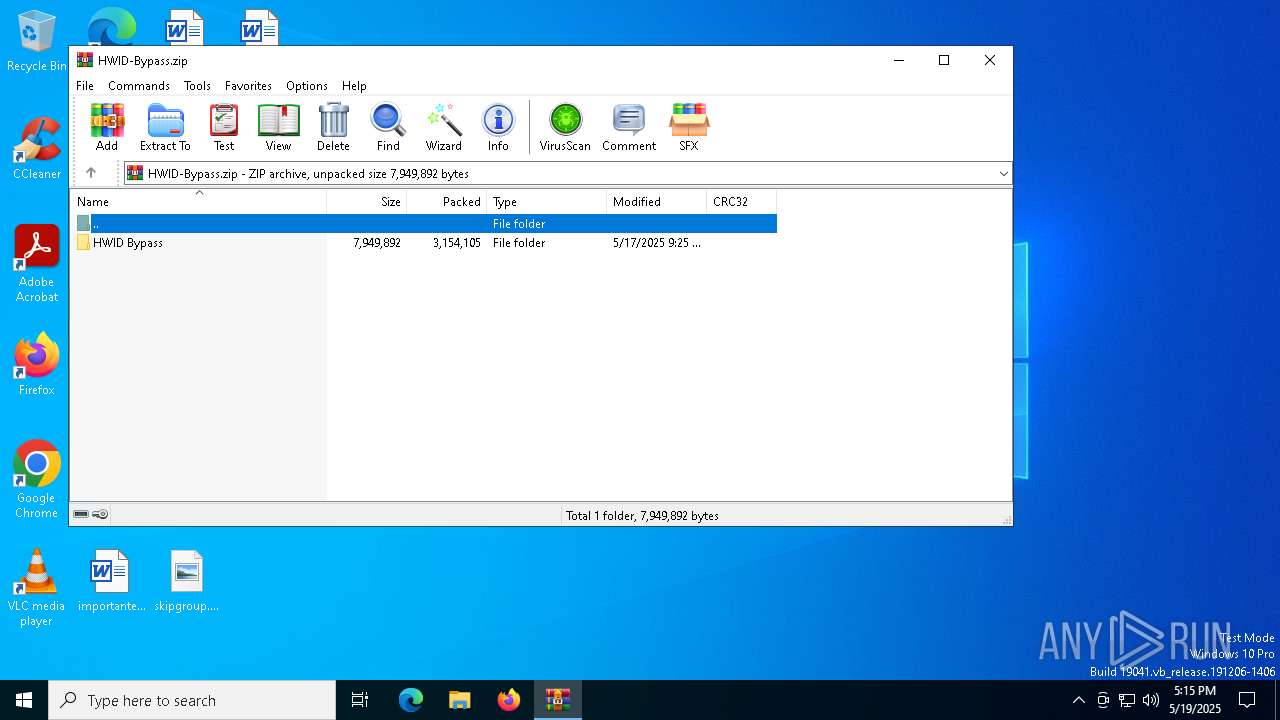
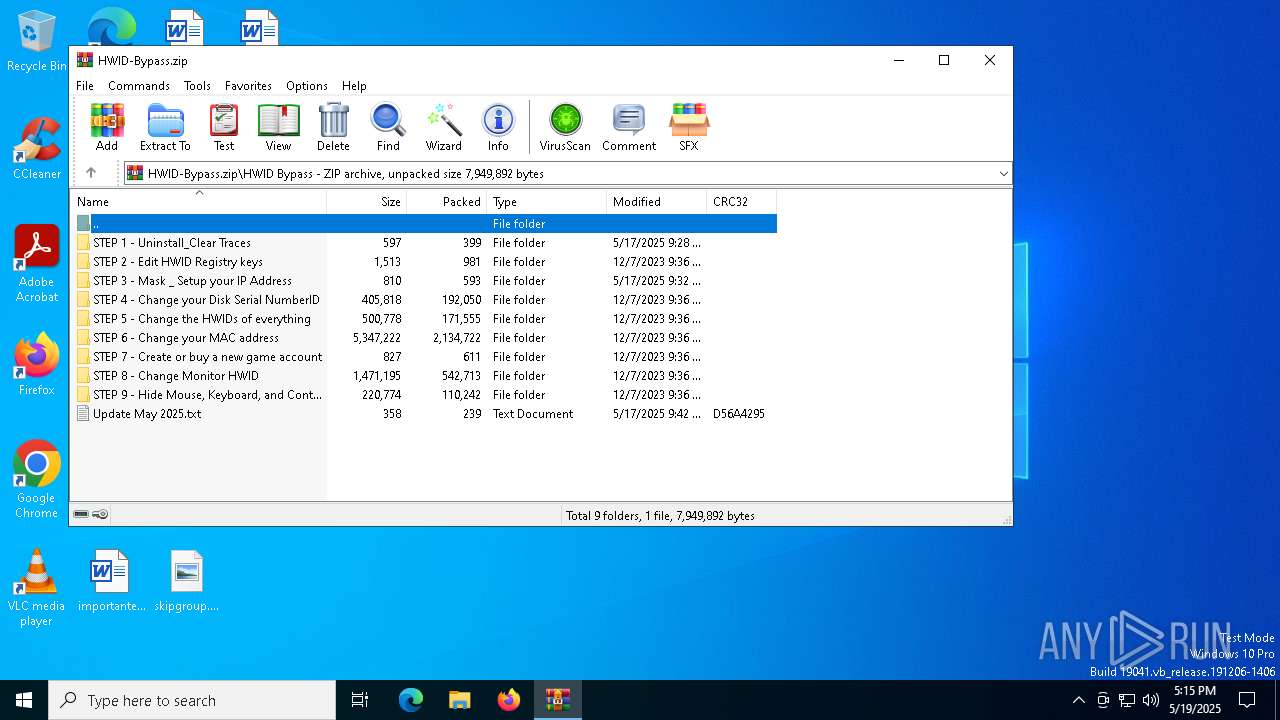
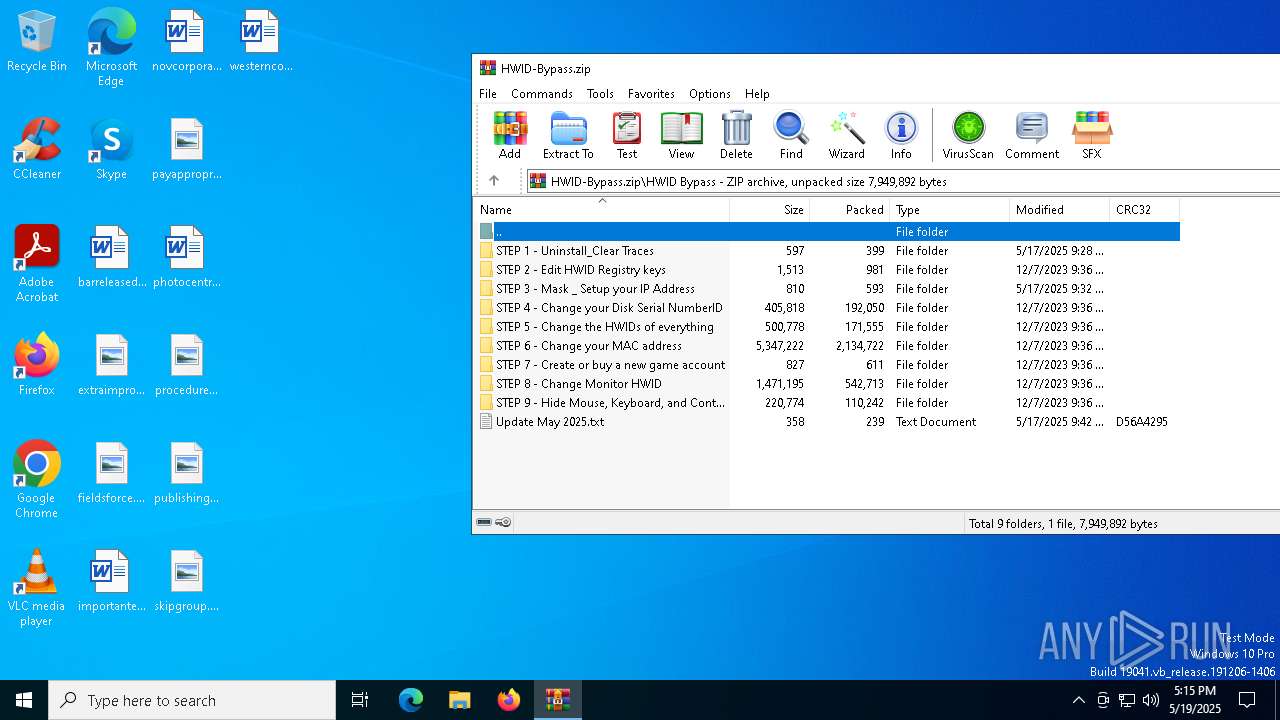
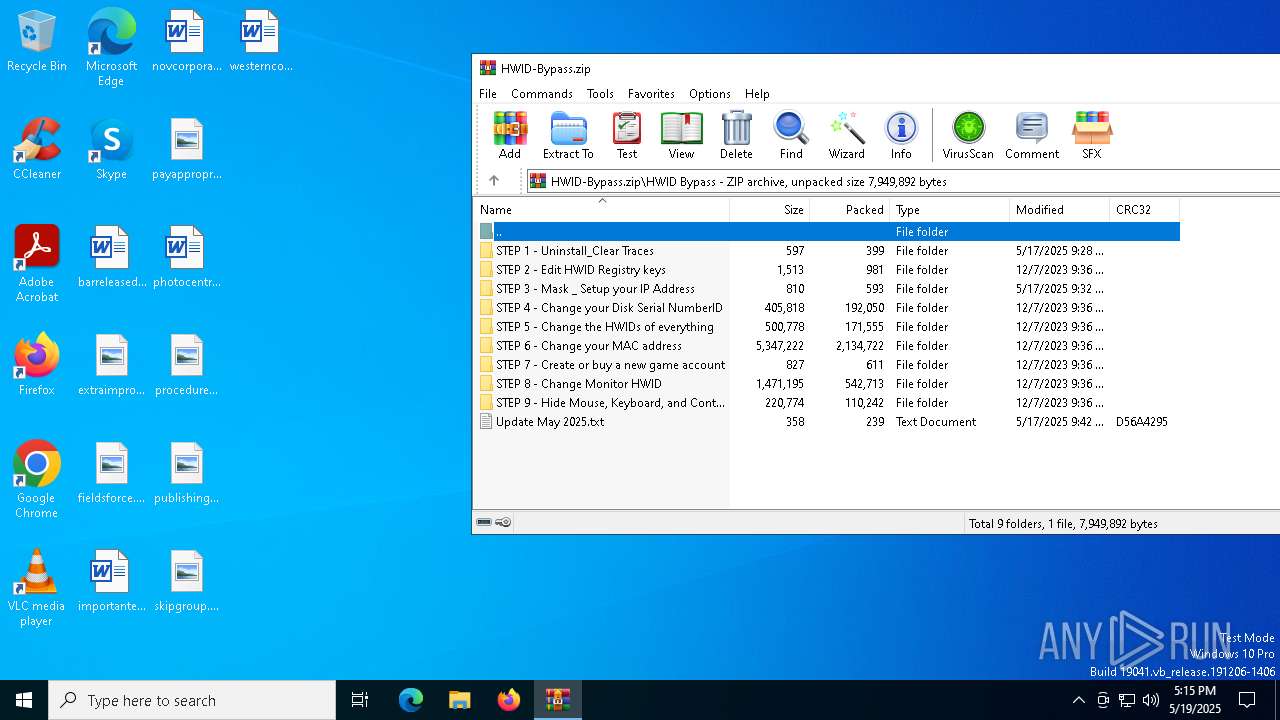
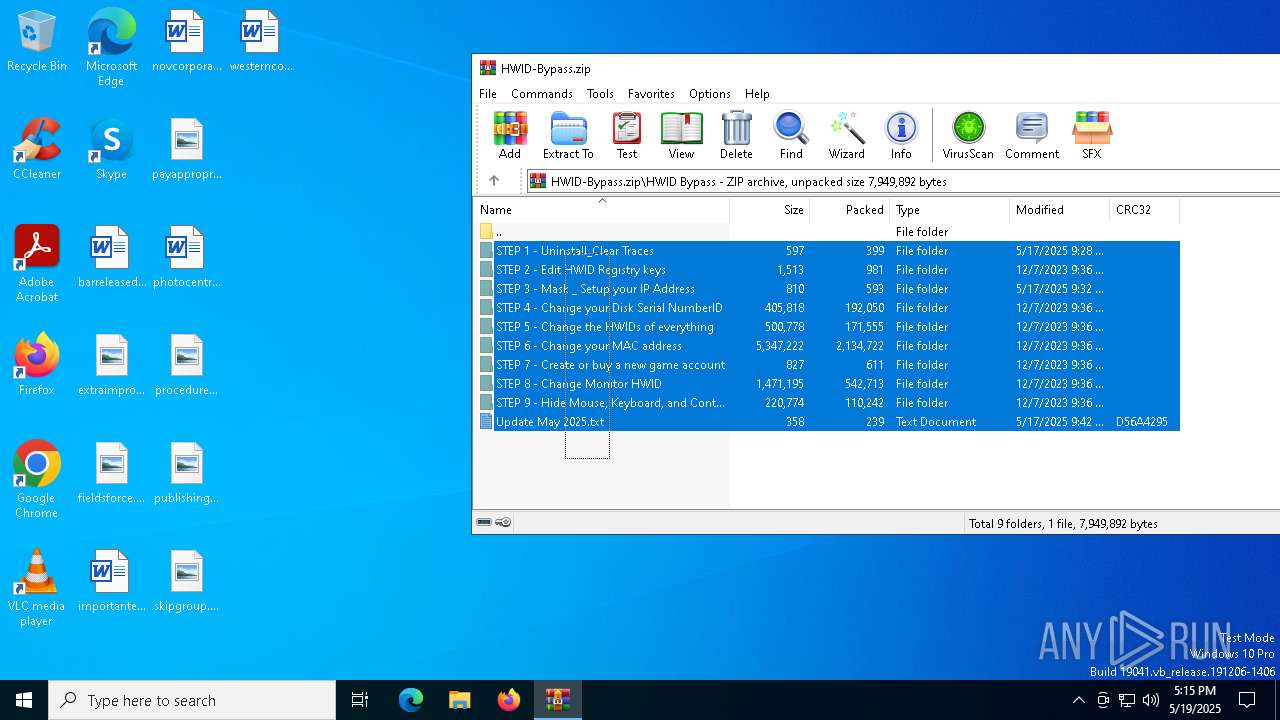
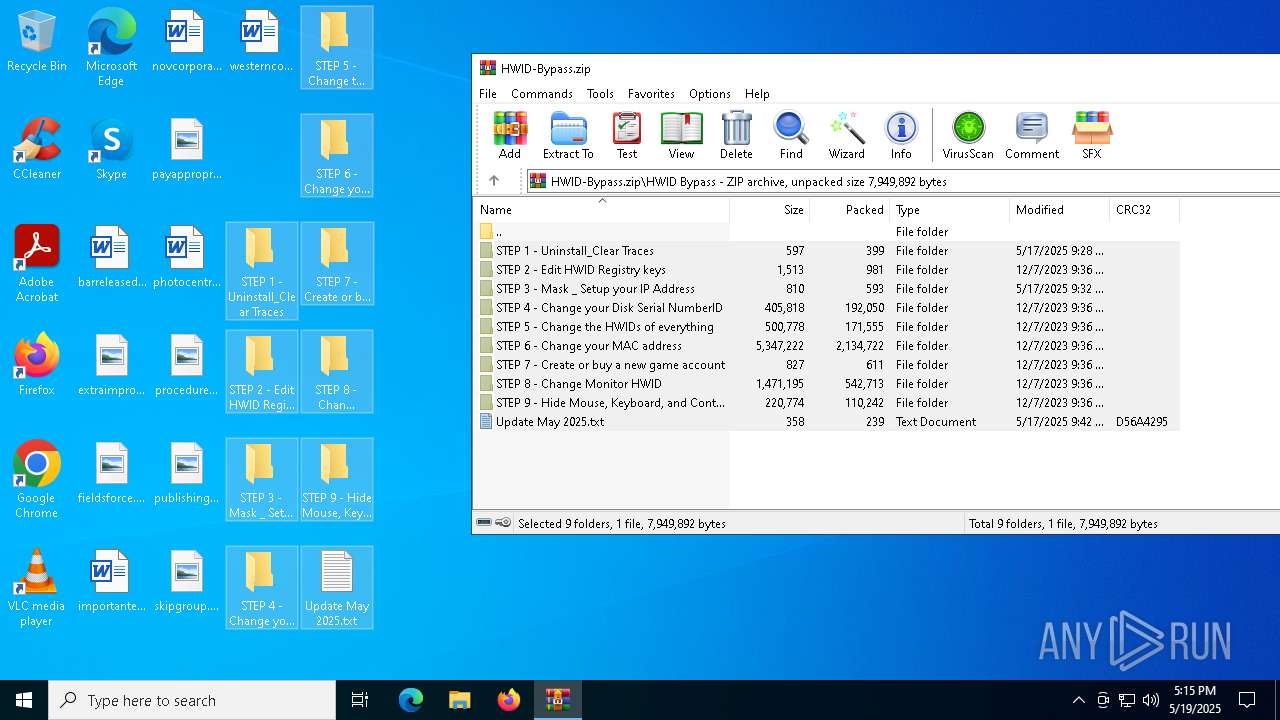
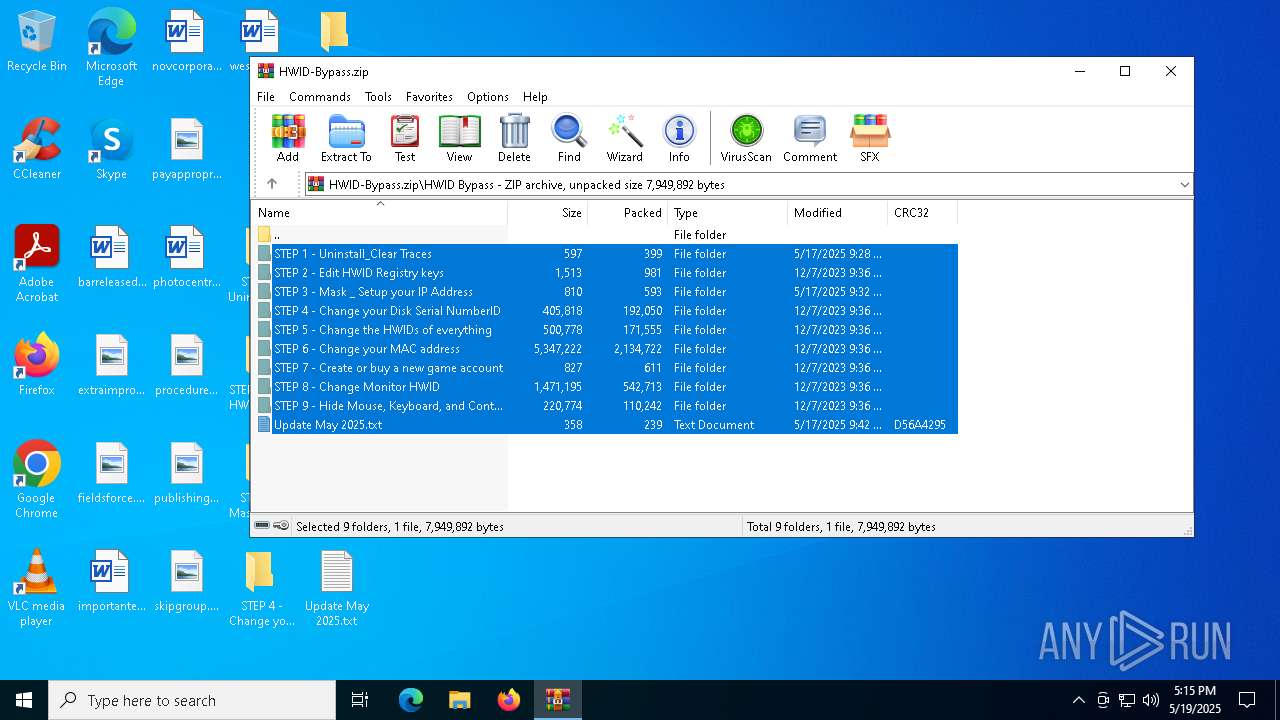
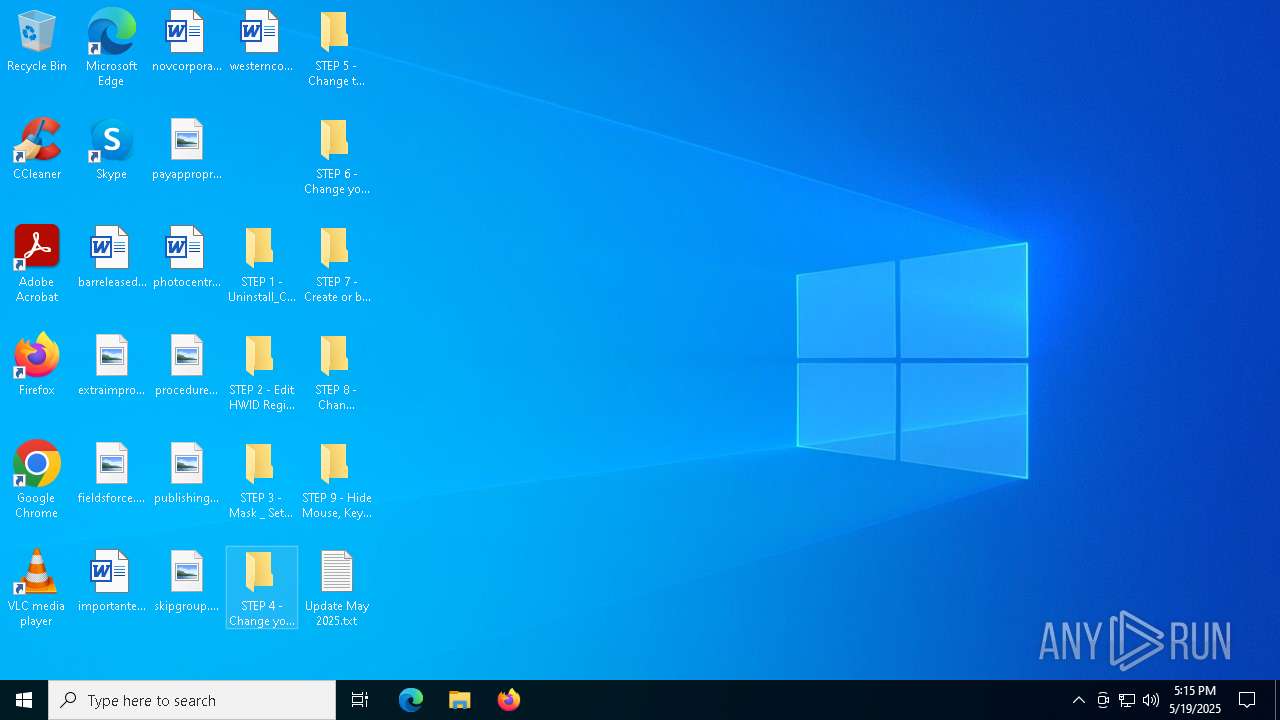
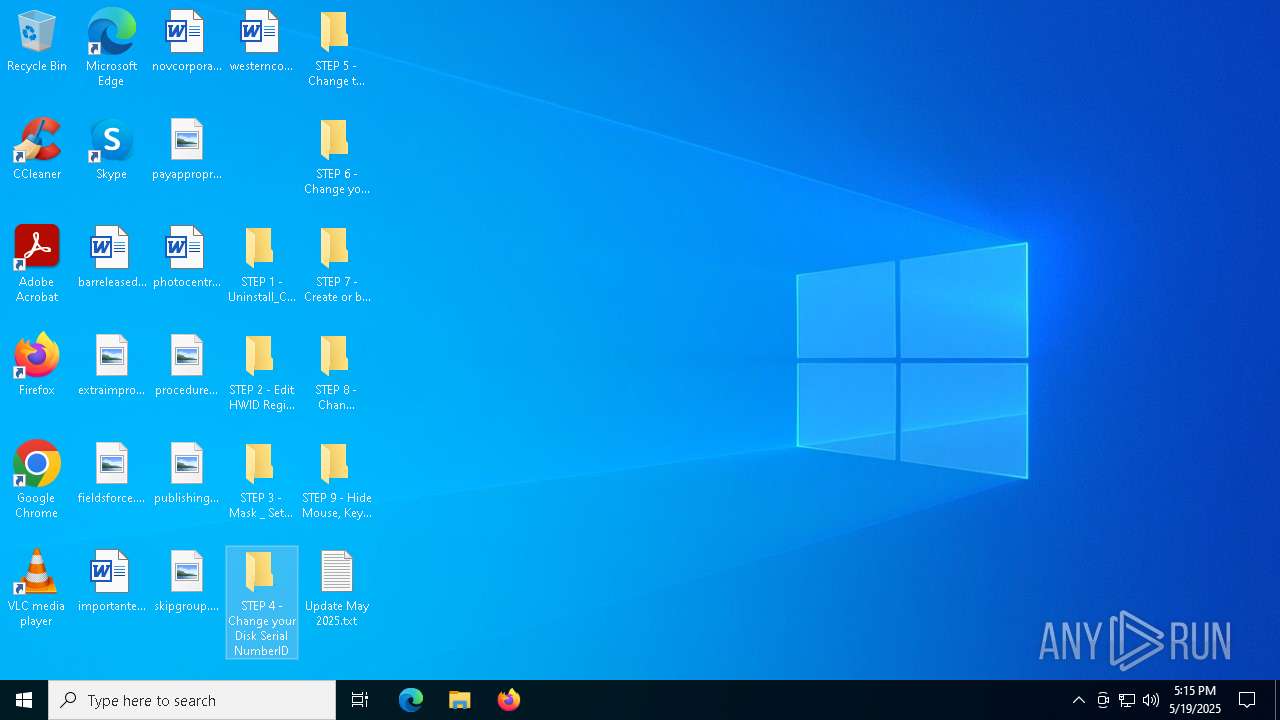
| File name: | HWID-Bypass.zip |
| Full analysis: | https://app.any.run/tasks/e1a6a802-55ae-413f-af99-2bcc47f978ef |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 17:15:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | E72190A060DC20F57F3F92708FB2C394 |
| SHA1: | 6D91E473A3B9E012DDD4F6A54A6C299CD23A7413 |
| SHA256: | 553FBC28506401379B938E293D4B47CA2133AA34A5CD09D8A6C8C02FE67BD5C7 |
| SSDEEP: | 98304:USgJwVuFCJBFy13WeumeMvwPFyiQwqVh+XMr1w4a5ThKVvE7X+sO2MvoNbJIZEyN:YsO6gF9P |
MALICIOUS
Vulnerable driver has been detected
- WinRAR.exe (PID: 4880)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 4880)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 4880)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4880)
Checks proxy server information
- slui.exe (PID: 8100)
Reads the software policy settings
- slui.exe (PID: 8100)
- slui.exe (PID: 7280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:18 00:25:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
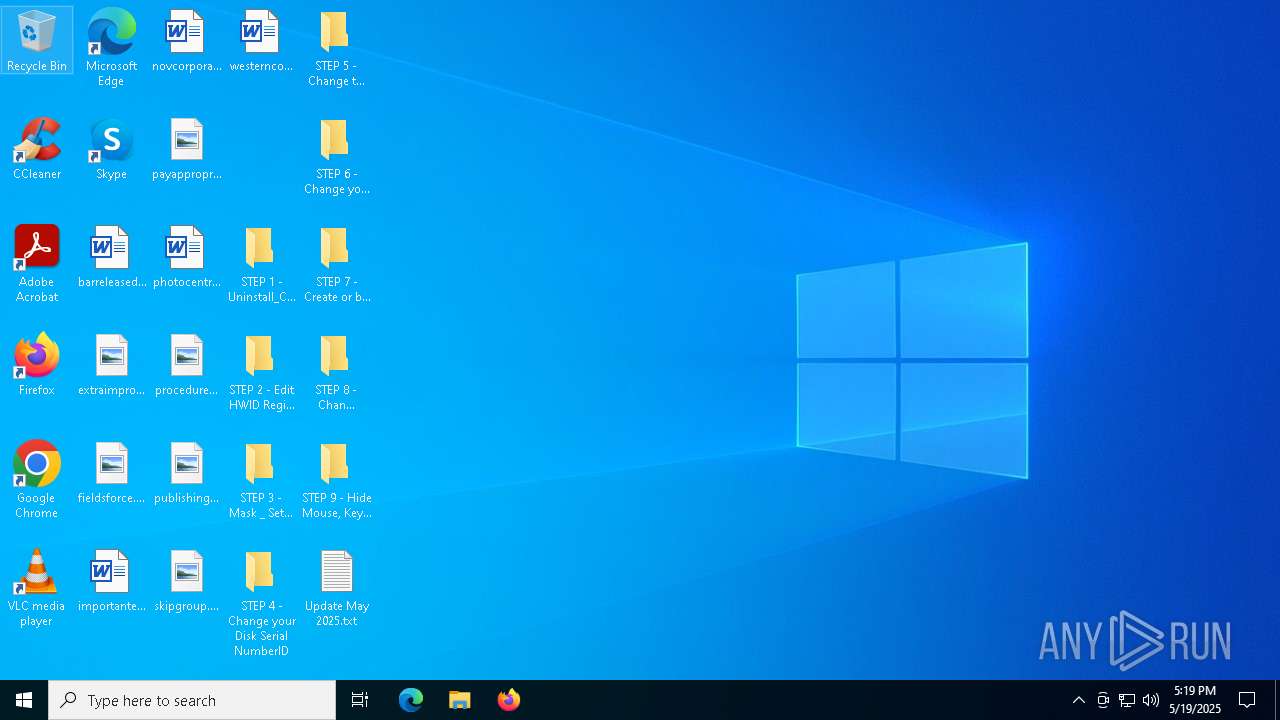
| ZipFileName: | HWID Bypass/ |
Total processes
140
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4880 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\HWID-Bypass.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7248 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 7280 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7780 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8100 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 723
Read events
2 705
Write events
18
Delete events
0
Modification events
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HWID-Bypass.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF200000038000000B204000021020000 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
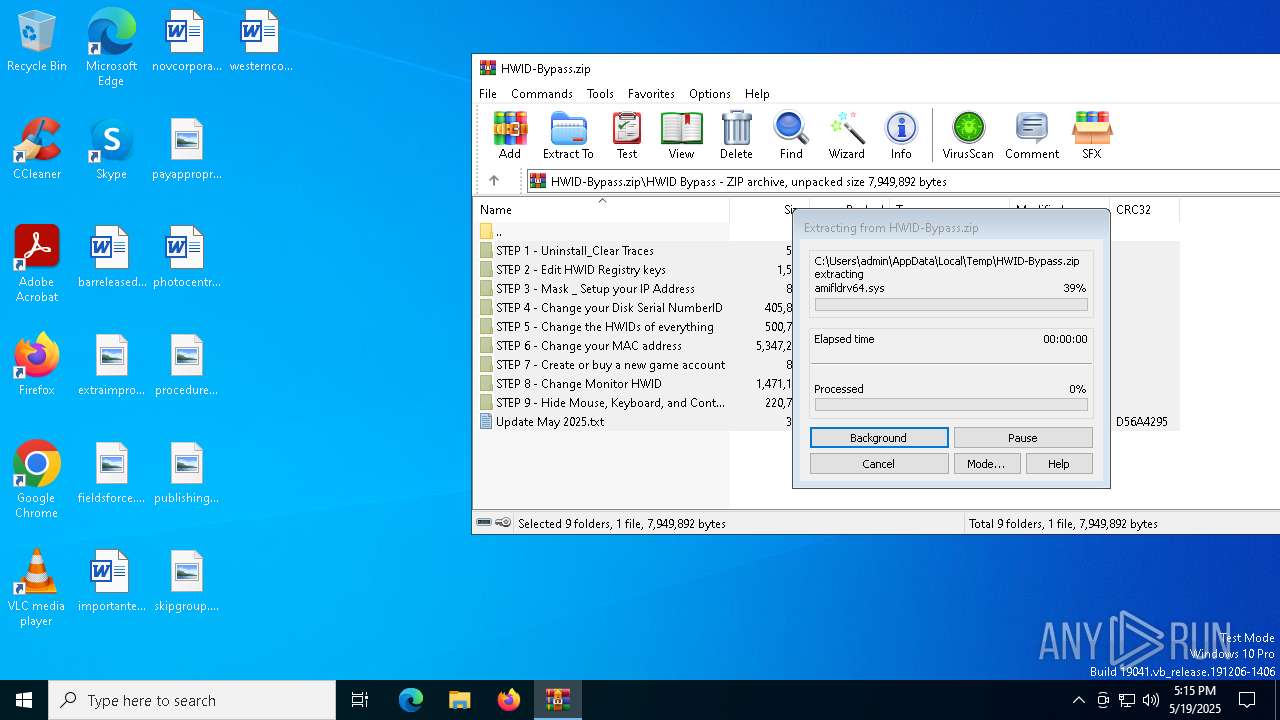
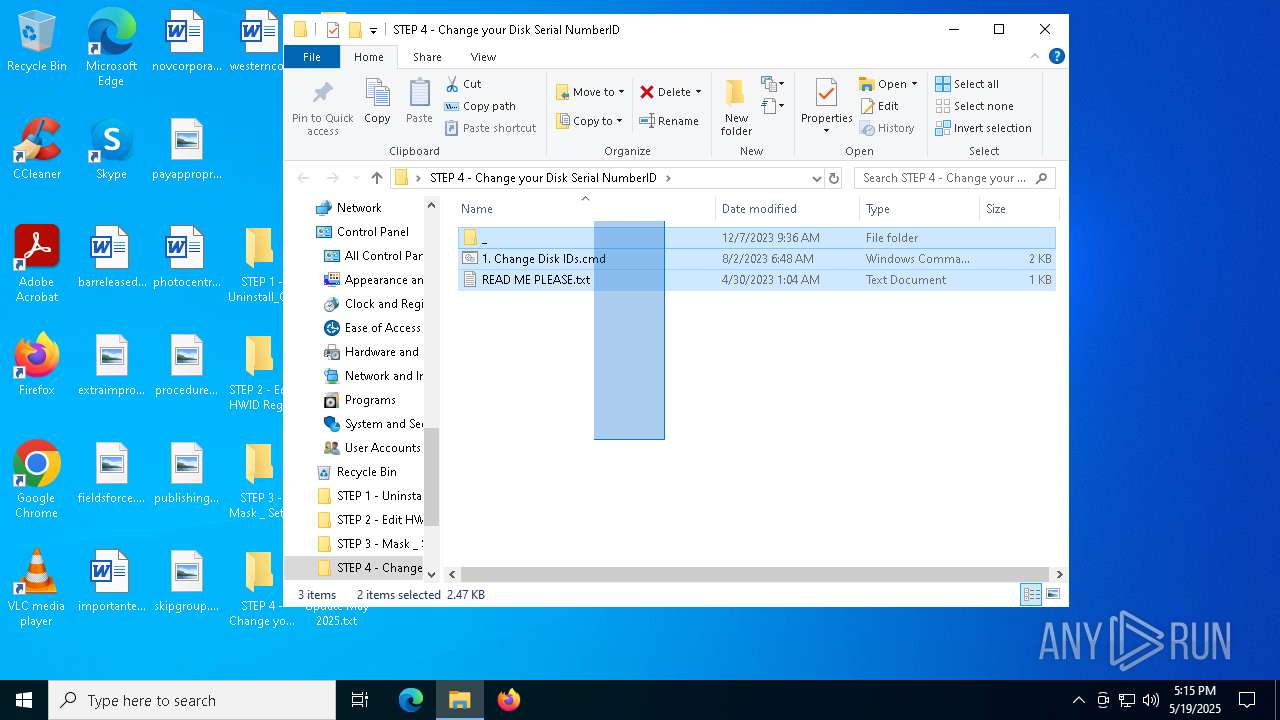
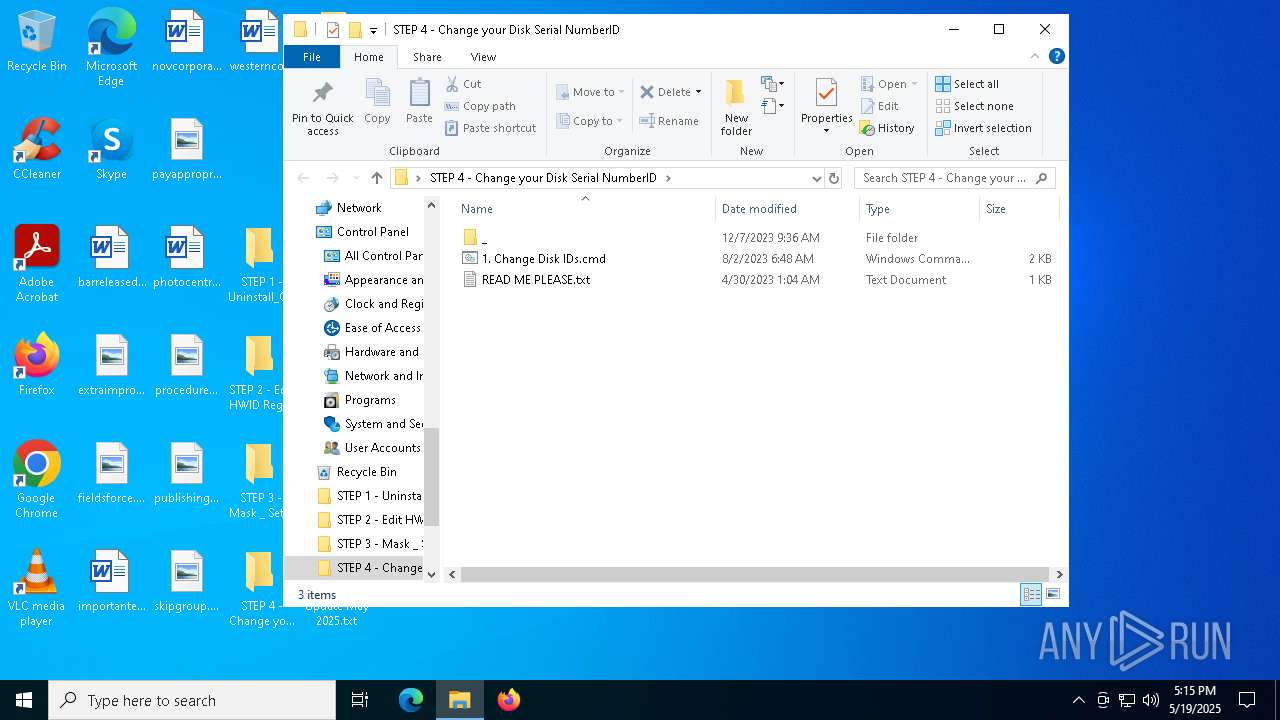
Executable files
10
Suspicious files
10
Text files
14
Unknown types
0
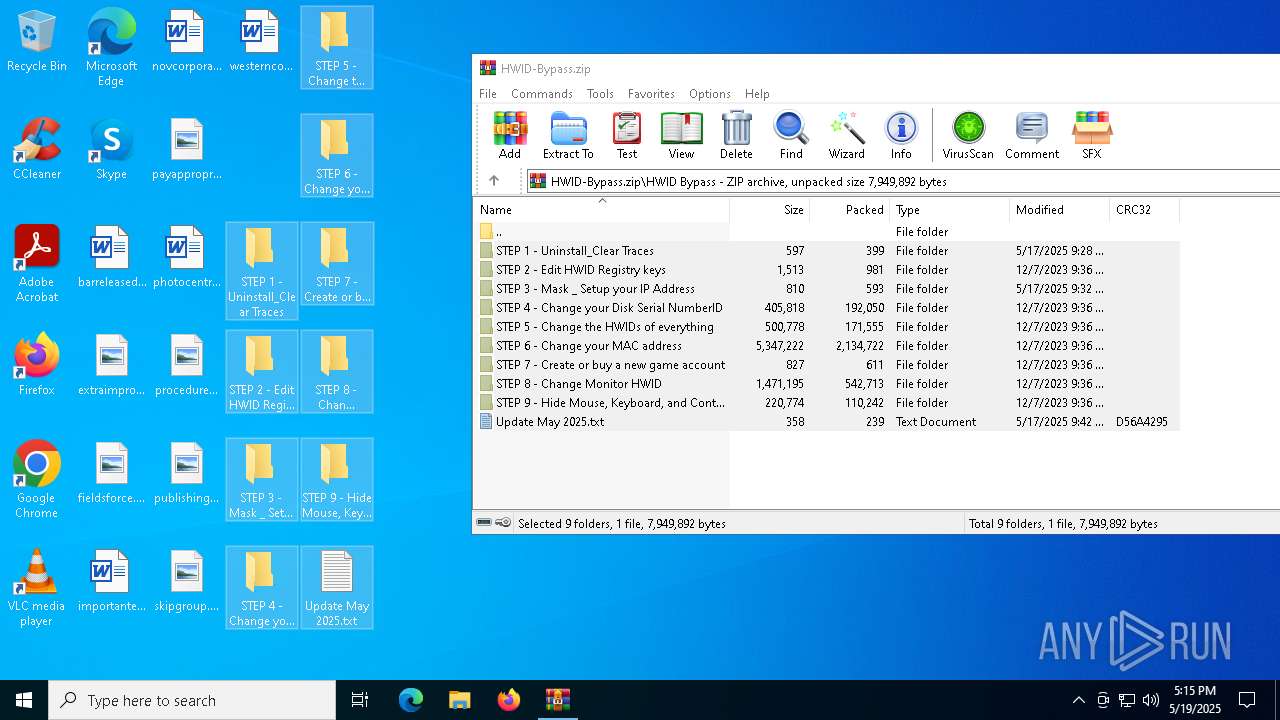
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
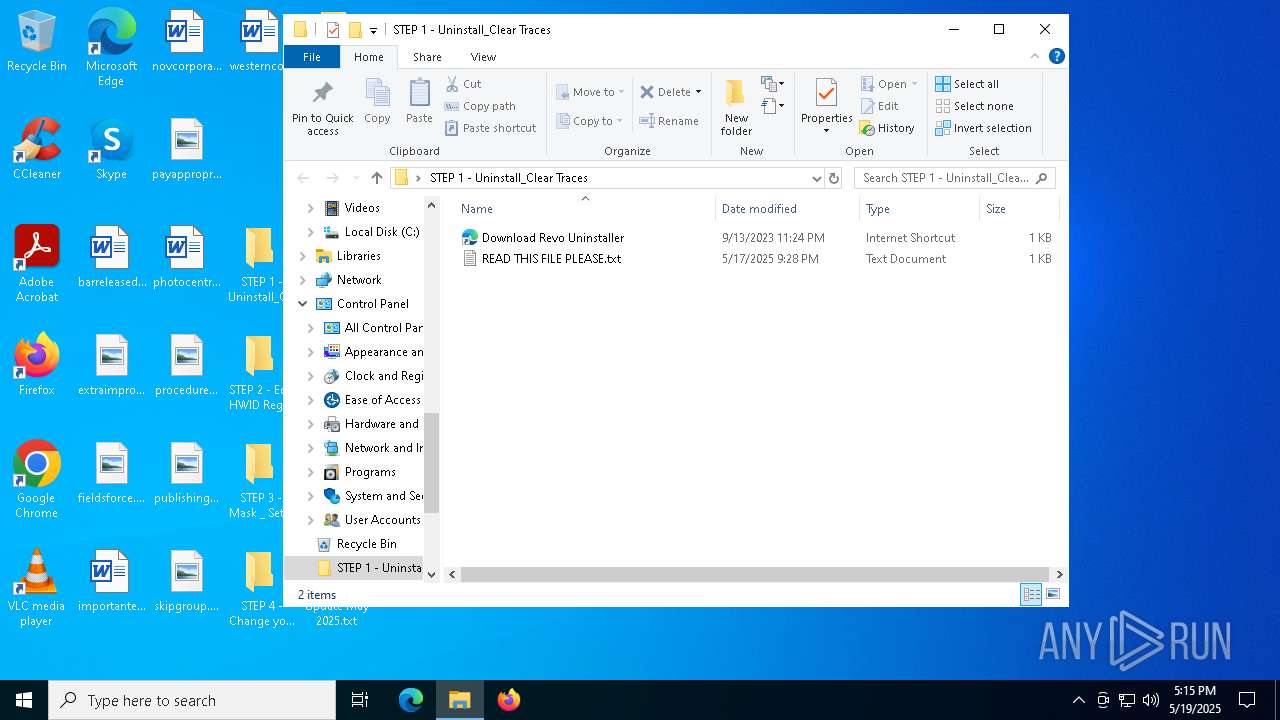
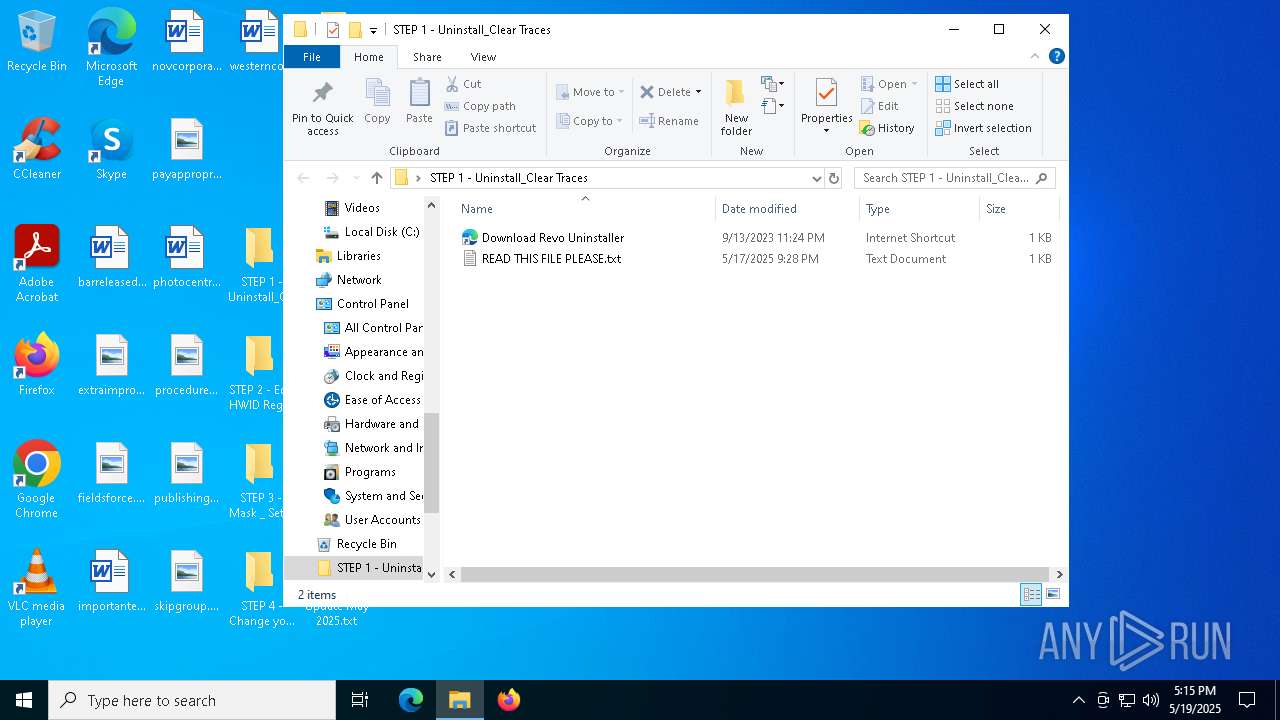
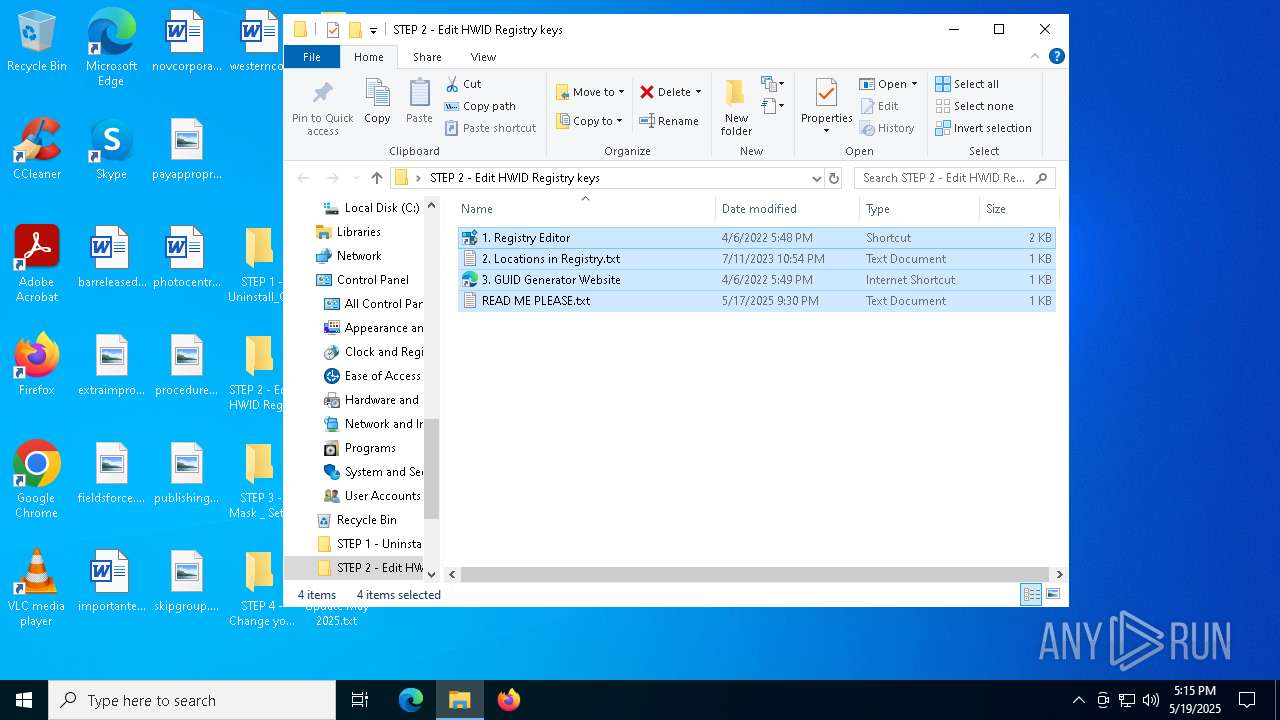
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 4 - Change your Disk Serial NumberID\1. Change Disk IDs.cmd | text | |
