| File name: | 2020-05-31_01-26-34.exe |
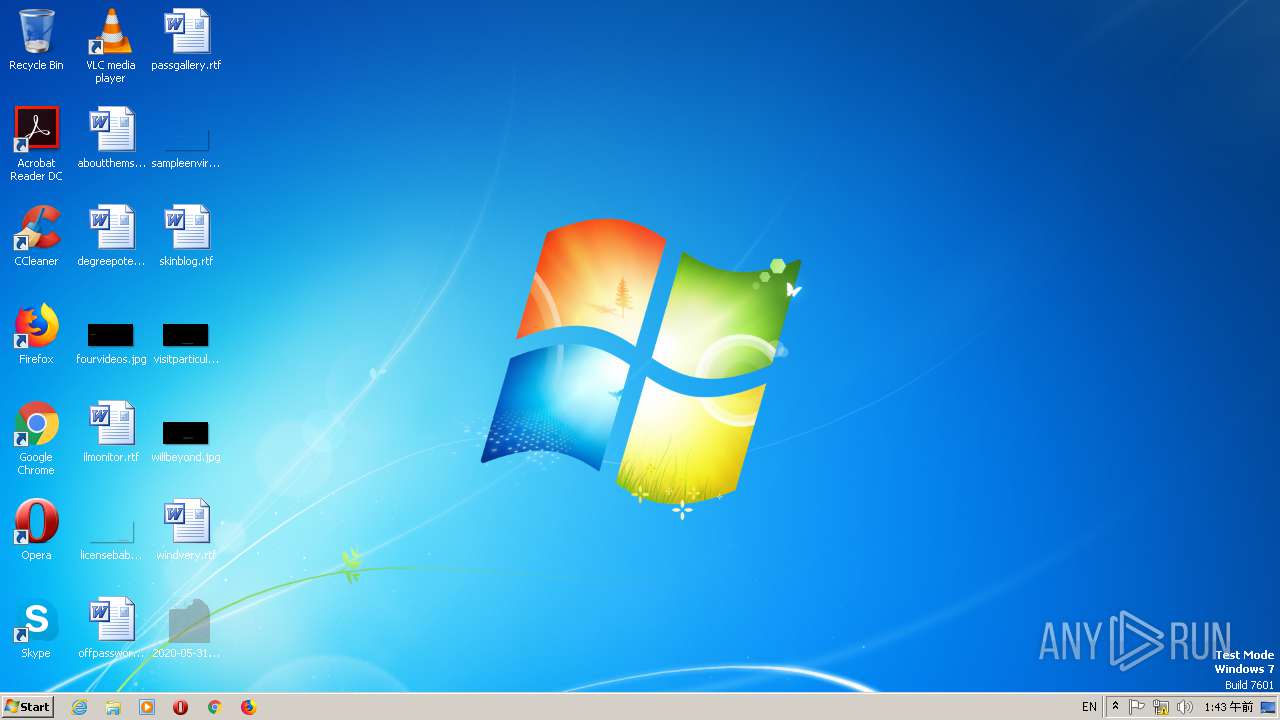
| Full analysis: | https://app.any.run/tasks/992fed91-33b4-4c55-818d-69b1bfdc428b |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 16:43:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F55AFA581373EAB464F8227BEAE5B451 |
| SHA1: | A9FDBBE35DDEC97416B2DCA7A06C23447A63ACA5 |
| SHA256: | 56043E7597F457B55A4F6D7B98589F49C98C78A8E360C6ACB6C2D2BAD676CF21 |
| SSDEEP: | 12288:+/jSbNiEPX0iYBFyBvfLsPoaWpyeueVAACPbkS93HCjPK5+7opZF3ScGP/HD:hbNFYSB3RNpyexObjd3iji5+uSvr |
MALICIOUS
Changes settings of System certificates
- 2020-05-31_01-26-34.exe (PID: 3012)
Actions looks like stealing of personal data
- 2020-05-31_01-26-34.exe (PID: 3012)
Runs injected code in another process
- powercfg.exe (PID: 2280)
- rundll32.exe (PID: 692)
Application was injected by another process
- svchost.exe (PID: 624)
- SearchIndexer.exe (PID: 1576)
- svchost.exe (PID: 888)
- svchost.exe (PID: 332)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 692)
SUSPICIOUS
Reads the cookies of Google Chrome
- 2020-05-31_01-26-34.exe (PID: 3012)
Application launched itself
- 2020-05-31_01-26-34.exe (PID: 2400)
Removes files from Windows directory
- taskhost.exe (PID: 2508)
- powercfg.exe (PID: 2280)
- rundll32.exe (PID: 692)
Executed as Windows Service
- taskhost.exe (PID: 2508)
- powercfg.exe (PID: 2280)
- rundll32.exe (PID: 692)
- lpremove.exe (PID: 2296)
- vssvc.exe (PID: 1704)
Creates files in the Windows directory
- taskhost.exe (PID: 2508)
- powercfg.exe (PID: 2280)
- rundll32.exe (PID: 692)
Creates a software uninstall entry
- 2020-05-31_01-26-34.exe (PID: 3012)
Reads the machine GUID from the registry
- wmiprvse.exe (PID: 2796)
- powercfg.exe (PID: 2280)
- rundll32.exe (PID: 692)
- vssvc.exe (PID: 1704)
- SearchProtocolHost.exe (PID: 1224)
Creates files in the program directory
- powercfg.exe (PID: 2280)
- SearchIndexer.exe (PID: 1576)
Searches for installed software
- rundll32.exe (PID: 692)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 1704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:05 08:46:26+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 729600 |
| InitializedDataSize: | 43585024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2f3d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.5.1 |
| ProductVersionNumber: | 1.9.0.1 |
| FileFlagsMask: | 0x006f |
| FileFlags: | Private build |
| FileOS: | Unknown (0x40314) |
| ObjectFileType: | Static library |
| FileSubtype: | 49 |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unknown (05B0) |
| InternalName: | awizegpoz.im |
| LegalCopyright: | Copyright (C) 2020, kilu |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jul-2019 06:46:26 |
| Detected languages: |
|
| Debug artifacts: |
|
| InternalName: | awizegpoz.im |
| LegalCopyright: | Copyright (C) 2020, kilu |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Jul-2019 06:46:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B2192 | 0x000B2200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.9904 |
.data | 0x000B4000 | 0x0297AD44 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.965163 |
.rsrc | 0x02A2F000 | 0x00013A28 | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09911 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42781 | 372 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 5.30308 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.83996 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.39501 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.6258 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.86815 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.94975 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 5.75304 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.84558 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.6321 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
48
Monitored processes
14
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 624 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | C:\Windows\system32\rundll32.exe /d srrstr.dll,ExecuteScheduledSPPCreation | C:\Windows\system32\rundll32.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1224 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.23930 (win7sp1_ldr.171011-1526) Modules
| |||||||||||||||
| 1576 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\System32\SearchIndexer.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | C:\Windows\System32\powercfg.exe -energy -auto | C:\Windows\System32\powercfg.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | C:\Windows\system32\lpremove.exe | C:\Windows\system32\lpremove.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: MUI Language pack cleanup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\Desktop\2020-05-31_01-26-34.exe" | C:\Users\admin\Desktop\2020-05-31_01-26-34.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 286
Read events
1 999
Write events
283
Delete events
4
Modification events
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000007F000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\131\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000001BAA5A0ECD1ED4B64DFBF621DC9044BF0F000000010000002000000061905BC048345D3815587E318FEAAE705D07527F3B5BD1B2A6AF514E29BA46525C000000010000000400000000080000030000000100000014000000E02357FC7708441D4B0BE5F371F4B28961870F70140000000100000014000000ECCD4BA46722CB4F92060701865DDF09D8AF68B41900000001000000100000000FB5FACA274B0EA933E42C34A45C2D5620000000010000006A030000308203663082024EA003020102020900EE1E7E5DC92BCE32300D06092A864886F70D01010B05003048310B30090603550406130241553113301106035504080C0A536F6D652D5374617465310D300B06035504070C044369747931153013060355040A0C0C536F6D6520436F6D70616E79301E170D3137303932393132323035305A170D3230303932383132323035305A3048310B30090603550406130241553113301106035504080C0A536F6D652D5374617465310D300B06035504070C044369747931153013060355040A0C0C536F6D6520436F6D70616E7930820122300D06092A864886F70D01010105000382010F003082010A0282010100C213E403EA7099364CC3D32AE10D85F8364F3874F86A14DAD9972751C9F548F6025F083F3F8BE947523744A631B6E409CF2CEFBC28F5C9F16ACD3C88ABE7BA7A5871A1CBF3562F7A576C3E9FAED296B5B9867651DB238499683B4E9D768FDA49C5BCA2A9928AFAF2EAD01F1FBE679E6D8ECC7BA57BB55DFA44C03A14BF11D36C7F9D654AC6B76DF9E8D83E1D238A1BCFAA22BADF071A9300CBDCC71C58846BD4ECB7F2BA7BBEF630C61B4FB01BC67E022BE89E243B0EF7F6ABBAC502A48E1DE65787B538F842E83652C365E26F2D47BFA5132215B96E2725AC3FD496BAE376D778A2C3C35D0382B89F61961BF6BA08DB4A892B4BCE3FA96FF3990C6066F1E1FF0203010001A3533051301D0603551D0E04160414ECCD4BA46722CB4F92060701865DDF09D8AF68B4301F0603551D23041830168014ECCD4BA46722CB4F92060701865DDF09D8AF68B4300F0603551D130101FF040530030101FF300D06092A864886F70D01010B0500038201010095A081FEE7794AAE6A222E01AD459EB4288CA6DCD8E1A4F5EDF609C4ACB16E19F51B543E8C75E6B833556E22641E3619EE31F26A7F5477CA8AB8F7417BFDAE076DD329D01C490D1551313F6BA132F46CAFB608C0378CBB1F1C019C573824F7758EAB50AACBE52E4D7B2EC5BD50B555CF4EC9A29892E262ED148EEC6C07F8BDD9D3BECE8402498A490A20A7F518A918065213AE11EBAC77BD1504B4E60EB2C928DA2ACE10A2B7BB7398D229D3EC6A1C2C2BE2E9C5B10C62E4012057E62598096315D01E46D8BC72E239374AB31A79CA0FE4BA94A64B3934E5C618DDB3B56089FEA4D8BAF00EC868FEE19ECCD0EA27360E690B838D3AD4DBF5BF6448F4894867E3 | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\E02357FC7708441D4B0BE5F371F4B28961870F70 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3012) 2020-05-31_01-26-34.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | 2020-05-31_01-26-34.exe | C:\Users\admin\AppData\Local\Temp\1058671.dat | — | |
MD5:— | SHA256:— | |||
| 3012 | 2020-05-31_01-26-34.exe | C:\Users\admin\AppData\Local\Temp\1058750.dat | — | |
MD5:— | SHA256:— | |||
| 3012 | 2020-05-31_01-26-34.exe | C:\Users\admin\AppData\Local\Temp\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 3012 | 2020-05-31_01-26-34.exe | C:\Users\admin\AppData\Local\Temp\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2508 | taskhost.exe | \SystemRoot\System32\Config\RegBack\SECURITY.OLD | — | |
MD5:— | SHA256:— | |||
| 2508 | taskhost.exe | C:\Windows\System32\Config\RegBack\SECURITY | — | |
MD5:— | SHA256:— | |||
| 2508 | taskhost.exe | \SystemRoot\System32\Config\RegBack\SOFTWARE.OLD | — | |
MD5:— | SHA256:— | |||
| 2508 | taskhost.exe | C:\Windows\System32\Config\RegBack\SOFTWARE | — | |
MD5:— | SHA256:— | |||
| 2508 | taskhost.exe | \SystemRoot\System32\Config\RegBack\SYSTEM.OLD | — | |
MD5:— | SHA256:— | |||
| 2508 | taskhost.exe | C:\Windows\System32\Config\RegBack\SYSTEM | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | 2020-05-31_01-26-34.exe | GET | 200 | 149.28.244.249:80 | http://www.ipcode.pw/ | US | text | 2 b | malicious |
3012 | 2020-05-31_01-26-34.exe | POST | 200 | 38.27.96.30:80 | http://www.infokscents.com/ | US | — | — | malicious |
3012 | 2020-05-31_01-26-34.exe | GET | 200 | 88.99.66.31:443 | https://iplogger.org/1PDhe7 | DE | image | 116 b | shared |
3012 | 2020-05-31_01-26-34.exe | POST | 200 | 38.27.96.30:80 | http://www.infokscents.com/Home/Index/getdata | US | text | 7 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | 2020-05-31_01-26-34.exe | 149.28.244.249:80 | www.ipcode.pw | — | US | suspicious |
3012 | 2020-05-31_01-26-34.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
3012 | 2020-05-31_01-26-34.exe | 38.27.96.30:80 | www.infokscents.com | HOSTSPACE NETWORKS LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ipcode.pw |
| malicious |
iplogger.org |
| shared |
www.infokscents.com |
| malicious |
teredo.ipv6.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
332 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3012 | 2020-05-31_01-26-34.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
3012 | 2020-05-31_01-26-34.exe | A Network Trojan was detected | SPYWARE [PTsecurity] Socelars |
3 ETPRO signatures available at the full report