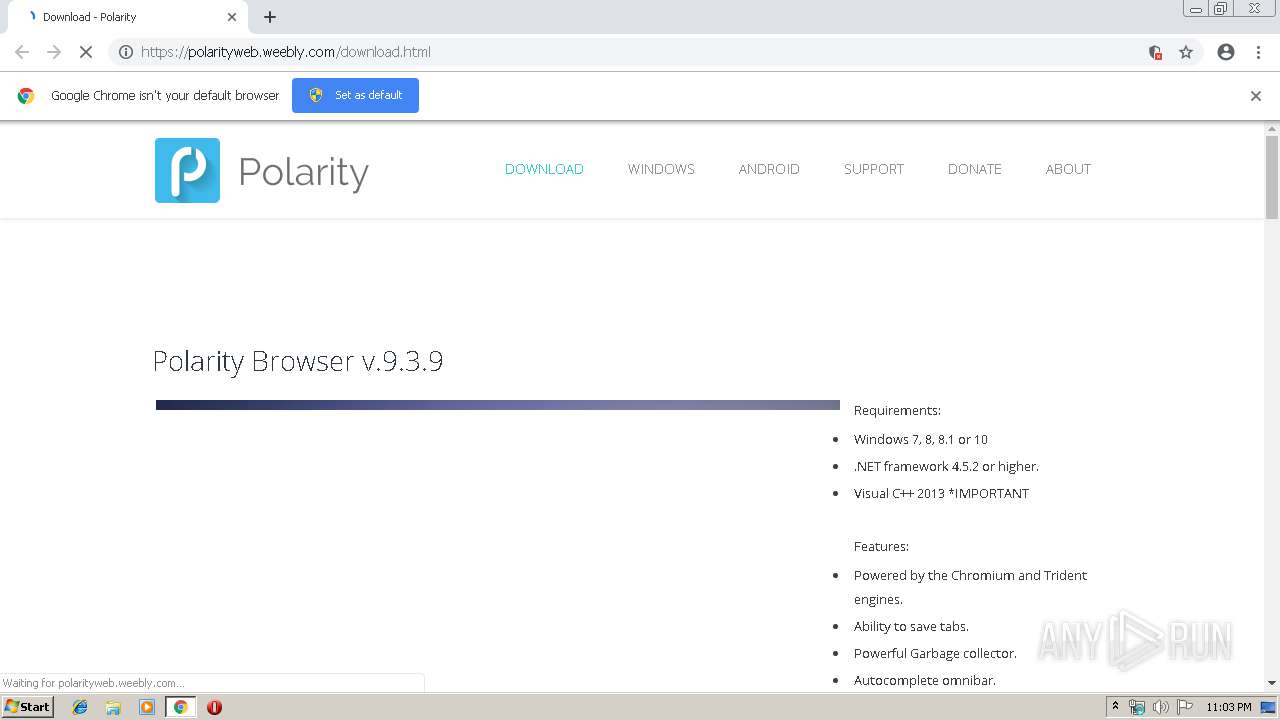
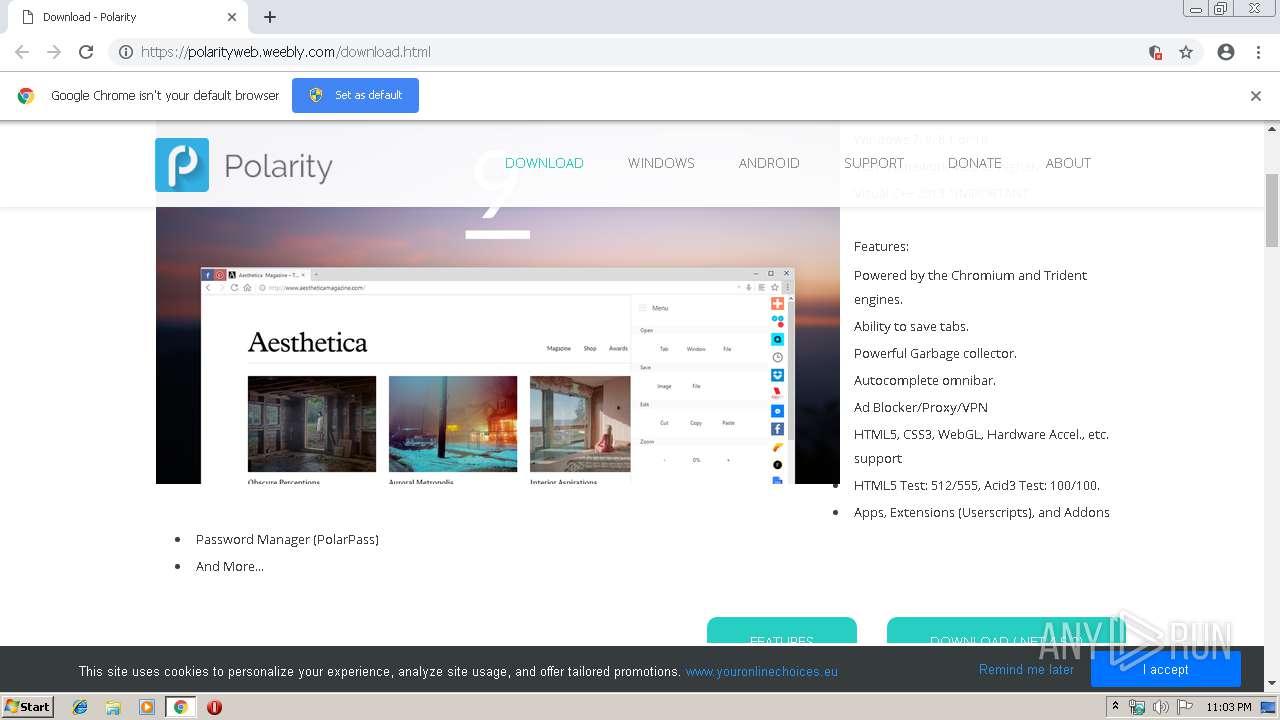
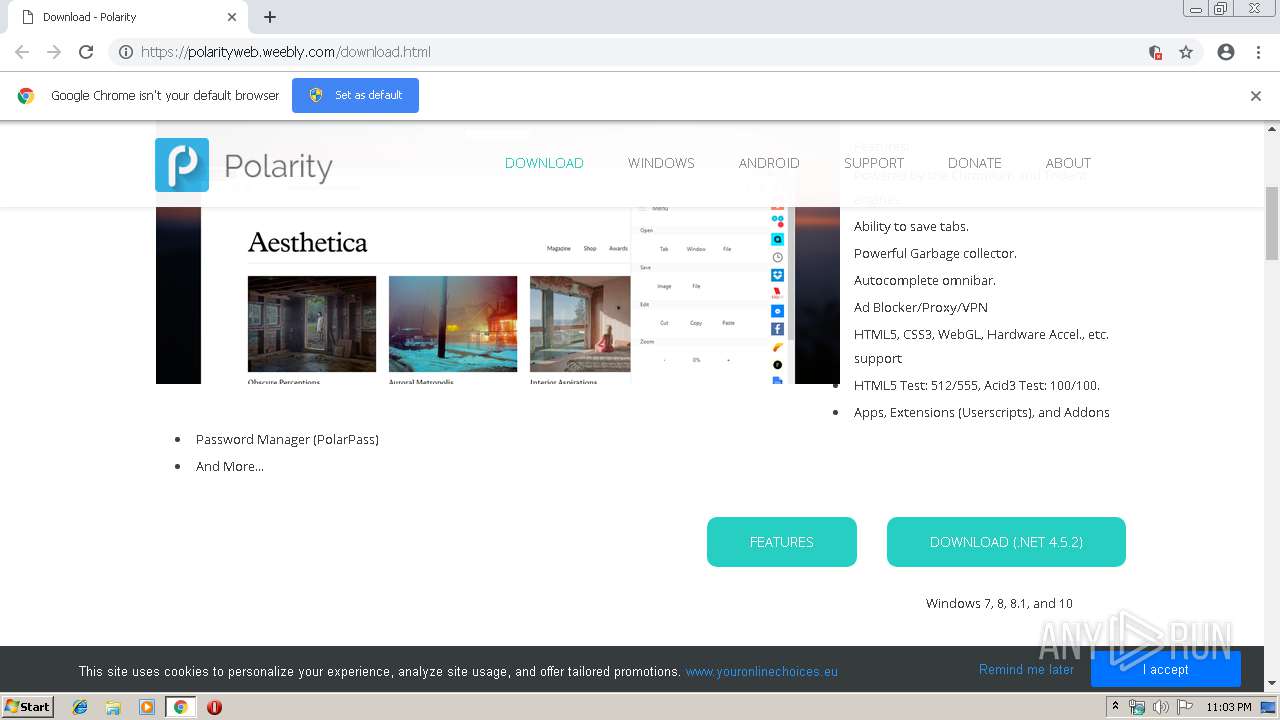
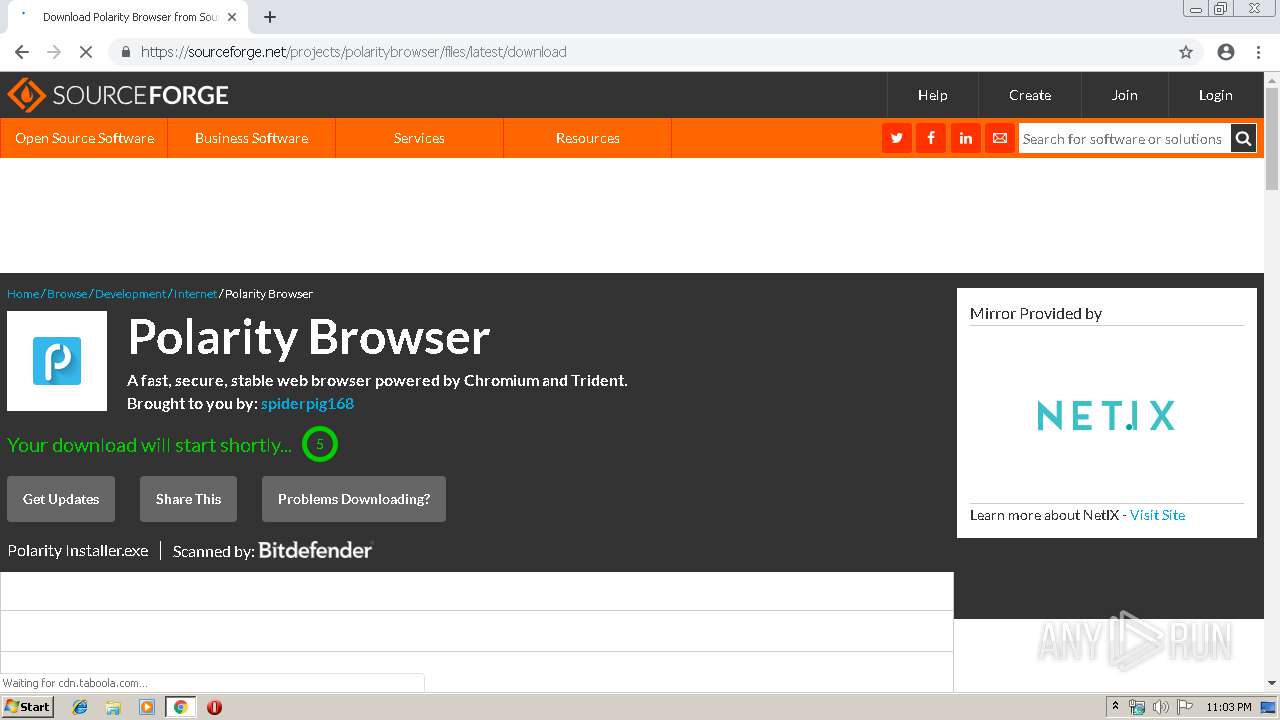
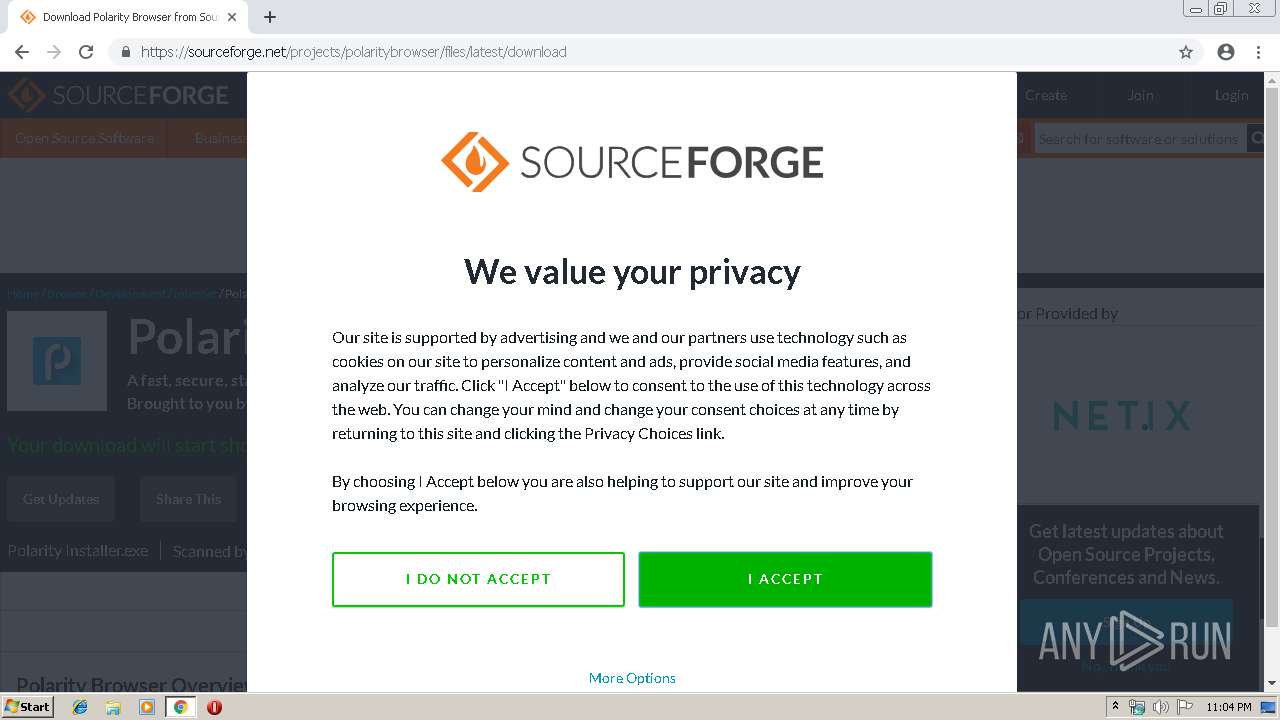
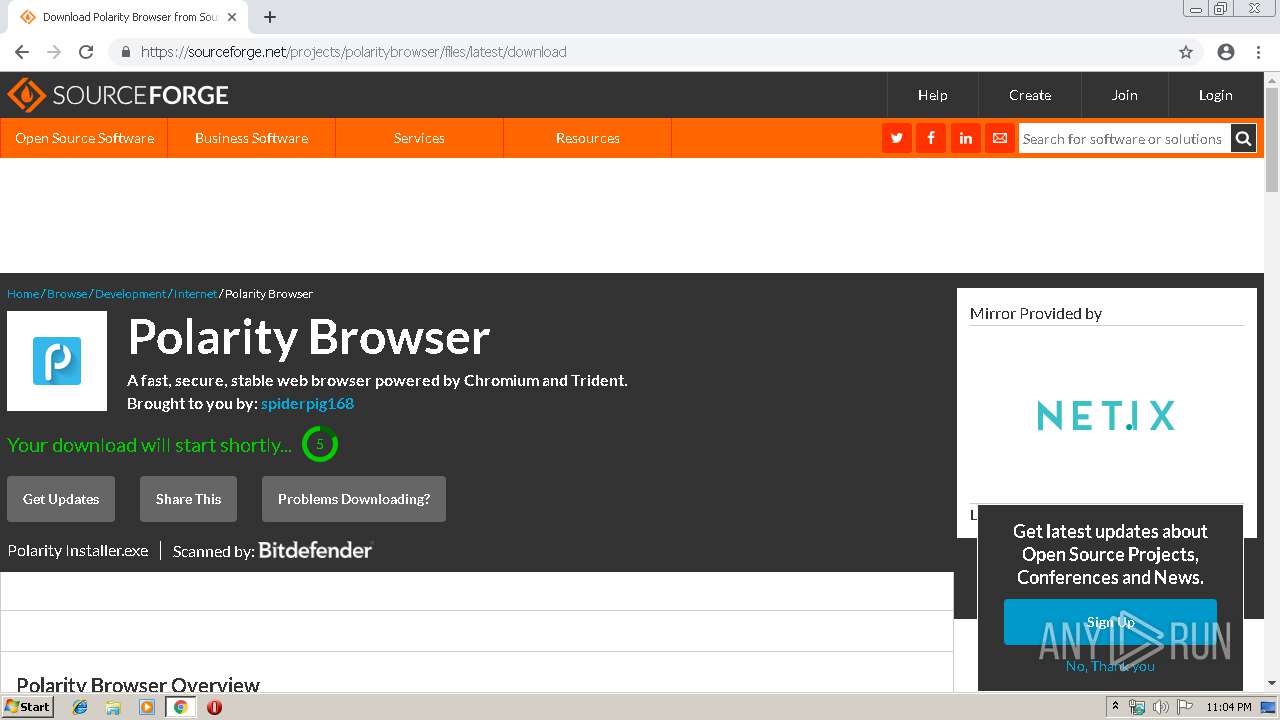
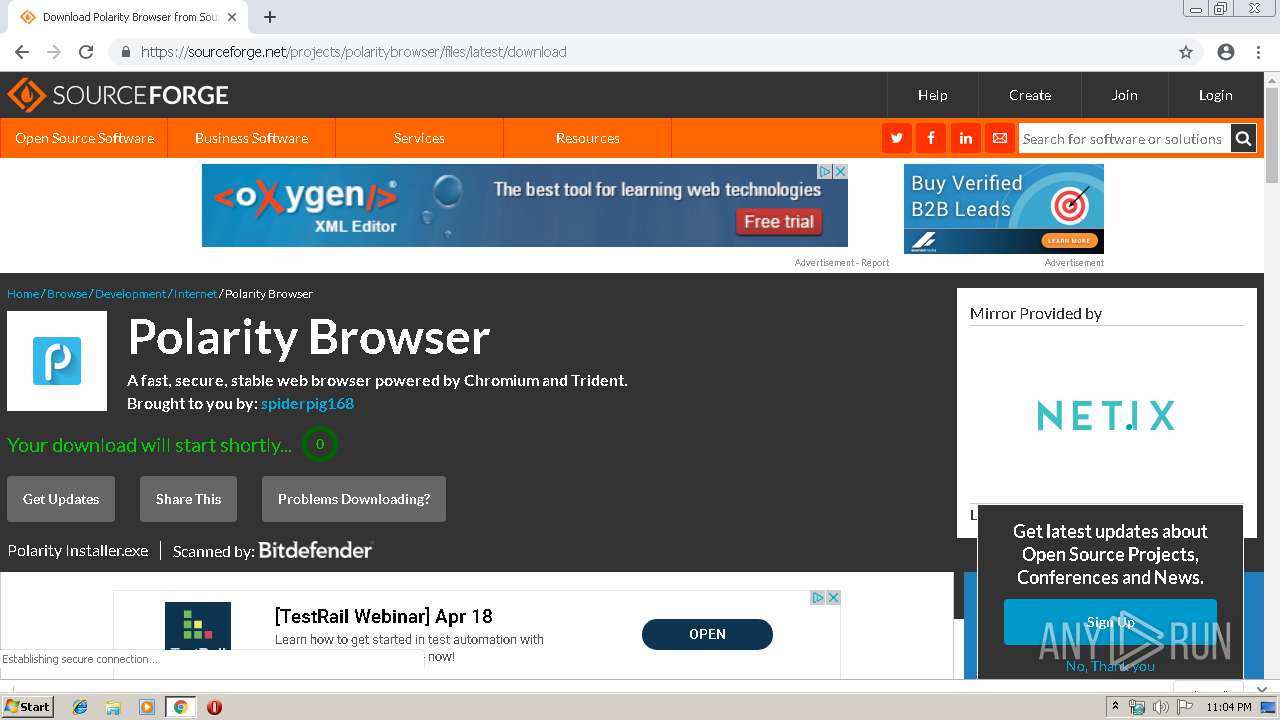
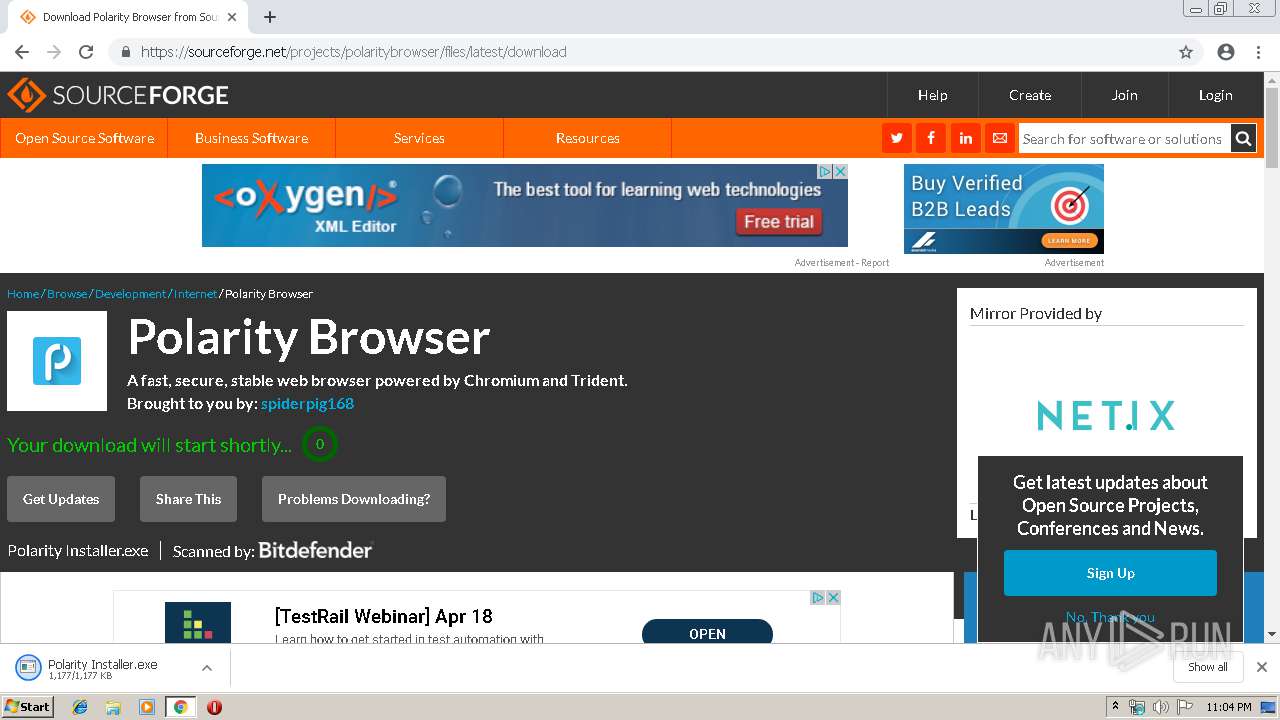
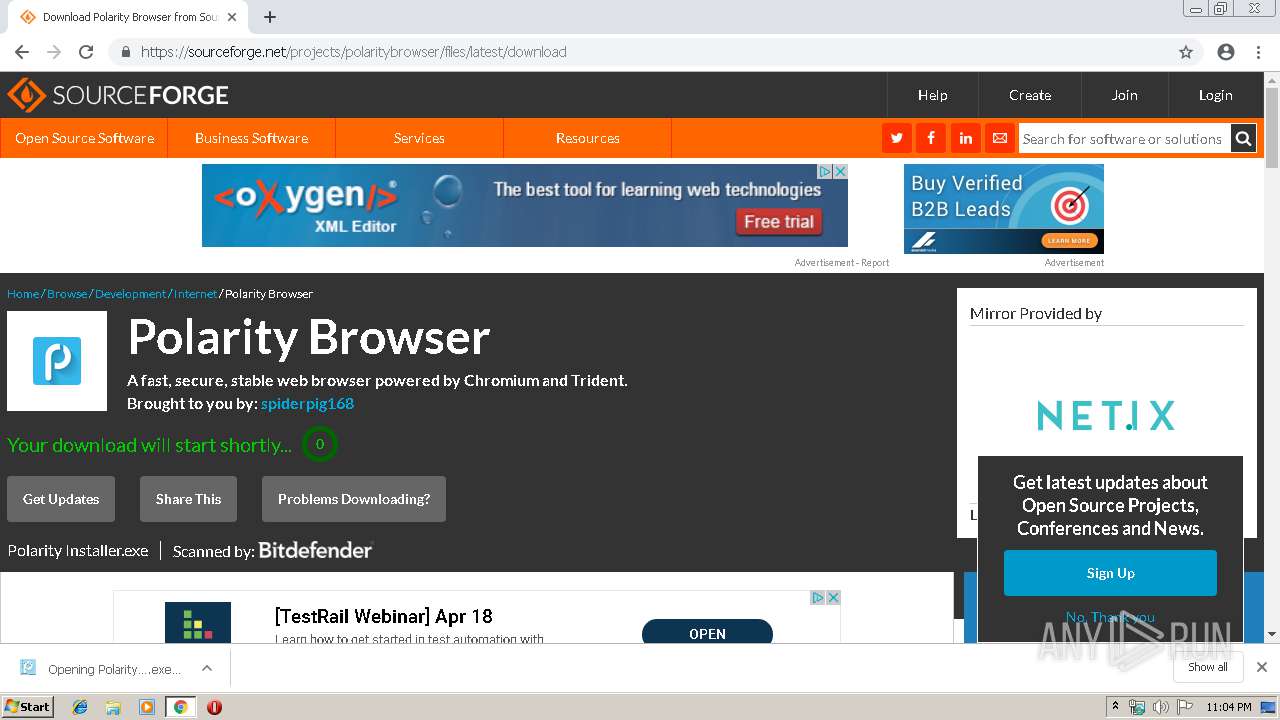
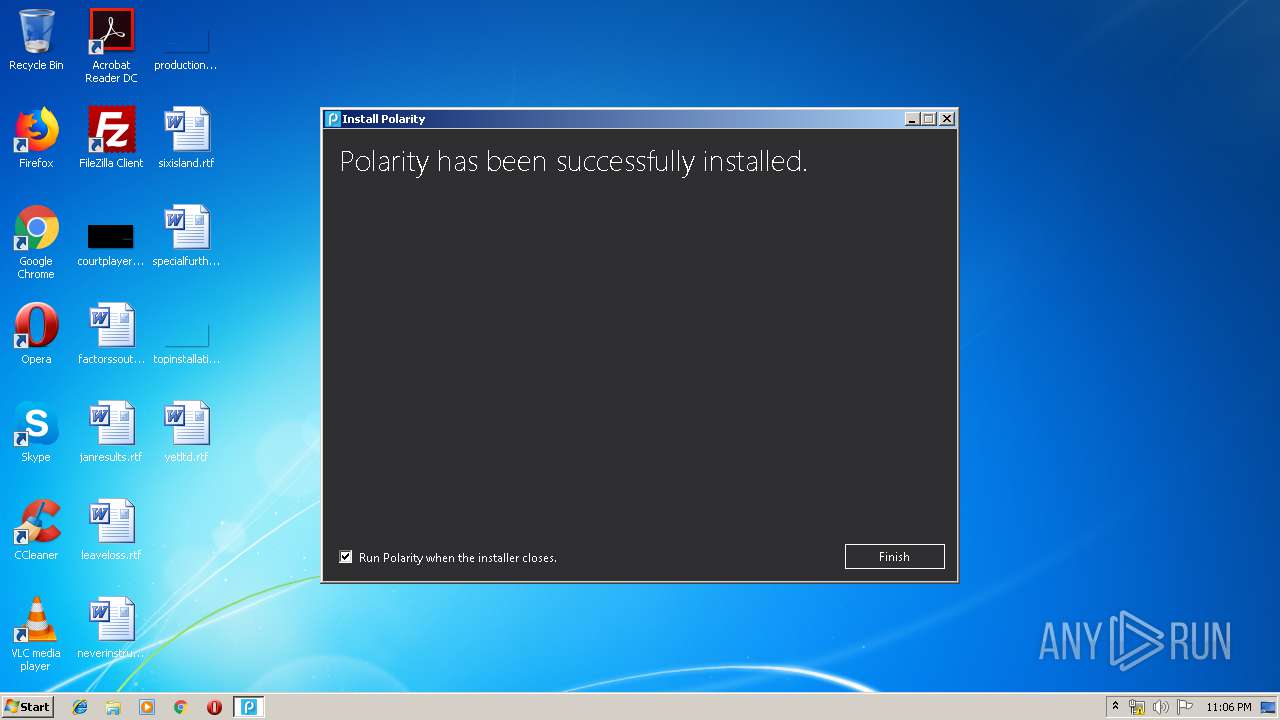
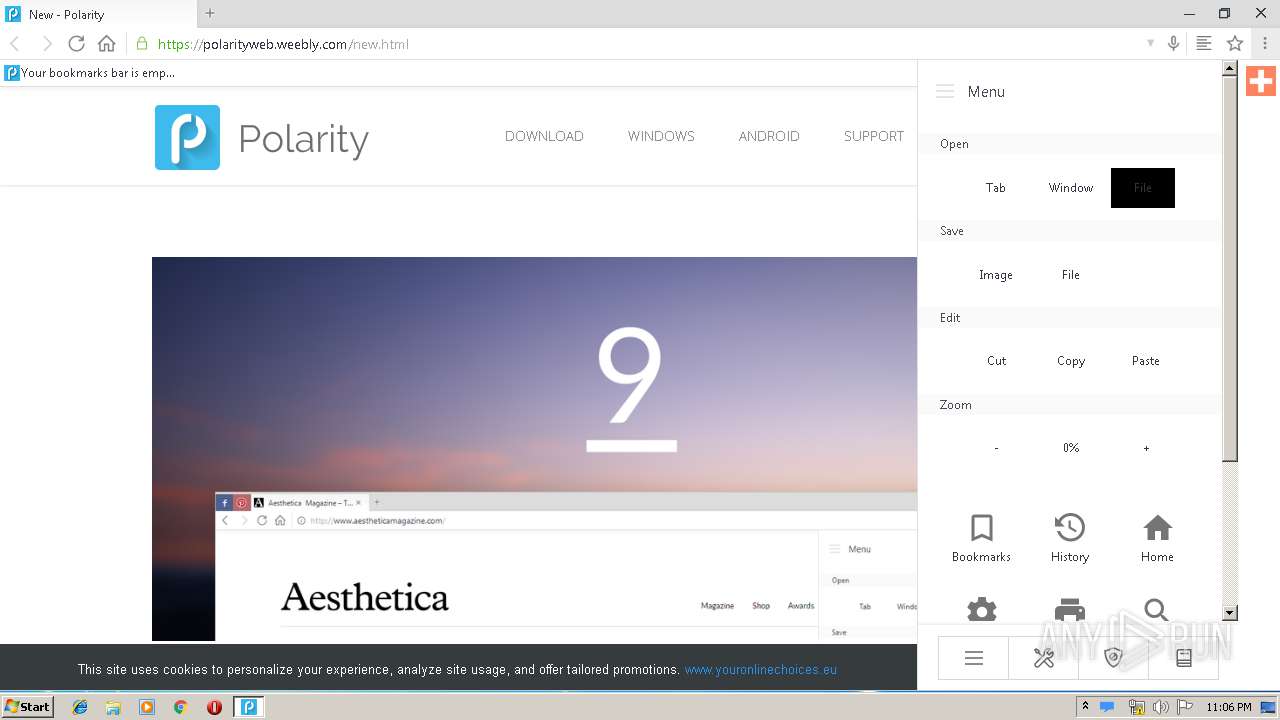
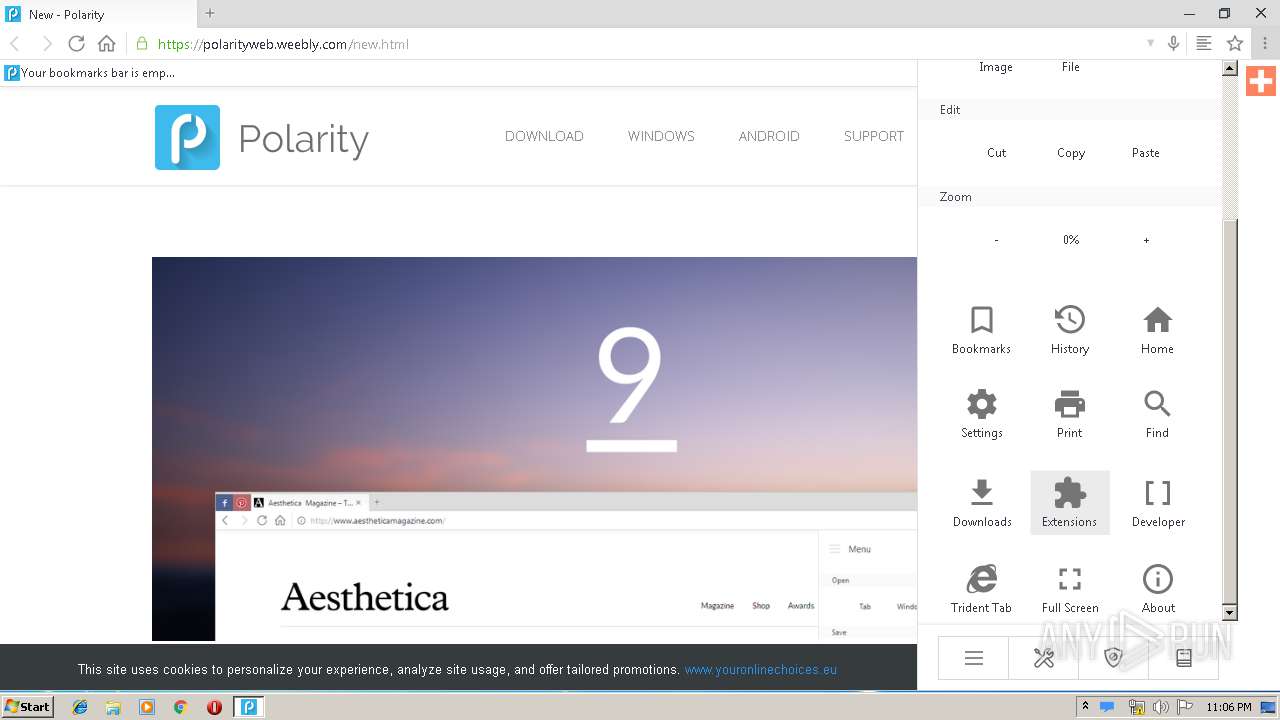
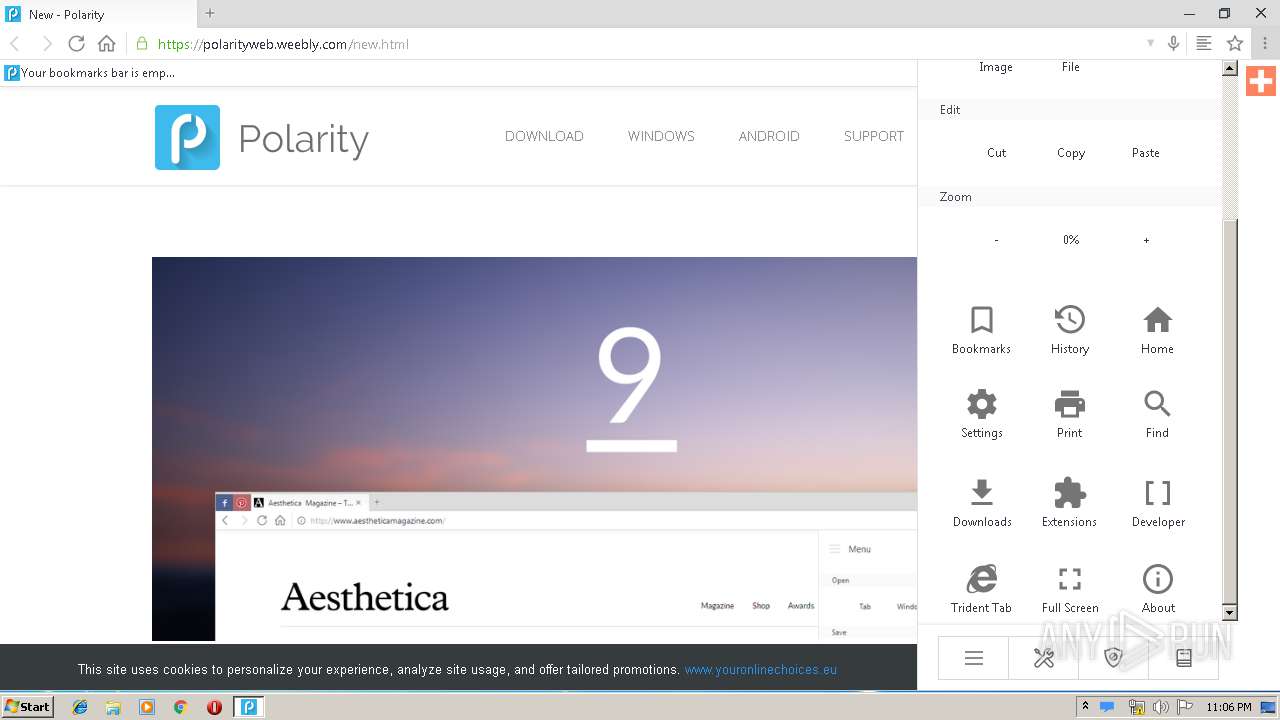
| URL: | https://polarityweb.weebly.com/download.html |
| Full analysis: | https://app.any.run/tasks/9d2271b7-8788-43ee-9157-e0e34bd46f65 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 22:03:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EA1C5BB6C94F01E640107ACD01E73BF3 |
| SHA1: | F915521E9E4507B34BCA24DF01DF346EA2B76DB9 |
| SHA256: | 55723AF68A5F9985EE51E790FBFC5CA756F0F2D673F8B97EB4F32BCAF91CA1AB |
| SSDEEP: | 3:N8OArLsyLdMKQ:2OArLsyZMKQ |
