| File name: | SmartPlayer.exe |
| Full analysis: | https://app.any.run/tasks/df49ec0d-410b-43df-9449-1c6358510df7 |
| Verdict: | Suspicious activity |
| Analysis date: | April 11, 2019, 07:36:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 654A8C9787E0F19DCE9BDE0304D1042F |
| SHA1: | 67F3628419866DE462DCA0FACA9A10B51996159D |
| SHA256: | 561A47832A85426D915E9B17AA67FDC4BA32FAAE20AF82CB894A6228AFC726A0 |
| SSDEEP: | 12288:f46yxkmE9X2OW83HvGjIckRuzXWiF2kZzz7p2ZJ+vGop8S7HQ6fldJlRlndBAYVC:fwq4t0ckRuDjF20H7kZkvGLSTflDO |
MALICIOUS
Loads dropped or rewritten executable
- play.exe (PID: 2340)
Application was dropped or rewritten from another process
- play.exe (PID: 2340)
SUSPICIOUS
Creates files in the user directory
- SmartPlayer.exe (PID: 3276)
Executable content was dropped or overwritten
- SmartPlayer.exe (PID: 3276)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:02 08:44:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 61440 |
| InitializedDataSize: | 589824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7478 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Aug-2016 06:44:42 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Aug-2016 06:44:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000EB0F | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59869 |
.rdata | 0x00010000 | 0x0000252A | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69804 |
.data | 0x00013000 | 0x00004BC0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.32896 |