MD5:6346B33980B7D8946C1F0DBA5CBFD7F9 | SHA256:282932D8CAACF613B7167F674A84D320AF5B9E253F21C8134C46CE25FF4BB07B | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 1 - Uninstall_Clear Traces\Download Revo Uninstaller.url | binary | |
MD5:B8AF8AA3D0D8003E486B3F952BAFBAAC | SHA256:F6DB928C42771E18D7795DAB63DC991EC8D3DC371E8B4804D467F65CE11C607F | |||
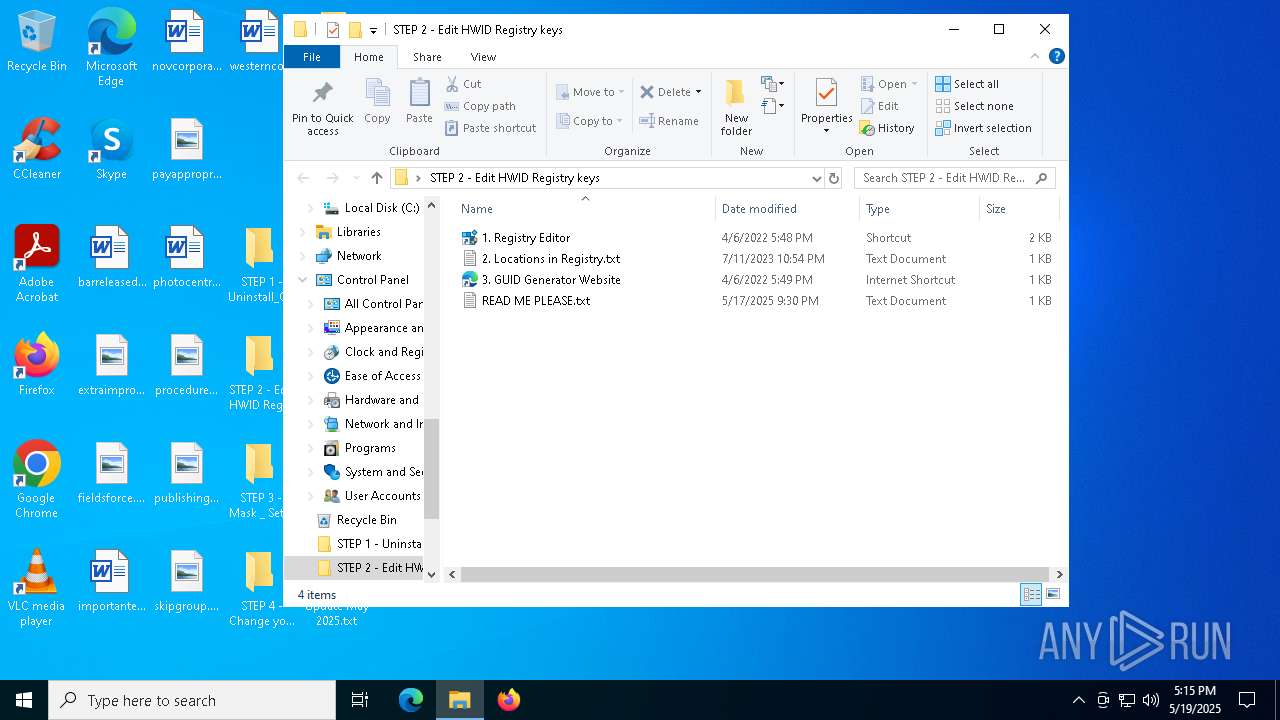
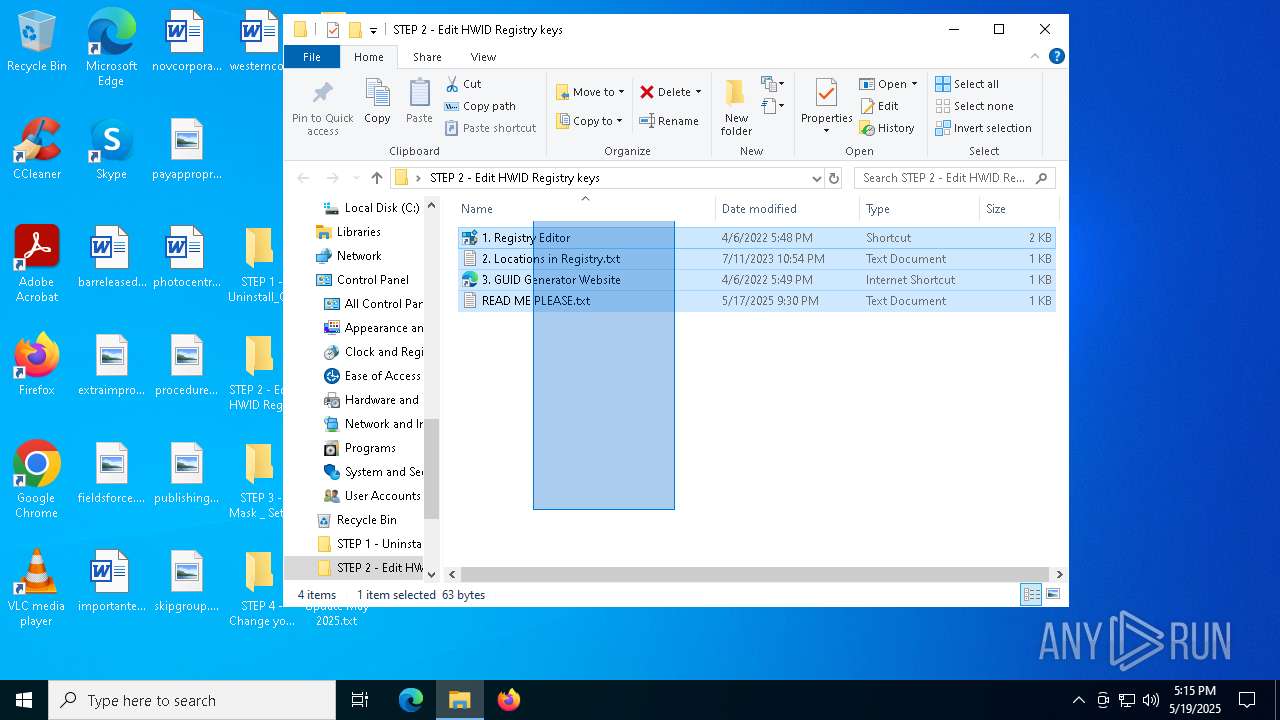
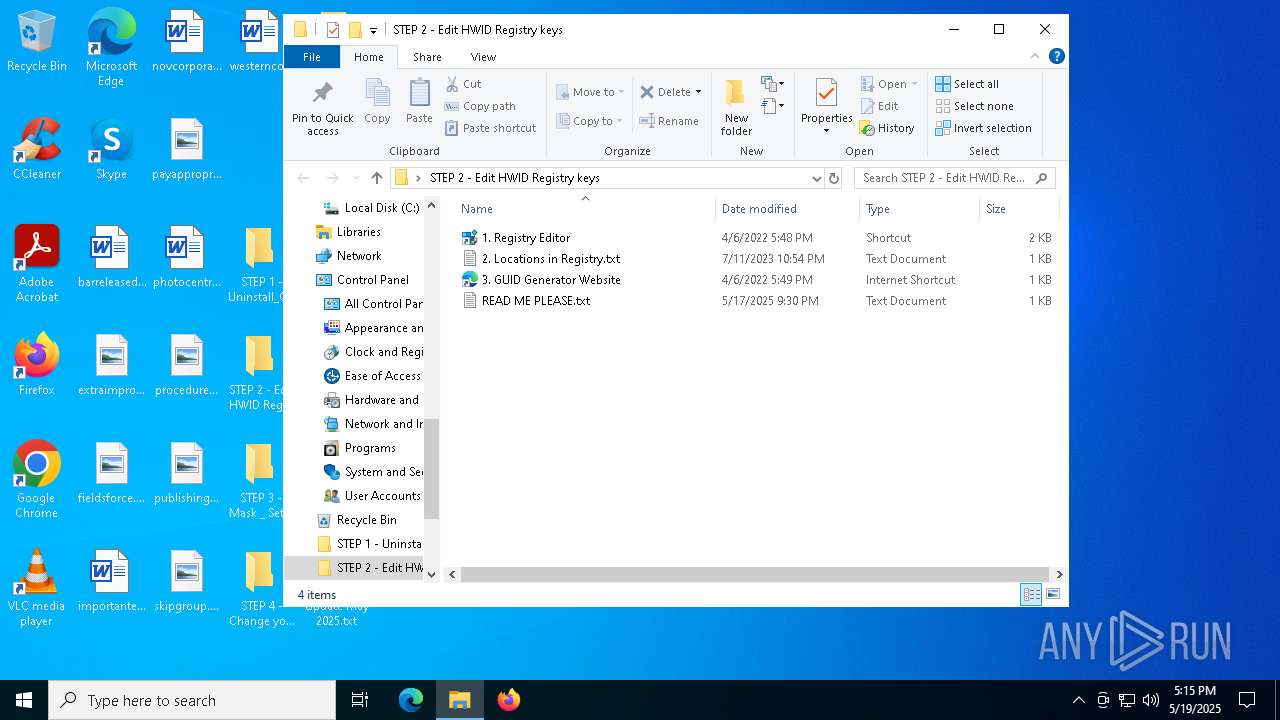
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 2 - Edit HWID Registry keys\3. GUID Generator Website.url | binary | |
