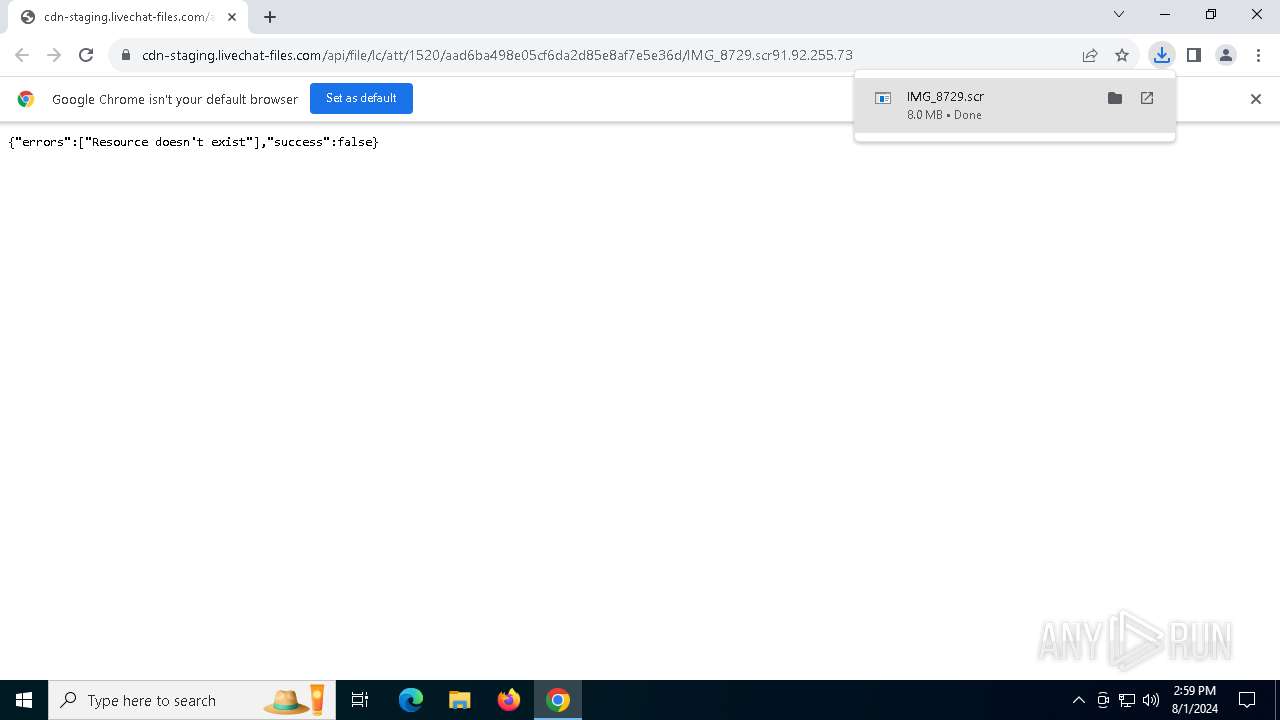
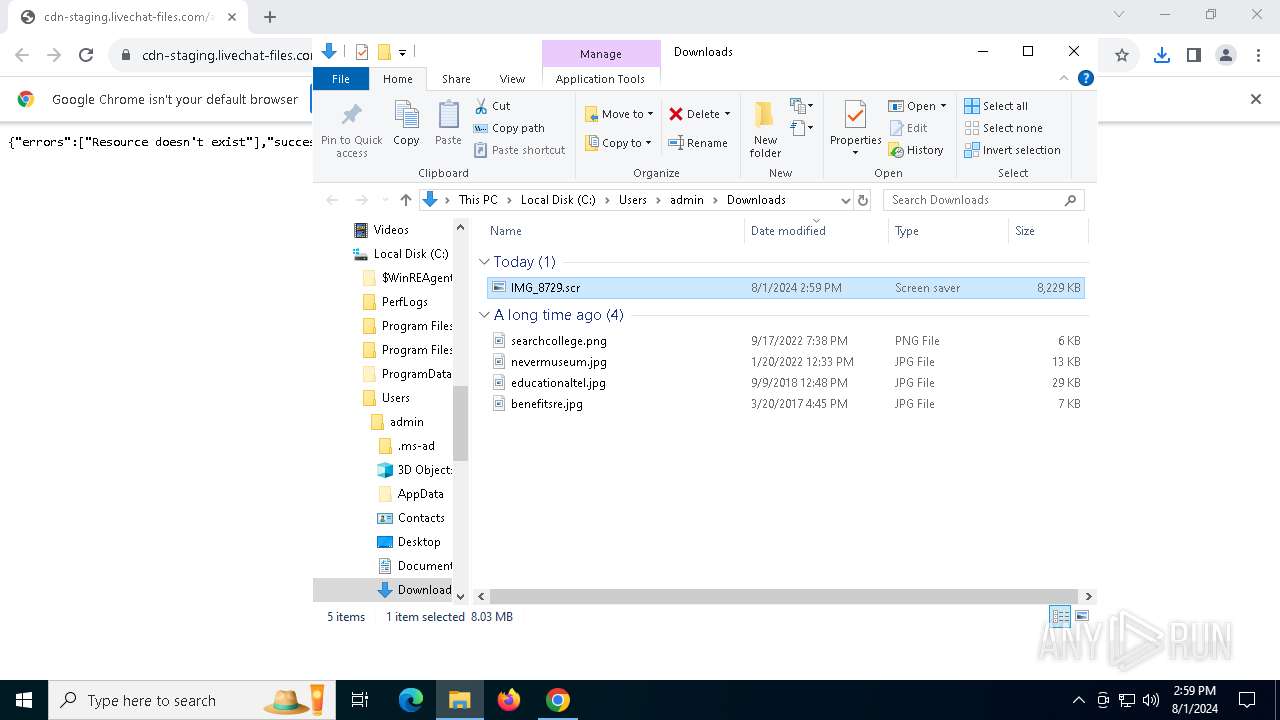
| URL: | https://cdn-staging.livechat-files.com/api/file/lc/att/1520/aad6ba498e05cf6da2d85e8af7e5e36d/IMG_8729.scr91.92.255.73 |
| Full analysis: | https://app.any.run/tasks/7e3fd102-92fc-4680-82ef-6b11b39d93db |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | August 01, 2024, 14:58:29 |
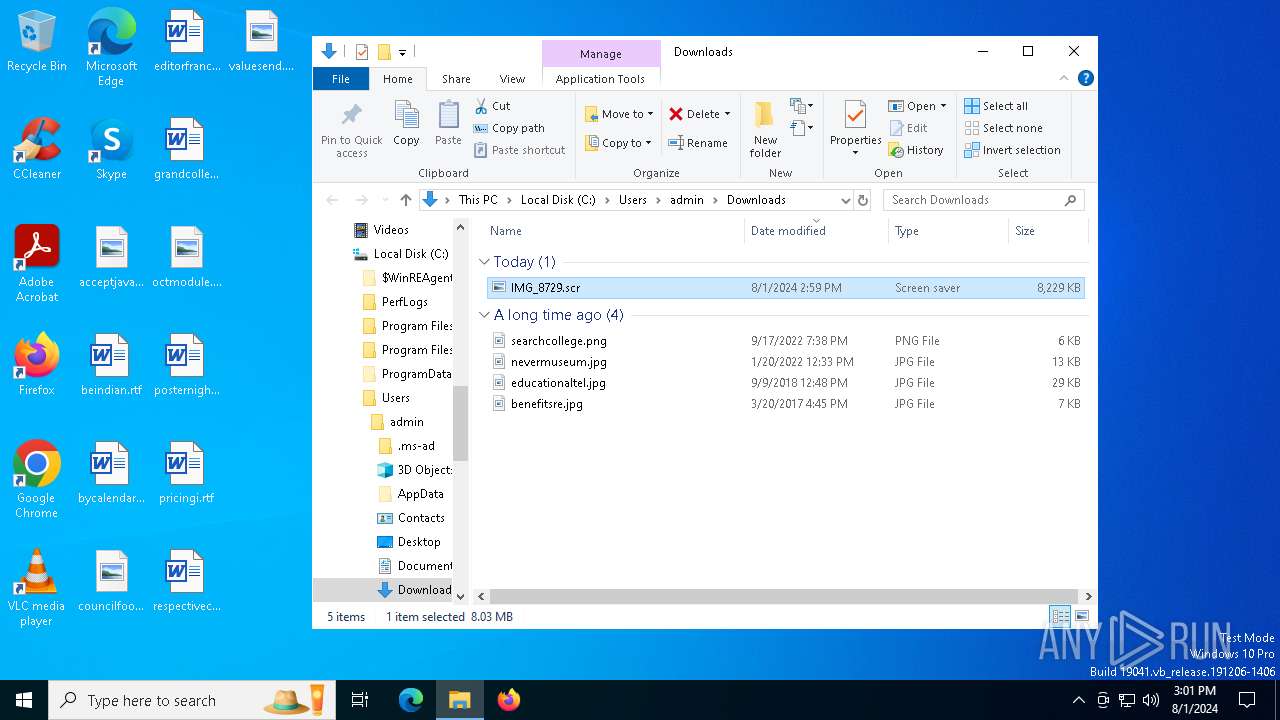
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E55E561B2E063B355FB35FA876826D07 |
| SHA1: | B350DDFA74FAF66A34CA868112296A4CAD55A198 |
| SHA256: | 553BA23D22AA6A390B68342E903FECC04BD54E19A57BD03E0EA43225D0B5DFB4 |
| SSDEEP: | 3:N8cHaLZS+MOzf9OE6UCxhVTDTyZus2hBXRkn:2cHaLZHMOzfkE6UqVPej2hhqn |
MALICIOUS
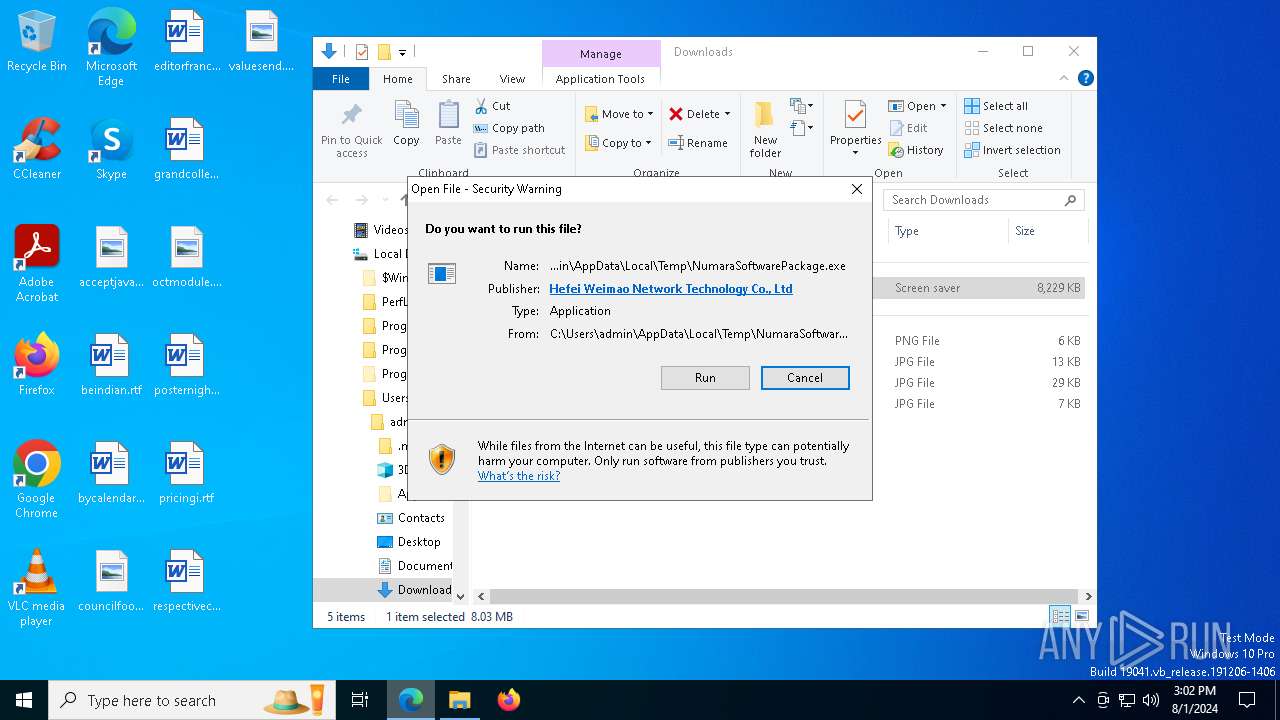
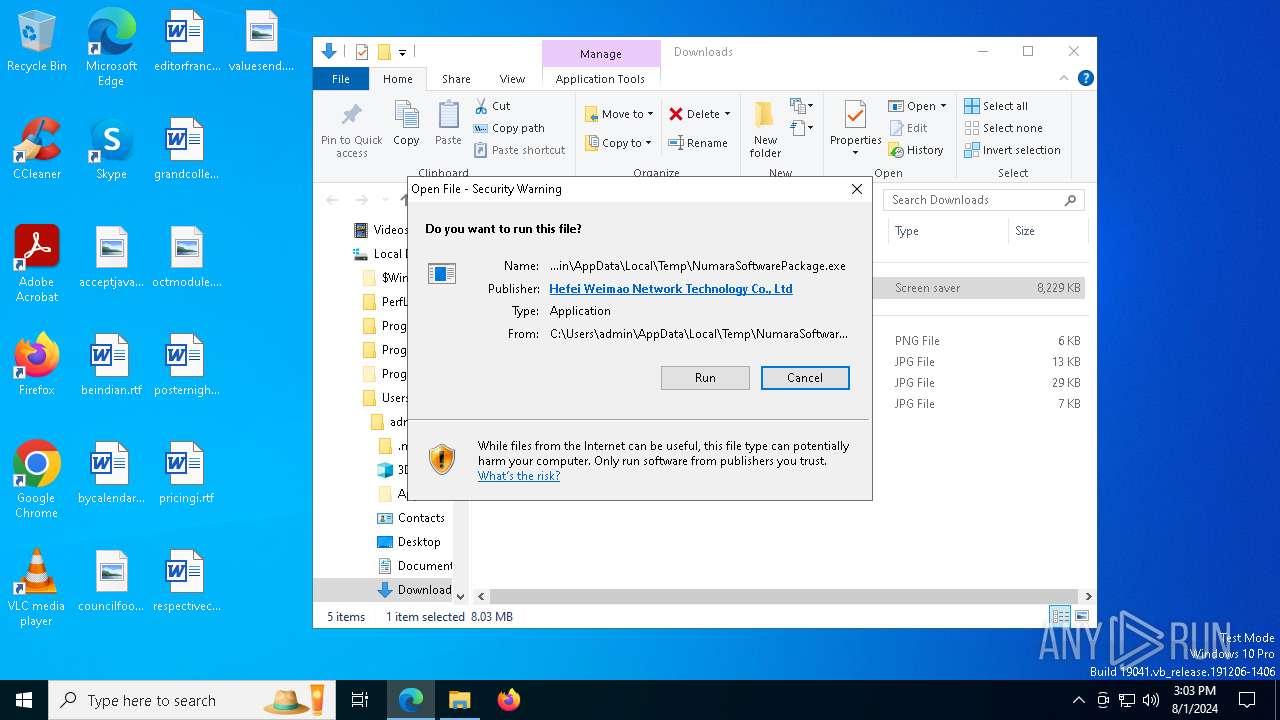
SPECTRERAT has been detected (YARA)
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
Starts CMD.EXE for commands execution
- msedge.exe (PID: 1248)
- msedge.exe (PID: 1812)
Connects to the CnC server
- msedge.exe (PID: 1248)
Actions looks like stealing of personal data
- Robocopy.exe (PID: 936)
SUSPICIOUS
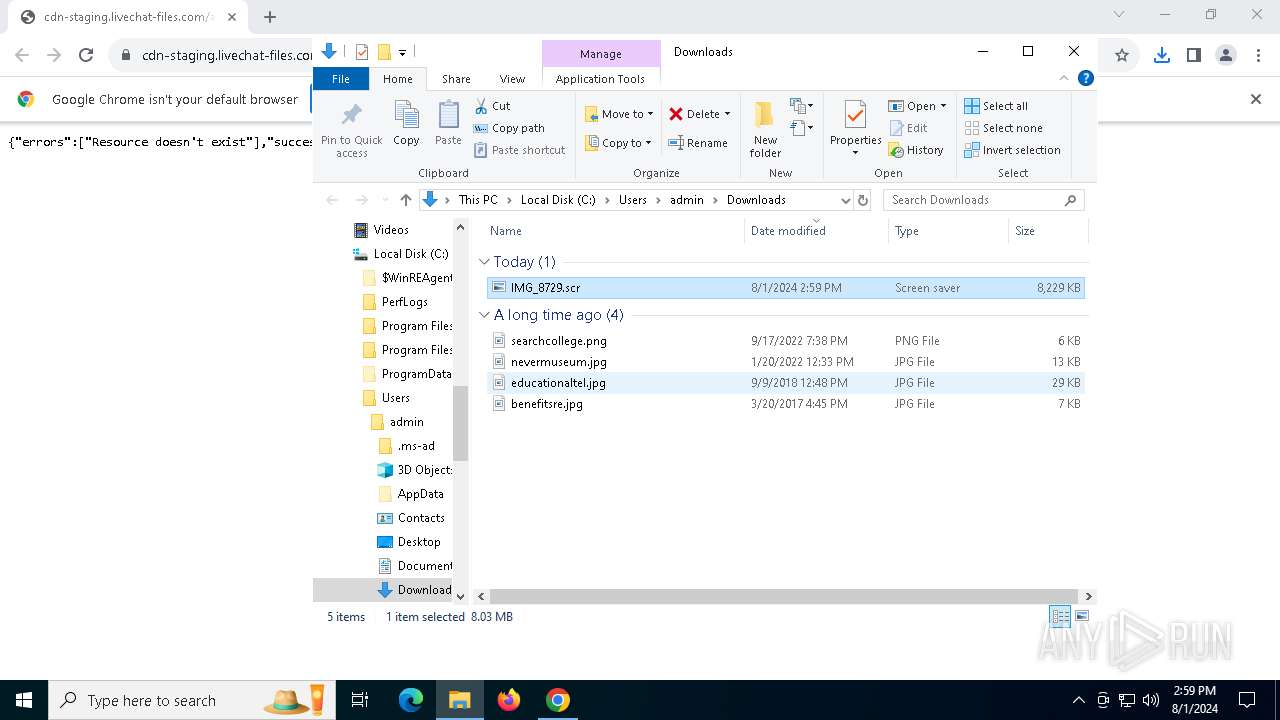
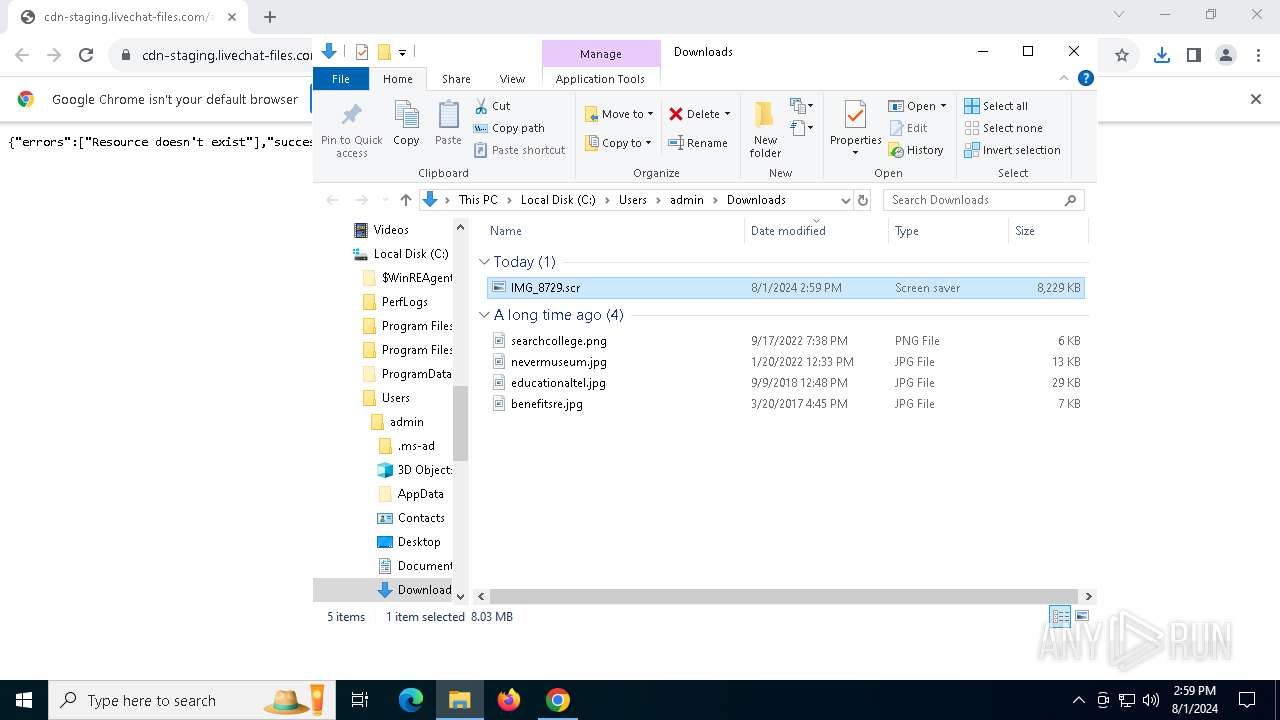
Executable content was dropped or overwritten
- IMG_8729.scr (PID: 7796)
- kedb.exe (PID: 7384)
- kedb.exe (PID: 752)
