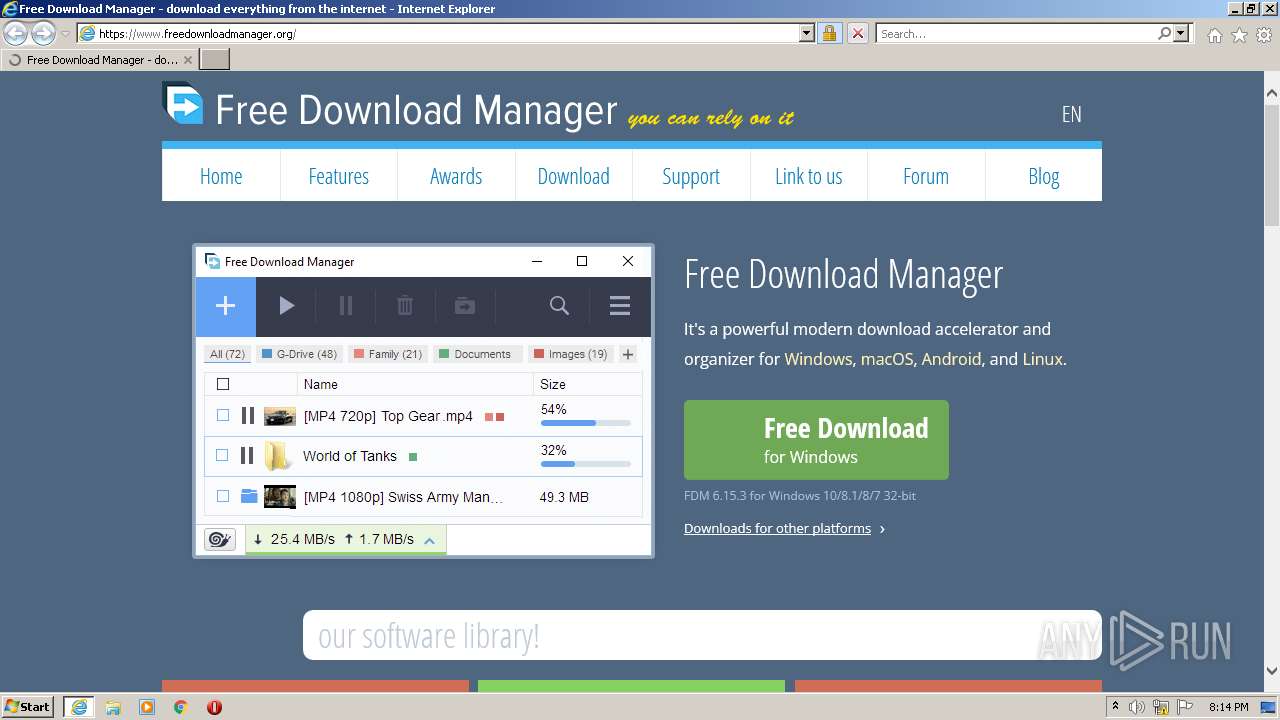
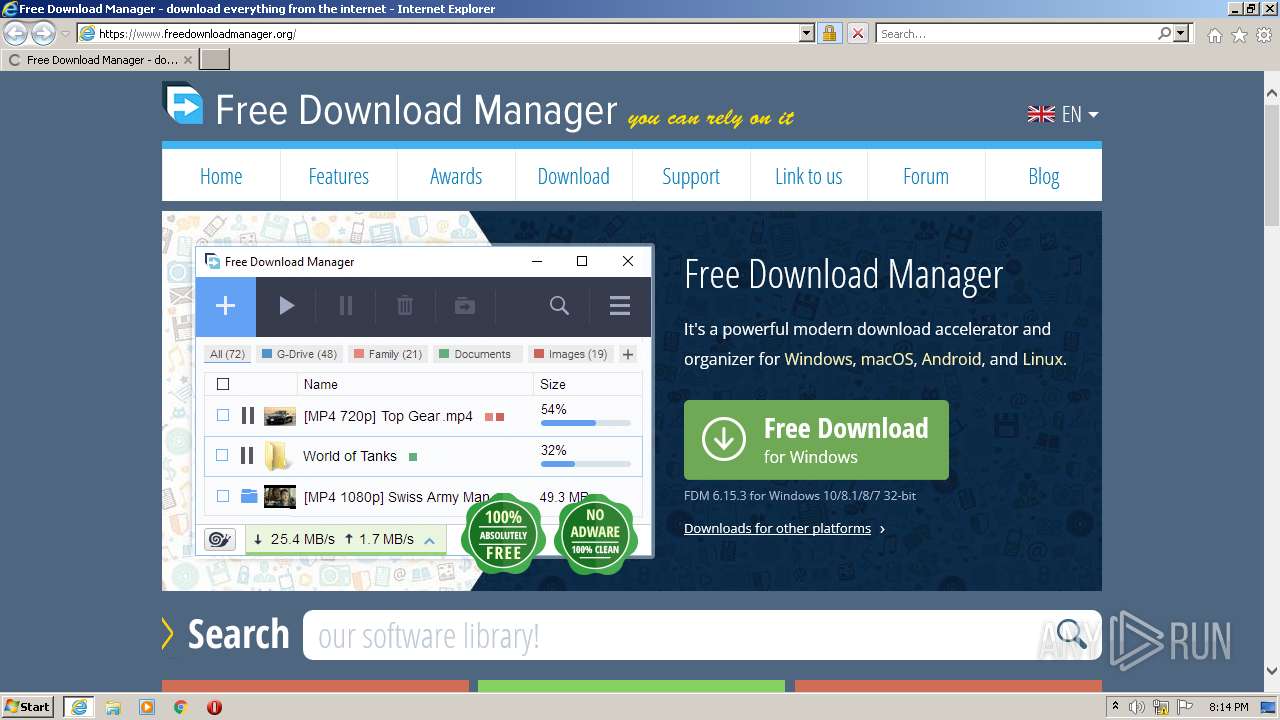
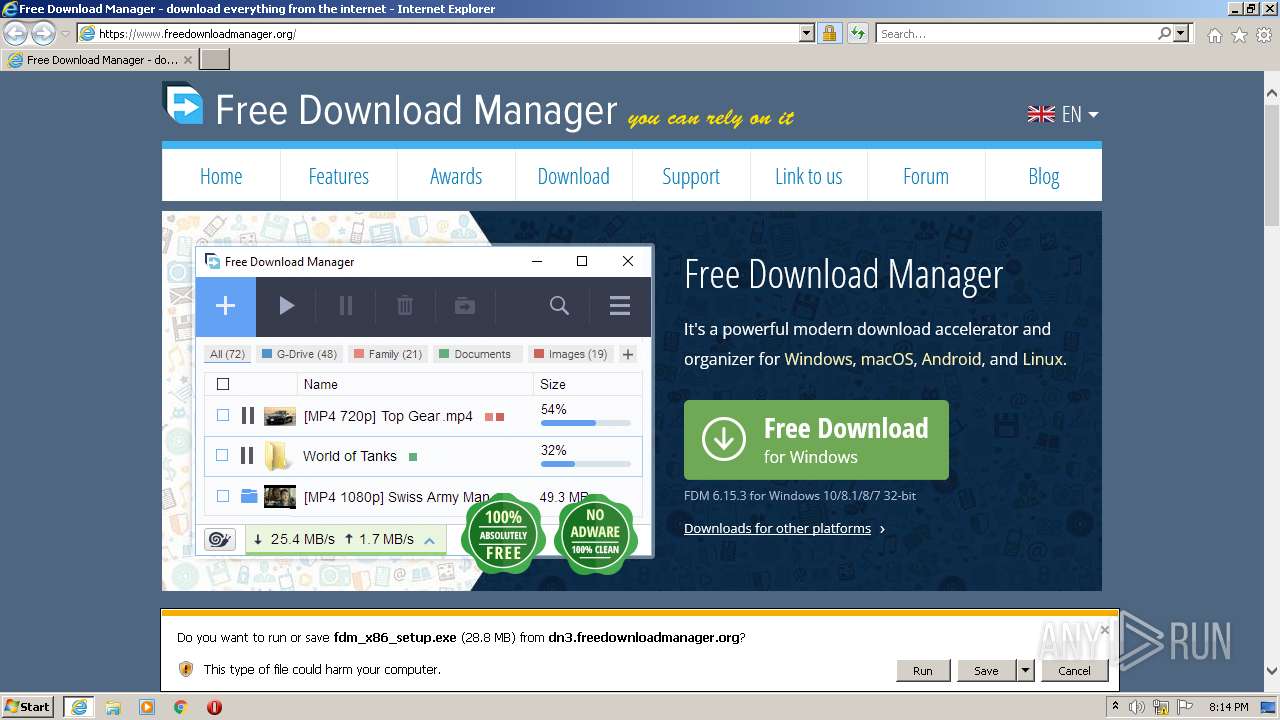
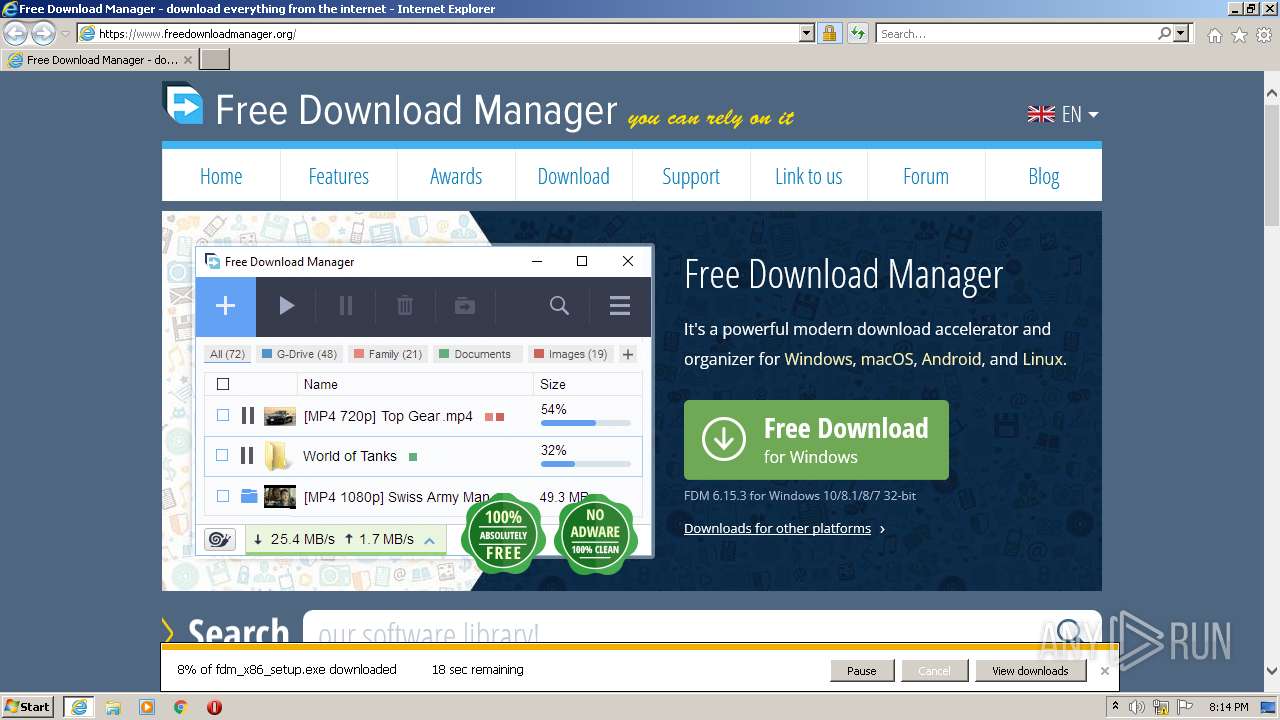
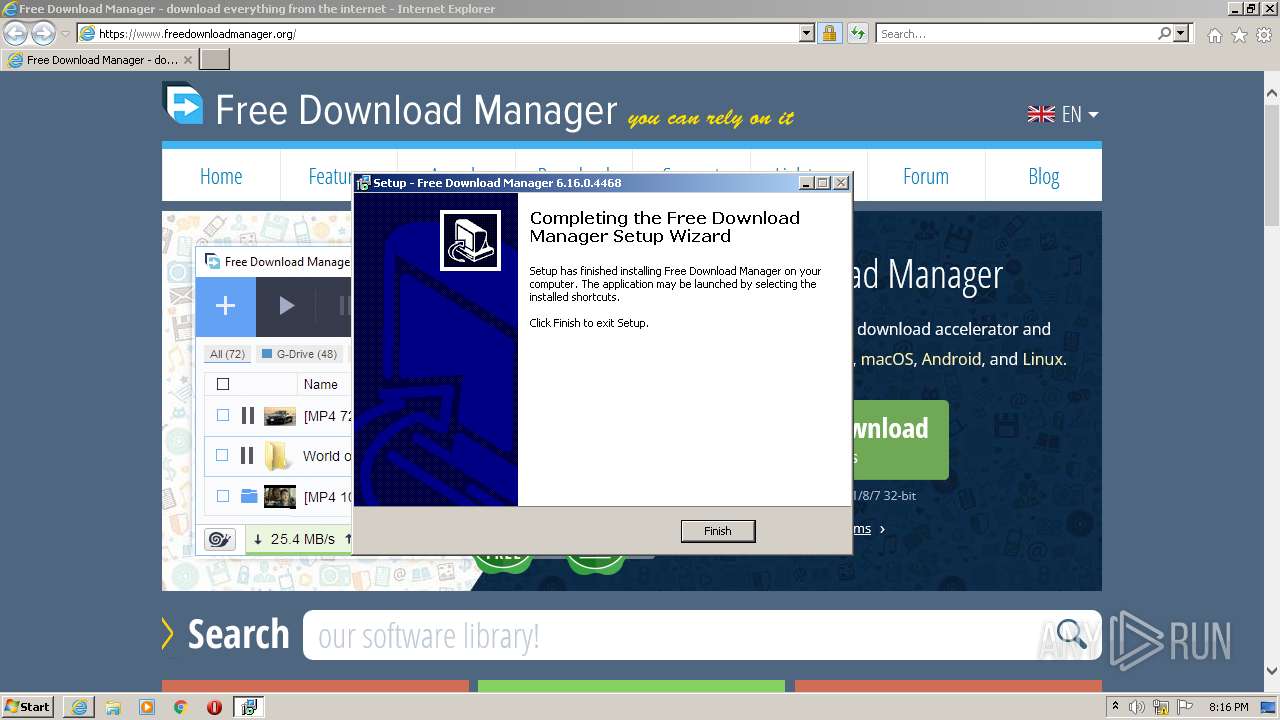
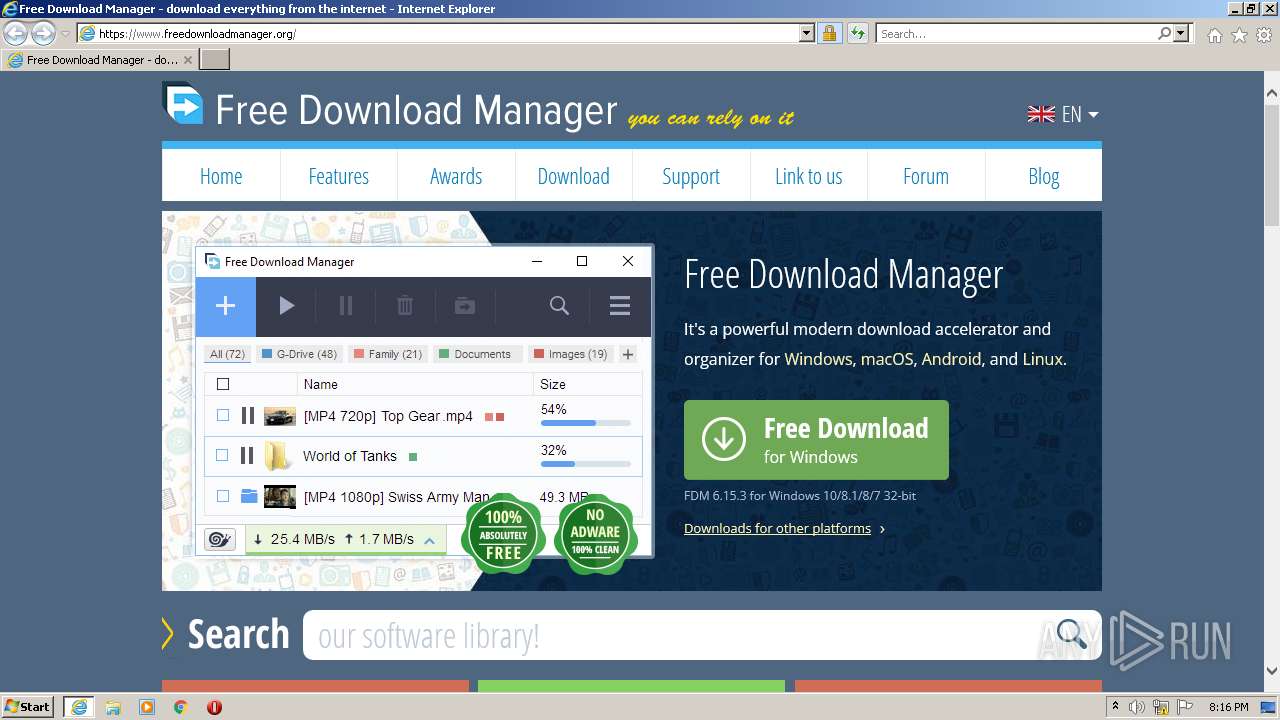
| URL: | https://www.freedownloadmanager.org/ |
| Full analysis: | https://app.any.run/tasks/109c4396-deea-4a11-81b3-0597a54e1994 |
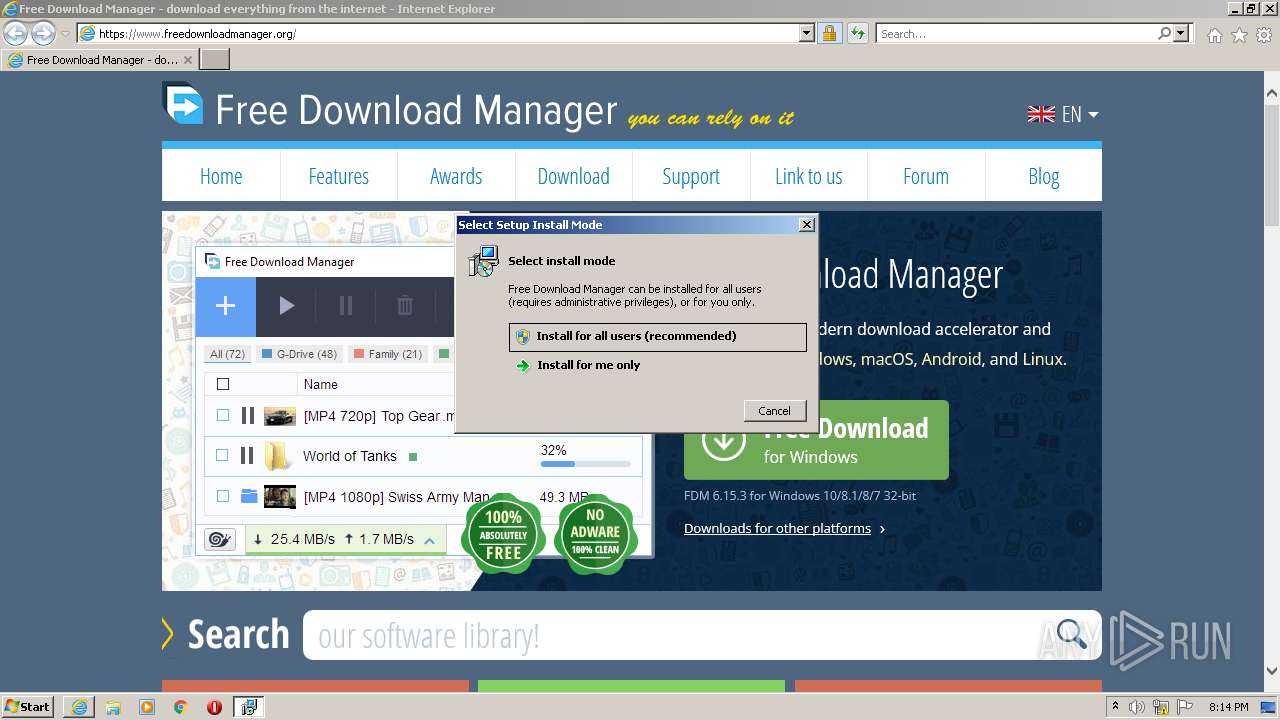
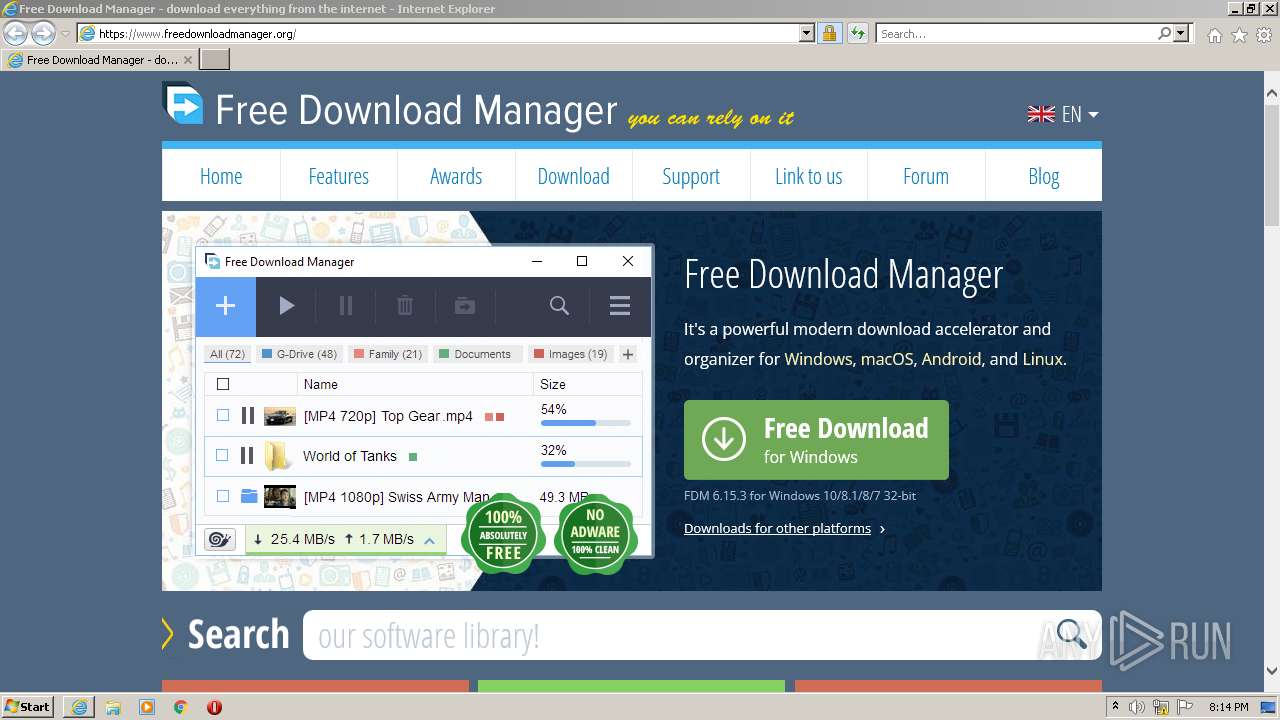
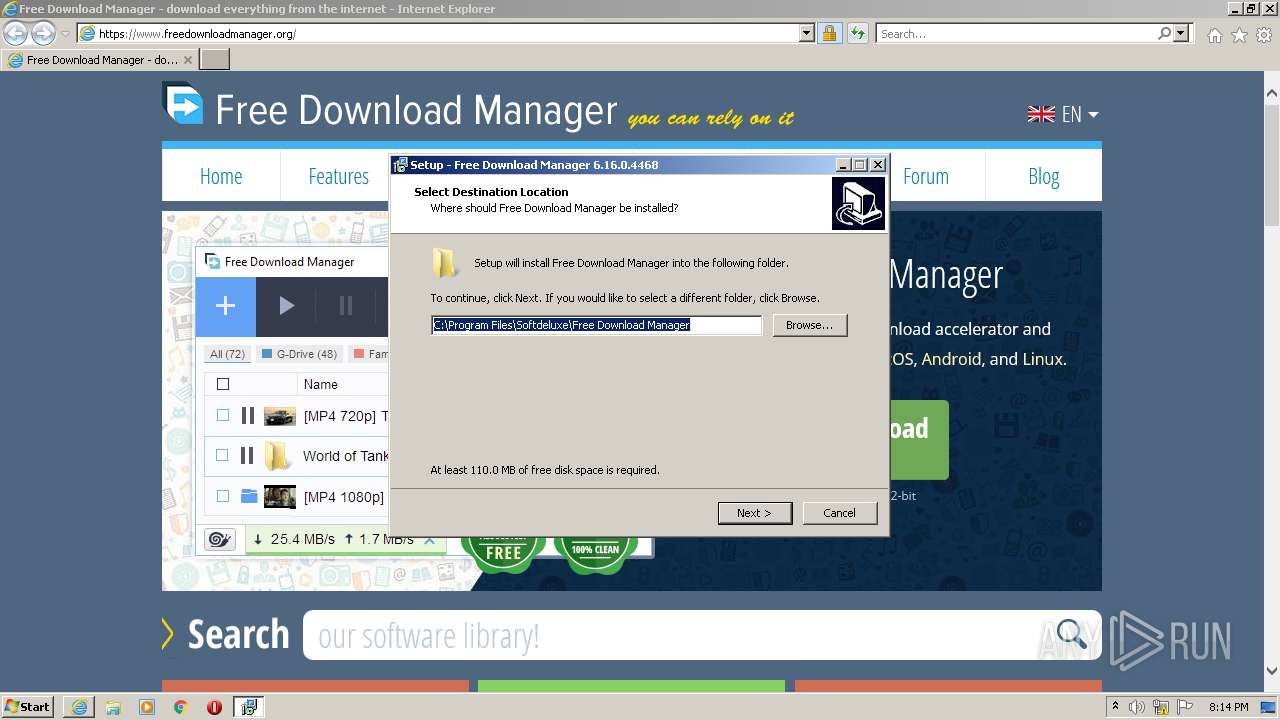
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2022, 20:14:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4D56C38C28CC8A5360D672DC2BB14B56 |
| SHA1: | 50D32BA1CCA503765861B2B934F785C4E505966D |
| SHA256: | 553FD82D9FD1A3D4B98D5F989095345361F9B33EA579FDF5C4D113AA79AB39B7 |
| SSDEEP: | 3:N8DSLLHKVELUXoCKn:2OLHwXin |
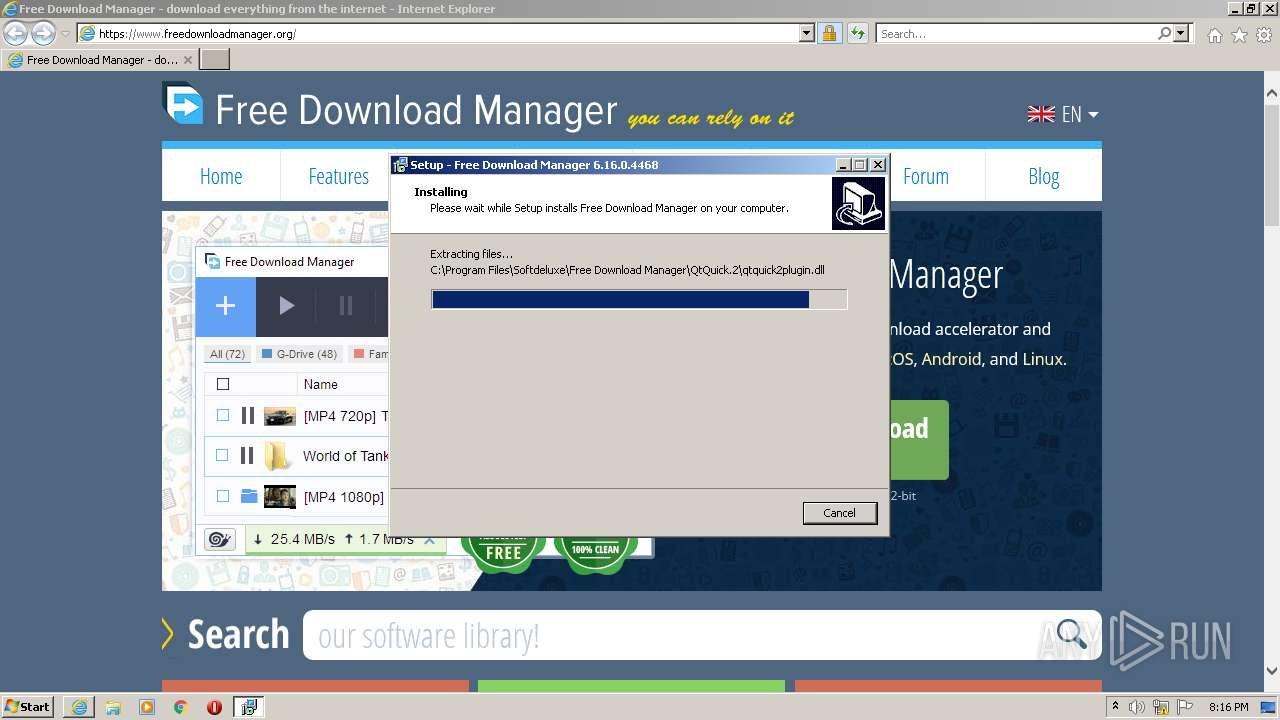
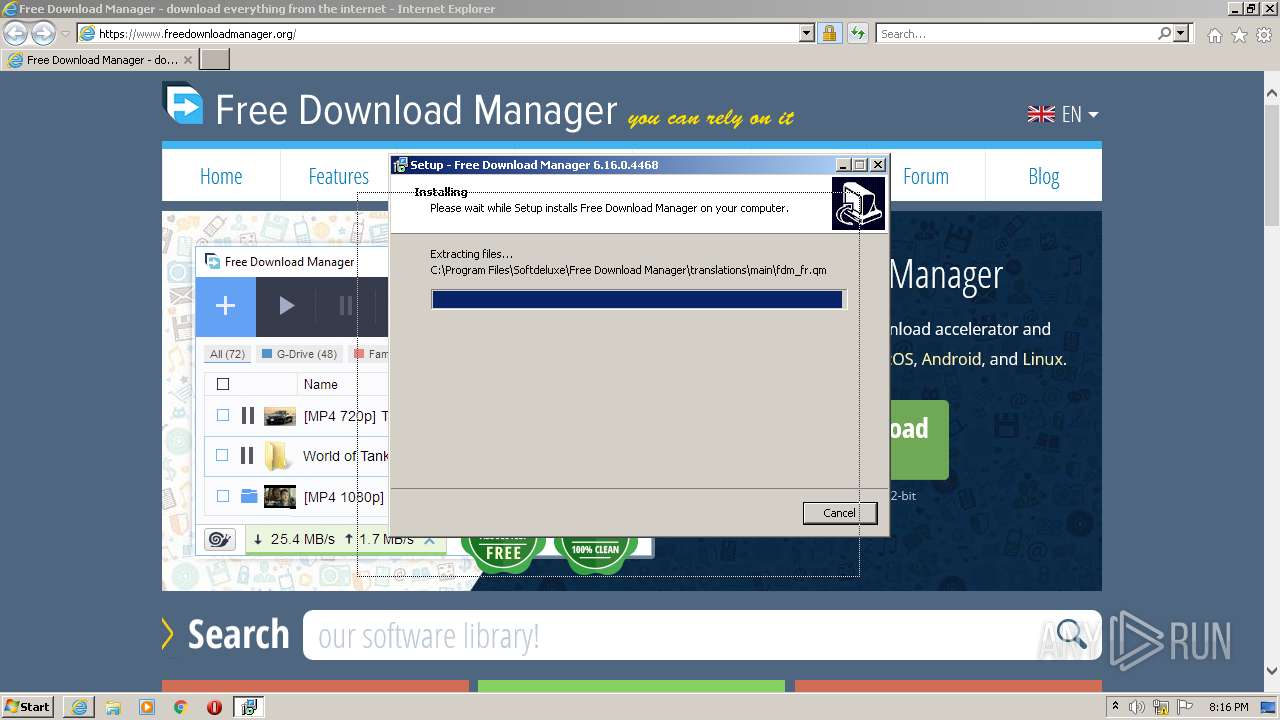
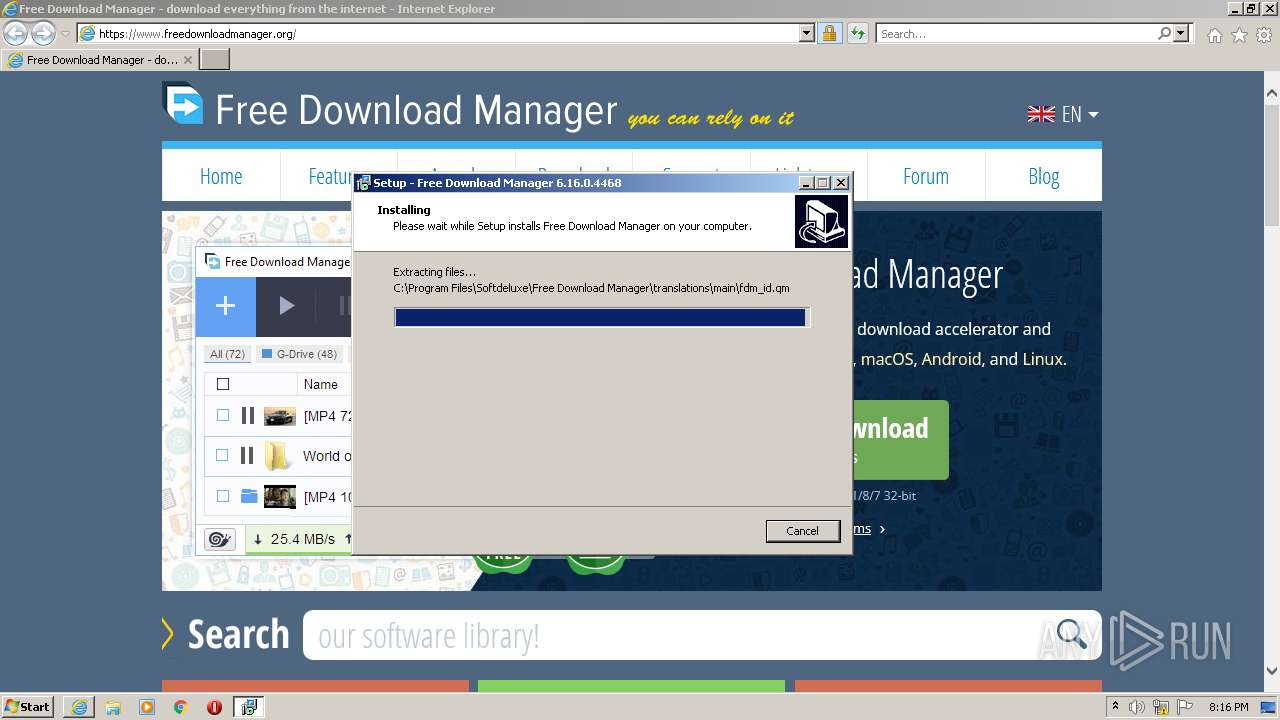
MALICIOUS
Application was dropped or rewritten from another process
- fdm_x86_setup.exe (PID: 2244)
- fdm_x86_setup.exe (PID: 3464)
- fdm.exe (PID: 3572)
- helperservice.exe (PID: 3976)
- importwizard.exe (PID: 3172)
- fdm5rhwin.exe (PID: 560)
- fdm5rhwin.exe (PID: 2088)
- fdm.exe (PID: 2428)
- importwizard.exe (PID: 3416)
