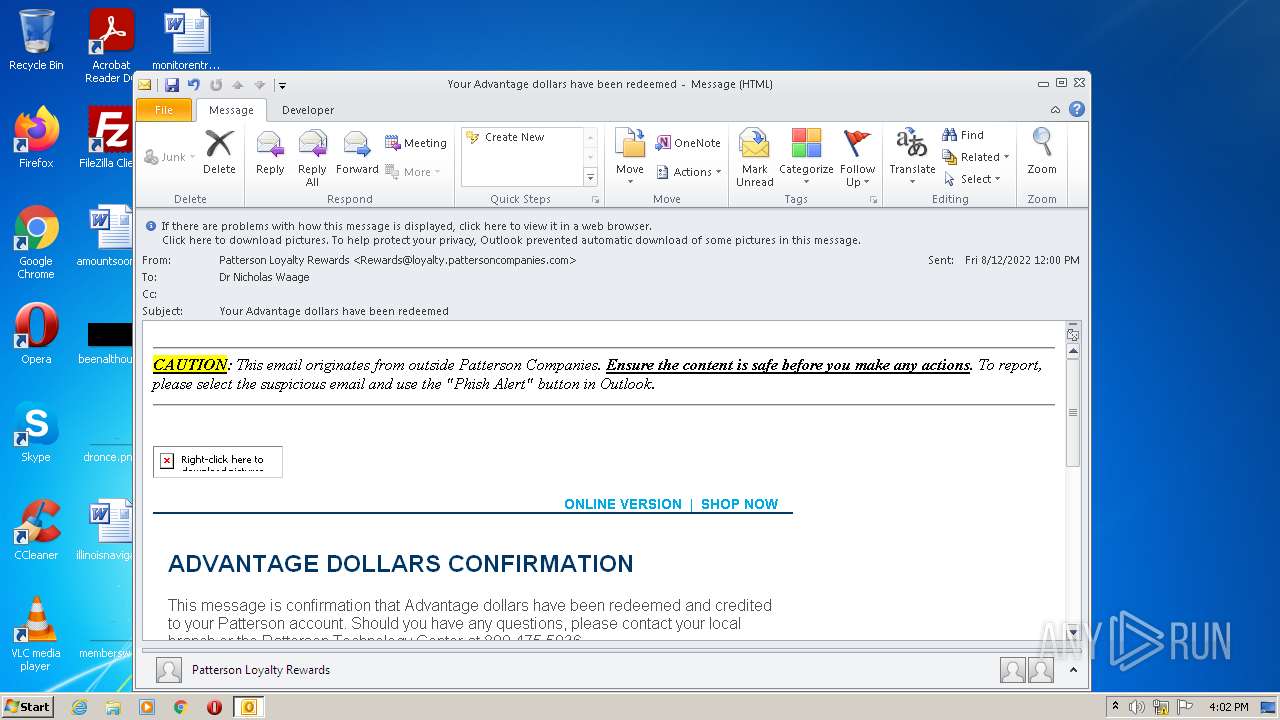
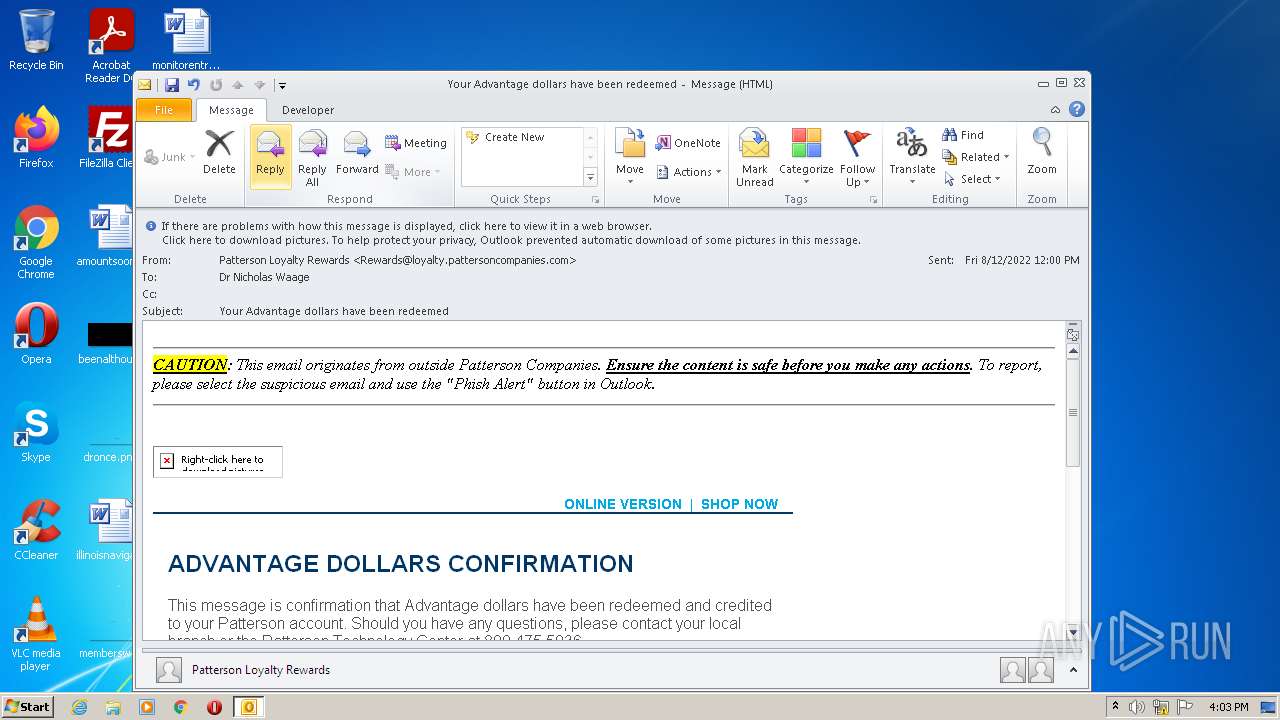
| File name: | phish_alert_sp2_2.0.0.0.eml |
| Full analysis: | https://app.any.run/tasks/31918060-085a-46c8-b975-b0cd92ff65ed |
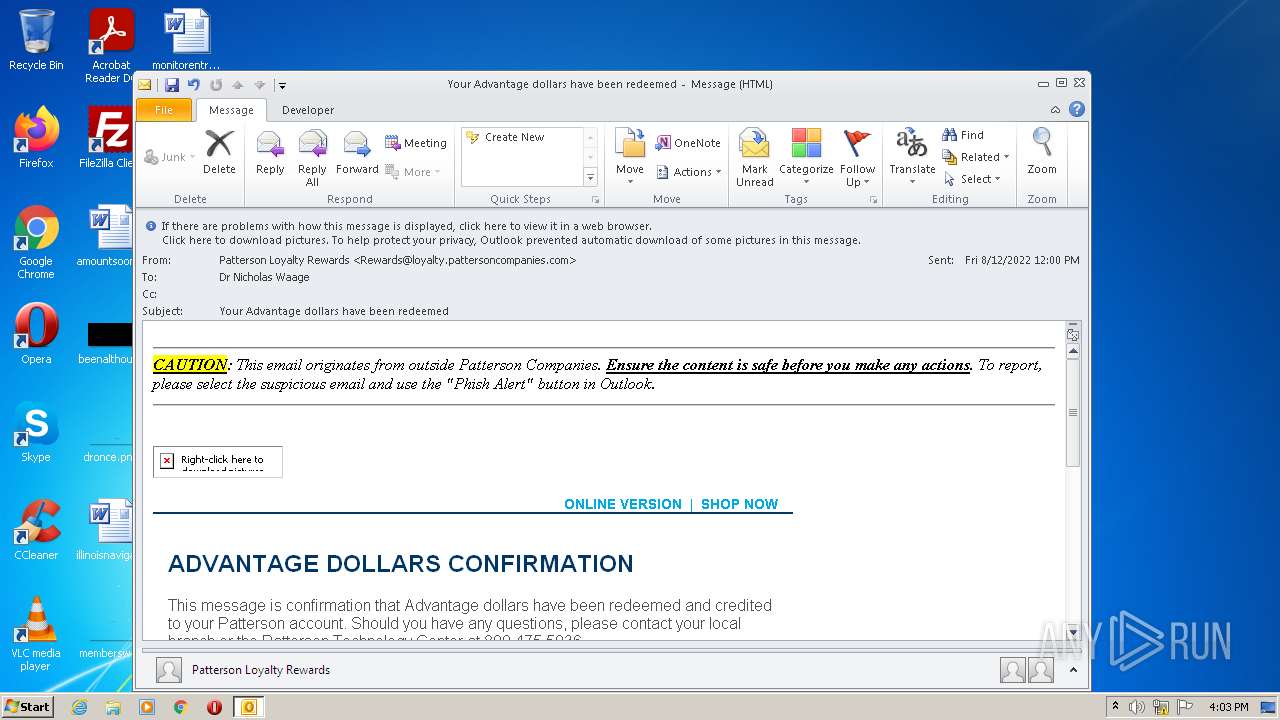
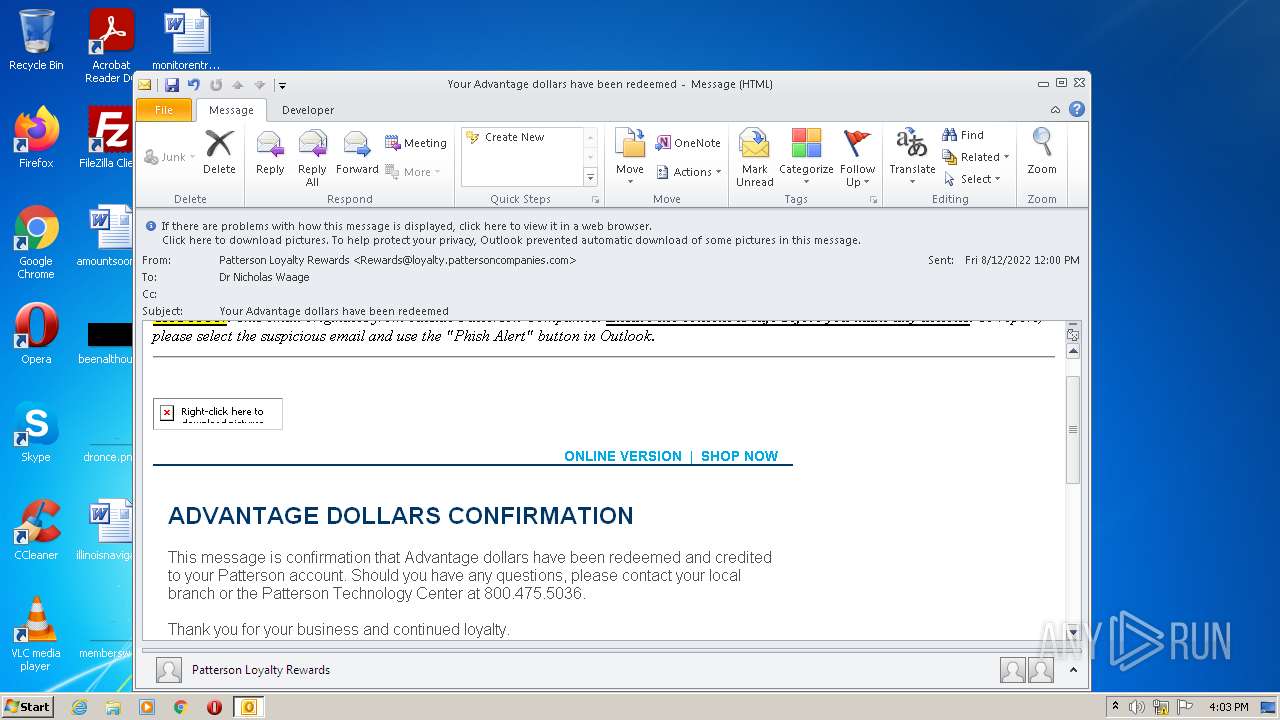
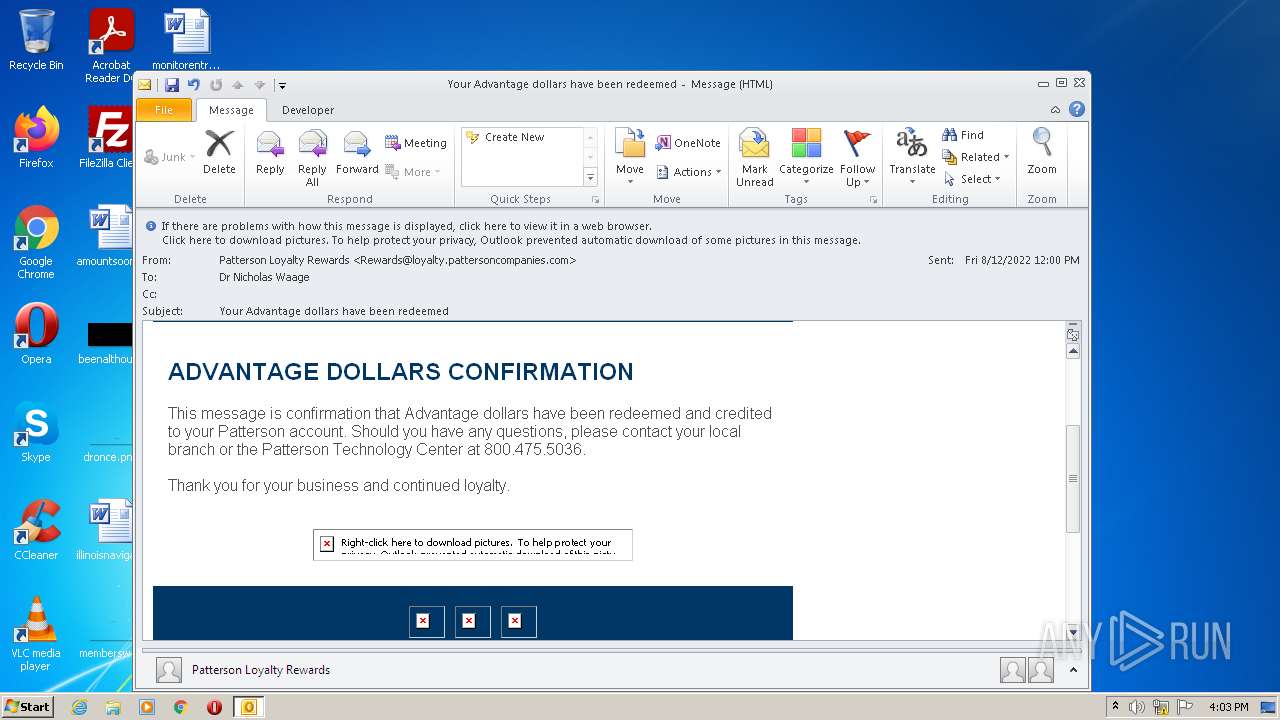
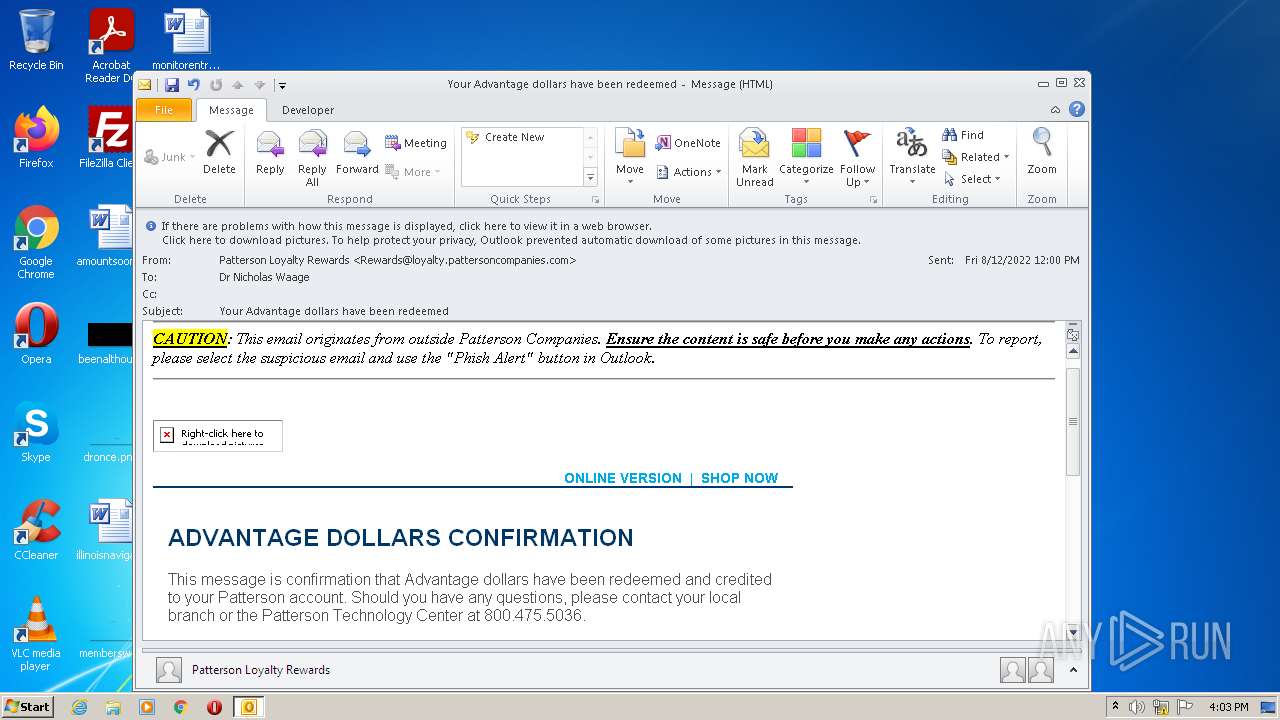
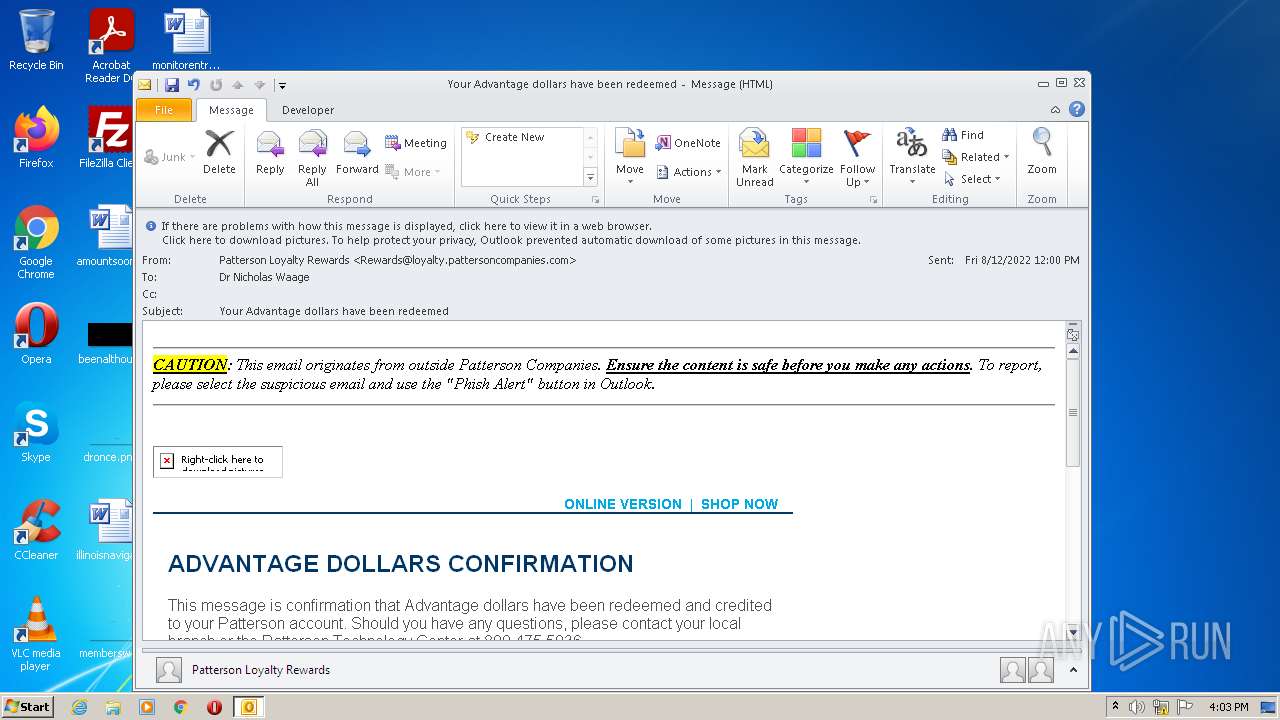
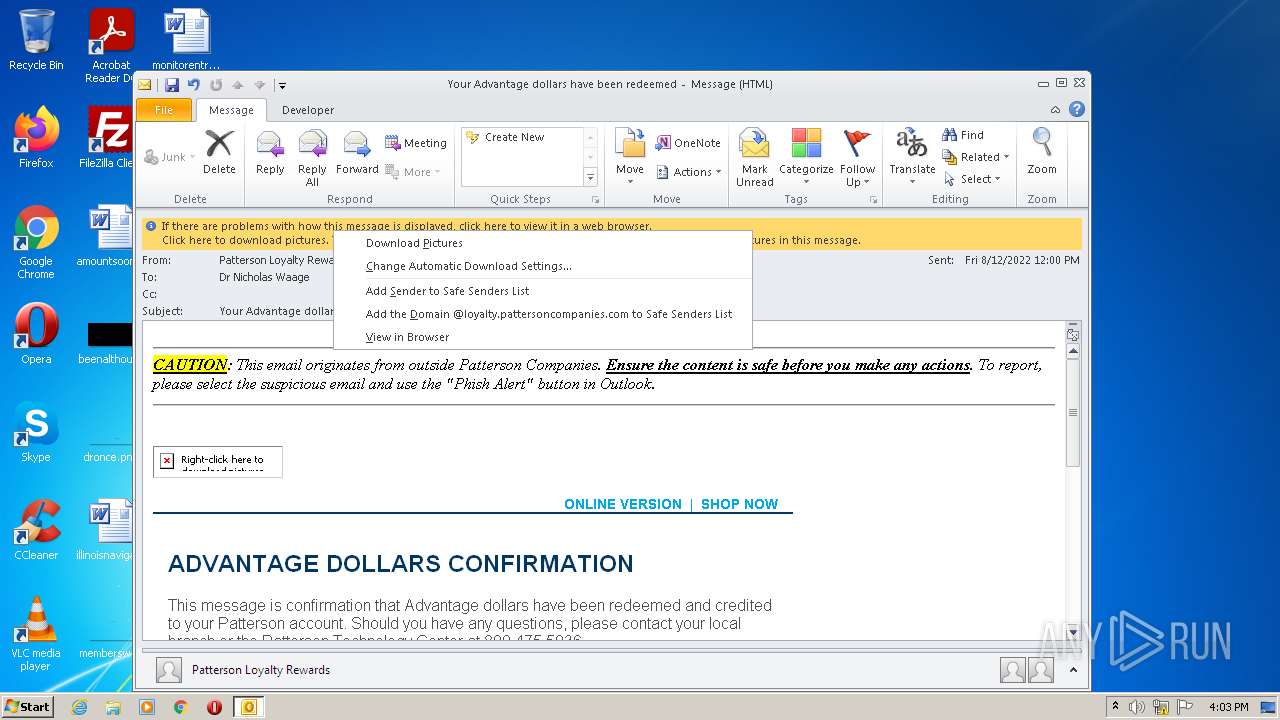
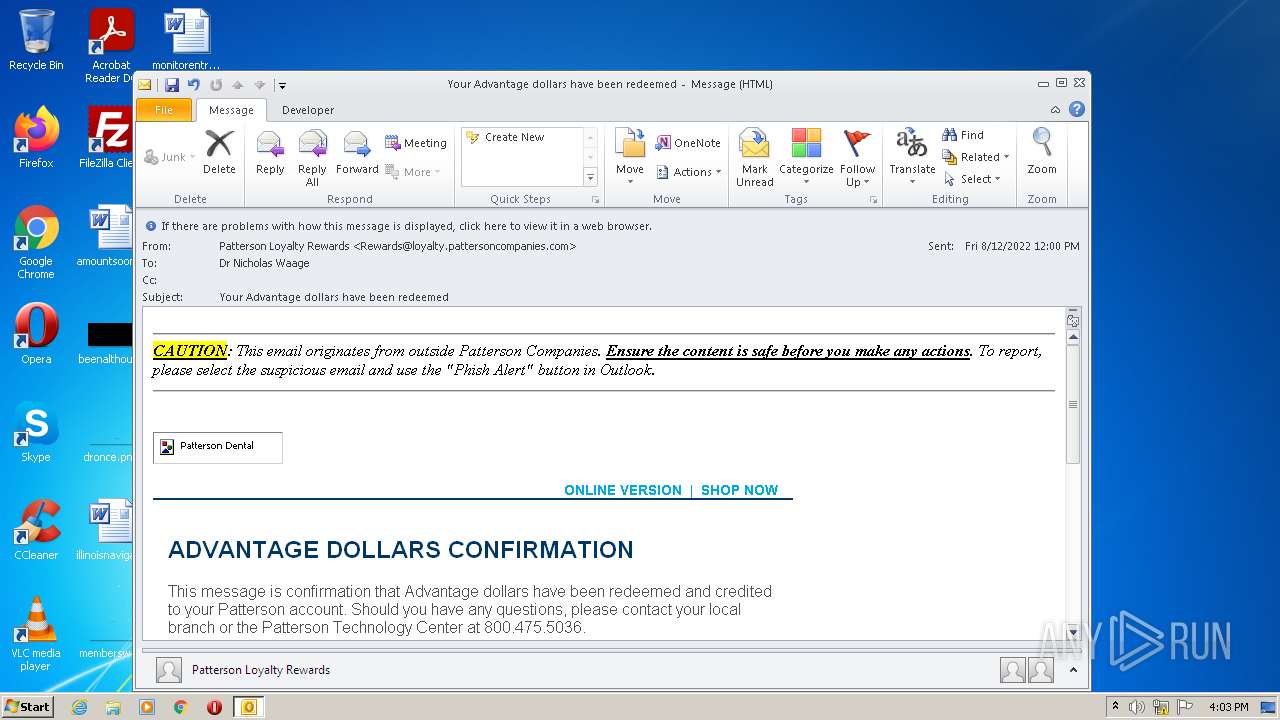
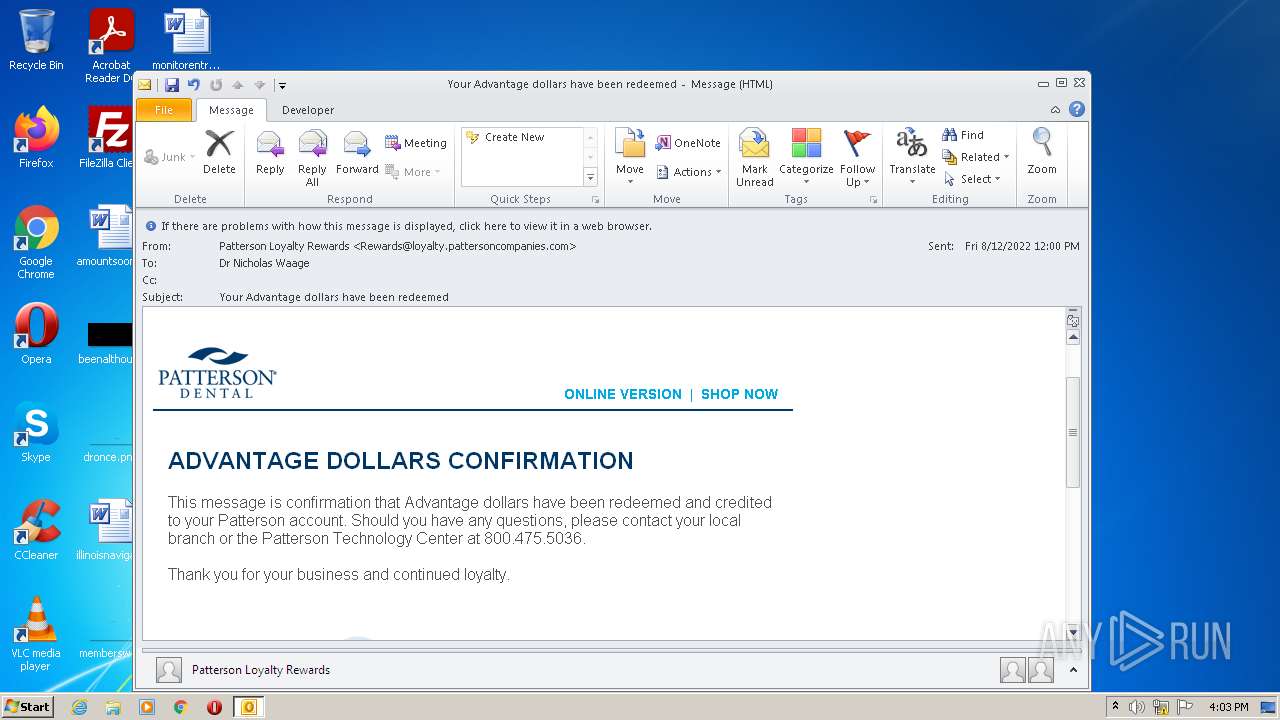
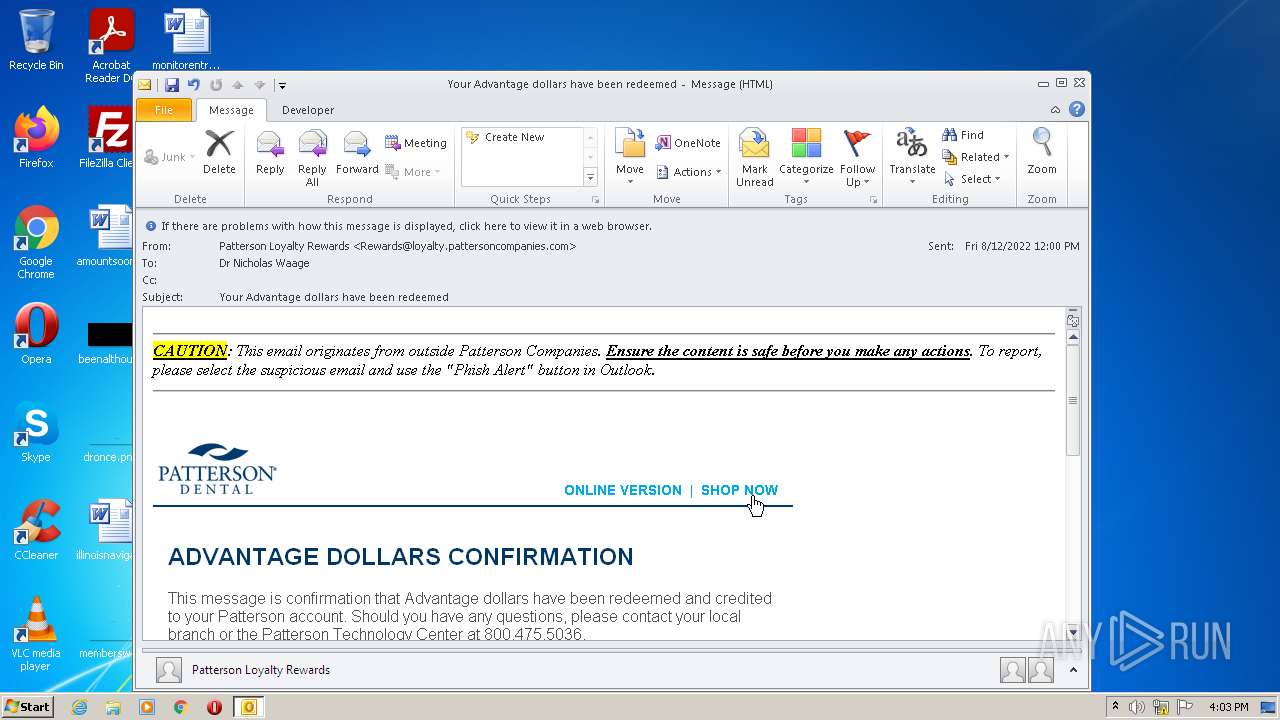
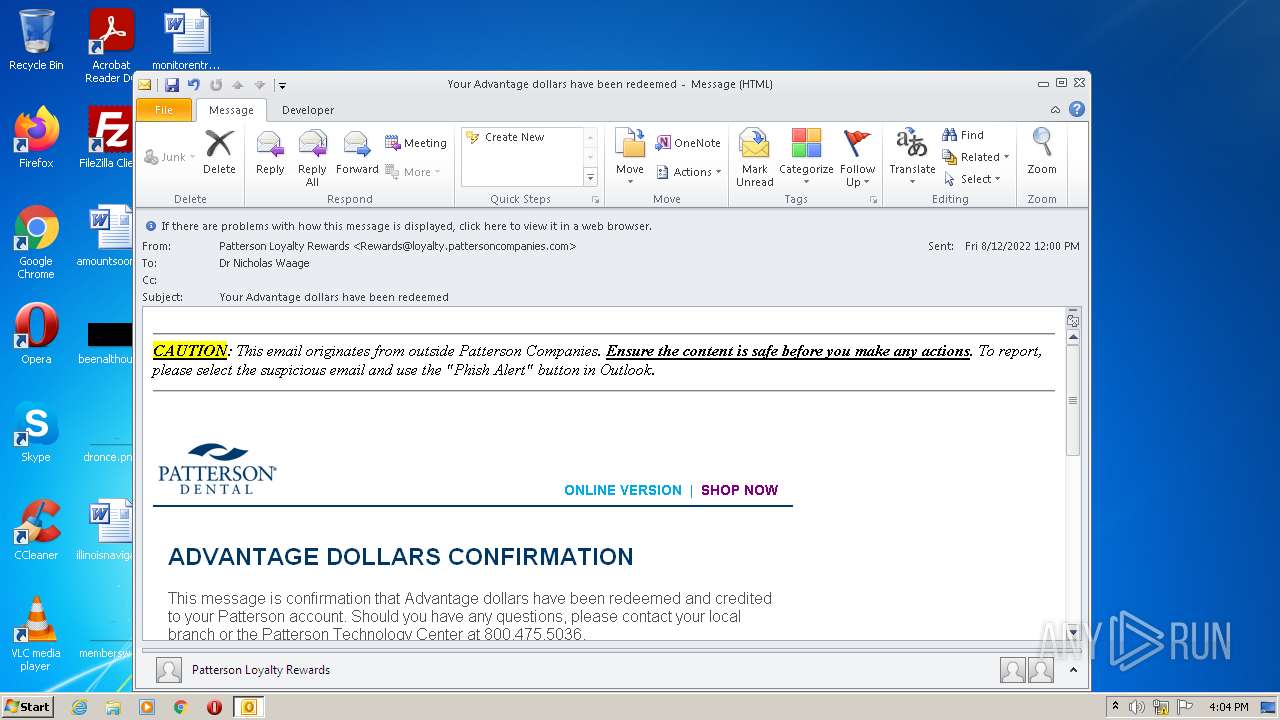
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 15:02:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 0D2601500F6770522F57086EA9B166AC |
| SHA1: | EECC338E4D28924532305370A592A120298CE688 |
| SHA256: | 55F3BF0011102B6B0674550BBC7B812B1DDFB6285FC39CF210A61A8D8A4BCED8 |
| SSDEEP: | 768:nmBhDmznYEqwZk4/gB/KCH+/gN/gC/gWgnGhEuEQZRw28af:m+Z4Lw28af |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 3332)
Reads the computer name
- OUTLOOK.EXE (PID: 3332)
Searches for installed software
- OUTLOOK.EXE (PID: 3332)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2404)
INFO
Checks supported languages
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 2404)
Reads the computer name
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 2404)
Changes internet zones settings
- iexplore.exe (PID: 2676)
Application launched itself
- iexplore.exe (PID: 2676)
Reads settings of System Certificates
- iexplore.exe (PID: 2404)
Reads internet explorer settings
- iexplore.exe (PID: 2404)
Checks Windows Trust Settings
- iexplore.exe (PID: 2404)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
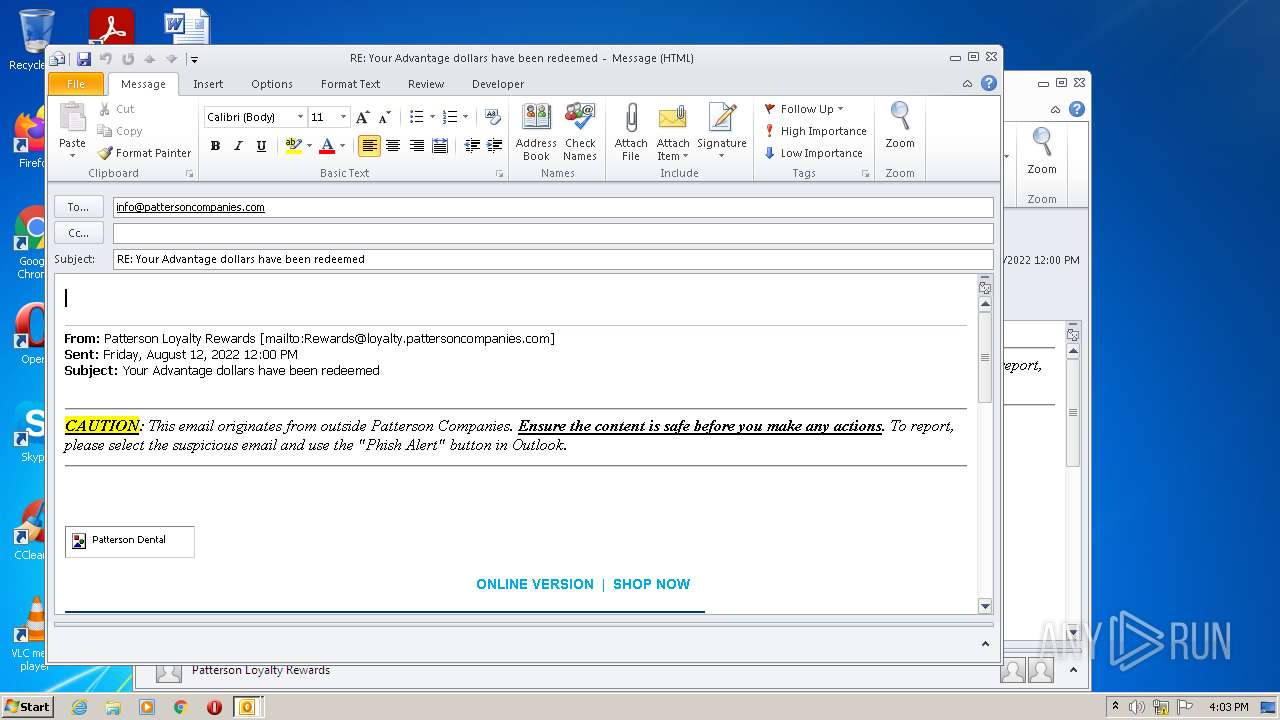
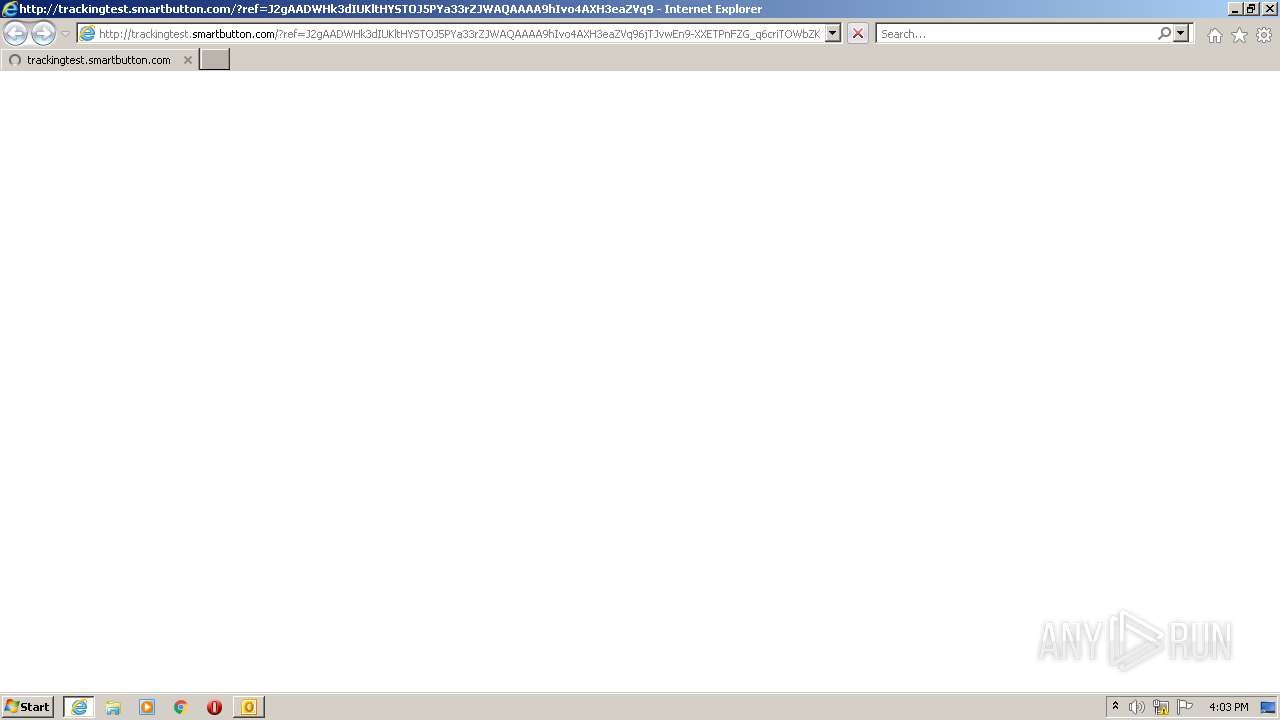
| 2676 | "C:\Program Files\Internet Explorer\iexplore.exe" http://trackingtest.smartbutton.com/?ref=J2gAADWHk3dIUKltHYSTOJ5PYa33rZJWAQAAAA9hIvo4AXH3eaZVq96jTJvwEn9-XXETPnFZG_q6criTOWbZKxrbko7TfPWMonrVVy0Ks0X5HT2xVA8K_jCcdc5jjek4uxUkOpoZrMbfT_IRdvVeNPYLH-2eg9zriVfB2GrP2CP0xtSHVb6R-WkSwSUnmFm717agekd2MOcuxctglVWBrbt37YOFWOogDWMnaQYwaYJftBeE6DcFI0i6TVjApBCtMUL6LkLS7fAKwUj_bII56rcoaZx82vCZDk0geA | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3332 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\phish_alert_sp2_2.0.0.0.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