.rsrc | 0x00018000 | 0x0008B040 | 0x0008C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99793 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
102 | 7.99969 | 561650 | Latin 1 / Western European | Chinese - PRC | ZIP |
103 | 1.91924 | 20 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHELL32.dll |
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Users\admin\AppData\Roaming\SPTemp\play.exe" C:\Users\admin\AppData\Local\Temp | C:\Users\admin\AppData\Roaming\SPTemp\play.exe | — | SmartPlayer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2, 1, 4, 18685 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\AppData\Local\Temp\SmartPlayer.exe" | C:\Users\admin\AppData\Local\Temp\SmartPlayer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 094
Read events
936
Write events
157
Delete events
1
Modification events
| (PID) Process: | (3276) SmartPlayer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3276) SmartPlayer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
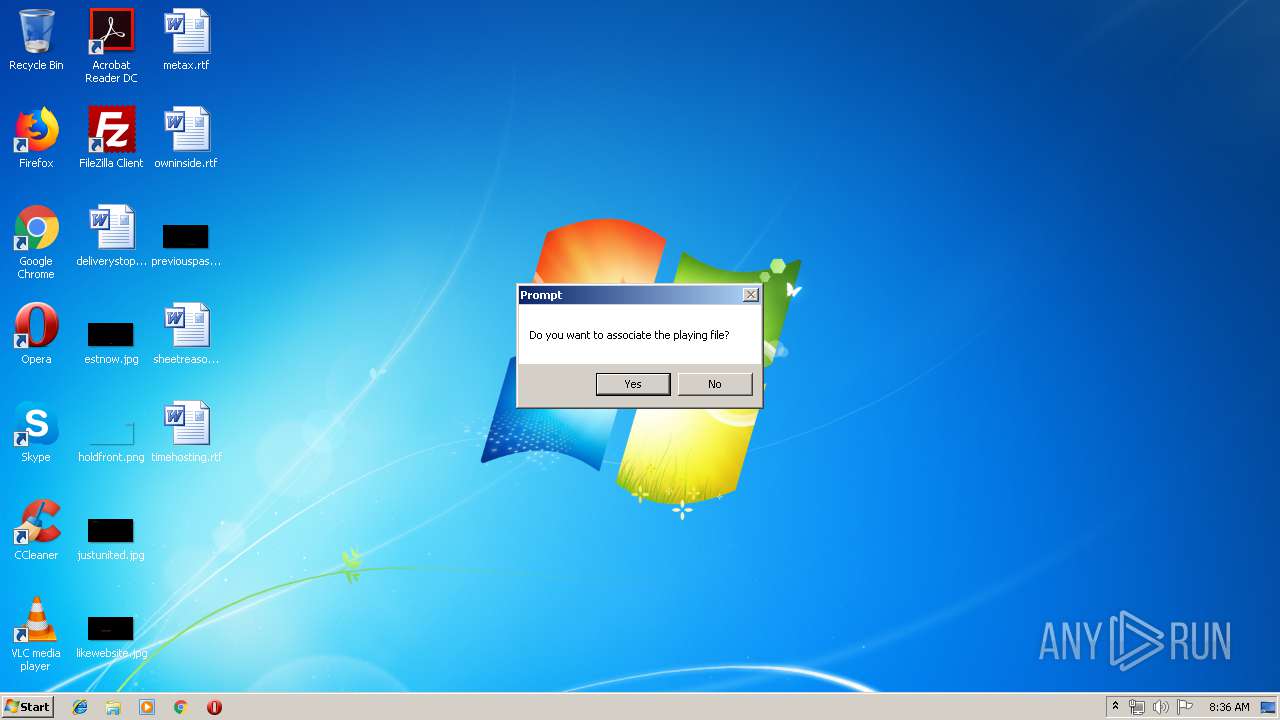
| (PID) Process: | (2340) play.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: play.exe | |||
| (PID) Process: | (2340) play.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DAV Player |
| Operation: | write | Name: | Path |
Value: c:\users\admin\appdata\roaming\sptemp\ | |||
| (PID) Process: | (2340) play.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.asf |
| Operation: | write | Name: | |
Value: player.asf | |||
| (PID) Process: | (2340) play.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 57 | |||
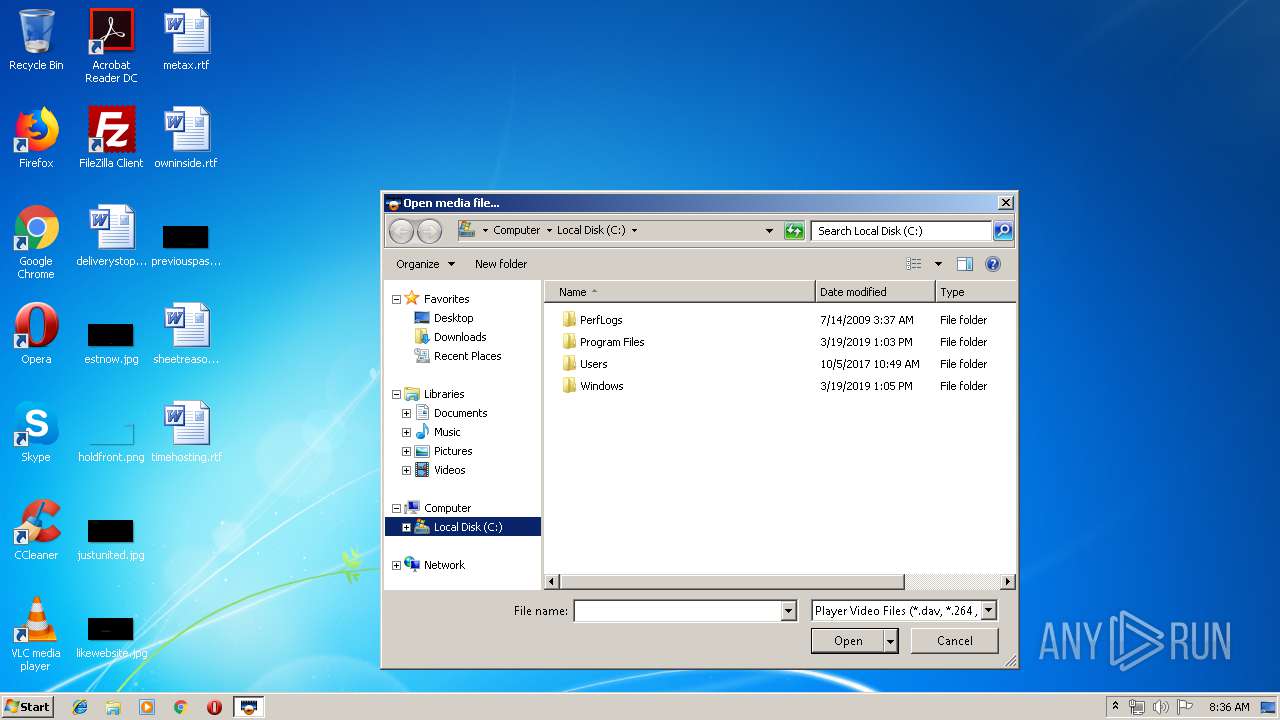
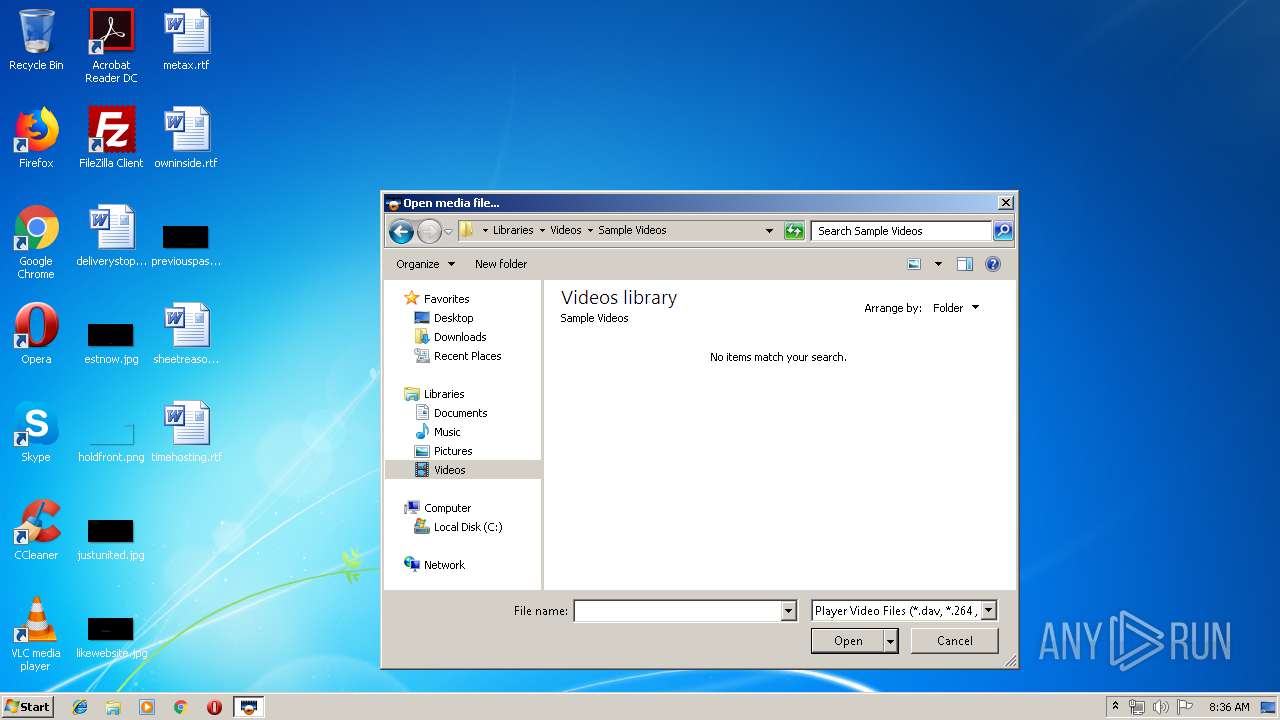
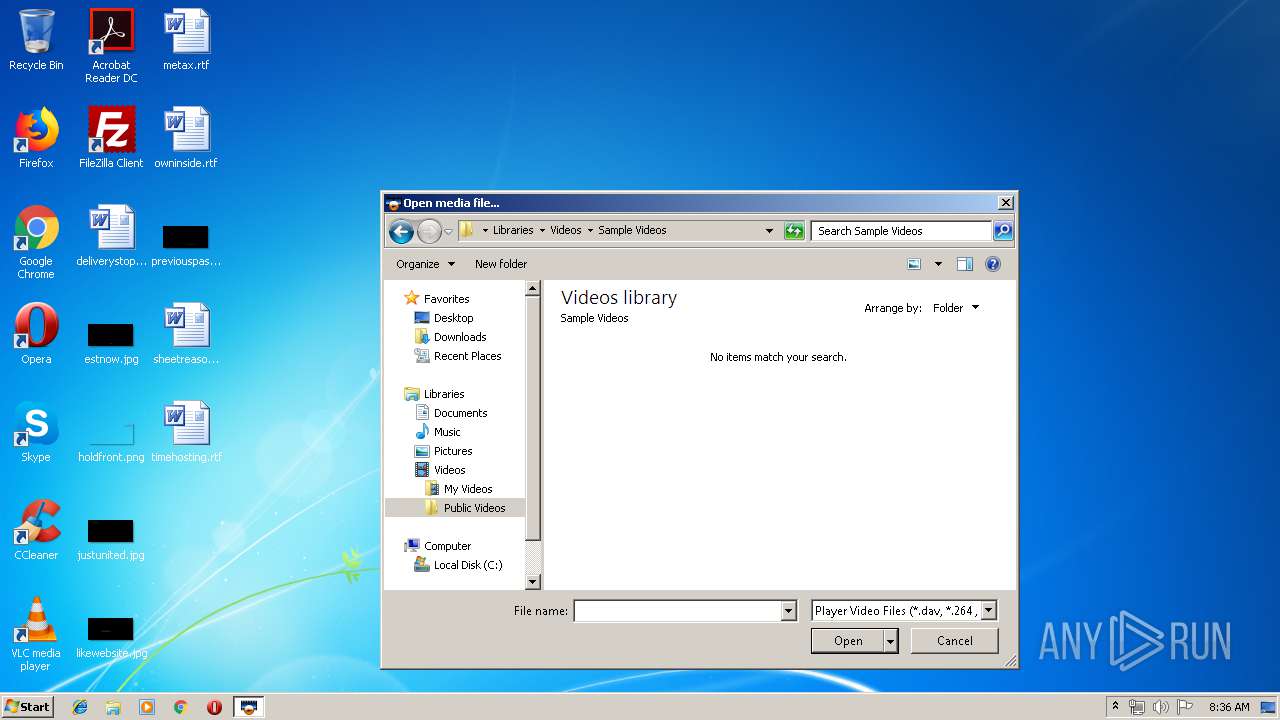
| (PID) Process: | (2340) play.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C0053005000540065006D0070005C0070006C00610079002E00650078006500000043003A005C000000 | |||
| (PID) Process: | (2340) play.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2340) play.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (2340) play.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
Executable files
5
Suspicious files
1
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\play.exe | executable | |
MD5:E109B91B38028C9B181694920F260D0B | SHA256:4E2EA65E8832047C727444FD910842C77A4C5C4491938222E8D9ECAB1AED26D0 | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\player.ini | text | |
MD5:4BC1E735A2B2D8D792245354F709439B | SHA256:EEBBE3795426F38883E6B460EAA2924911AB6CF8265C20EBB3ED111BD0BE5073 | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\dhplay.dll | executable | |
MD5:C286E3AAC630991C40DD03C8653FF2D9 | SHA256:51A7669492EEF20D4AF3DA1067E7ECEC8DE8FE002AC1B83E6CC7CE3074C60D52 | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\eng.ini | text | |
MD5:424EAA3C1A977E1C4237AD286BAC2CC2 | SHA256:AE0B771A7541003BA04AD77F4B401D3B4CDDC17067C91067F8C3F3C971469EB3 | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\SmartPlayer.7z | compressed | |
MD5:9C50BC41E47424FEE2B4B42C2CE24791 | SHA256:66C2055128DFEC76D52EC0E2ECAB1686D4E6F85D3CC7EBC9D58D8537DAA01C0E | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\postproc.dll | executable | |
MD5:72F3B9040826E524473B9DA836A3A5E3 | SHA256:B057F6571A95CFD35E16AAE5513918BA6235EE24809E70AA63FAE714468F583A | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\skin.ini | text | |
MD5:5A0E389416FDEED00DF131712B90C91A | SHA256:234D9AEFCD510E41760544BCFEECBE7AA0CDF6CD1E500A4316496AF74A293B44 | |||
| 2340 | play.exe | C:\users\admin\appdata\roaming\sptemp\player.ini | text | |
MD5:4BC1E735A2B2D8D792245354F709439B | SHA256:EEBBE3795426F38883E6B460EAA2924911AB6CF8265C20EBB3ED111BD0BE5073 | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\resDll.dll | executable | |
MD5:8194C84330D5E1D7561A4535E6C6773D | SHA256:B369EC201FDDB21F9492BE809748CF5B2FAC1B81D7B2E7333A985CBC61D9F811 | |||
| 3276 | SmartPlayer.exe | C:\Users\admin\AppData\Roaming\SPTemp\h264dec.dll | executable | |
MD5:7D6A901633D97AC3D21272F3C99C1B6F | SHA256:DE86264EC5FFB0C9FD20BF7BB6298089A68F403012342C88EE3BFED9C9DE6470 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
SmartPlayer.exe |
ERROR: |
SmartPlayer.exe | start 7zUnzip main! |
SmartPlayer.exe |
ERROR: |
SmartPlayer.exe | Extract7zZip succeed! |
SmartPlayer.exe |
ERROR: |
SmartPlayer.exe | ShellExecute succeed! |