MD5:DC2726585A60180658C2FB0714E436B8 | SHA256:21C4DE7B2083D60D3F0D2F38E70D1B2A1E0049279B1ADE9BA900A77D2E3A64E4 | |||
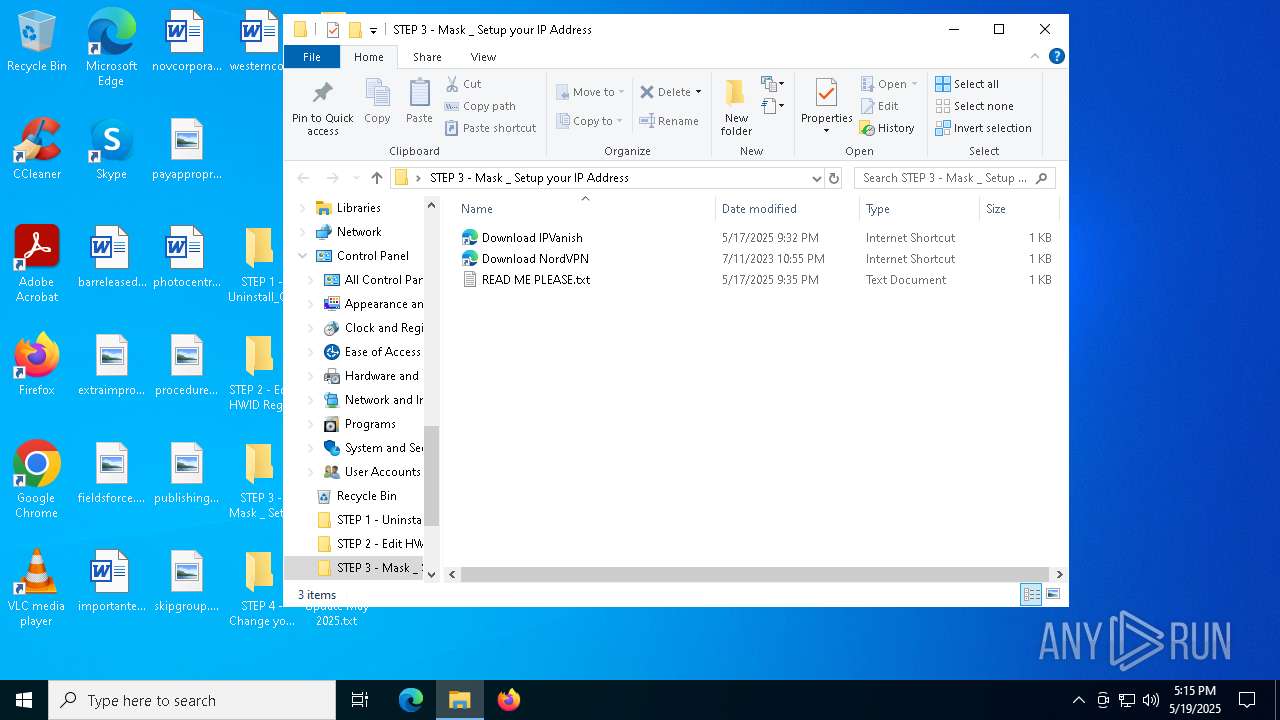
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 3 - Mask _ Setup your IP Address\Download IPVanish.url | binary | |
MD5:722B1424183BF095CBC02A742A5239EC | SHA256:EDD1240A3B15A9619CCF265DC59FB2D85371B9D162C5EEE7831ED8B3360F859A | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 2 - Edit HWID Registry keys\2. Locations in Registry.txt | text | |
MD5:FB9405B514D82E994F83F67C5A712351 | SHA256:446A8E31EC8925D9BBF7FC92A5A3C77B13A6597376C30AFAB869BF0D2F7B462D | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 3 - Mask _ Setup your IP Address\READ ME PLEASE.txt | text | |
