| File name: | 55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a |
| Full analysis: | https://app.any.run/tasks/03b61f51-e86f-4f97-8868-234239240073 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 01:28:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 68C916013CCF156AAA684340FAFD70AC |
| SHA1: | 045EFCB6279B8FC6FD2D5E0F7DF36121CE6DA720 |
| SHA256: | 55CDD4E7299B3BF8930087494B6B2FDFF60EA62B9C8D201797C7284767D7A98A |
| SSDEEP: | 49152:sdcgTVBPthrYm1BjhpTglY5HIZ0DQvS1Xgd5:sdcgTDrYmppTglYqFvgQd5 |
MALICIOUS
Changes the login/logoff helper path in the registry
- errorResponder.exe (PID: 2800)
SUSPICIOUS
Creates files in the program directory
- 55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe (PID: 3272)
Starts itself from another location
- 55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe (PID: 3272)
Executable content was dropped or overwritten
- 55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe (PID: 3272)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:19 11:42:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 24576 |
| InitializedDataSize: | 51200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x42a000 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Apr-2020 09:42:51 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 19-Apr-2020 09:42:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x0000A000 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95102 | |
.rsrc | 0x0000B000 | 0x00009B8E | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.84123 |
.idata | 0x00015000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.30872 |
0x00016000 | 0x0027E000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.251484 | |
haufgyfn | 0x00294000 | 0x00196000 | 0x00195800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92911 |
vzoaupnr | 0x0042A000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03734 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28794 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.35004 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.10795 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 4.36124 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 4.91149 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 4.97199 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 3.01287 | 21410 | UNKNOWN | English - United States | RT_ICON |
8 | 5.58588 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 5.66158 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
comctl32.dll |
kernel32.dll |
Total processes
42
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2800 | C:\ProgramData\ErrorResponder\errorResponder.exe "C:\Users\admin\AppData\Local\Temp\55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe" ensgJJ | C:\ProgramData\ErrorResponder\errorResponder.exe | 55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe" | C:\Users\admin\AppData\Local\Temp\55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\AppData\Local\Temp\55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe" | C:\Users\admin\AppData\Local\Temp\55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
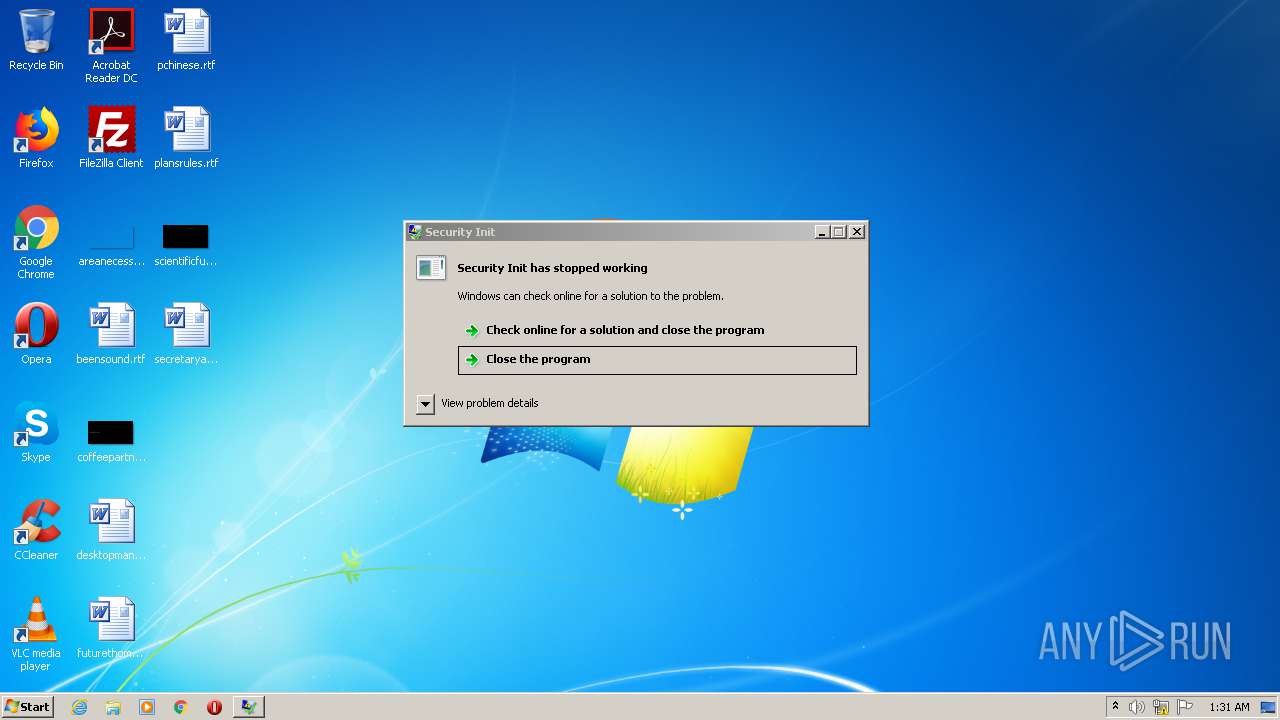
| 3572 | C:\ProgramData\ErrorResponder\errorResponder.exe | C:\Windows\system32\secinit.exe | errorResponder.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Security Init Exit code: 3221225622 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
22
Read events
21
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2800) errorResponder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe, "C:\ProgramData\ErrorResponder\errorResponder.exe" | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | 55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe | C:\ProgramData\ErrorResponder\errorResponder.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
13
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
burload01.top |
| unknown |
burload02.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
Process | Message |
|---|---|
55cdd4e7299b3bf8930087494b6b2fdff60ea62b9c8d201797c7284767d7a98a.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
errorResponder.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|