18 897
Read events
18 213
Write events
656
Delete events
28
Modification events
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
17
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8444.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\logo_blue%20copy[1].png | image | |
MD5:— | SHA256:— | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_48AD483ABF78FE478949835320F05A28.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{F20D80AE-6F0B-4064-B1B9-10663B0EFAD4}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_68DF0798AC434D44A0F6D94772854C5A.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\l[1].gif | image | |
MD5:FF2EA3B92A9CDCB889BD2F7E44F4F34E | SHA256:4608A599D57A7E04349290E6F13722506B1F39D5B15F0C67D9108E302B6C4E0E | |||
| 3332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_0049C52D51EA264A8125EF0878EAF4C3.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
17
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
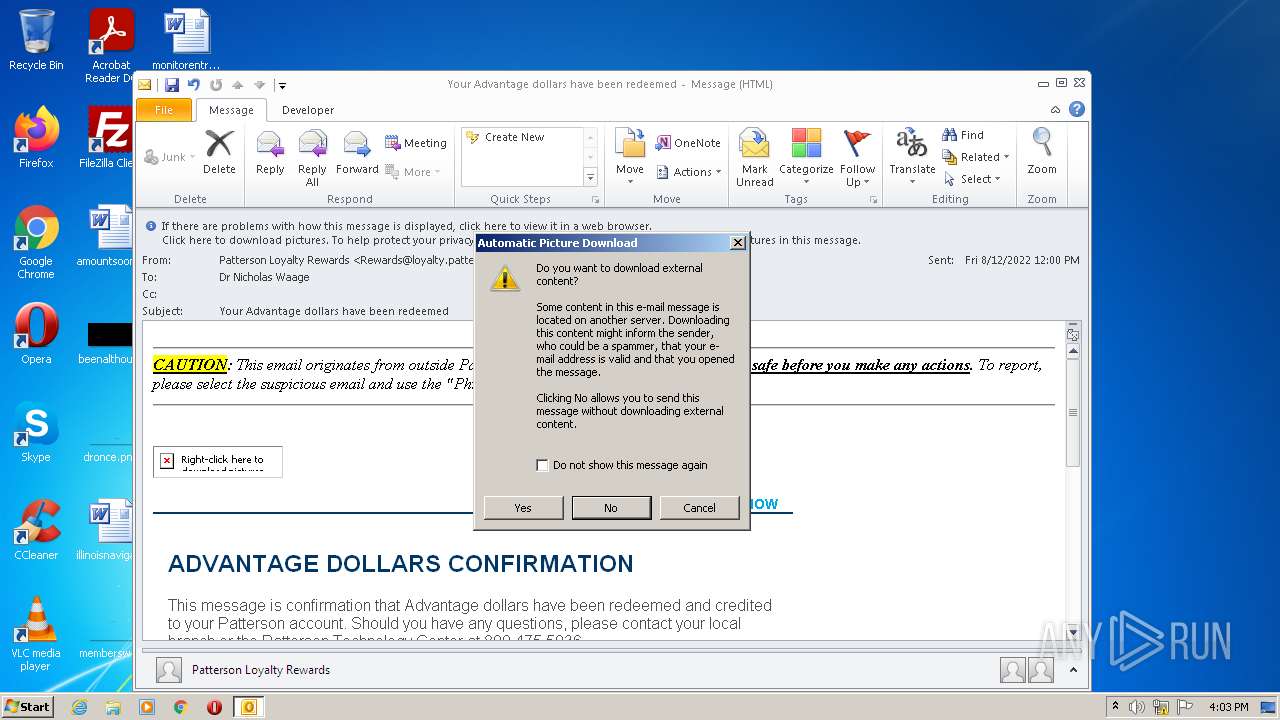
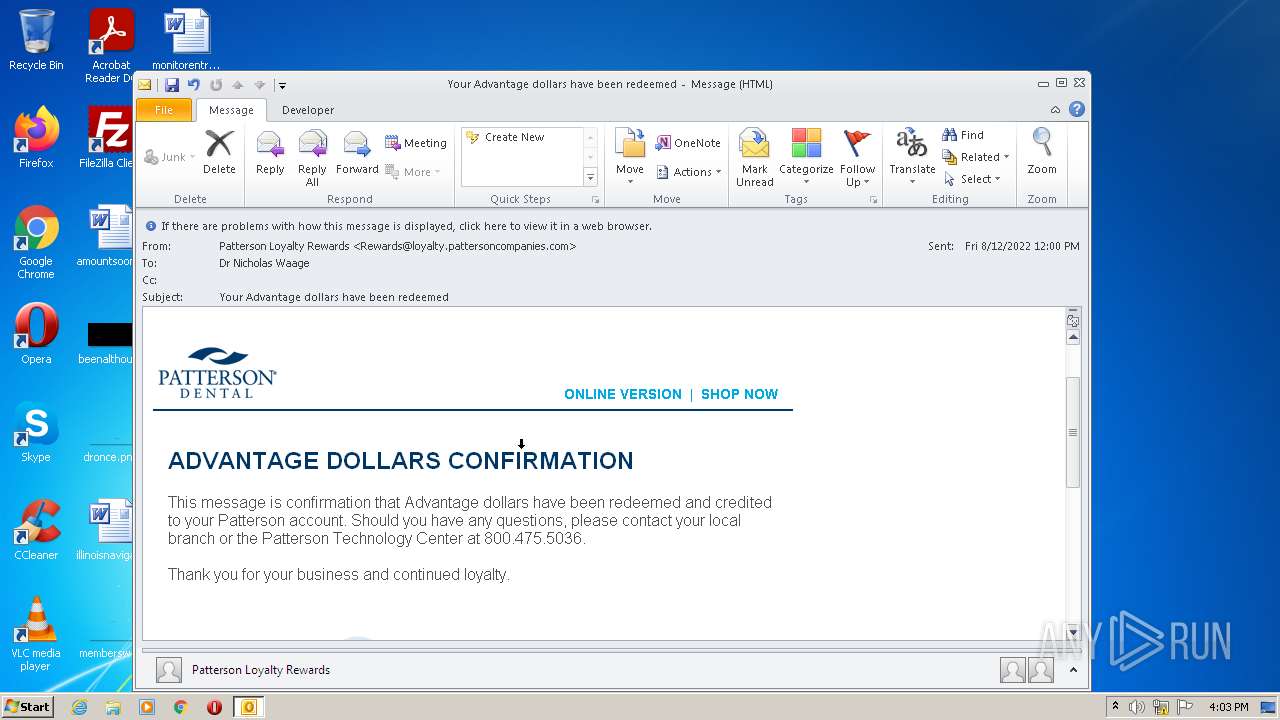
3332 | OUTLOOK.EXE | GET | 200 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/template/logo_blue%20copy.png | US | image | 31.5 Kb | unknown |
3332 | OUTLOOK.EXE | GET | 200 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/2018/Advantage/12.6%20Advantage%20Teaser%20email/19PD0337_TeaserEmail_Logo_r1.jpg?c=1545072196054 | US | image | 8.76 Kb | unknown |
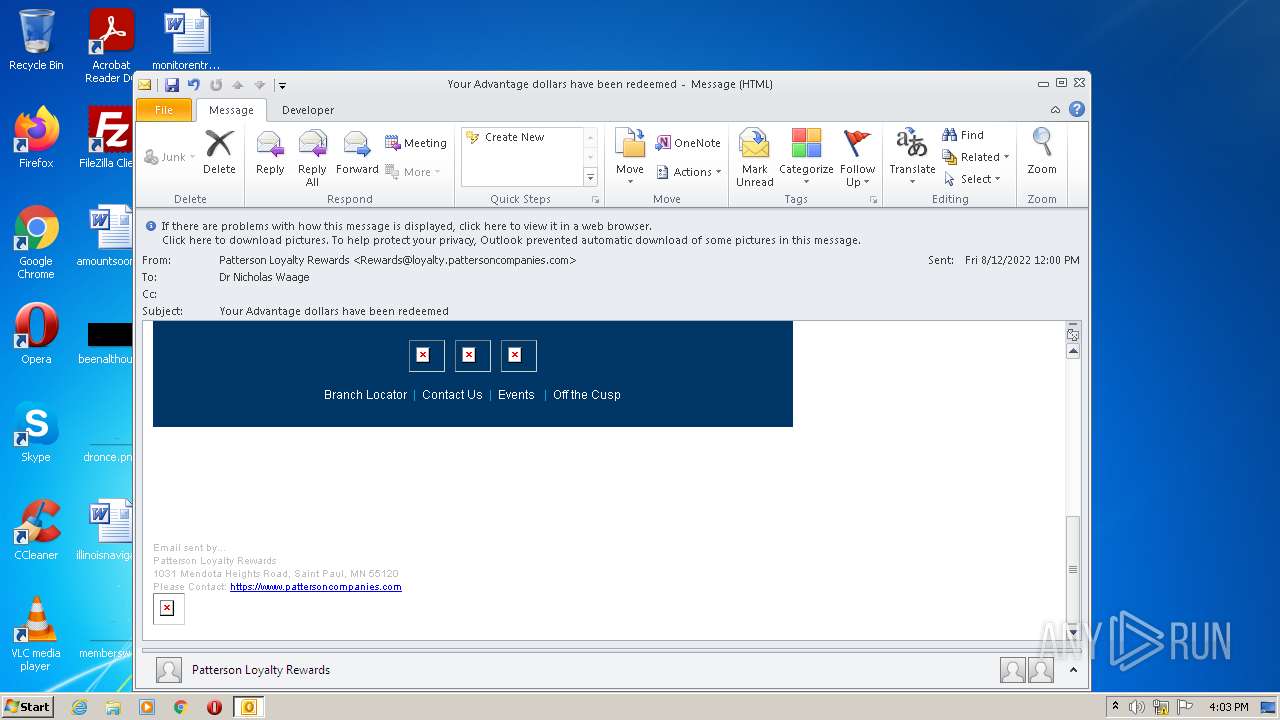
3332 | OUTLOOK.EXE | GET | 404 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/Dental_Template_2018/Facebook_icon.jpg | US | html | 249 b | unknown |
3332 | OUTLOOK.EXE | GET | 404 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/Dental_Template_2018/Twitter_icon.jpg | US | html | 248 b | unknown |
3332 | OUTLOOK.EXE | GET | 200 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/template/logo_blue%20copy.png | US | image | 31.5 Kb | unknown |
3332 | OUTLOOK.EXE | GET | 404 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/Dental_Template_2018/LinkedIn_icon.jpg | US | html | 249 b | unknown |
3332 | OUTLOOK.EXE | GET | 200 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/2018/Advantage/12.6%20Advantage%20Teaser%20email/19PD0337_TeaserEmail_Logo_r1.jpg?c=1545072196054 | US | image | 8.76 Kb | unknown |
