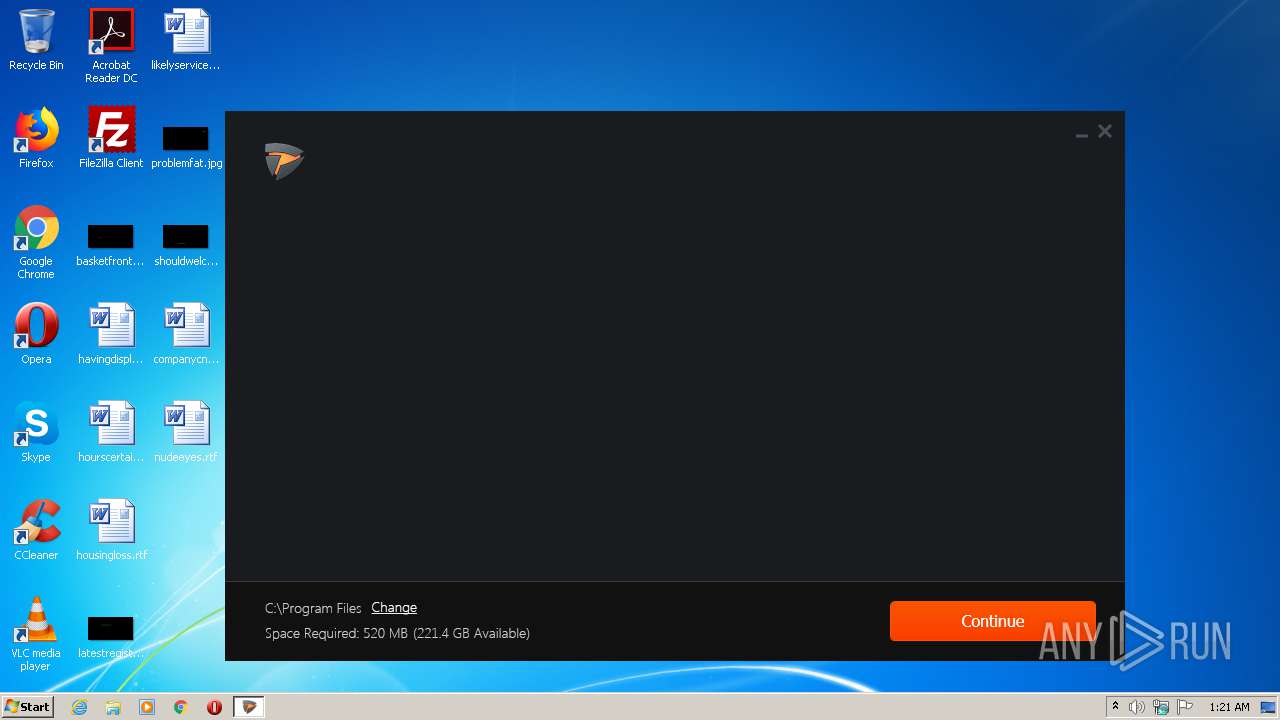
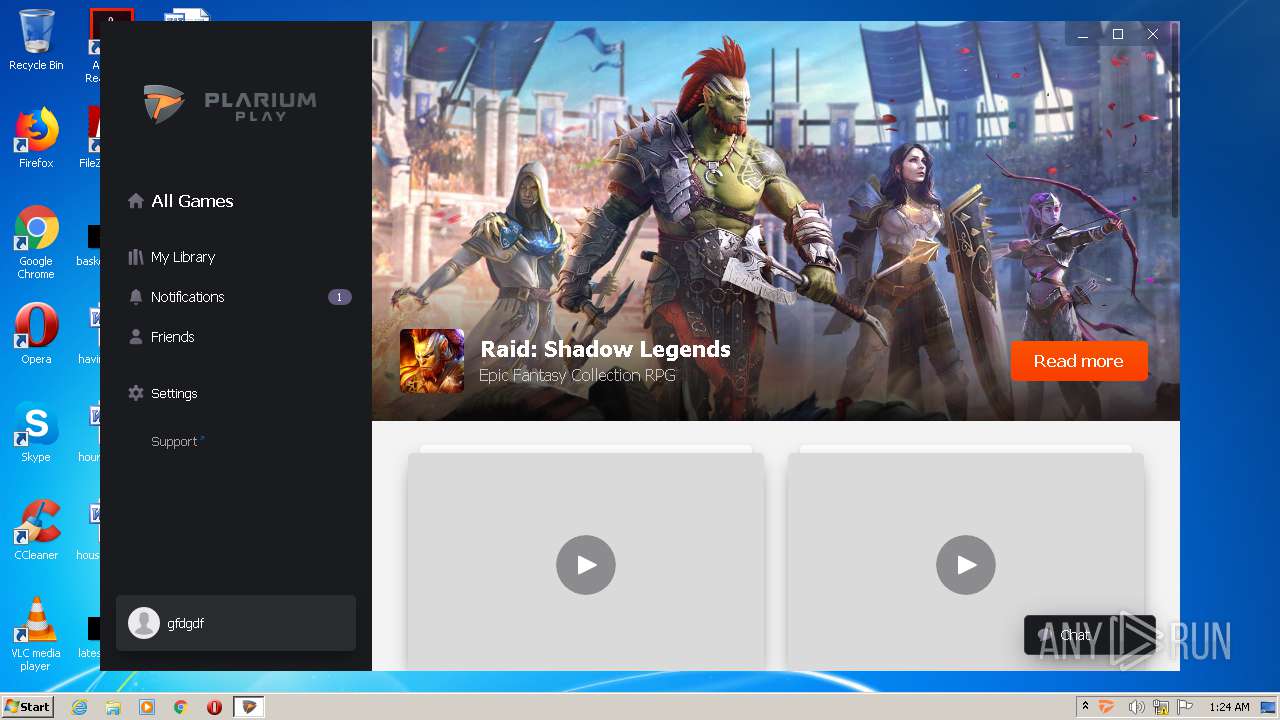
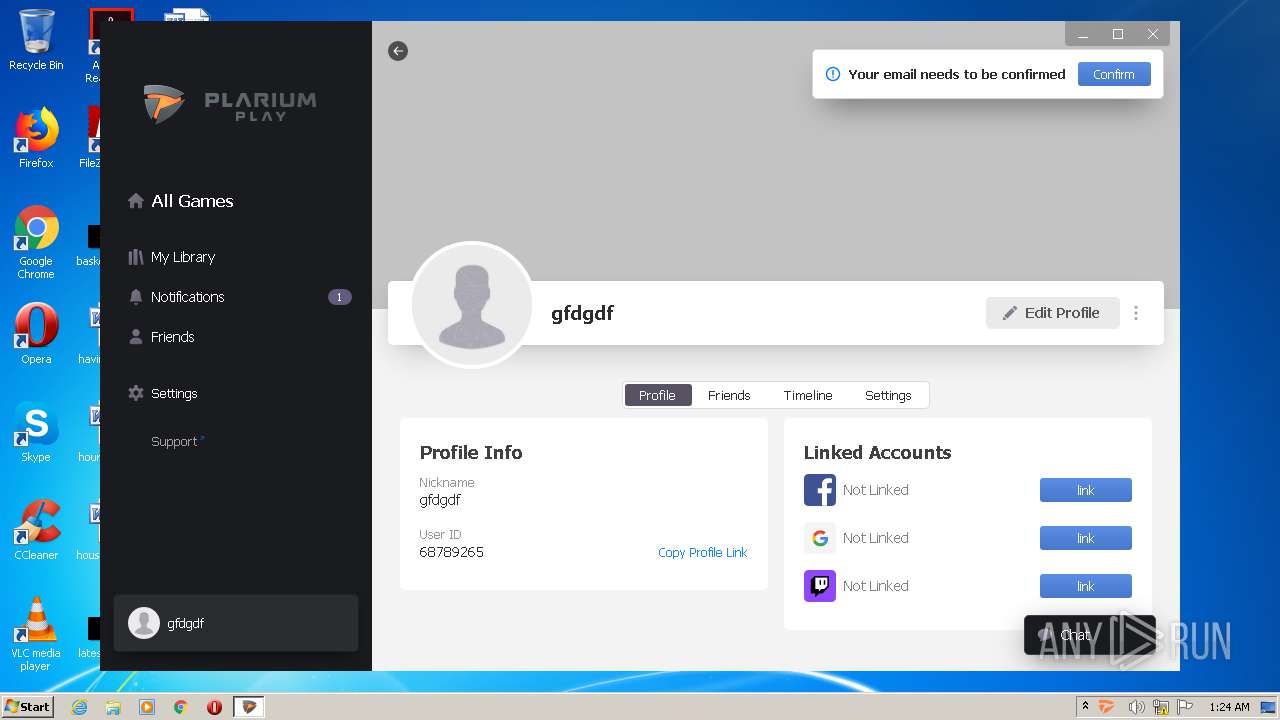
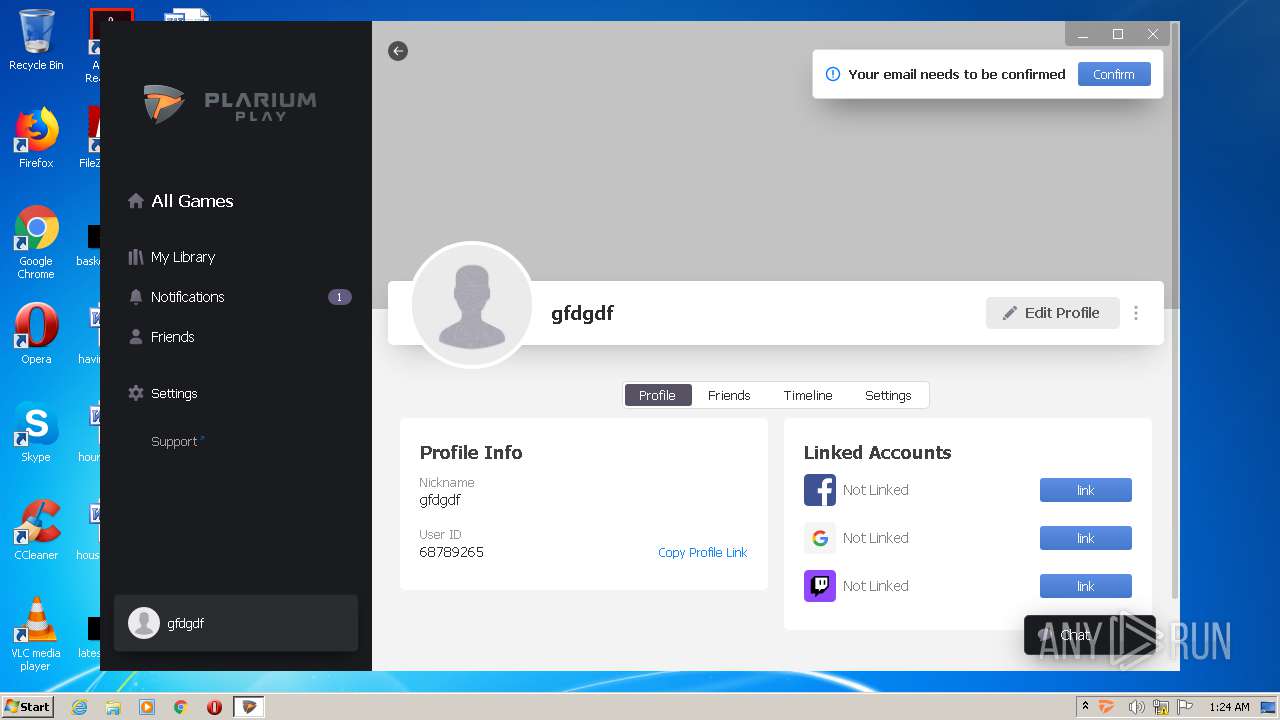
| File name: | PlariumPlaySetup.exe |
| Full analysis: | https://app.any.run/tasks/54051a66-f7c5-4e16-be6c-cc79394b1212 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 00:21:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E1D5F09FEB2E58B647757AEF943C3B5E |
| SHA1: | B1AFD91FC5FDF9FC22171053C1A1C1D03CCB945E |
| SHA256: | 553490394EE4344507A29BD9848C053BA58BD18DD4984B893A747B83788CCE96 |
| SSDEEP: | 24576:1NsfiTdYSuVzZH9tH1v142wsUq6/amlgcMCl2TZQTHCXEEQqtnZHVpT9v75lej52:xT2pZ1hwsf3ClEZQTmBxpT9vtUuczc |
MALICIOUS
Application was dropped or rewritten from another process
- PlariumPlaySetup.exe (PID: 3856)
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlaySetup.exe (PID: 2172)
- PlariumPlay.exe (PID: 2688)
- PlariumPlayClientService.exe (PID: 2056)
- PlariumPlay.exe (PID: 672)
- PlariumPlayClientService.exe (PID: 2428)
- PlariumPlay.exe (PID: 2468)
- TrayPP.exe (PID: 332)
- PlariumPlay.exe (PID: 2524)
- PlariumPlay.exe (PID: 1324)
- PlariumPlay.exe (PID: 3200)
- vc_redist.x86.exe (PID: 2944)
- vc_redist.x86.exe (PID: 1676)
- VC_redist.x86.exe (PID: 3456)
- VC_redist.x86.exe (PID: 876)
- VC_redist.x86.exe (PID: 3132)
- VC_redist.x86.exe (PID: 2344)
Loads dropped or rewritten executable
- PlariumPlaySetup.exe (PID: 3856)
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlayClientService.exe (PID: 2428)
- PlariumPlayClientService.exe (PID: 2056)
- TrayPP.exe (PID: 332)
- PlariumPlay.exe (PID: 672)
- PlariumPlay.exe (PID: 2468)
- PlariumPlay.exe (PID: 2524)
- PlariumPlay.exe (PID: 1324)
- PlariumPlay.exe (PID: 3200)
- vc_redist.x86.exe (PID: 1676)
- VC_redist.x86.exe (PID: 3132)
Changes the autorun value in the registry
- PlariumPlaySetup.exe (PID: 2172)
- PlariumPlaySetup.exe (PID: 2712)
- VC_redist.x86.exe (PID: 3456)
Changes settings of System certificates
- msiexec.exe (PID: 3852)
- PlariumPlayClientService.exe (PID: 2428)
- PlariumPlaySetup.exe (PID: 2712)
SUSPICIOUS
Executable content was dropped or overwritten
- PlariumPlaySetup.exe (PID: 2664)
- PlariumPlaySetup.exe (PID: 3856)
- PlariumPlaySetup.exe (PID: 4032)
- PlariumPlaySetup.exe (PID: 2172)
- msiexec.exe (PID: 3852)
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlayClientService.exe (PID: 2428)
