| File name: | 在线工具包.exe |
| Full analysis: | https://app.any.run/tasks/7308cd1a-b4e9-4a90-8706-0168f52a2744 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2020, 13:47:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 1E7EF0FBE9DC5468A41A0F00C0CBC54D |
| SHA1: | 8BE548C3C5C79B1A55E2927F90AFFA2ED9805193 |
| SHA256: | 559D6BF7529B1EABFA9DF65A5C1CDAB19CEAA3305146BF82D81FFA00568F5D6C |
| SSDEEP: | 49152:nME4yKP7QZu19hKSJ3KaAVYh0mJ8RGDa4qE3dVb:MEbKP0ZuXAVYh0m7DaWPb |
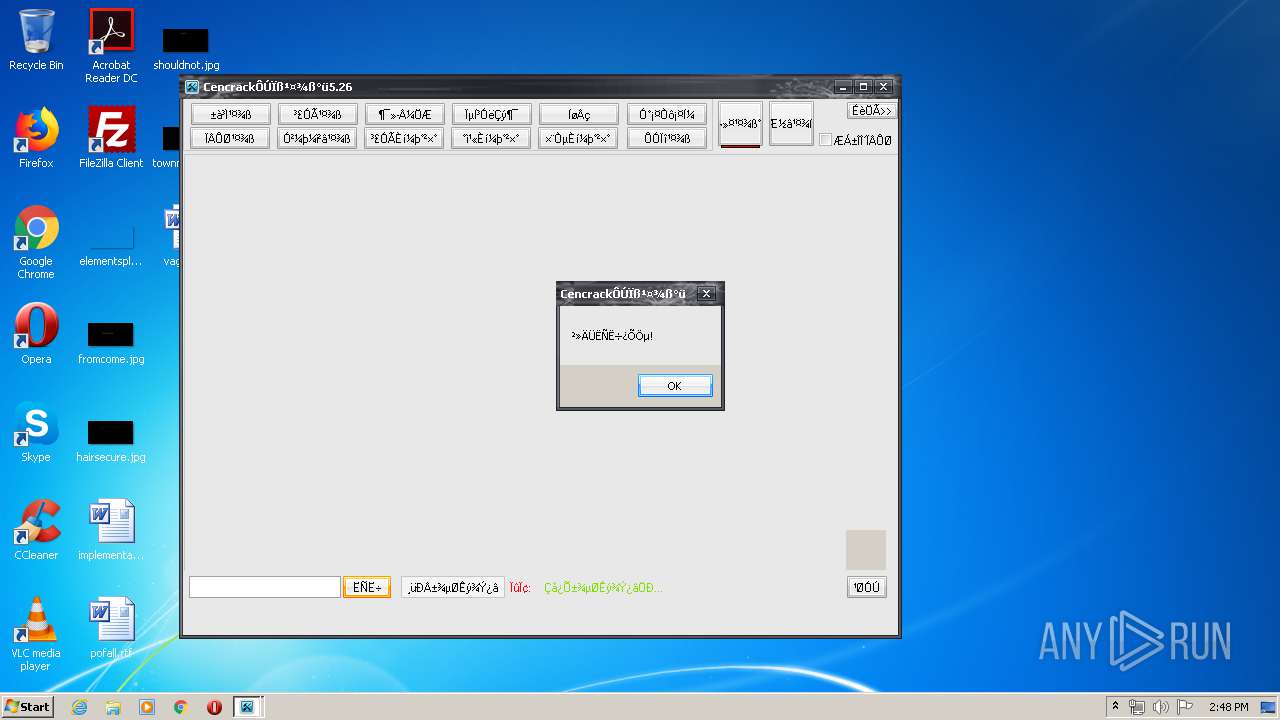
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 4036)
- 在线工具包.exe (PID: 3720)
Actions looks like stealing of personal data
- SearchProtocolHost.exe (PID: 4036)
- 在线工具包.exe (PID: 3720)
SUSPICIOUS
Executable content was dropped or overwritten
- 在线工具包.exe (PID: 3720)
Reads Internet Cache Settings
- 在线工具包.exe (PID: 3720)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:20 03:22:43+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 2170880 |
| InitializedDataSize: | 323584 |
| UninitializedDataSize: | 2863104 |
| EntryPoint: | 0x4cd010 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
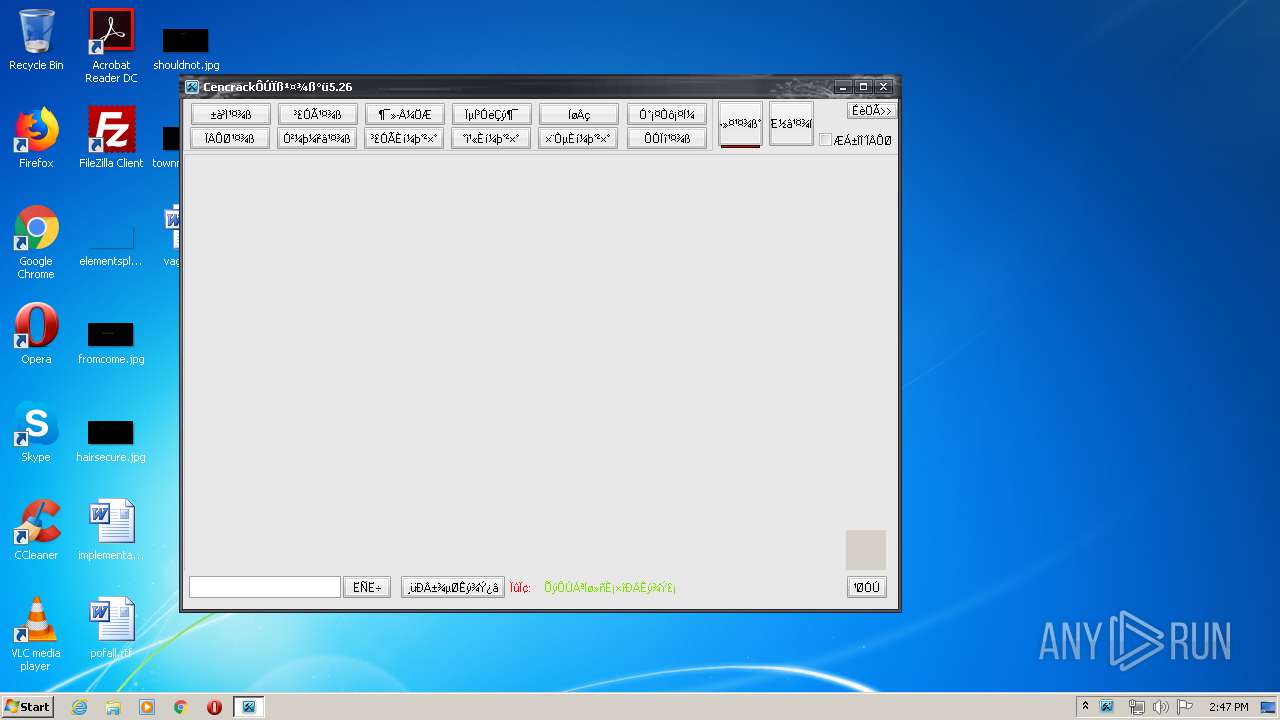
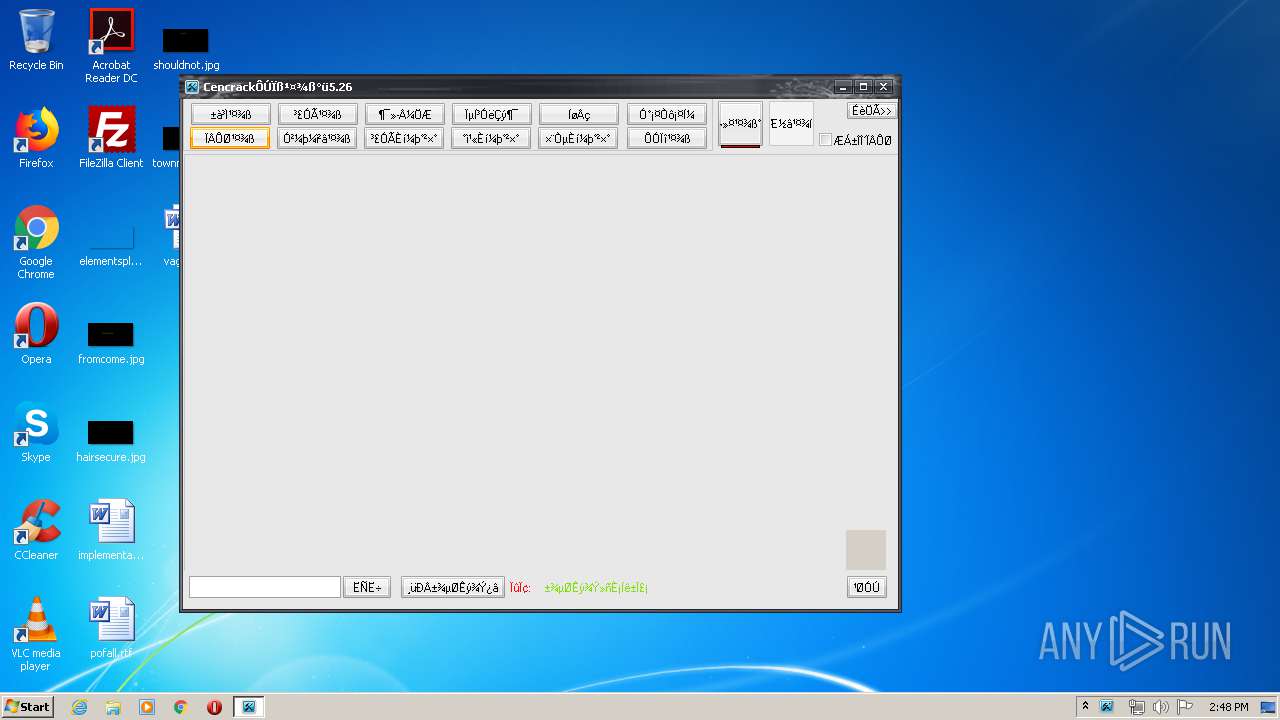
| FileDescription: | cencrack |
| ProductName: | cencrack |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | cencrack |
| LegalCopyright: | cencrack |
| Comments: | cencrack |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Mar-2020 02:22:43 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | cencrack |
| ProductName: | cencrack |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | cencrack |
| LegalCopyright: | cencrack |
| Comments: | cencrack |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Mar-2020 02:22:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x002BB000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x002BC000 | 0x00212000 | 0x00211C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9999 |
.rsrc | 0x004CE000 | 0x0004F000 | 0x0004F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.50363 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 7.24009 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.26547 | 1640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.13886 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.10709 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.53816 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.04618 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.84608 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.4846 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.676 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVFW32.dll |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
Total processes
41
Monitored processes
2
Malicious processes
2
Suspicious processes
0
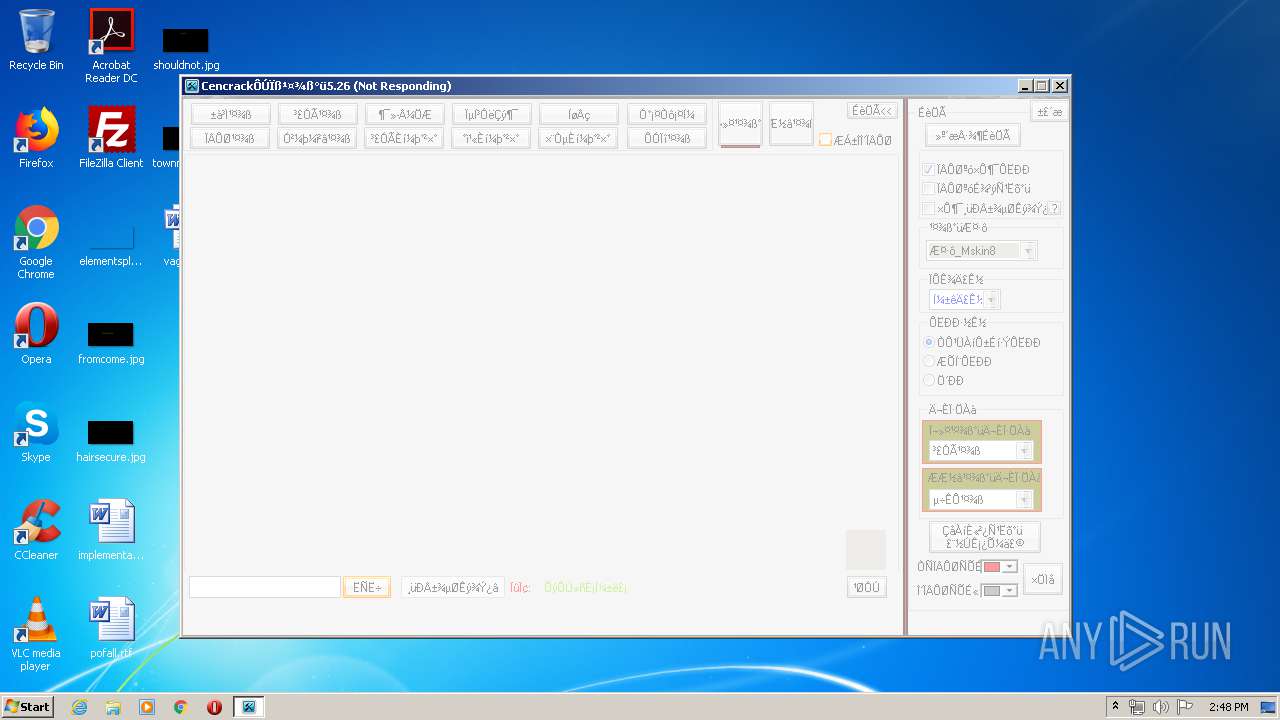
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3720 | "C:\Users\admin\AppData\Local\Temp\在线工具包.exe" | C:\Users\admin\AppData\Local\Temp\在线工具包.exe | explorer.exe | ||||||||||||
User: admin Company: cencrack Integrity Level: MEDIUM Description: cencrack Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4036 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | SearchIndexer.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
433
Read events
419
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Version |
Value: 00070000 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: 在线工具包.EXE | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Id |
Value: 在线工具包.EXE5E7428F300261000 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | MostRecentStart |
Value: DA38185B0826D601 | |||
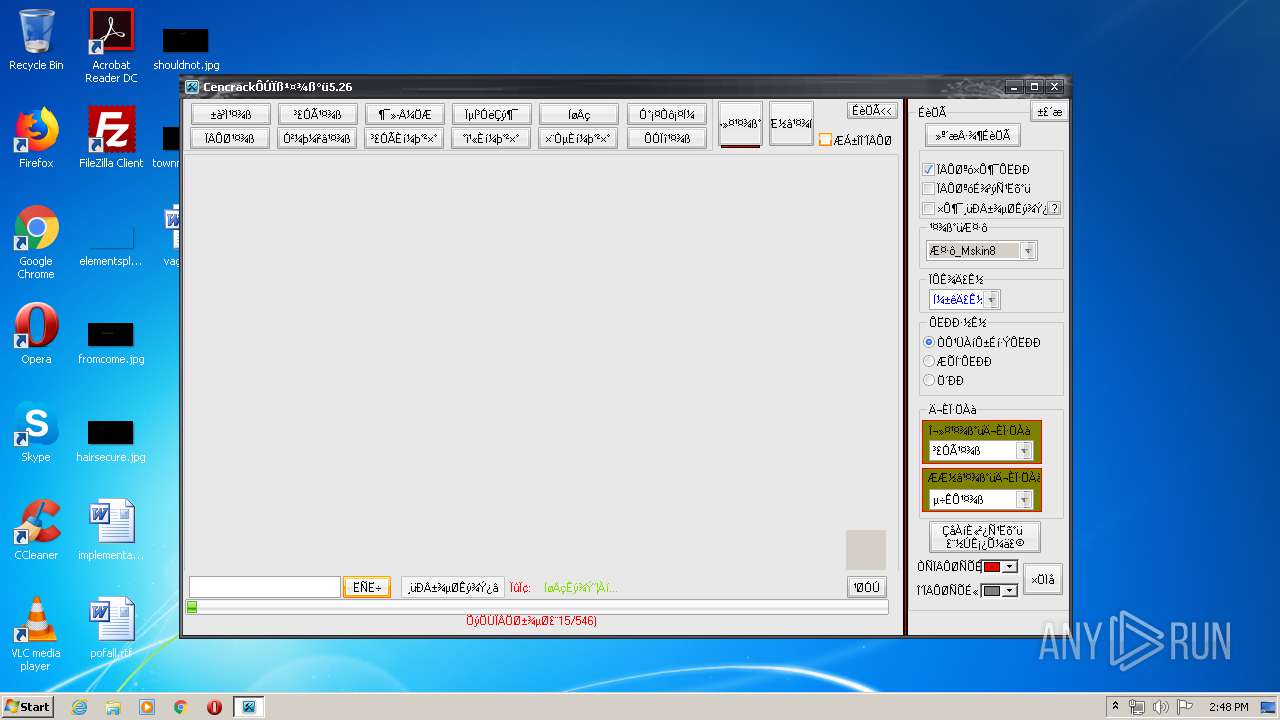
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3720) 在线工具包.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
1
Suspicious files
1
Text files
552
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | 在线工具包.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\tools[1].htm | — | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\tools[1].htm | — | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ping[1].htm | text | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\Documents\one.ini | text | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\Documents\cencrack_tool.mdb | mdb | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\Documents\¹¤¾ß°üÎļþ\icon.rar | compressed | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ping[1].htm | text | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\Documents\Cencrack_tool_5.02.ini | text | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\Documents\¦ñ+¯¦n+-+¦\_-+¦O\ACProtect Stripper.png | image | |
MD5:— | SHA256:— | |||
| 3720 | 在线工具包.exe | C:\Users\admin\Documents\¦ñ+¯¦n+-+¦\_-+¦O\Add PE bytes.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
6
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
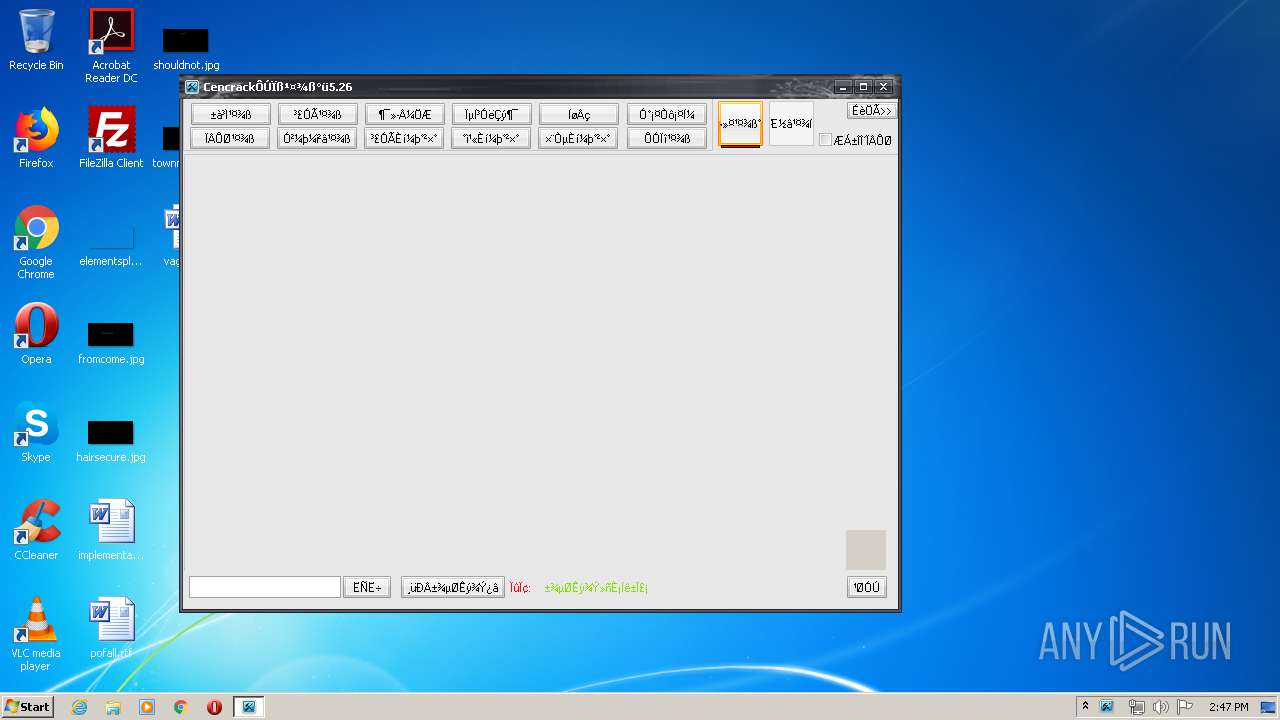
3720 | 在线工具包.exe | GET | — | 116.10.127.142:88 | http://a.cencrack.com:88/tools/tool/_%E5%9B%BE%E6%A0%87.rar | CN | — | — | suspicious |
3720 | 在线工具包.exe | GET | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/tools/tool/ping.php | CN | text | 53 b | suspicious |
3720 | 在线工具包.exe | POST | — | 116.10.127.142:88 | http://a.cencrack.com:88/pan/tools.php | CN | — | — | suspicious |
3720 | 在线工具包.exe | GET | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/tools/tool/ping.php | CN | text | 53 b | suspicious |
3720 | 在线工具包.exe | POST | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/pan/tools.php | CN | text | 144 Kb | suspicious |
3720 | 在线工具包.exe | POST | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/pan/tools.php | CN | text | 2.99 Kb | suspicious |
3720 | 在线工具包.exe | GET | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/tools/tool/_%E5%9B%BE%E6%A0%87.rar | CN | compressed | 743 Kb | suspicious |
3720 | 在线工具包.exe | GET | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/tools/tool/_%E5%9B%BE%E6%A0%87.rar | CN | compressed | 743 Kb | suspicious |
3720 | 在线工具包.exe | POST | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/pan/tools.php | CN | text | 144 Kb | suspicious |
3720 | 在线工具包.exe | GET | 200 | 116.10.127.142:88 | http://a.cencrack.com:88/tools/tool/ping.php | CN | text | 53 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | 在线工具包.exe | 116.10.127.142:88 | a.cencrack.com | No.31,Jin-rong Street | CN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a.cencrack.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3720 | 在线工具包.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |
3720 | 在线工具包.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |