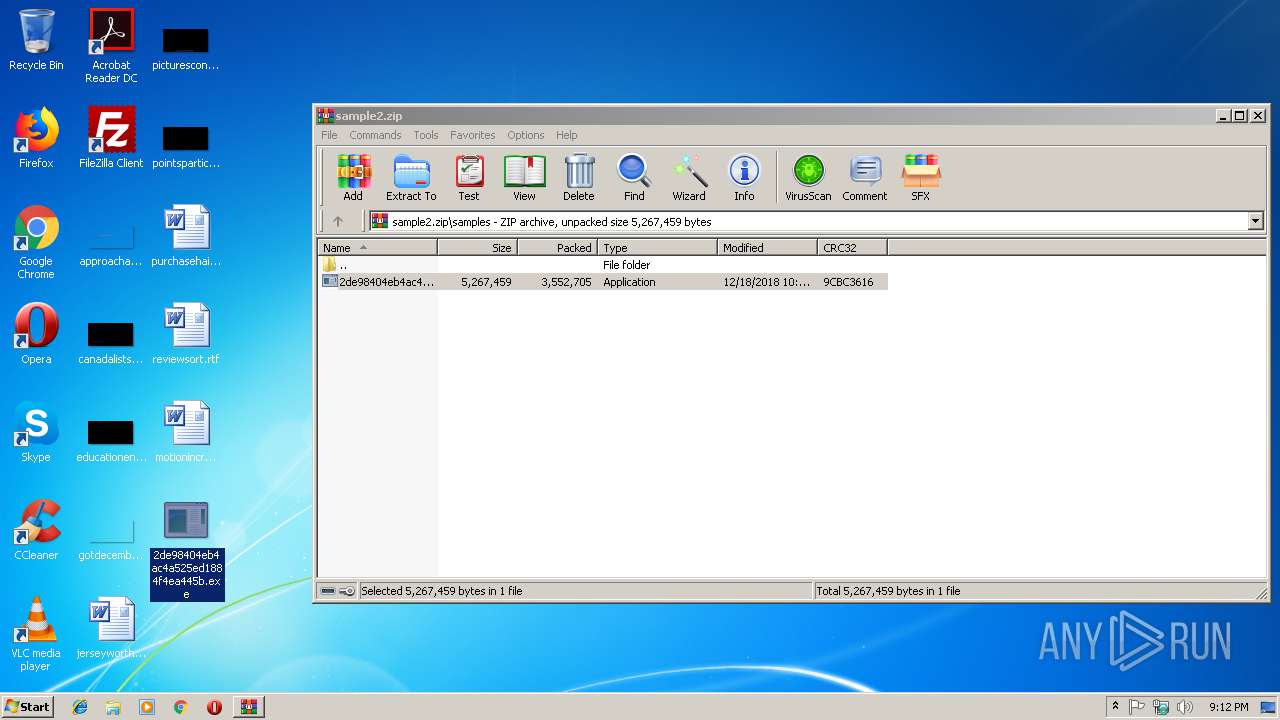
| File name: | sample2.zip |
| Full analysis: | https://app.any.run/tasks/5f6d7b5c-2d7b-40d6-8e45-7f250634eb05 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 21:11:36 |
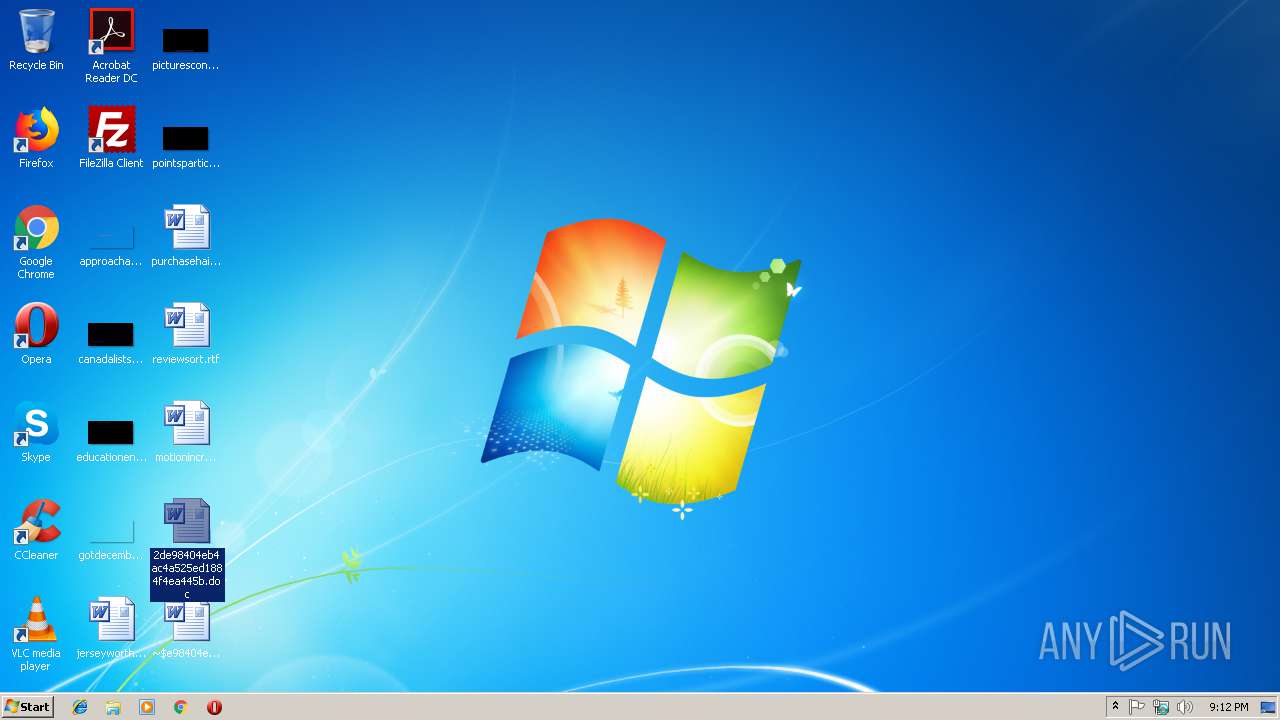
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9D21ACAB8CD32FEEC8827E0D94513110 |
