| File name: | rizzles.exe |
| Full analysis: | https://app.any.run/tasks/9e6884ed-f9eb-44a4-ab32-026998656714 |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2019, 17:14:39 |
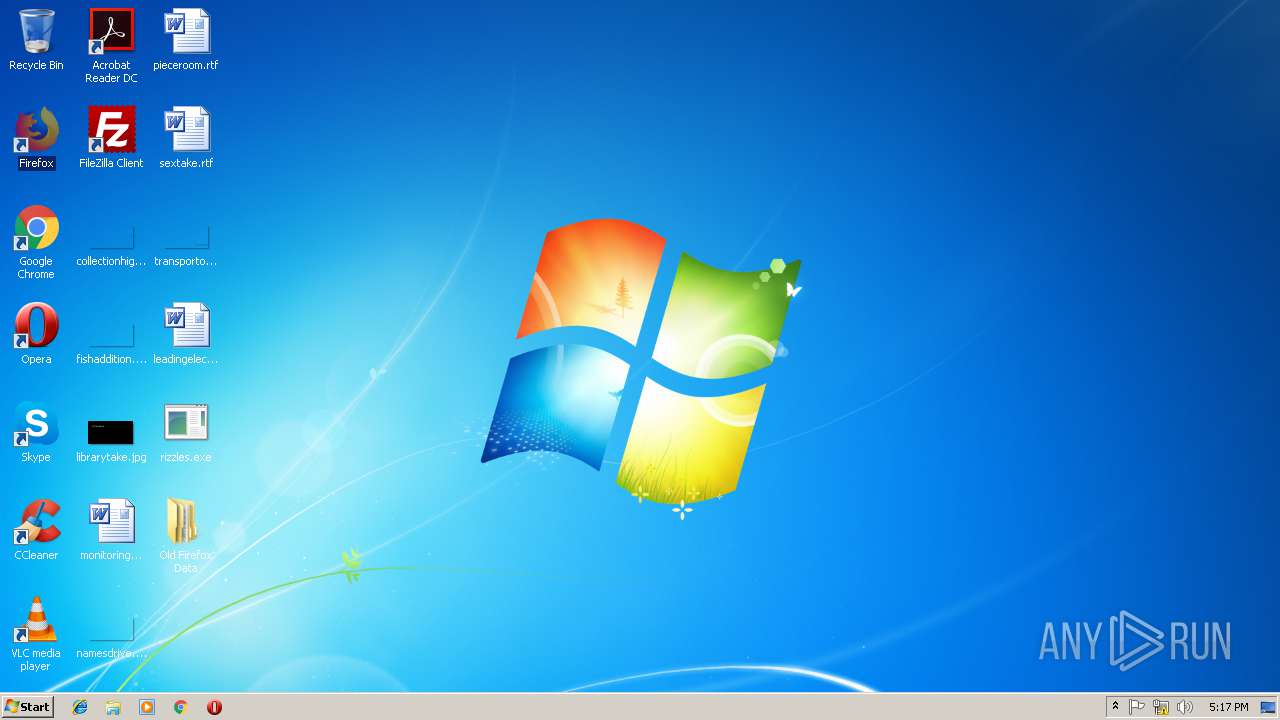
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2BA8F16EB5EE42D2AD01AD78731435CD |
| SHA1: | 48E32005DBB9B17926A3803F5ED930B0E736D565 |
| SHA256: | 54FF13D508071D9363F9A4FE83B34D5C001037C172DDB3C0BEE0A2BE05A5A0E5 |
| SSDEEP: | 12288:x82tivJVKYa6KMpVNOu7QFbLnACr0xerW57ldaqqge6WqVf:2oivjKYa6p7Ou7QhnDrGgqVP |
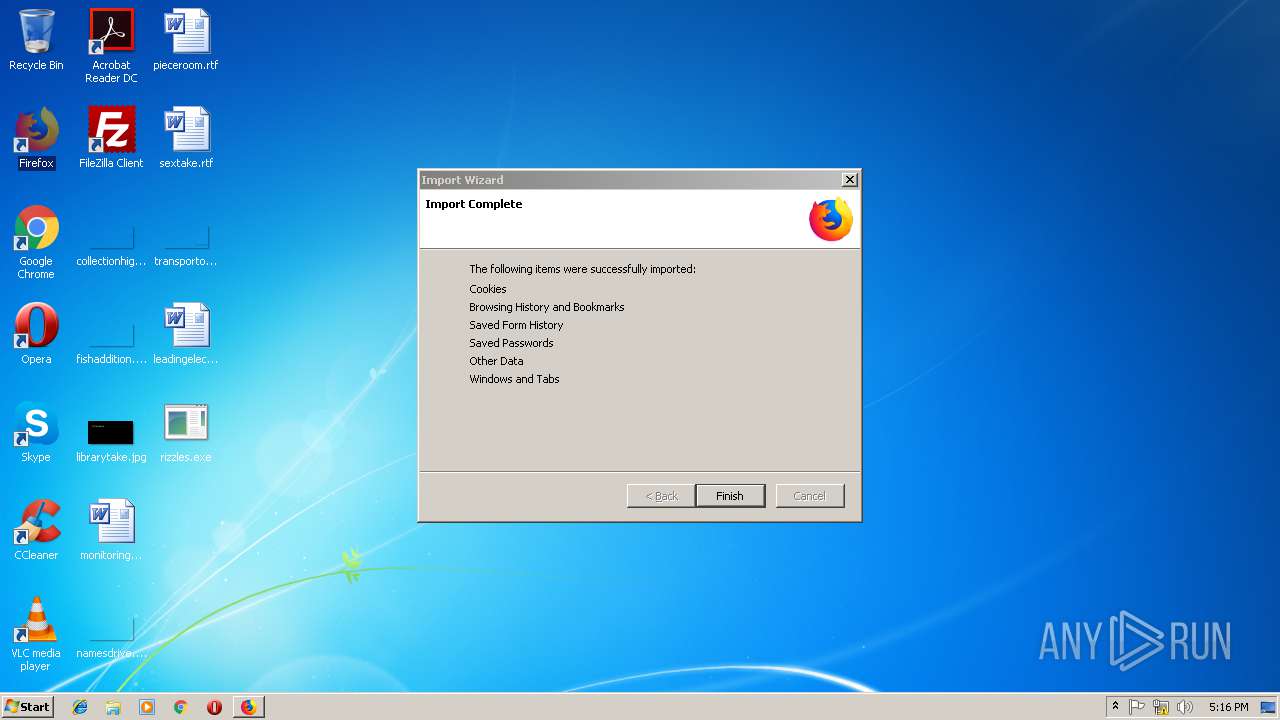
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2644)
SUSPICIOUS
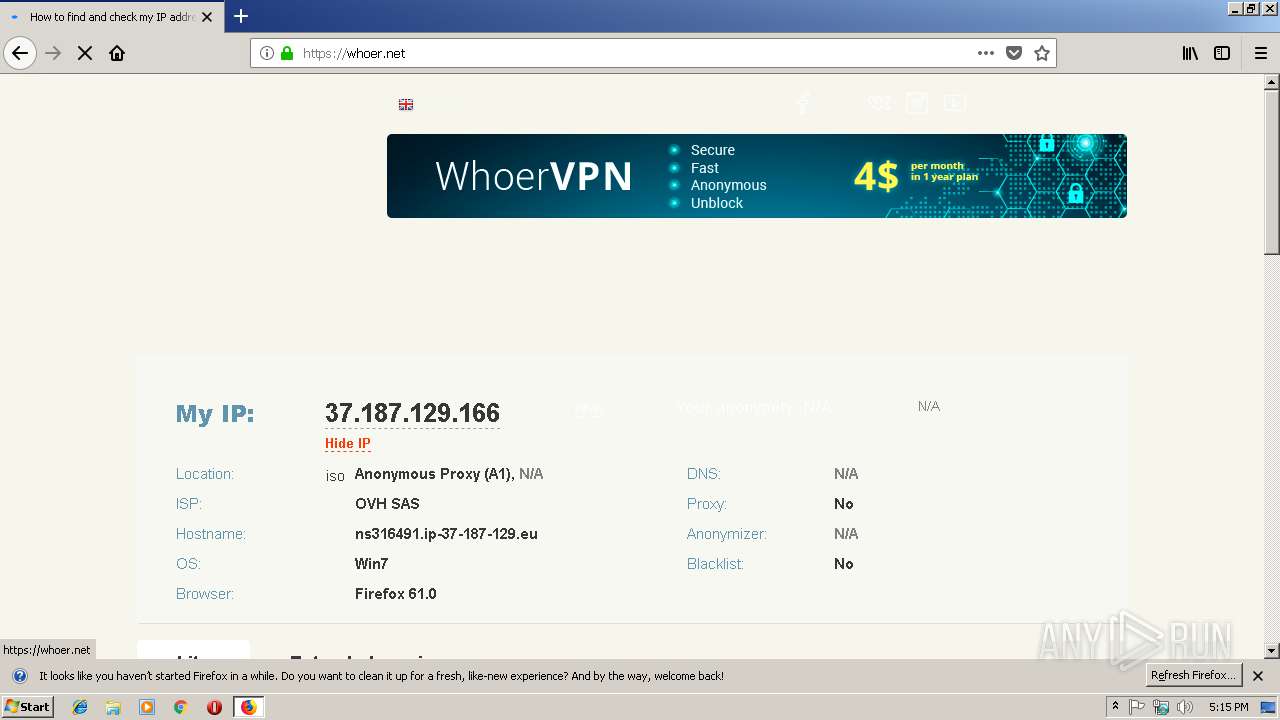
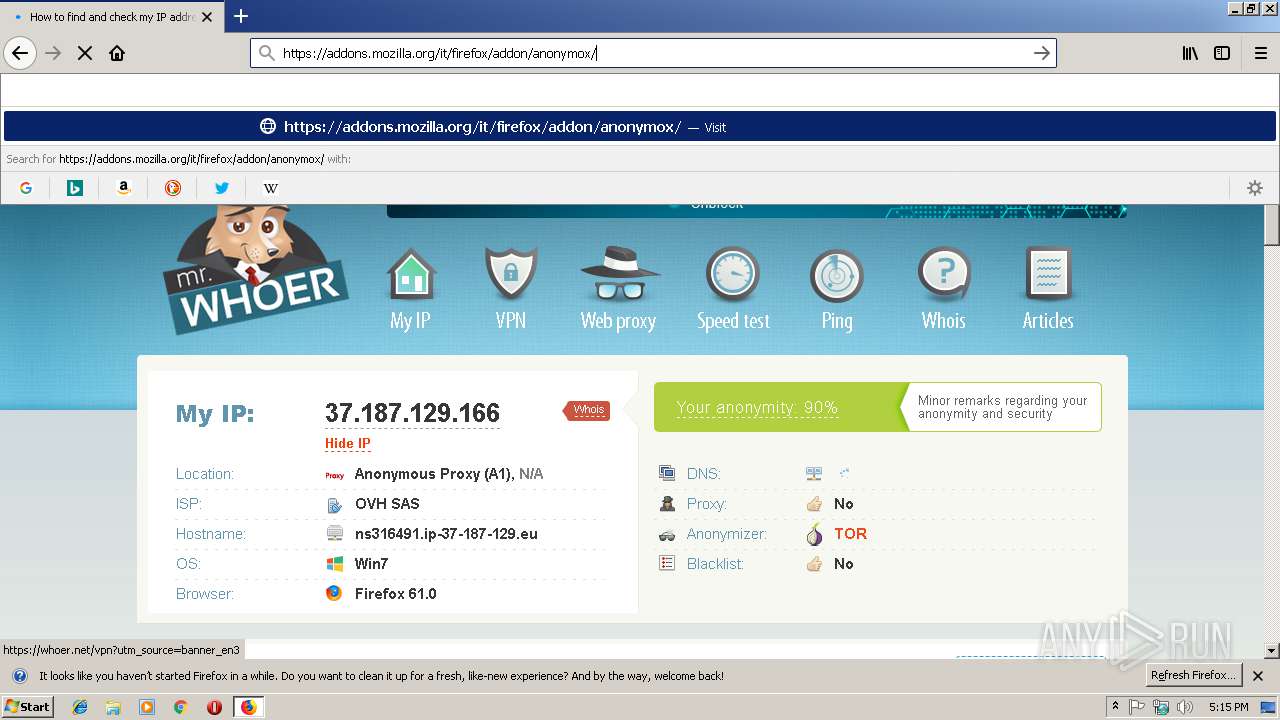
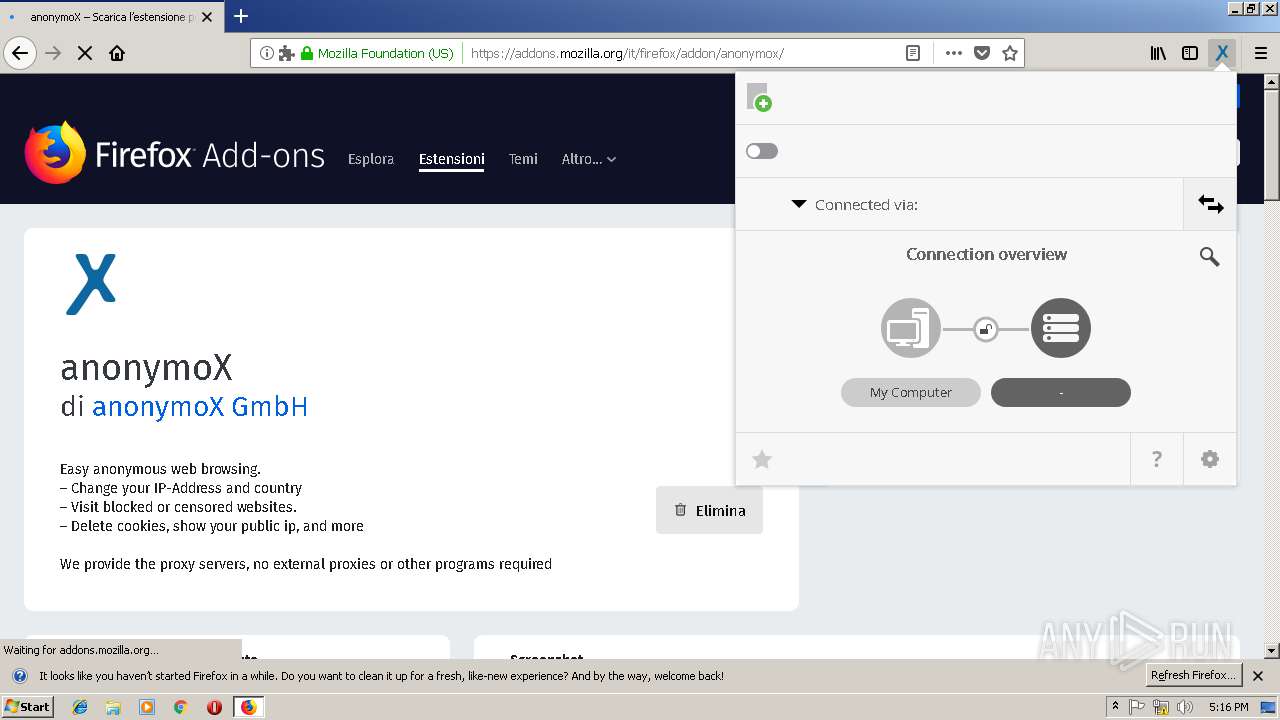
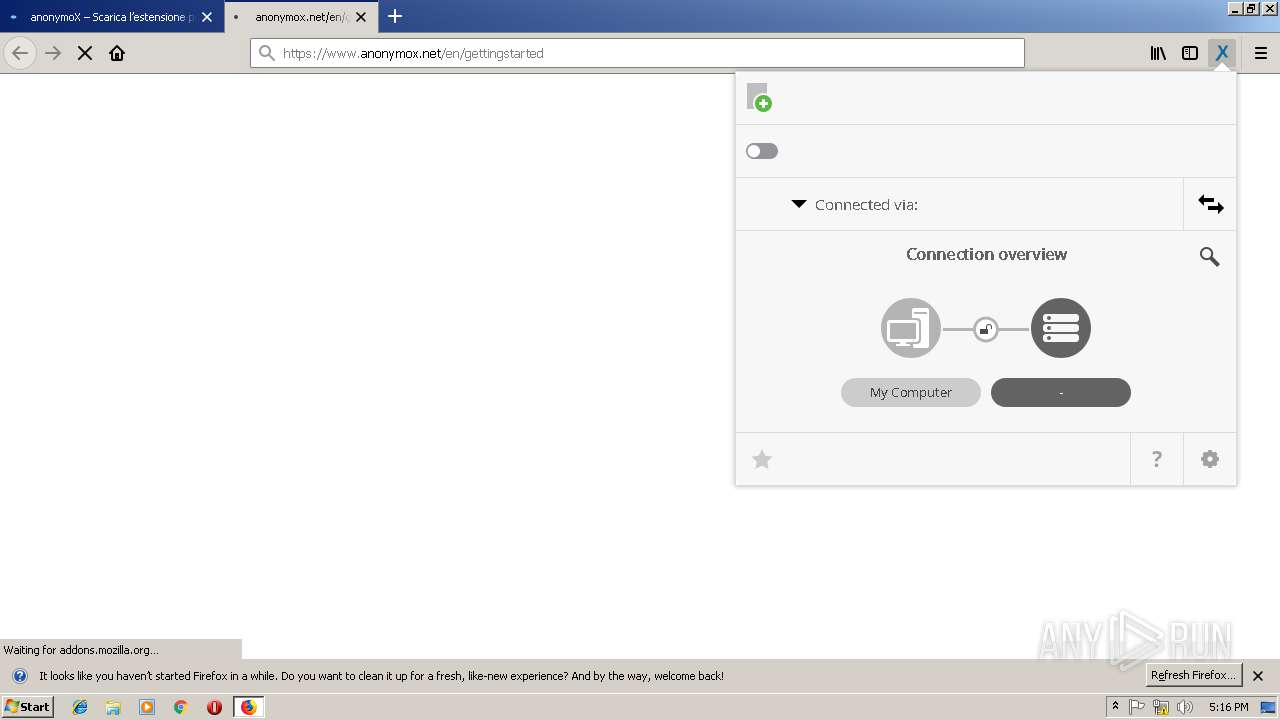
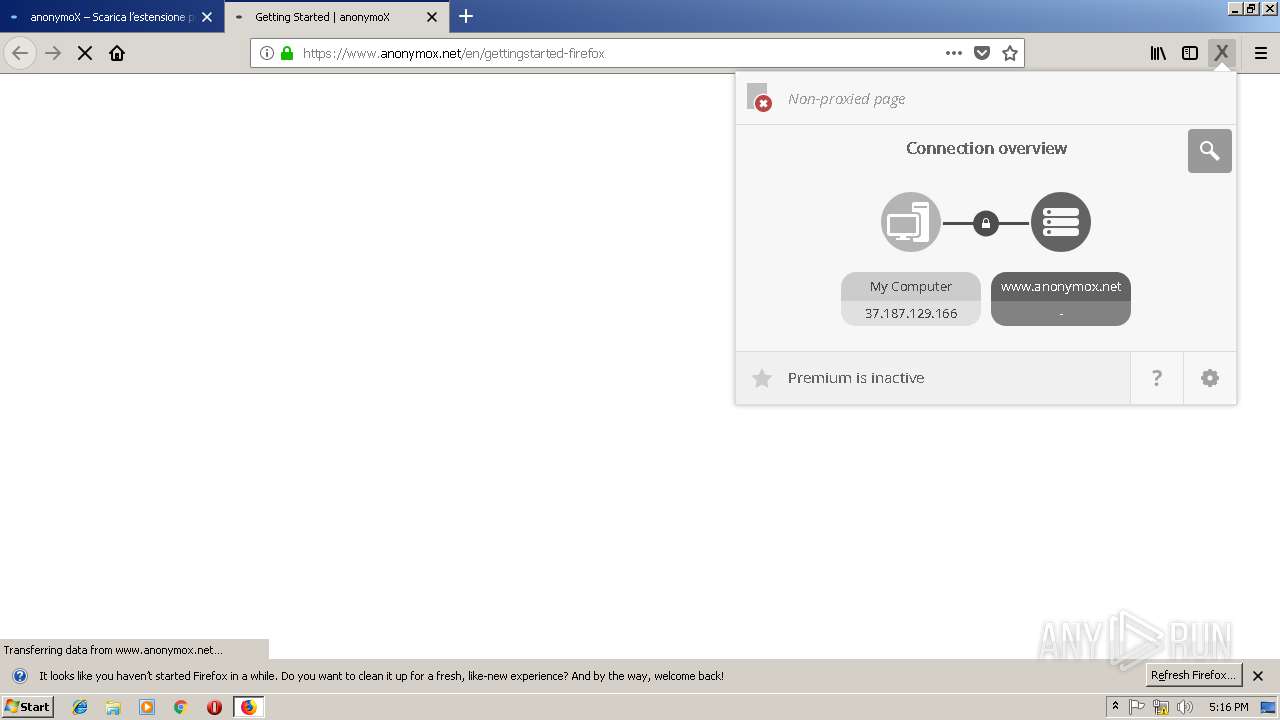
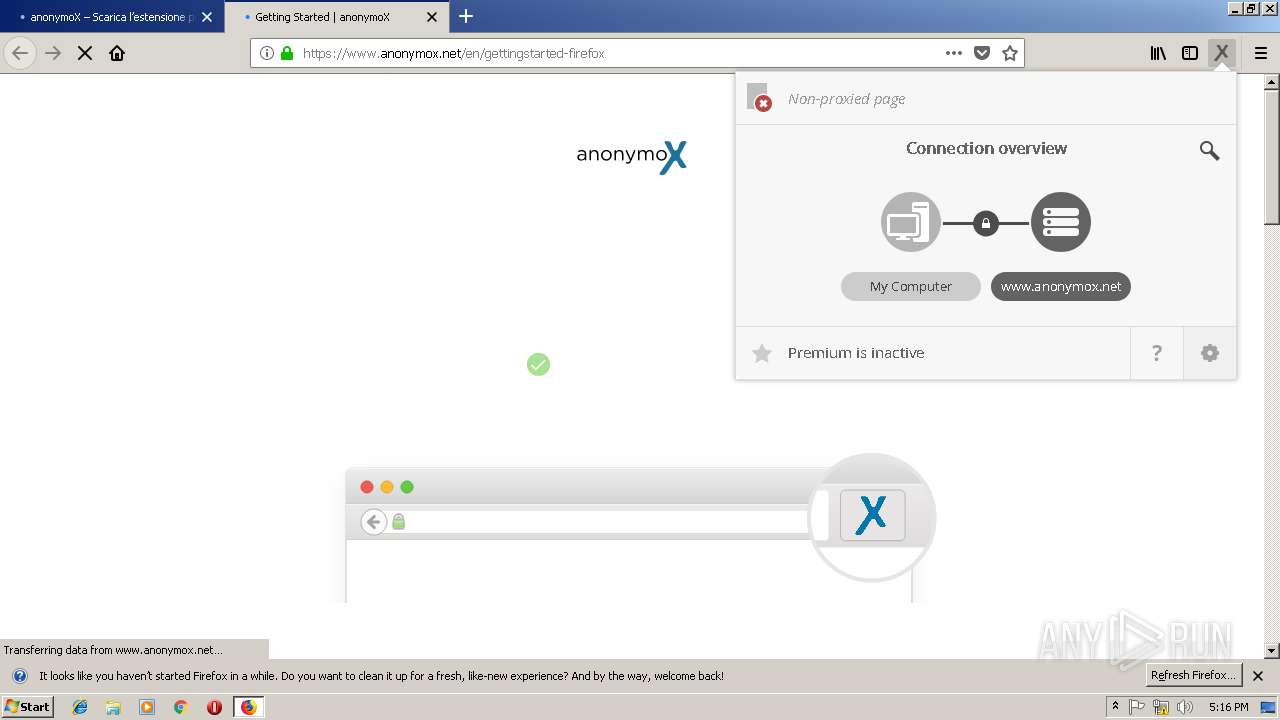
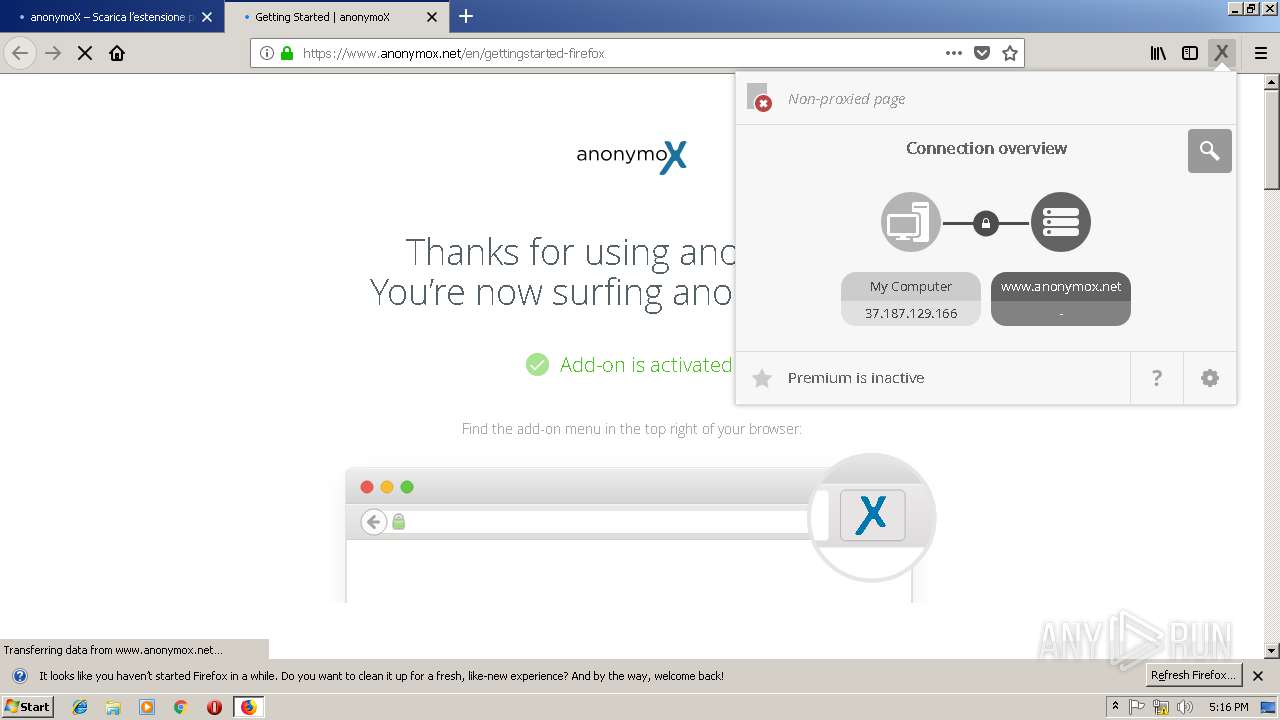
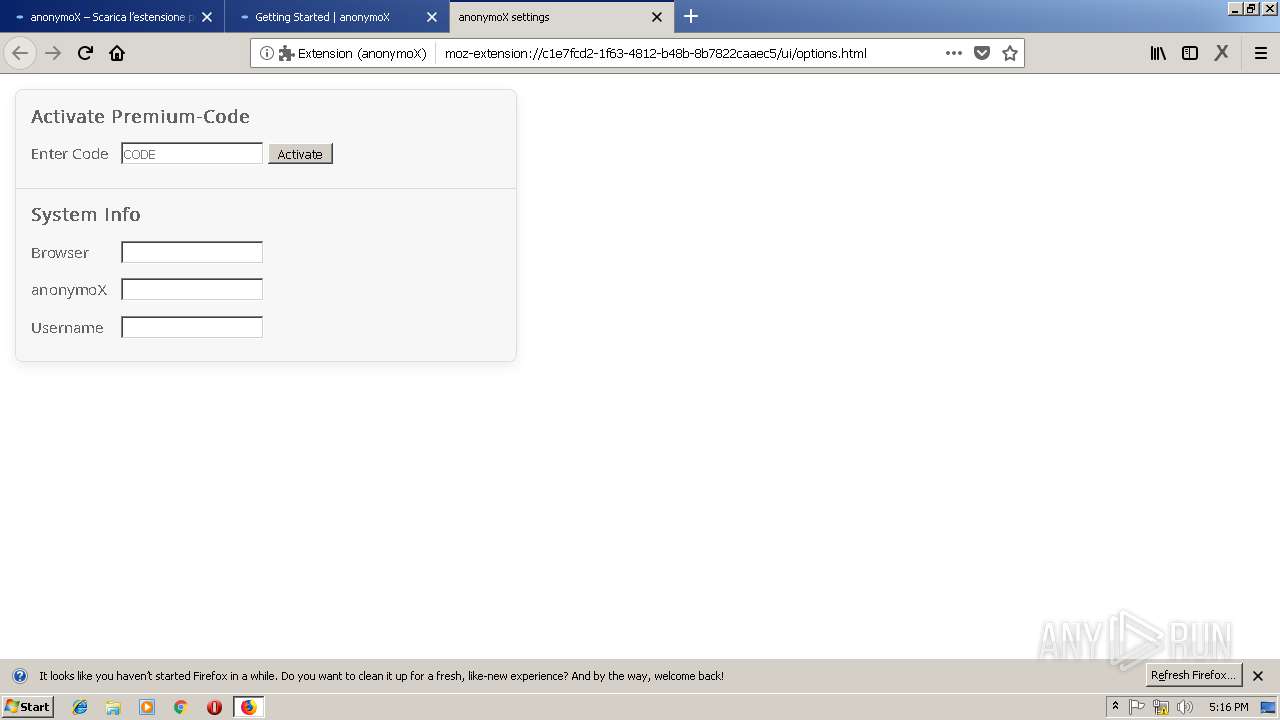
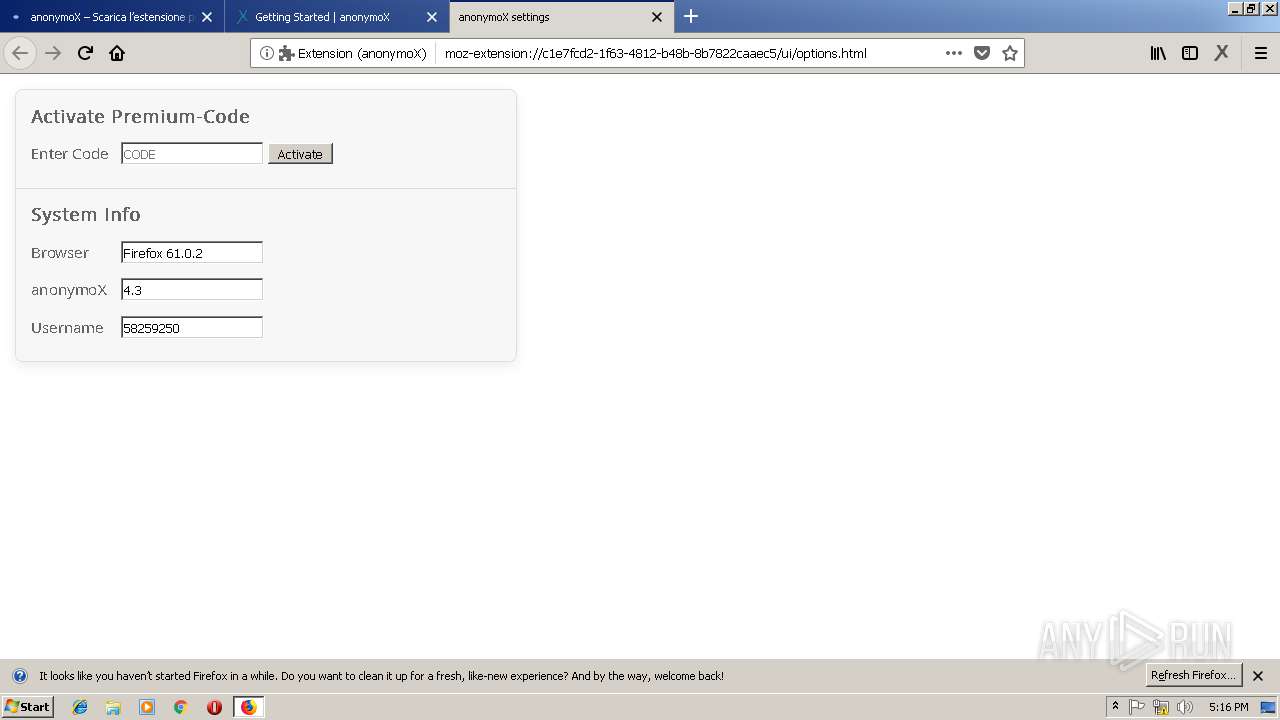
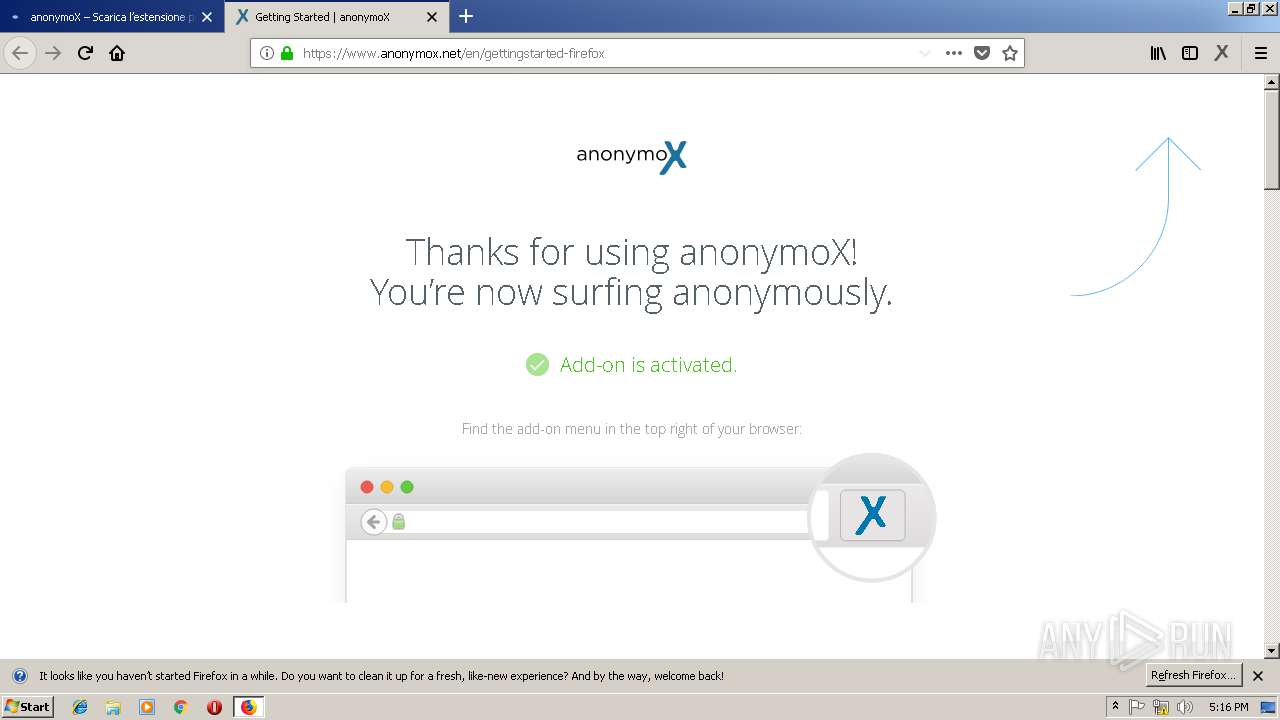
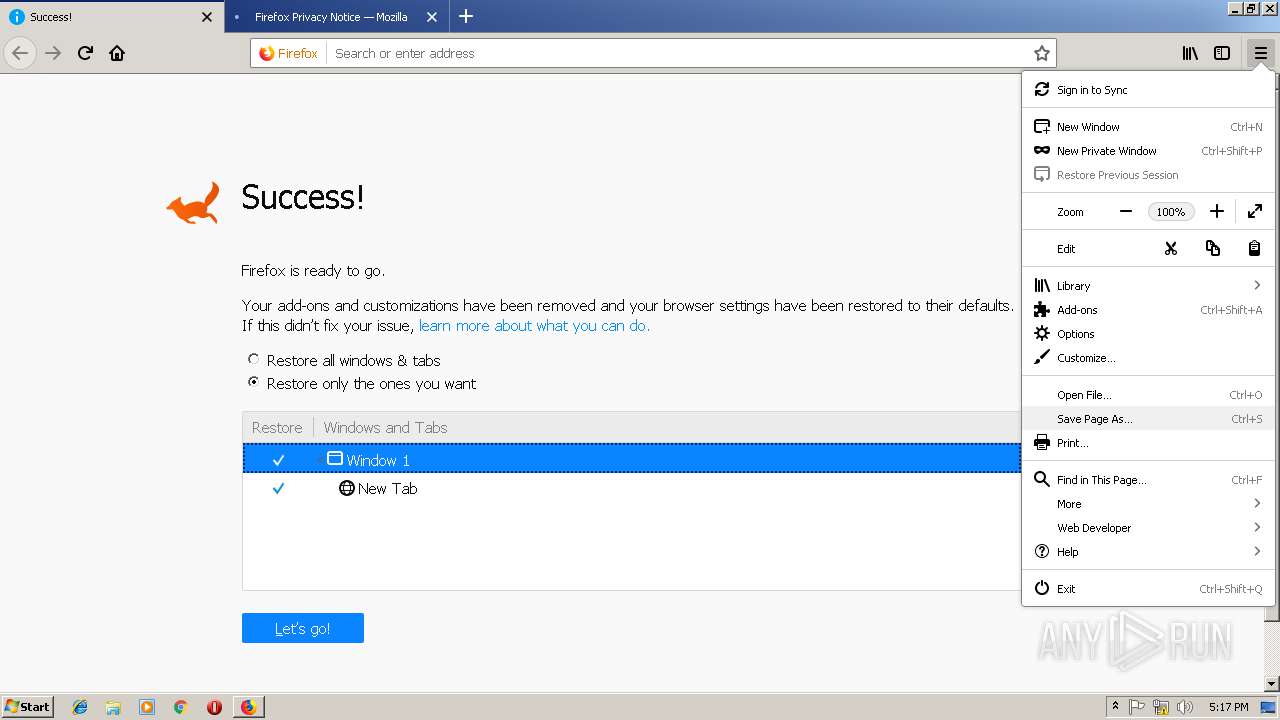
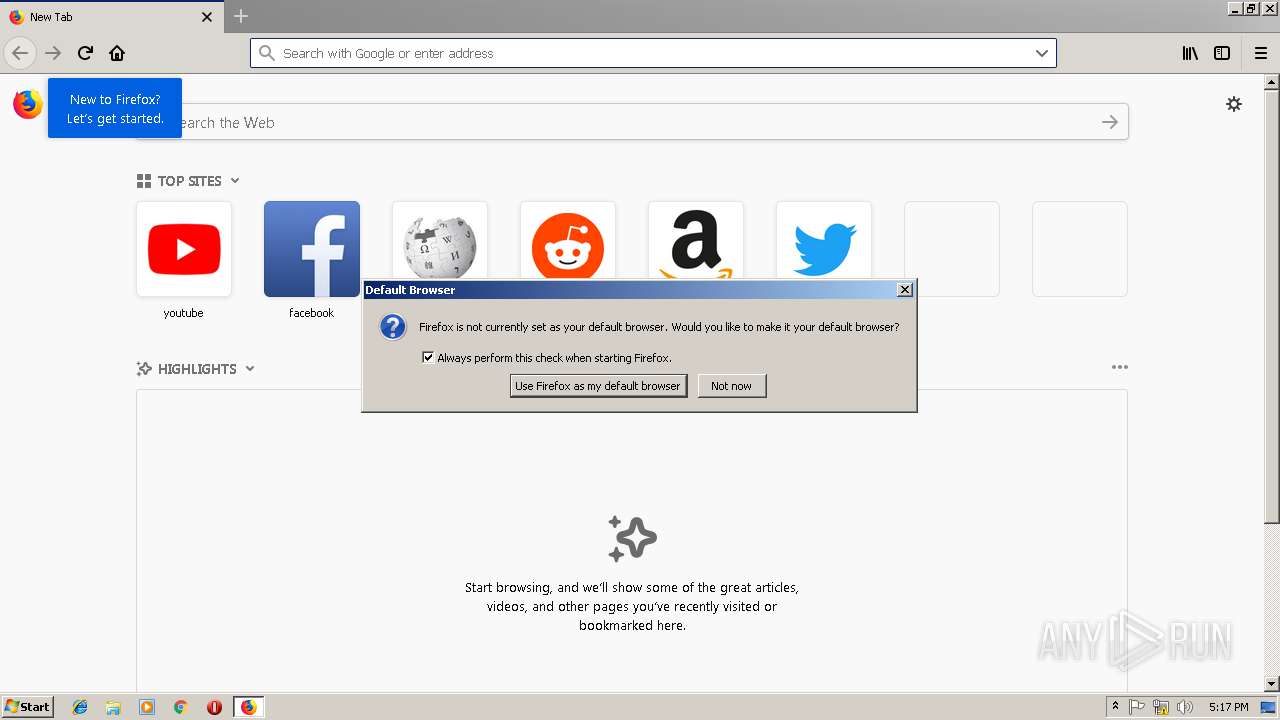
Checks for external IP
- firefox.exe (PID: 2932)
Executable content was dropped or overwritten
- firefox.exe (PID: 3044)
- firefox.exe (PID: 3920)
Loads DLL from Mozilla Firefox
- plugin-container.exe (PID: 3116)
Creates files in the user directory
- plugin-container.exe (PID: 3116)
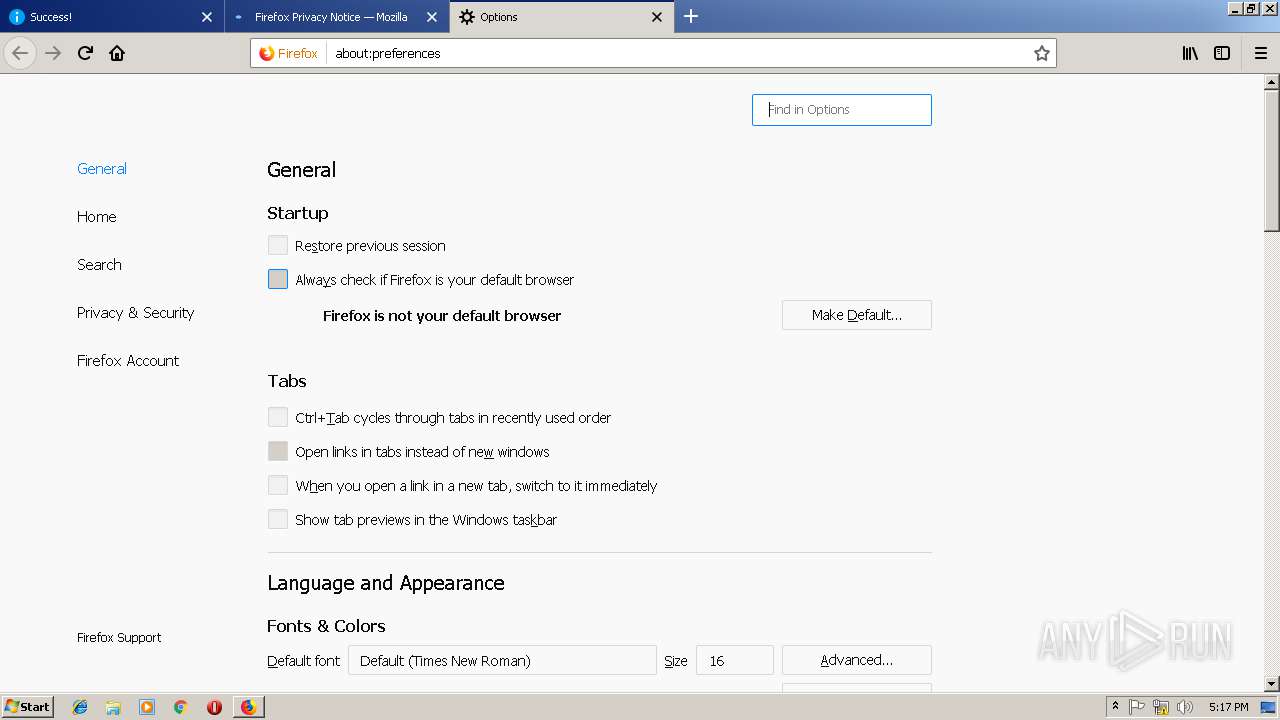
Modifies the open verb of a shell class
- helper.exe (PID: 1064)
INFO
Reads CPU info
- firefox.exe (PID: 3412)
- firefox.exe (PID: 2932)
- firefox.exe (PID: 3988)
- firefox.exe (PID: 3416)
- firefox.exe (PID: 2172)
- firefox.exe (PID: 3044)
- firefox.exe (PID: 2364)
- firefox.exe (PID: 2900)
- firefox.exe (PID: 2352)
- firefox.exe (PID: 2488)
- firefox.exe (PID: 3784)
- firefox.exe (PID: 3500)
- firefox.exe (PID: 3428)
- firefox.exe (PID: 2176)
- firefox.exe (PID: 2756)
- firefox.exe (PID: 3272)
- firefox.exe (PID: 3920)
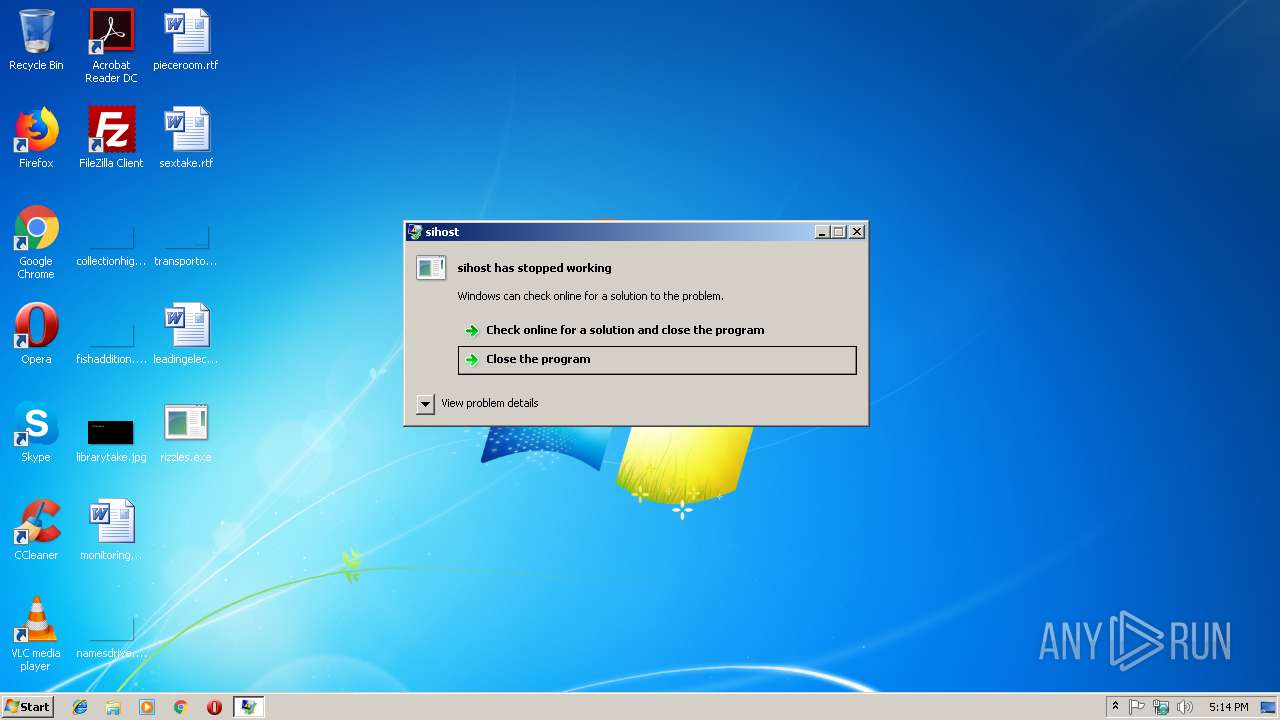
Application was crashed
- rizzles.exe (PID: 3156)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3044)
- firefox.exe (PID: 2932)
- firefox.exe (PID: 3920)
Application launched itself
- firefox.exe (PID: 2932)
- firefox.exe (PID: 3920)
- firefox.exe (PID: 3044)
Writes to a desktop.ini file (may be used to cloak folders)
- firefox.exe (PID: 3412)
Connects to unusual port
- firefox.exe (PID: 2932)
Creates files in the user directory
- firefox.exe (PID: 2932)
- firefox.exe (PID: 3044)
- firefox.exe (PID: 3920)
Dropped object may contain TOR URL's
- firefox.exe (PID: 3044)
- firefox.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:01 18:55:10+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 262656 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x413be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | sihost |
| FileVersion: | 1.0.0.0 |
| InternalName: | ovokado.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | ovokado.exe |
| ProductName: | sihost |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Mar-2018 17:55:10 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | sihost |
| FileVersion: | 1.0.0.0 |
| InternalName: | ovokado.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | ovokado.exe |
| ProductName: | sihost |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Mar-2018 17:55:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0004001C | 0x00040200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.23145 |
.rsrc | 0x00044000 | 0x0000059C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.0413 |
.reloc | 0x00046000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.9606 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
67
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Program Files\Mozilla Firefox\uninstall\helper.exe" /SetAsDefaultAppUser | C:\Program Files\Mozilla Firefox\uninstall\helper.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Helper Exit code: 2 Version: 61.0.2 Modules
| |||||||||||||||
| 2168 | "C:\Windows\system32\Macromed\Flash\FlashPlayerPlugin_26_0_0_131.exe" --proxy-stub-channel=Flash3116.64D50D30.12631 --host-broker-channel=Flash3116.64D50D30.3737 --host-pid=3116 --host-npapi-version=29 --plugin-path="C:\Windows\system32\Macromed\Flash\NPSWF32_26_0_0_131.dll" | C:\Windows\system32\Macromed\Flash\FlashPlayerPlugin_26_0_0_131.exe | — | plugin-container.exe | |||||||||||
User: admin Company: Adobe Systems, Inc. Integrity Level: MEDIUM Description: Adobe Flash Player 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2932.6.803141934\734297279" -childID 2 -isForBrowser -prefsHandle 2316 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2932 "\\.\pipe\gecko-crash-server-pipe.2932" 2324 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3044.30.1263232536\400749902" -childID 6 -isForBrowser -prefsHandle 2712 -prefsLen 8332 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3044 "\\.\pipe\gecko-crash-server-pipe.3044" 3652 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/362beb94-3c59-47c4-b441-dbe8fc482328/health/Firefox/61.0.2/release/20180807170231?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\g8kxoufv.default-1549473414296\saved-telemetry-pings\362beb94-3c59-47c4-b441-dbe8fc482328 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/31c0e33b-ec81-44d6-bd70-f269ae7afdcb/update/Firefox/61.0.2/release/20180807170231?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\g8kxoufv.default-1549473414296\saved-telemetry-pings\31c0e33b-ec81-44d6-bd70-f269ae7afdcb | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/66788f10-cc9b-45e8-9e14-9b438d9c9cf0/main/Firefox/61.0.2/release/20180807170231?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\66788f10-cc9b-45e8-9e14-9b438d9c9cf0 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 1 Version: 61.0.2 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3044.12.499494771\969495671" -childID 3 -isForBrowser -prefsHandle 2040 -prefsLen 2403 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3044 "\\.\pipe\gecko-crash-server-pipe.3044" 2060 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3044.0.236589936\944561290" -childID 1 -isForBrowser -prefsHandle 1836 -prefsLen 2358 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3044 "\\.\pipe\gecko-crash-server-pipe.3044" 1896 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3044.24.430114793\543484756" -childID 5 -isForBrowser -prefsHandle 3292 -prefsLen 8332 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3044 "\\.\pipe\gecko-crash-server-pipe.3044" 3336 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
3 737
Read events
3 622
Write events
115
Delete events
0
Modification events
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2336) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2336) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006A000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2336) pingsender.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3044) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3044) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2644) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2644) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (2644) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
Executable files
4
Suspicious files
461
Text files
244
Unknown types
290
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flash-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\block-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
154
DNS requests
279
Threats
74
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2932 | firefox.exe | POST | — | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | — | — | whitelisted |
2932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2932 | firefox.exe | POST | 200 | 216.58.215.99:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
2932 | firefox.exe | POST | 200 | 2.21.89.18:80 | http://ocsp.comodoca.com/ | AT | der | 471 b | whitelisted |
2932 | firefox.exe | CONNECT | 407 | 207.244.89.75:80 | http://location.services.mozilla.com:443 | US | html | 3.19 Kb | unknown |
2932 | firefox.exe | GET | 200 | 104.25.39.26:80 | http://whoer.net/.well-known/http-opportunistic | US | text | 90 b | shared |
2932 | firefox.exe | GET | 200 | 92.123.102.154:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
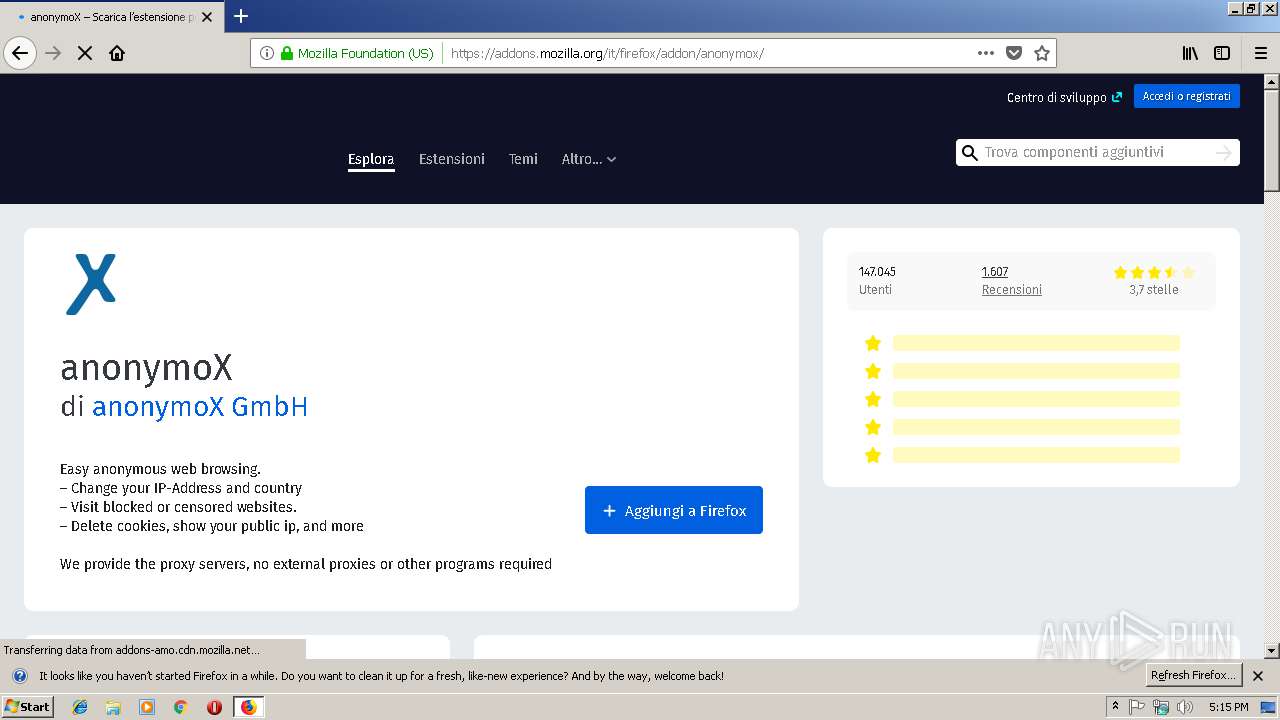
2932 | firefox.exe | GET | 200 | 207.244.89.75:80 | http://us15.sc.nwi.anonymox.net/selfcheck?gw=us15 | US | text | 2 b | unknown |
2932 | firefox.exe | GET | 200 | 95.211.211.182:80 | http://nl8c.sc.nwi.anonymox.net/selfcheck?gw=nl8c | NL | text | 2 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | firefox.exe | 52.89.32.107:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2932 | firefox.exe | 54.186.163.246:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2932 | firefox.exe | 104.25.39.26:80 | whoer.net | Cloudflare Inc | US | shared |
2932 | firefox.exe | 216.58.215.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2932 | firefox.exe | 92.123.102.154:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2932 | firefox.exe | 104.25.39.26:443 | whoer.net | Cloudflare Inc | US | shared |
2932 | firefox.exe | 172.217.20.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2932 | firefox.exe | 193.108.117.116:443 | tcp.whoer.net | GlobalTeleHost Corp. | DE | suspicious |
2932 | firefox.exe | 172.217.20.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.youtube.com |
| whitelisted |
www.amazon.de |
| whitelisted |
www.facebook.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
whoer.net |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid handshake message |
2932 | firefox.exe | Generic Protocol Command Decode | SURICATA TLS invalid record/traffic |