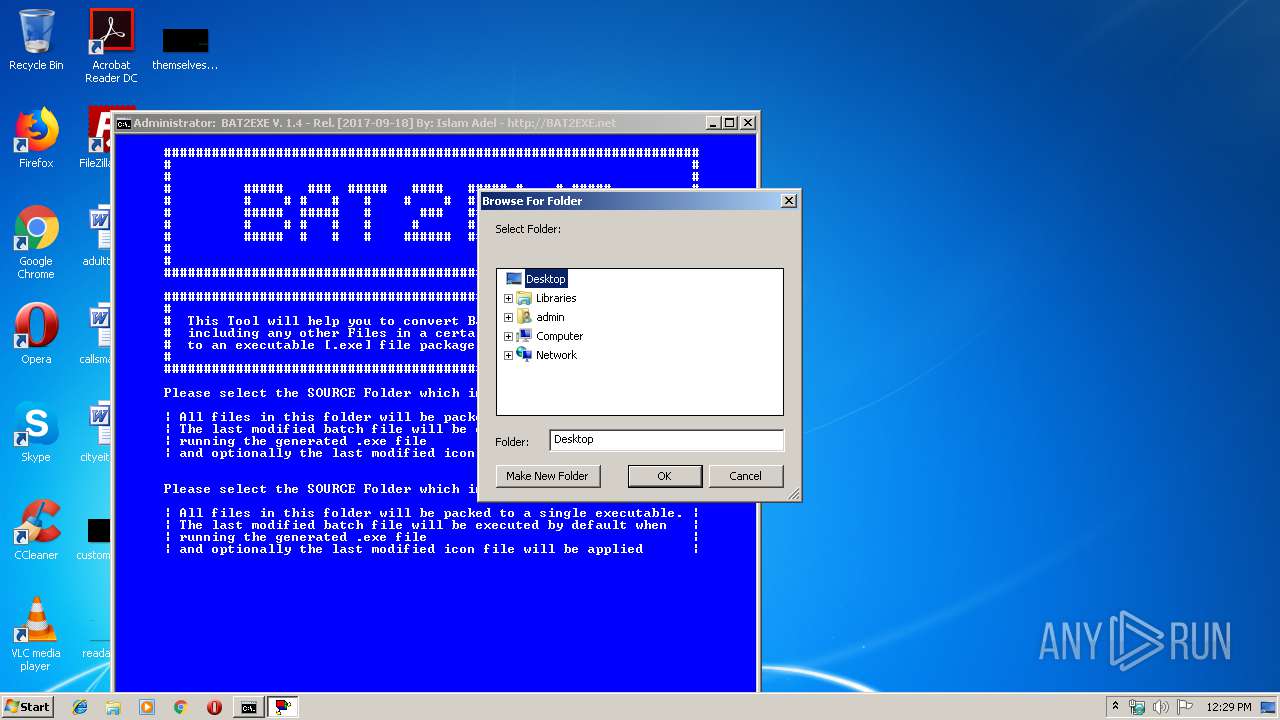
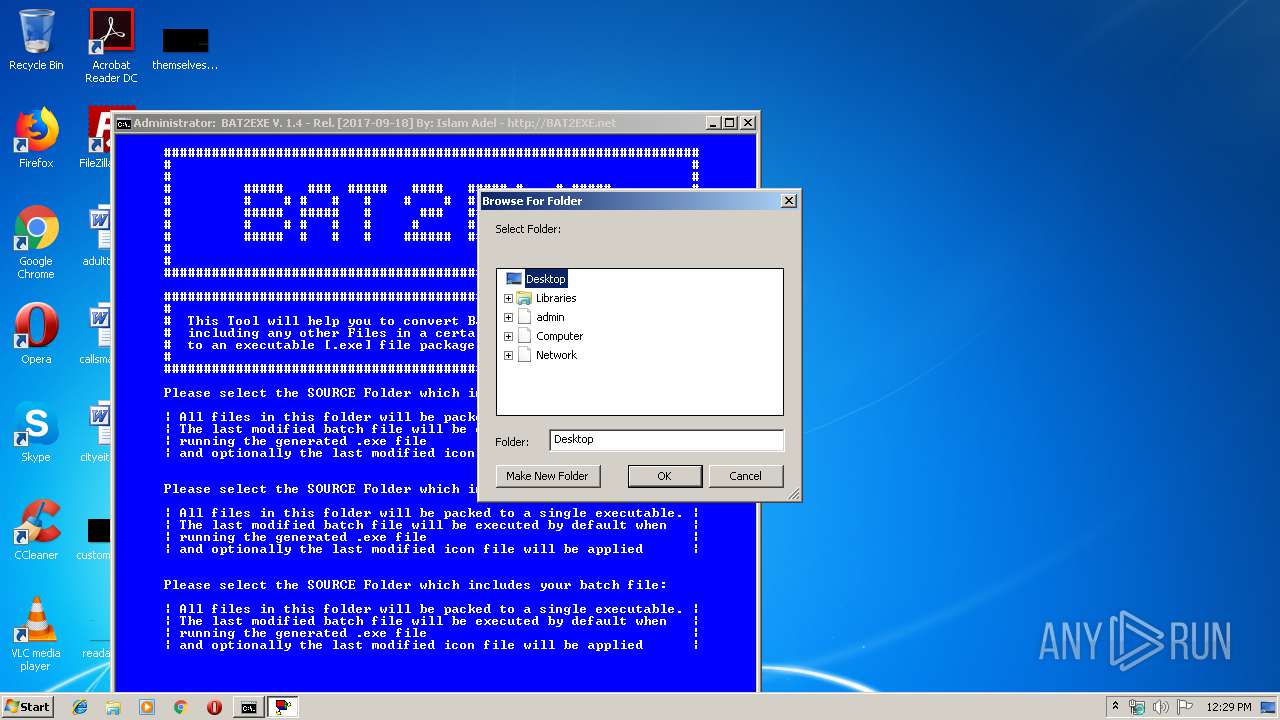
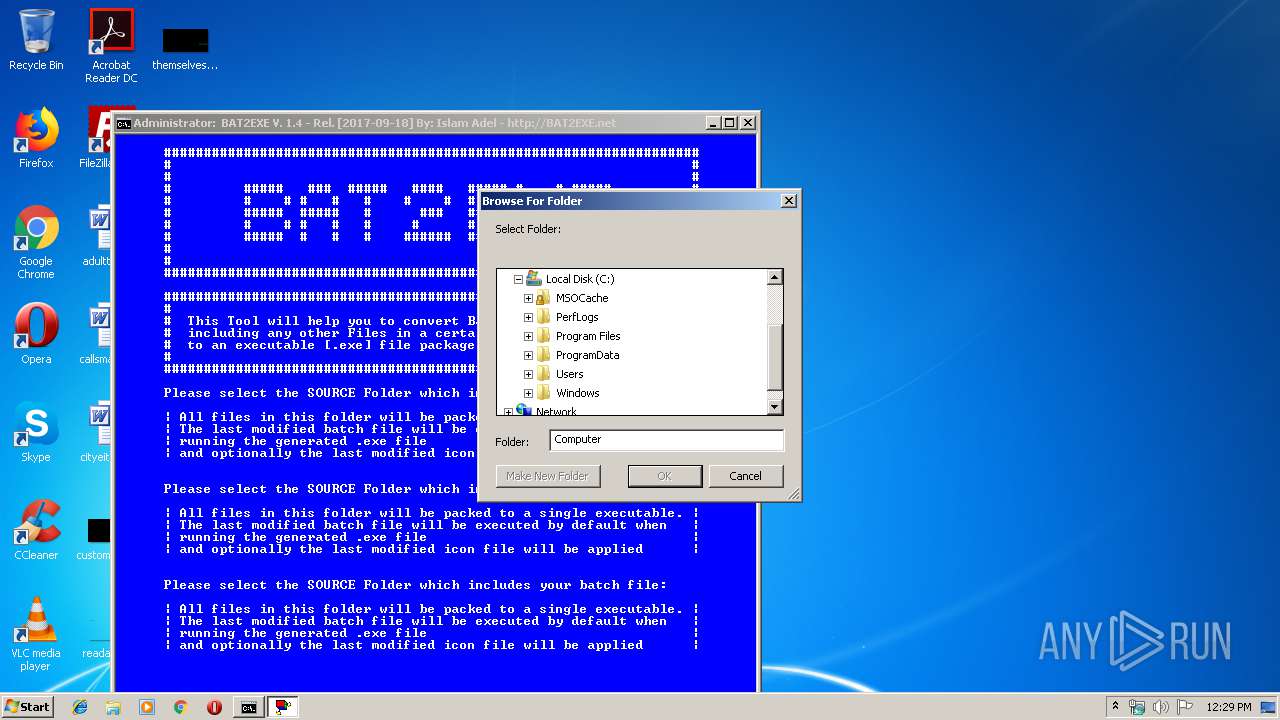
| (PID) Process: | (2304) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (2304) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (2768) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2768) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (2768) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (2448) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2448) cscript.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-2 |
Value: Access the computers and devices that are on your network. | |||
Executable files
6
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bat2exe.bat | text | |
MD5:— | SHA256:— | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\res.exe | executable | |
MD5:— | SHA256:— | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\browse.vbs | text | |
MD5:8580D8CAB38506F200F4D935EDCC19BE | SHA256:CBAF396FF11D723E0FFF497C6B7AFEDABE6975BCB32B7512058732911111AB15 | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\7z.exe | executable | |
MD5:93C7B7A3E3051BBB9630E41425CFDB3C | SHA256:C0791FE9D96325F3CF42B263FD1F5FFF65F734FA3B64FD4C597234653A26A711 | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\7zSD.sfx | executable | |
MD5:2C3AABD41C65C6AF31375208F52B9DCA | SHA256:1DD1615A327096181BDC5B2E3BE440DC67BD8D4536621150E26E823609832C92 | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\upx.exe | executable | |
MD5:FFA637ABD482B5E7D3FB75182F43F080 | SHA256:4D3D363B5B3DCD9FA516B481C92D62C02AED804318BDC4D5E97A68BB6E6D62DB | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\7z.dll | executable | |
MD5:CA41D56630191E61565A343C59695CA1 | SHA256:6C80E3F49FCF561E6A0B52F9B4C81D1D07B22085F7864EE4CFD30DD10F6B3B12 | |||
| 1920 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7zS08752B96\bin\choice.exe | executable | |
MD5:E8F8B1058775103AC8BA6381345A4A57 | SHA256:4A1B84960EBB5E98F945A1935952633CD805A86B199D2DBCD140D75033636EC7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report