| File name: | 5628dab224ebad1364bf2ac4815b8b9b32b143055262a57ddc13ff1bf42ba46f.apk |
| Full analysis: | https://app.any.run/tasks/01919928-1d57-4996-a0fe-c08295a4152b |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 12:27:05 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties, with APK Signing Block |
| MD5: | F1323F138D69C6A95B0FF960F4F83BF4 |
| SHA1: | 58E66A580A7BC0DBCADEF9404ABD1EC972C622A8 |
| SHA256: | 5628DAB224EBAD1364BF2AC4815B8B9B32B143055262A57DDC13FF1BF42BA46F |
| SSDEEP: | 98304:5mUFWrg1STWKuv7iBIfd54s5l14fa6HJGrHiW9h4xv+EJ9Pub3q94u6VCDMMQrHT:bDl |
MALICIOUS
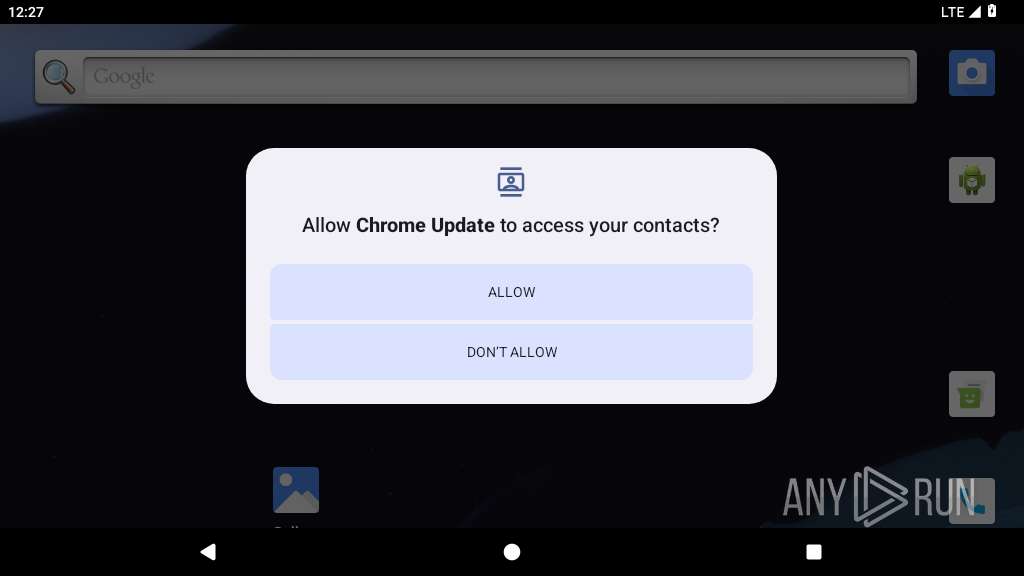
Returns the phone's primary line number (MSISDN)
- app_process64 (PID: 2280)
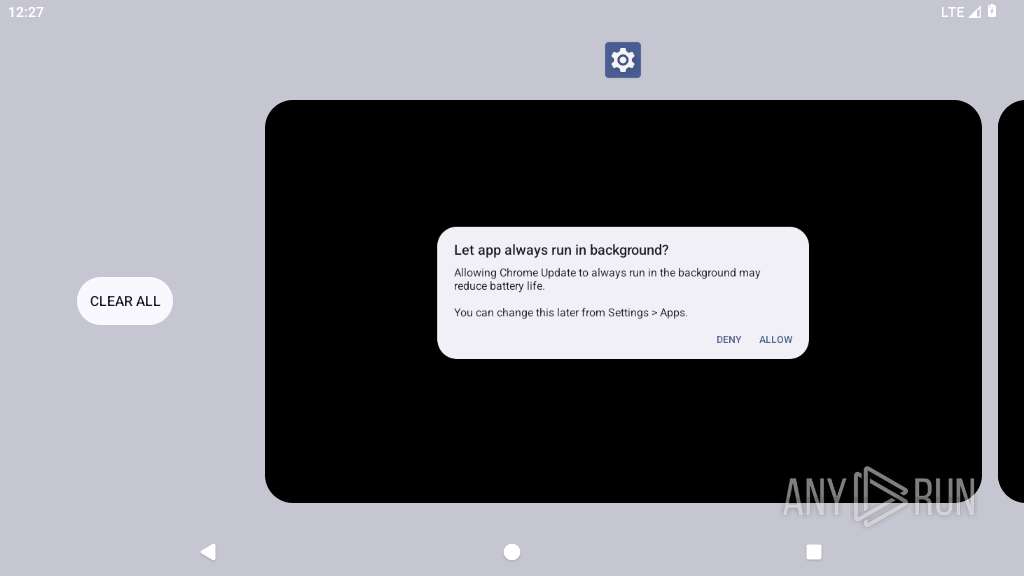
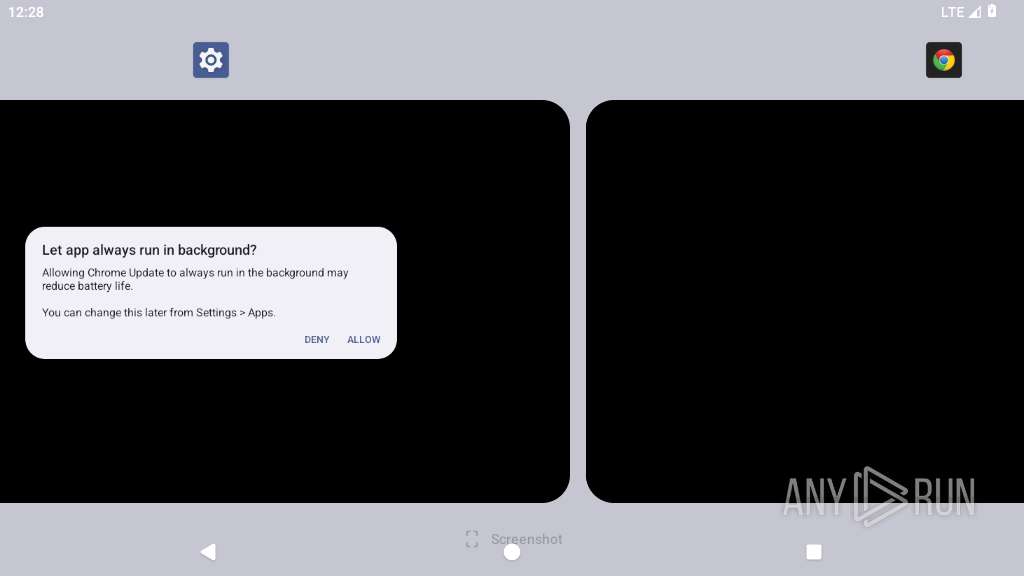
Hides app icon from display
- app_process64 (PID: 2280)
SUSPICIOUS
Checks if the device's lock screen is showing
- app_process64 (PID: 2280)
Scans for installed antivirus apps
- app_process64 (PID: 2280)