- vc_redist.x86.exe (PID: 2944)
- vc_redist.x86.exe (PID: 1676)
- VC_redist.x86.exe (PID: 3456)
- VC_redist.x86.exe (PID: 2344)
- VC_redist.x86.exe (PID: 3132)
Reads Environment values
- PlariumPlaySetup.exe (PID: 3856)
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlayClientService.exe (PID: 2428)
Creates files in the Windows directory
- PlariumPlaySetup.exe (PID: 4032)
- PlariumPlaySetup.exe (PID: 2712)
- vc_redist.x86.exe (PID: 2944)
- VC_redist.x86.exe (PID: 3456)
- vc_redist.x86.exe (PID: 1676)
- VC_redist.x86.exe (PID: 2344)
- msiexec.exe (PID: 3852)
- VC_redist.x86.exe (PID: 3132)
Reads Internet Cache Settings
- PlariumPlaySetup.exe (PID: 2712)
Starts itself from another location
- PlariumPlaySetup.exe (PID: 2712)
- vc_redist.x86.exe (PID: 1676)
Executed as Windows Service
- vssvc.exe (PID: 3788)
- PlariumPlayClientService.exe (PID: 2428)
Searches for installed software
- PlariumPlaySetup.exe (PID: 2172)
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlayClientService.exe (PID: 2428)
Creates a software uninstall entry
- PlariumPlaySetup.exe (PID: 2172)
- VC_redist.x86.exe (PID: 3456)
- VC_redist.x86.exe (PID: 2344)
Creates files in the program directory
- PlariumPlaySetup.exe (PID: 2172)
- PlariumPlay.exe (PID: 2688)
- PlariumPlay.exe (PID: 2468)
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlay.exe (PID: 1324)
- PlariumPlayClientService.exe (PID: 2428)
- VC_redist.x86.exe (PID: 3456)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3852)
- PlariumPlayClientService.exe (PID: 2428)
- PlariumPlaySetup.exe (PID: 2712)
Creates or modifies windows services
- PlariumPlayClientService.exe (PID: 2056)
Creates files in the user directory
- PlariumPlaySetup.exe (PID: 2712)
Modifies the open verb of a shell class
- PlariumPlaySetup.exe (PID: 2712)
Removes files from Windows directory
- PlariumPlaySetup.exe (PID: 4032)
- vc_redist.x86.exe (PID: 1676)
- VC_redist.x86.exe (PID: 3132)
- vc_redist.x86.exe (PID: 2944)
Application launched itself
- PlariumPlay.exe (PID: 2468)
- VC_redist.x86.exe (PID: 3132)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3788)
Creates a software uninstall entry
- msiexec.exe (PID: 3852)
Dropped object may contain Bitcoin addresses
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlayClientService.exe (PID: 2428)
- TrayPP.exe (PID: 332)
- PlariumPlay.exe (PID: 2468)
Reads settings of System Certificates
- PlariumPlaySetup.exe (PID: 2712)
- PlariumPlay.exe (PID: 2468)
Reads the hosts file
- PlariumPlay.exe (PID: 2468)
- PlariumPlay.exe (PID: 1324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:17 07:33:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 299008 |
| InitializedDataSize: | 295424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2df71 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Plarium |
| FileDescription: | Plarium Play |
| FileVersion: | 6.1.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Plarium. All rights reserved. |
| OriginalFileName: | PlariumPlaySetup.exe |
| ProductName: | Plarium Play |
| ProductVersion: | 6.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2019 05:33:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Plarium |
| FileDescription: | Plarium Play |
| FileVersion: | 6.1.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Plarium. All rights reserved. |
| OriginalFilename: | PlariumPlaySetup.exe |
| ProductName: | Plarium Play |
| ProductVersion: | 6.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Sep-2019 05:33:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00048FF7 | 0x00049000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57206 |
.rdata | 0x0004A000 | 0x0001F760 | 0x0001F800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13752 |
.data | 0x0006A000 | 0x000016FC | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15516 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.7135 |
.rsrc | 0x0006D000 | 0x00023E28 | 0x00024000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.83886 |
.reloc | 0x00091000 | 0x00003DD0 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78827 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.2847 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.80747 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.63651 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.28711 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.97384 | 34401 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
65
Monitored processes
22
Malicious processes
16
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\TrayPP.exe" + logdir="C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1" -validation-key=21aa5ce8-2bdd-43ab-9c07-d60a4d330a2b | C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\TrayPP.exe | PlariumPlay.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: TrayPP Exit code: 0 Version: 6.1.0.0 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlay.exe" --type=gpu-process --field-trial-handle=1452,116025233406711733,10332077730356469347,131072 --disable-features=OutOfBlinkCors --no-sandbox --log-file="C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\debug.log" --log-severity=disable --lang=en-US --gpu-preferences=IAAAAAAAAADgACAgAAAAAAAAYAAAAAAACAAAAAAAAAAoAAAABAAAACAAAAAAAAAAKAAAAAAAAAAwAAAAAAAAADgAAAAAAAAAEAAAAAAAAAAAAAAABQAAABAAAAAAAAAAAAAAAAYAAAAQAAAAAAAAAAEAAAAFAAAAEAAAAAAAAAABAAAABgAAAA== --log-file="C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\debug.log" --service-request-channel-token=8186051023502098156 --mojo-platform-channel-handle=1460 /prefetch:2 | C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlay.exe | — | PlariumPlay.exe | |||||||||||
User: admin Company: Plarium Integrity Level: MEDIUM Description: Plarium Play Exit code: 0 Version: 6.1.0 Modules
| |||||||||||||||
| 876 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -uninstall -quiet -burn.related.upgrade -burn.ancestors={86380aef-fd23-4fc3-8723-a98ccad8f2c6} -burn.filehandle.self=836 -burn.embedded BurnPipe.{AC4FF1D9-FA84-4EF7-8EDC-9F638898DDFA} {DAA26CA9-42B6-40F2-8181-4DA4086EA8F0} 3456 | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | — | VC_redist.x86.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.21.27702 Exit code: 0 Version: 14.21.27702.2 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlay.exe" --type=utility --field-trial-handle=1452,116025233406711733,10332077730356469347,131072 --disable-features=OutOfBlinkCors --lang=en-US --service-sandbox-type=network --no-sandbox --log-file="C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\debug.log" --log-severity=disable --lang=en-US --log-file="C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\debug.log" --service-request-channel-token=5434429212823206956 --mojo-platform-channel-handle=2260 /prefetch:8 | C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlay.exe | PlariumPlay.exe | ||||||||||||
User: admin Company: Plarium Integrity Level: MEDIUM Description: Plarium Play Exit code: 0 Version: 6.1.0 Modules