Drops executable file immediately after starts
- fdm_x86_setup.exe (PID: 3464)
- fdm_x86_setup.exe (PID: 2244)
Uses Task Scheduler to run other applications
- fdm_x86_setup.tmp (PID: 2484)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 188)
- schtasks.exe (PID: 3568)
- schtasks.exe (PID: 3708)
- schtasks.exe (PID: 3860)
Loads dropped or rewritten executable
- fdm.exe (PID: 3572)
- helperservice.exe (PID: 3976)
- importwizard.exe (PID: 3172)
- fdm.exe (PID: 2428)
- importwizard.exe (PID: 3416)
Changes the autorun value in the registry
- fdm.exe (PID: 3572)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3760)
Executable content was dropped or overwritten
- fdm_x86_setup.exe (PID: 2244)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2120)
- fdm_x86_setup.exe (PID: 3464)
- fdm_x86_setup.tmp (PID: 2484)
Checks supported languages
- fdm_x86_setup.exe (PID: 2244)
- fdm_x86_setup.tmp (PID: 2392)
- fdm_x86_setup.tmp (PID: 2484)
- fdm_x86_setup.exe (PID: 3464)
- helperservice.exe (PID: 3976)
- fdm.exe (PID: 3572)
- importwizard.exe (PID: 3172)
- fdm5rhwin.exe (PID: 560)
- fdm5rhwin.exe (PID: 2088)
- fdm.exe (PID: 2428)
- importwizard.exe (PID: 3416)
Reads the computer name
- fdm_x86_setup.tmp (PID: 2392)
- fdm_x86_setup.tmp (PID: 2484)
- fdm.exe (PID: 3572)
- fdm.exe (PID: 2428)
Reads Windows owner or organization settings
- fdm_x86_setup.tmp (PID: 2484)
Reads the Windows organization settings
- fdm_x86_setup.tmp (PID: 2484)
Drops a file with a compile date too recent
- fdm_x86_setup.tmp (PID: 2484)
Creates files in the user directory
- fdm_x86_setup.tmp (PID: 2484)
Changes IE settings (feature browser emulation)
- fdm_x86_setup.tmp (PID: 2484)
Drops a file that was compiled in debug mode
- fdm_x86_setup.tmp (PID: 2484)
Executed via Task Scheduler
- helperservice.exe (PID: 3976)
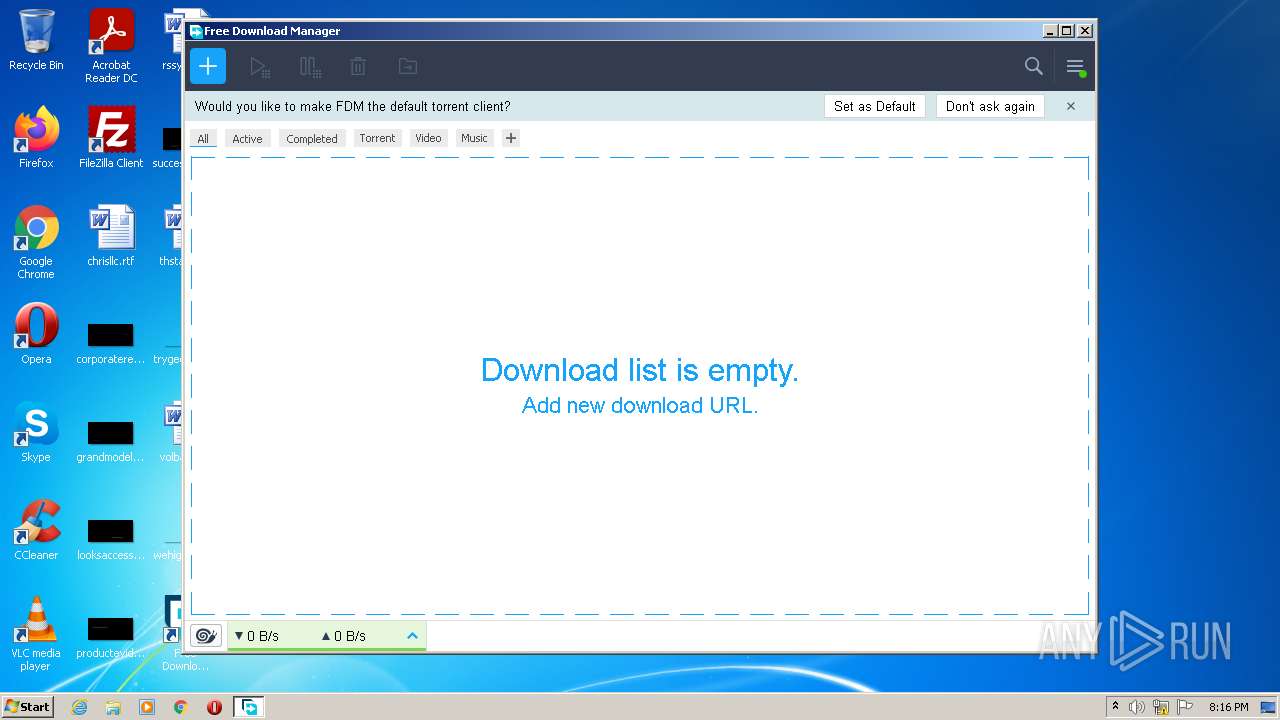
Starts Internet Explorer
- fdm.exe (PID: 3572)
Searches for installed software
- fdm5rhwin.exe (PID: 560)
- fdm5rhwin.exe (PID: 2088)
Reads Environment values
- netsh.exe (PID: 120)
- netsh.exe (PID: 3208)
Uses NETSH.EXE for network configuration
- fdm_x86_setup.tmp (PID: 2484)
Changes default file association
- fdm.exe (PID: 2428)
Creates a directory in Program Files
- fdm_x86_setup.tmp (PID: 2484)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3488)
INFO
Reads the computer name
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 2120)
- schtasks.exe (PID: 188)
- schtasks.exe (PID: 3568)
- schtasks.exe (PID: 3708)
- schtasks.exe (PID: 3860)
- iexplore.exe (PID: 1672)
- iexplore.exe (PID: 3760)
- netsh.exe (PID: 120)
- netsh.exe (PID: 3208)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2272)
Application launched itself
- iexplore.exe (PID: 3556)
- chrome.exe (PID: 3488)
Checks supported languages
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3556)
- schtasks.exe (PID: 188)
- schtasks.exe (PID: 3568)
- schtasks.exe (PID: 3708)
- schtasks.exe (PID: 3860)
- iexplore.exe (PID: 1672)
- iexplore.exe (PID: 3760)
- netsh.exe (PID: 120)
- netsh.exe (PID: 3208)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 976)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 2708)
- chrome.exe (PID: 1312)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3036)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 1452)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2272)
Checks Windows Trust Settings
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 3760)
Reads internet explorer settings
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3760)
Changes internet zones settings
- iexplore.exe (PID: 3556)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3556)
Reads settings of System Certificates
- iexplore.exe (PID: 2120)
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 3760)
- chrome.exe (PID: 2188)
- fdm.exe (PID: 2428)
Changes settings of System certificates
- iexplore.exe (PID: 3556)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3556)
Application was dropped or rewritten from another process
- fdm_x86_setup.tmp (PID: 2392)
- fdm_x86_setup.tmp (PID: 2484)
Creates files in the user directory
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 3760)
Creates a software uninstall entry
- fdm_x86_setup.tmp (PID: 2484)
Dropped object may contain Bitcoin addresses
- fdm_x86_setup.tmp (PID: 2484)
Creates files in the program directory
- fdm_x86_setup.tmp (PID: 2484)
Reads the date of Windows installation
- iexplore.exe (PID: 3556)
- chrome.exe (PID: 2272)
Manual execution by user
- chrome.exe (PID: 3488)
Reads the hosts file
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
37
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "netsh.exe" firewall add allowedprogram program="C:\Program Files\Softdeluxe\Free Download Manager\fdm.exe" name="Free Download Manager" ENABLE scope=ALL profile=ALL | C:\Windows\system32\netsh.exe | — | fdm_x86_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | "schtasks.exe" /end /tn FreeDownloadManagerHelperService | C:\Windows\system32\schtasks.exe | — | fdm_x86_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | "C:\Program Files\Softdeluxe\Free Download Manager\fdm5rhwin.exe" 21907CB0205CFF989F82C03684A01B86 phase1 | C:\Program Files\Softdeluxe\Free Download Manager\fdm5rhwin.exe | — | fdm_x86_setup.tmp | |||||||||||
User: admin Company: Softdeluxe Integrity Level: HIGH Description: Free Download Manager Exit code: 1 Version: 6.16.0.4468 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12949790135020609366,5502617911079038696,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12949790135020609366,5502617911079038696,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1068,12949790135020609366,5502617911079038696,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2940 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12949790135020609366,5502617911079038696,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
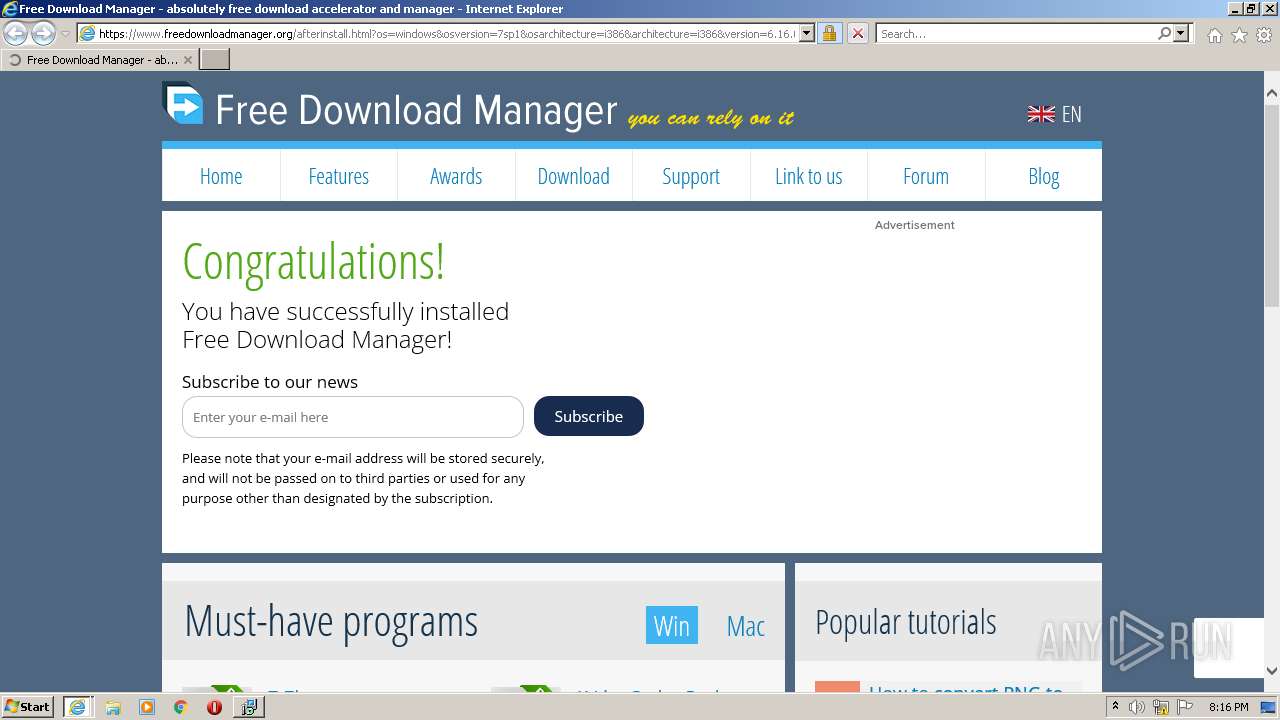
| 1672 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.freedownloadmanager.org/afterinstall.html?os=windows&osversion=7sp1&osarchitecture=i386&architecture=i386&version=6.16.0.4468&uuid=5b71fa37-8964-486e-99d4-505e4b7aa72e&locale=en_US&ac=1&au=1 | C:\Program Files\Internet Explorer\iexplore.exe | — | fdm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Softdeluxe\Free Download Manager\fdm5rhwin.exe" 21907CB0205CFF989F82C03684A01B86 phase2 | C:\Program Files\Softdeluxe\Free Download Manager\fdm5rhwin.exe | — | fdm_x86_setup.tmp | |||||||||||
User: admin Company: Softdeluxe Integrity Level: HIGH Description: Free Download Manager Exit code: 1 Version: 6.16.0.4468 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3556 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
45 327
Read events
44 822
Write events
497
Delete events
8
Modification events
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30942870 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30942870 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
307
Suspicious files
939
Text files
1 325
Unknown types
206
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\index[1].css | text | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\QQ00DYQL.htm | html | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F2DDCD2B5F37625B82E81F4976CEE400_6D1A6BB068AC5192F6B6E5E6012FB974 | der | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B0072932F1C594C39661F7C8C24DF0D4 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
135
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCocHHgurGh6qOXCw3WX0C4 | US | der | 472 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCaHSGzPVJWThIAAAAAAGGw | US | der | 472 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEJSUTLL3p2xCgAAAAEz%2BUQ%3D | US | der | 471 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEC5GLYwFefbxEgAAAAAAYIc%3D | US | der | 471 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCYyccBU%2BO5JwoAAAABM%2FlK | US | der | 472 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEC5GLYwFefbxEgAAAAAAYIc%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDJmHVPyDipnxIAAAAAAF9n | US | der | 472 b | whitelisted |
2120 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA9kYXpA%2F4XAEgAAAAAAY4g%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | iexplore.exe | 199.101.132.243:443 | www.freedownloadmanager.org | WZ Communications Inc. | US | unknown |
2120 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3556 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2120 | iexplore.exe | 142.250.185.164:443 | www.google.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 142.250.181.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.freedownloadmanager.org |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
static.freedownloadmanager.org |
| suspicious |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
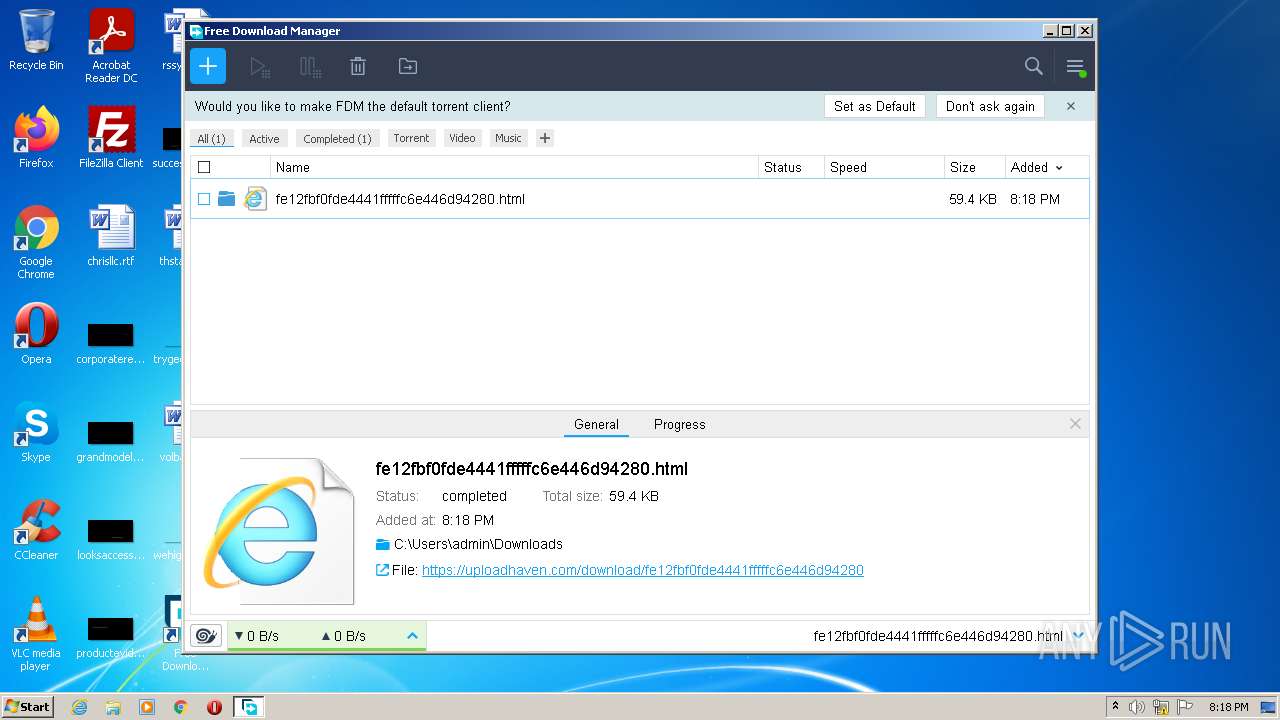
fdm.exe | qml: adding request id: 2 (downloadId: 2 )
|