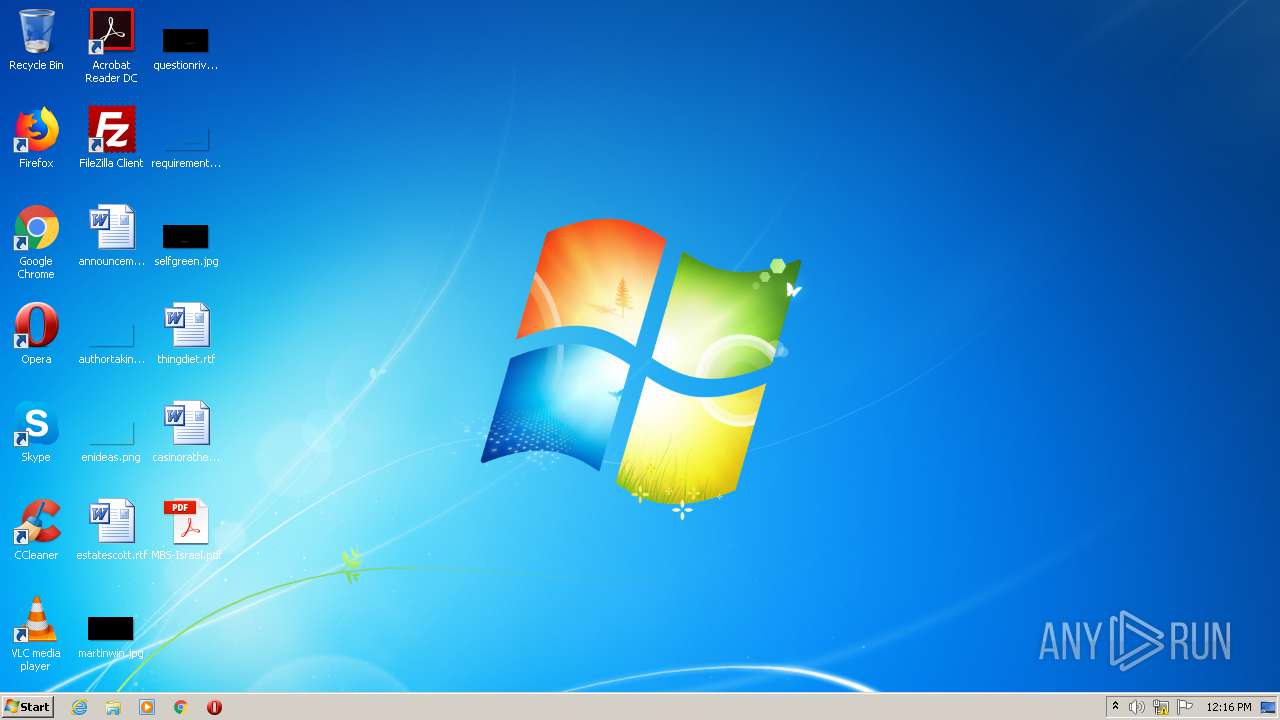
| File name: | MBS-Israel.pdf |
| Full analysis: | https://app.any.run/tasks/48288509-deb2-4e5b-89ae-c049863388e3 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 12:16:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.4 |
| MD5: | 4C61985A5C8C11EB516E592397343F27 |
| SHA1: | 0A2B7AC50F1467588B0E0B1B73FDFD270EAF86A0 |
| SHA256: | 553127CB586591CBFBAE54DD4E28D4CD40FDDDEBAF4E0E7E1F3F23C446A621BB |
| SSDEEP: | 768:G/5p2k9F7m37fOVU1QdwZZE9KKgoqf3o8inTeFYXvvKWH+uSukp7XwVeqOACl5nu:MkfXkO3o8u33KAH2DYD8JE |
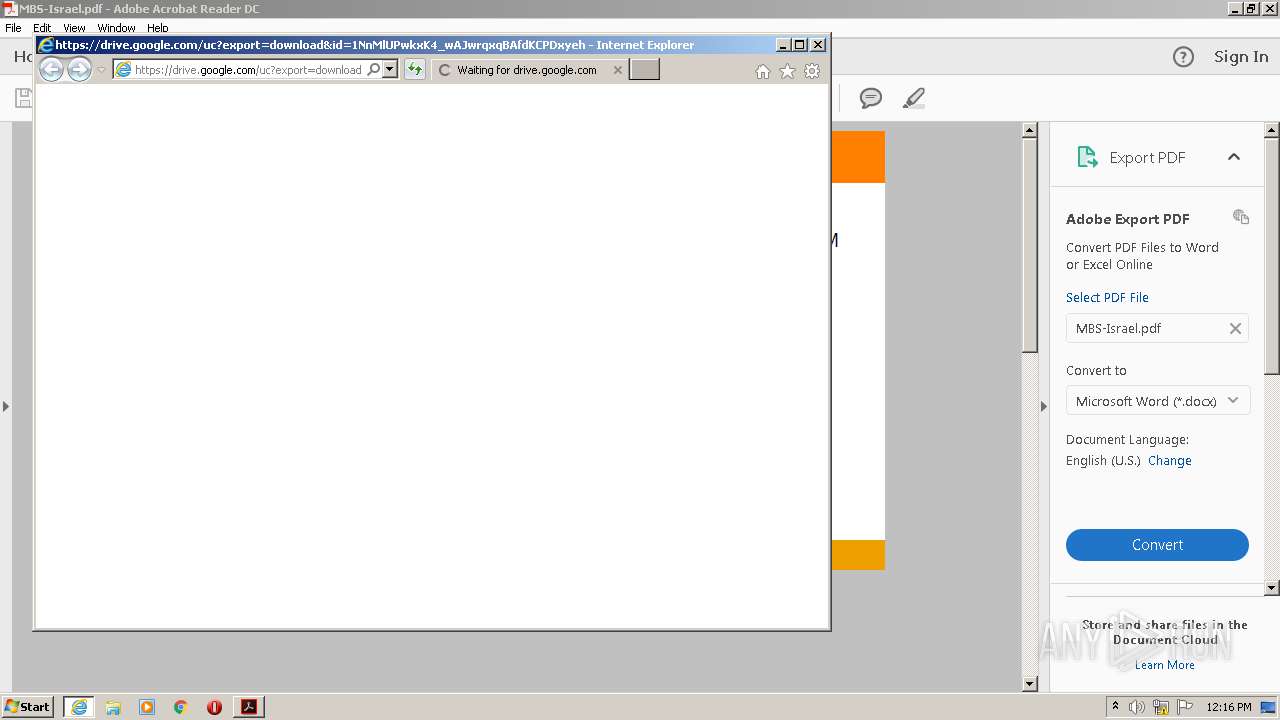
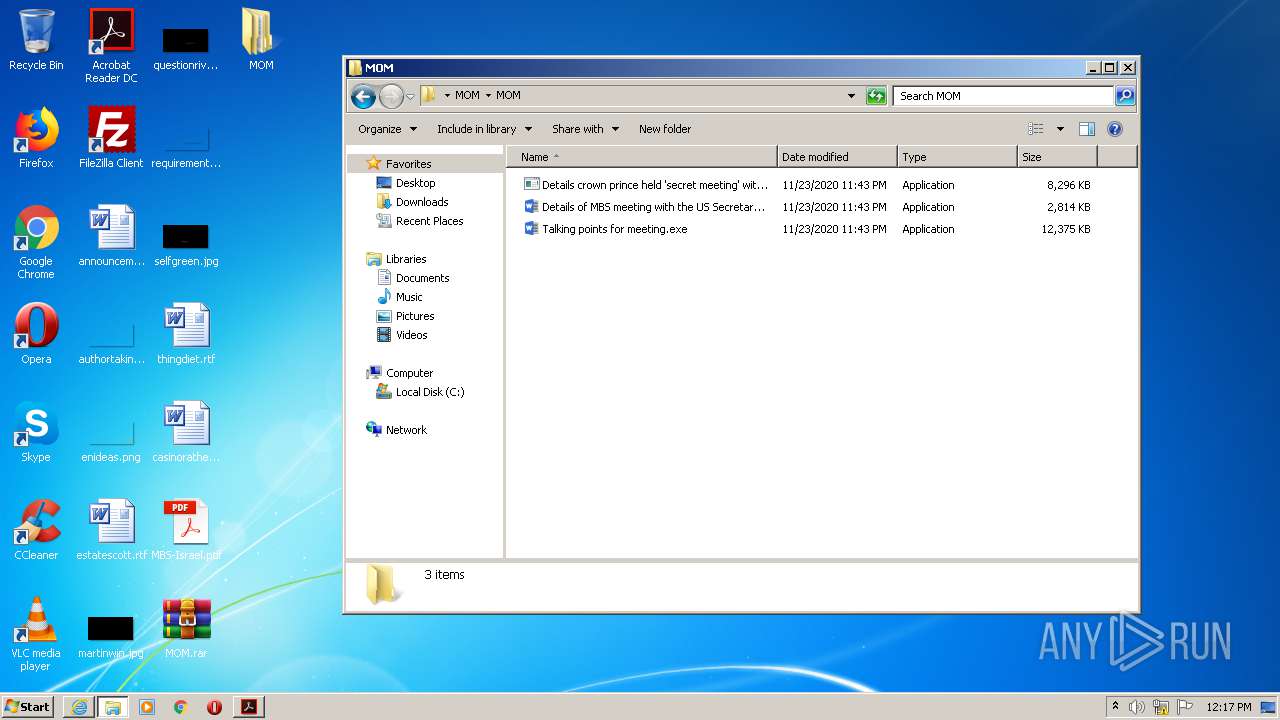
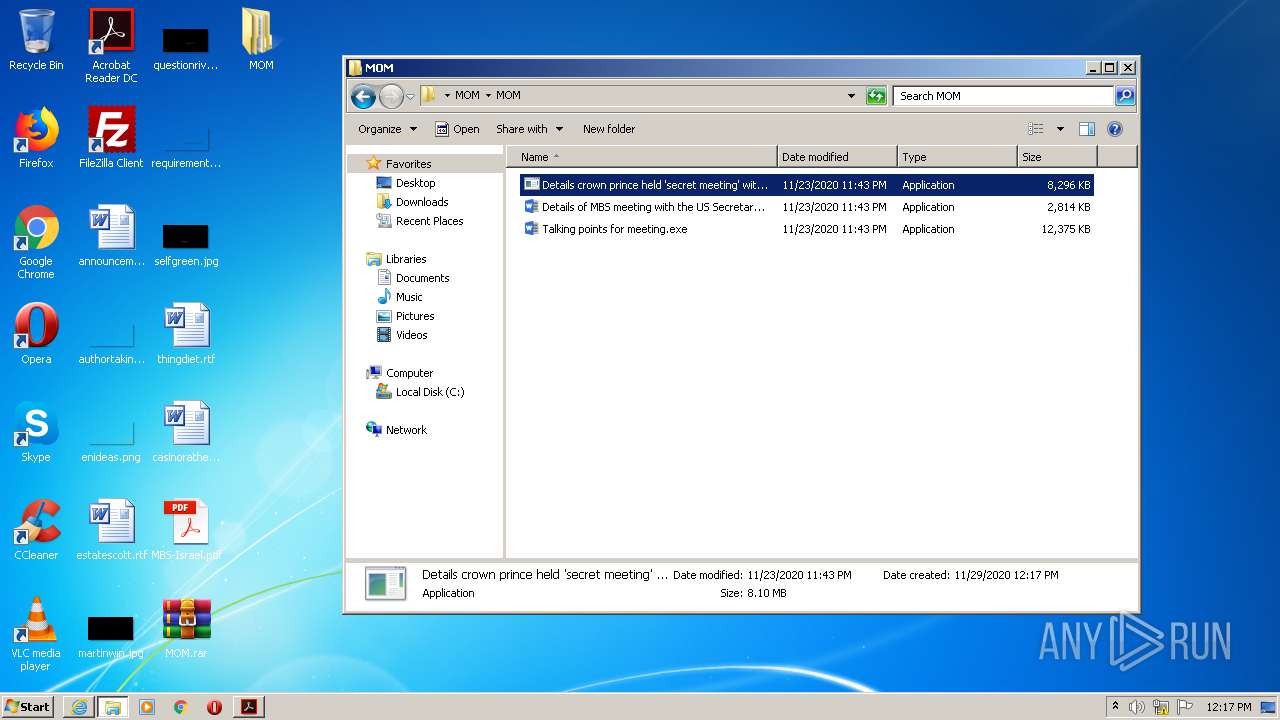
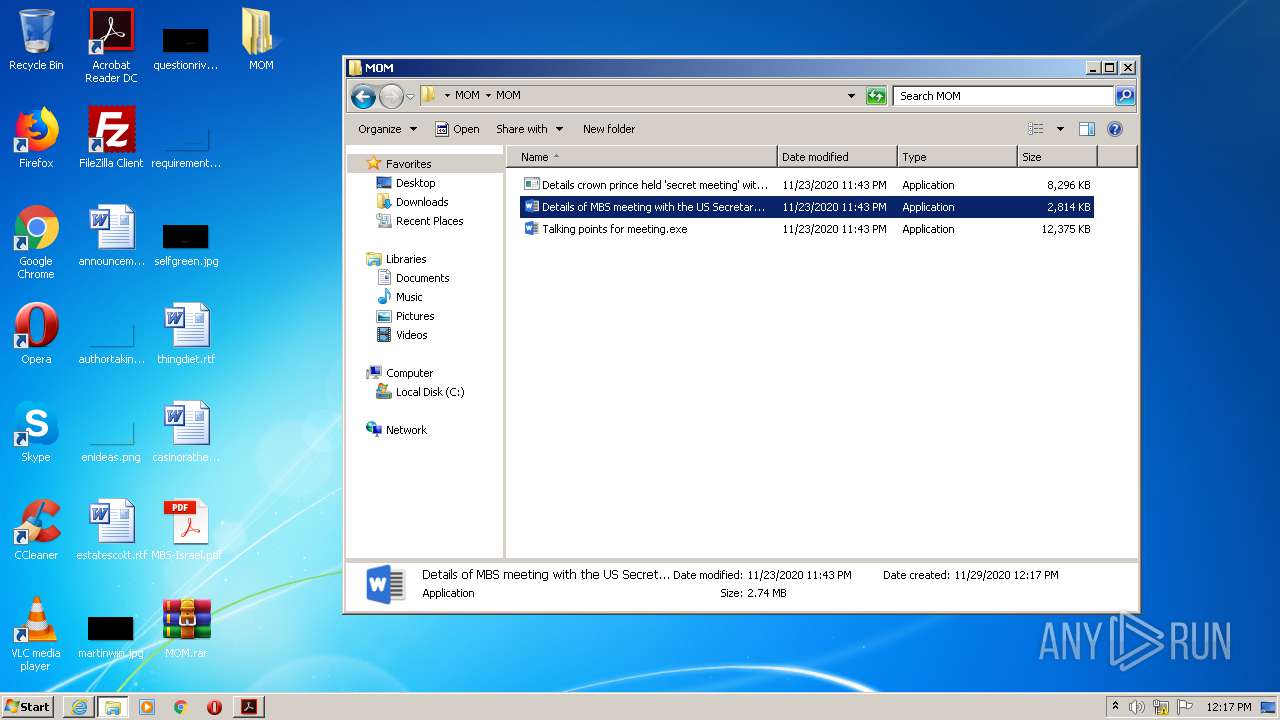
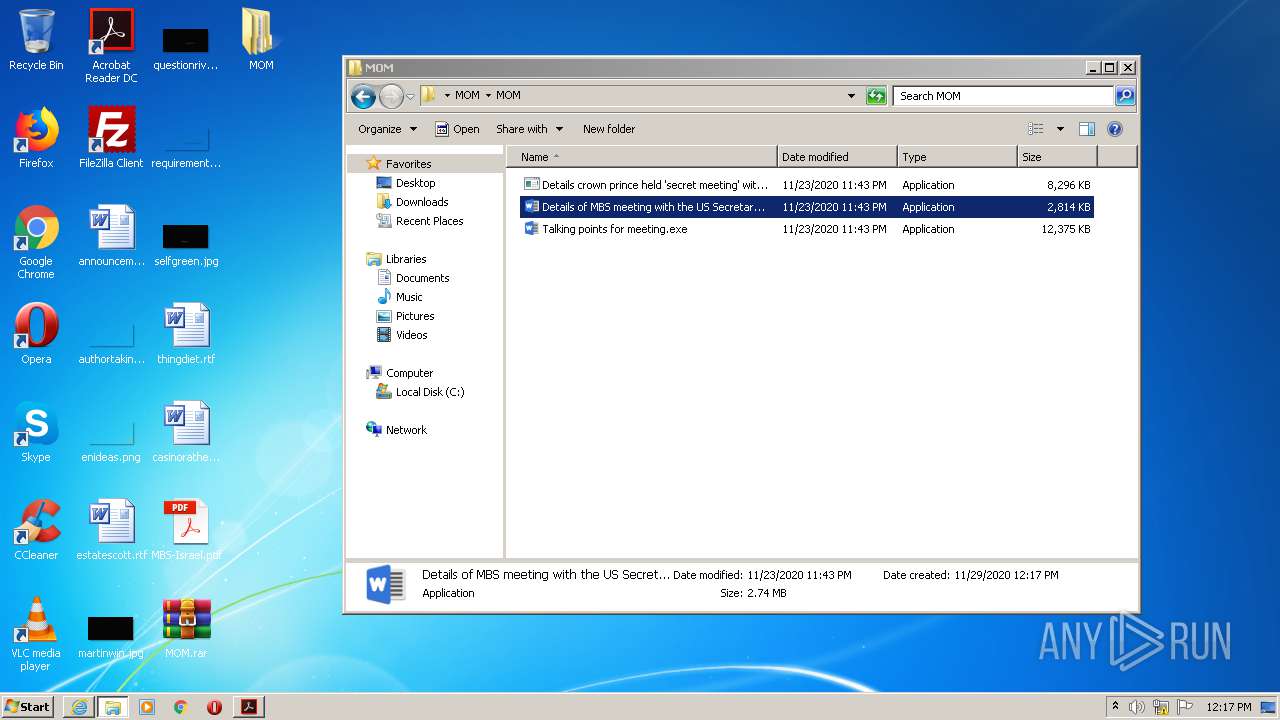
MALICIOUS
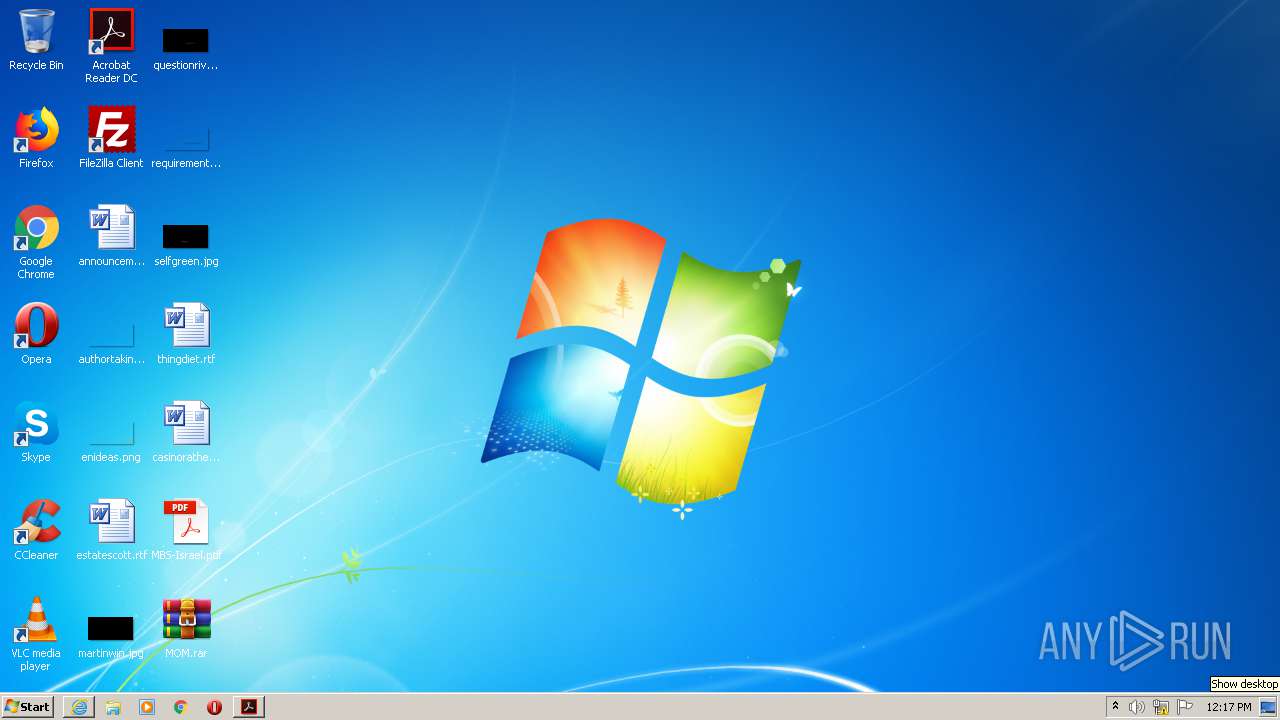
Application was dropped or rewritten from another process
- Details of MBS meeting with the US Secretary of State.Nov.23.20.MoM.exe (PID: 2468)
- Details crown prince held 'secret meeting' with Israeli PM.Nov.23.20.MoM.exe (PID: 3132)
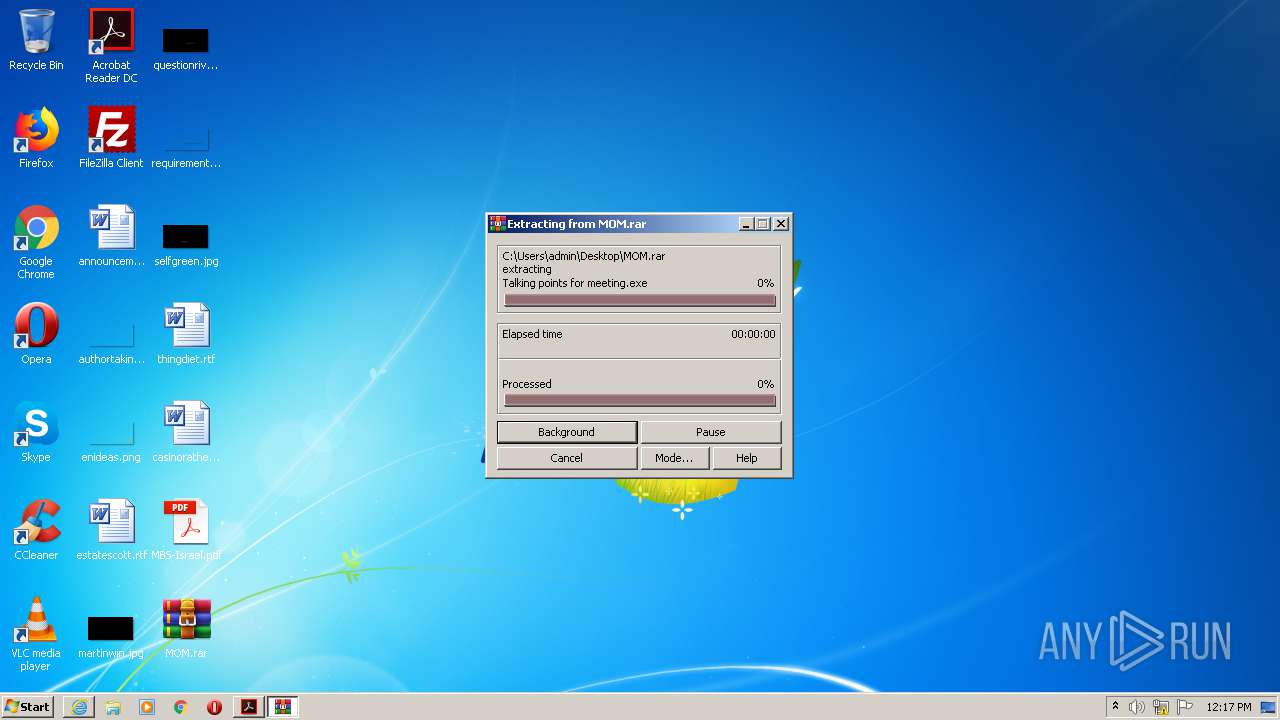
- Talking points for meeting.exe (PID: 2876)
- Talking points for meeting.exe (PID: 2544)
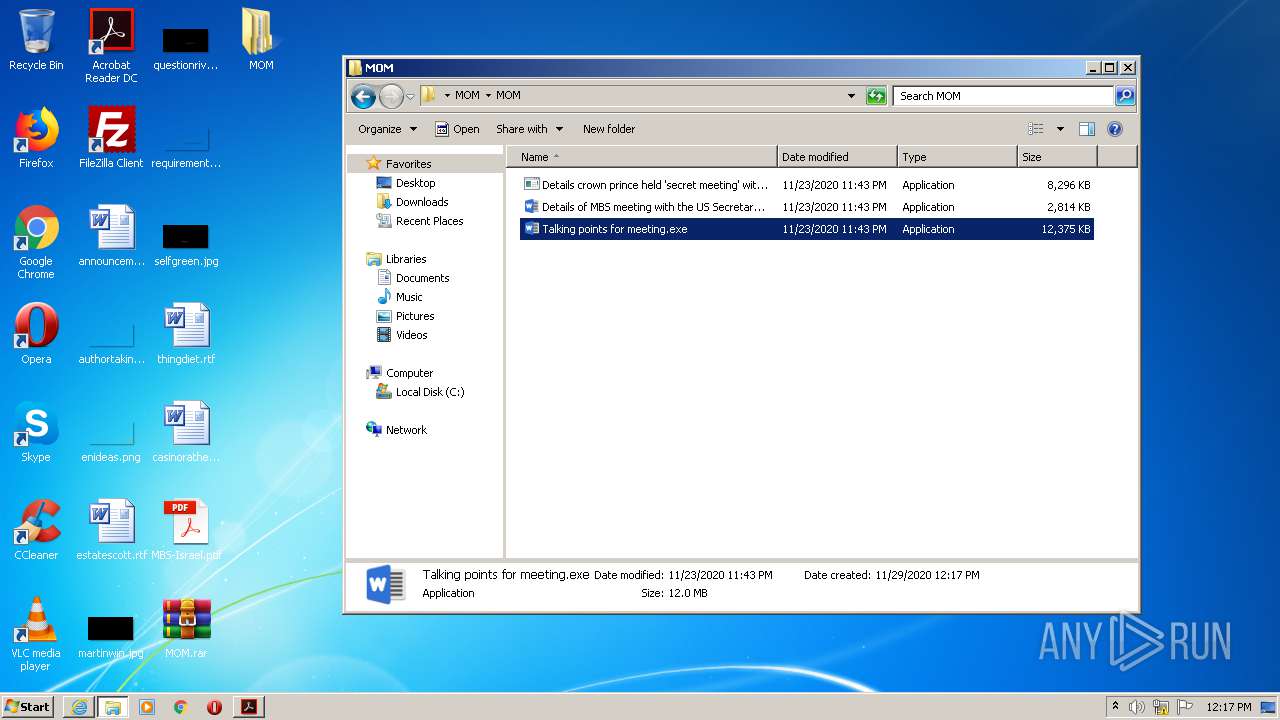
Drops executable file immediately after starts
- Talking points for meeting.exe (PID: 2876)
Loads dropped or rewritten executable
- Talking points for meeting.exe (PID: 2544)
SUSPICIOUS
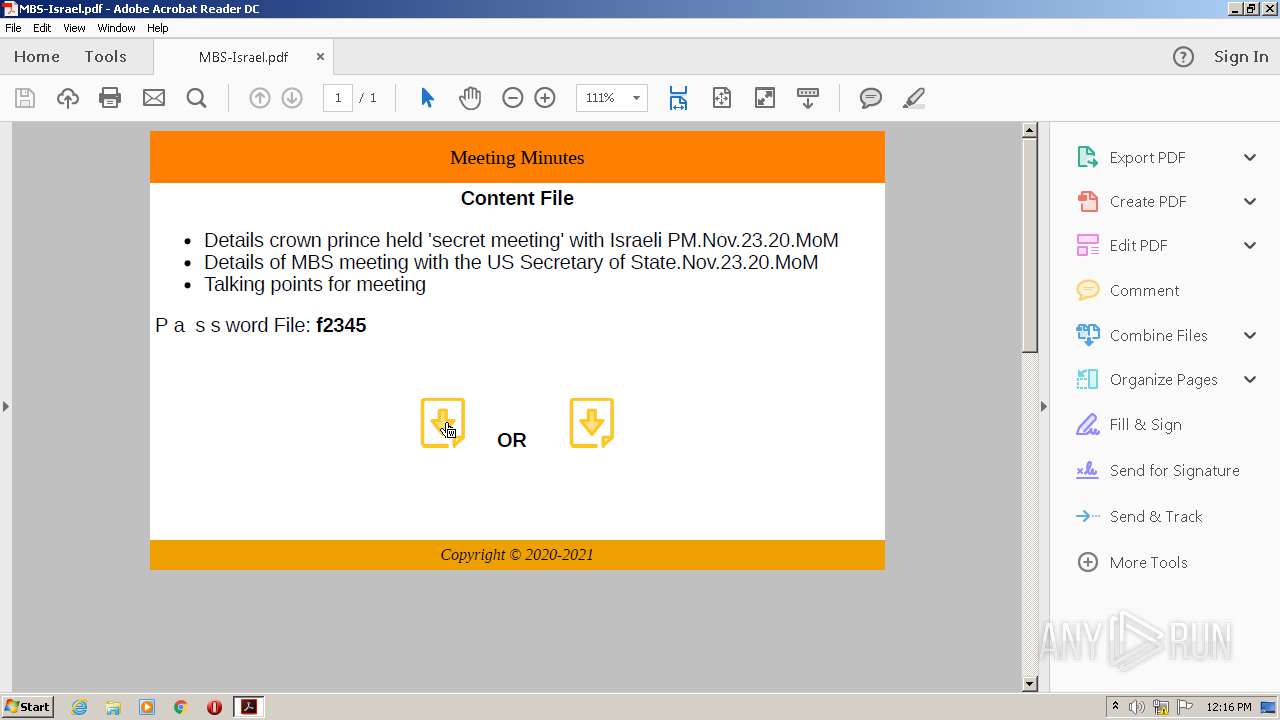
Starts Internet Explorer
- AcroRd32.exe (PID: 2760)
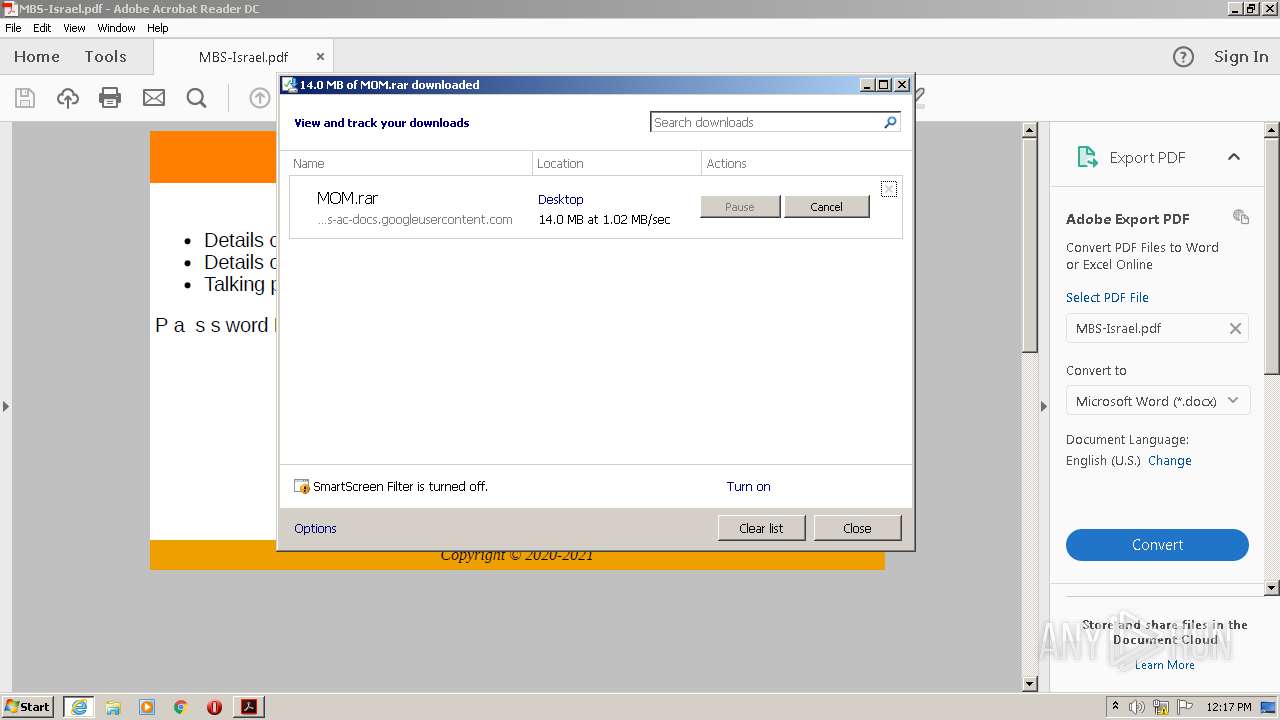
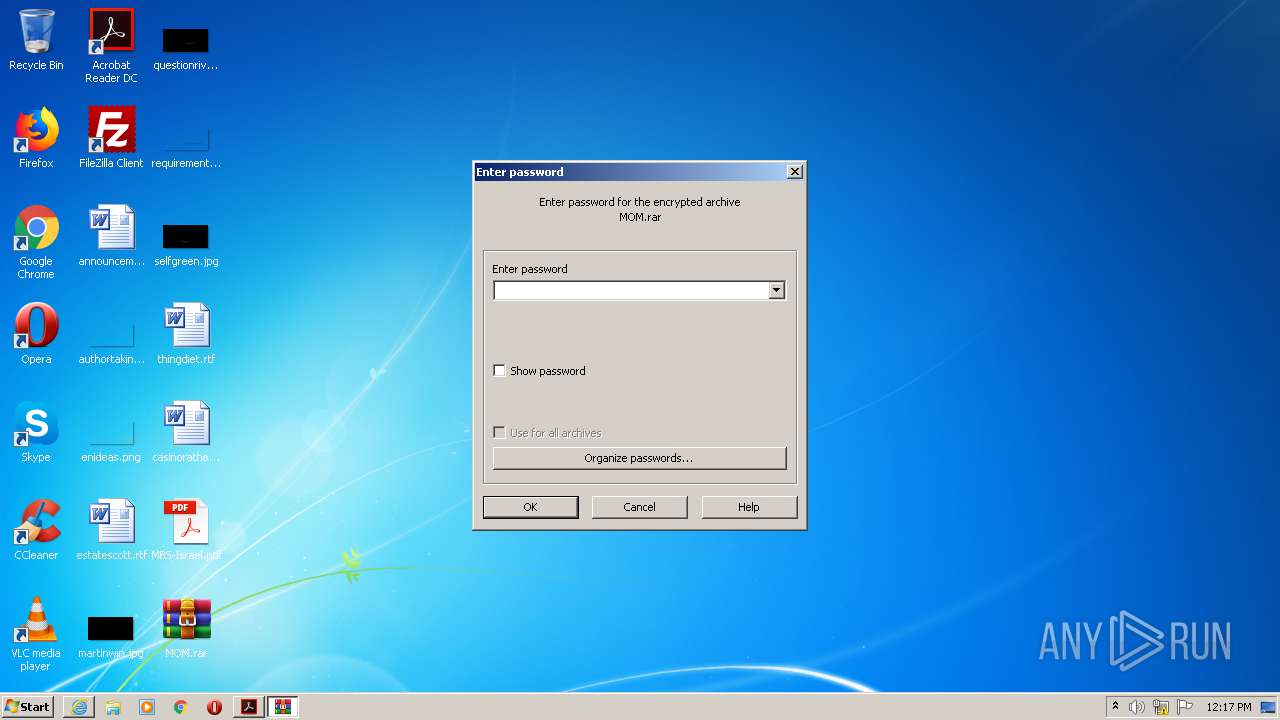
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3156)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3156)
- Talking points for meeting.exe (PID: 2876)
Creates files in the program directory
- AdobeARM.exe (PID: 3212)
- Details crown prince held 'secret meeting' with Israeli PM.Nov.23.20.MoM.exe (PID: 3132)
Drops a file that was compiled in debug mode
- Talking points for meeting.exe (PID: 2876)
Application launched itself
- Talking points for meeting.exe (PID: 2876)
Loads Python modules
- Talking points for meeting.exe (PID: 2544)
INFO
Changes internet zones settings
- iexplore.exe (PID: 856)
Application launched itself
- RdrCEF.exe (PID: 2772)
- AcroRd32.exe (PID: 2760)
- iexplore.exe (PID: 856)
Creates files in the user directory
- iexplore.exe (PID: 3760)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2760)
- iexplore.exe (PID: 3760)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2760)
Reads the hosts file
- RdrCEF.exe (PID: 2772)
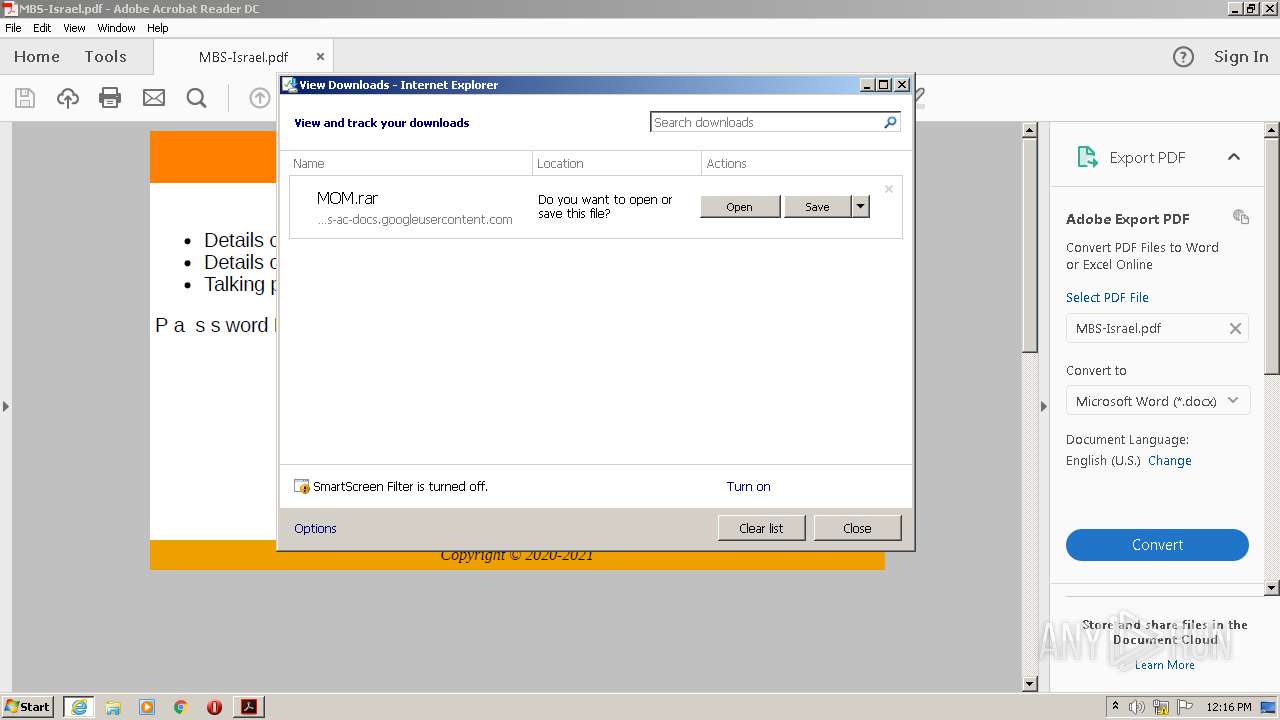
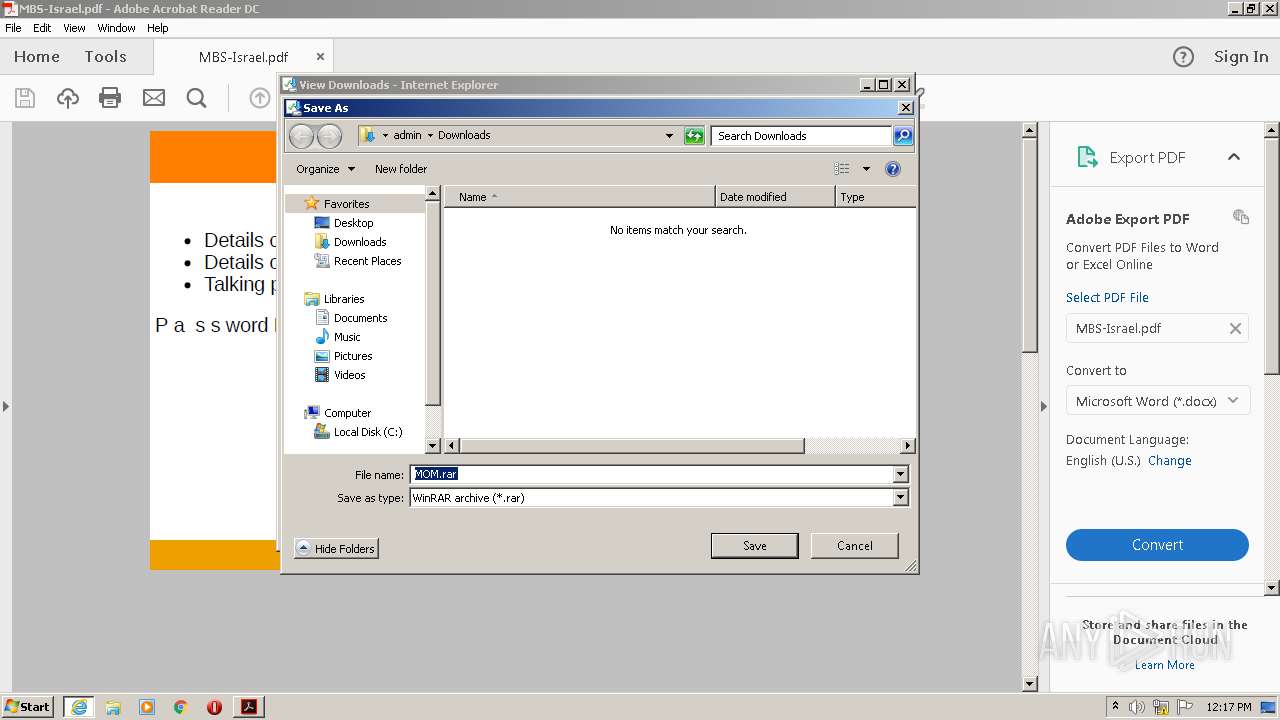
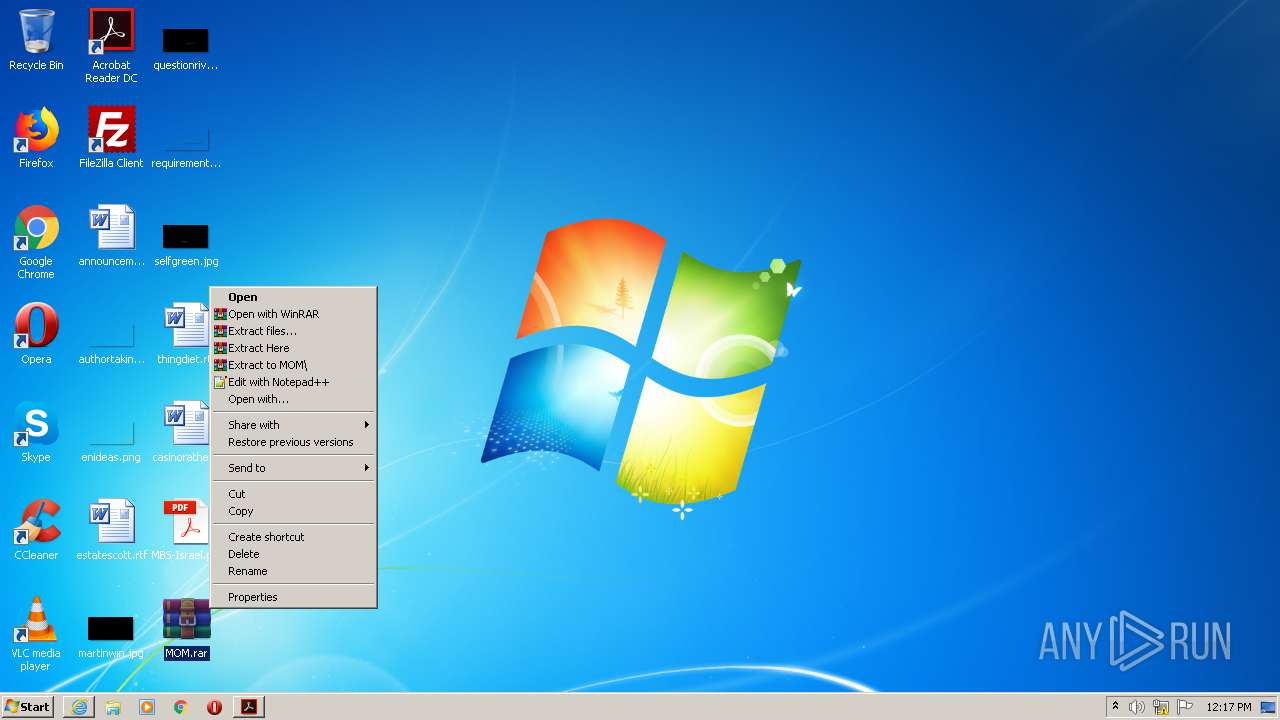
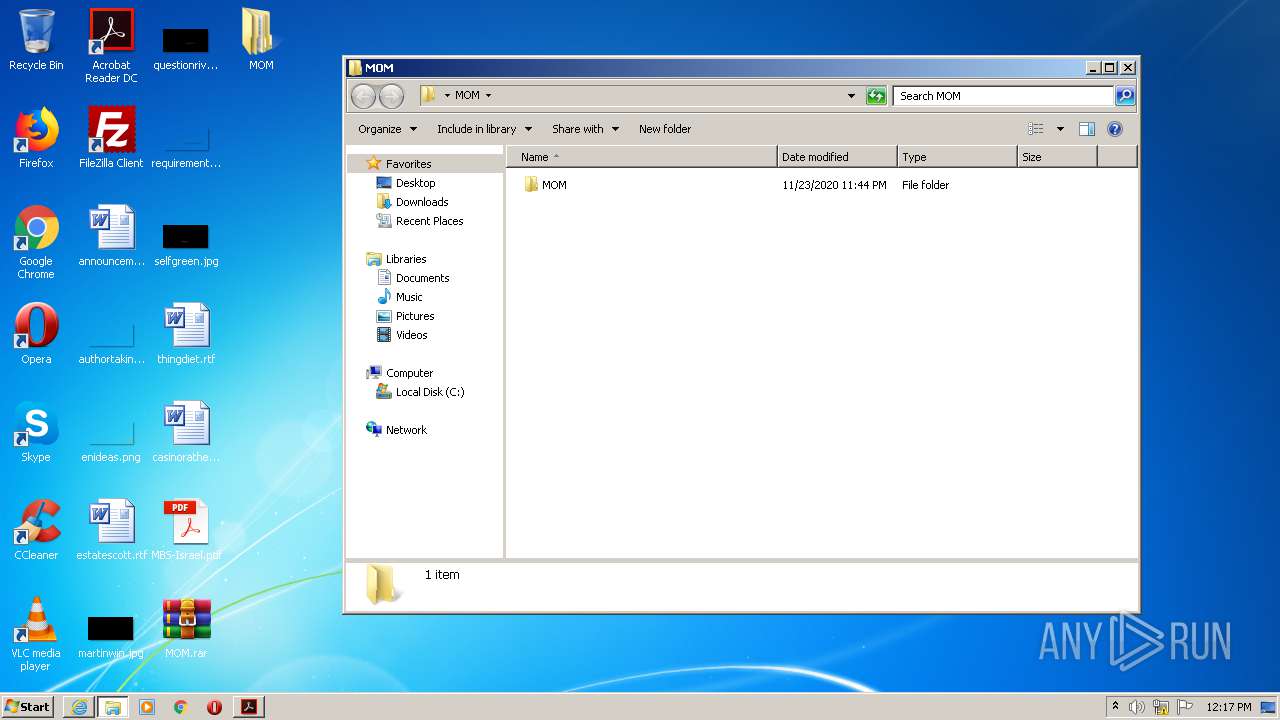
Manual execution by user
- WinRAR.exe (PID: 3156)
- Details crown prince held 'secret meeting' with Israeli PM.Nov.23.20.MoM.exe (PID: 3132)
- Details of MBS meeting with the US Secretary of State.Nov.23.20.MoM.exe (PID: 2468)
- Talking points for meeting.exe (PID: 2876)
Modifies the phishing filter of IE
- iexplore.exe (PID: 856)
Dropped object may contain Bitcoin addresses
- Talking points for meeting.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.4 |
|---|---|
| Linearized: | No |
| PageCount: | 1 |
| Creator: | Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.66 Safari/537.36 |
| Producer: | Skia/PDF m87 |
| CreateDate: | 2020:11:24 08:37:26+00:00 |
| ModifyDate: | 2020:11:24 08:37:26+00:00 |
Total processes
52
Monitored processes
14
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\Internet Explorer\iexplore.exe" https://drive.google.com/uc?export=download&id=1NnMlUPwkxK4_wAJwrqxqBAfdKCPDxyeh | C:\Program Files\Internet Explorer\iexplore.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2772.0.39598891\623797318" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\Desktop\MOM\MOM\Details of MBS meeting with the US Secretary of State.Nov.23.20.MoM.exe" | C:\Users\admin\Desktop\MOM\MOM\Details of MBS meeting with the US Secretary of State.Nov.23.20.MoM.exe | explorer.exe | ||||||||||||
User: admin Company: Open Office World Integrity Level: MEDIUM Description: World Exit code: 0 Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\Desktop\MOM\MOM\Talking points for meeting.exe" | C:\Users\admin\Desktop\MOM\MOM\Talking points for meeting.exe | — | Talking points for meeting.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\Desktop\MBS-Israel.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2876 | "C:\Users\admin\Desktop\MOM\MOM\Talking points for meeting.exe" | C:\Users\admin\Desktop\MOM\MOM\Talking points for meeting.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\Desktop\MBS-Israel.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2772.1.1582301984\2051139371" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
1 431
Read events
1 258
Write events
171
Delete events
2
Modification events
| (PID) Process: | (2912) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2760) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000E06C868549C6D601 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2541273174 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852681 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (856) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
29
Suspicious files
16
Text files
29
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5751.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5752.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rysuftu_1ab6xkk_28w.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R57iwr_1ab6xkl_28w.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rzmx9us_1ab6xkm_28w.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Racref6_1ab6xkj_28w.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Cab8C6B.tmp | — | |
MD5:— | SHA256:— | |||
| 2760 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Tar8C6C.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\MOM[1].rar | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
13
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3760 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | der | 472 b | whitelisted |
2760 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAhrYrWeURCWAgAAAACAVck%3D | US | der | 471 b | whitelisted |
3760 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2760 | AcroRd32.exe | GET | 304 | 92.122.188.31:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2760 | AcroRd32.exe | GET | 304 | 92.122.188.31:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3760 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAhrYrWeURCWAgAAAACAVck%3D | US | der | 471 b | whitelisted |
2760 | AcroRd32.exe | GET | 304 | 92.122.188.31:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3760 | iexplore.exe | 172.217.22.78:443 | drive.google.com | Google Inc. | US | whitelisted |
3760 | iexplore.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3760 | iexplore.exe | 216.58.206.1:443 | doc-0s-ac-docs.googleusercontent.com | Google Inc. | US | whitelisted |
2760 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2760 | AcroRd32.exe | 104.79.88.64:443 | armmf.adobe.com | Time Warner Cable Internet LLC | US | suspicious |
— | — | 104.111.214.232:443 | ardownload2.adobe.com | Akamai International B.V. | NL | whitelisted |
— | — | 104.79.88.64:443 | armmf.adobe.com | Time Warner Cable Internet LLC | US | suspicious |
2760 | AcroRd32.exe | 92.122.188.31:80 | acroipm2.adobe.com | NTT America, Inc. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
doc-0s-ac-docs.googleusercontent.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Details of MBS meeting with the US Secretary of State.Nov.23.20.MoM.exe | Click on : x=583,y=229
|