| File name: | crack.dll |
| Full analysis: | https://app.any.run/tasks/f8a57188-eabe-400a-981e-f293885cd828 |
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2024, 15:30:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (DLL) (console) x86-64, for MS Windows |
| MD5: | B20AEA020A8614176072DA7B04296D22 |
| SHA1: | 1508768117167EF69CD5C4182097304F520F9D9B |
| SHA256: | 5607F154872D0BA75144E05DC1A507A37D2E3856D6670CFE04DC7B0EC7597D9F |
| SSDEEP: | 24576:AU1FaOBP0BGV2YCYYyzEOSso2WP+Ec0xMkN8JsU3Ao/fdmjLdGGf:AYFaOIg2YCYY6nSso2WefdmjLdGGf |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process creates files with name similar to system file names
- WerFault.exe (PID: 2892)
Process drops python dynamic module
- loader.exe (PID: 5000)
- main.exe (PID: 360)
- main.exe (PID: 66144)
- loader.exe (PID: 66028)
Executes application which crashes
- rundll32.exe (PID: 6732)
Process drops legitimate windows executable
- loader.exe (PID: 5000)
- main.exe (PID: 360)
- loader.exe (PID: 66028)
- main.exe (PID: 66144)
Executable content was dropped or overwritten
- loader.exe (PID: 5000)
- main.exe (PID: 360)
- main.exe (PID: 66144)
- loader.exe (PID: 66028)
The process drops C-runtime libraries
- loader.exe (PID: 5000)
- main.exe (PID: 360)
- loader.exe (PID: 66028)
- main.exe (PID: 66144)
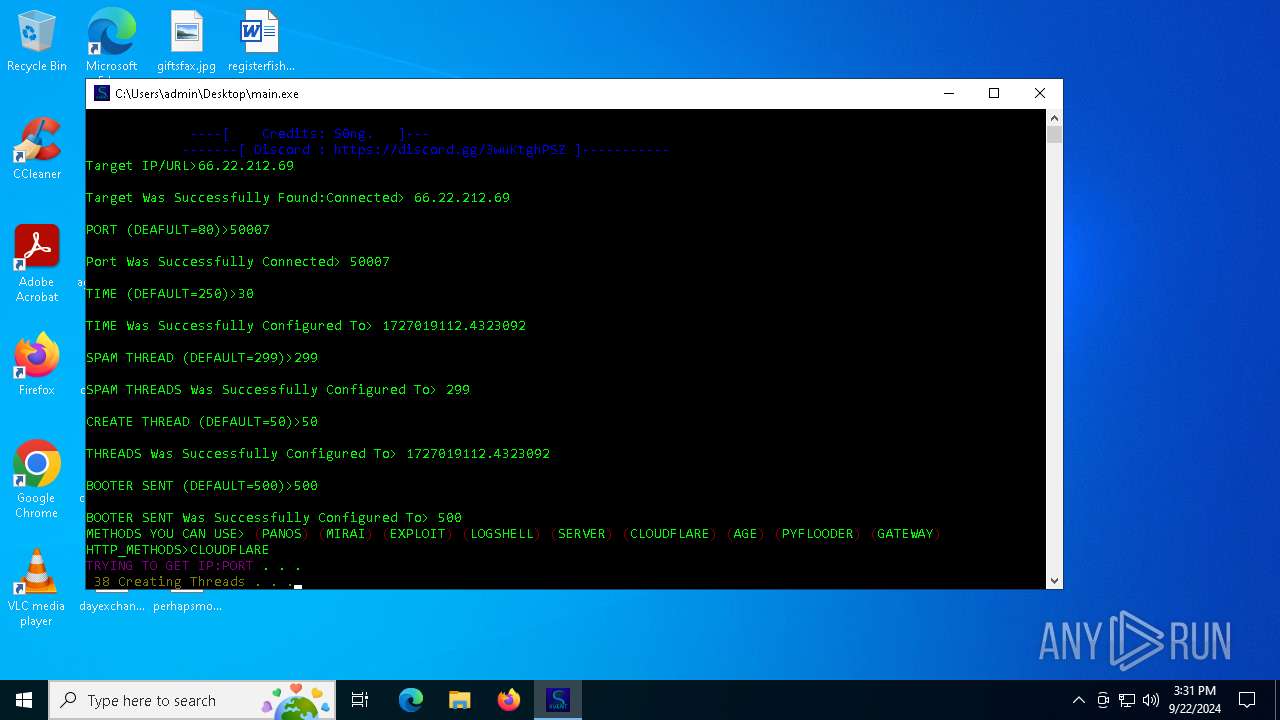
Loads Python modules
- loader.exe (PID: 2648)
- main.exe (PID: 7052)
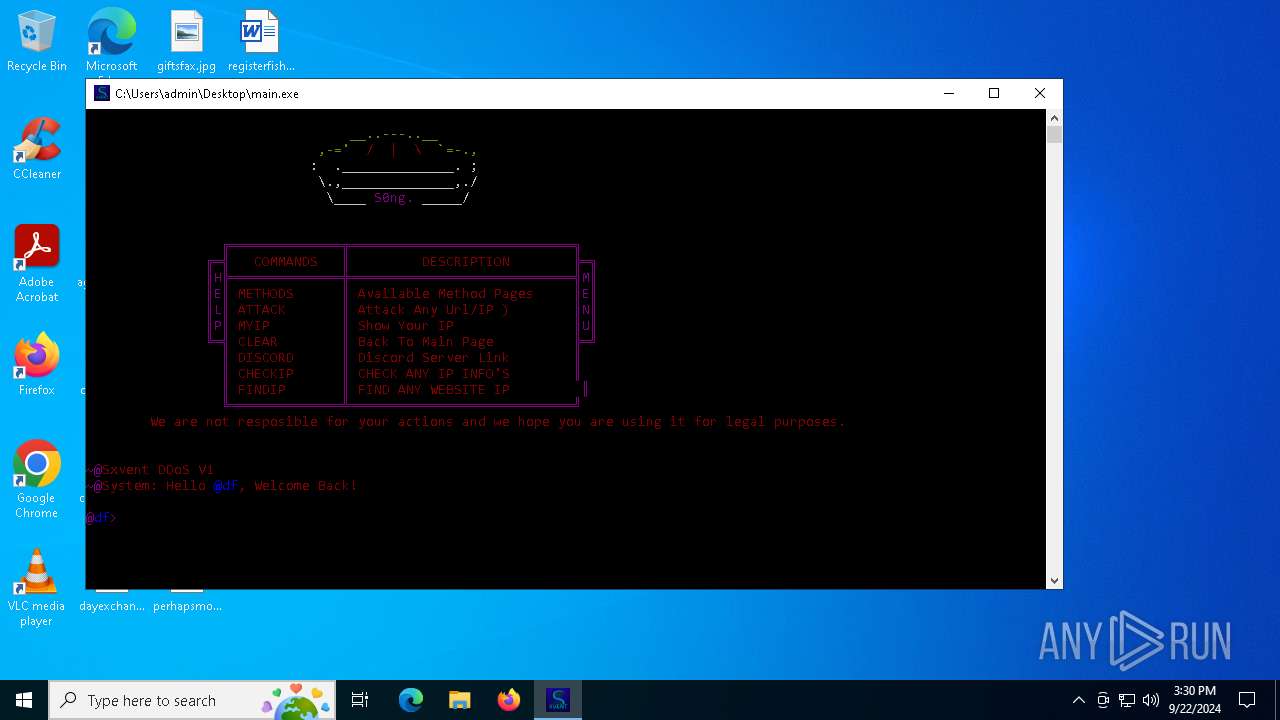
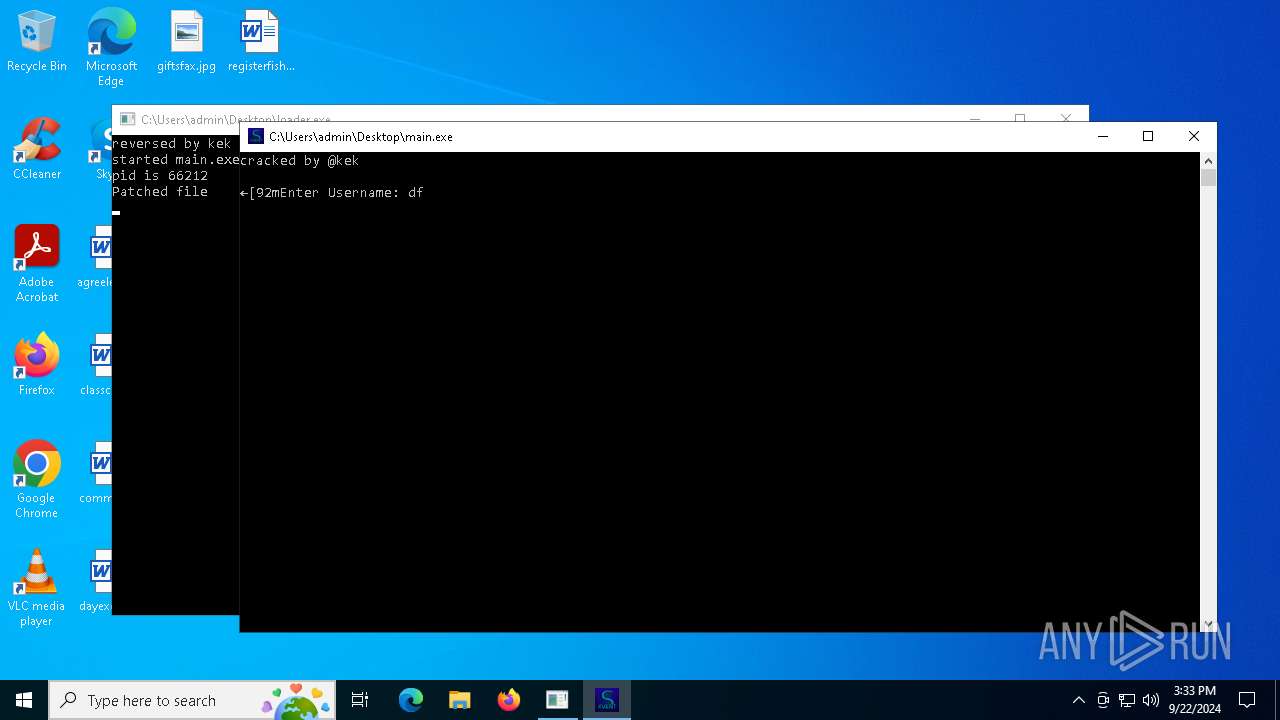
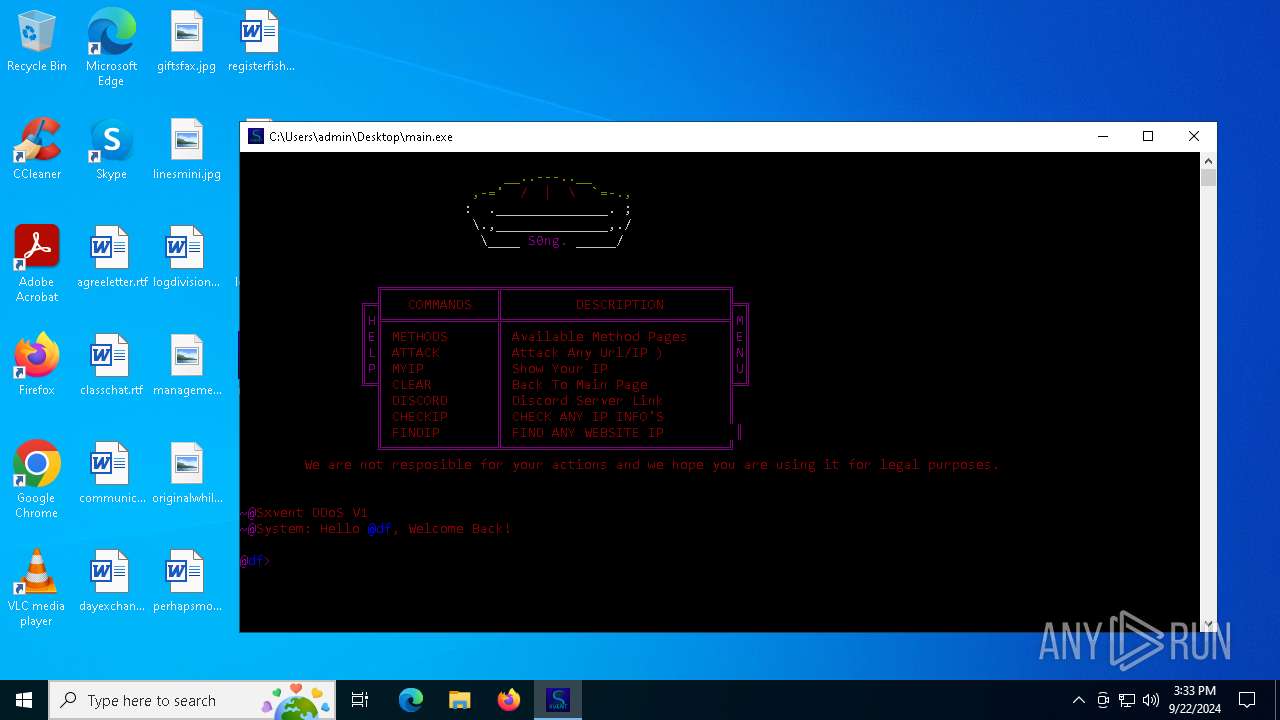
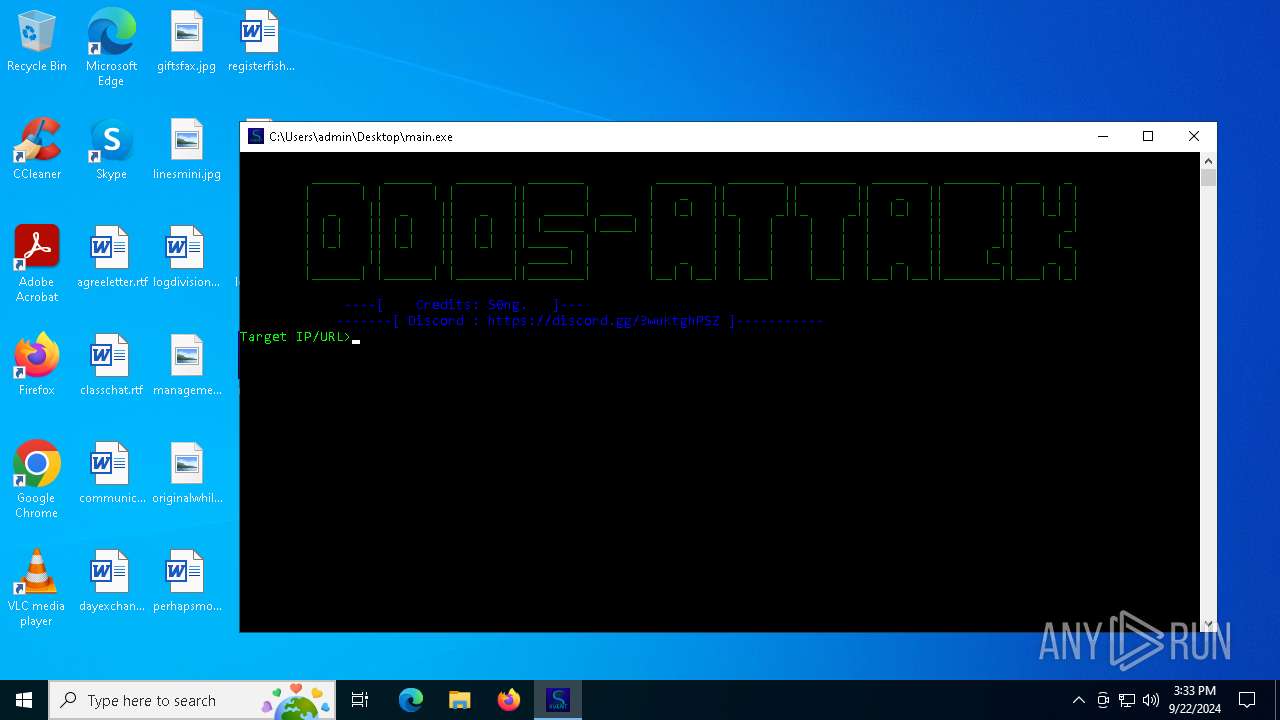
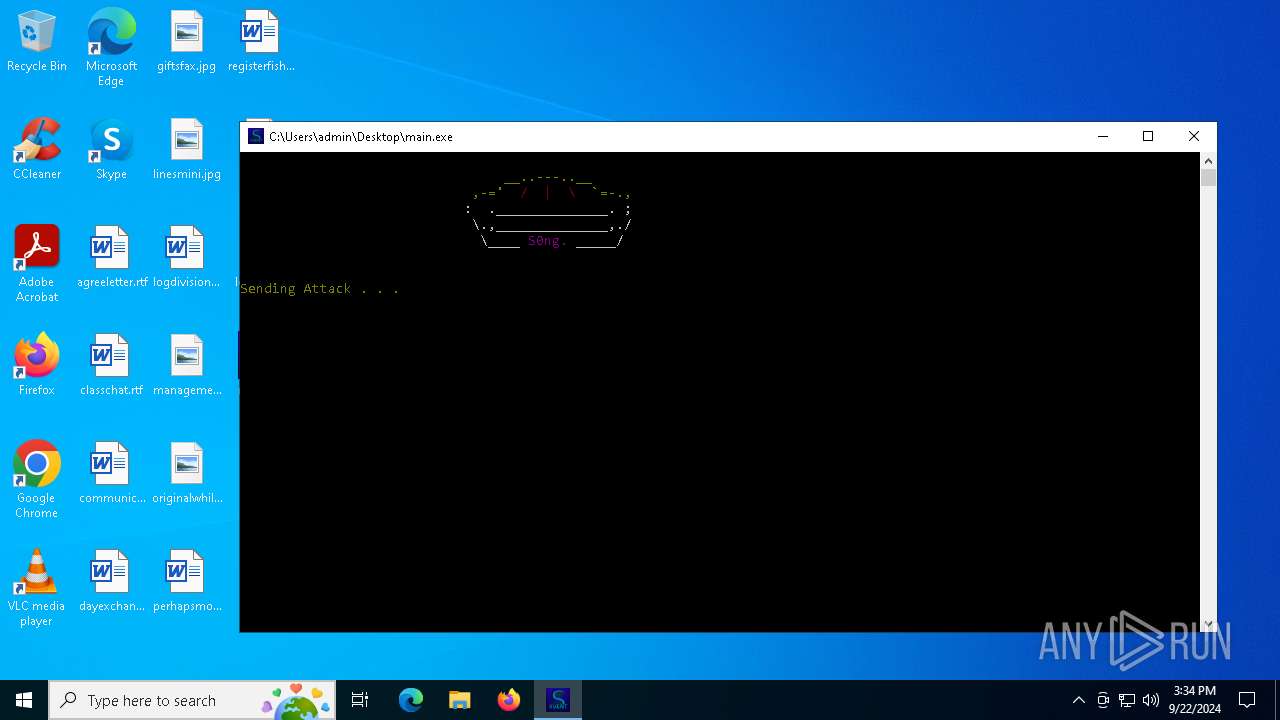
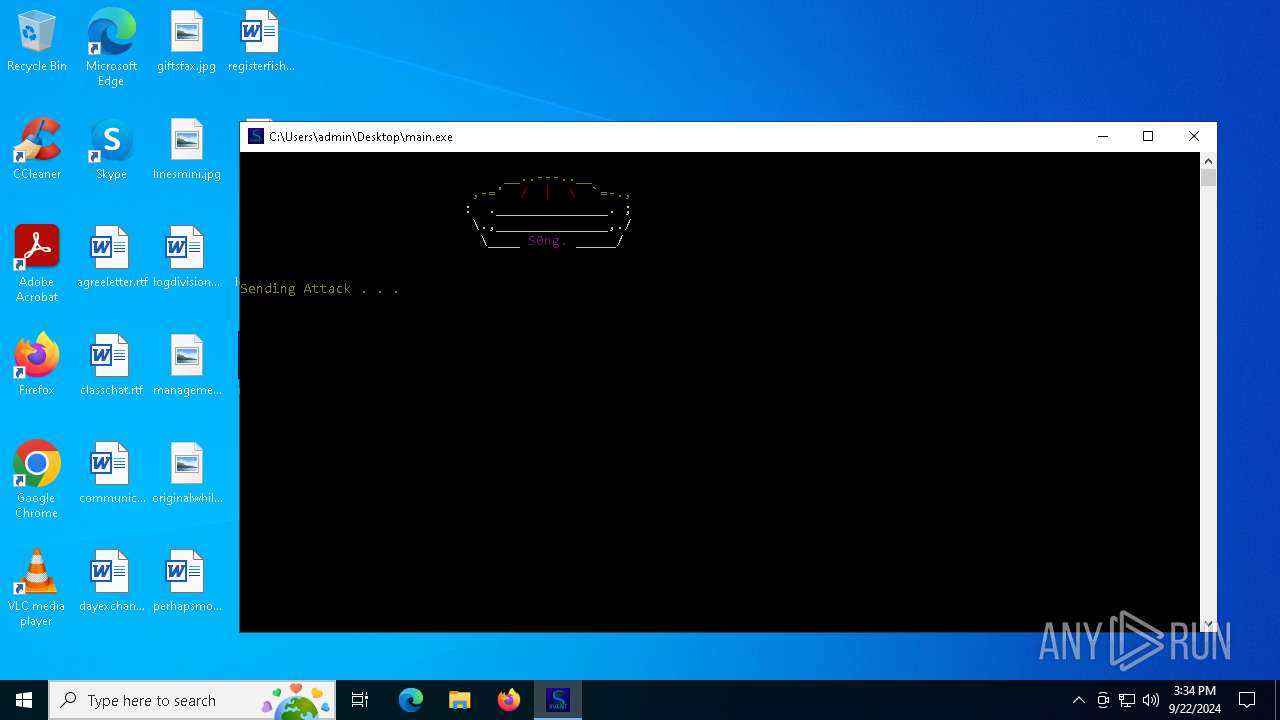
Starts CMD.EXE for commands execution
- loader.exe (PID: 2648)
- main.exe (PID: 7052)
- main.exe (PID: 66212)
- loader.exe (PID: 66100)
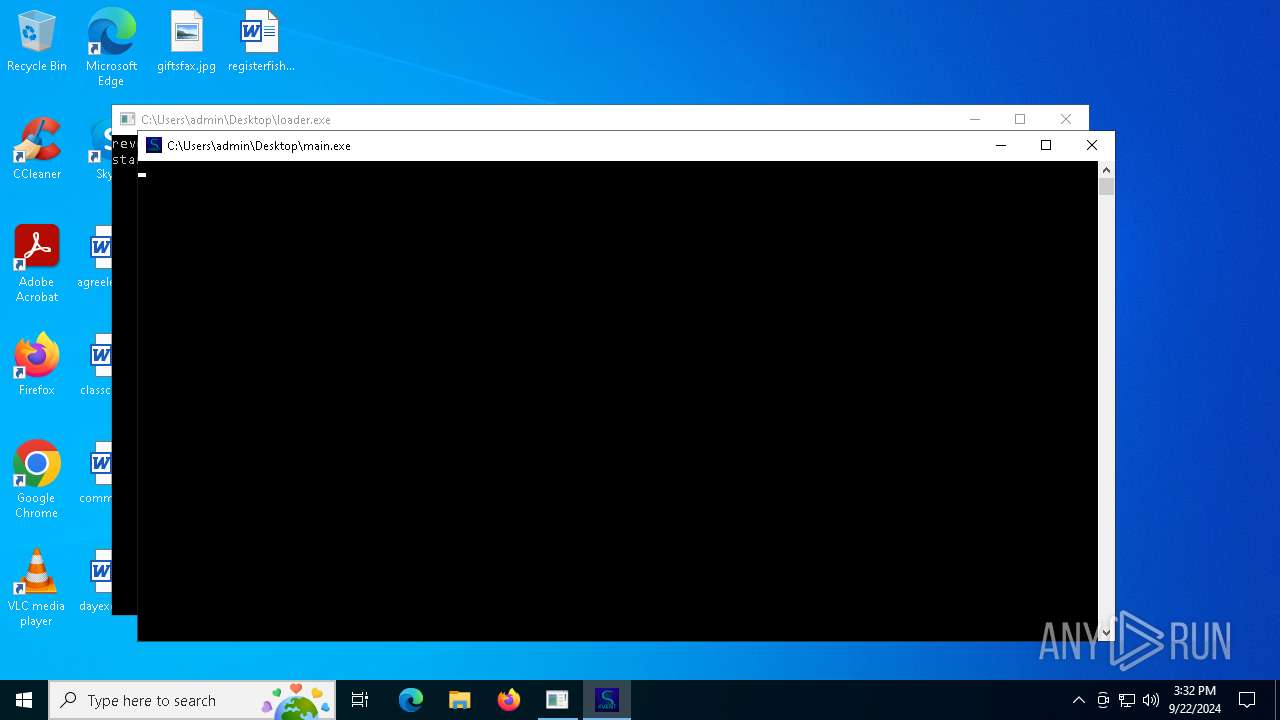
Application launched itself
- main.exe (PID: 360)
- main.exe (PID: 66144)
Reads security settings of Internet Explorer
- loader.exe (PID: 5000)
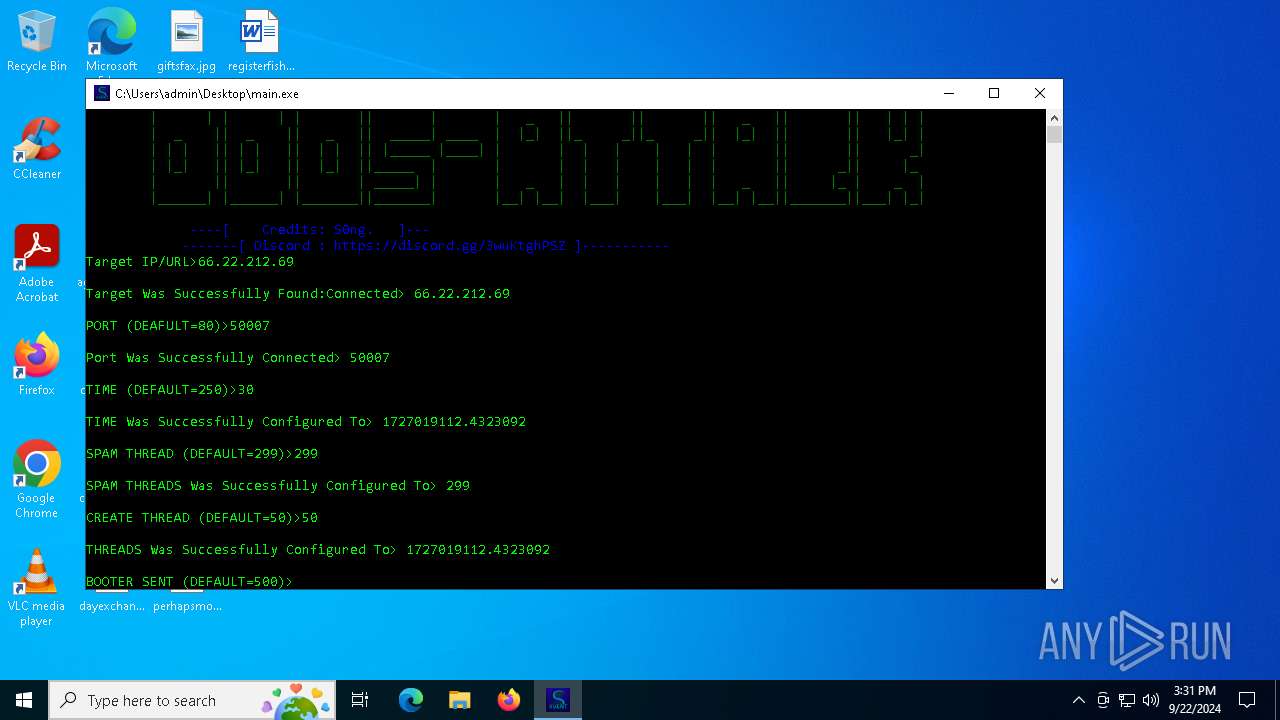
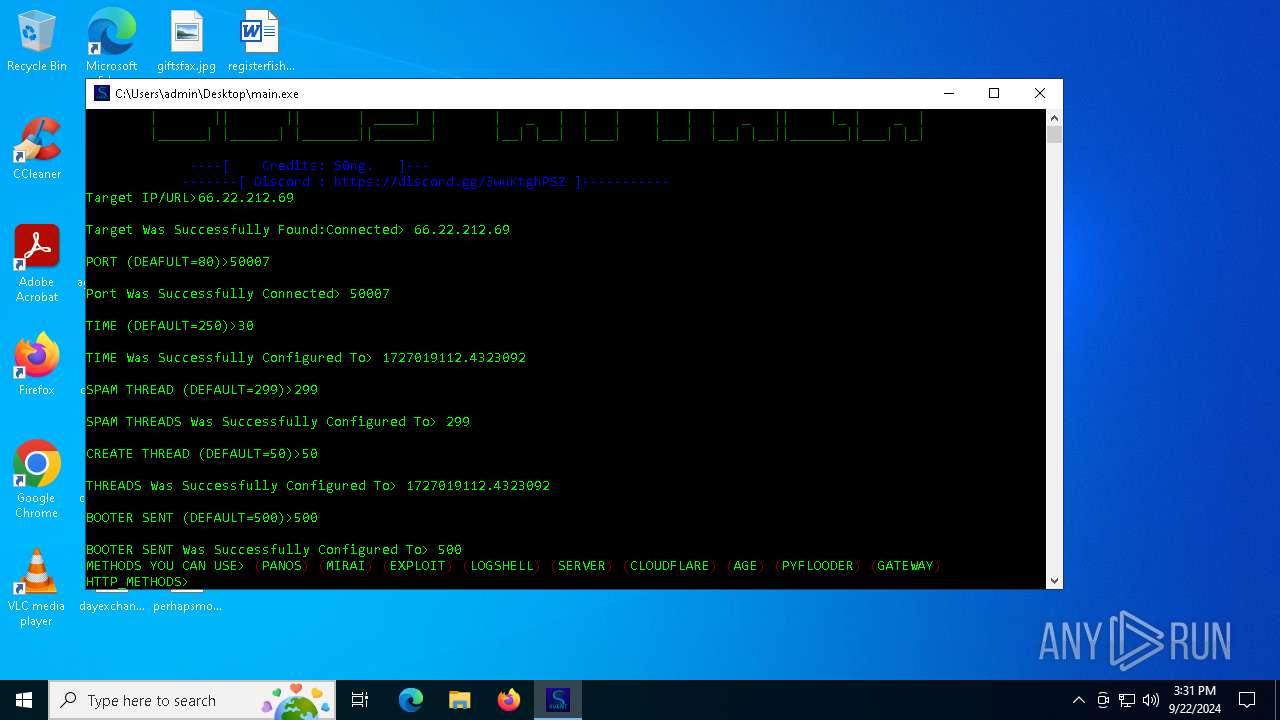
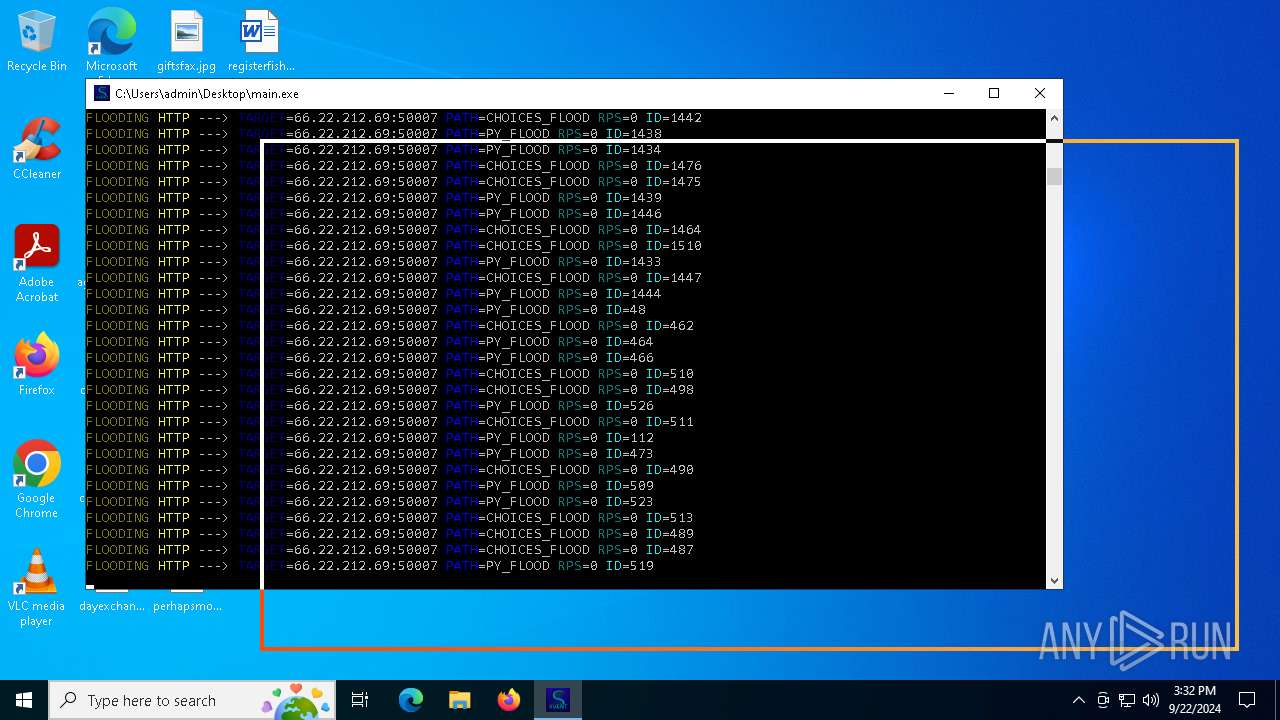
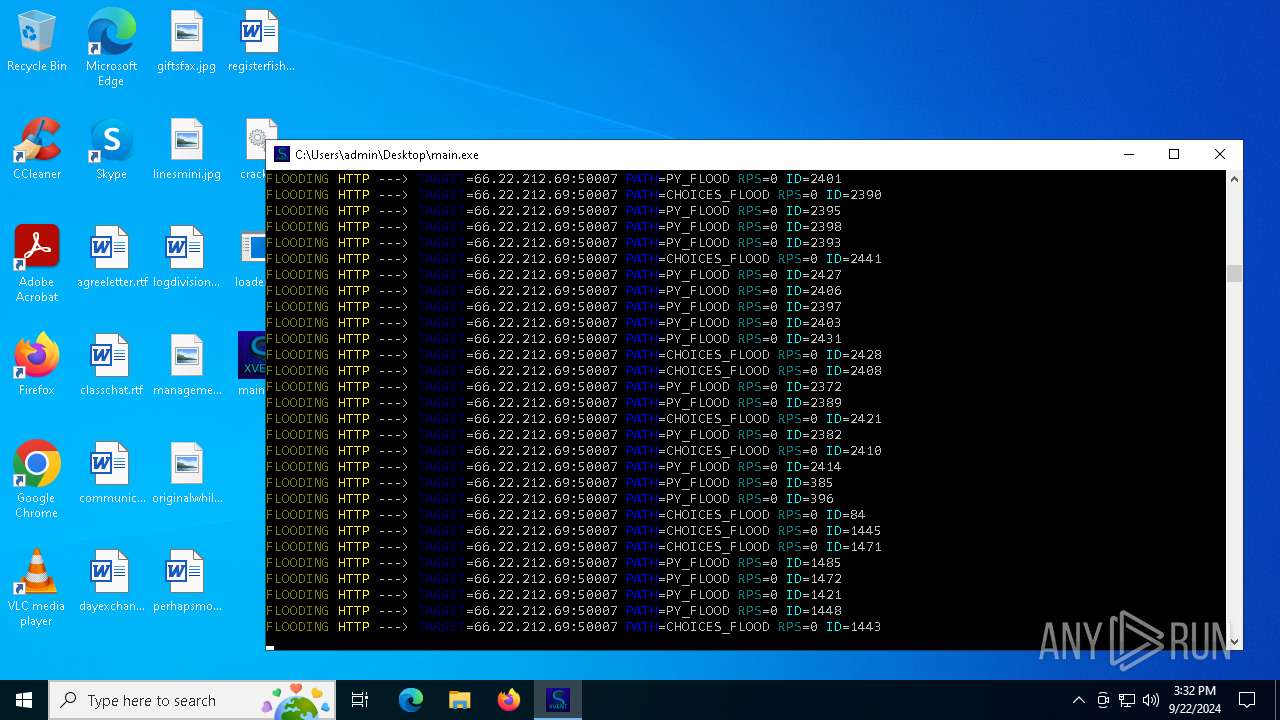
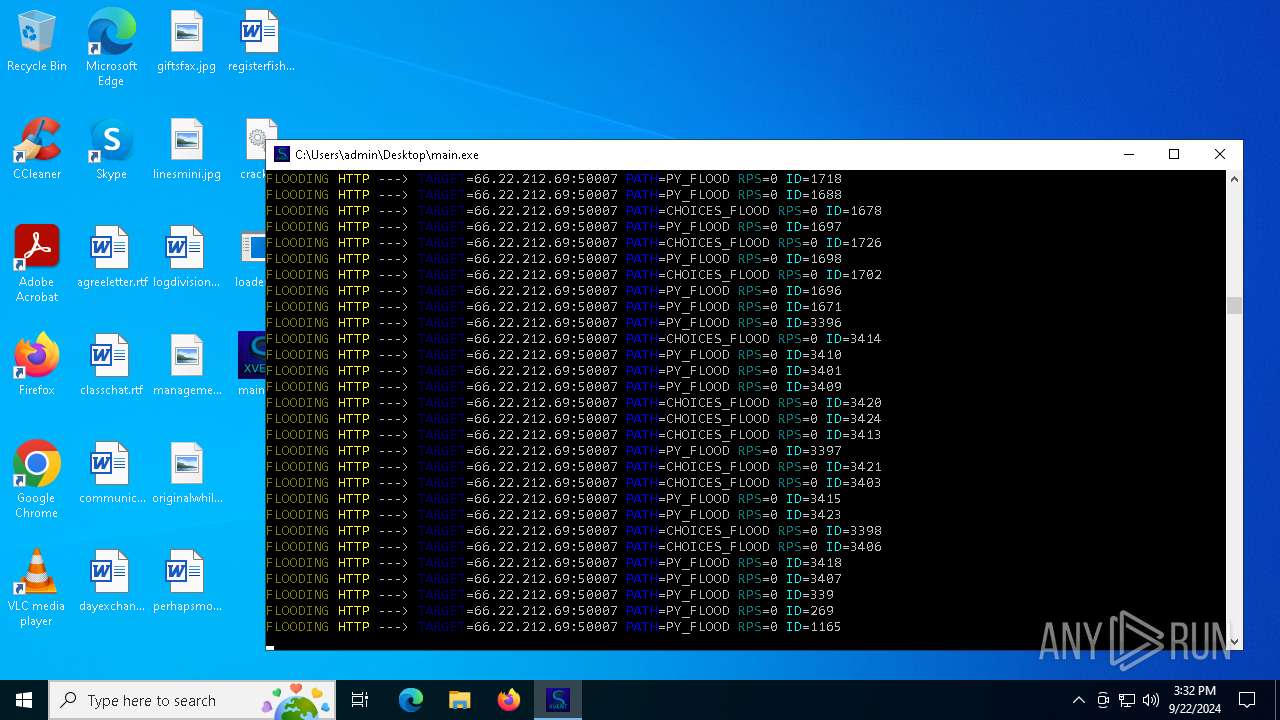
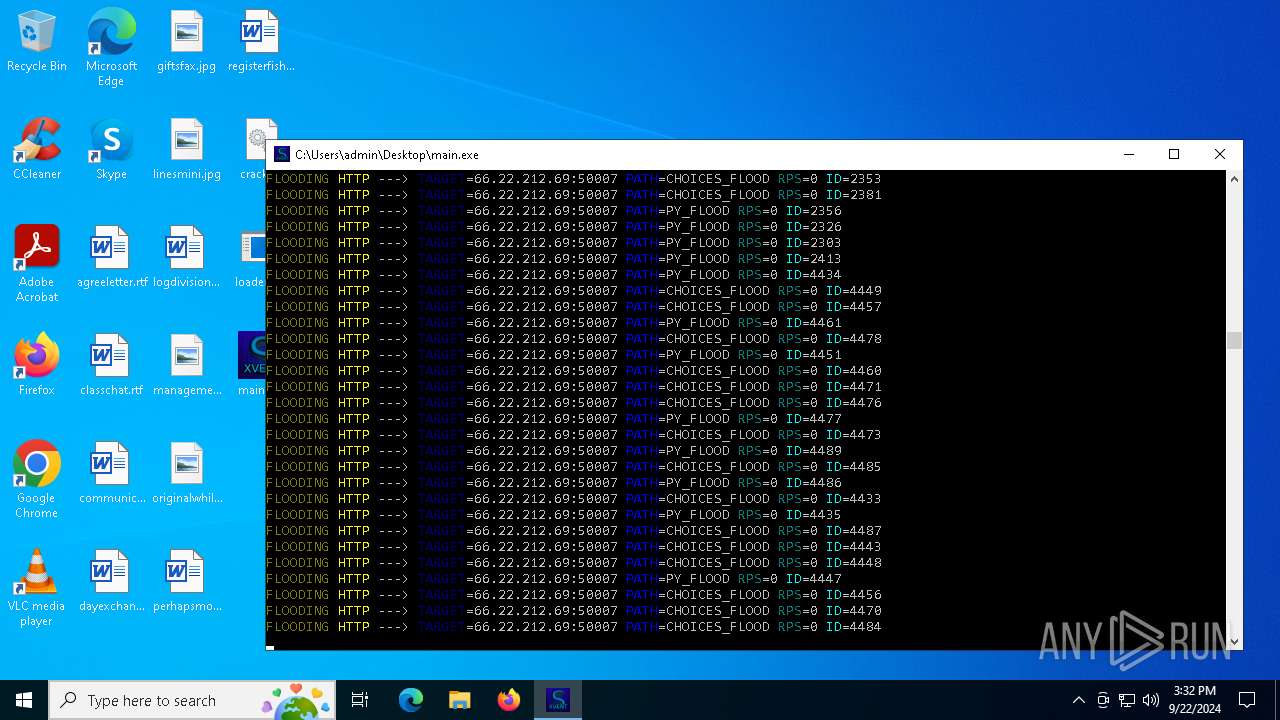