| SHA1: | 78F2CAA1A0B906892F0070ADF5710EAC4848949D |
| SHA256: | 553FB24BBD0689647A3E60C177A5722DC802252D6332772E381C81D83C88EB35 |
| SSDEEP: | 98304:oV2d29ifgVav9dUfJiSUhkl6Eeu7hh5WYlzbpBpucAV7CL:c9ugVqdIJinkl9euQYVLpucUuL |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 416)
- explorer.exe (PID: 116)
- svchost.exe (PID: 844)
SUSPICIOUS
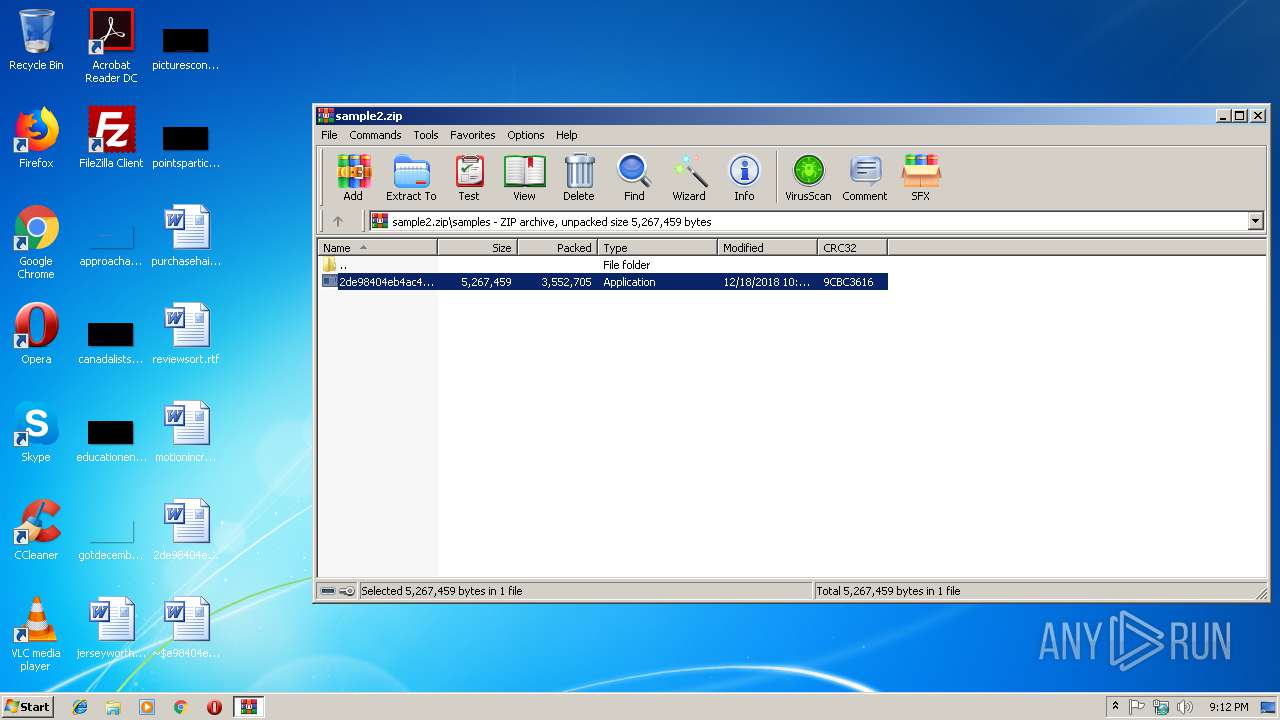
Executable content was dropped or overwritten
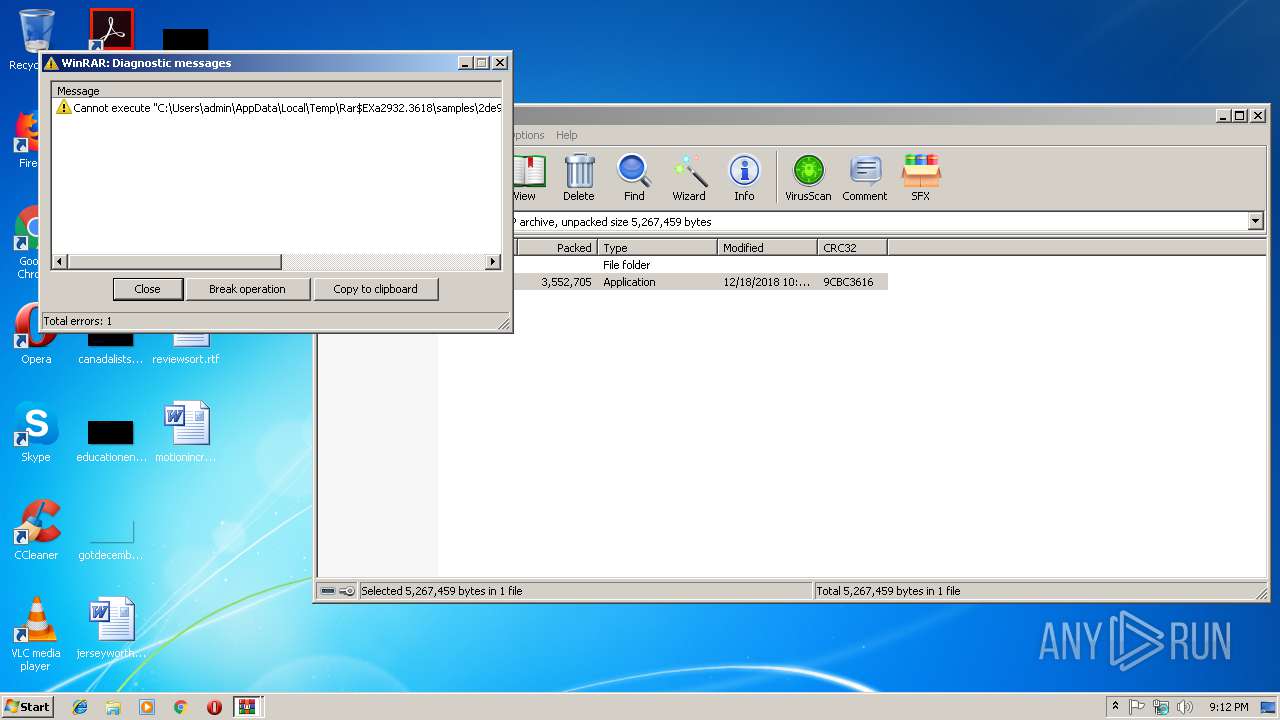
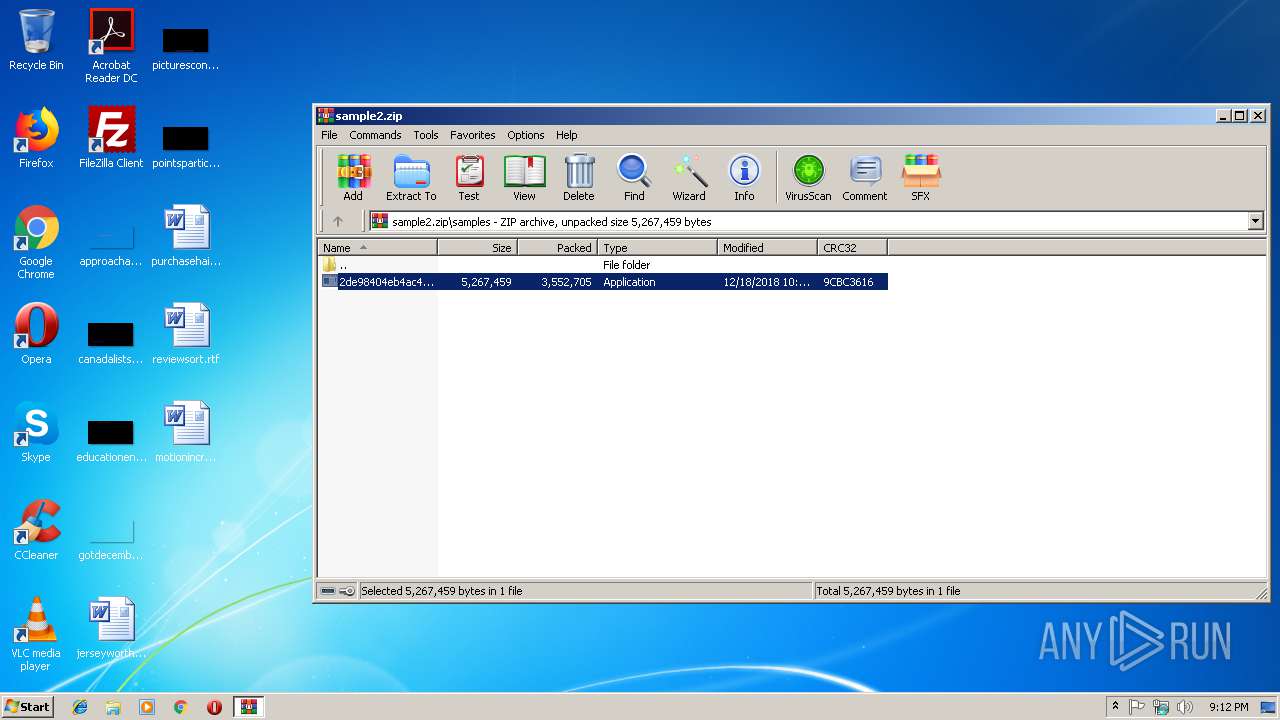
- WinRAR.exe (PID: 2932)
- explorer.exe (PID: 116)
Creates files in the user directory
- explorer.exe (PID: 116)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
INFO
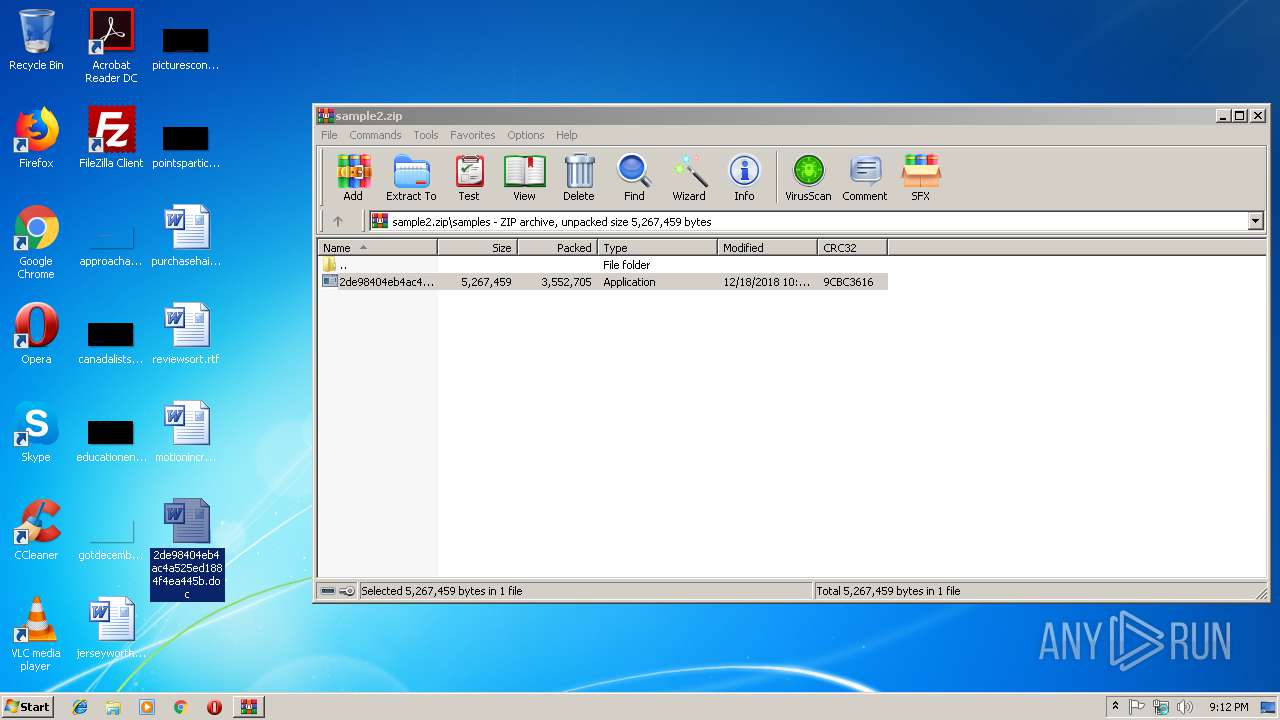
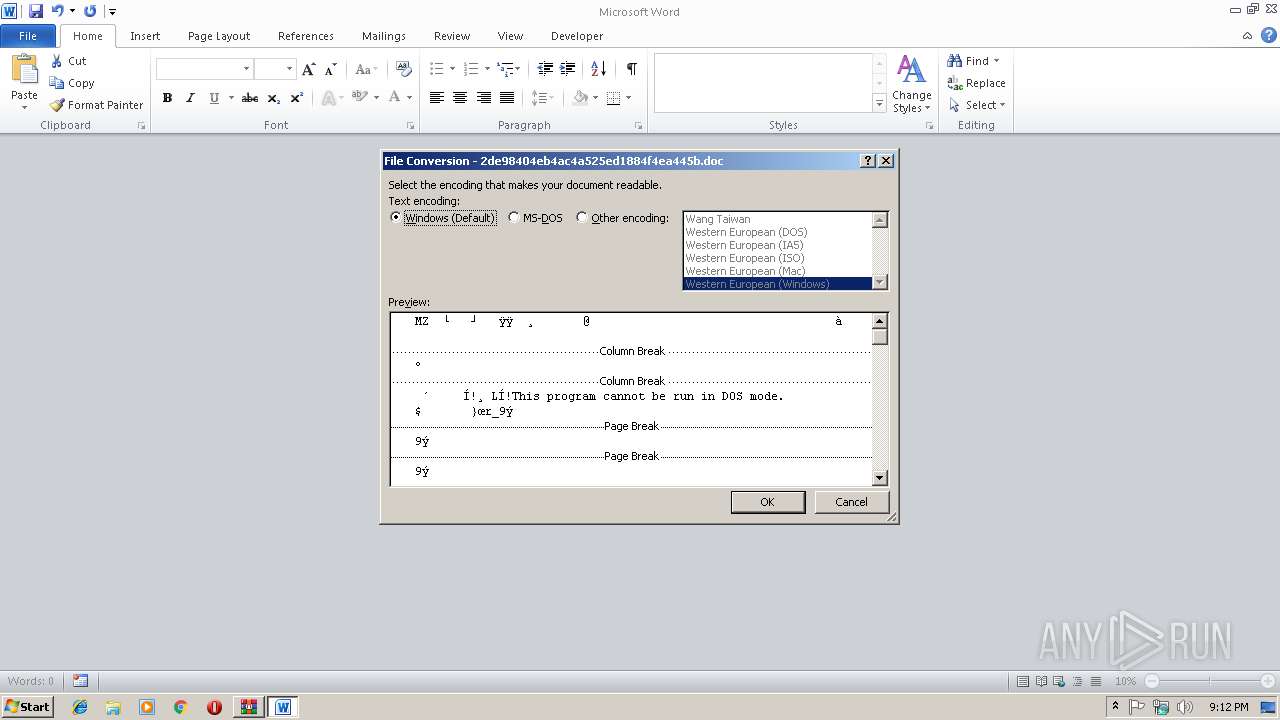
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Creates files in the user directory
- WINWORD.EXE (PID: 3116)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
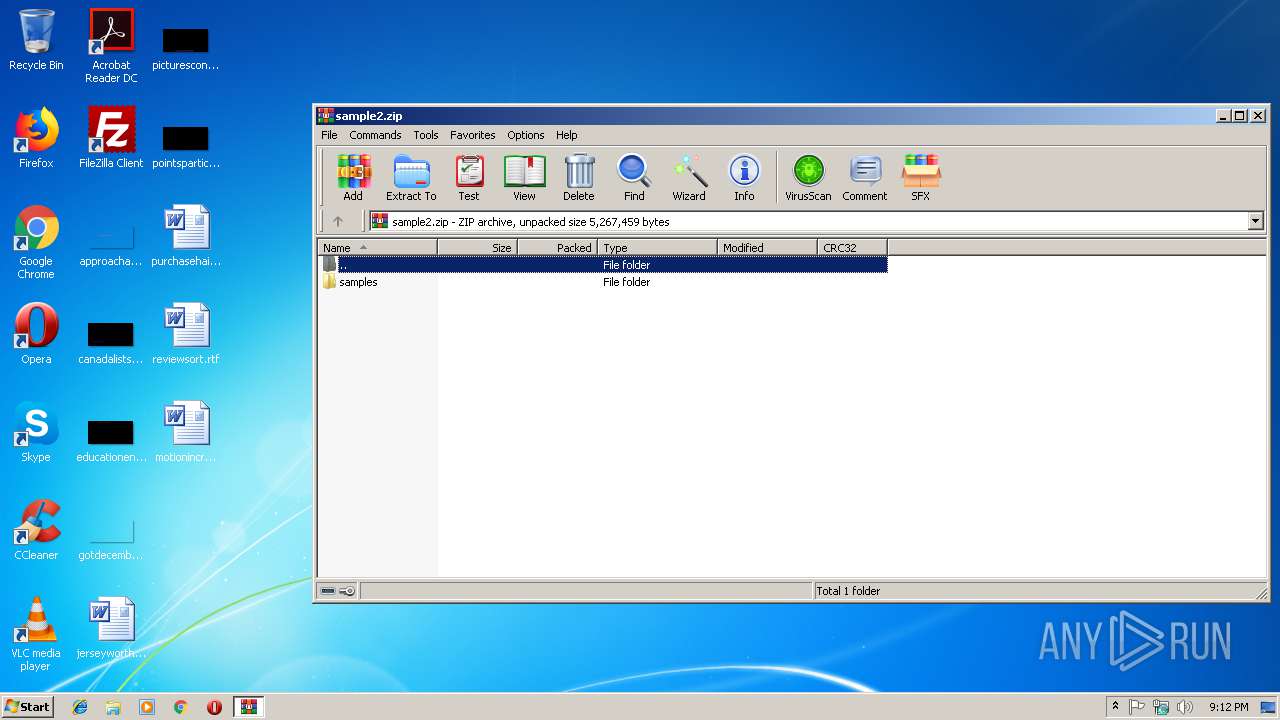
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:18 22:00:01 |
| ZipCRC: | 0x9cbc3616 |
| ZipCompressedSize: | 3552705 |
| ZipUncompressedSize: | 5267459 |
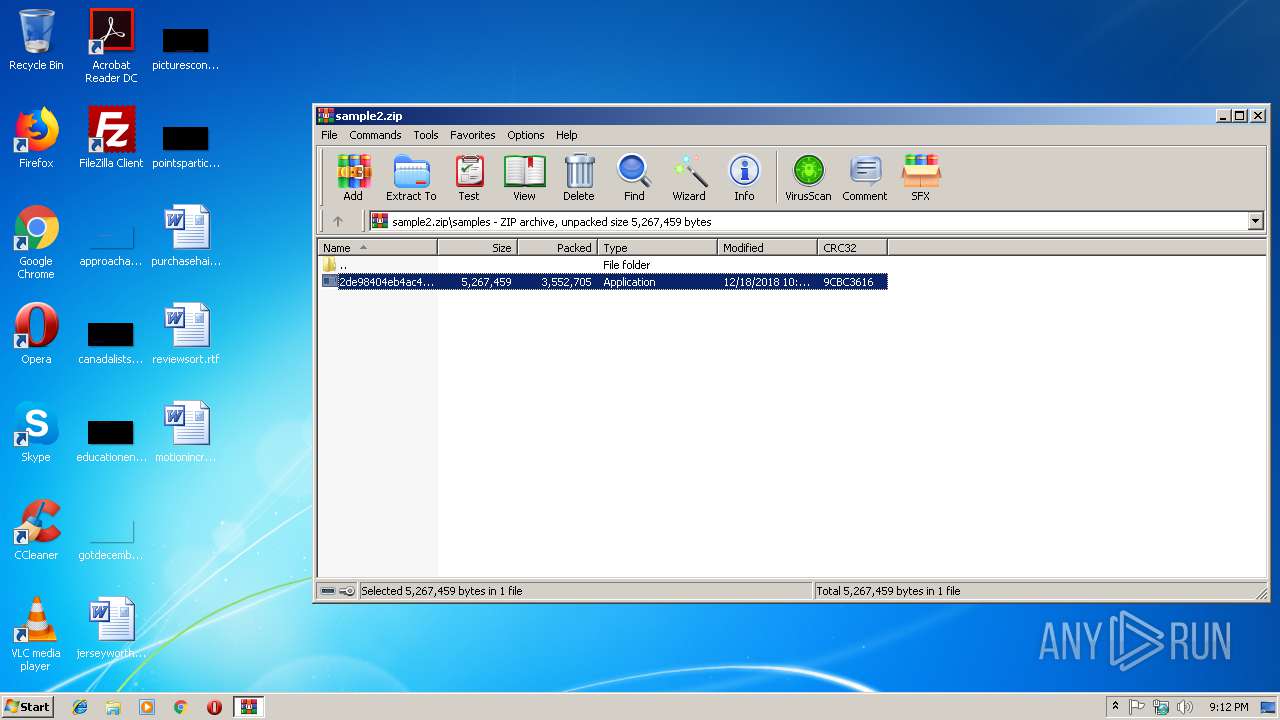
| ZipFileName: | samples/2de98404eb4ac4a525ed1884f4ea445b.exe |
Total processes
34
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 416 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3116 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\2de98404eb4ac4a525ed1884f4ea445b.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 410
Read events
4 317
Write events
85
Delete events
8
Modification events
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample2.zip | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2932.4272\samples\2de98404eb4ac4a525ed1884f4ea445b.exe | — | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF24.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0000.doc | — | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0001.doc | — | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{75FF1A1A-C08F-42E0-BA27-E0A9B6E46CC9}.tmp | — | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{76182A57-469D-4881-A174-804807B1712D}.tmp | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
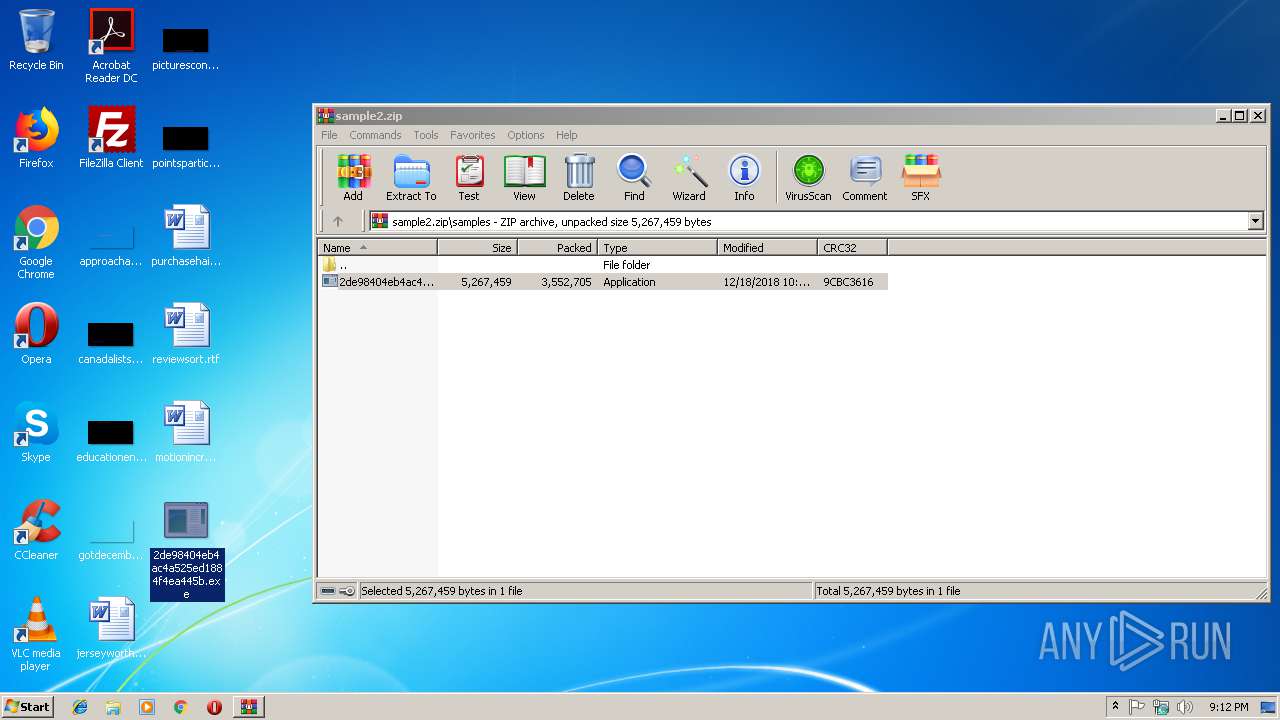
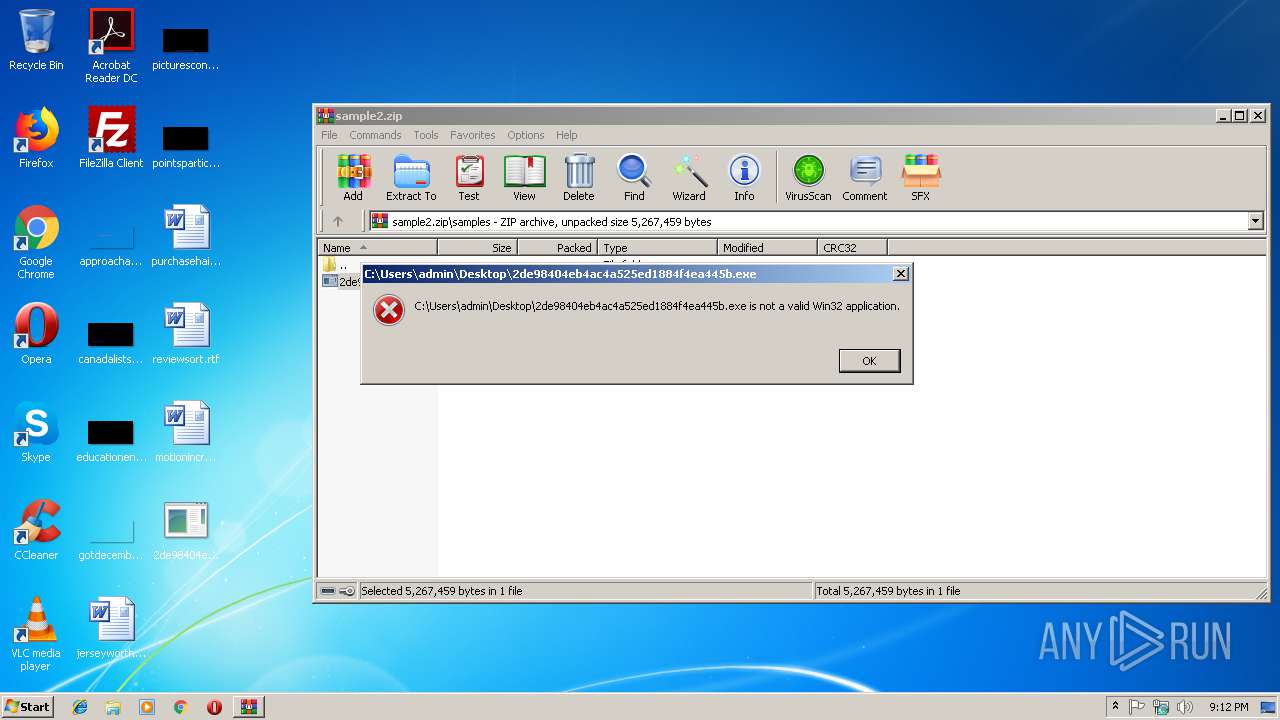
| 116 | explorer.exe | C:\Users\admin\Desktop\2de98404eb4ac4a525ed1884f4ea445b.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\a7bd71699cd38d1c.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\2de98404eb4ac4a525ed1884f4ea445b.doc.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report