MALICIOUS
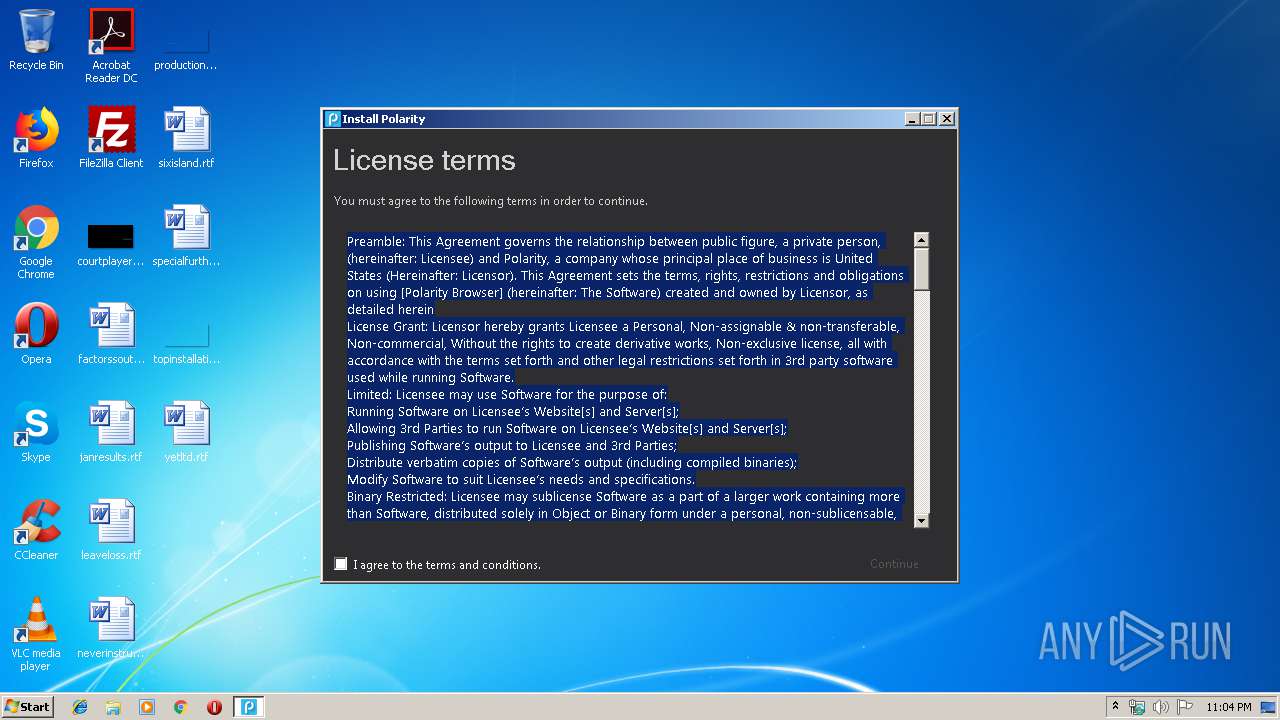
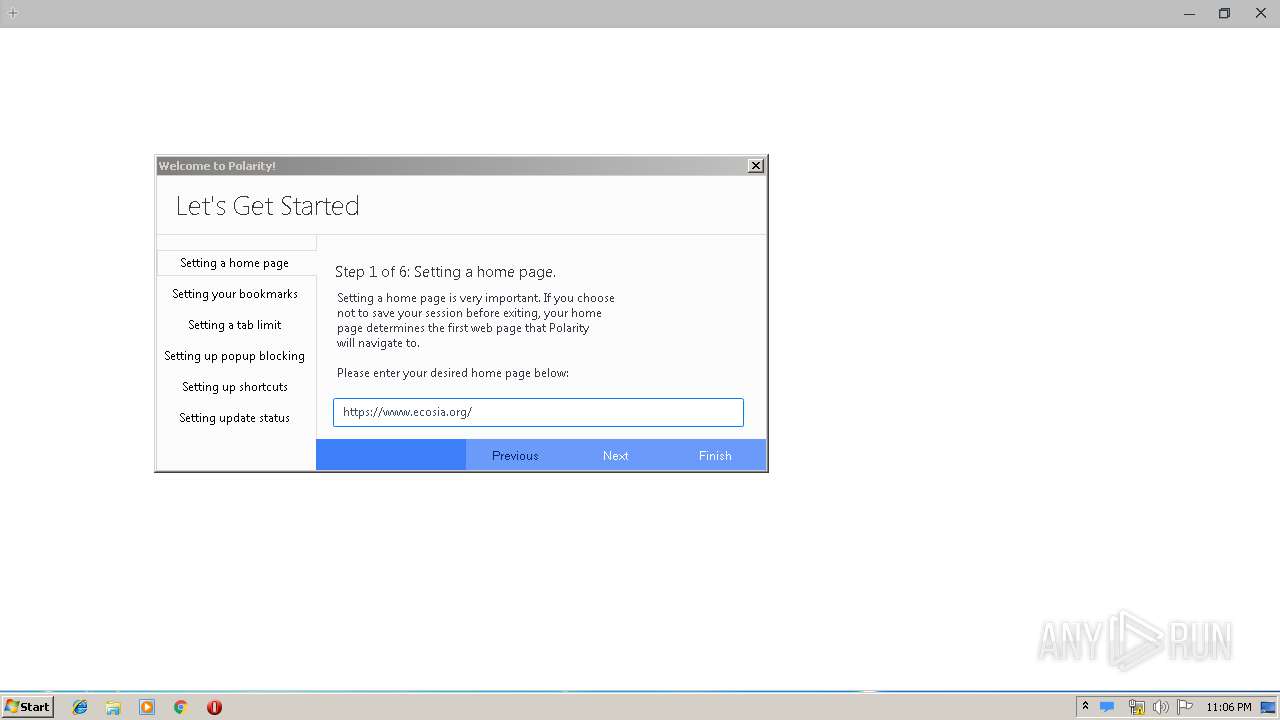
Application was dropped or rewritten from another process
- Polarity Installer.exe (PID: 3880)
- Polarity Installer.exe (PID: 3144)
- polarity.exe (PID: 3020)
- PolarityAddonHelper.exe (PID: 3276)
- PolarityInstance.exe (PID: 2244)
Loads dropped or rewritten executable
- polarity.exe (PID: 3020)
- PolarityInstance.exe (PID: 2244)
Changes settings of System certificates
- Polarity Installer.exe (PID: 3144)
- polarity.exe (PID: 3020)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2968)
- chrome.exe (PID: 1948)
- Polarity Installer.exe (PID: 3144)
Creates a software uninstall entry
- Polarity Installer.exe (PID: 3144)
Creates files in the user directory
- polarity.exe (PID: 3020)
Creates files in the program directory
- Polarity Installer.exe (PID: 3144)
Adds / modifies Windows certificates
- Polarity Installer.exe (PID: 3144)
- polarity.exe (PID: 3020)
Reads Environment values
- polarity.exe (PID: 3020)
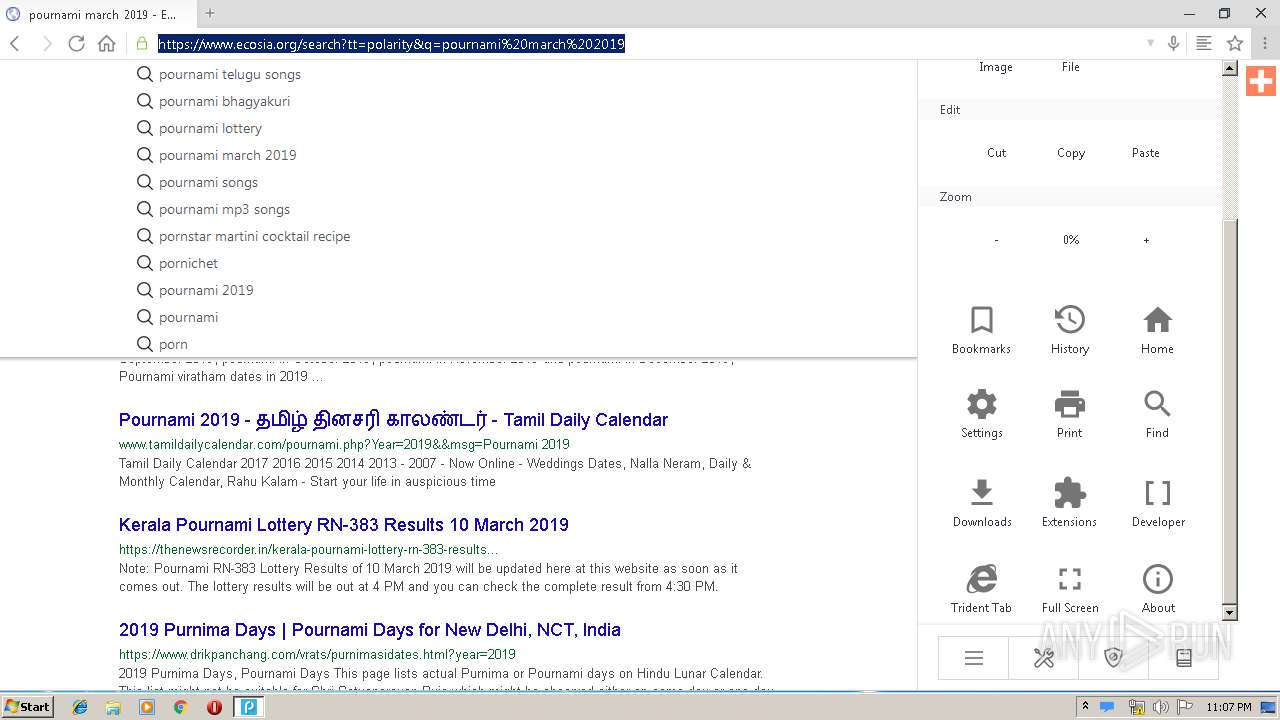
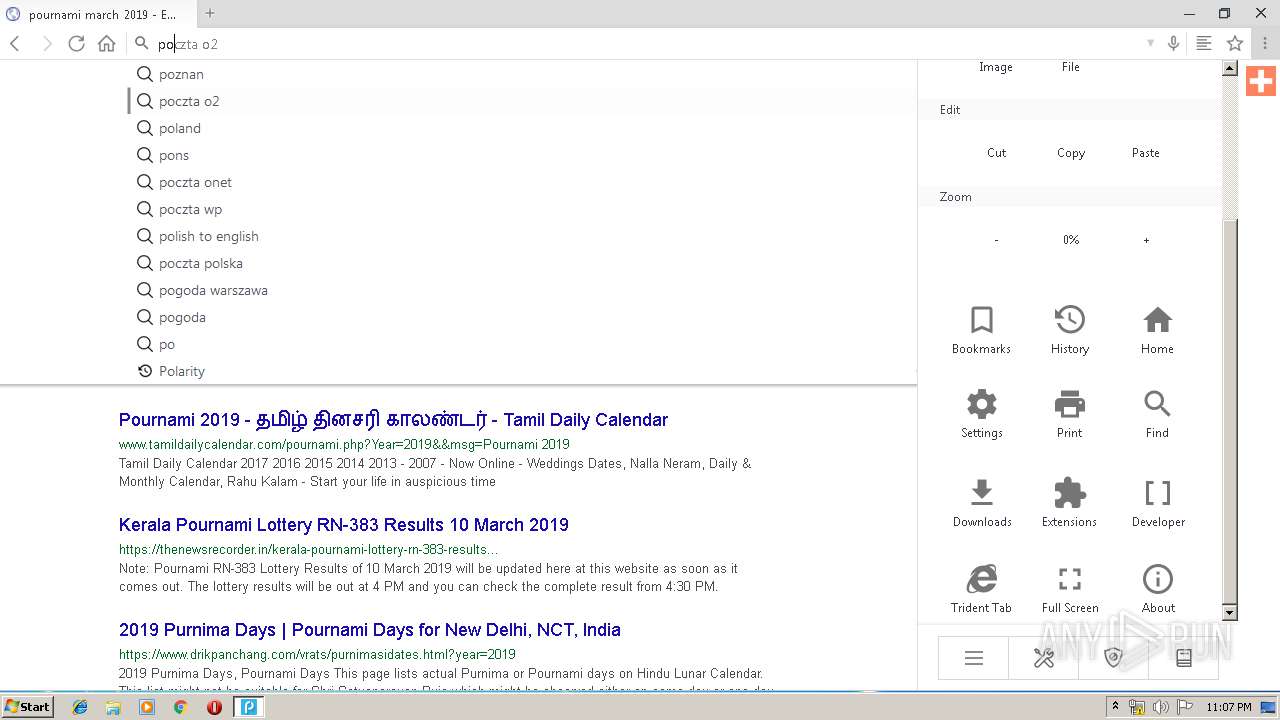
Changes IE settings (feature browser emulation)
- Polarity Installer.exe (PID: 3144)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2968)
INFO
Application launched itself
- chrome.exe (PID: 2968)
Changes settings of System certificates
- chrome.exe (PID: 1948)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1948)
- Polarity Installer.exe (PID: 3144)
Reads settings of System Certificates
- polarity.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
23
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16250394780961177299 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16250394780961177299 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12260655920339028539 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18179149644818833761 --mojo-platform-channel-handle=3268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
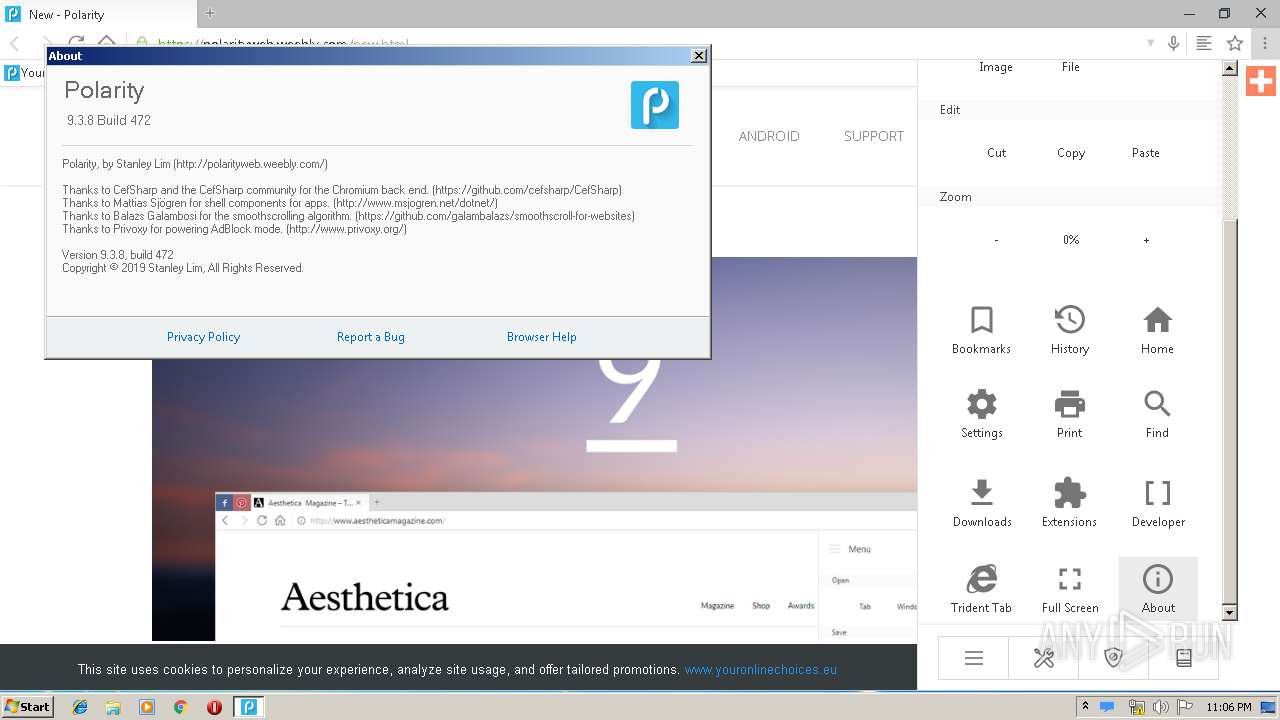
| 2244 | PolarityInstance.exe --type=renderer --disable-gpu-vsync=0 --enable-experimental-canvas-features=1 --enable-pinch=1 --enable-touch-drag-drop=1 --no-sandbox --touch-events=enabled --primordial-pipe-token=66303F9AE898FB80A8330EAB74FEF400 --lang=en-US --lang=en-US --log-file="C:\Program Files\Polarity\debug.log" --log-severity=disable --user-agent="Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/57.0.2987.133 Safari/537.36 Polarity/9.3.8" --enable-speech-input=1 --enable-system-flash=1 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=66303F9AE898FB80A8330EAB74FEF400 --renderer-client-id=2 --mojo-platform-channel-handle=3076 /prefetch:1 --wcf-enabled --wcf-host-process-id=3020 | C:\Program Files\Polarity\PolarityInstance.exe | — | polarity.exe | |||||||||||
User: admin Company: The CefSharp Authors Integrity Level: HIGH Description: CefSharp.BrowserSubprocess Exit code: 0 Version: 57.0.0.0 Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2297314291403837450 --mojo-platform-channel-handle=3548 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14086183016770745119 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14086183016770745119 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6796024288209745602 --mojo-platform-channel-handle=3360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6490948634350519524 --mojo-platform-channel-handle=3384 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --service-pipe-token=8224781245461163953 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8224781245461163953 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,16223523501231843240,1896361858351148309,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6650207923981712164 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6650207923981712164 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
959
Read events
786
Write events
168
Delete events
5
Modification events
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2968-13199753026986000 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
52
Suspicious files
199
Text files
252
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a3ac0e52-6889-4fc1-b59d-8235ce1b745d.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
192
DNS requests
101
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
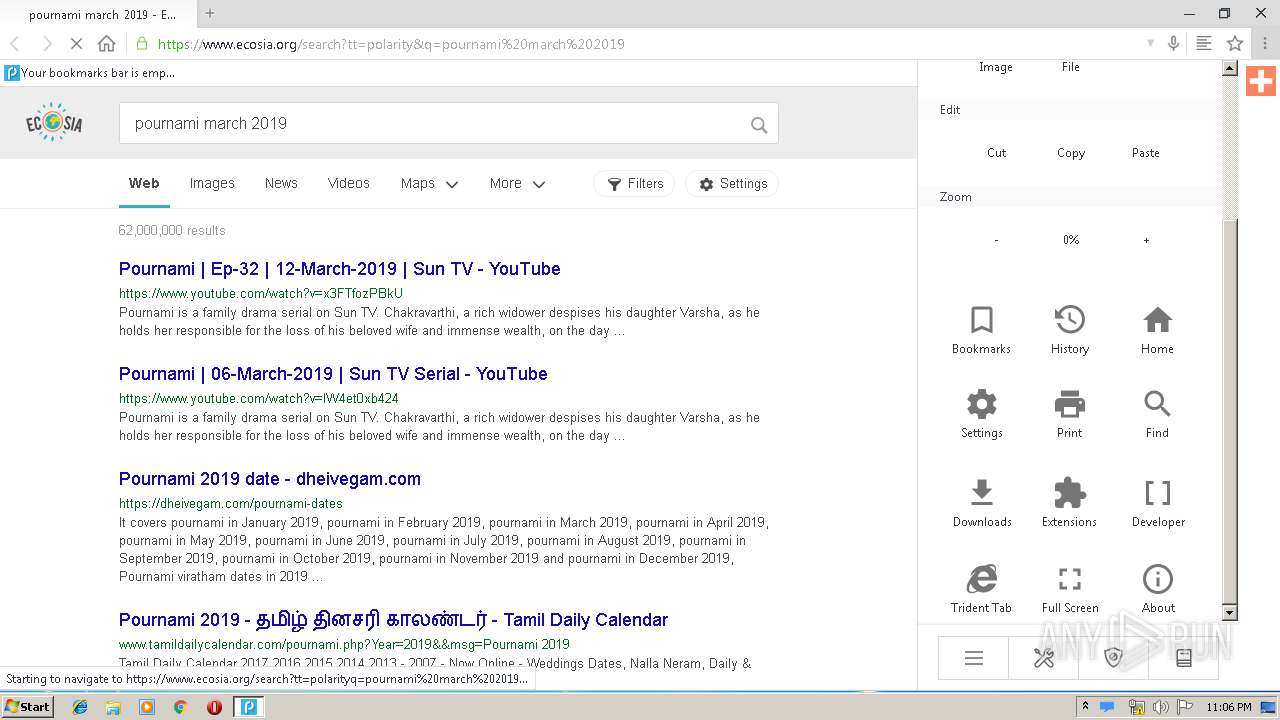
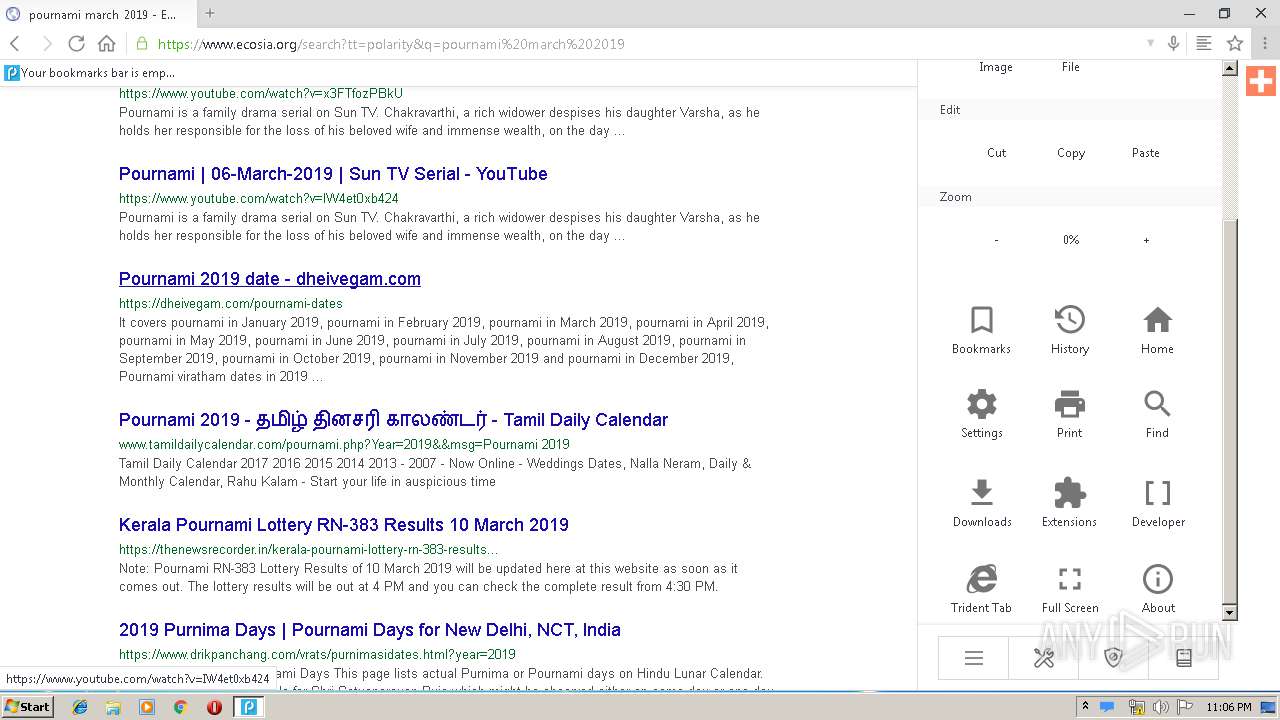
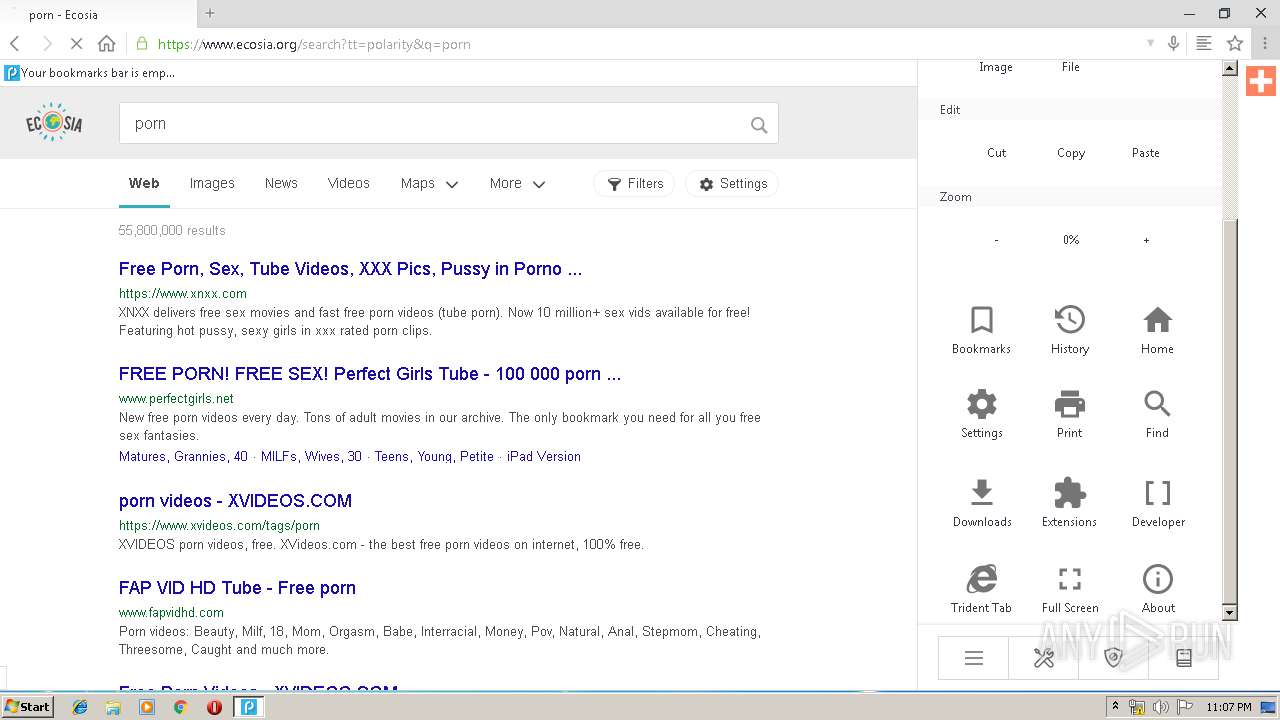
3020 | polarity.exe | GET | 200 | 54.187.27.208:80 | http://api.mywot.com/0.4/public_query2?target=polarityweb.weebly.com | US | xml | 233 b | unknown |
3020 | polarity.exe | GET | 200 | 199.34.228.54:80 | http://polarityweb.weebly.com/uploads/2/1/4/7/21476634/4032559.png?116 | US | image | 6.27 Kb | suspicious |
1948 | chrome.exe | GET | 200 | 199.34.228.54:80 | http://polarityweb.weebly.com/uploads/2/1/4/7/21476634/4032559.png?116 | US | image | 6.27 Kb | suspicious |
3020 | polarity.exe | GET | 301 | 199.34.228.54:80 | http://polarityweb.weebly.com/new.html | US | html | 400 b | suspicious |
3020 | polarity.exe | GET | 200 | 54.187.27.208:80 | http://api.mywot.com/0.4/public_query2?target=www.ecosia.org | US | xml | 221 b | unknown |
3020 | polarity.exe | GET | 200 | 54.187.27.208:80 | http://api.mywot.com/0.4/public_query2?target=www.ecosia.org | US | xml | 221 b | unknown |
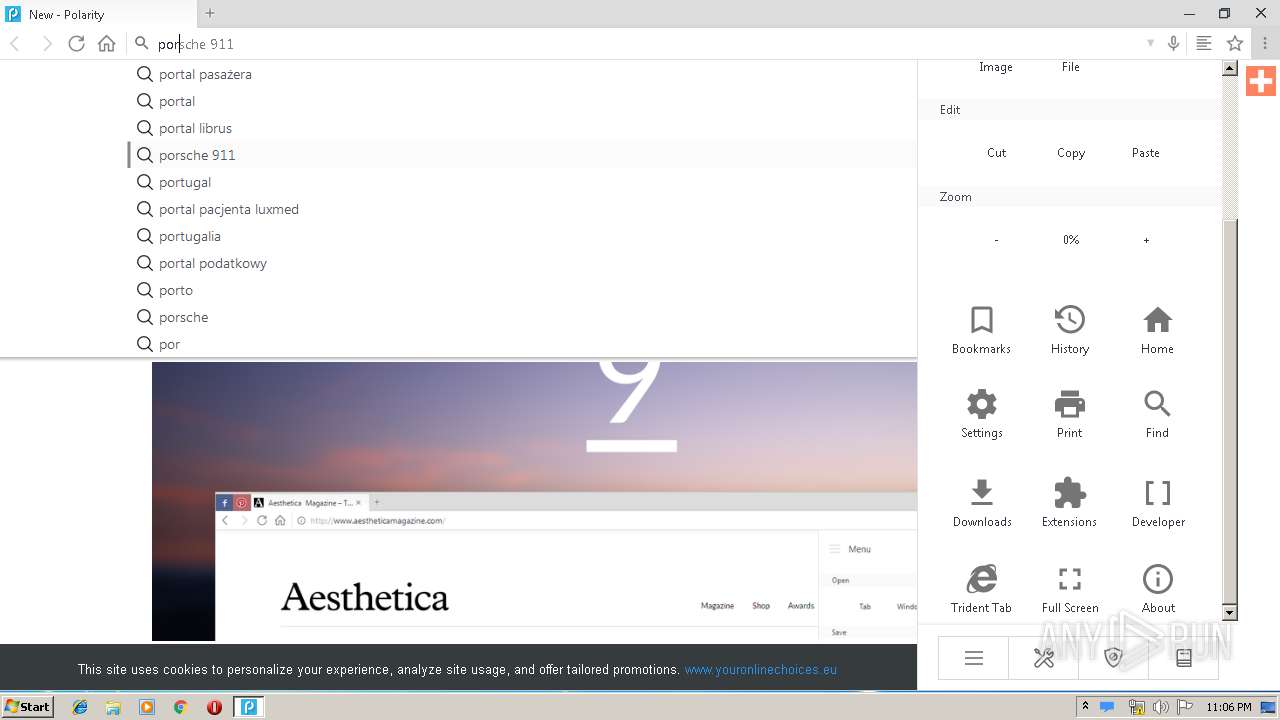
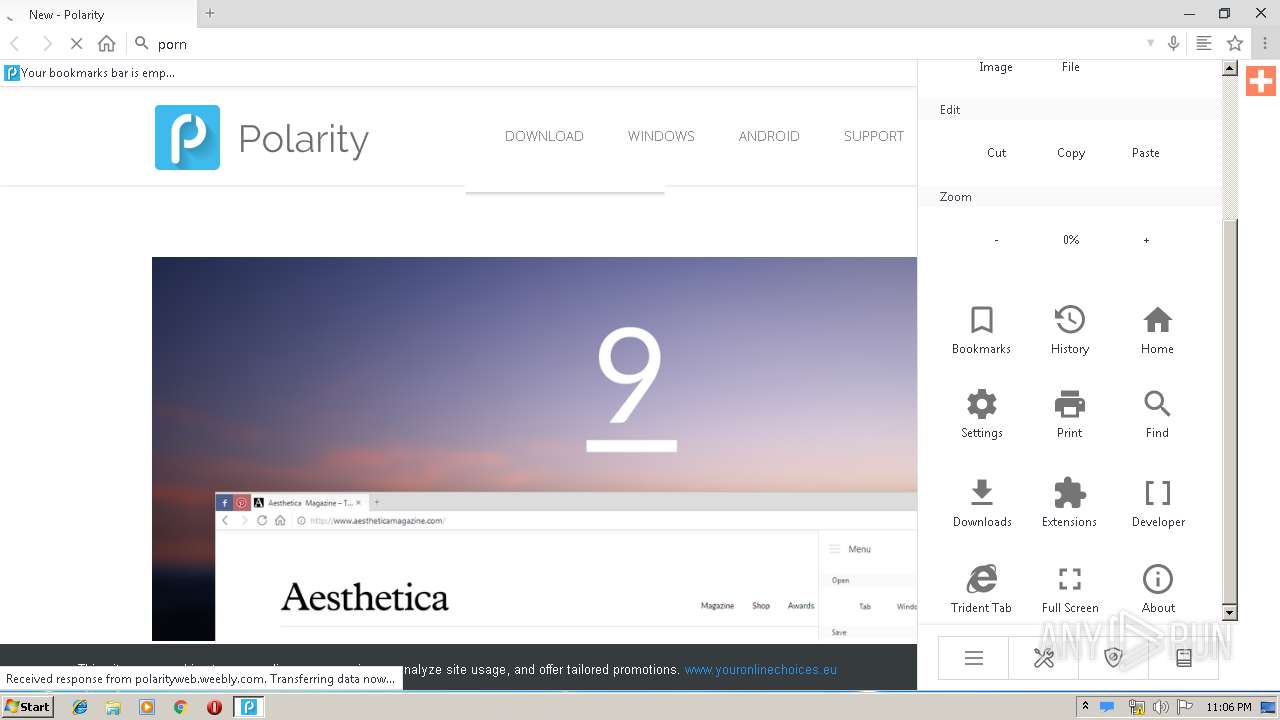
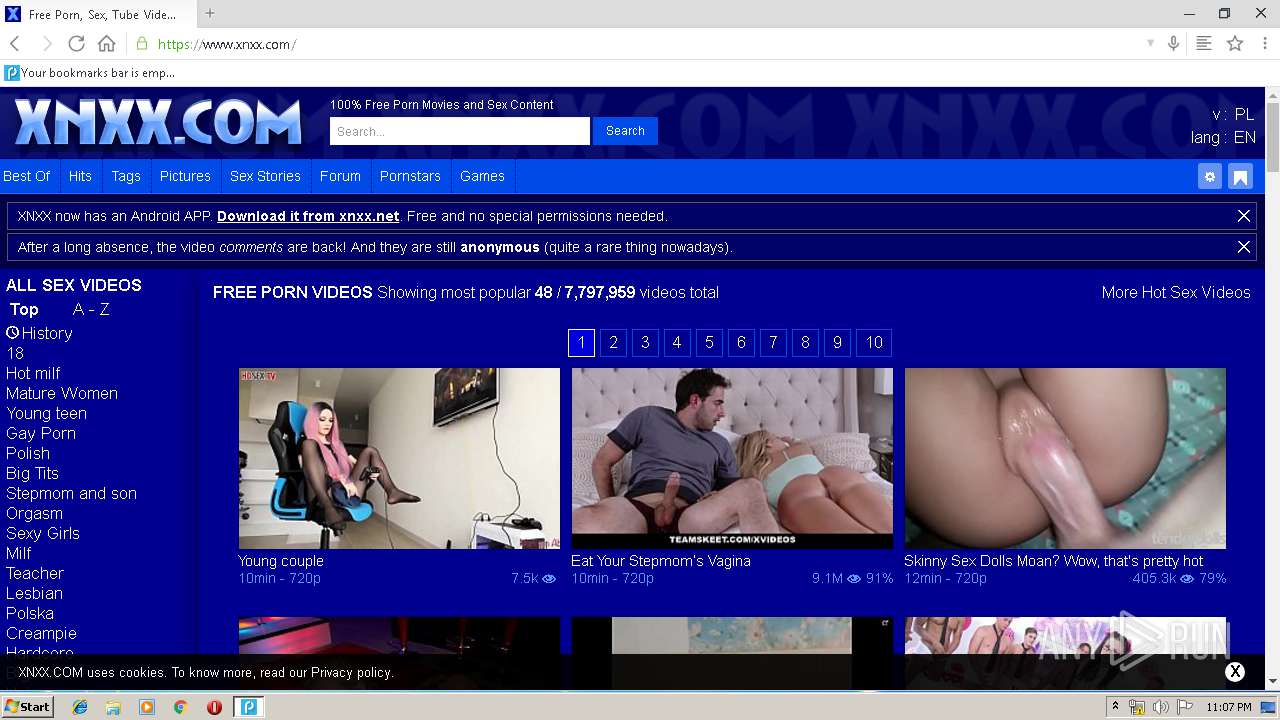
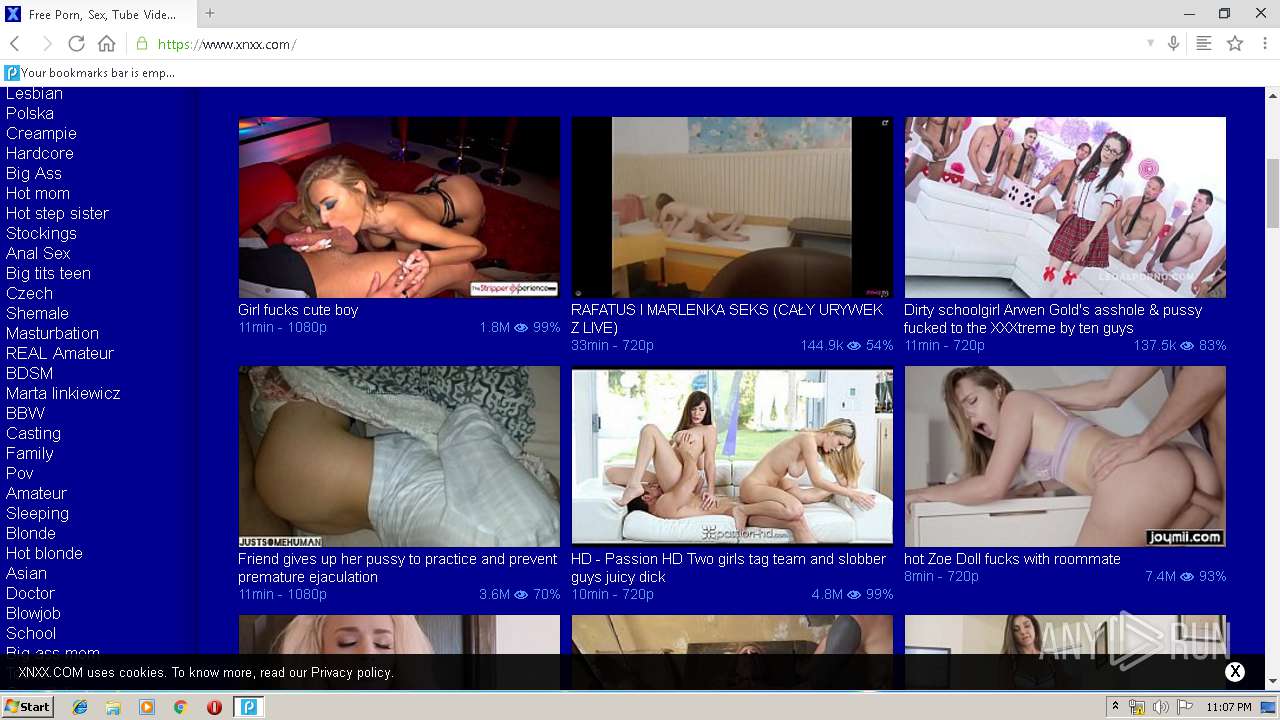
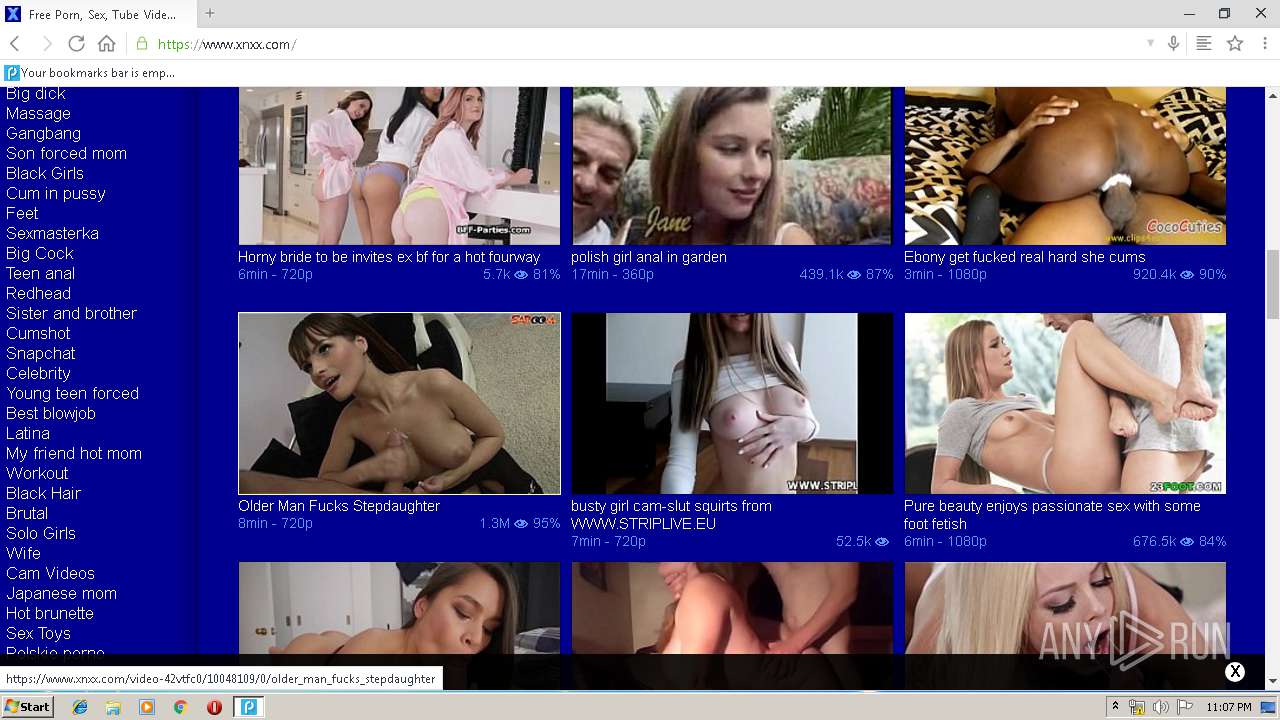
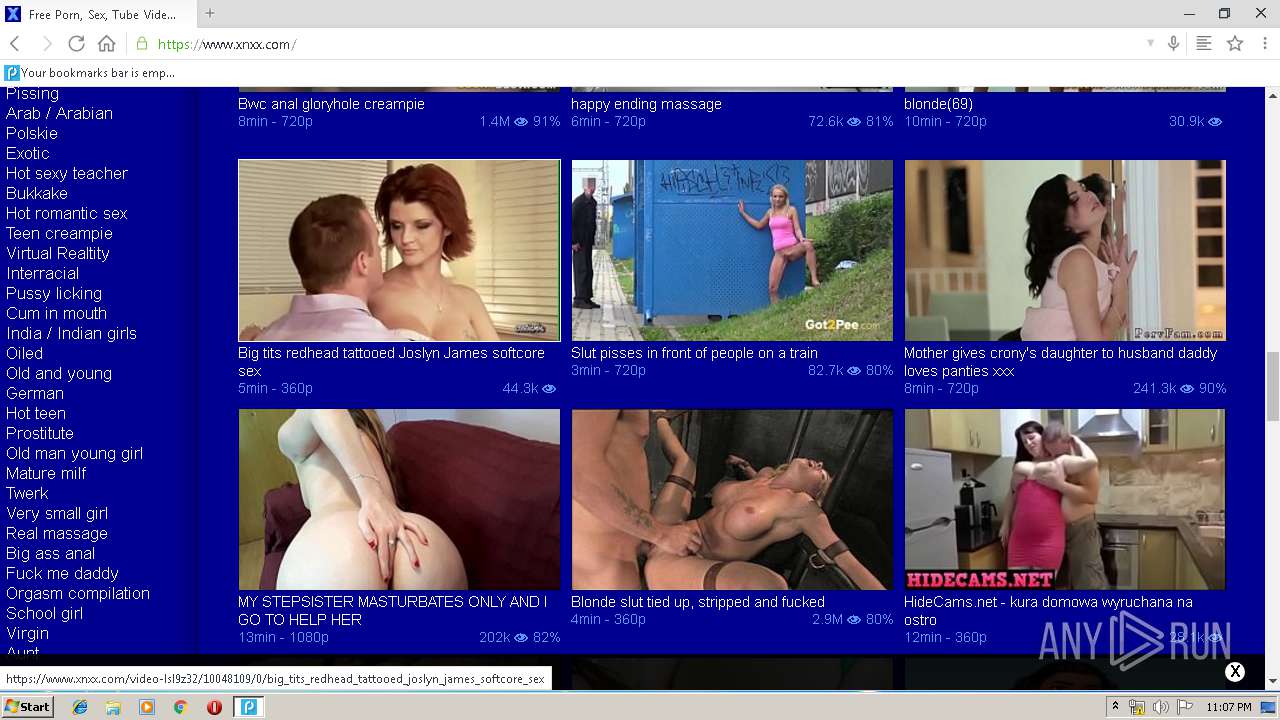
3020 | polarity.exe | GET | 200 | 54.187.27.208:80 | http://api.mywot.com/0.4/public_query2?target=www.xnxx.com | US | xml | 219 b | unknown |
1948 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
1948 | chrome.exe | GET | 200 | 194.9.24.113:80 | http://r6---sn-5uh5o-f5fd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.217.54&mm=28&mn=sn-5uh5o-f5fd&ms=nvh&mt=1555278442&mv=u&pl=21&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
1948 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 507 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1948 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1948 | chrome.exe | 172.217.18.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 199.34.228.54:443 | polarityweb.weebly.com | Weebly, Inc. | US | suspicious |
1948 | chrome.exe | 151.139.242.29:443 | images.dmca.com | netDNA | US | unknown |
1948 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 199.34.228.54:80 | polarityweb.weebly.com | Weebly, Inc. | US | suspicious |
1948 | chrome.exe | 172.217.16.206:443 | translate.google.com | Google Inc. | US | whitelisted |
1948 | chrome.exe | 172.217.23.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
polarityweb.weebly.com |
| suspicious |
accounts.google.com |
| shared |
cdn2.editmysite.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
images.dmca.com |
| whitelisted |
translate.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |