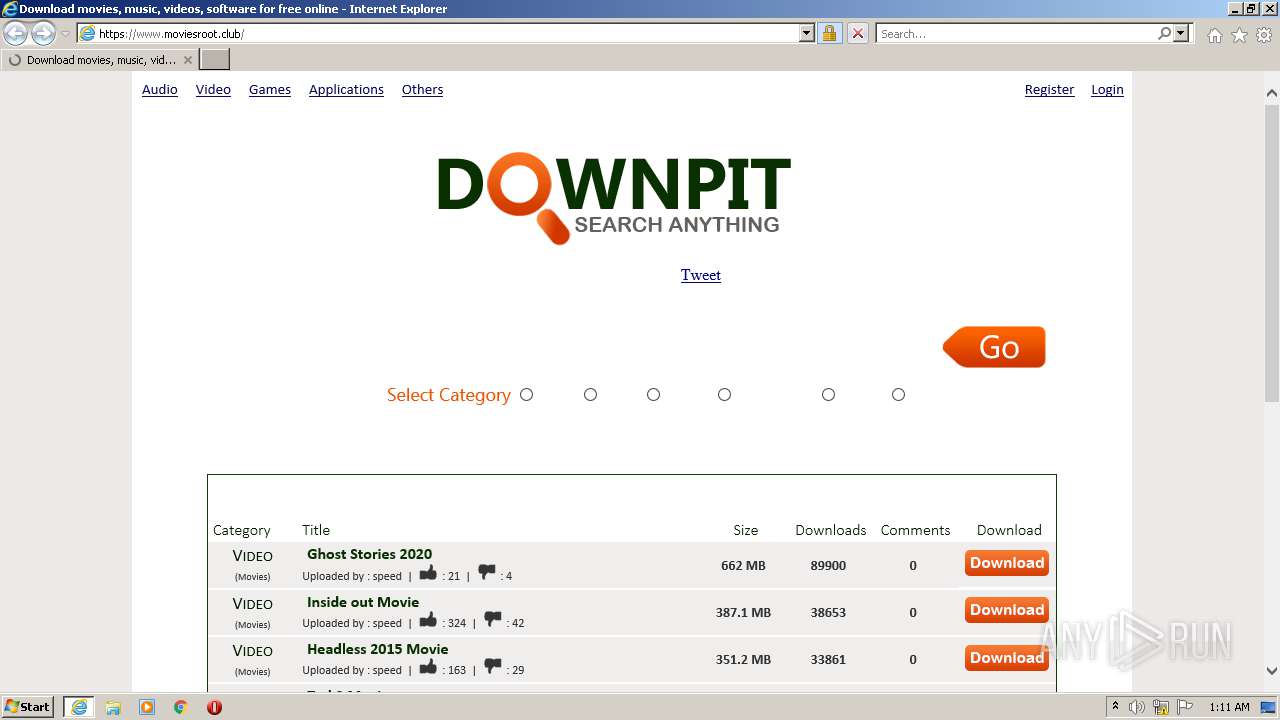
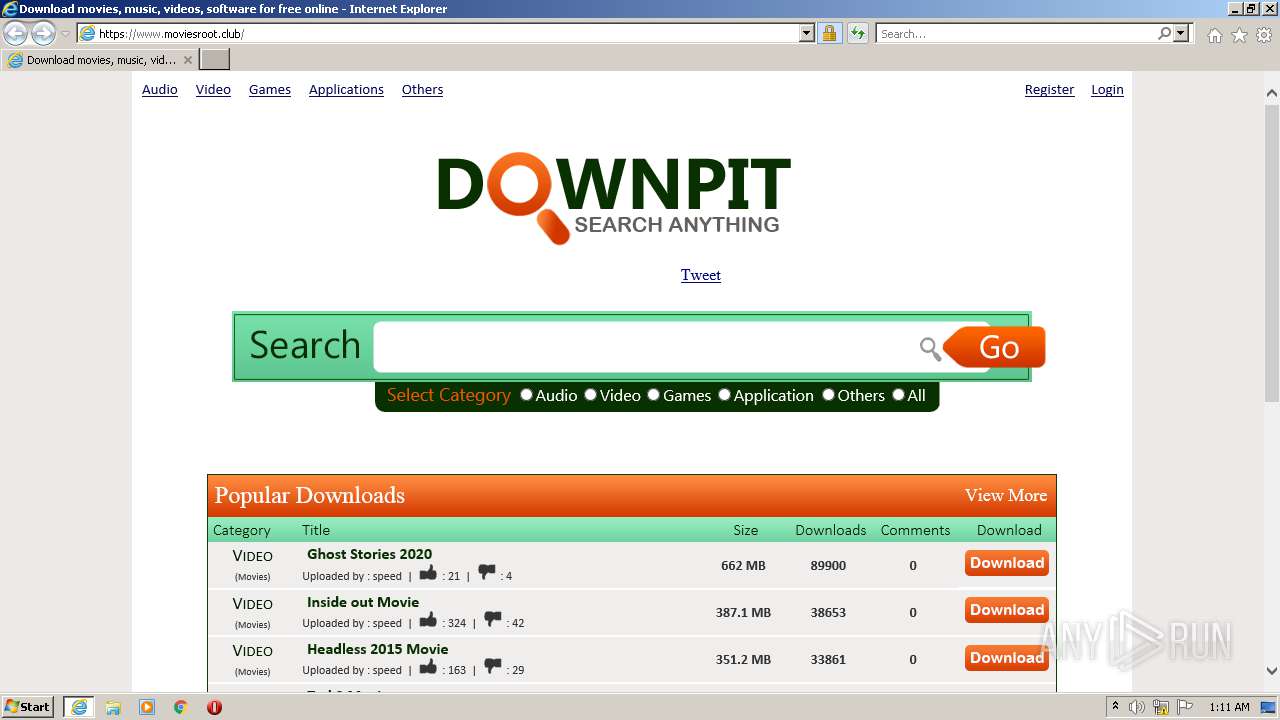
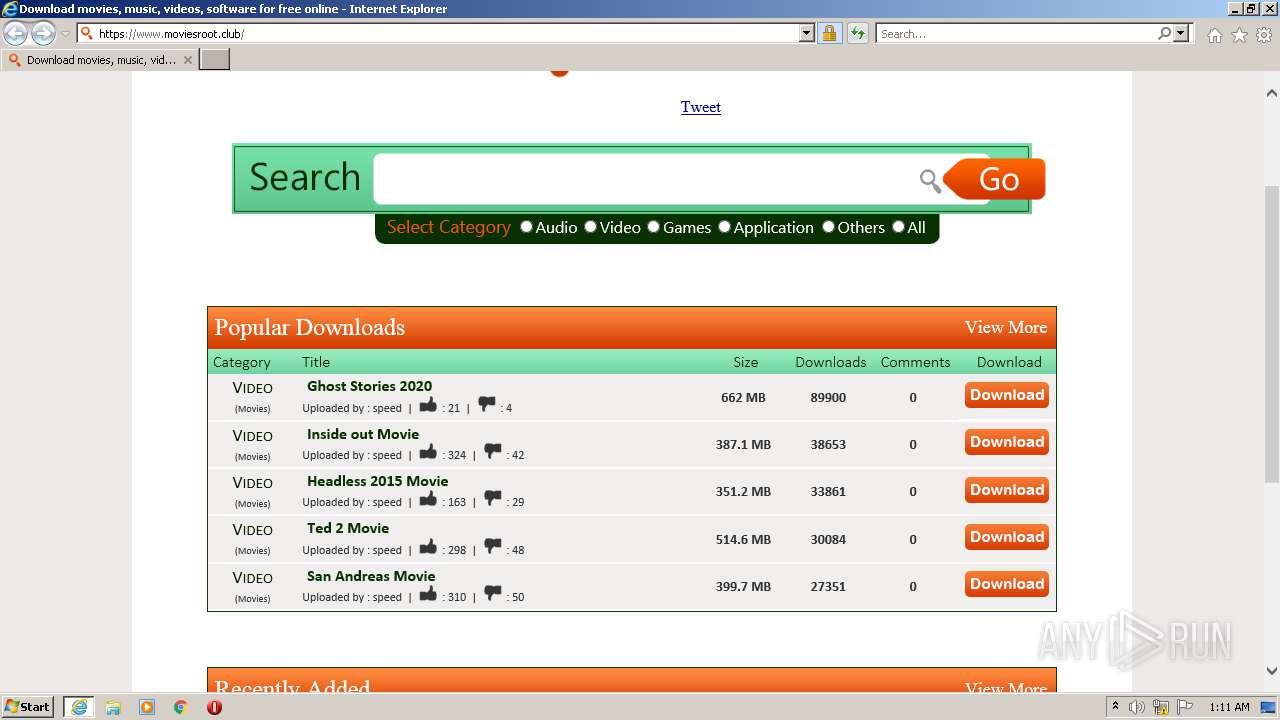
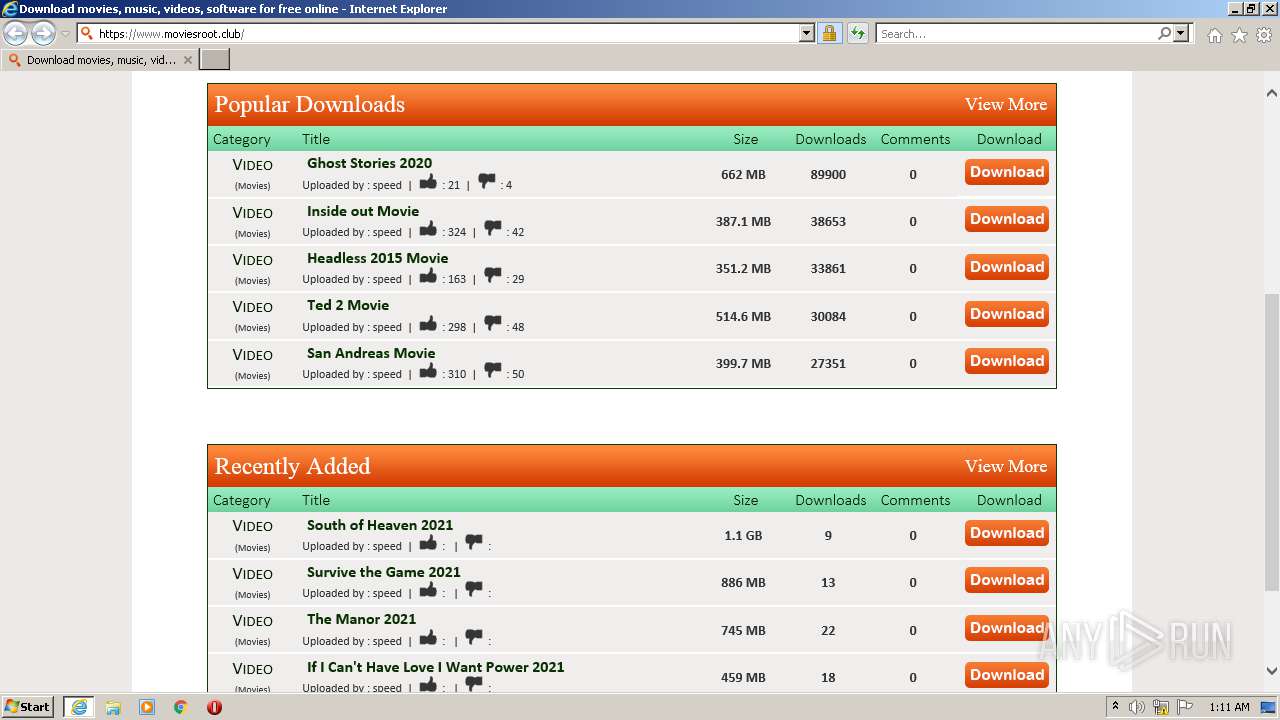
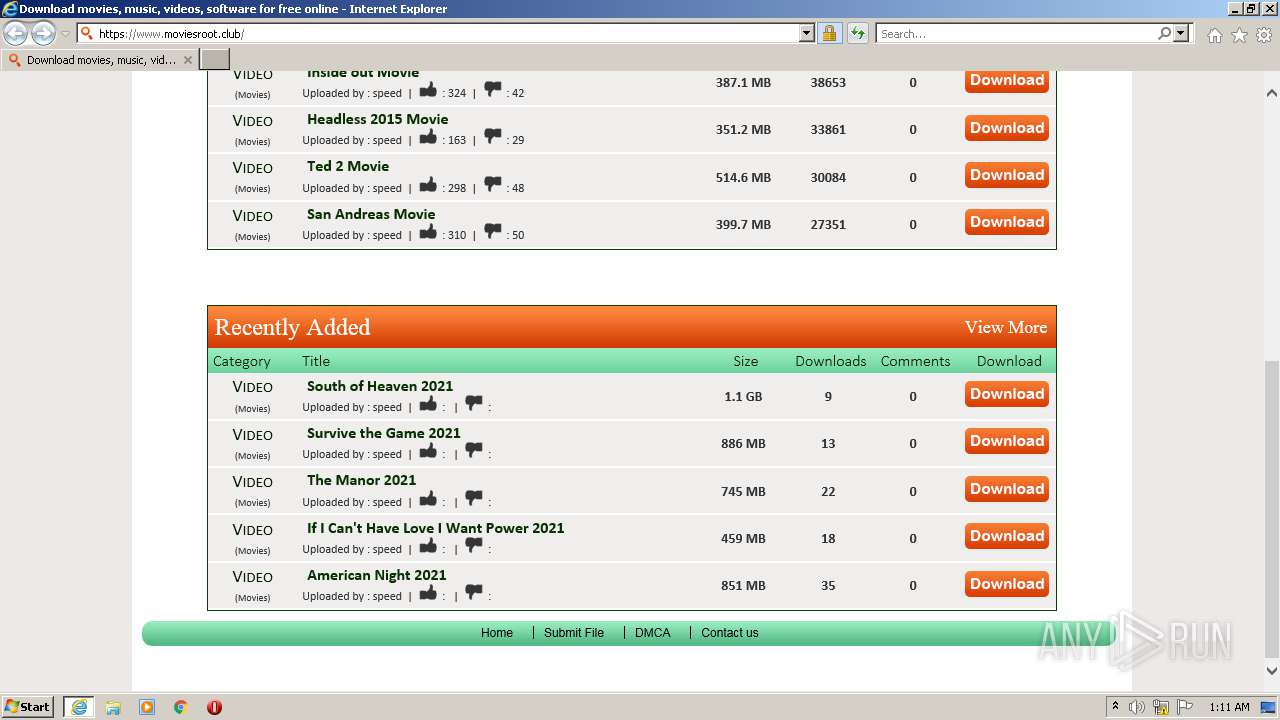
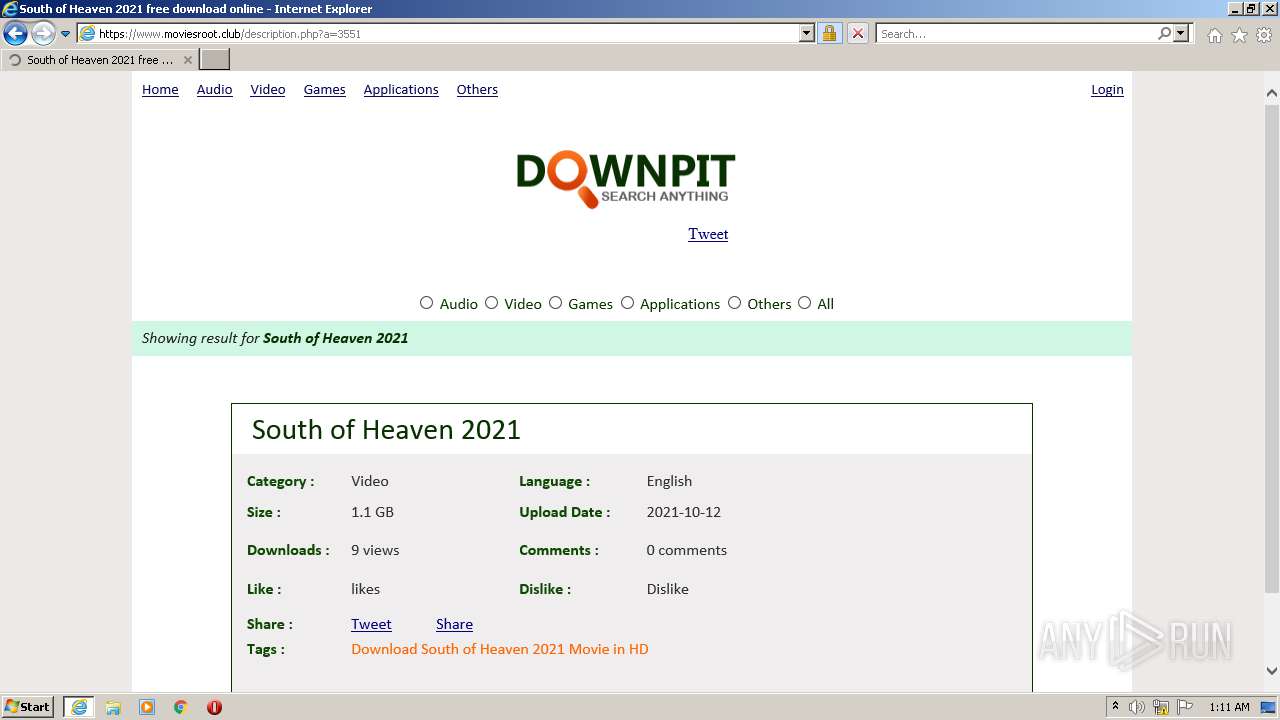
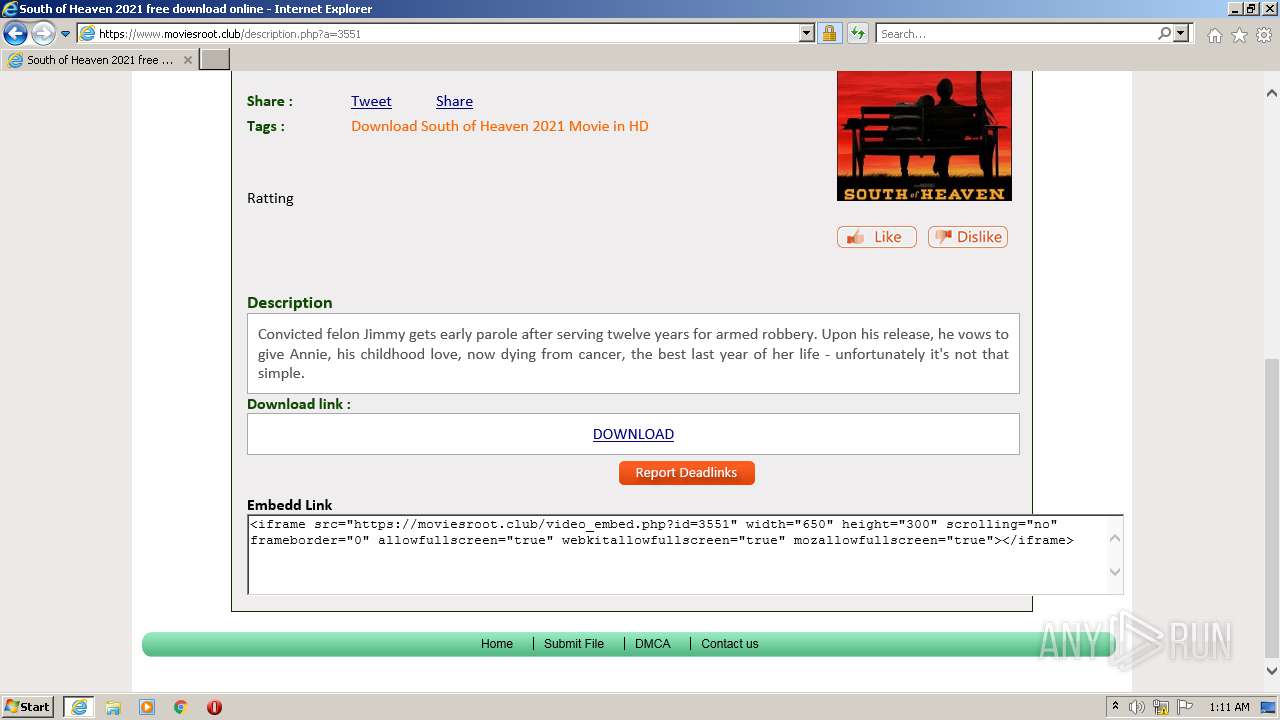
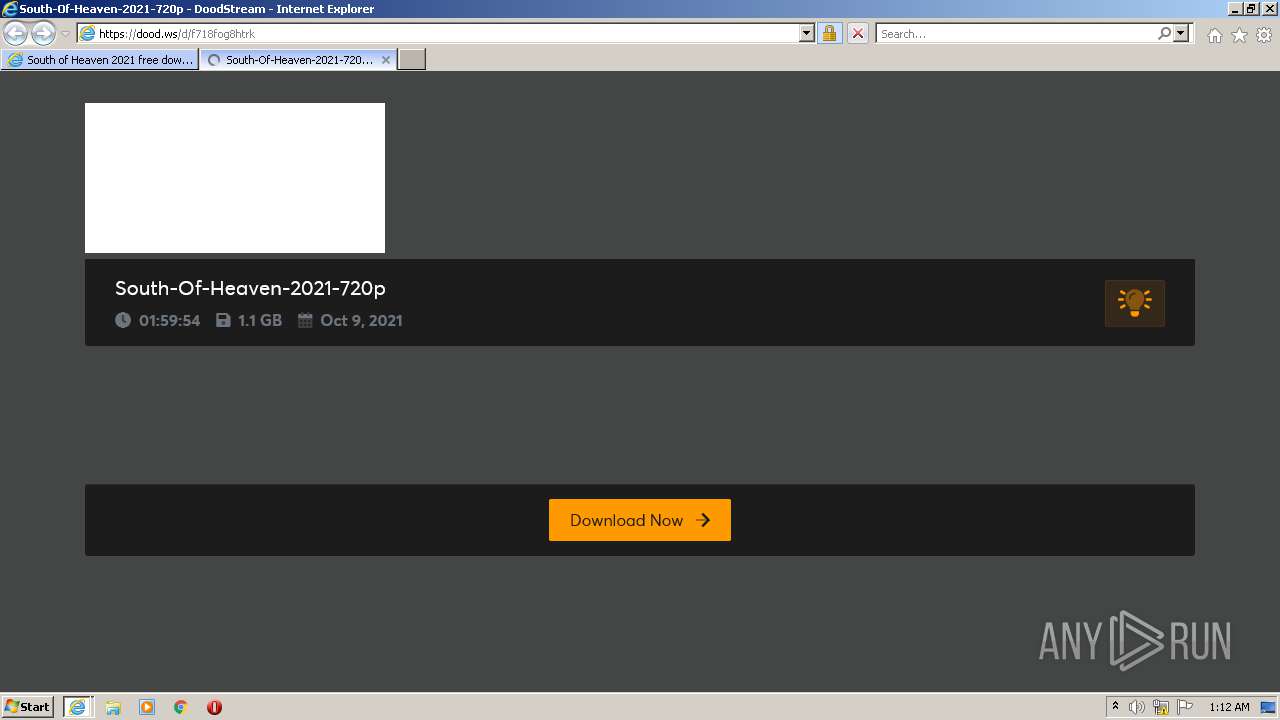
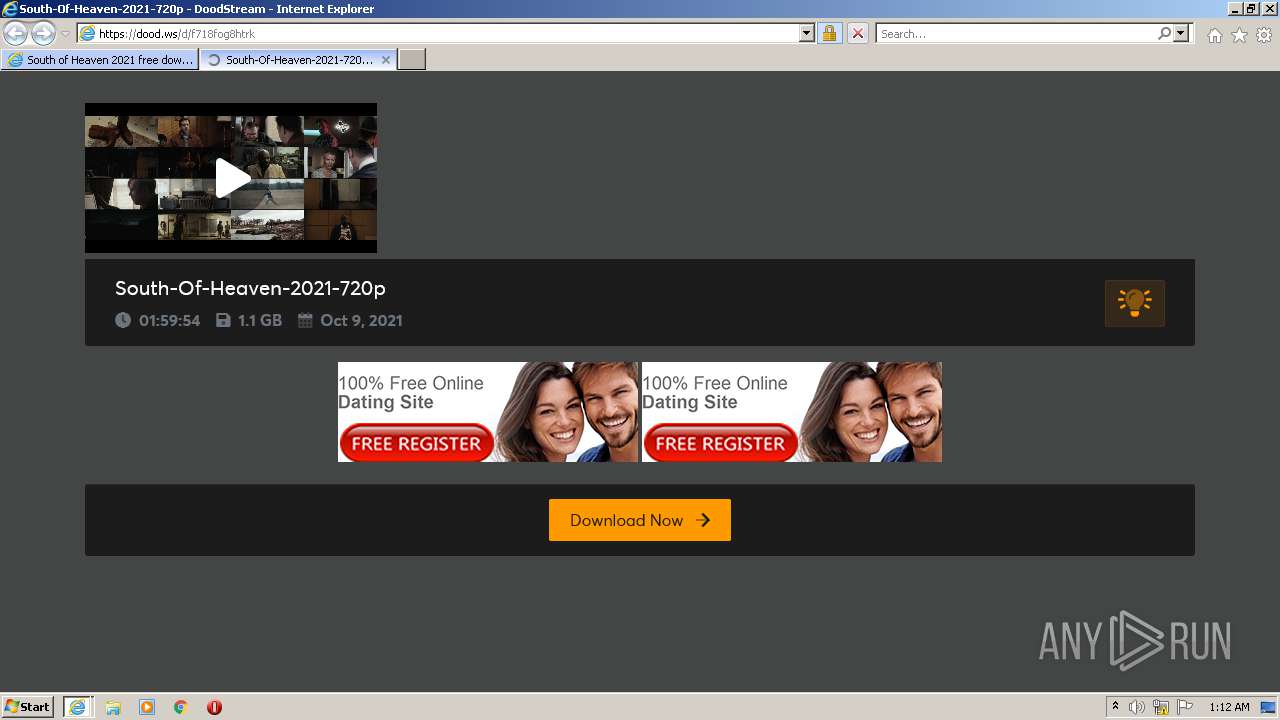
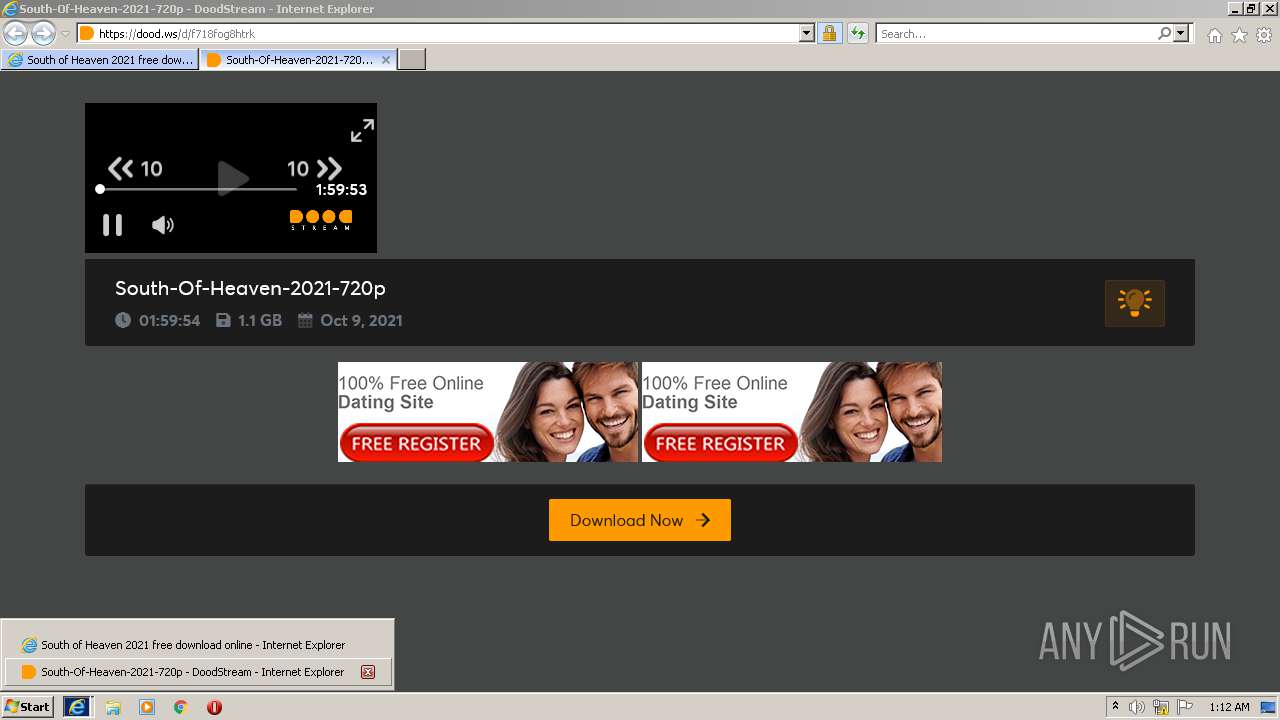
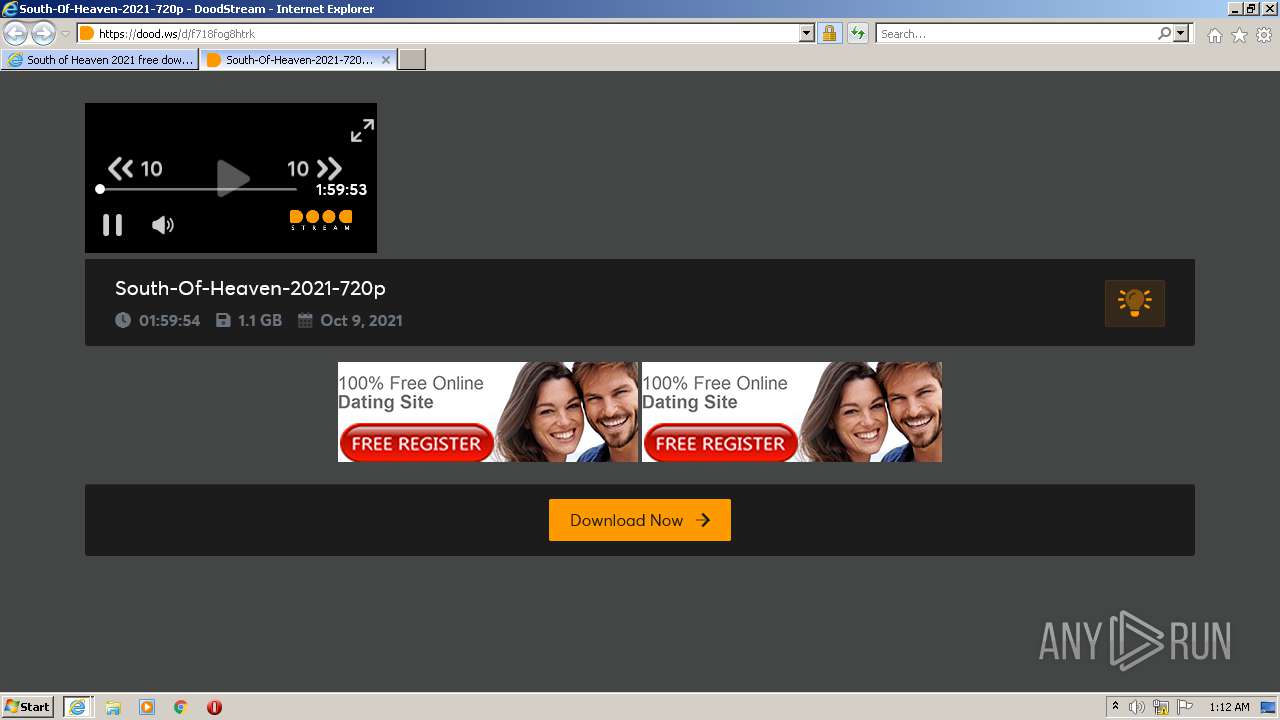
| URL: | https://www.moviesroot.club |
| Full analysis: | https://app.any.run/tasks/9926fb1d-31f8-4fd0-abee-724e4ccb40e0 |
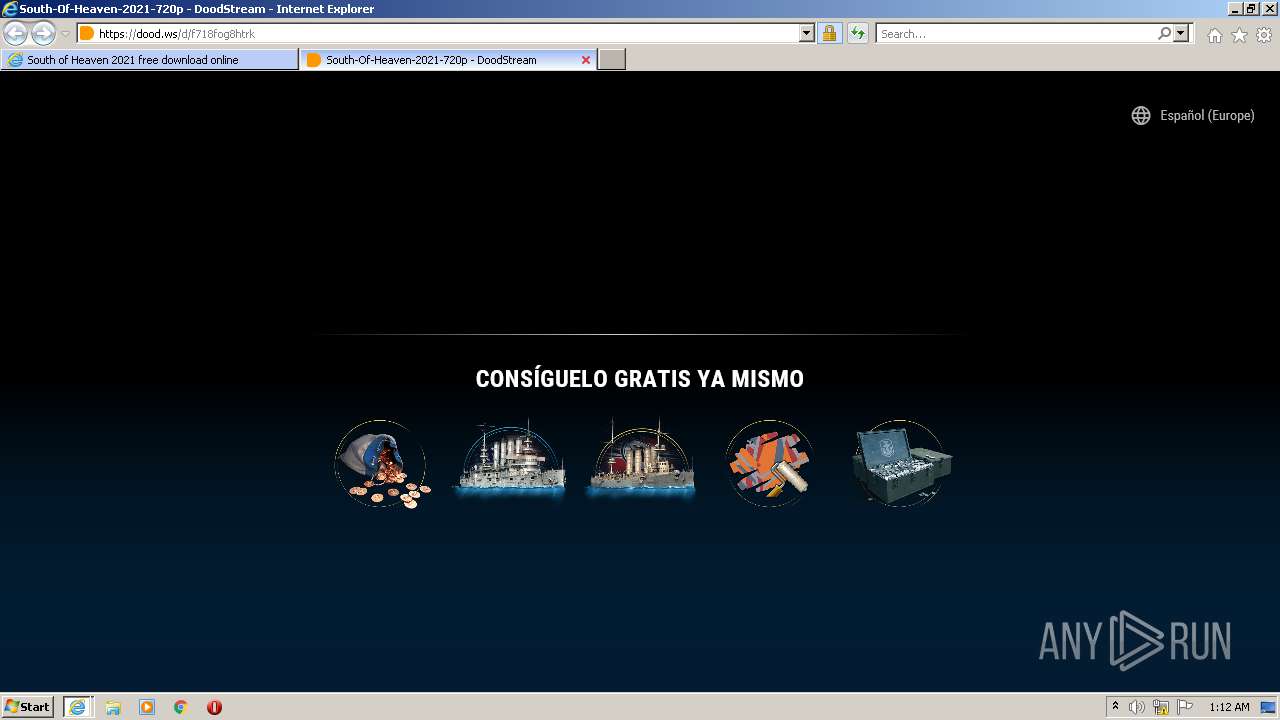
| Verdict: | Malicious activity |
| Analysis date: | October 13, 2021, 00:10:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F62E3C391ADBC65C0192D12B4D0C63DF |
| SHA1: | 60E897738F8244B5D7684365270060B1F2F58B6A |
| SHA256: | 5521A70E45F1B7B294E40039FEB832F6CEE30CBAC2756D6D743C7AD08B0C86C4 |
| SSDEEP: | 3:N8DSLjIj:2OLO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3080)
INFO
Reads the computer name
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3080)
Checks supported languages
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3080)
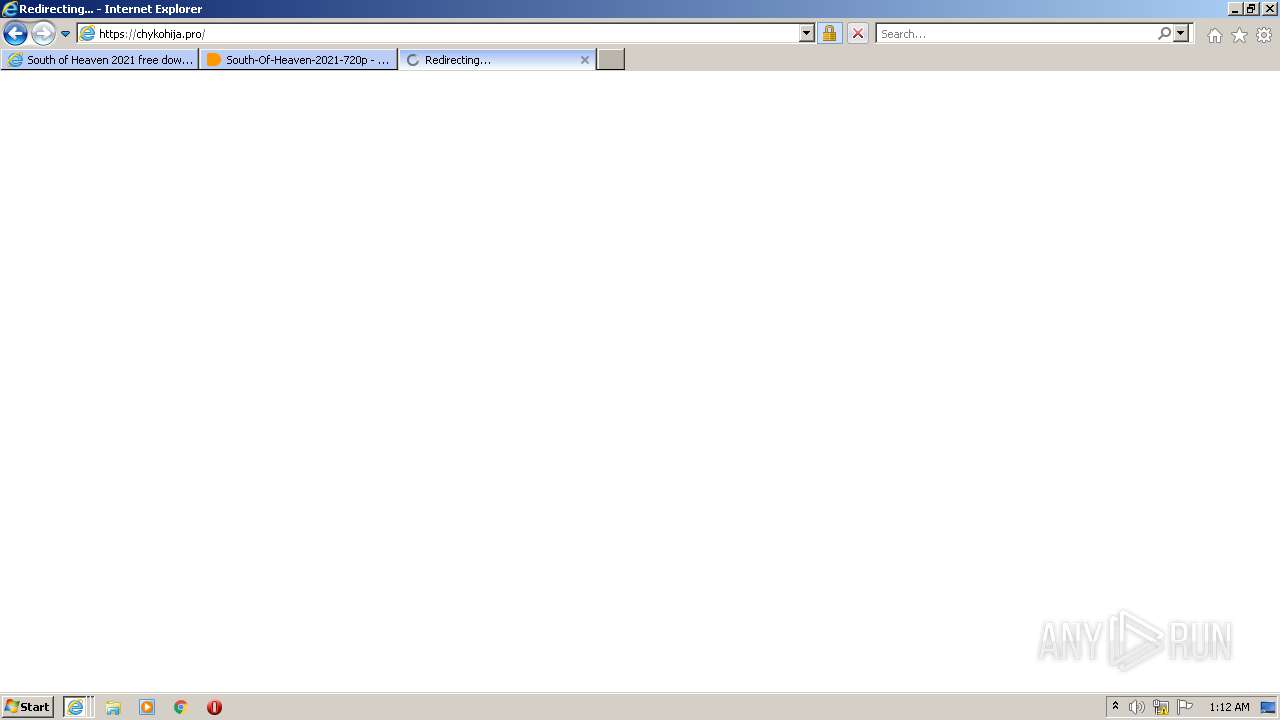
Changes internet zones settings
- iexplore.exe (PID: 1796)
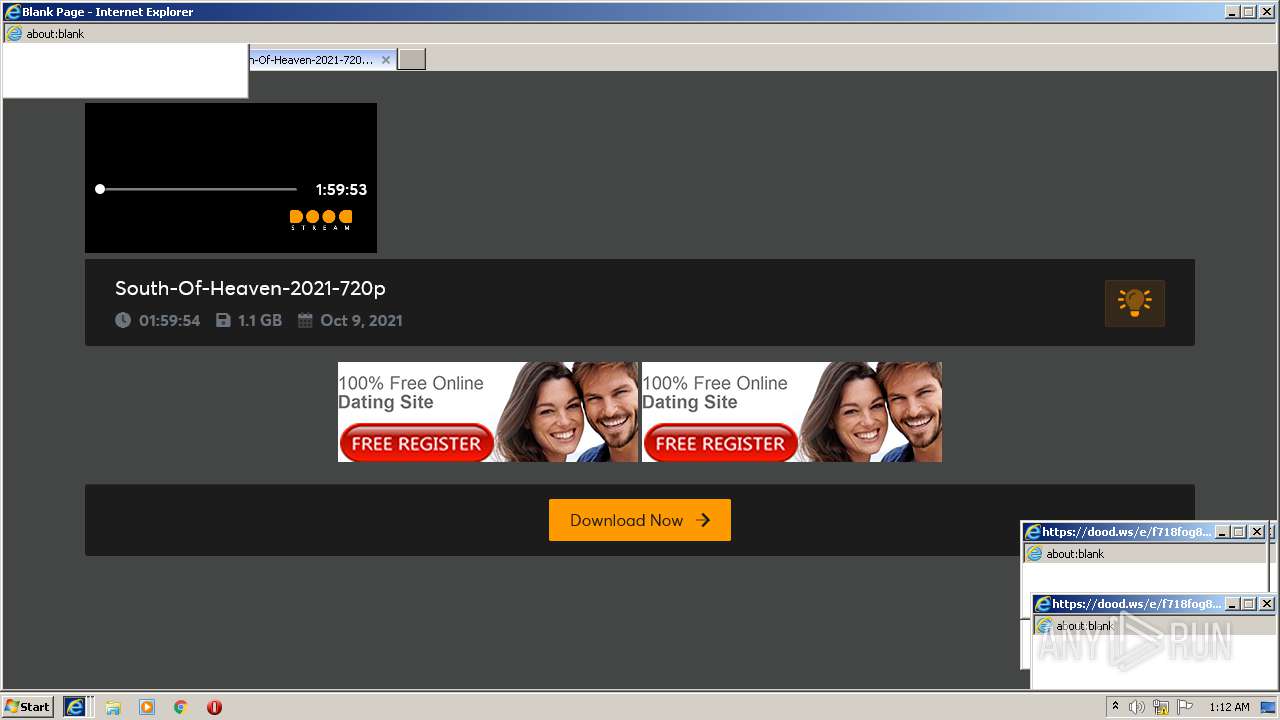
Application launched itself
- iexplore.exe (PID: 1796)
Checks Windows Trust Settings
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 3080)
- iexplore.exe (PID: 2748)
Reads internet explorer settings
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3080)
Reads settings of System Certificates
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 3080)
Creates files in the user directory
- iexplore.exe (PID: 2332)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 1796)
- iexplore.exe (PID: 3080)
Changes settings of System certificates
- iexplore.exe (PID: 1796)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1796)
Reads the date of Windows installation
- iexplore.exe (PID: 1796)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1796 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.moviesroot.club" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1796 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1796 CREDAT:988445 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1796 CREDAT:2954511 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
41 816
Read events
41 506
Write events
306
Delete events
4
Modification events
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30916550 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30916550 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1796) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
65
Text files
173
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1796 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:04B1FF103233164595D0B7AECB657DED | SHA256:772E3E3CDFF00B1552F1AB0DD27DD98E0BBC875D216EE5B57C8D68D8175BB89B | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:A65591A91AD826EA2F7BCFDBA441A81B | SHA256:9AB2E8332CB84355C763D6BEBEBEE5695697F2171F666287B4399D58B03F25A1 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEBAC.tmp | compressed | |
MD5:AB5C36D10261C173C5896F3478CDC6B7 | SHA256:F8E90FB0557FE49D7702CFB506312AC0B24C97802F9C782696DB6D47F434E8E9 | |||
| 1796 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:FAF3892962BAF3DCA7704C6AED0571C7 | SHA256:3E79581CC89B16FDEF8423584D276C81B0954C7BAE04B01000B3448D27D8F4E3 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\969E0CB71BD3ACEAB05D4D903B0B2FF3 | der | |
MD5:DDA63E183B5087721DB6CD515C0552F4 | SHA256:C65B5C521FDEF41454DD2B791663FAB72A29D1031D3C96BA6BCBE6631DAF57E9 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEBAA.tmp | compressed | |
MD5:AB5C36D10261C173C5896F3478CDC6B7 | SHA256:F8E90FB0557FE49D7702CFB506312AC0B24C97802F9C782696DB6D47F434E8E9 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AB5C36D10261C173C5896F3478CDC6B7 | SHA256:F8E90FB0557FE49D7702CFB506312AC0B24C97802F9C782696DB6D47F434E8E9 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:F706DAC244BA8C2216C33F0C910253C1 | SHA256:3EF8B4AE854636E47C38E8E368C0ADD178110C55F86BABFEBC4D0C54D4C93A04 | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEBAB.tmp | cat | |
MD5:E9E21888D1DC2348DEE343980E7188FA | SHA256:3D249DB46B4BD1CFAE8F56B272F7116B218AC9D64225D1109751EE487FA9F3AE | |||
| 2332 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEBAD.tmp | cat | |
MD5:E9E21888D1DC2348DEE343980E7188FA | SHA256:3D249DB46B4BD1CFAE8F56B272F7116B218AC9D64225D1109751EE487FA9F3AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
181
DNS requests
82
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2332 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?7f056f10f998b3e0 | US | compressed | 59.7 Kb | whitelisted |
1796 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?06d0dc43f640557d | US | compressed | 4.70 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a566a1b3045672d6 | US | compressed | 59.7 Kb | whitelisted |
2332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAabDtMQzKUWkARaV838pvw%3D | US | der | 471 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1796 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
2332 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
1084 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d8362a2e56ad649b | US | — | — | whitelisted |
2332 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDN2kMnYNBcUwoAAAAA%2F2Z4 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2332 | iexplore.exe | 104.21.81.107:443 | www.moviesroot.club | Cloudflare Inc | US | unknown |
1796 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1796 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2332 | iexplore.exe | 172.67.141.227:443 | www.moviesroot.club | — | US | malicious |
1796 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2332 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
2332 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2332 | iexplore.exe | 95.101.89.75:80 | r3.o.lencr.org | Akamai International B.V. | — | unknown |
2332 | iexplore.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2332 | iexplore.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.moviesroot.club |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.facebook.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
moviesroot.club |
| malicious |