Reads security settings of Internet Explorer
- IMG_8729.scr (PID: 7796)
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
Reads the date of Windows installation
- IMG_8729.scr (PID: 7796)
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
Hides command output
- cmd.exe (PID: 7844)
Starts CMD.EXE for commands execution
- IMG_8729.scr (PID: 7796)
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7844)
The executable file from the user directory is run by the CMD process
- NumaraSoftwarePackage.exe (PID: 8076)
- kedb.exe (PID: 7384)
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
- kedb.exe (PID: 752)
- 7za.exe (PID: 2468)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5744)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 1488)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 5924)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 4936)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 1120)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6148)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 5464)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 3980)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3980)
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 1248)
Searches for installed software
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
Reads the Windows owner or organization settings
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
The process checks if it is being run in the virtual environment
- PsInfo64.exe (PID: 1120)
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
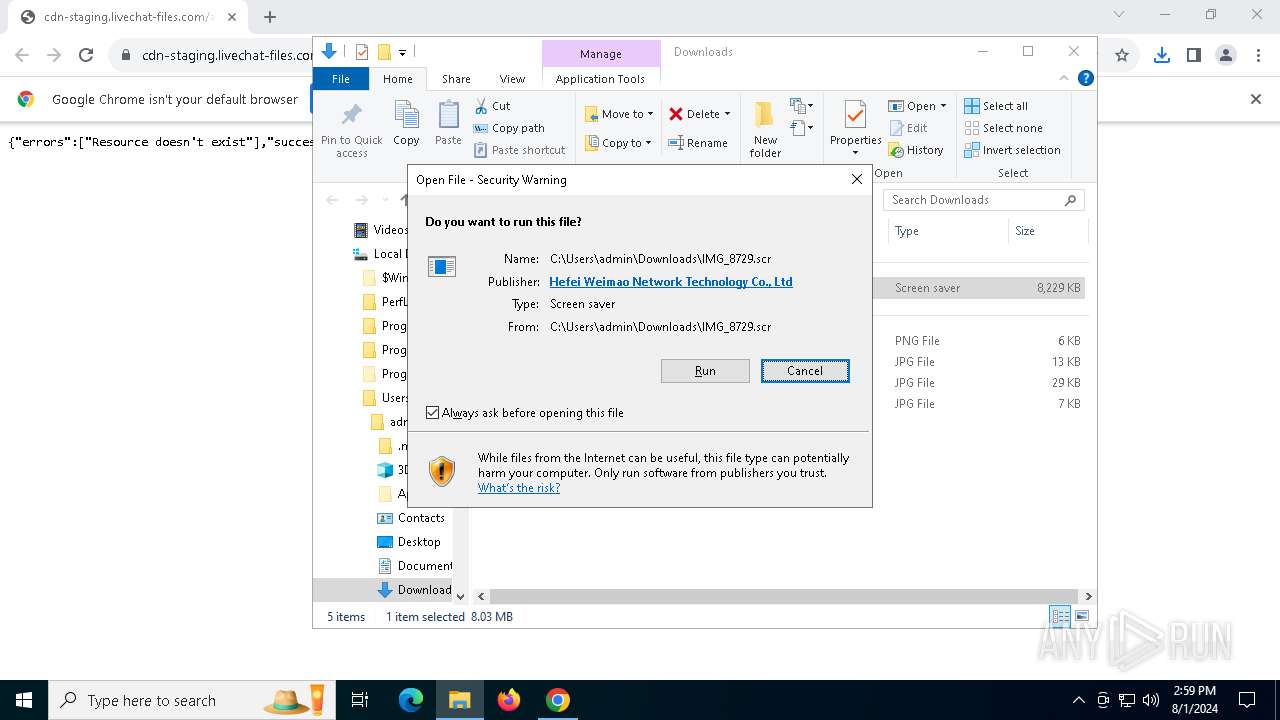
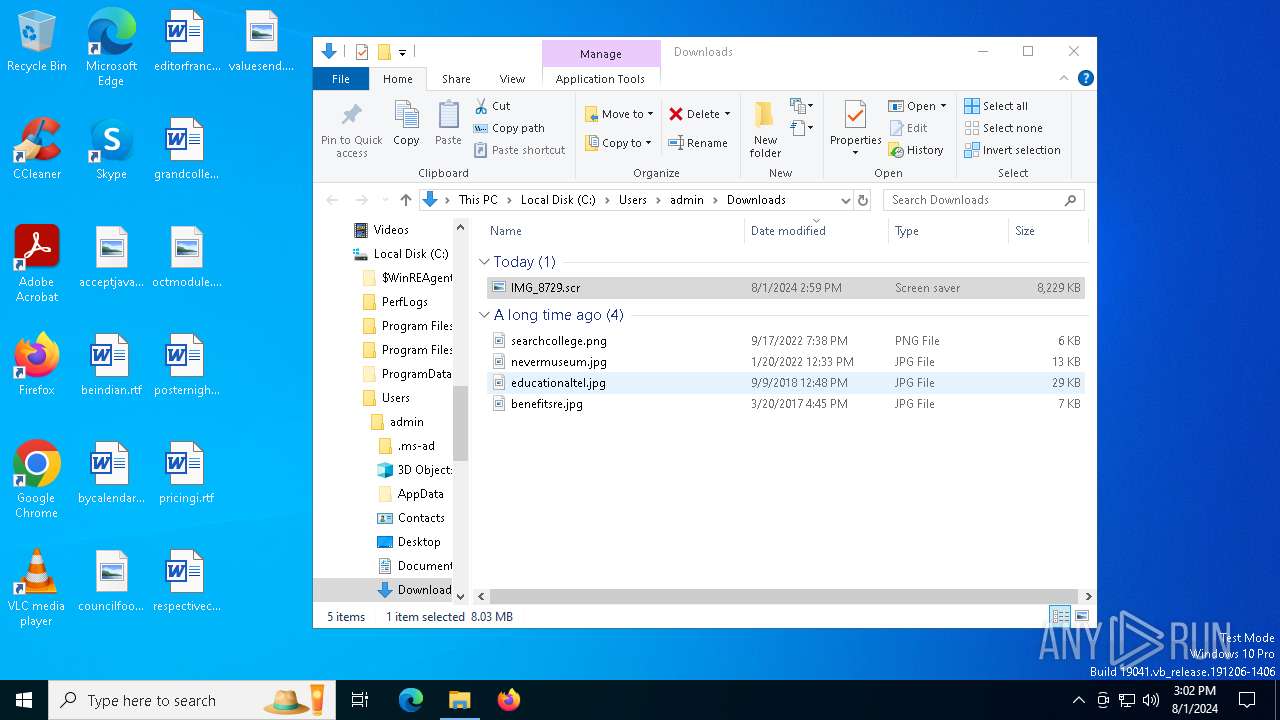
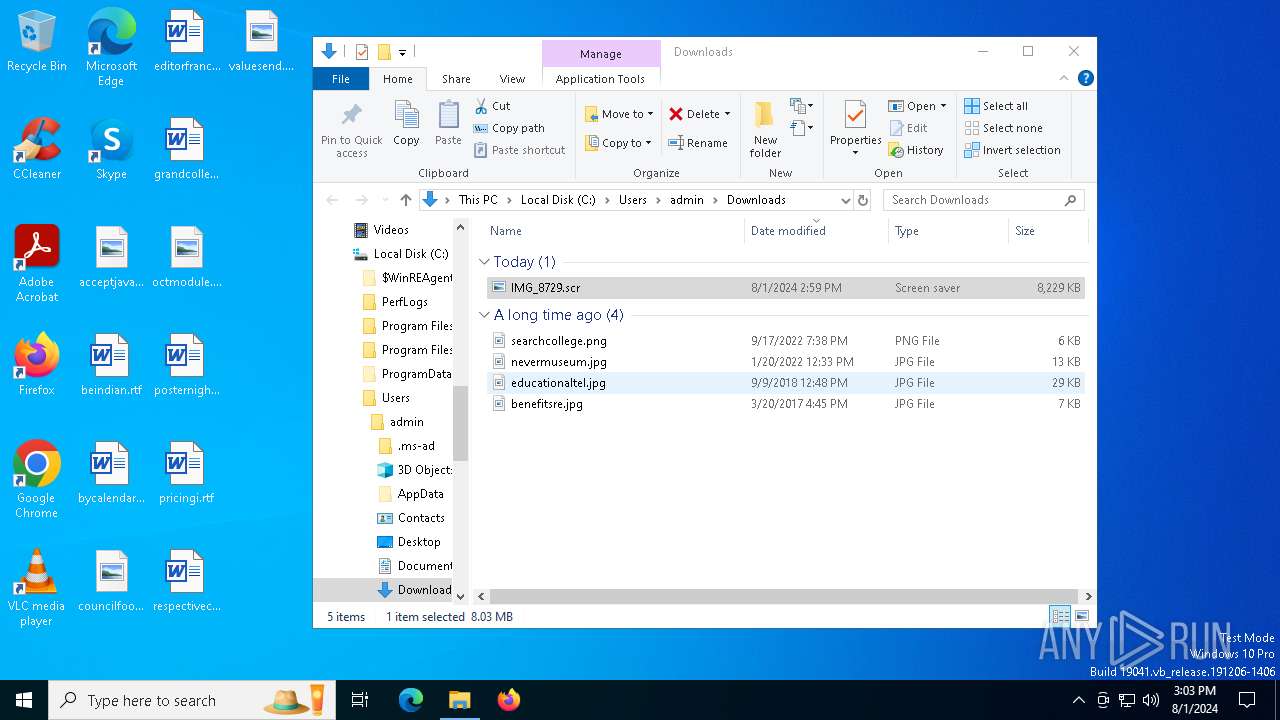
Starts application with an unusual extension
- explorer.exe (PID: 4552)
Creates file in the systems drive root
- explorer.exe (PID: 4552)
Lists all scheduled tasks
- schtasks.exe (PID: 7680)
- schtasks.exe (PID: 7028)
- schtasks.exe (PID: 7652)
- schtasks.exe (PID: 6888)
- schtasks.exe (PID: 6896)
- schtasks.exe (PID: 7200)
- schtasks.exe (PID: 7088)
- schtasks.exe (PID: 8128)
- schtasks.exe (PID: 7552)
- schtasks.exe (PID: 2524)
INFO
The process uses the downloaded file
- explorer.exe (PID: 4552)
- chrome.exe (PID: 7544)
- IMG_8729.scr (PID: 7796)
- msedge.exe (PID: 1812)
Reads the computer name
- TextInputHost.exe (PID: 6996)
- IMG_8729.scr (PID: 7796)
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
- 7za.exe (PID: 2468)
Checks supported languages
- TextInputHost.exe (PID: 6996)
- NumaraSoftwarePackage.exe (PID: 8076)
- kedb.exe (PID: 7384)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
- IMG_8729.scr (PID: 7796)
- kedb.exe (PID: 752)
- 7za.exe (PID: 2468)
- NumaraSoftwarePackage.exe (PID: 6672)
- NumaraSoftwarePackage.exe (PID: 4084)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6308)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
- WMIC.exe (PID: 5464)
Executable content was dropped or overwritten
- chrome.exe (PID: 6308)
- chrome.exe (PID: 8072)
- msedge.exe (PID: 1248)
- msedge.exe (PID: 1812)
Application launched itself
- chrome.exe (PID: 6308)
Reads the software policy settings
- explorer.exe (PID: 4552)
Checks proxy server information
- explorer.exe (PID: 4552)
Creates files or folders in the user directory
- explorer.exe (PID: 4552)
- kedb.exe (PID: 7384)
- 7za.exe (PID: 2468)
- kedb.exe (PID: 752)
- Robocopy.exe (PID: 936)
Manual execution by a user
- IMG_8729.scr (PID: 7796)
Process checks computer location settings
- IMG_8729.scr (PID: 7796)
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
Create files in a temporary directory
- NumaraSoftwarePackage.exe (PID: 8076)
- a2-stl-0729-early-(1)-TESTED.exe (PID: 7704)
- IMG_8729.scr (PID: 7796)
Reads CPU info
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
Reads Environment values
- PsInfo.exe (PID: 7464)
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
Reads product name
- PsInfo64.exe (PID: 1120)
- PsInfo64.exe (PID: 6244)
- PsInfo64.exe (PID: 6156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
326
Monitored processes
183
Malicious processes
15
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | kedb.exe -o jucq_x64.zip | C:\Users\admin\AppData\Roaming\VirtualComputerToolkit\kedb.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 936 | robocopy "C:\Users\admin\AppData\Roaming\Mozilla\Firefox" "C:\Users\admin\AppData\Roaming\Mozilla\Firefoxcopy" /E /XF *.lock favicons.sqlite favicons.sqlite-shm favicons.sqlite-wal /XD "Background Tasks Profiles" "Pending Pings" "Crash Reports" bookmarkbackups browser-extension-data features personality-provider settings crashes datareporting extensions minidumps saved-telemetry-pings security_state sessionstore-backups storage weave gmp-widevinecdm gmp-gmpopenh264 | C:\Windows\System32\Robocopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Robocopy Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | "C:\Windows\System32\cmd.exe" /C REG QUERY HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v VirtualComputerToolkit | C:\Windows\System32\cmd.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | findstr /C:"OS Name" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1108 | "C:\Windows\System32\cmd.exe" /C SCHTASKS /QUERY /TN MyTasks\VirtualComputerToolkit | C:\Windows\System32\cmd.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | "C:\Users\admin\AppData\Roaming\VirtualComputerToolkit\PsInfo64.exe" -s /accepteula applications | C:\Users\admin\AppData\Roaming\VirtualComputerToolkit\PsInfo64.exe | — | cmd.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Local and remote system information viewer Exit code: 0 Version: 1.78 Modules
| |||||||||||||||
| 1120 | "C:\Windows\System32\cmd.exe" /C TIMEOUT /T 60 | C:\Windows\System32\cmd.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Windows\System32\cmd.exe" /C TIMEOUT /T 10 | C:\Windows\System32\cmd.exe | — | NumaraSoftwarePackage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
67 389
Read events
67 153
Write events
173
Delete events
63
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000F028A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456033BCEE44DE41B4E8AEC331E84F566D2 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | Chrome |
Value: 5 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6308) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
17
Suspicious files
197
Text files
69
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe7aaa.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe7ab9.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFe7d98.TMP | text | |
MD5:4320BE33704F77FF4DF4921358D2C50C | SHA256:8FDF7387C47EB272670EFF935D71492F03EAFAA55A8B22C05658BB0F1AC472EE | |||
| 6308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:668BAE5C0A00EF466FA52102A122346C | SHA256:A366BA8B2FD21BB25B17C6AC8A2C07428AEE94E6EA8CB14E204E4F77F61E2D40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
141
TCP/UDP connections
72
DNS requests
36
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5300 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | — | 471 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | — | 313 b | whitelisted |
7112 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | — | 471 b | whitelisted |
7060 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | — | 471 b | whitelisted |
4552 | explorer.exe | GET | 200 | 2.18.64.86:80 | http://cevcsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR2rKuShFxBxX%2BVZ%2F8jiOwbsyptXQQUrFfKCBbcP8UxHApN2%2Fvx3pknLTQCEHEck3IiUUKT7QGna8h3sgM%3D | UY | — | 2.28 Kb | unknown |
4552 | explorer.exe | GET | 200 | 2.18.64.86:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQC78My1t7gx%2FSGuMneK5AyJ | UY | — | 1.80 Kb | whitelisted |
7944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | US | — | 1.09 Kb | whitelisted |
7944 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | US | — | — | whitelisted |
7944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | US | — | 1.48 Kb | whitelisted |
7944 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kct3f2b256c6ad54mamrbriypm_3037/jflookgnkcckhobaglndicnbbgbonegd_3037_all_acsnwcofavbntb2tnme2h7xagkka.crx3 | US | — | 21.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
1420 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2472 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
6308 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
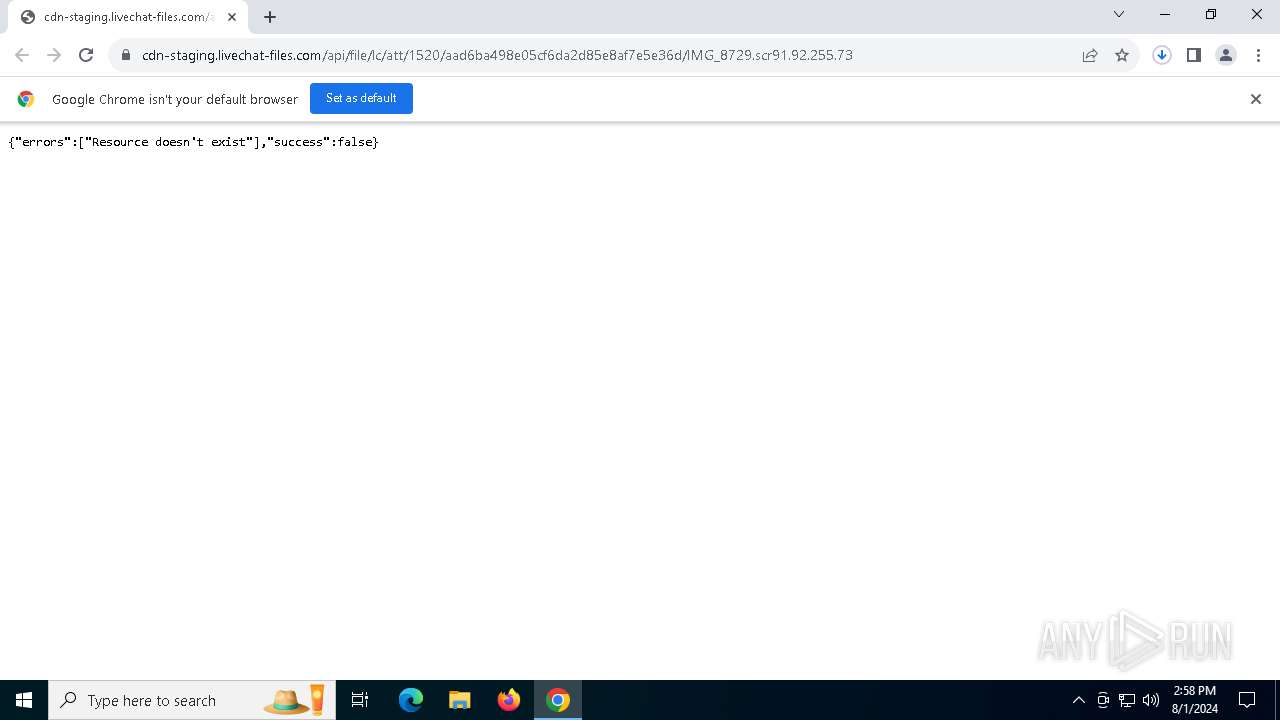
— | — | 2.16.1.243:443 | cdn-staging.livechat-files.com | Akamai International B.V. | NL | unknown |
5336 | SearchApp.exe | 184.86.251.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
cdn-staging.livechat-files.com |
| unknown |
accounts.google.com |
| unknown |
www.bing.com |
| unknown |
ocsp.digicert.com |
| unknown |
client.wns.windows.com |
| unknown |
login.live.com |
| unknown |
www.google.com |
| unknown |
th.bing.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1248 | msedge.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |
1248 | msedge.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
1248 | msedge.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
3 ETPRO signatures available at the full report