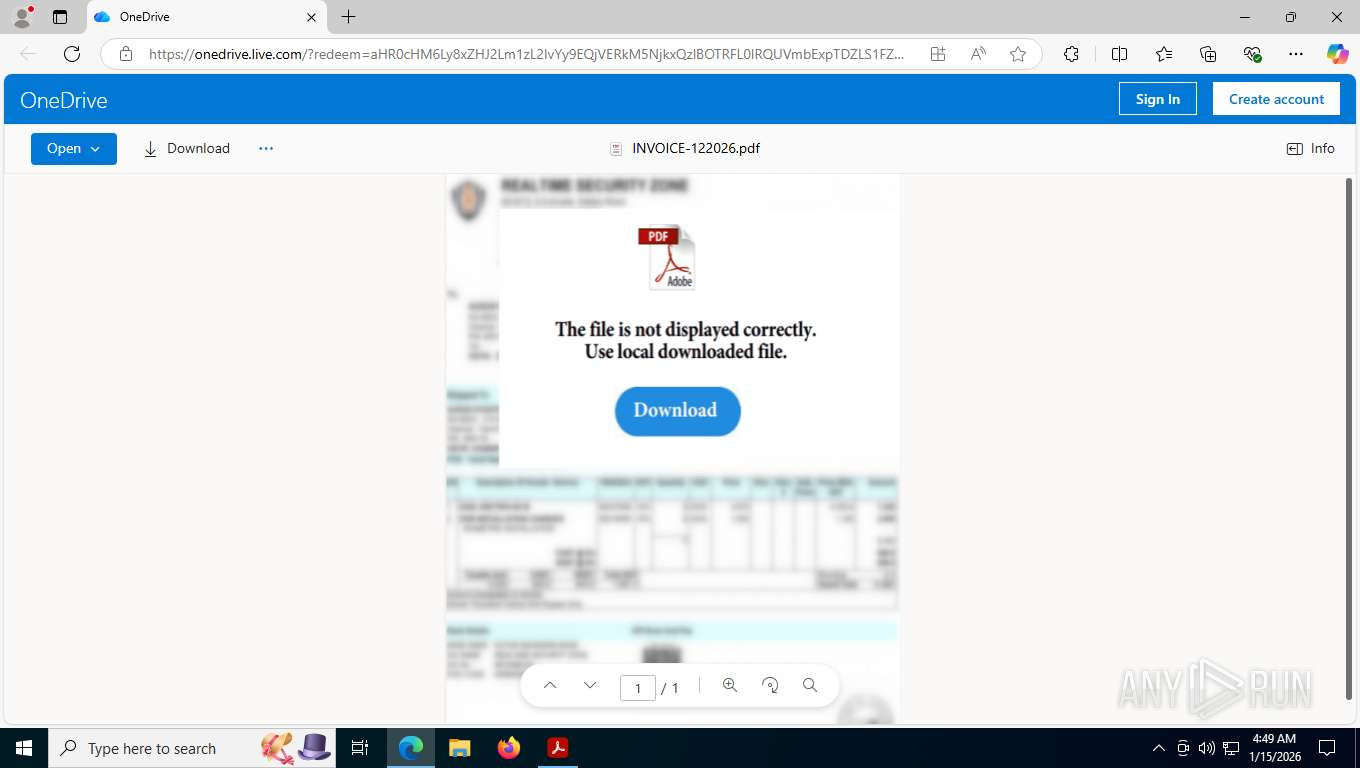
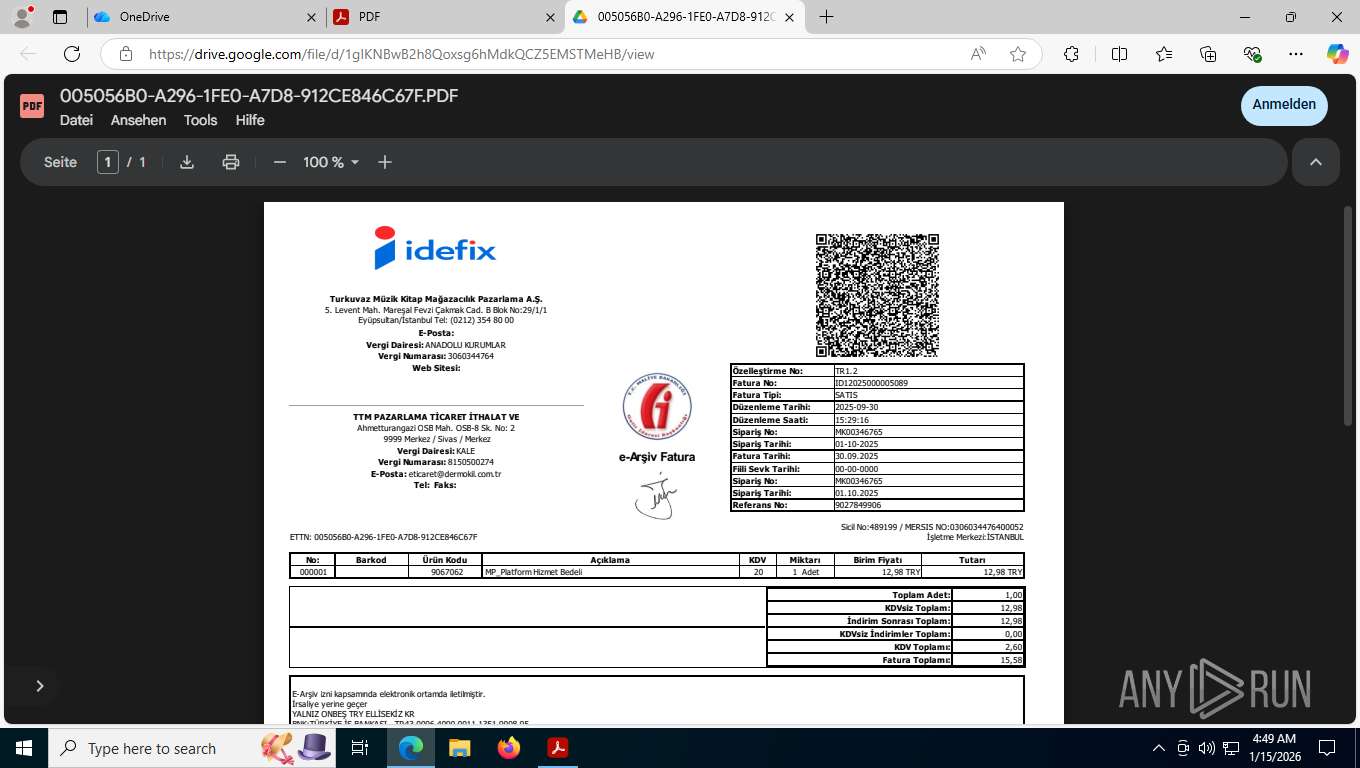
| File name: | INVOICE-122026.pdf |
| Full analysis: | https://app.any.run/tasks/58b99584-319a-48db-9b5a-c3cd4c092c5b |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2026, 09:48:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.5 |
| MD5: | 7CFFAA70D59C5D3FFDC4C746A90910B5 |
| SHA1: | 6875C5574238DB580F757D75EAD0AEDA5FF9D7A8 |
| SHA256: | 55F3A67197C383310A38B7CEE7653212CAB108F62963387B59FC0A0E6F064C89 |
| SSDEEP: | 3072:dRTkTlYKH+OnUsq9/GErSVvNolYwfFfFmRwOBIxfa:nTgljUsqnuVClX9F4tB |
MALICIOUS
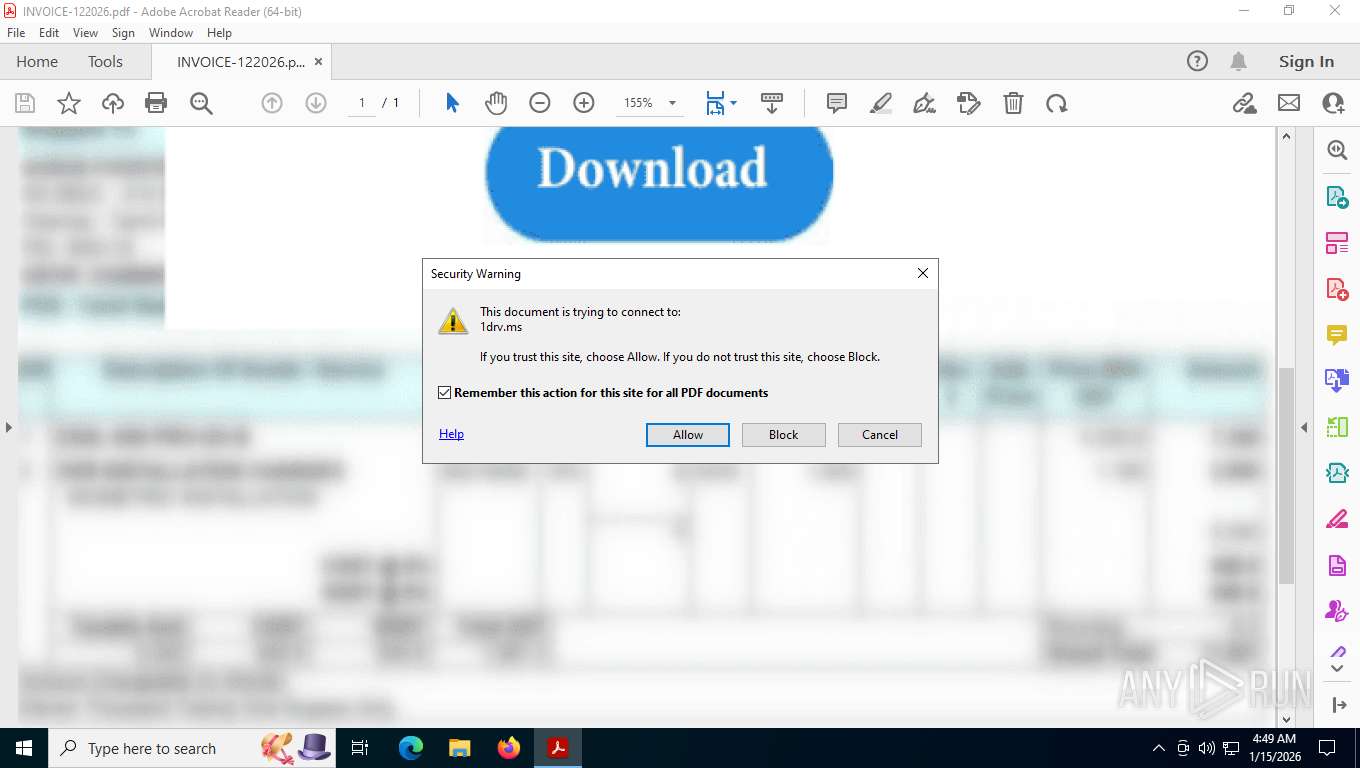
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 8480)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 8480)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 8480)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 8480)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 8480)
Changes the autorun value in the registry
- reg.exe (PID: 7180)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8480)
SUSPICIOUS
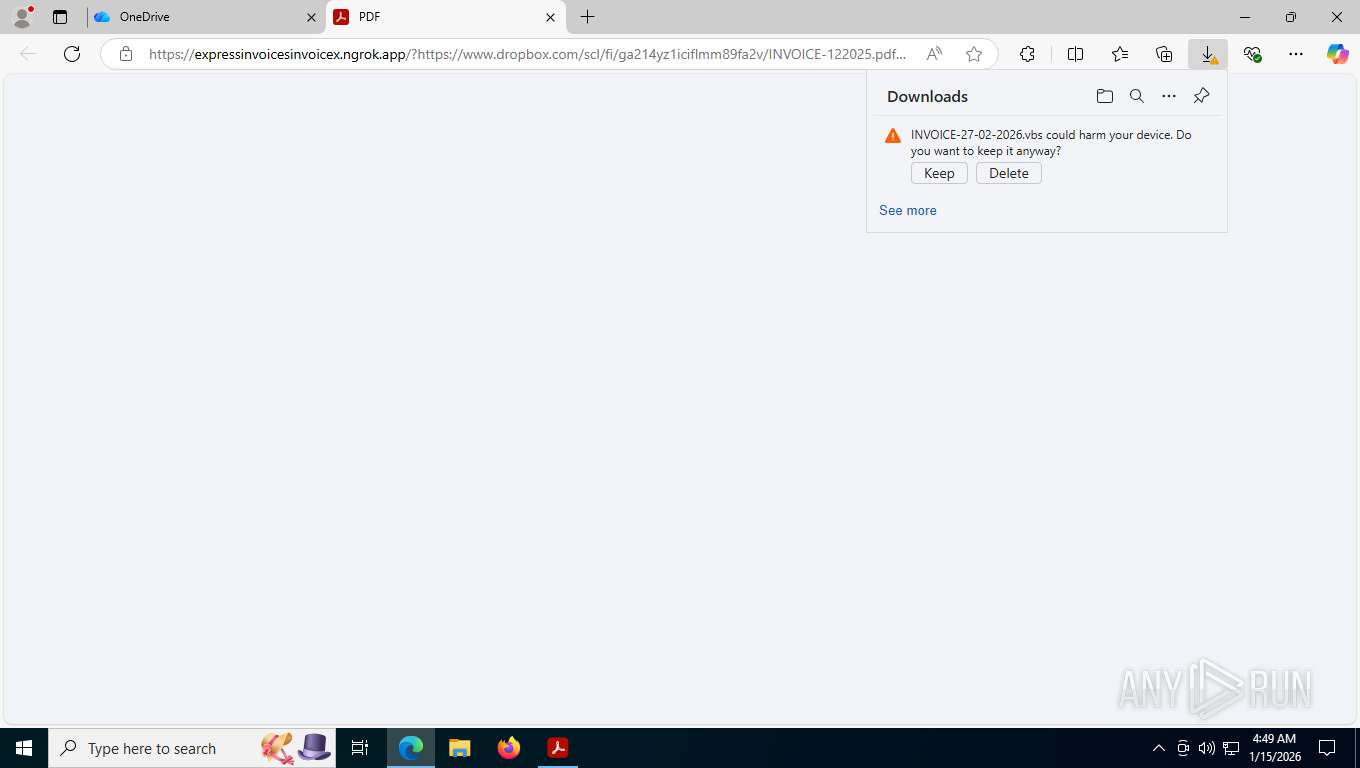
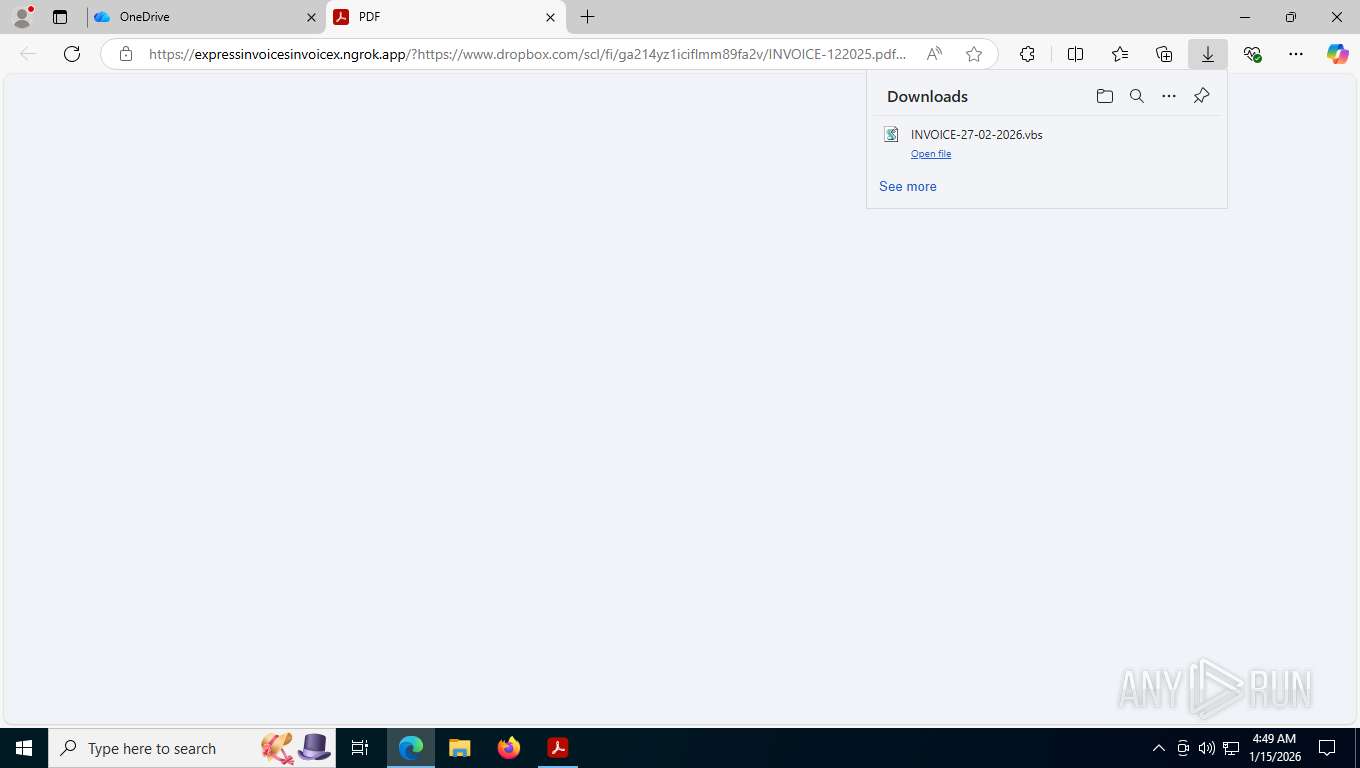
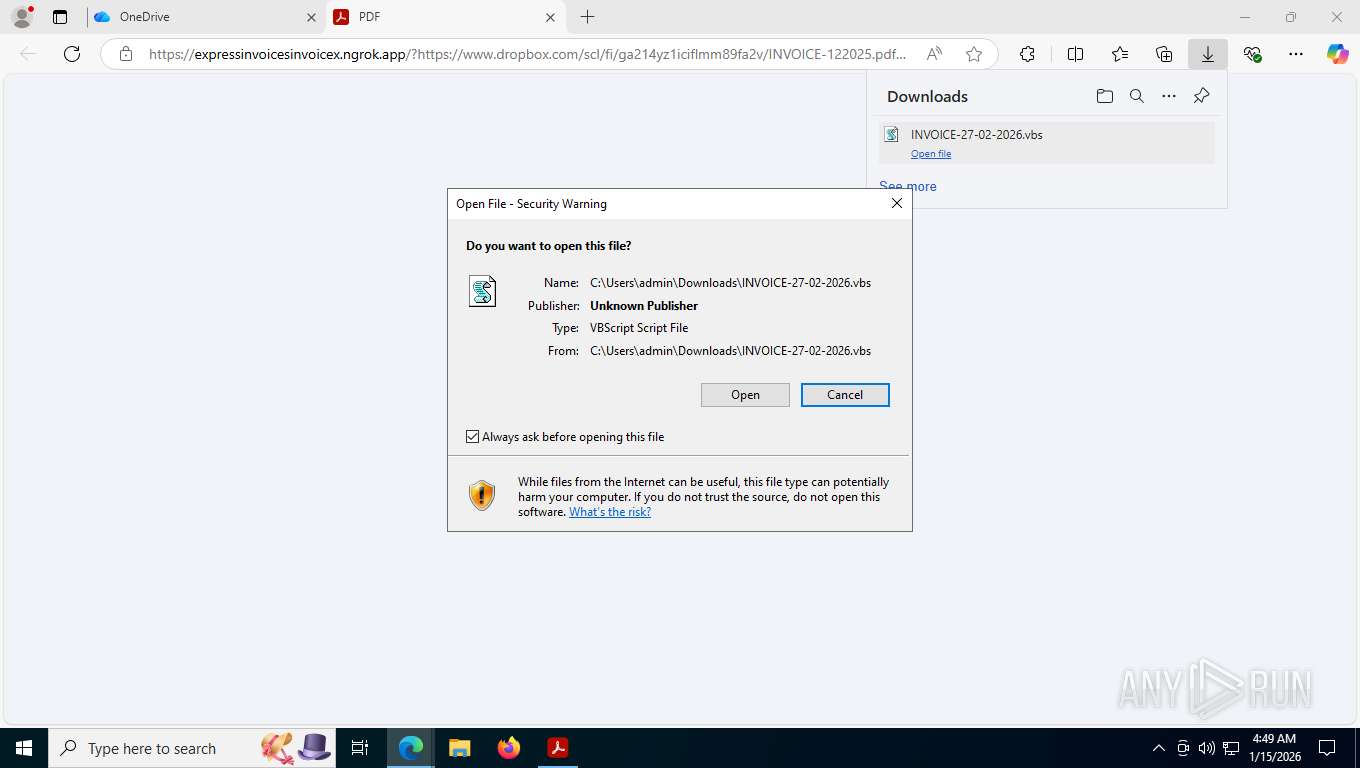
The process executes VB scripts
- msedge.exe (PID: 8112)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8480)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8480)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8480)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 8480)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 8480)
Creates a Folder object (SCRIPT)
- wscript.exe (PID: 8480)
Process drops legitimate windows executable
- wscript.exe (PID: 8480)
Executable content was dropped or overwritten
- wscript.exe (PID: 8480)
The process drops C-runtime libraries
- wscript.exe (PID: 8480)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8480)
- java.exe (PID: 8988)
Likely accesses (executes) a file from the Public directory
- java.exe (PID: 8988)
- cmd.exe (PID: 5080)
- reg.exe (PID: 7180)
- cmd.exe (PID: 8652)
Executing commands from ".cmd" file
- wscript.exe (PID: 8480)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5080)
Connects to unusual port
- java.exe (PID: 8988)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7552)
Uses WMIC.EXE to obtain Windows Installer data
- java.exe (PID: 8988)
INFO
Application launched itself
- Acrobat.exe (PID: 7576)
- AcroCEF.exe (PID: 7892)
- msedge.exe (PID: 8112)
Checks supported languages
- identity_helper.exe (PID: 8228)
- java.exe (PID: 8988)
Launching a file from the Downloads directory
- msedge.exe (PID: 8112)
Reads the computer name
- identity_helper.exe (PID: 8228)
- java.exe (PID: 8988)
Reads Environment values
- identity_helper.exe (PID: 8228)
Checks proxy server information
- wscript.exe (PID: 8480)
The sample compiled with english language support
- wscript.exe (PID: 8480)
Create files in a temporary directory
- java.exe (PID: 8988)