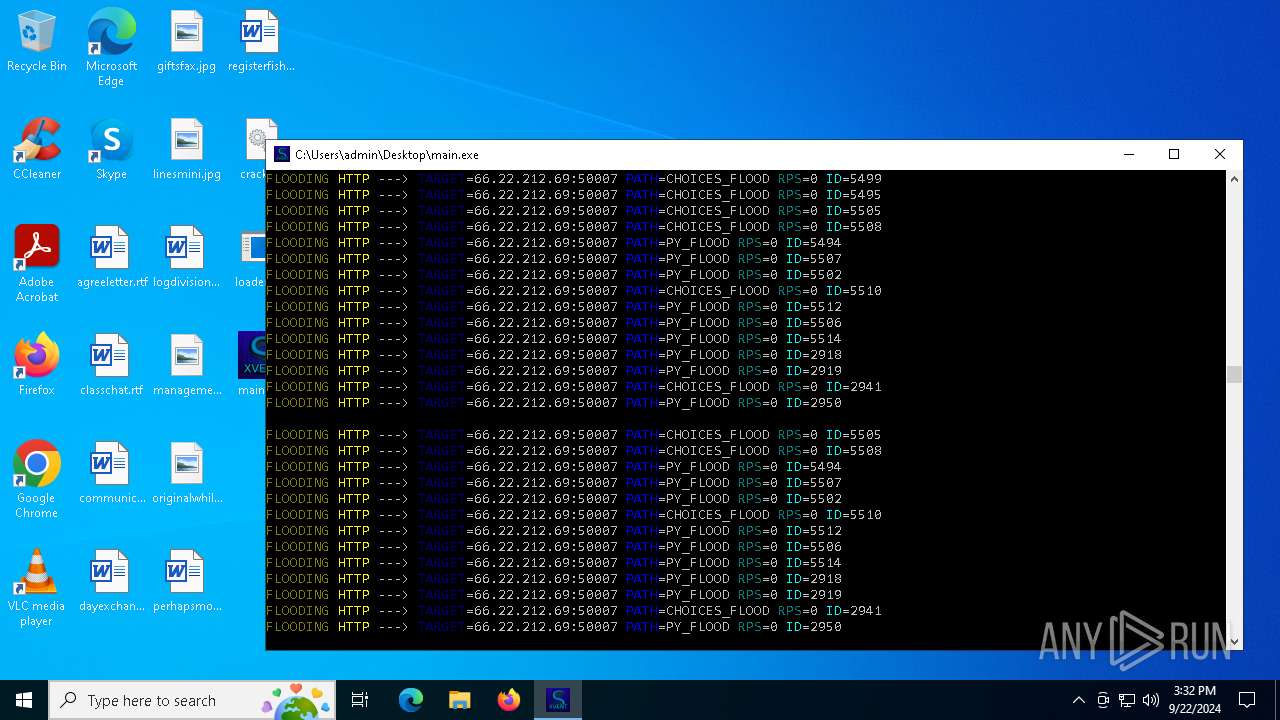
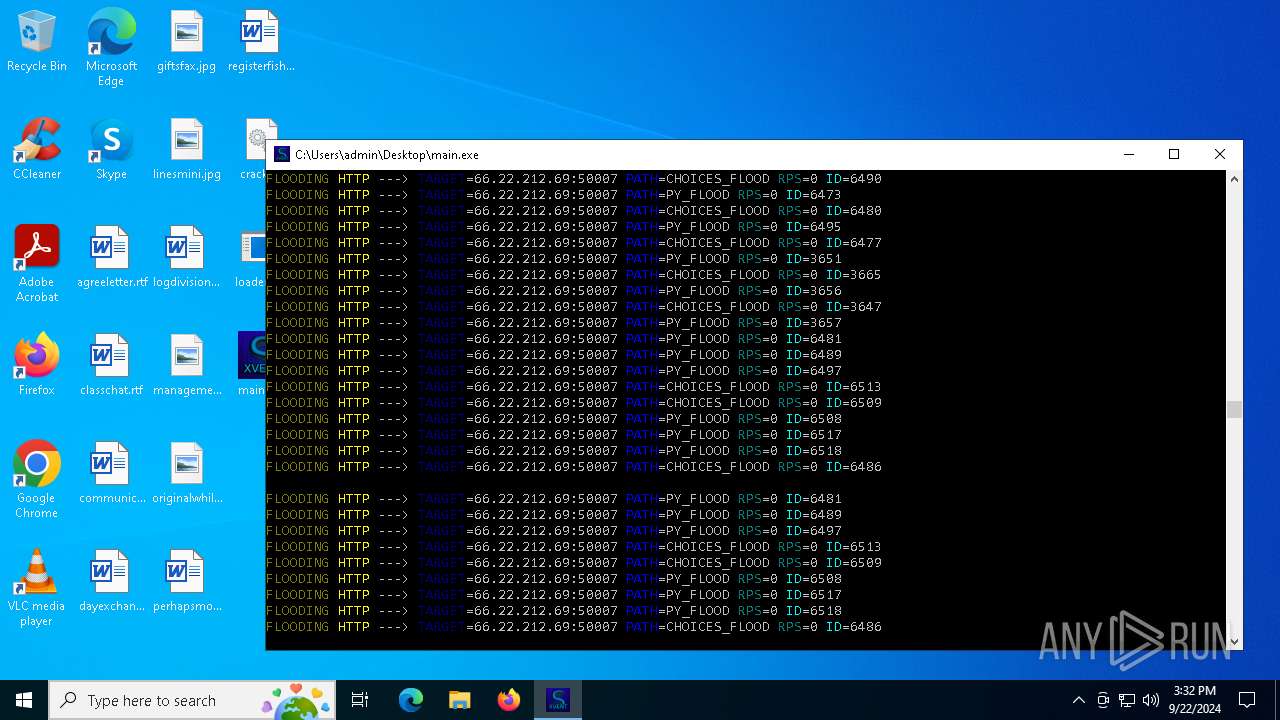
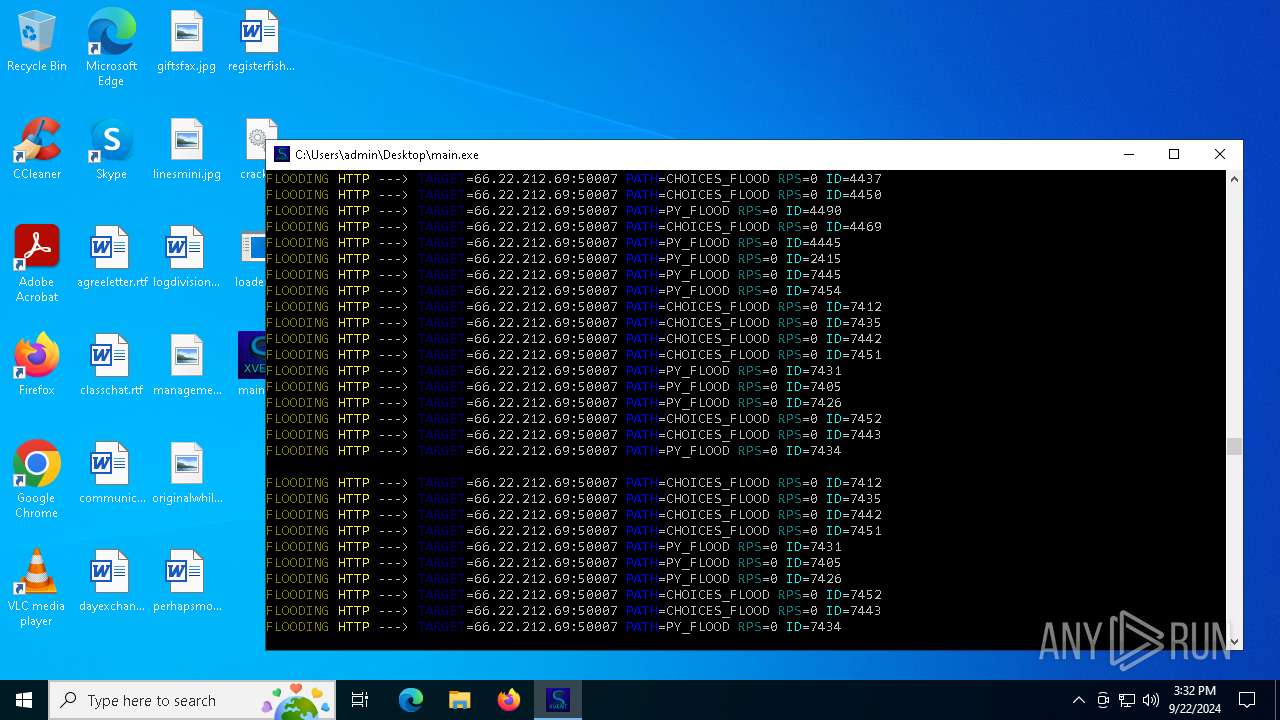
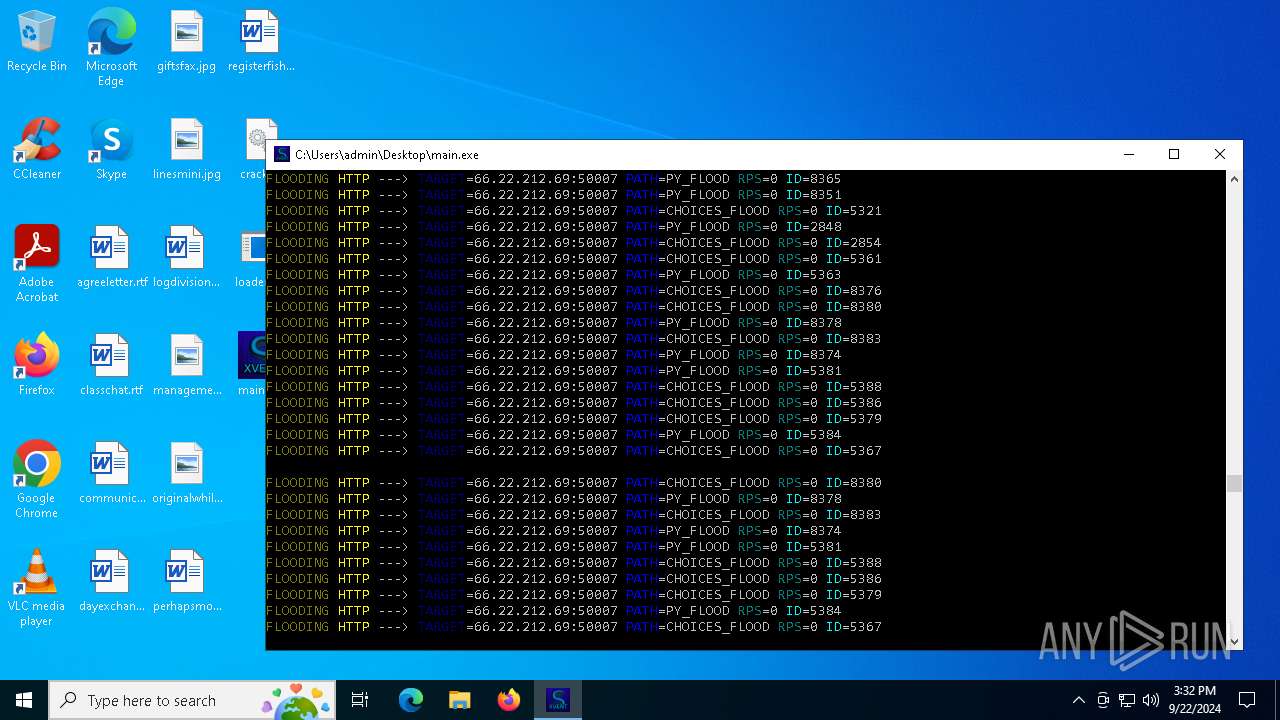
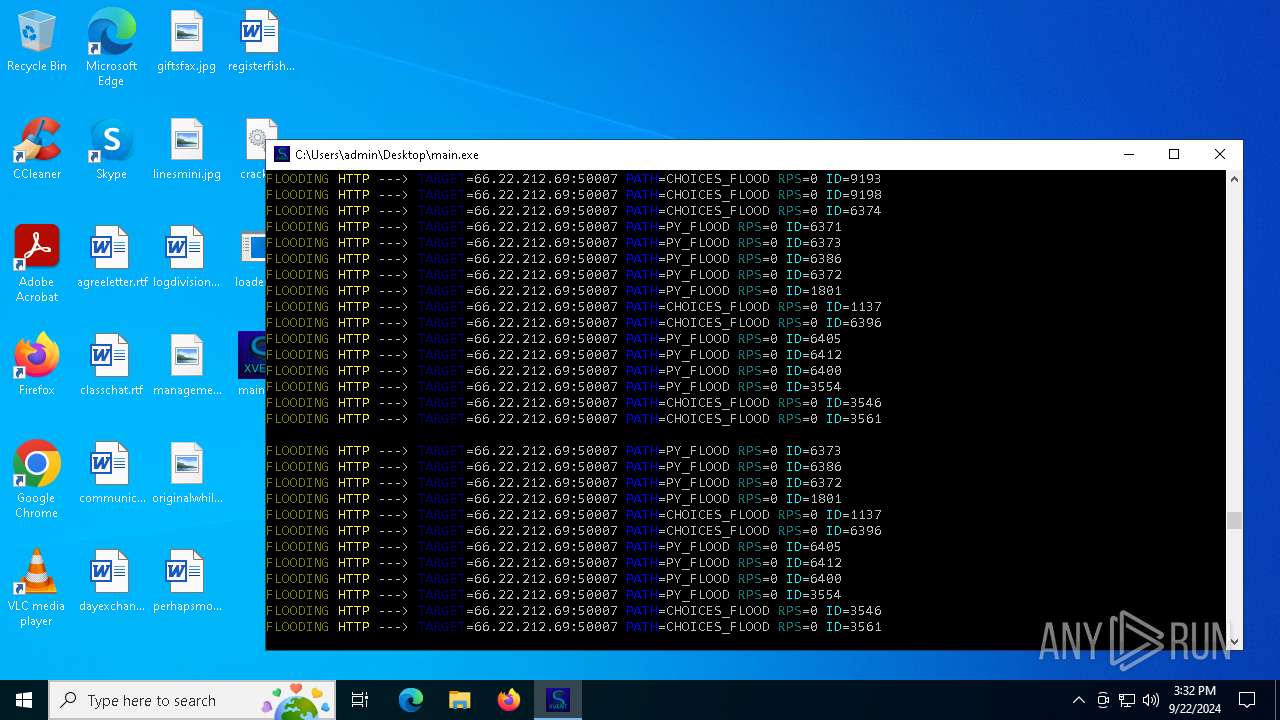
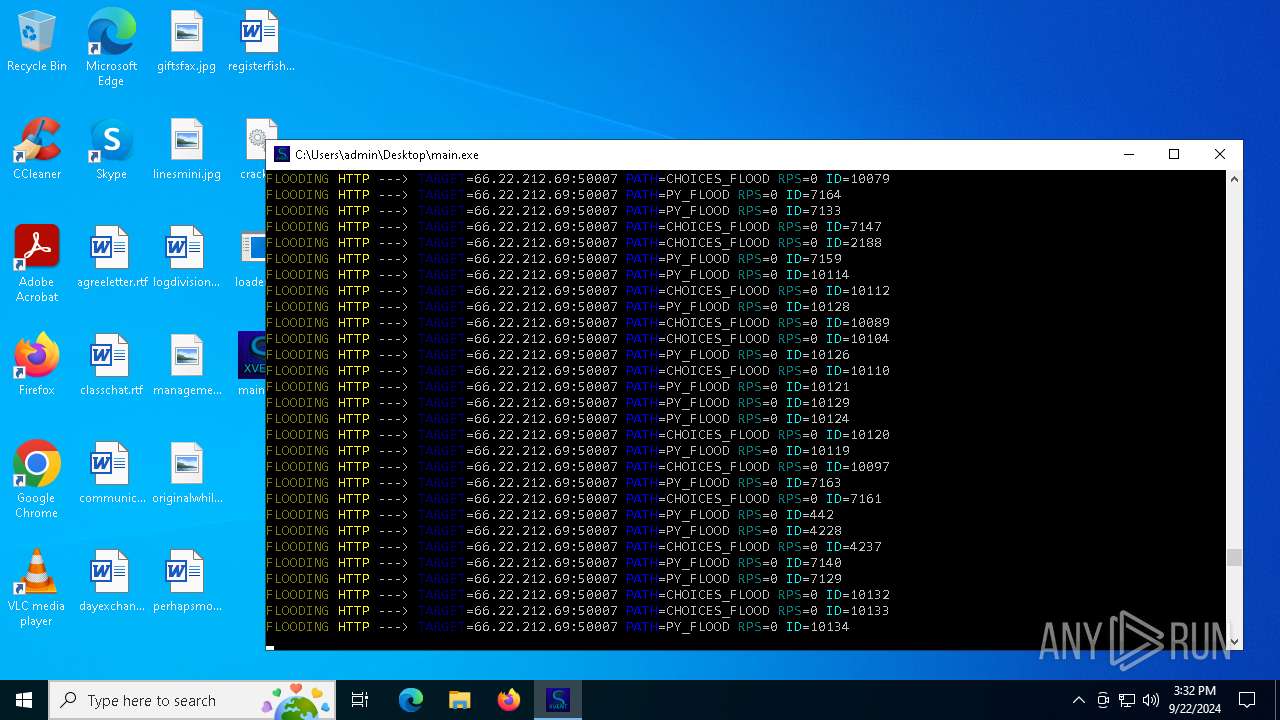
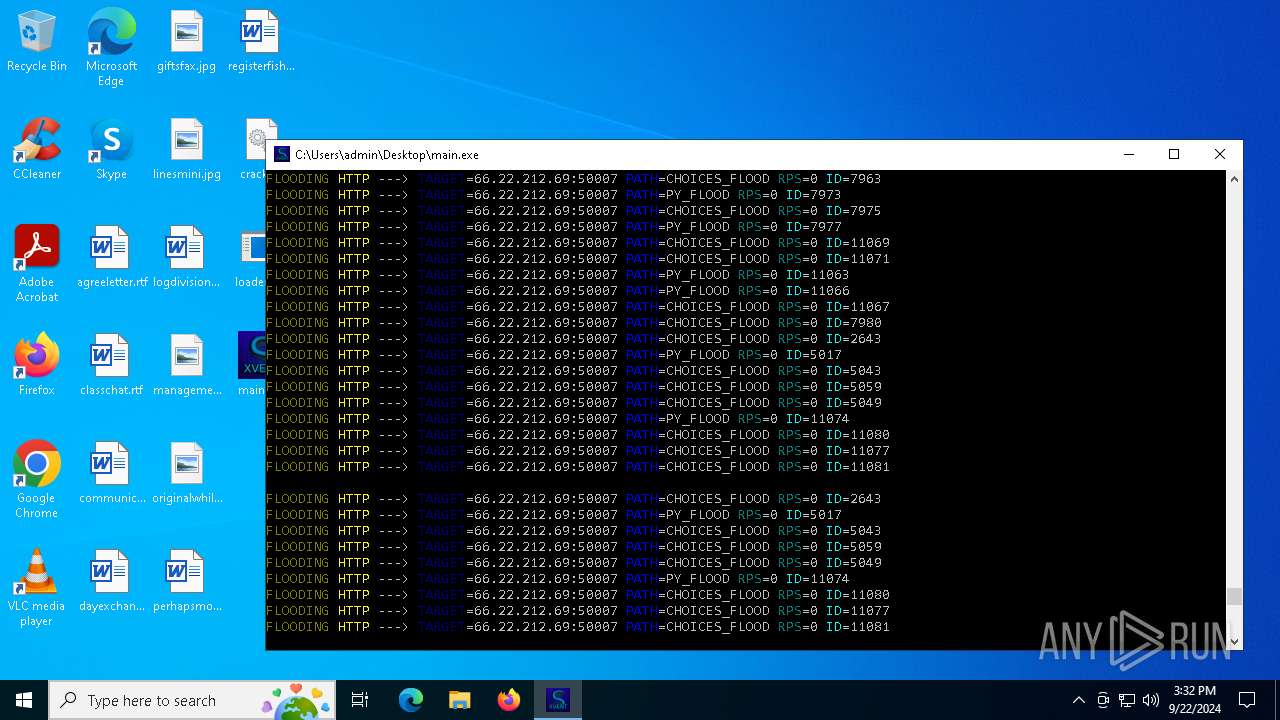
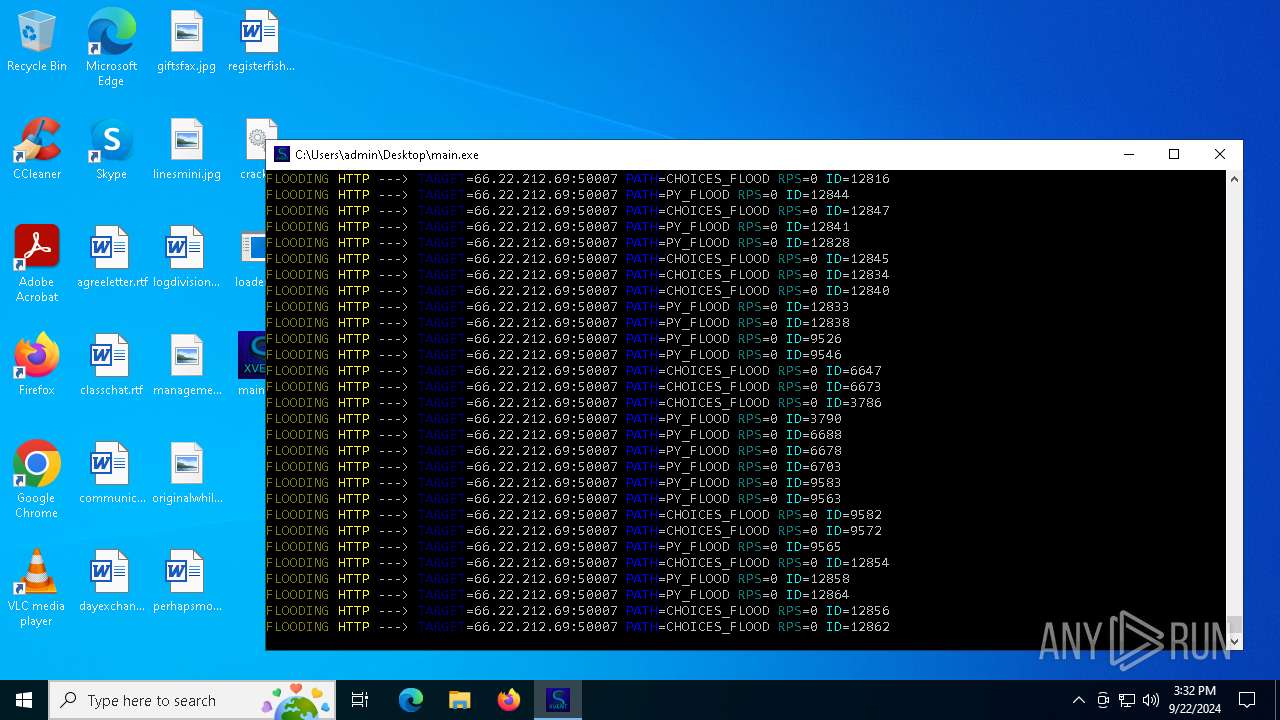
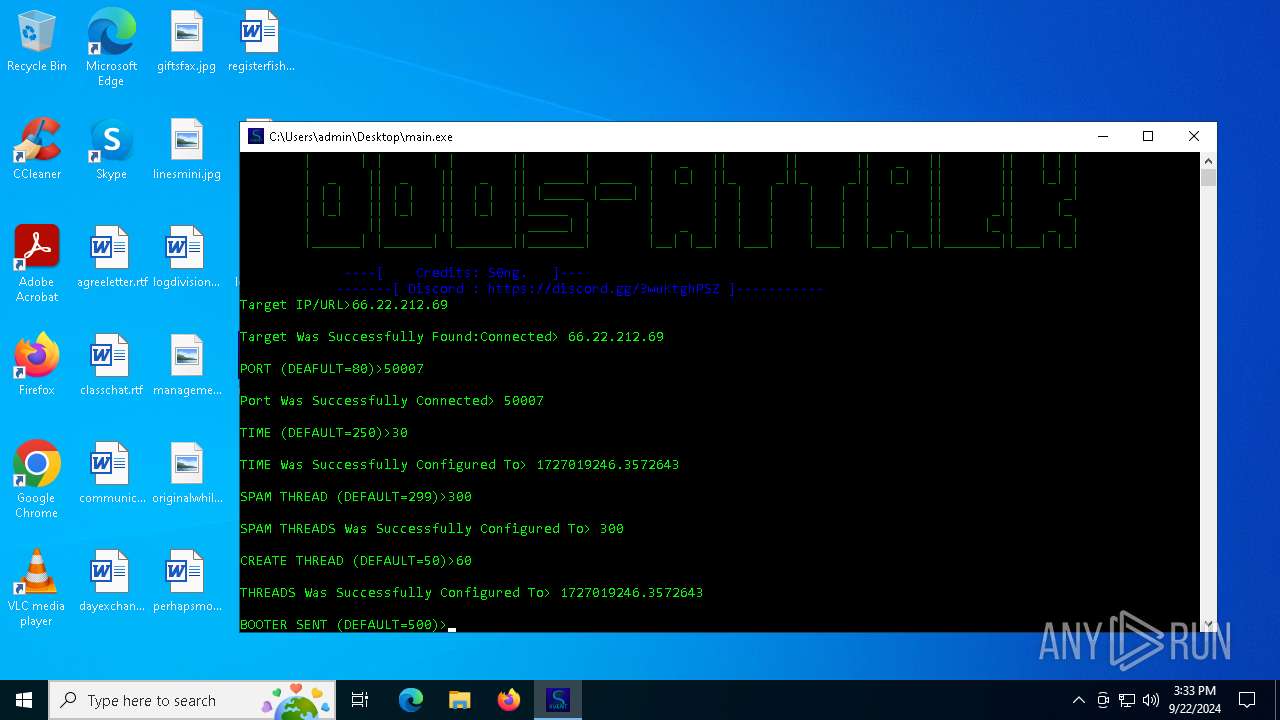
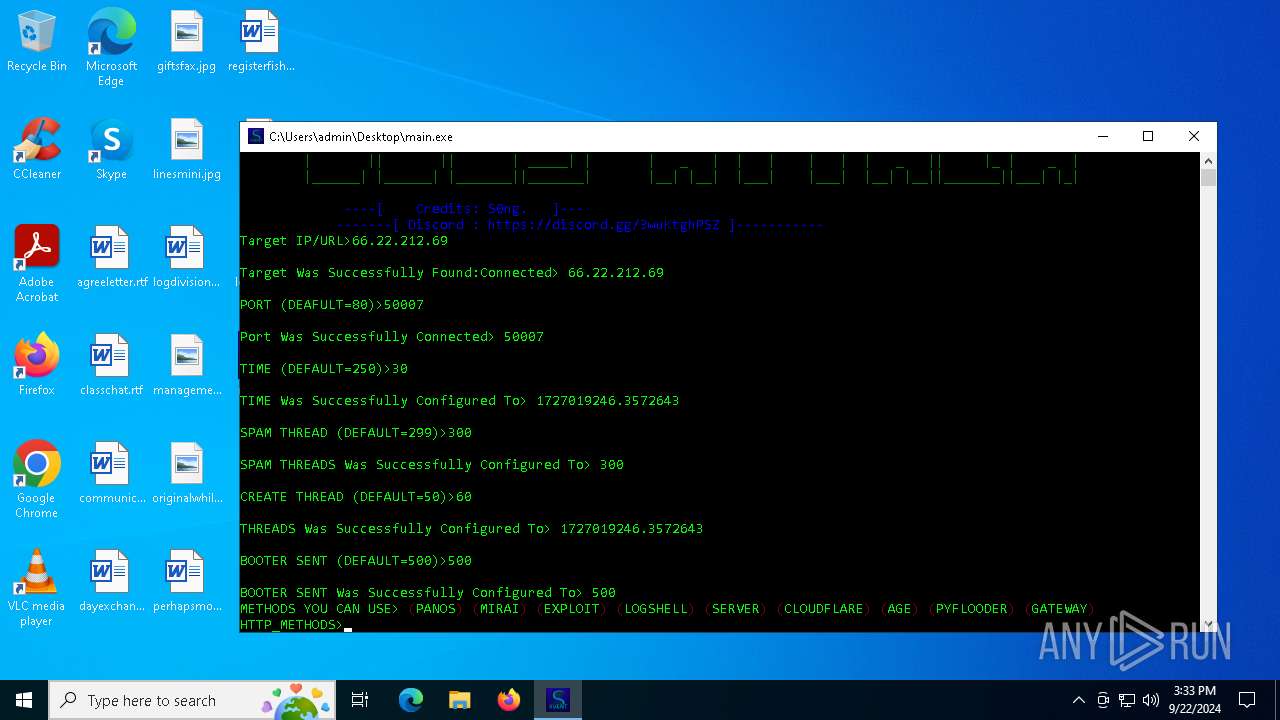
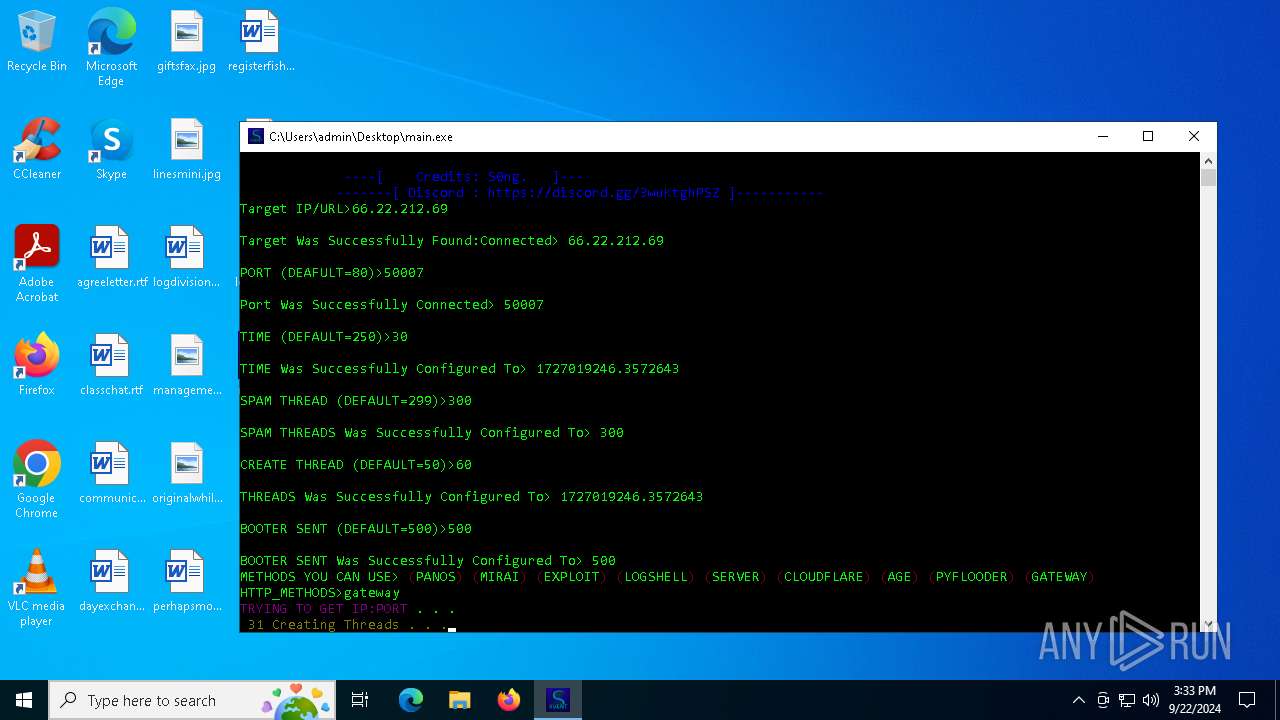
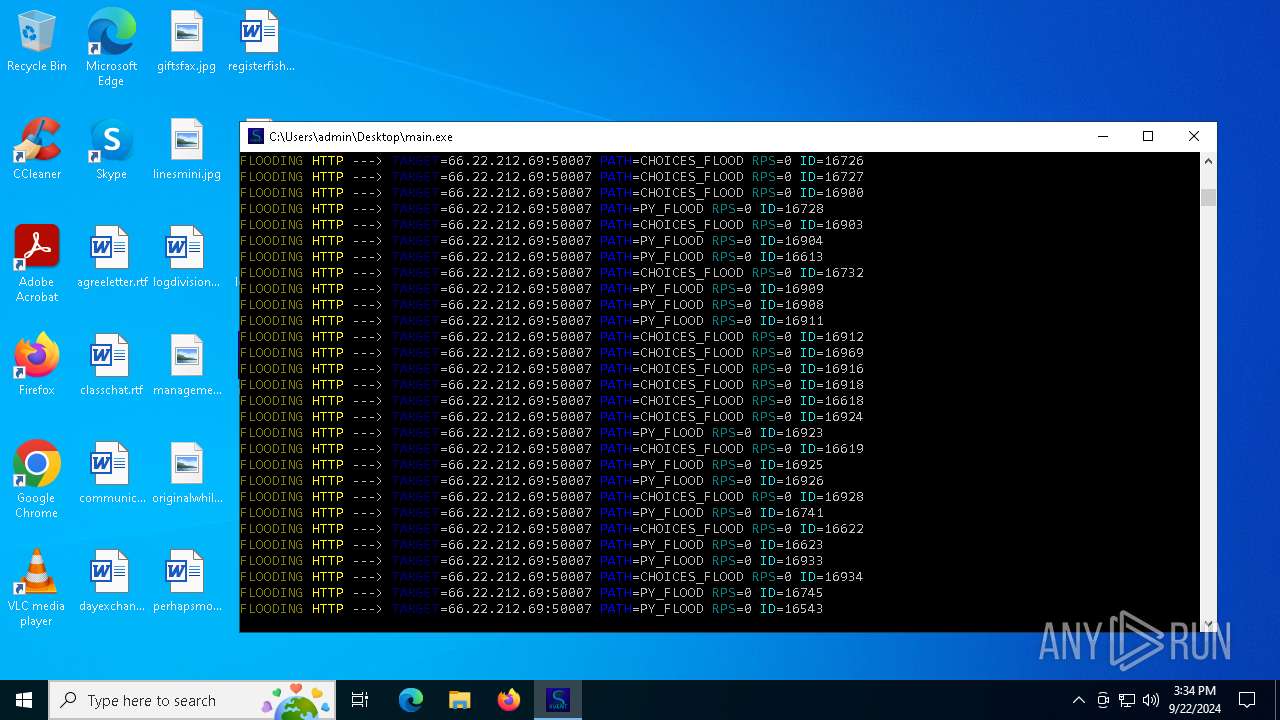
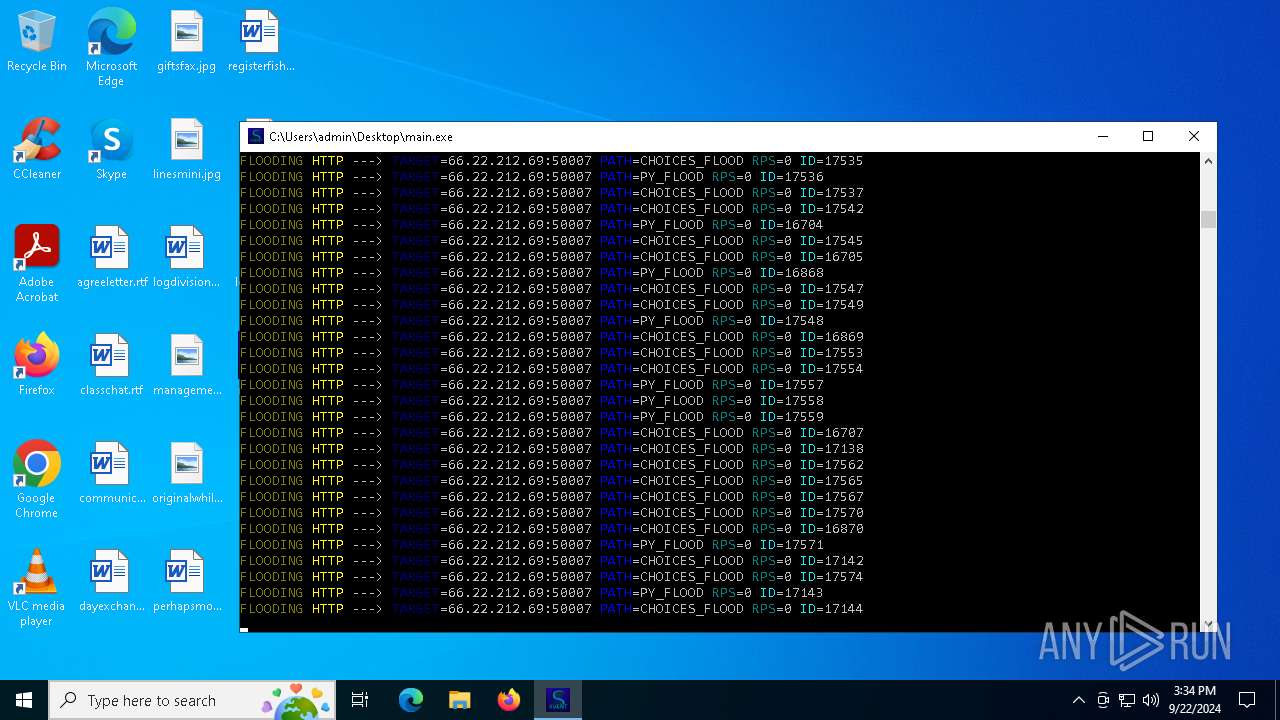
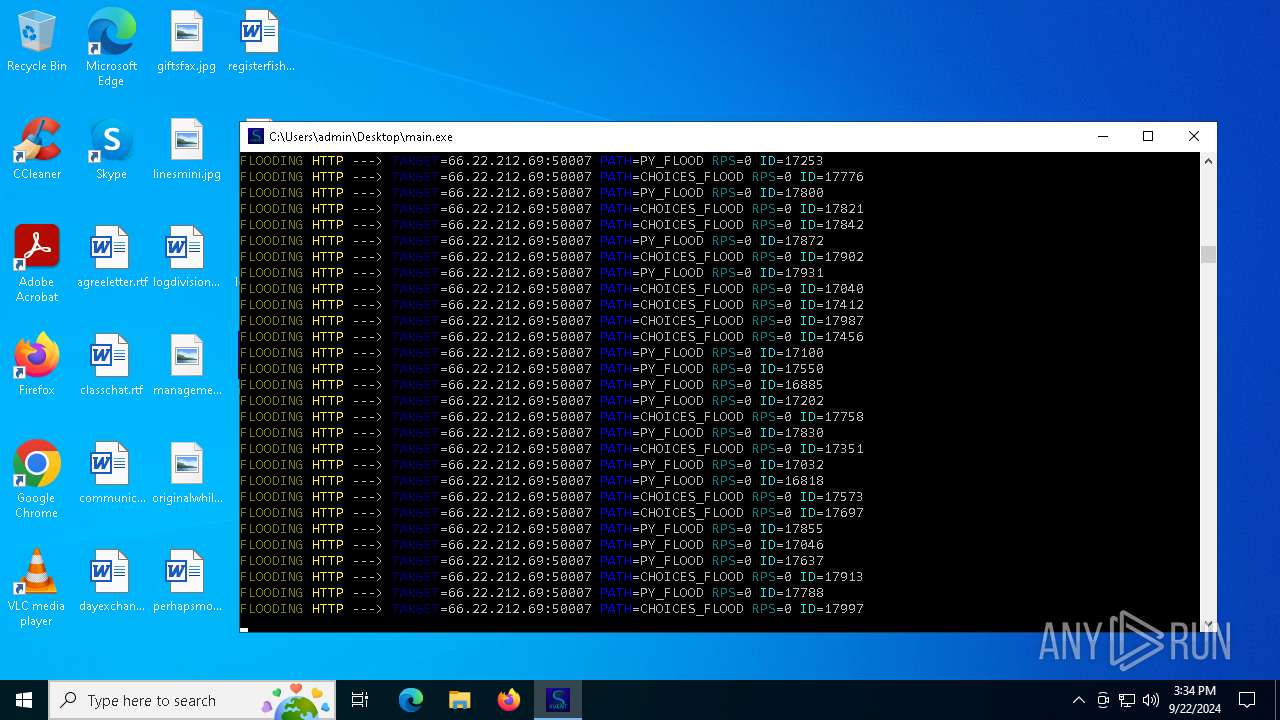
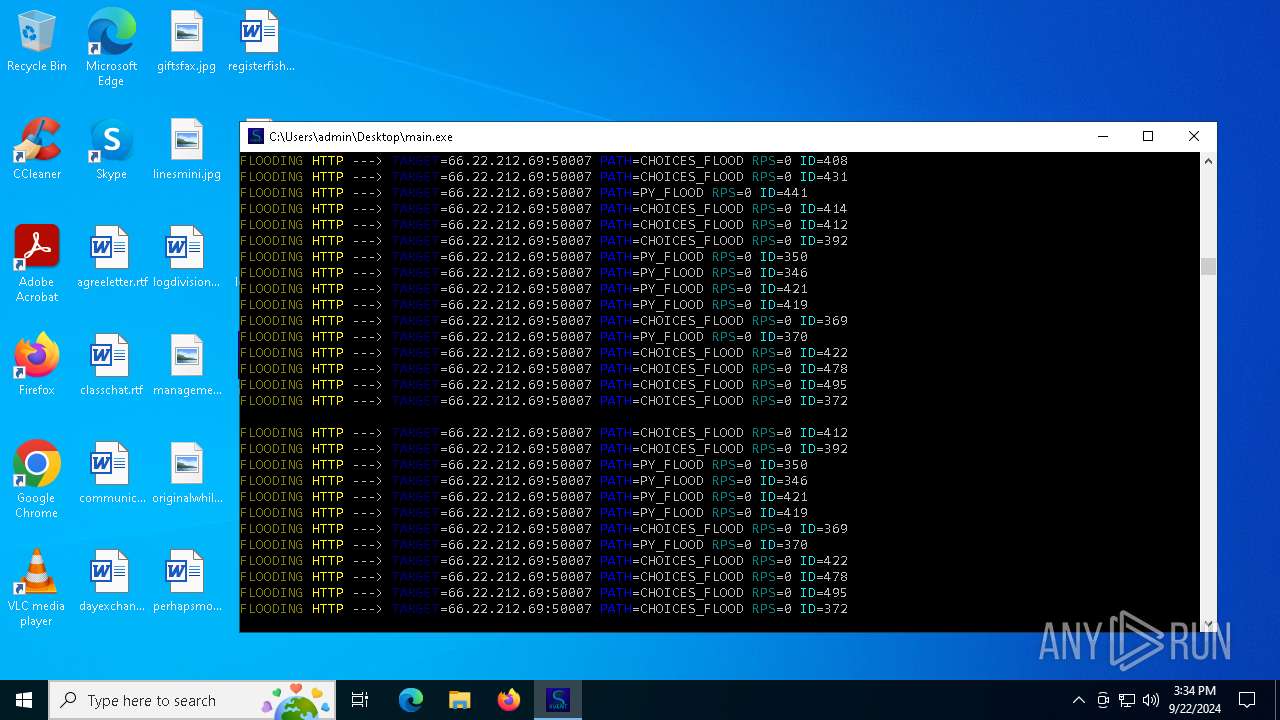
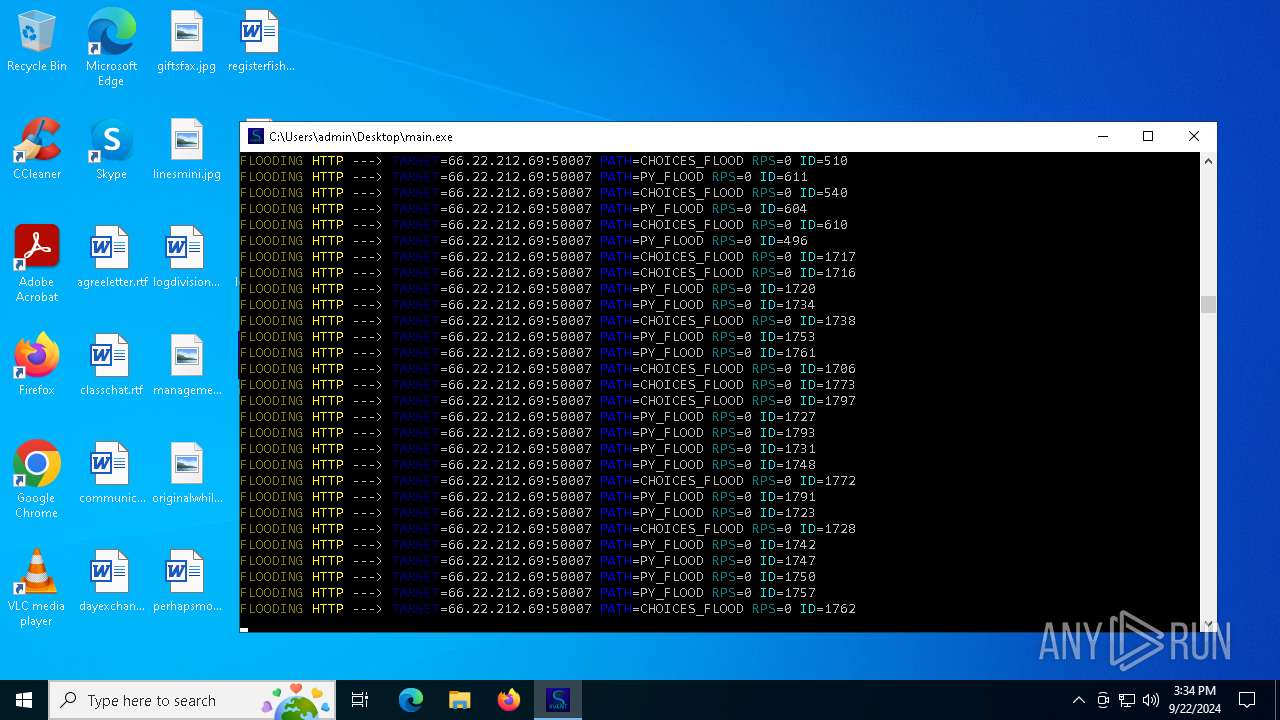
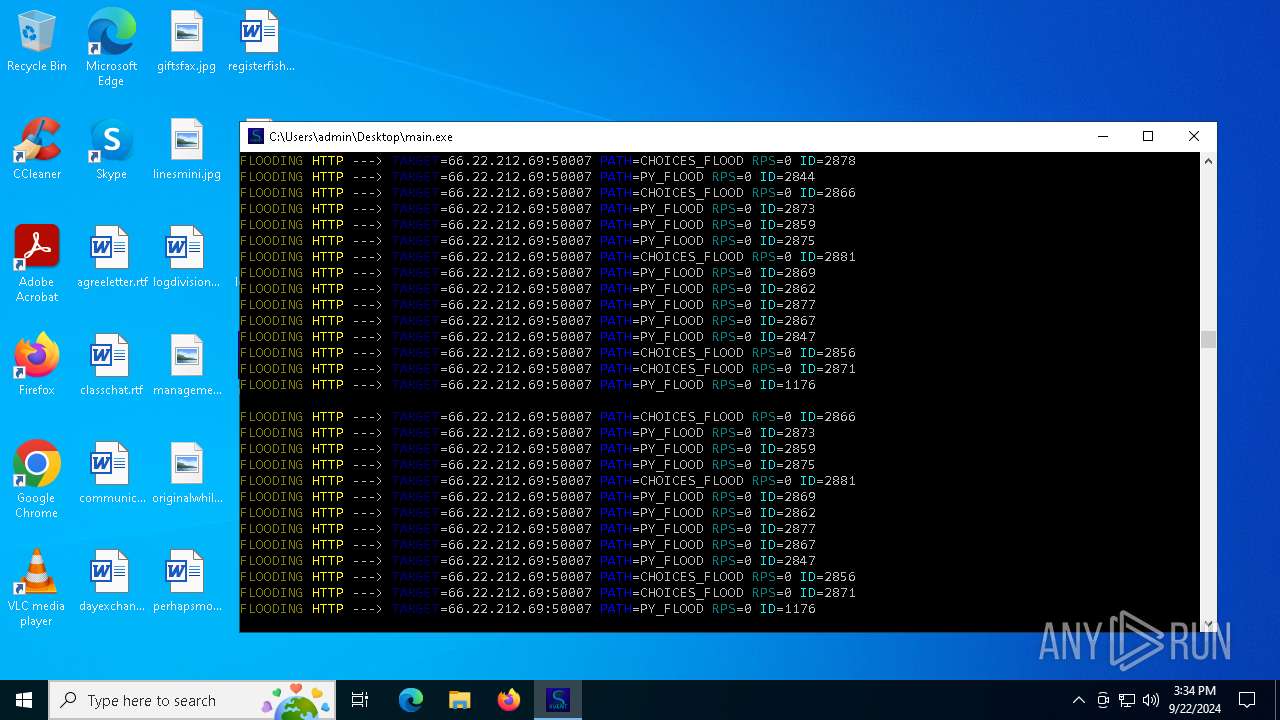
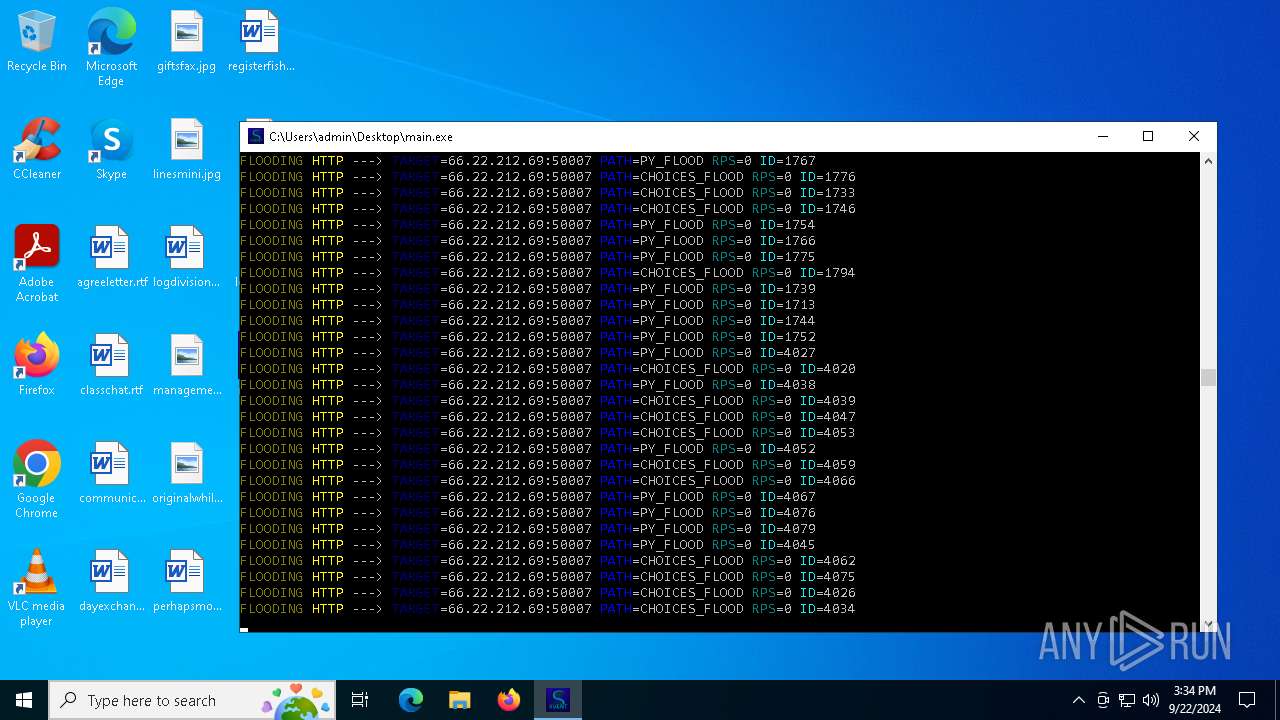
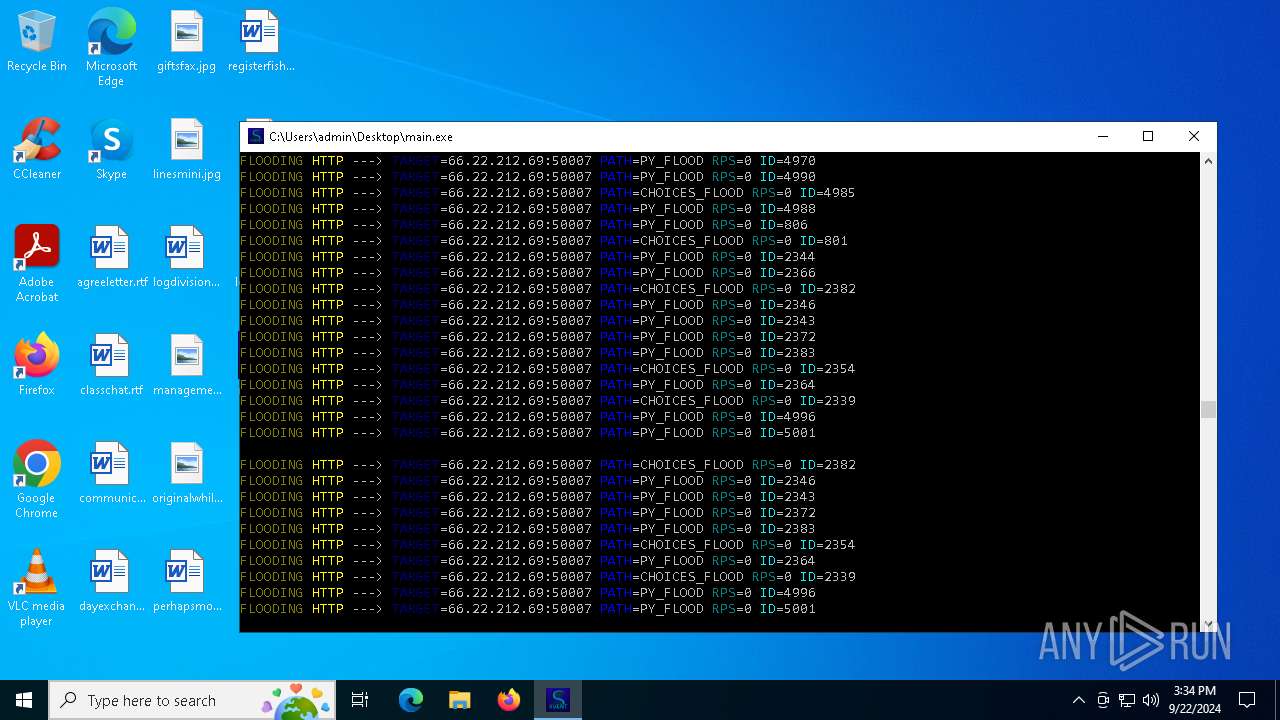
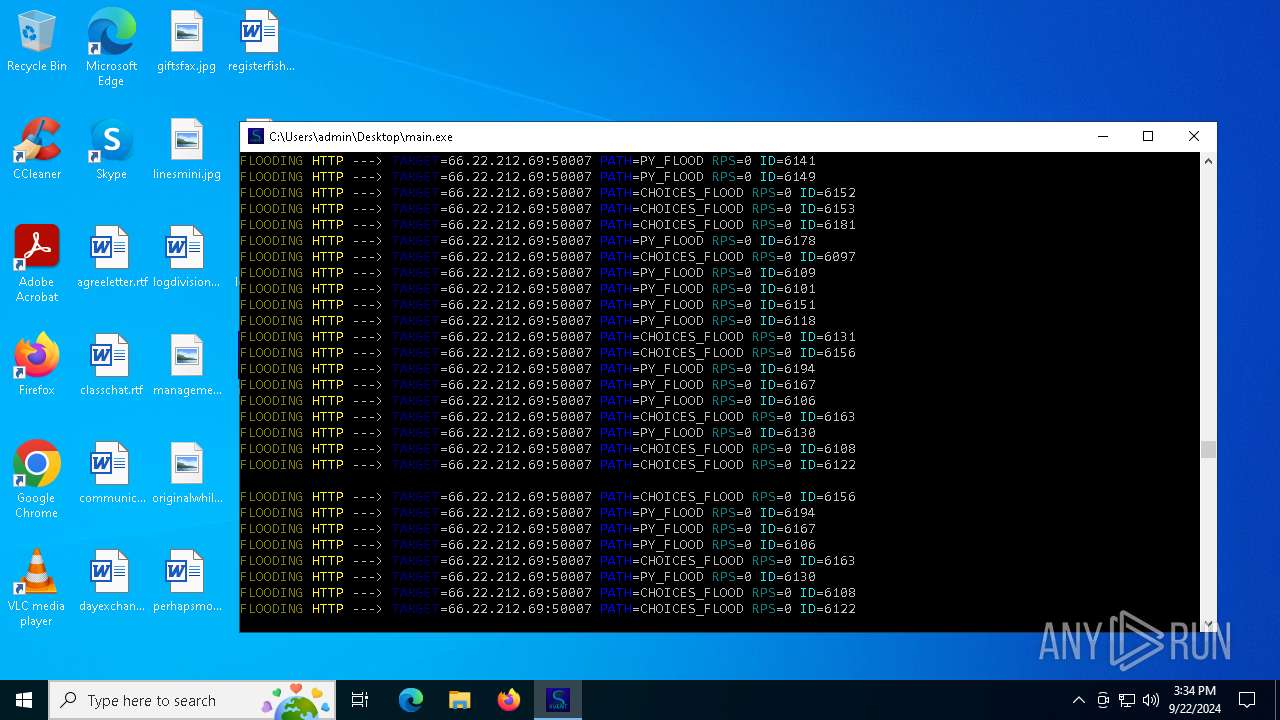
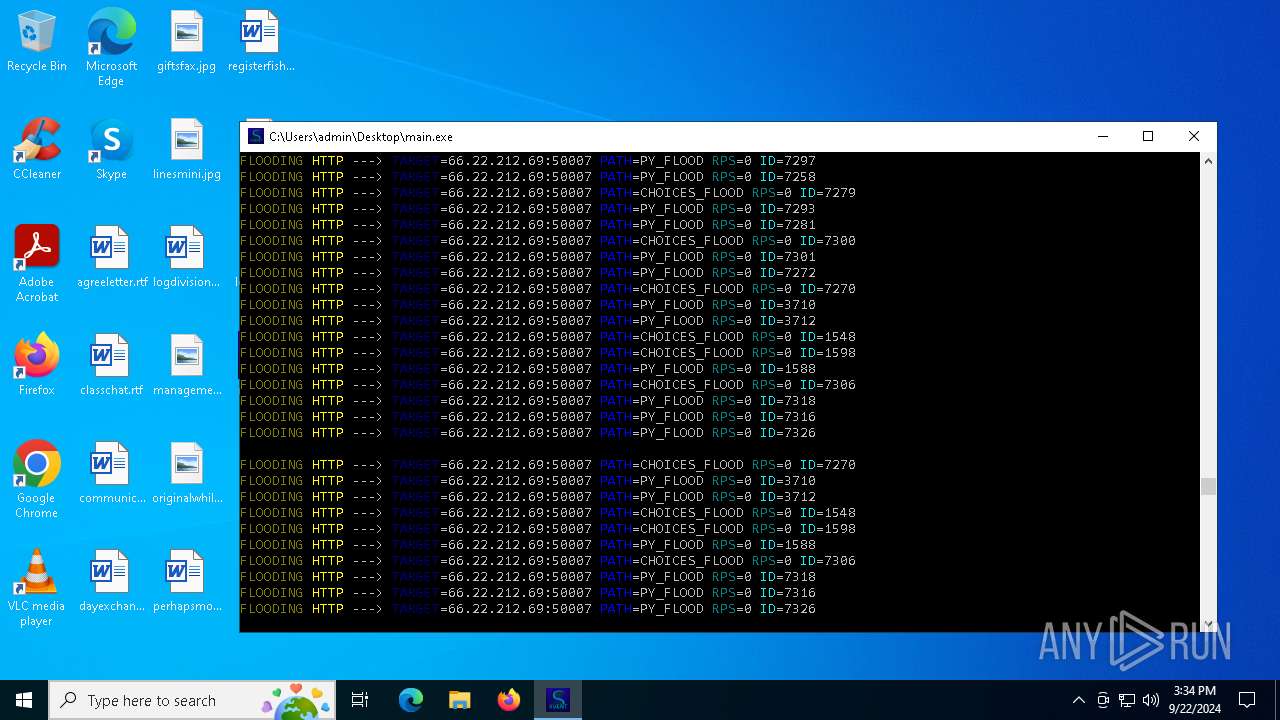
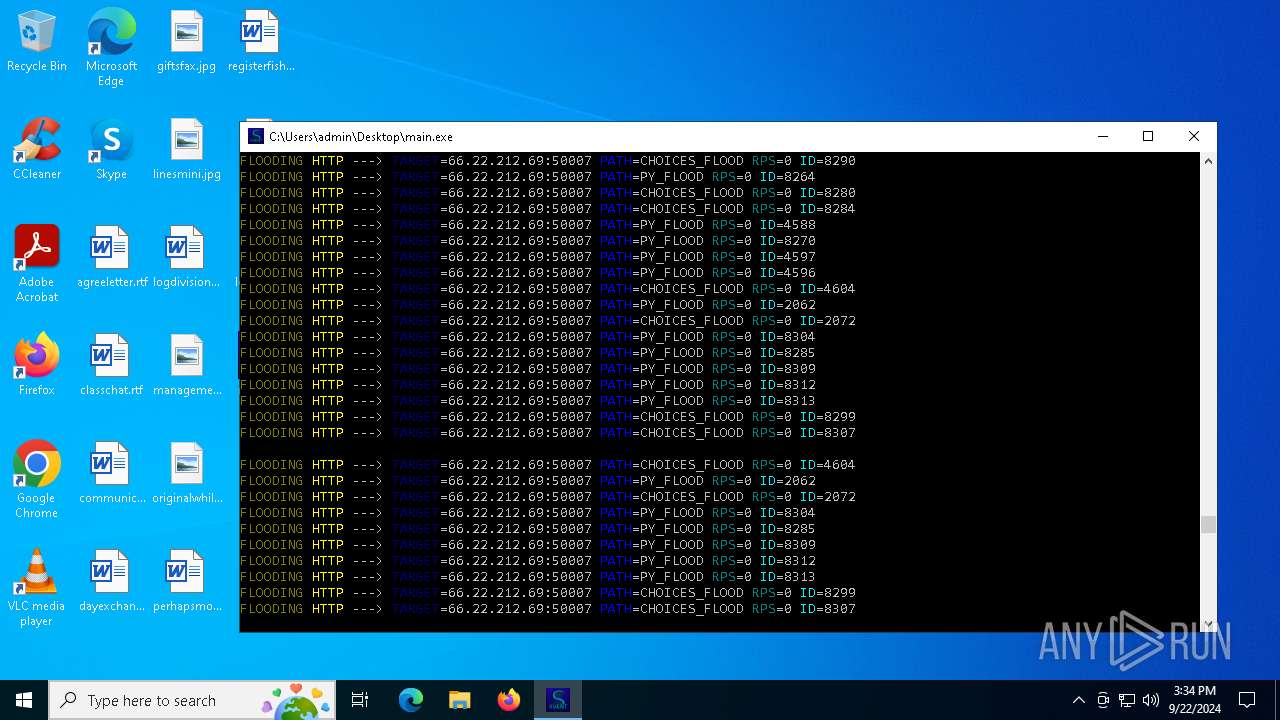
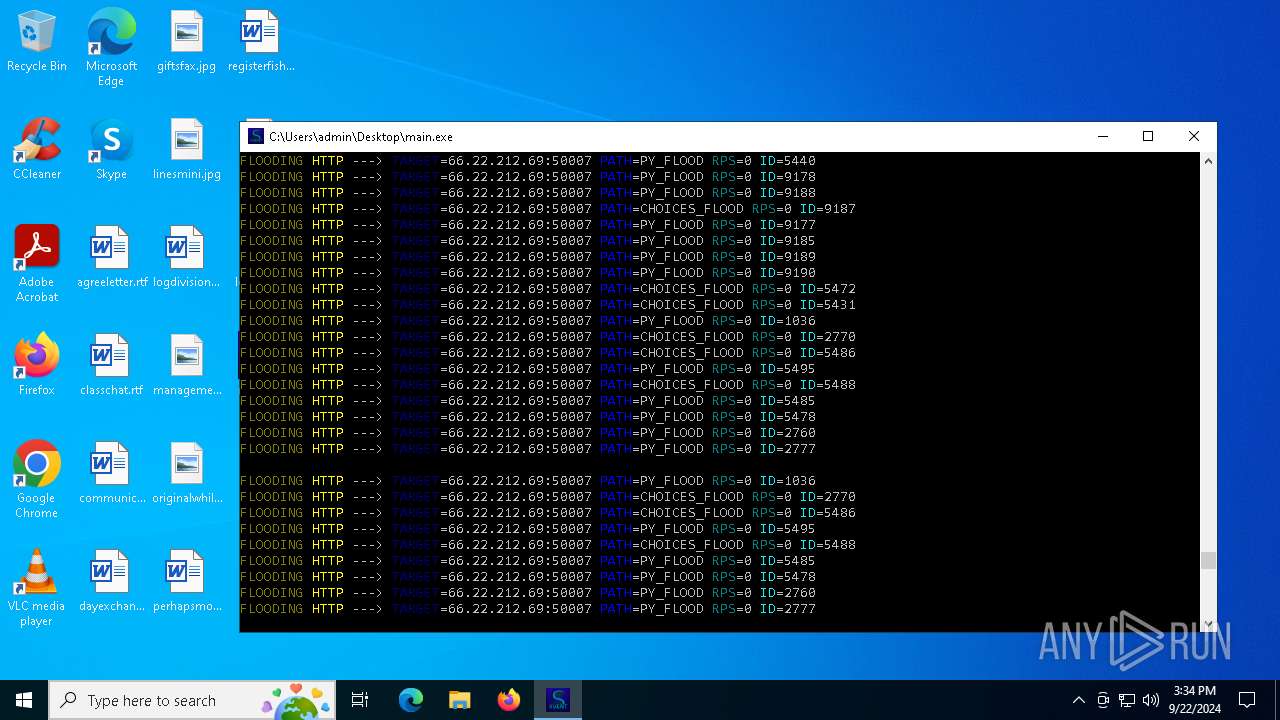
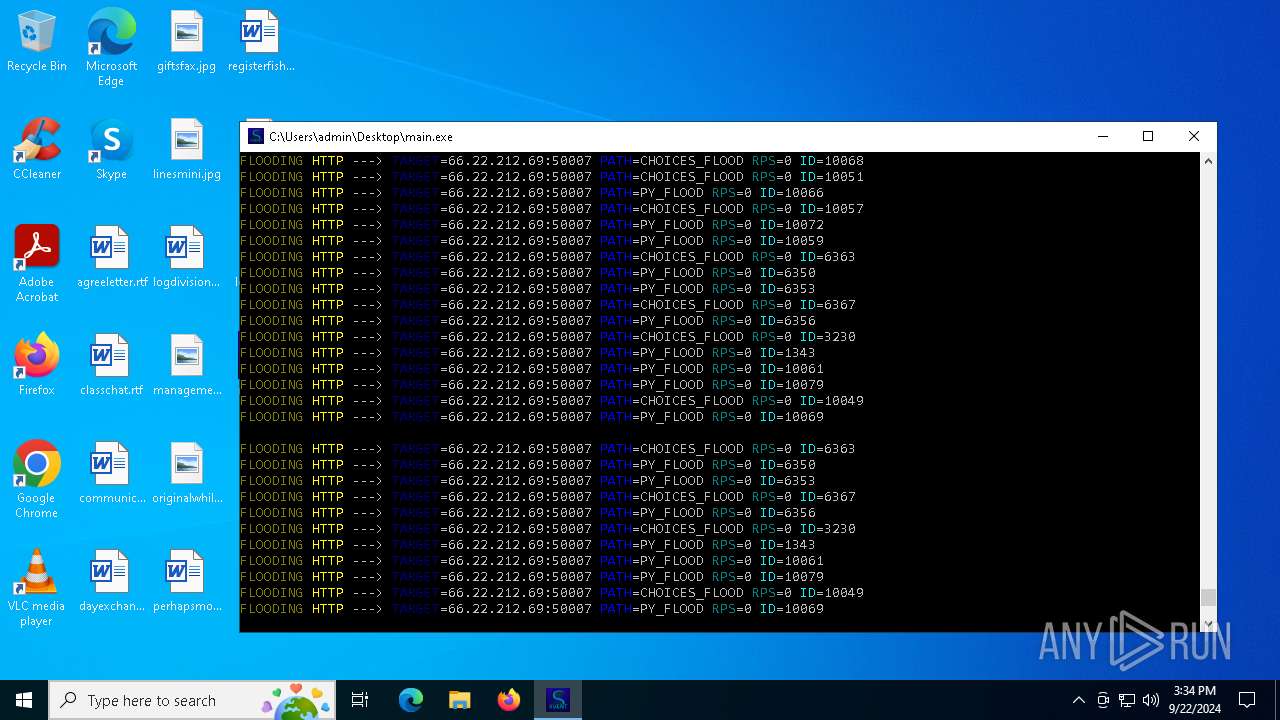
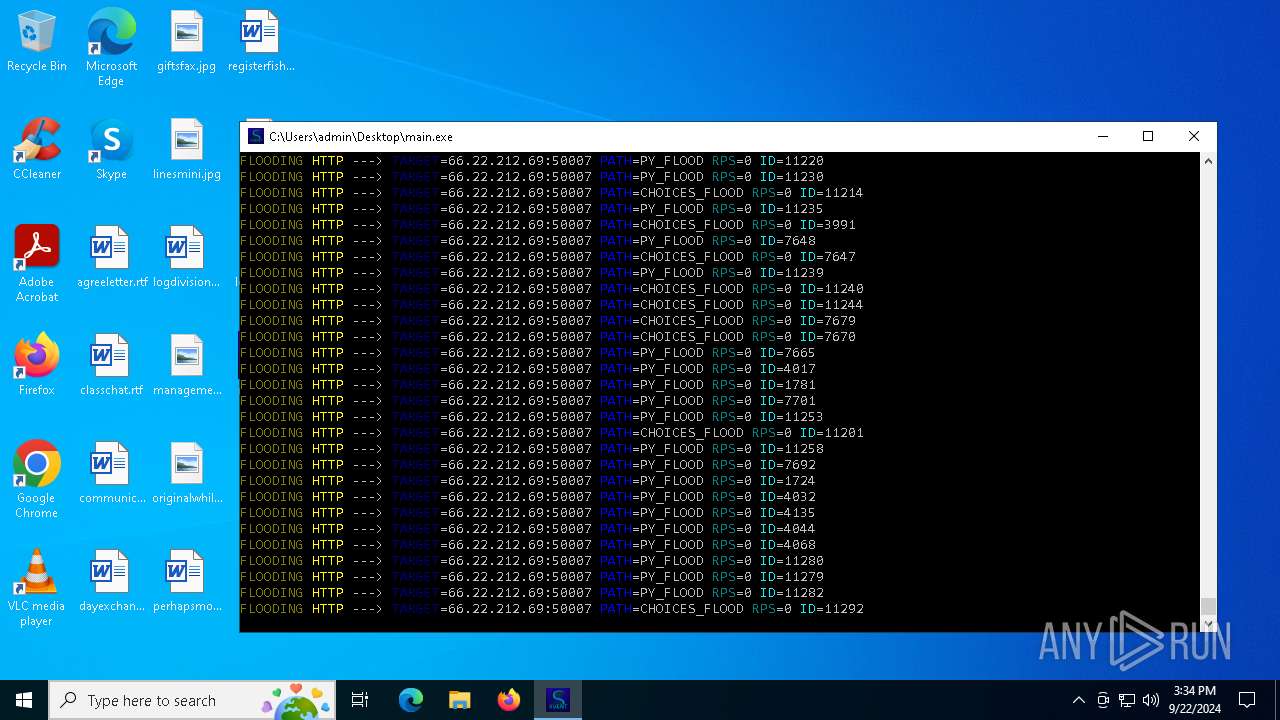
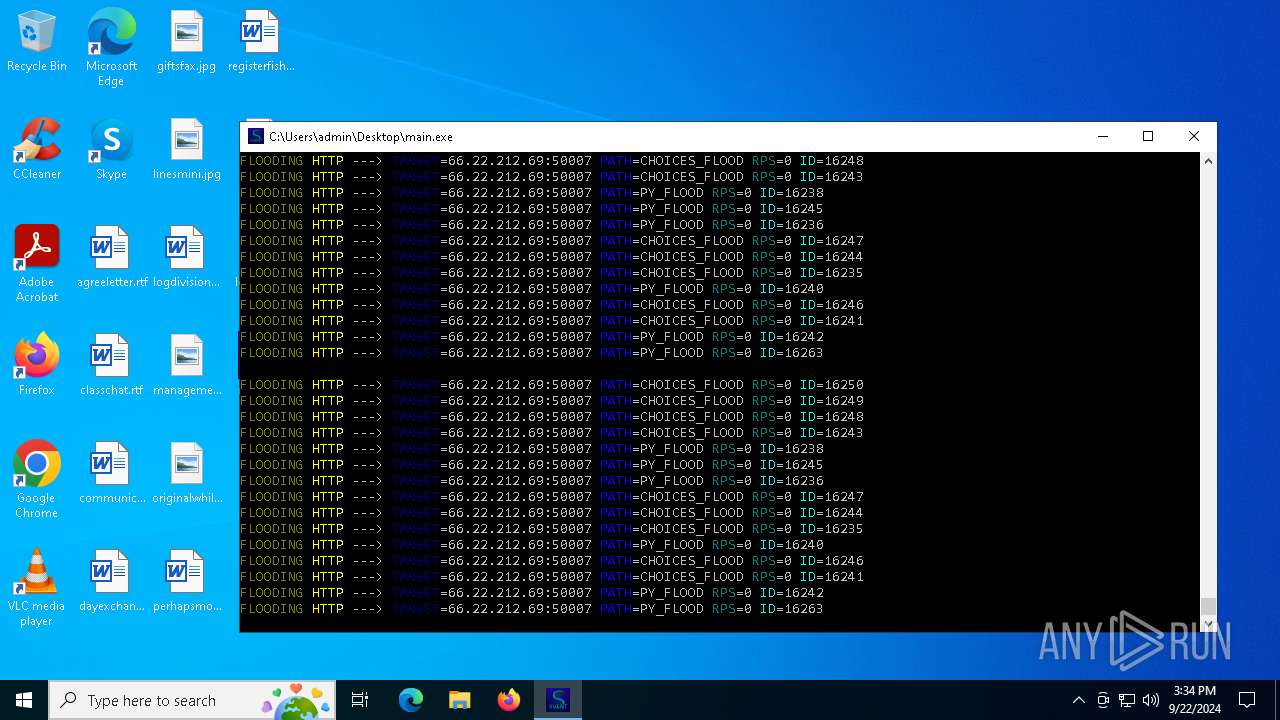
Connects to unusual port
- main.exe (PID: 66212)
- main.exe (PID: 7052)
INFO
Checks supported languages
- loader.exe (PID: 5000)
- loader.exe (PID: 2648)
- main.exe (PID: 360)
- main.exe (PID: 7052)
Creates files or folders in the user directory
- WerFault.exe (PID: 2892)
Manual execution by a user
- loader.exe (PID: 5000)
- loader.exe (PID: 66028)
Reads the software policy settings
- WerFault.exe (PID: 2892)
Checks proxy server information
- WerFault.exe (PID: 2892)
Create files in a temporary directory
- loader.exe (PID: 5000)
- main.exe (PID: 360)
Reads the computer name
- loader.exe (PID: 2648)
- main.exe (PID: 360)
- loader.exe (PID: 5000)
Checks operating system version
- main.exe (PID: 7052)
- main.exe (PID: 66212)
PyInstaller has been detected (YARA)
- main.exe (PID: 7052)
- main.exe (PID: 360)
- main.exe (PID: 66144)
- main.exe (PID: 66212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:03:30 00:20:39+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, Large address aware, DLL |
| PEType: | PE32+ |
| LinkerVersion: | 2.3 |
| CodeSize: | 655872 |
| InitializedDataSize: | 853504 |
| UninitializedDataSize: | 5632 |
| EntryPoint: | 0x1330 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
160
Monitored processes
26
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
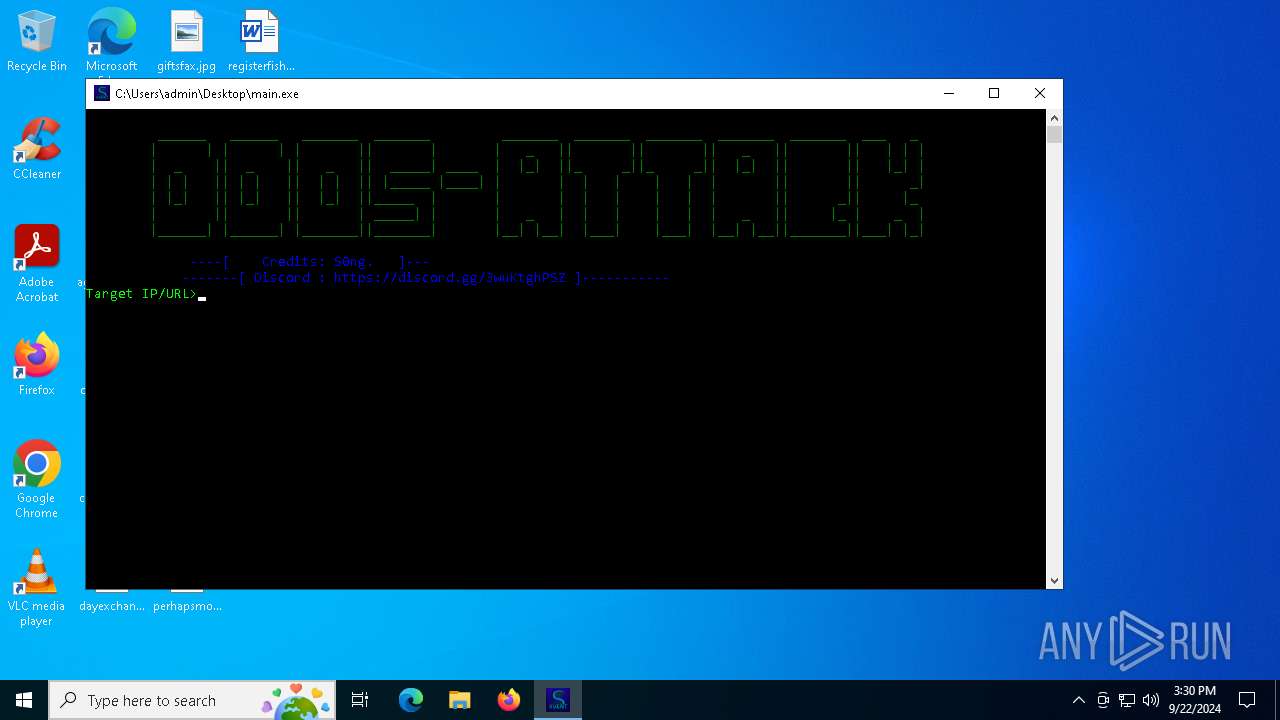
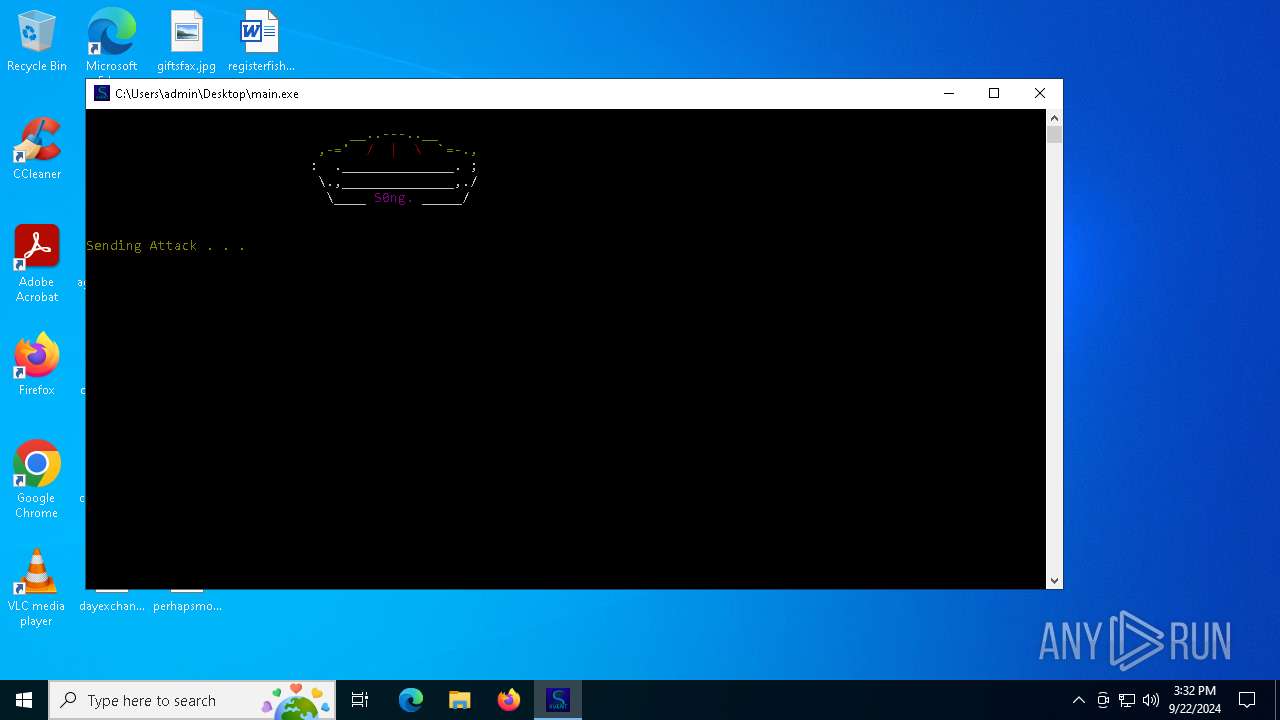
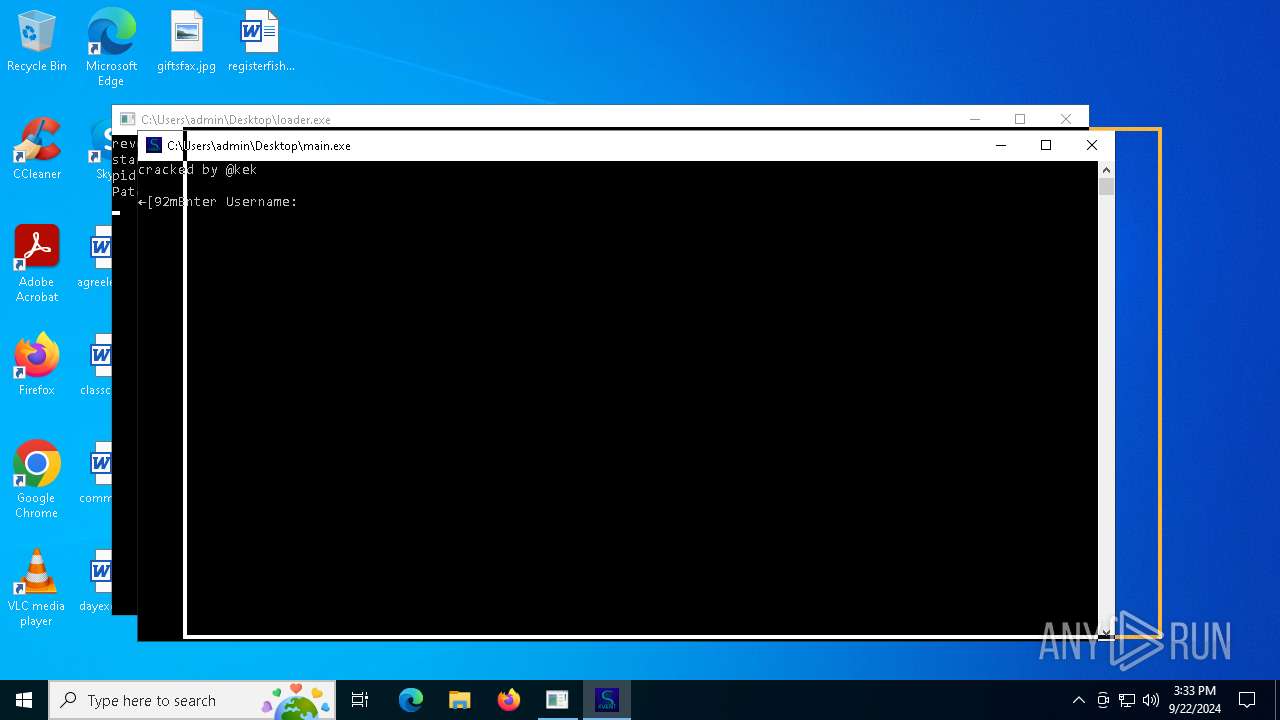
| 360 | main.exe | C:\Users\admin\Desktop\main.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2568 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | C:\WINDOWS\system32\cmd.exe /c "start main.exe" | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\Users\admin\Desktop\loader.exe" | C:\Users\admin\AppData\Local\Temp\onefile_5000_133714926279001590\loader.exe | — | loader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2892 | C:\WINDOWS\system32\WerFault.exe -u -p 6732 -s 328 | C:\Windows\System32\WerFault.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5000 | "C:\Users\admin\Desktop\loader.exe" | C:\Users\admin\Desktop\loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6108 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6432 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6560 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | main.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 966
Read events
4 966
Write events
0
Delete events
0
Modification events
Executable files
240
Suspicious files
6
Text files
20
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_rundll32.exe_cra_55dfcc179d57d77bdbe4c7db11533abed872fb9_cc536f9c_f2fdac44-85d7-40ad-b6e3-495228de9c28\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2892 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:1B7FD5177461034E4086724C5845E927 | SHA256:065AF18C229898A1C2A8D989911ADCD9B1E2AB14B1953EBF8EAF34AE37EA1627 | |||
| 2892 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:C2236F83ABAD6E4950AEE0AD2DB9A62E | SHA256:E35E14AFB787A552438871B7278395C647FF3E64D899ACC04B556FDEB96C2ED1 | |||
| 2892 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA939.tmp.dmp | binary | |
MD5:38B72E242D614D851E932CA61827456F | SHA256:BEBA7DA363341A17C26285DB8484BEF825A4B03BAC4A3AF4FE732BC268780823 | |||
| 2892 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rundll32.exe.6732.dmp | binary | |
MD5:E1BF8A9AC89F27C281730545B9C4D70F | SHA256:34B581346B4987C837BDA20DAD86B45B6DC15AE70C0E465162A999850FC9EA03 | |||
| 5000 | loader.exe | C:\Users\admin\AppData\Local\Temp\onefile_5000_133714926279001590\_socket.pyd | executable | |
MD5:8140BDC5803A4893509F0E39B67158CE | SHA256:39715EF8D043354F0AB15F62878530A38518FB6192BC48DA6A098498E8D35769 | |||
| 5000 | loader.exe | C:\Users\admin\AppData\Local\Temp\onefile_5000_133714926279001590\_ctypes.pyd | executable | |
MD5:6A9CA97C039D9BBB7ABF40B53C851198 | SHA256:E662D2B35BB48C5F3432BDE79C0D20313238AF800968BA0FAA6EA7E7E5EF4535 | |||
| 5000 | loader.exe | C:\Users\admin\AppData\Local\Temp\onefile_5000_133714926279001590\_elementtree.pyd | executable | |
MD5:63629A705BFFCA85CE6A4539BFBDD760 | SHA256:DF71D64818CFECD61AD0122BEA23B685D01BD241F1B06879A2999917818B0787 | |||
| 5000 | loader.exe | C:\Users\admin\AppData\Local\Temp\onefile_5000_133714926279001590\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:40BA4A99BF4911A3BCA41F5E3412291F | SHA256:AF0E561BB3B2A13AA5CA9DFC9BC53C852BAD85075261AF6EF6825E19E71483A6 | |||
| 5000 | loader.exe | C:\Users\admin\AppData\Local\Temp\onefile_5000_133714926279001590\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:EA00855213F278D9804105E5045E2882 | SHA256:F2F74A801F05AB014D514F0F1D0B3DA50396E6506196D8BECCC484CD969621A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16 421
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | WerFault.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
2928 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3180 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
65720 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6252 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6252 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 52.182.143.210:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2892 | WerFault.exe | 20.189.173.20:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2892 | WerFault.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2928 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2928 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3180 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |