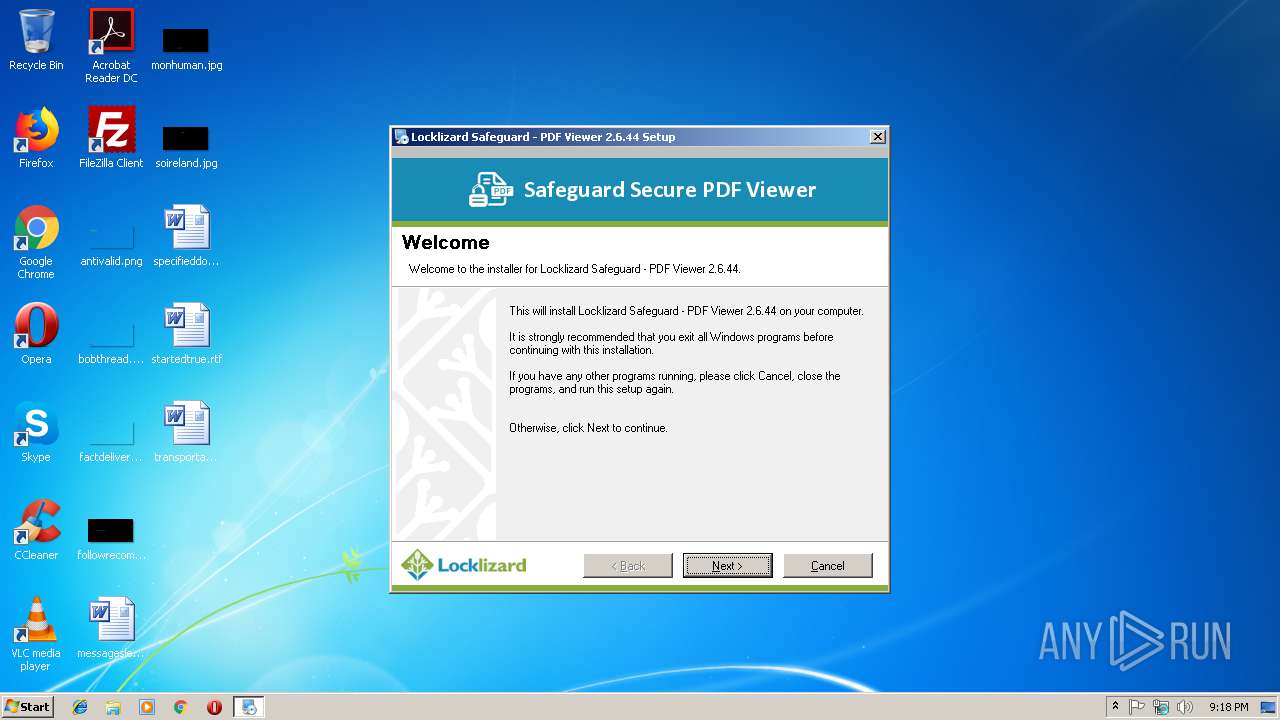
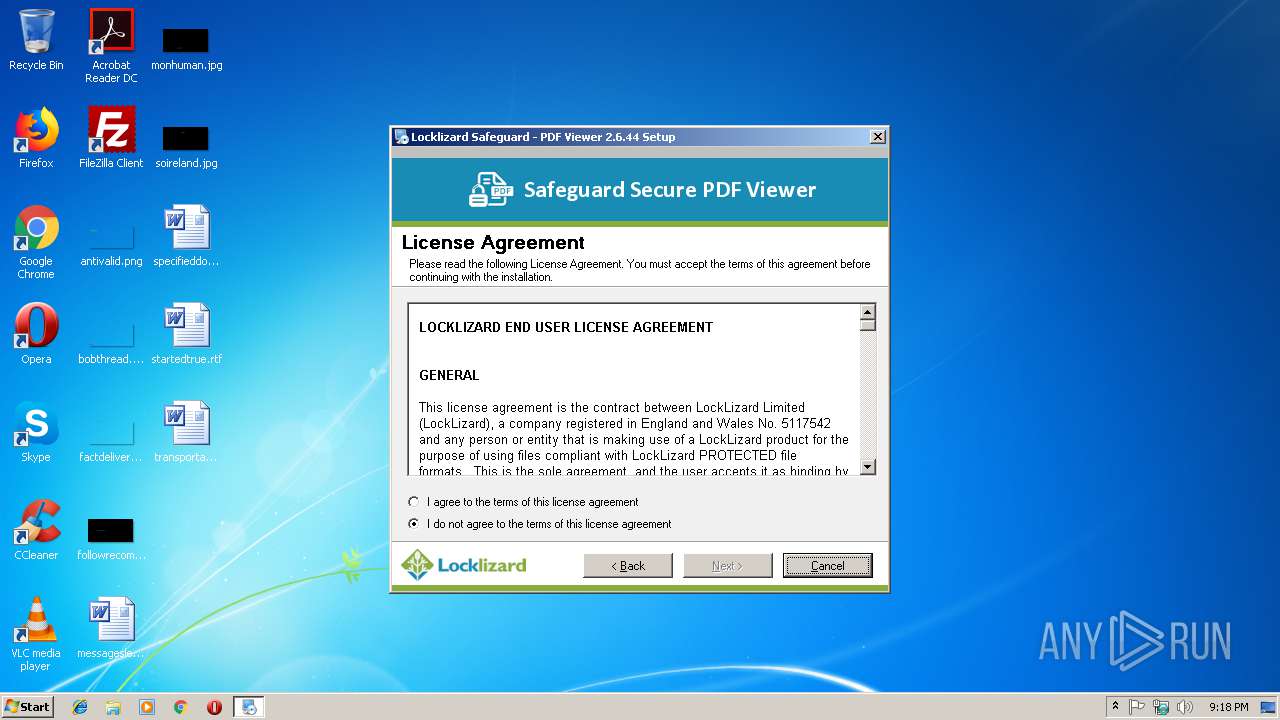
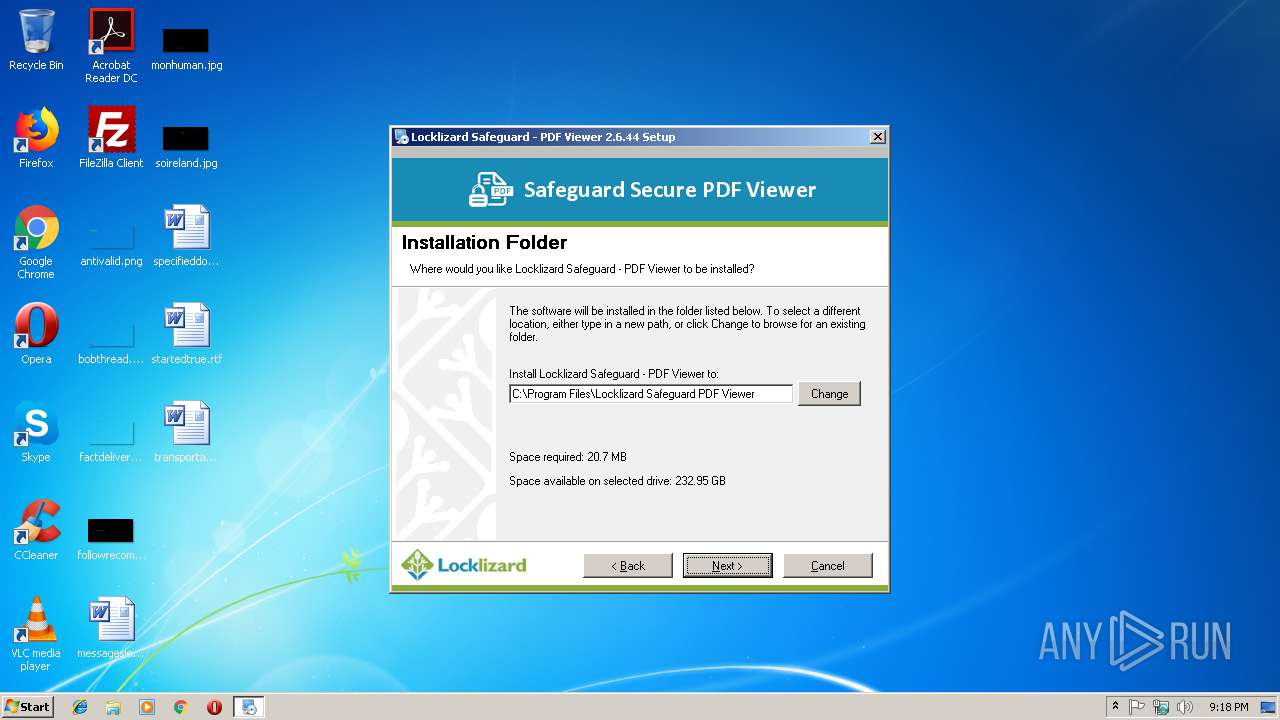
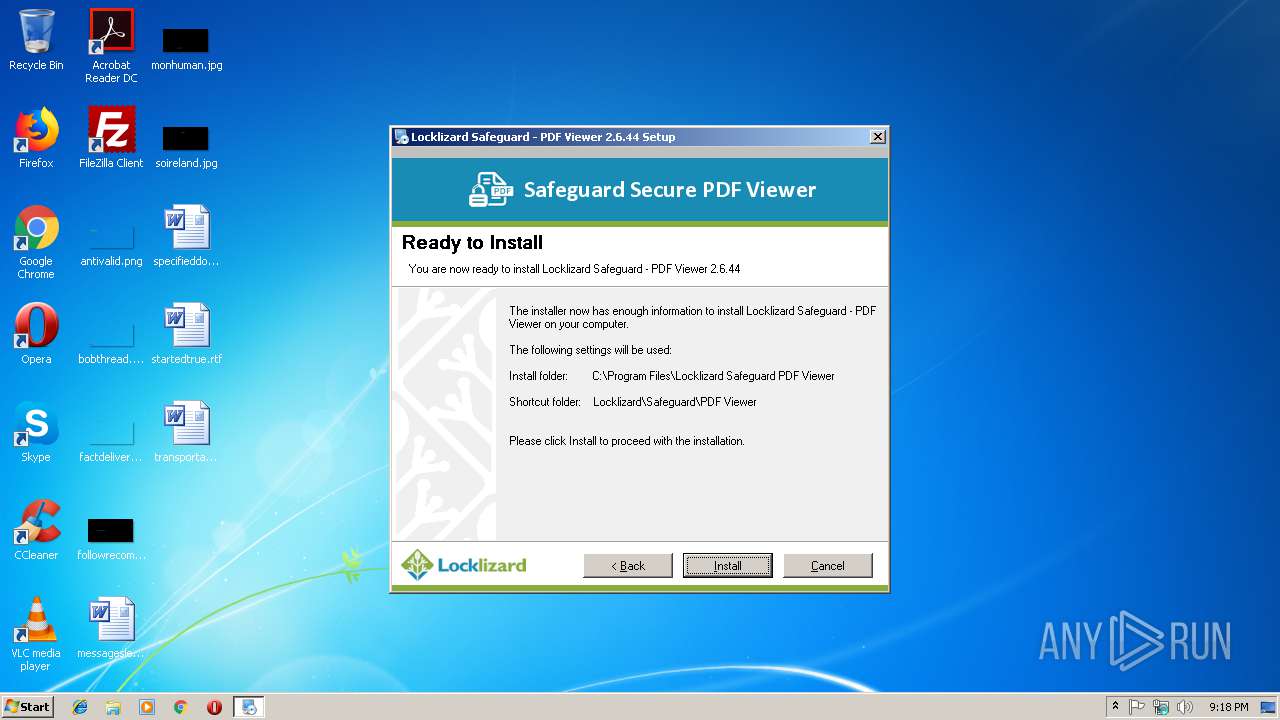
| download: | SafeguardPDFViewer.exe |
| Full analysis: | https://app.any.run/tasks/bf777938-ffb9-4a7a-bced-42ef536f02b3 |
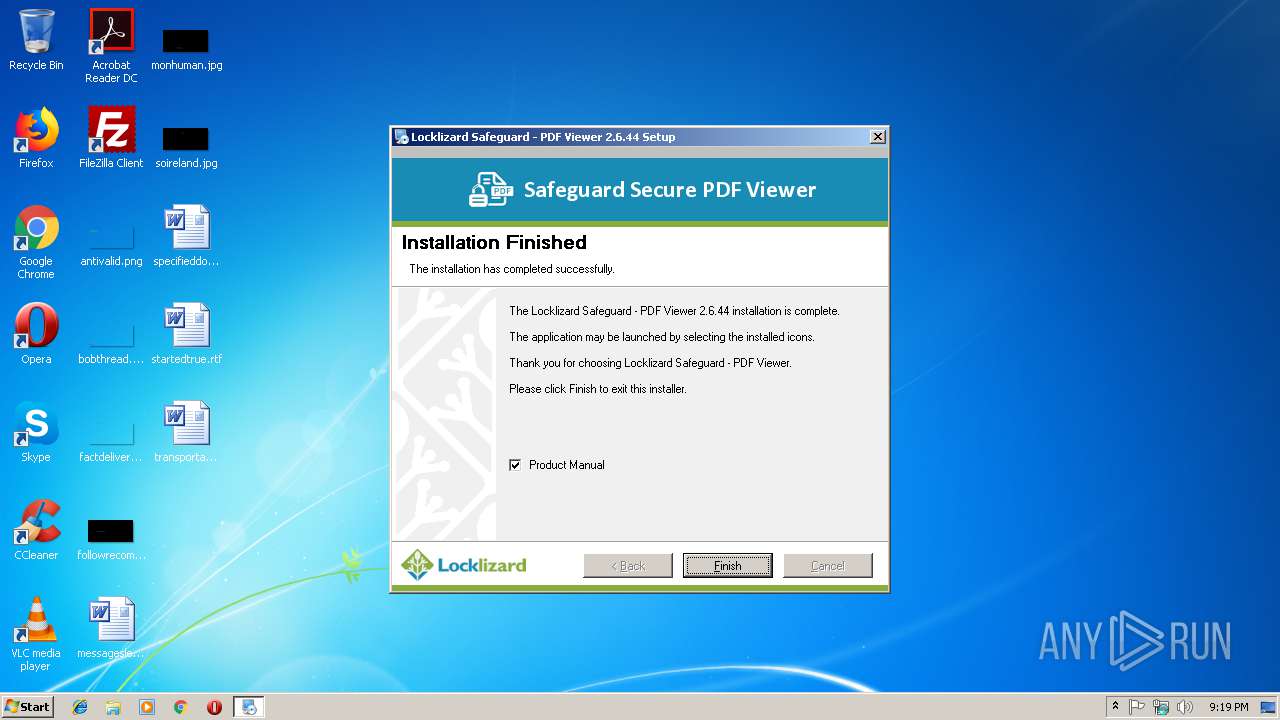
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2018, 21:18:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B838C8D96387F57C807ECD2924335066 |
| SHA1: | 965910048AD06E82CD36F091980547B8F322EBDF |
| SHA256: | 55AD6422D1F1AE91300127E666DC6C8ACDA5D33B6BE2B6443FFF8A27FEE9420E |
| SSDEEP: | 393216:1p0AgF7UFl5RGPhuJcIBHLwQfSAQk/hqPYUlsmHKg8:rgF7UFrRGJecIJ0QfJQk/APY+HKg8 |
MALICIOUS
Loads dropped or rewritten executable
- irsetup.exe (PID: 4072)
- regsvr32.exe (PID: 3992)
Application was dropped or rewritten from another process
- irsetup.exe (PID: 4072)
Registers / Runs the DLL via REGSVR32.EXE
- irsetup.exe (PID: 4072)
SUSPICIOUS
Executable content was dropped or overwritten
- irsetup.exe (PID: 4072)
- SafeguardPDFViewer.exe (PID: 2852)
Reads internet explorer settings
- irsetup.exe (PID: 4072)
Creates COM task schedule object
- regsvr32.exe (PID: 3992)
Creates a software uninstall entry
- irsetup.exe (PID: 4072)
Modifies the open verb of a shell class
- irsetup.exe (PID: 4072)
Creates files in the program directory
- irsetup.exe (PID: 4072)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:02:26 19:08:50+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 22528 |
| InitializedDataSize: | 48640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29f1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.6.44.0 |
| ProductVersionNumber: | 2.6.44.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.locklizard.com |
| CompanyName: | Locklizard |
| FileDescription: | Locklizard Safeguard - PDF Viewer |
| FileVersion: | 2.6.44.0 |
| InternalName: | PDCViewerSetup |
| LegalCopyright: | Copyright © 2014 Locklizard |
| LegalTrademarks: | http://www.locklizard.com |
| OriginalFileName: | suf_launch.exe |
| ProductName: | Locklizard Safeguard - PDF Viewer |
| ProductVersion: | 2.6.44.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Feb-2016 18:08:50 |
| Detected languages: |
|
| Comments: | http://www.locklizard.com |
| CompanyName: | Locklizard |
| FileDescription: | Locklizard Safeguard - PDF Viewer |
| FileVersion: | 2.6.44.0 |
| InternalName: | PDCViewerSetup |
| LegalCopyright: | Copyright © 2014 Locklizard |
| LegalTrademarks: | http://www.locklizard.com |
| OriginalFilename: | suf_launch.exe |
| ProductName: | Locklizard Safeguard - PDF Viewer |
| ProductVersion: | 2.6.44.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Feb-2016 18:08:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005728 | 0x00005800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46549 |
.rdata | 0x00007000 | 0x00002E82 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97407 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.58269 |
.rsrc | 0x0000C000 | 0x00006E8C | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87272 |
.reloc | 0x00013000 | 0x00001094 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.72353 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.36998 | 1425 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.31421 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.9477 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.78233 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.14953 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.83714 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.64397 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.84115 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.41049 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.89097 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2852 | "C:\Users\admin\AppData\Local\Temp\SafeguardPDFViewer.exe" | C:\Users\admin\AppData\Local\Temp\SafeguardPDFViewer.exe | explorer.exe | ||||||||||||
User: admin Company: Locklizard Integrity Level: HIGH Description: Locklizard Safeguard - PDF Viewer Exit code: 0 Version: 2.6.44.0 Modules
| |||||||||||||||
| 3992 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Locklizard Safeguard PDF Viewer\IShellPropSheet.dll" | C:\Windows\system32\regsvr32.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | "C:\Users\admin\AppData\Local\Temp\SafeguardPDFViewer.exe" | C:\Users\admin\AppData\Local\Temp\SafeguardPDFViewer.exe | — | explorer.exe | |||||||||||
User: admin Company: Locklizard Integrity Level: MEDIUM Description: Locklizard Safeguard - PDF Viewer Exit code: 3221226540 Version: 2.6.44.0 Modules
| |||||||||||||||
| 4072 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1802394 "__IRAFN:C:\Users\admin\AppData\Local\Temp\SafeguardPDFViewer.exe" "__IRCT:3" "__IRTSS:16049976" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | SafeguardPDFViewer.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.1.0 Modules
| |||||||||||||||
Total events
598
Read events
535
Write events
61
Delete events
2
Modification events
| (PID) Process: | (2852) SafeguardPDFViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2852) SafeguardPDFViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018110920181110 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018110920181110 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018110920181110 |
| Operation: | write | Name: | CachePrefix |
Value: :2018110920181110: | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018110920181110 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018110920181110 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018110920181110 |
| Operation: | write | Name: | CacheRepair |
Value: 0 | |||
| (PID) Process: | (4072) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018082720180903 |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
21
Suspicious files
1
Text files
52
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Program Files\Locklizard Safeguard PDF Viewer\Uninstall Viewer\uni7153.tmp | — | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Program Files\Locklizard Safeguard PDF Viewer\Uninstall Viewer\uninstall.dat | — | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG1.PNG | image | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG2.PNG | image | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018110920181110\index.dat | dat | |
MD5:— | SHA256:— | |||
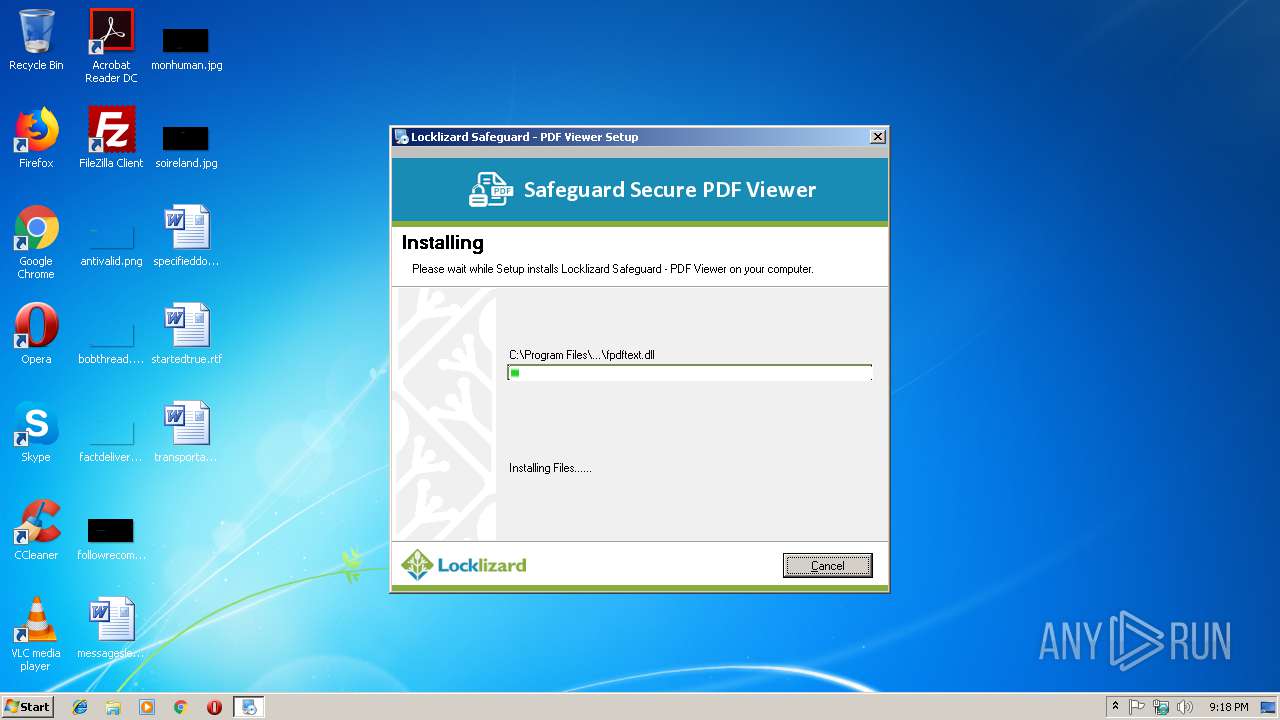
| 4072 | irsetup.exe | C:\Program Files\Locklizard Safeguard PDF Viewer\fpdftext.dll | executable | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Program Files\Locklizard Safeguard PDF Viewer\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Program Files\Locklizard Safeguard PDF Viewer\Helpus.dll | executable | |
MD5:— | SHA256:— | |||
| 4072 | irsetup.exe | C:\Program Files\Locklizard Safeguard PDF Viewer\hdl.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report