Creates files in the program directory
- java.exe (PID: 8988)
Creates files or folders in the user directory
- java.exe (PID: 8988)
Launching a file from a Registry key
- reg.exe (PID: 7180)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| Linearized: | No |
|---|---|
| PageCount: | 1 |
| HasXFA: | No |
| PDFVersion: | 1.5 |
| Producer: | 3.0.31 (5.1.15) |
| Author: | Test |
| CreateDate: | 2024:07:25 18:32:19 |
| ModifyDate: | 2026:01:15 04:07:26+01:00 |
Total processes
198
Monitored processes
53
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
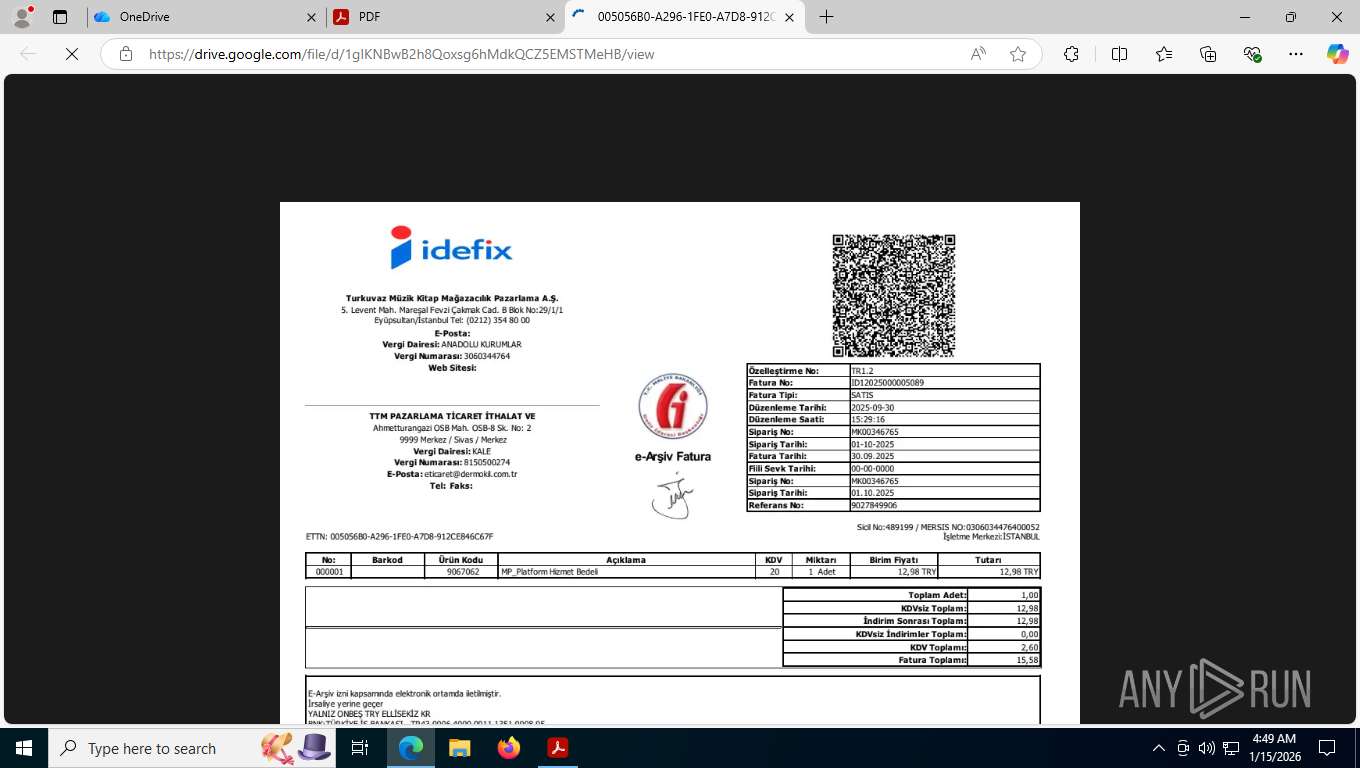
| 468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://drive.google.com/file/d/1gIKNBwB2h8Qoxsg6hMdkQCZ5EMSTMeHB/view?usp=sharing?invoice | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1784 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2272,i,8101974168089172053,5488960628447689688,262144 --variations-seed-version --mojo-platform-channel-handle=2252 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2256 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=21 --always-read-main-dll --field-trial-handle=7512,i,8101974168089172053,5488960628447689688,262144 --variations-seed-version --mojo-platform-channel-handle=5516 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=disabled --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1652 --field-trial-handle=1620,i,10970031951268056321,17674591705313312019,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Version: 23.1.20093.0 Modules
| |||||||||||||||
| 3112 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2336,i,8101974168089172053,5488960628447689688,262144 --variations-seed-version --mojo-platform-channel-handle=2444 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7748,i,8101974168089172053,5488960628447689688,262144 --variations-seed-version --mojo-platform-channel-handle=8136 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=5524,i,8101974168089172053,5488960628447689688,262144 --variations-seed-version --mojo-platform-channel-handle=7900 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5080 | cmd.exe /c "REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v AutoRunKey /d "C:\Users\Public\invoiceservice\bin\javaw.exe -jar C:\Users\admin\AppData\Roaming\DATA\1768470581456.png" /f" | C:\Windows\System32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 398
Read events
24 286
Write events
110
Delete events
2
Modification events
| (PID) Process: | (7576) Acrobat.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | DisplayName |
Value: Adobe Acrobat Reader Protected Mode | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVEntitlement |
| Operation: | write | Name: | bSynchronizeOPL |
Value: 0 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVGeneral |
| Operation: | write | Name: | uLastAppLaunchTimeStamp |
Value: | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVGeneral |
| Operation: | write | Name: | iNumAcrobatLaunches |
Value: 7 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\ToolsSearch |
| Operation: | write | Name: | iSearchHintIndex |
Value: 3 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bForms_AdhocWorkflowBackup |
Value: 0 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\DLLInjection |
| Operation: | write | Name: | bBlockDLLInjection |
Value: 0 | |||
| (PID) Process: | (7672) Acrobat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Adobe\Adobe Acrobat\DC\AVEntitlement |
| Operation: | write | Name: | sProductGUID |
Value: 4143524F4241545F475549445F4E474C5F44554D4D5900 | |||
Executable files
198
Suspicious files
390
Text files
217
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt23.lst.7672 | binary | |
MD5:366B140BAFC863B7E366AA1E51604759 | SHA256:CBC8B288DBD2C72432081CF33CEF431572A94C7FB89DBCD59973B99E3871814E | |||
| 7672 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\SOPHIA.json | text | |
MD5:837C1211E392A24D64C670DC10E8DA1B | SHA256:8013AC030684B86D754BBFBAB8A9CEC20CAA4DD9C03022715FF353DC10E14031 | |||
| 7892 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Local Storage\leveldb\LOG.old~RFfed64.TMP | text | |
MD5:ED7D8AAE48211E2BFAF557130572C62A | SHA256:A5CF8D8ADC86DCA357396AF7E3A24A116072D5C1E5552EEB76601AE2673DED6E | |||
| 7576 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeSysFnt23.lst | binary | |
MD5:366B140BAFC863B7E366AA1E51604759 | SHA256:CBC8B288DBD2C72432081CF33CEF431572A94C7FB89DBCD59973B99E3871814E | |||
| 7672 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\TESTING | binary | |
MD5:DC84B0D741E5BEAE8070013ADDCC8C28 | SHA256:81FF65EFC4487853BDB4625559E69AB44F19E0F5EFBD6D5B2AF5E3AB267C8E06 | |||
| 7892 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Session Storage\LOG.old | text | |
MD5:EB1590F2607E1CE46DBF6A521F772EA0 | SHA256:4355D9A8A115BA4E41178B456A8A5578846EB1F7EC9509249C2405F758F31731 | |||
| 7672 | Acrobat.exe | C:\Users\admin\AppData\Local\Temp\acrobat_sbx\NGL\NGLClient_AcrobatReader123.1.20093.6 2026-01-15 04-48-59-172.log | text | |
MD5:460C6041966002D8384A18C895A65EB0 | SHA256:C83EC6E8FB3EC62481289C033238C1D9B08DB8076EAAD304099FD7A7F594F1B9 | |||
| 7672 | Acrobat.exe | C:\Users\admin\AppData\Local\Temp\acrobat_sbx\acroNGLLog.txt | text | |
MD5:698FF64F5970781685A569C33B309835 | SHA256:035A8FD8A2EA34FEEC68B7156FA20B1B897A2437F6606BFCC3E067959591340F | |||
| 7892 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Session Storage\LOG.old~RFfed74.TMP | text | |
MD5:7383516745DEC1E86152192435F92D1F | SHA256:E22D34BBD915EEB277D4F4138D176EACE5577CF035EF7C2C80A4BC4D9B6C0E1D | |||
| 7892 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\LOG.old~RFfeb12.TMP | text | |
MD5:D012E5B4EB91B61F6E8AE2F8EC3C623E | SHA256:1BDA750084F20306722008016420E1912BA608CA8EFB9C661F7E7EFCF5E89673 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
339
TCP/UDP connections
128
DNS requests
138
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3112 | msedge.exe | GET | 301 | 150.171.22.11:443 | https://1drv.ms/b/c/DB5DFC9691C9A94E/IQAEflLiL6KKQYYwouHN9jTGAXdQQl3-t3yUBLfSU04s_xM?e=cfLcjL | unknown | — | — | unknown |
1164 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1164 | svchost.exe | POST | 200 | 20.190.160.22:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
1948 | svchost.exe | GET | 200 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | text | 5.58 Kb | whitelisted |
1164 | svchost.exe | POST | 200 | 20.190.160.22:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
3112 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
3112 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
3112 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | text | 892 b | whitelisted |
3112 | msedge.exe | GET | 302 | 13.107.137.11:443 | https://onedrive.live.com/redir?cid=DB5DFC9691C9A94E&resid=DB5DFC9691C9A94E!se2527e04a22f418a8630a2e1cdf634c6&ithint=file%2cpdf&e=cfLcjL&migratedtospo=true&redeem=aHR0cHM6Ly8xZHJ2Lm1zL2IvYy9EQjVERkM5NjkxQzlBOTRFL0lRQUVmbExpTDZLS1FZWXdvdUhOOWpUR0FYZFFRbDMtdDN5VUJMZlNVMDRzX3hNP2U9Y2ZMY2pM | unknown | html | 450 b | whitelisted |
3112 | msedge.exe | GET | 200 | 13.107.137.11:443 | https://onedrive.live.com/?cid=db5dfc9691c9a94e&id=DB5DFC9691C9A94E!se2527e04a22f418a8630a2e1cdf634c6&resid=DB5DFC9691C9A94E!se2527e04a22f418a8630a2e1cdf634c6&ithint=file,pdf&e=cfLcjL&migratedtospo=true&redeem=aHR0cHM6Ly8xZHJ2Lm1zL2IvYy9EQjVERkM5NjkxQzlBOTRFL0lRQUVmbExpTDZLS1FZWXdvdUhOOWpUR0FYZFFRbDMtdDN5VUJMZlNVMDRzX3hNP2U9Y2ZMY2pM | unknown | html | 128 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1948 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1136 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8084 | AcroCEF.exe | 88.221.168.141:443 | geo2.adobe.com | AKAMAI-AS | US | whitelisted |
8084 | AcroCEF.exe | 18.213.11.84:443 | p13n.adobe.io | AMAZON-AES | US | whitelisted |
1164 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1164 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
1drv.ms |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3112 | msedge.exe | Misc activity | ET INFO Observed DNS Query to *.ngrok Domain (ngrok .app) |
3112 | msedge.exe | Misc activity | ET INFO Observed DNS Query to *.ngrok Domain (ngrok .app) |
3112 | msedge.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (ngrok .app) in TLS SNI |
3112 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Request to load WebAssembly module |
2292 | svchost.exe | Misc activity | ET INFO Observed DNS Query to *.ngrok Domain (ngrok .app) |
8480 | wscript.exe | Misc activity | ET INFO Observed Network Tunneling Service Domain (ngrok .app) in TLS SNI |
— | — | A Network Trojan was detected | ET MALWARE Possible Malicious Invoice EXE |
— | — | Misc activity | ET INFO Observed UA-CPU Header |