| |||||||||||||||
| 1676 | "C:\Windows\Temp\{1E5AF1EB-5818-4498-B102-8D36CDFB25E2}\.cr\vc_redist.x86.exe" -burn.clean.room="C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\Requirements\vc_redist.x86.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 /quiet /norestart | C:\Windows\Temp\{1E5AF1EB-5818-4498-B102-8D36CDFB25E2}\.cr\vc_redist.x86.exe | vc_redist.x86.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.26.28720 Exit code: 0 Version: 14.26.28720.3 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlayClientService.exe" install start --sudo | C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlayClientService.exe | PlariumPlaySetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PlariumPlayClientService Exit code: 0 Version: 6.1.0.0 Modules
| |||||||||||||||
| 2172 | "C:\Windows\Temp\{4ACB9C5F-2181-4D83-B89D-BFC4BA6F58E6}\.be\PlariumPlaySetup.exe" -q -burn.elevated BurnPipe.{2855DEBC-A65B-428D-8157-B5018B6BF84A} {8D0C6882-DC45-4E53-91C1-DB51454A330E} 2712 | C:\Windows\Temp\{4ACB9C5F-2181-4D83-B89D-BFC4BA6F58E6}\.be\PlariumPlaySetup.exe | PlariumPlaySetup.exe | ||||||||||||
User: admin Company: Plarium Integrity Level: HIGH Description: Plarium Play Exit code: 0 Version: 6.1.0 Modules
| |||||||||||||||
| 2344 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{A202AE8A-7DC4-4D30-A234-AD8F2F5CC03B} {7B04129A-05BF-40EA-B76E-CC7F6452F113} 3132 | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlayClientService.exe" -displayname "Plarium Play Client Service" -servicename "Plarium Play Client Service" | C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlayClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: PlariumPlayClientService Exit code: 0 Version: 6.1.0.0 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlay.exe" -setup-file="C:\Users\admin\AppData\Local\Temp\PlariumPlaySetup.exe" -preloader-id=2688 | C:\Program Files\Plarium\PlariumPlay\6.1.0-0.0.1\PlariumPlay.exe | PlariumPlay.exe | ||||||||||||
User: admin Company: Plarium Integrity Level: MEDIUM Description: Plarium Play Exit code: 0 Version: 6.1.0 Modules
| |||||||||||||||
Total events
5 467
Read events
2 832
Write events
2 336
Delete events
299
Modification events
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3856) PlariumPlaySetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PlariumPlaySetup_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
417
Suspicious files
88
Text files
576
Unknown types
138
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{2665A878-F525-4D75-8DF3-9DBC8553E43A}\.cr\PlariumPlaySetup.exe | executable | |
MD5:04F583A8776CF5945BC249D496EAEF9B | SHA256:96AEBDB866C8210C676769E2146DF0D91C8186EB603CFFA50604965145F34982 | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\BootstrapperCore.dll | executable | |
MD5:2BED93A7DED1350DD7100778284DE0F9 | SHA256:C99A9A03D99C438C2F1FEC21BBA6D954E47B97E34EC6EC26FE56B55755CE182F | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\SetupWPF.dll | executable | |
MD5:14E925C11825F89CAB2DDC2E77D4688A | SHA256:DDBBCC19AEB097DE6C018EDBE2B326C9C31A3D77B82CA9DE741FFCDFB3D007F0 | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\mbahost.dll | executable | |
MD5:C59832217903CE88793A6C40888E3CAE | SHA256:9DFA1BC5D2AB4C652304976978749141B8C312784B05CB577F338A0AA91330DB | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\System.Windows.Interactivity.dll | executable | |
MD5:E677ED785F7270F9E5FDAE2F020DDA4D | SHA256:081C05B763E2023BA0B94B28415D9EAFA2A0EDACB011234072E22941CF9149DD | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\1035\mbapreq.wxl | xml | |
MD5:E338408F1101499EB22507A3451F7B06 | SHA256:B7D9528F29761C82C3D926EFE5E0D5036A0E0D83EB4CCA7282846C86A9D6F9F3 | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\mbapreq.wxl | xml | |
MD5:4D2C8D10C5DCCA6B938B71C8F02CA8A8 | SHA256:C63DE5F309502F9272402587A6BE22624D1BC2FEACD1BD33FB11E44CD6614B96 | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\mbapreq.png | image | |
MD5:A356956FD269567B8F4612A33802637B | SHA256:A401A225ADDAF89110B4B0F6E8CF94779E7C0640BCDD2D670FFCF05AAB0DAD03 | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\1031\mbapreq.wxl | xml | |
MD5:C8E7E0B4E63B3076047B7F49C76D56E1 | SHA256:631D46CB048FB6CF0B9A1362F8E5A1854C46E9525A0260C7841A04B2316C8295 | |||
| 3856 | PlariumPlaySetup.exe | C:\Users\admin\AppData\Local\Temp\{D681AA20-1FF4-42FE-B65D-CF6784EA95CC}\.ba\1041\mbapreq.wxl | xml | |
MD5:DB0F5BAB42403FD67C0A18E35E6880EC | SHA256:CCDCDB111EFA152C5F9FF4930033698B843390A549699AE802098D87431F16FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
48
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2712 | PlariumPlaySetup.exe | GET | 204 | 172.217.16.142:80 | http://google.com/generate_204 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1324 | PlariumPlay.exe | 172.67.16.8:443 | static.x-plarium.com | — | US | unknown |
— | — | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1324 | PlariumPlay.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1324 | PlariumPlay.exe | 216.58.212.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2428 | PlariumPlayClientService.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1324 | PlariumPlay.exe | 104.19.147.8:443 | script.crazyegg.com | Cloudflare Inc | US | shared |
— | — | 23.211.149.25:443 | aka.ms | Akamai Technologies, Inc. | NL | whitelisted |
1324 | PlariumPlay.exe | 172.217.23.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1324 | PlariumPlay.exe | 142.250.13.156:443 | stats.g.doubleclick.net | Google Inc. | US | suspicious |
3856 | PlariumPlaySetup.exe | 104.16.21.18:443 | desktop.plarium.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
desktop.plarium.com |
| suspicious |
cdn01.x-plarium.com |
| unknown |
tracker.x-plarium.com |
| unknown |
cdnjs.cloudflare.com |
| whitelisted |
browser.sentry-cdn.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
static.x-plarium.com |
| unknown |
apis.google.com |
| whitelisted |
aka.ms |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
PlariumPlayClientService.exe | Topshelf.HostFactory Information: 0 : |
PlariumPlayClientService.exe | Configuration Result:
[Success] Name Plarium Play Client Service
[Success] ServiceName Plarium Play Client Service
|
PlariumPlayClientService.exe | Topshelf v4.2.1.215, .NET Framework v4.0.30319.42000
|
PlariumPlayClientService.exe | Topshelf v4.2.1.215, .NET Framework v4.0.30319.42000
|
PlariumPlayClientService.exe | Installing Plarium Play Client Service service
|
PlariumPlayClientService.exe | Topshelf.Runtime.Windows.HostInstaller Information: 0 : |
PlariumPlayClientService.exe | Topshelf.HostFactory Information: 0 : |
PlariumPlayClientService.exe | Configuration Result:
[Success] Name Plarium Play Client Service
[Success] ServiceName Plarium Play Client Service
|
PlariumPlayClientService.exe | Topshelf.HostConfigurators.HostConfiguratorImpl Information: 0 : |
PlariumPlayClientService.exe | Topshelf v4.2.1.215, .NET Framework v4.0.30319.42000
|