MD5:E4C3DE19B8186669AB2A09EB614BF631 | SHA256:4CA9A3FFA7AD5C2E70CD5DE371916C08931EF74F7E1517A2126AA6424D46E14B | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 2 - Edit HWID Registry keys\READ ME PLEASE.txt | text | |
MD5:2AEBC589837988C5101853A23B5A1820 | SHA256:76EF3AA15C48ADA759E77C8F0ED57CE9030A3DDB3A87CDC0AA2FAD5A646F572A | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 2 - Edit HWID Registry keys\1. Registry Editor.lnk | binary | |
MD5:0E2092F136D0E7F155A6C688E34533DC | SHA256:64AA810FA77628DC199F75F54DD764C142B0A479CDB62E24F853A707CA3A2DB5 | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 4 - Change your Disk Serial NumberID\READ ME PLEASE.txt | text | |
MD5:50BC60383C45B15BB32F3168DCE065F9 | SHA256:240B617B3AC0232FDCECE77E79A9FD9D02BA0DECB252BBE5710B3634B4B87985 | |||
| 4880 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4880.23397\HWID Bypass\STEP 3 - Mask _ Setup your IP Address\Download NordVPN.url | binary | |
MD5:92A3E5DB54B4166E789B643B53BE9004 | SHA256:89FF7443CC30C87127B75FE899648C8729BEFFD67CB91940CA97CACF9085F17F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7900 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7900 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5216 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |