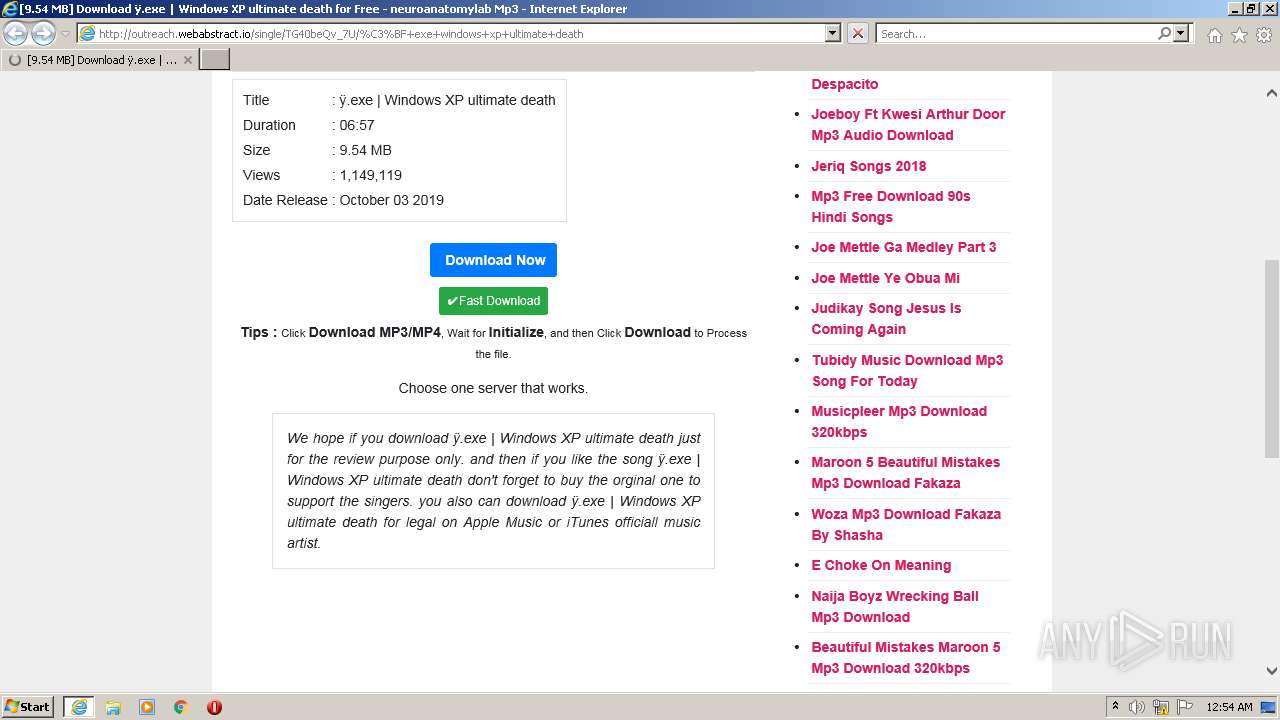
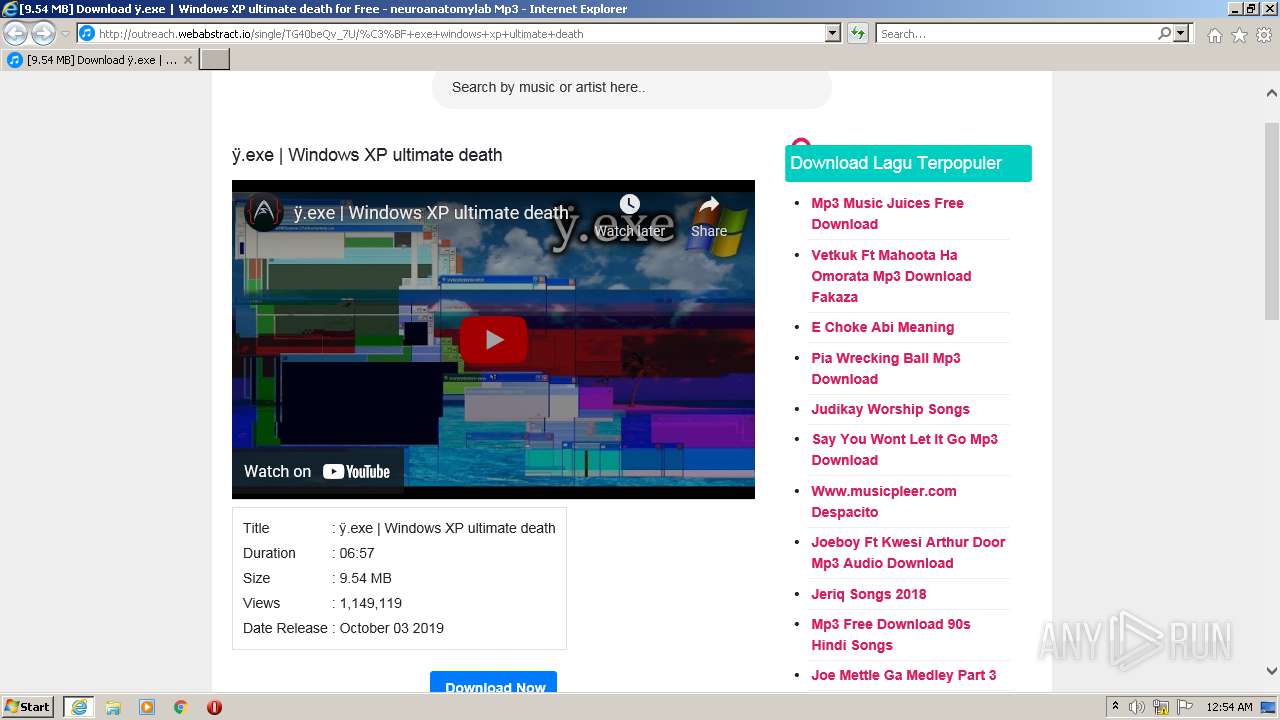
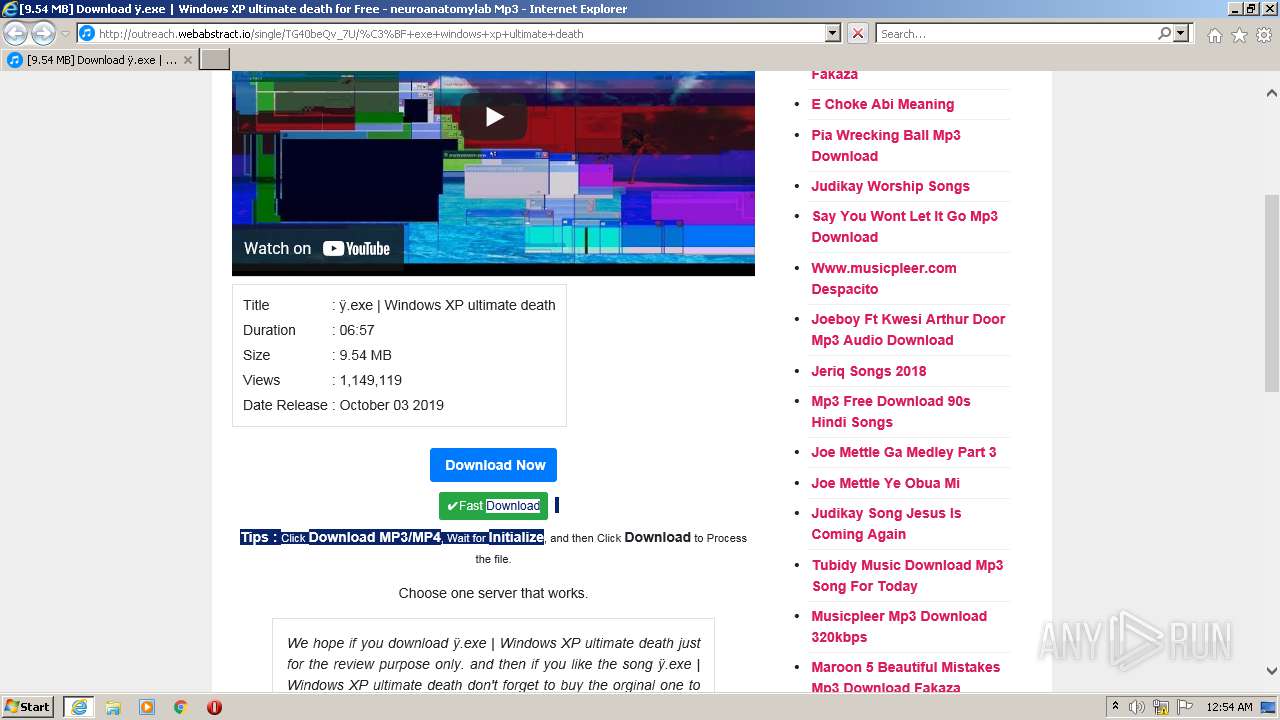
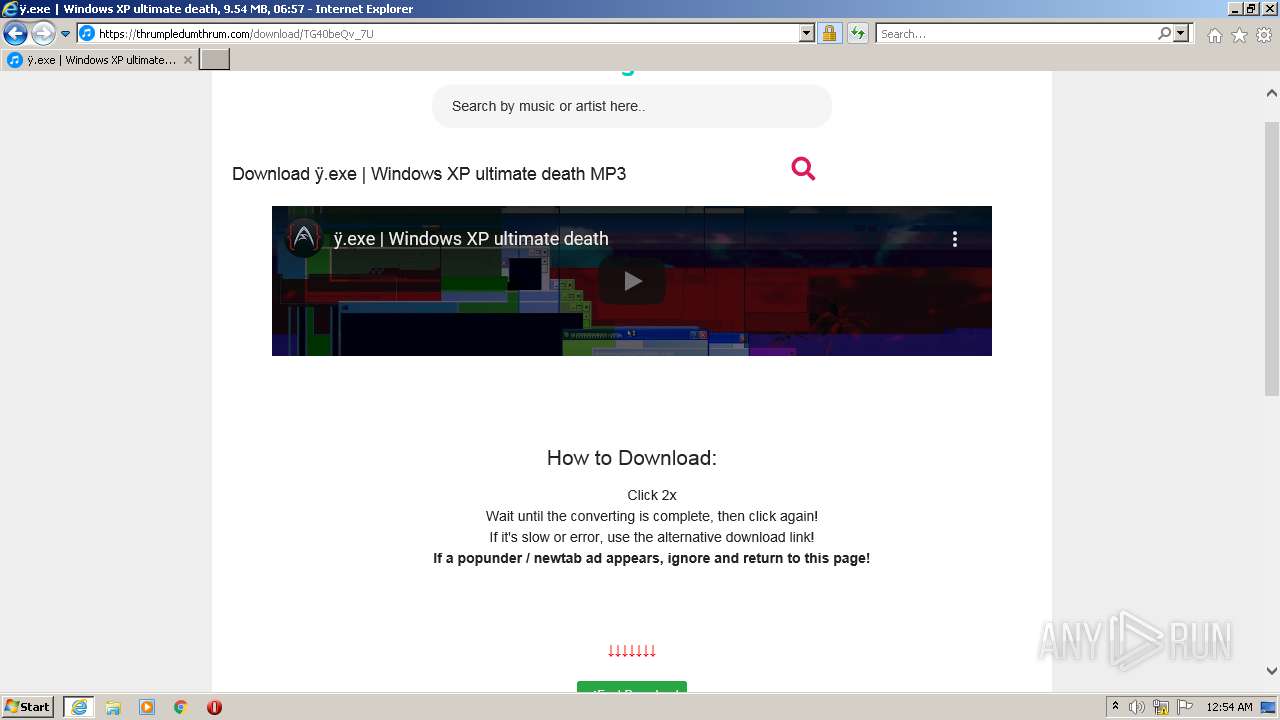
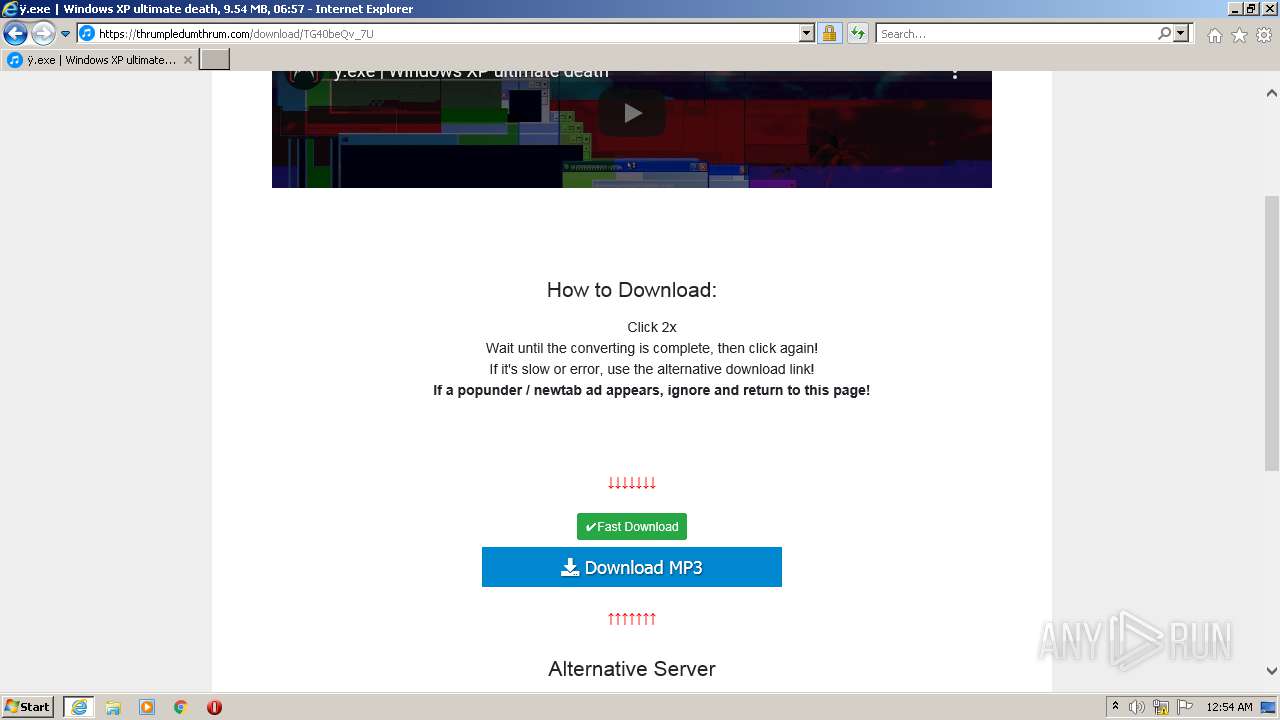
| URL: | http://outreach.webabstract.io/single/TG40beQv_7U/%C3%BF+exe+windows+xp+ultimate+death |
| Full analysis: | https://app.any.run/tasks/c3ea3333-1dbc-4897-ac0f-9827bf39843e |
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2021, 23:54:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C1242B01073FC9E84EF83EE995E70A80 |
| SHA1: | 0343CBE92932983D2036ADA3C1F8BBC826964B10 |
| SHA256: | 560759B0BA3B05923703C1256234ACF02FB4B119F1548BAC2B431847204D5B57 |
| SSDEEP: | 3:N1KRQGEa3E2fRLMwKCOrF/OcSkTkQyAEr:C2GEGVpKCI8cSkwQTEr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2120)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2584)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2584)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2584)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2584)
INFO
Checks supported languages
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 2120)
Changes internet zones settings
- iexplore.exe (PID: 3968)
Application launched itself
- iexplore.exe (PID: 3968)
Checks Windows Trust Settings