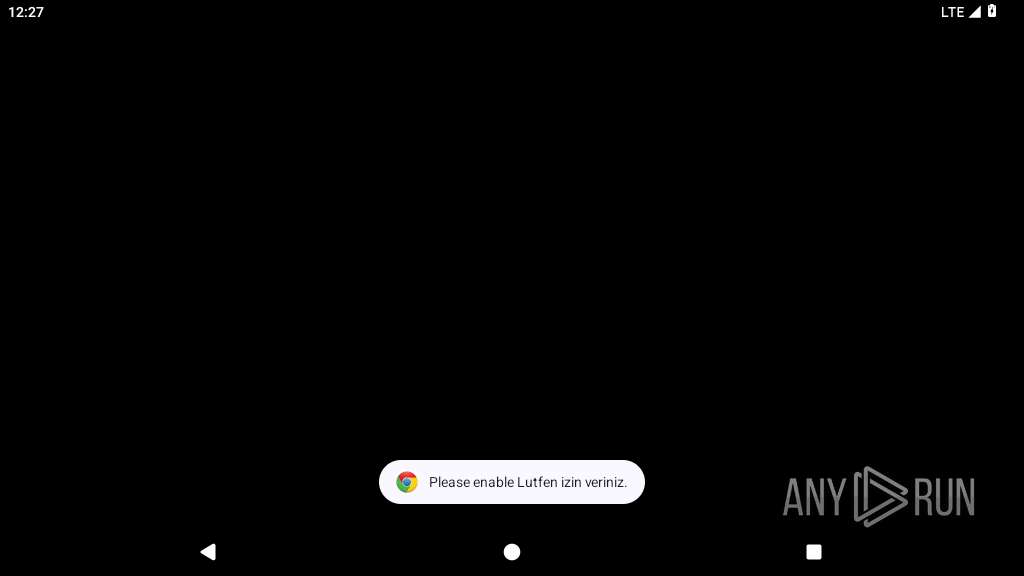
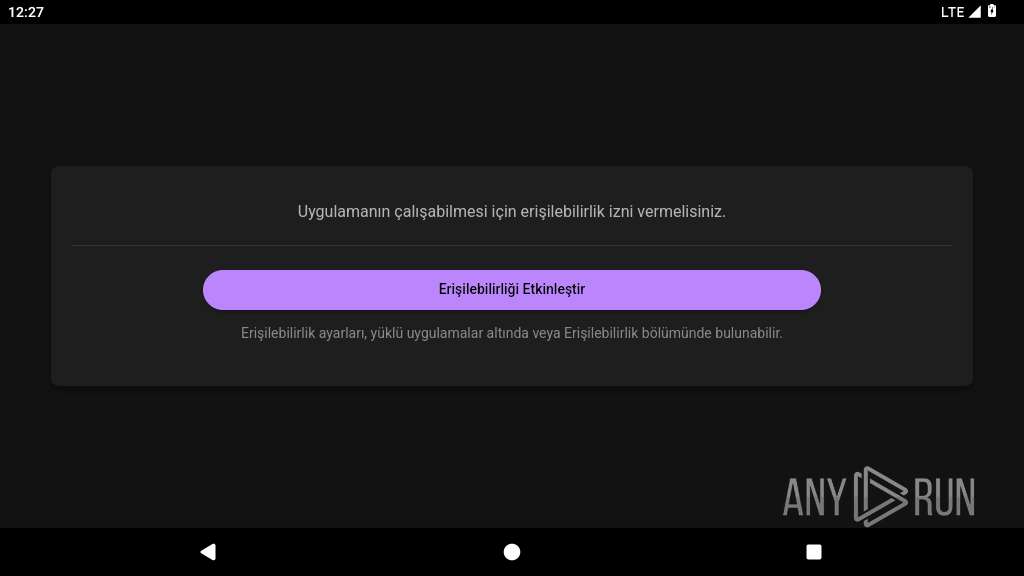
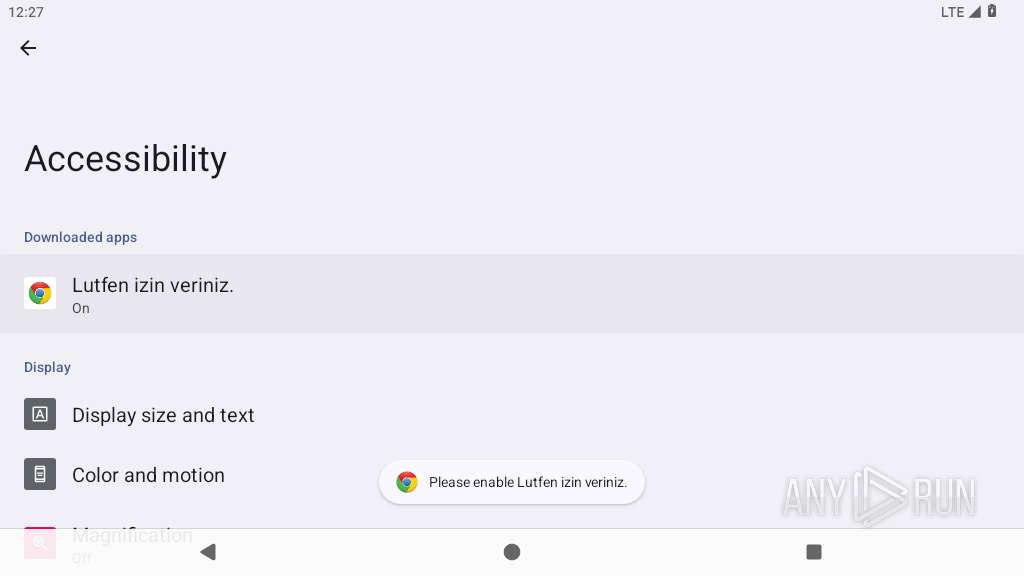
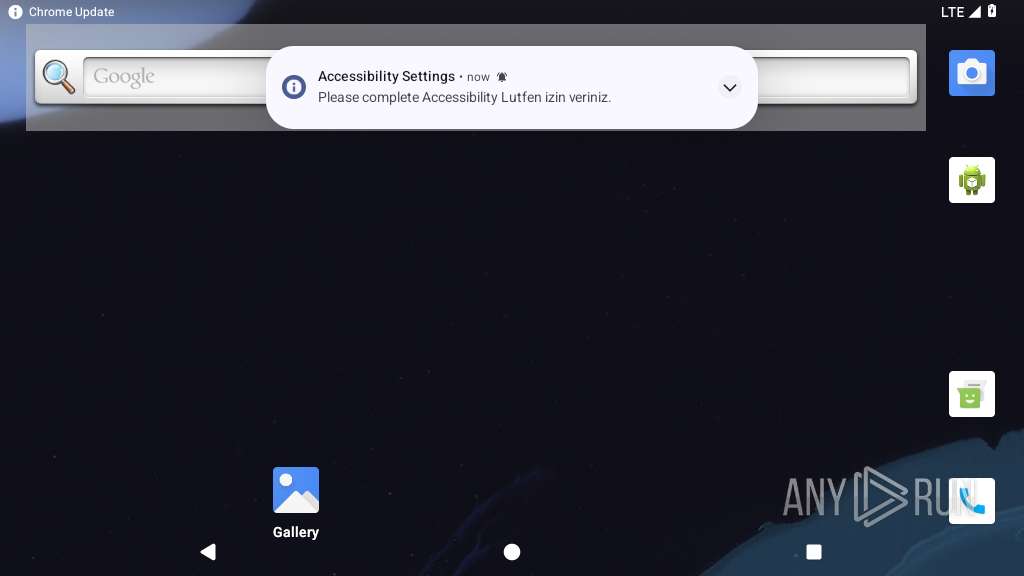
Requests access to accessibility settings
- app_process64 (PID: 2307)
Performs UI accessibility actions without user input
- app_process64 (PID: 2280)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2280)
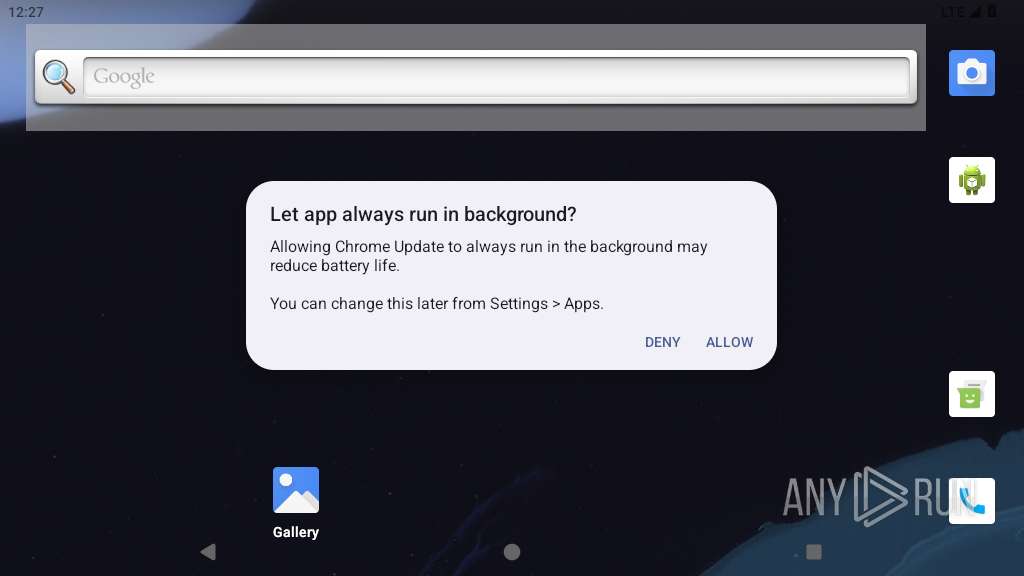
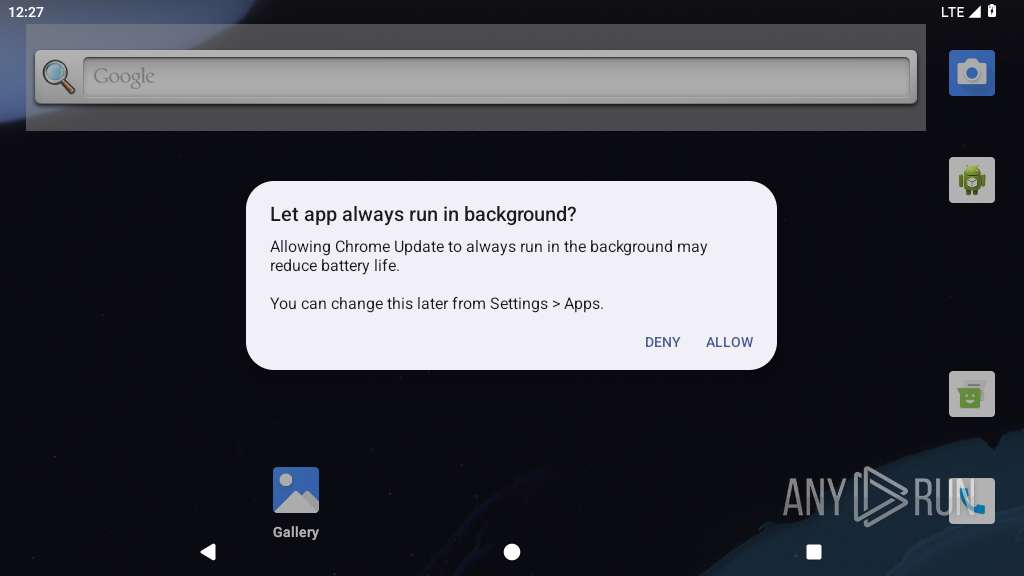
Checks exemption from battery optimization
- app_process64 (PID: 2280)
Starts a service
- app_process64 (PID: 2280)
Returns the name of the current network operator
- app_process64 (PID: 2280)
Prevents its uninstallation by user
- app_process64 (PID: 2280)
Launches a new activity
- app_process64 (PID: 2280)
- app_process64 (PID: 2307)
Leverages accessibility to control apps
- app_process64 (PID: 2280)
Intercepts events for accessibility services
- app_process64 (PID: 2280)
Retrieves a list of running services
- app_process64 (PID: 2280)
Establishing a connection
- app_process64 (PID: 2280)
INFO
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2280)
Retrieves the value of a secure system setting
- app_process64 (PID: 2280)
Detects device power status
- app_process64 (PID: 2280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (73.9) |
|---|---|---|
| .jar | | | Java Archive (20.4) |
| .zip | | | ZIP compressed archive (5.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0xbd71e113 |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
132
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2280 | unbraided.specimen.emperor.referee | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2307 | unbraided.specimen.emperor.referee:webview_process | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2335 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2353 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2432 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2486 | com.android.systemui.accessibility.accessibilitymenu | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2570 | com.android.settings | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
28
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | app_process64 | /data/data/unbraided.specimen.emperor.referee/code_cache/decrypted.dex | binary | |
MD5:— | SHA256:— | |||
| 2280 | app_process64 | /data/data/unbraided.specimen.emperor.referee/shared_prefs/SharedFiles.xml | xml | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/code_cache/decrypted.dex | dex | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/cache/WebView/font_unique_name_table.pb | binary | |
MD5:— | SHA256:— | |||
| 2280 | app_process64 | /data/data/unbraided.specimen.emperor.referee/cache/oat_primary/arm64/base.2280.tmp | binary | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/cache/WebView/Default/HTTP Cache/Code Cache/webui_js/index | binary | |
MD5:— | SHA256:— | |||
| 2307 | app_process64 | /data/data/unbraided.specimen.emperor.referee/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
21
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.186.35:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
2280 | app_process64 | POST | 521 | 104.21.91.68:80 | http://tonyspain.mom/RestApi | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
449 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.35:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.251.31.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
2335 | app_process32 | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2432 | app_process32 | 142.250.185.67:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2432 | app_process32 | 142.250.186.78:443 | dl.google.com | GOOGLE | US | whitelisted |
2280 | app_process64 | 104.21.91.68:80 | tonyspain.mom | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
tonyspain.mom |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |