| File name: | CTB-LOCKER (2).exe |
| Full analysis: | https://app.any.run/tasks/edfbf925-c0a0-4599-b6a0-eb3134877195 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2019, 13:22:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 489F698980136ED5D81C83F5921787B1 |
| SHA1: | 7441656C4778D2EC22D806715600BFFC0F10DAB0 |
| SHA256: | 554B22E4765856527E2FEE6B9EDFA8D323E5350BB447D872B07E905D15185145 |
| SSDEEP: | 24576:g3Yp5hJp6mrRSjmDoAz5f3bQyekGOQV/Cj+Jz9fMHnfdWw7askTj56L:g3SFKUlMzkG3/Cje9An1n7sA |
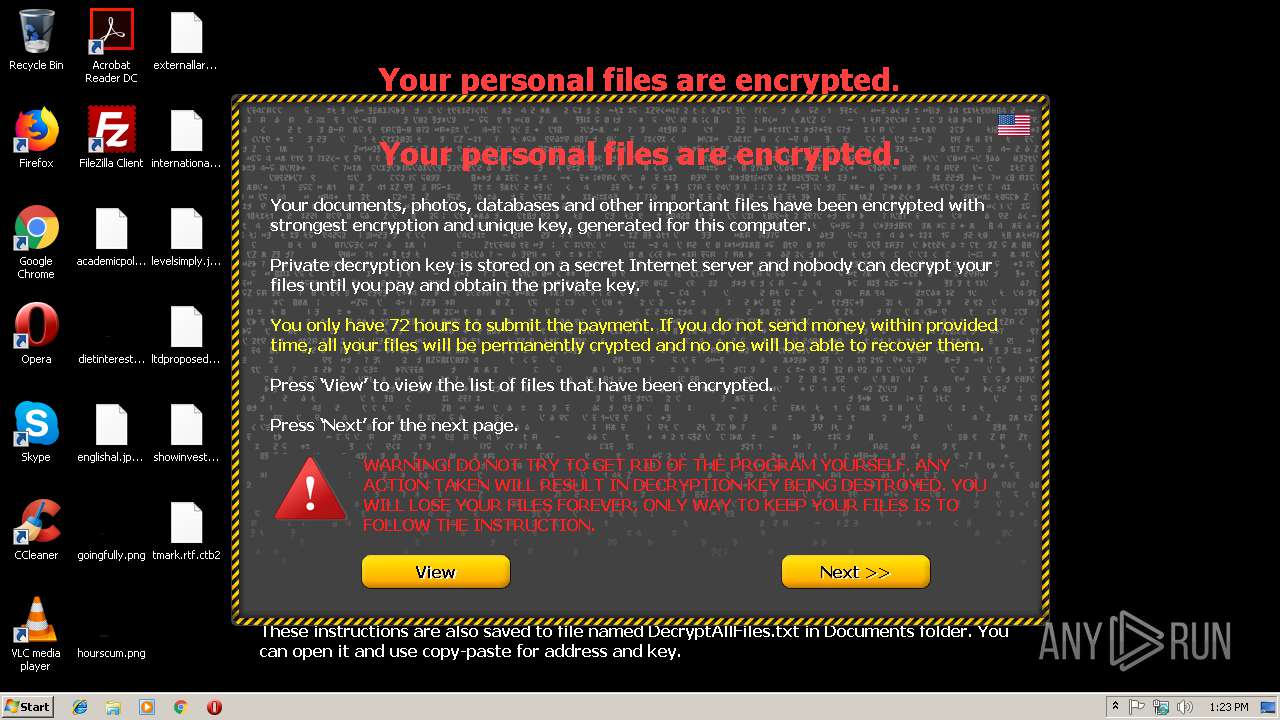
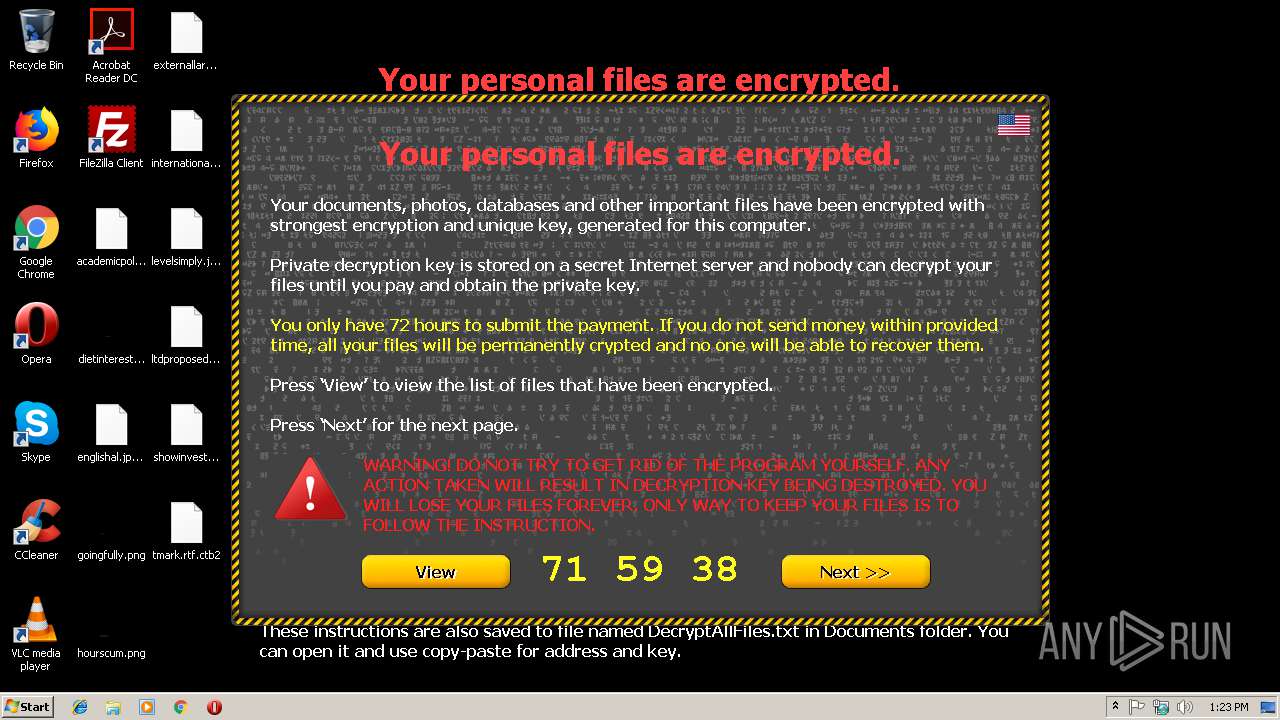
MALICIOUS
Actions looks like stealing of personal data
- CTB-LOCKER (2).exe (PID: 4008)
- ourkble.exe (PID: 2728)
Loads the Task Scheduler COM API
- CTB-LOCKER (2).exe (PID: 4008)
SUSPICIOUS
Application launched itself
- CTB-LOCKER (2).exe (PID: 3108)
- ourkble.exe (PID: 3984)
Creates files in the user directory
- CTB-LOCKER (2).exe (PID: 4008)
Executable content was dropped or overwritten
- CTB-LOCKER (2).exe (PID: 4008)
Creates files in the program directory
- ourkble.exe (PID: 2728)
Reads internet explorer settings
- ourkble.exe (PID: 2728)
Reads Internet Cache Settings
- ourkble.exe (PID: 2728)
INFO
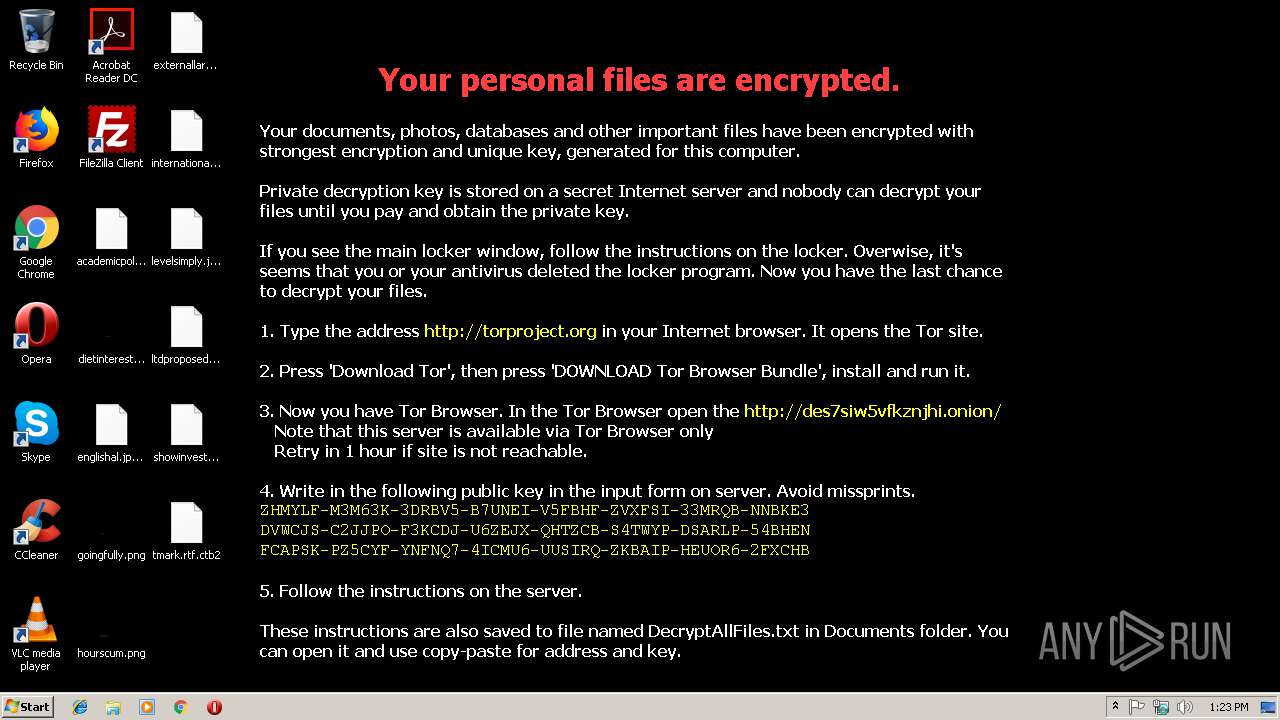
Dropped object may contain TOR URL's
- ourkble.exe (PID: 2728)
Dropped object may contain URL to Tor Browser
- ourkble.exe (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:08:25 11:36:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 57344 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1144 |
| OSVersion: | 4 |
| ImageVersion: | 5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Aug-2014 09:36:33 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Aug-2014 09:36:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text\x06\x06 | 0x00001000 | 0x0000DAD8 | 0x0000E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.41953 |
.data | 0x0000F000 | 0x00003738 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00013000 | 0x00000894 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.31139 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25807 | 552 | Unicode (UTF 16LE) | Czech - Czech Republic | UNKNOWN |
30001 | 3.91512 | 1384 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
NETAPI32.DLL |
SHELL32.DLL |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\Users\admin\AppData\Local\Temp\ourkble.exe" | C:\Users\admin\AppData\Local\Temp\ourkble.exe | ourkble.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3108 | "C:\Users\admin\AppData\Local\Temp\CTB-LOCKER (2).exe" | C:\Users\admin\AppData\Local\Temp\CTB-LOCKER (2).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3984 | C:\Users\admin\AppData\Local\Temp\ourkble.exe | C:\Users\admin\AppData\Local\Temp\ourkble.exe | — | taskeng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\AppData\Local\Temp\CTB-LOCKER (2).exe" | C:\Users\admin\AppData\Local\Temp\CTB-LOCKER (2).exe | CTB-LOCKER (2).exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
399
Read events
387
Write events
10
Delete events
2
Modification events
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019013020190131 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019013020190131 | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019013020190131 |
| Operation: | write | Name: | CachePrefix |
Value: :2019013020190131: | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019013020190131 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019013020190131 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019013020190131 |
| Operation: | write | Name: | CacheRepair |
Value: 0 | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018082720180903 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2728) ourkble.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012018090920180910 |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
1
Suspicious files
80
Text files
8
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\Temp\0.tmp | — | |
MD5:— | SHA256:— | |||
| 4008 | CTB-LOCKER (2).exe | C:\Users\admin\AppData\Roaming\Mozilla\sdvzsbm | binary | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Microsoft Office\CLIPART\PUB60COR\AllFilesAreLocked 2402921.bmp | image | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Common Files\Adobe\Reader\DC\Linguistics\LanguageNames2\DecryptAllFiles 2402578.txt | text | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Common Files\Adobe\Reader\DC\Linguistics\LanguageNames2\AllFilesAreLocked 2402578.bmp | image | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\databases\Databases.db.ctb2 | binary | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\previews_opt_out.db.ctb2 | binary | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\chrome_shutdown_ms.txt.ctb2 | binary | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Microsoft Office\CLIPART\PUB60COR\DecryptAllFiles 2402843.txt | text | |
MD5:— | SHA256:— | |||
| 2728 | ourkble.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\9cfa0dda3968329980b7e40c251f29bfef877f68\index.txt.ctb2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report