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3968)
Reads the computer name
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 2120)
Reads settings of System Certificates
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3968)
Reads internet explorer settings
- iexplore.exe (PID: 2120)
Creates files in the user directory
- iexplore.exe (PID: 2120)
Reads CPU info
- iexplore.exe (PID: 2120)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3968 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2584 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://outreach.webabstract.io/single/TG40beQv_7U/%C3%BF+exe+windows+xp+ultimate+death" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
24 235
Read events
24 053
Write events
182
Delete events
0
Modification events
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30902466 | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30902466 | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
26
Text files
60
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\�+exe+windows+xp+ultimate+death[1].htm | html | |
MD5:654D8EF0EC46DE1DA05822DFB9847C2A | SHA256:A4D84E5B8901849BC8D6E09BF1F2177FD9028FDB37D564B90C56880588EDF700 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C9812F57F38C9758D9721545BEB7F726 | SHA256:91571859F14F87DFD732B8245D8A8AE424C593B56355DF5963C265E02CBE95D4 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:8F9C8D7ABB4D17438C210AE69C1A1CF5 | SHA256:49E1B7F213831A5957F40D5A4EF6399477BCCFE5E5A25787637255D764486E7C | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:480D699659B685393294D0EFD9EF05BC | SHA256:7B8B42F54C9BF619227650A4B4392249E1A02EB2A598DB7B613C8D9A0193B07A | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:77354BB57812904DE3CA9B414407FE41 | SHA256:551223B16C2BBD86980B8D9A43B9BBBB682B9810011E41D910A8BEC92465A459 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:B62C2770EDCF285D50A0B48C35F91084 | SHA256:592D95A294CDA9D23B14D87E6D3EC0A2F6B595AE15EEA6D6497521A48359CB34 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:EC35D34E3B842C8F9A3D301986A91449 | SHA256:A053FCC23F9E8D1FD91C4A7B472E8335D786FCCD5EB881A4CFC757CE605BFF54 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A16C6C16D94F76E0808C087DFC657D99_140D080DA30165D01D9873A769BF7E33 | der | |
MD5:CF85497A5610347C684B287C76781526 | SHA256:5C9637E174E7B4FE643E2D756E8461BBEB0D3E4D1D4E09D498B0547D2C519146 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\TG40beQv_7U[1].htm | html | |
MD5:2D3FC93AF36F7479F852D422546D1739 | SHA256:8D18767FE913E925D0416432B2B509404A8FFD2CE7687819C50DCF867EFE4DD5 | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\fetch-polyfill[1].js | text | |
MD5:04E3CC8A9641B3F9F9C9370F4E9B5BDD | SHA256:DE6C4FFA2BD9FD283610E28D0DB2EC48607AAB39D213A51AEF248673A0A7E980 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
75
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | iexplore.exe | GET | 403 | 192.243.59.13:80 | http://albeitinflame.com/ad/48/62/ad48620f3e5007b84d90ccc8641bd3eb.js | US | — | — | malicious |
2120 | iexplore.exe | GET | 200 | 165.227.136.135:80 | http://outreach.webabstract.io/single/TG40beQv_7U/%C3%BF+exe+windows+xp+ultimate+death | DE | html | 8.71 Kb | unknown |
2120 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e3332f869ade4b0d | unknown | compressed | 4.70 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?55e4be5a032ed864 | unknown | compressed | 4.70 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3c01e8f344e98ae1 | unknown | compressed | 4.70 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6343a9d76e824cd | unknown | compressed | 4.70 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d316bb5a4a94e3ea | unknown | compressed | 4.70 Kb | whitelisted |
2120 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDjy1E0bEvIFQoAAAAA60qp | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | iexplore.exe | 142.250.184.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 142.250.185.246:443 | i.ytimg.com | Google Inc. | US | unknown |
2120 | iexplore.exe | 142.250.185.132:443 | www.google.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 165.227.136.135:80 | outreach.webabstract.io | Digital Ocean, Inc. | DE | unknown |
2120 | iexplore.exe | 192.243.59.13:80 | albeitinflame.com | DataWeb Global Group B.V. | US | malicious |
2120 | iexplore.exe | 104.16.19.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2120 | iexplore.exe | 104.22.53.65:443 | www.statcounter.com | Cloudflare Inc | US | suspicious |
2120 | iexplore.exe | 142.250.186.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 2.16.186.33:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2120 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
outreach.webabstract.io |
| unknown |
lh3.googleusercontent.com |
| whitelisted |
tpc.googlesyndication.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
i3.ytimg.com |
| whitelisted |
img.youtube.com |
| whitelisted |
albeitinflame.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.statcounter.com |
| whitelisted |