3332 | OUTLOOK.EXE | GET | 404 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/Dental_Template_2018/Facebook_icon.jpg | US | html | 249 b | unknown |
3332 | OUTLOOK.EXE | GET | 304 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/template/logo_blue%20copy.png | US | html | 249 b | unknown |
3332 | OUTLOOK.EXE | GET | 404 | 216.27.63.5:80 | http://hosting-source.bm23.com/35394/public/Dental_Template_2018/LinkedIn_icon.jpg | US | html | 249 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | OUTLOOK.EXE | 216.27.63.5:80 | hosting-source.bm23.com | Tierpoint, LLC | US | unknown |
3332 | OUTLOOK.EXE | 142.0.190.16:80 | trackingtest.smartbutton.com | Mobilenetics Corporation | US | unknown |
2404 | iexplore.exe | 142.0.190.16:80 | trackingtest.smartbutton.com | Mobilenetics Corporation | US | unknown |
2404 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
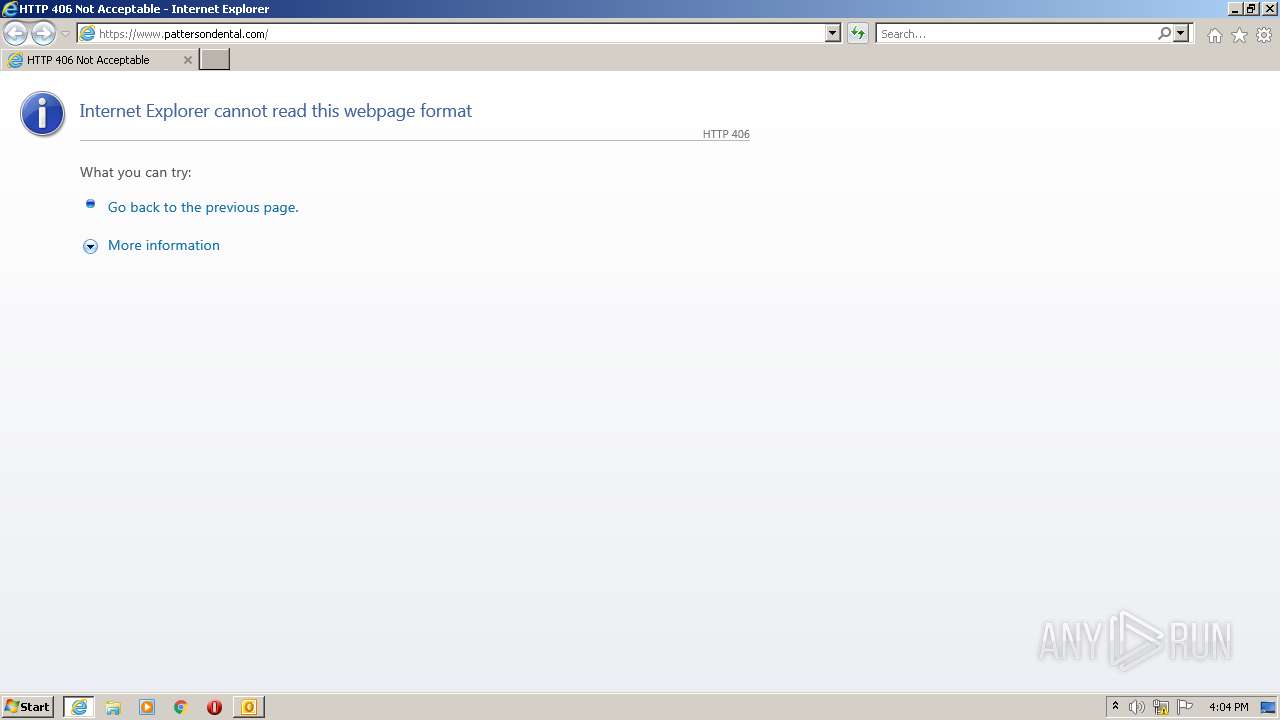
2404 | iexplore.exe | 204.231.241.161:443 | www.pattersondental.com | Patterson Companies, Inc. | US | unknown |
2404 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2676 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2676 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3332 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
hosting-source.bm23.com |
| unknown |
trackingtest.smartbutton.com |
| unknown |
www.pattersondental.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |