| URL: | http://evassmat.com/1990418/tenchu2 |
| Full analysis: | https://app.any.run/tasks/be179a9a-6d9d-45a9-9f9a-582dbdcbfc99 |
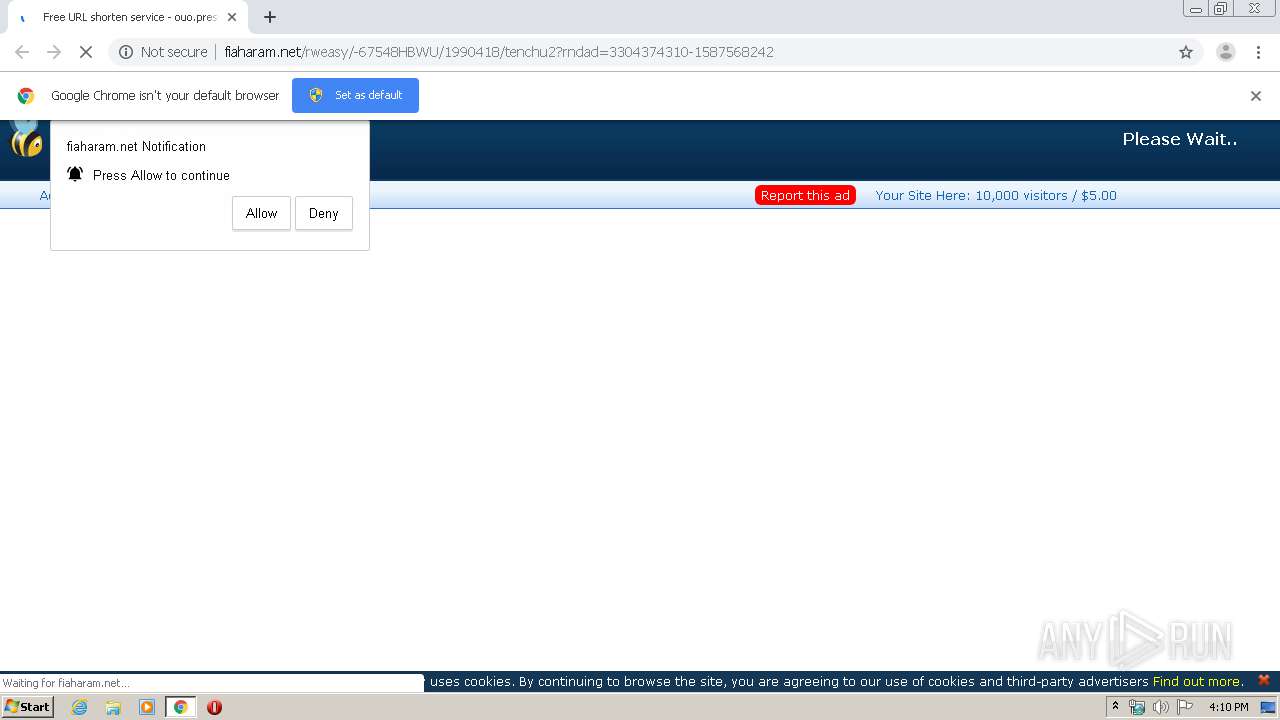
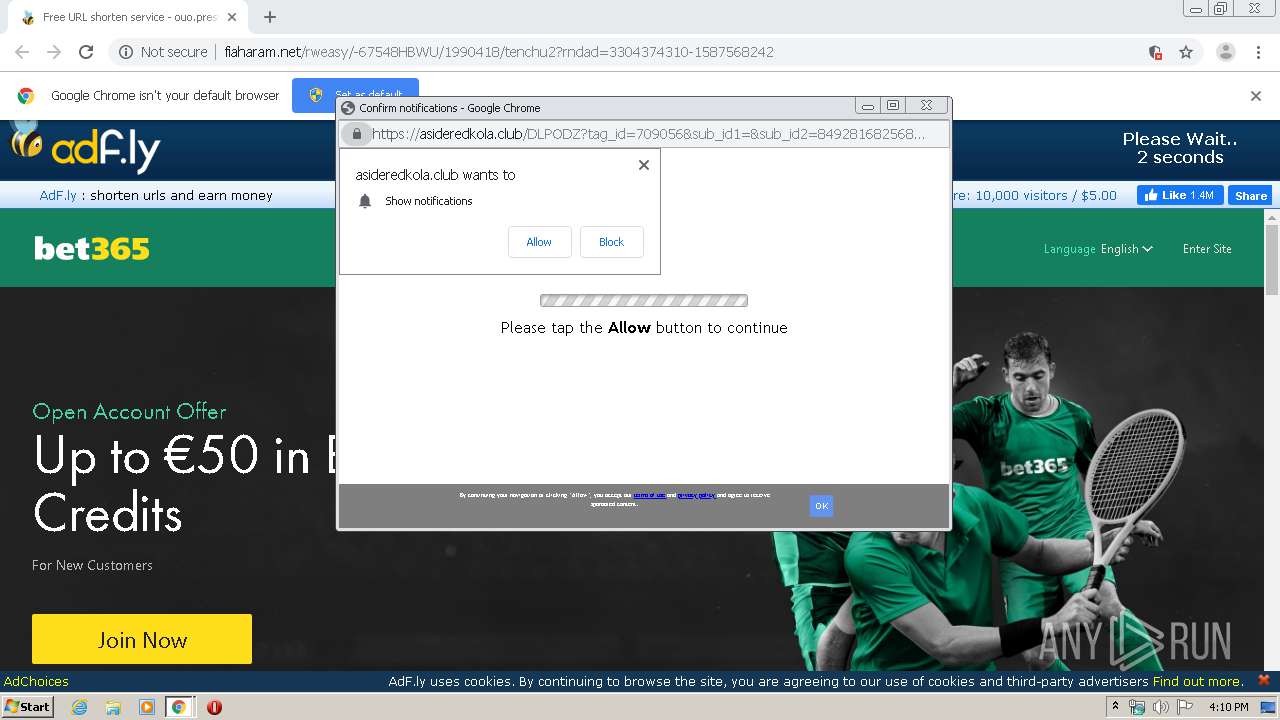
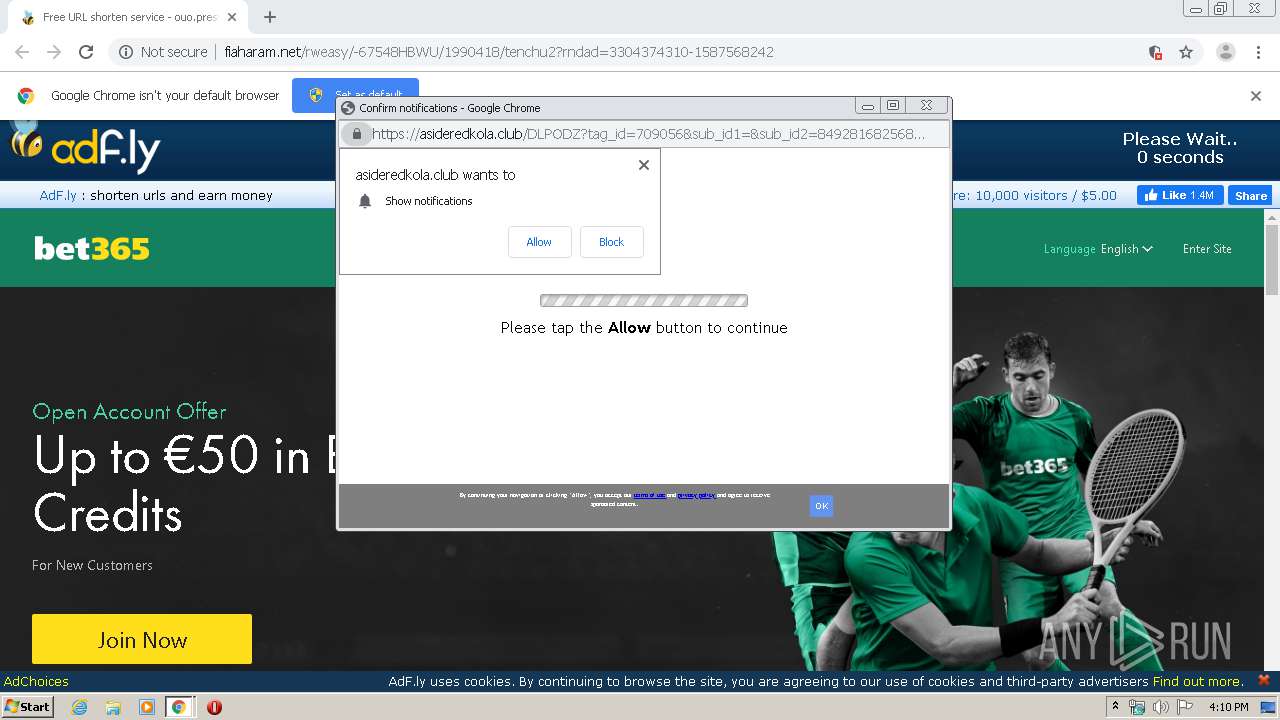
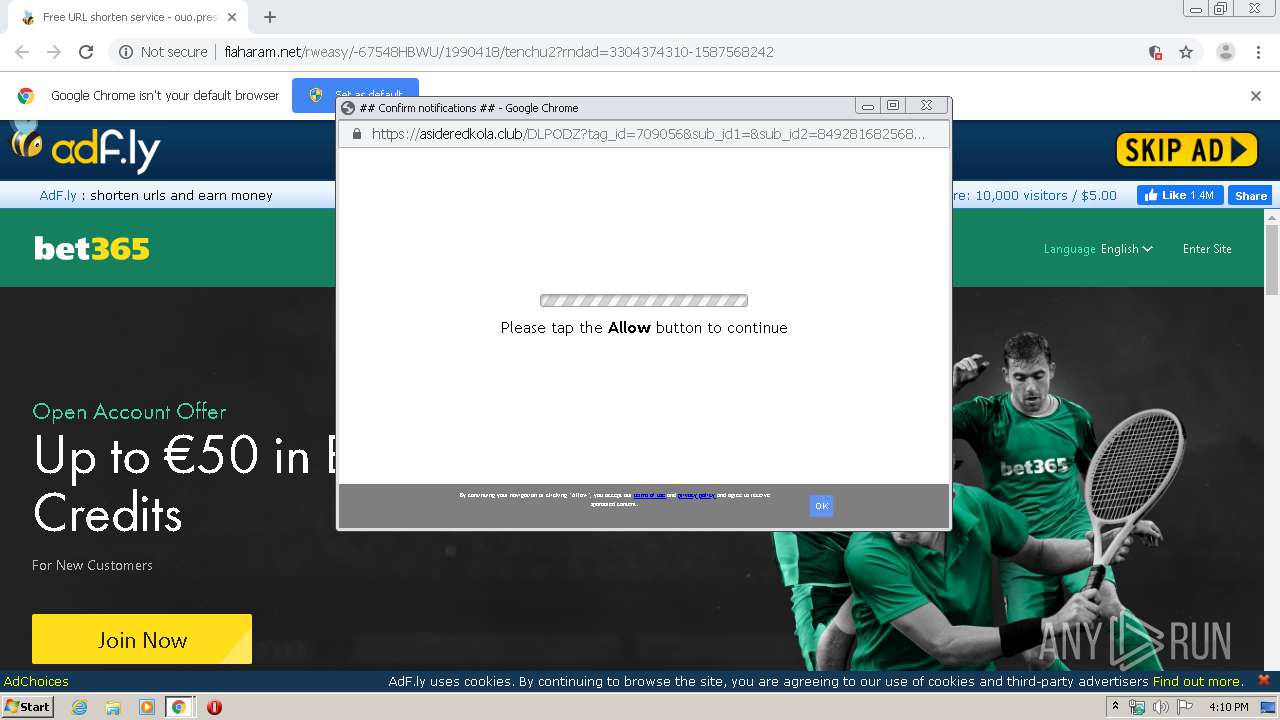
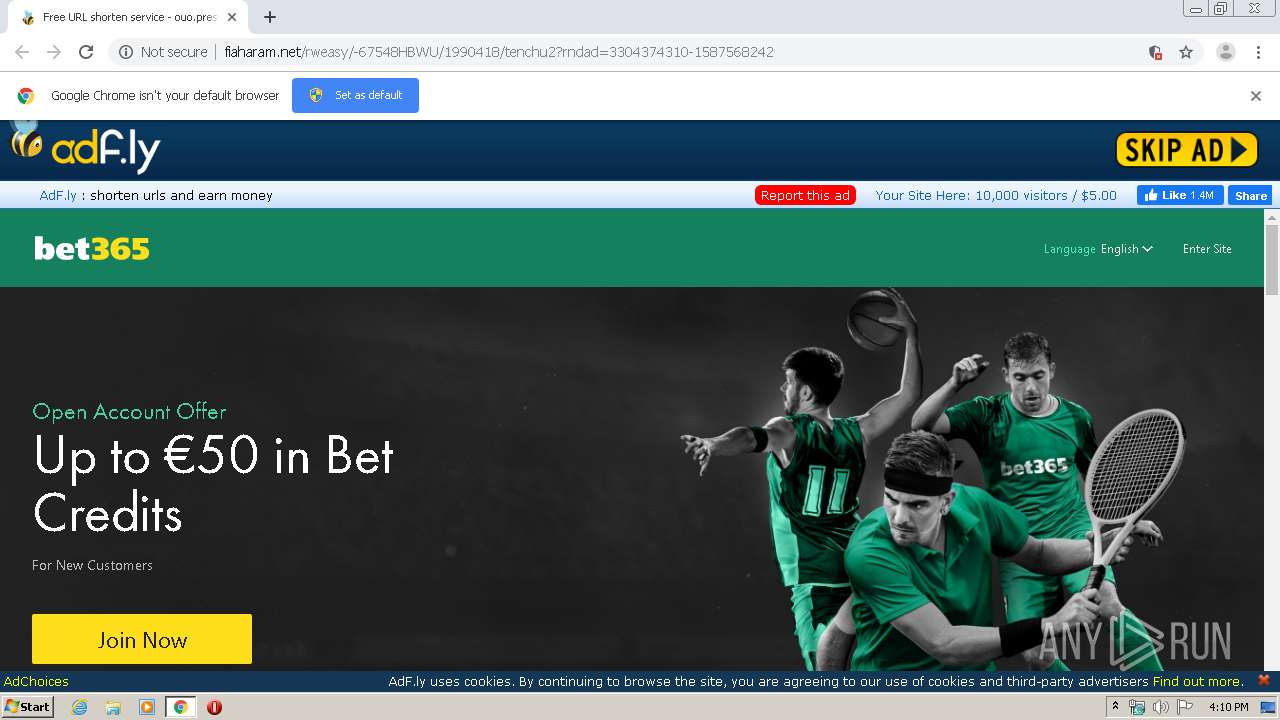
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2020, 15:10:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 450EC8D846D9DE5480F553C58D60F6C1 |
| SHA1: | 8C2D03A15CAF32D1288325BC8E99284708D1F654 |
| SHA256: | 54FC299A9431B1B9F7A15A8B71FE08BC3399E50DDD696AB05A9FA161E6A84D40 |
| SSDEEP: | 3:N1KbrAZIKUcctCn:C4ZIKUnCn |
MALICIOUS
No malicious indicators.SUSPICIOUS
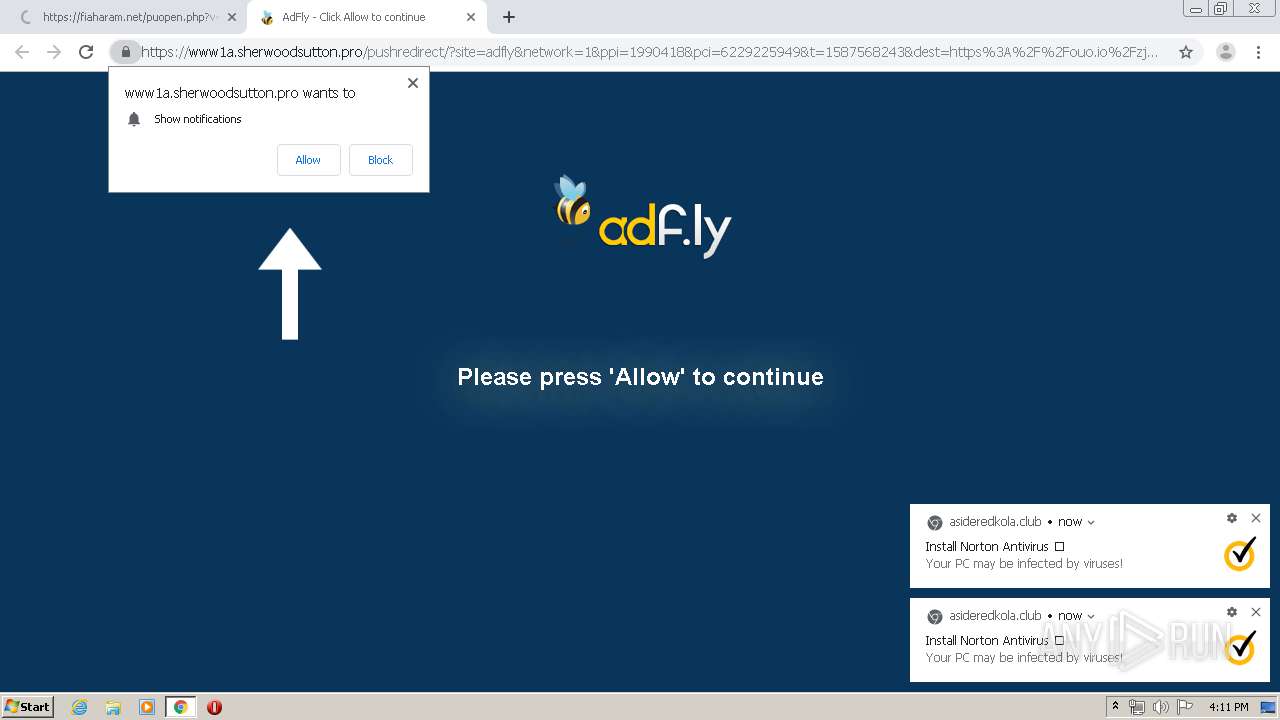
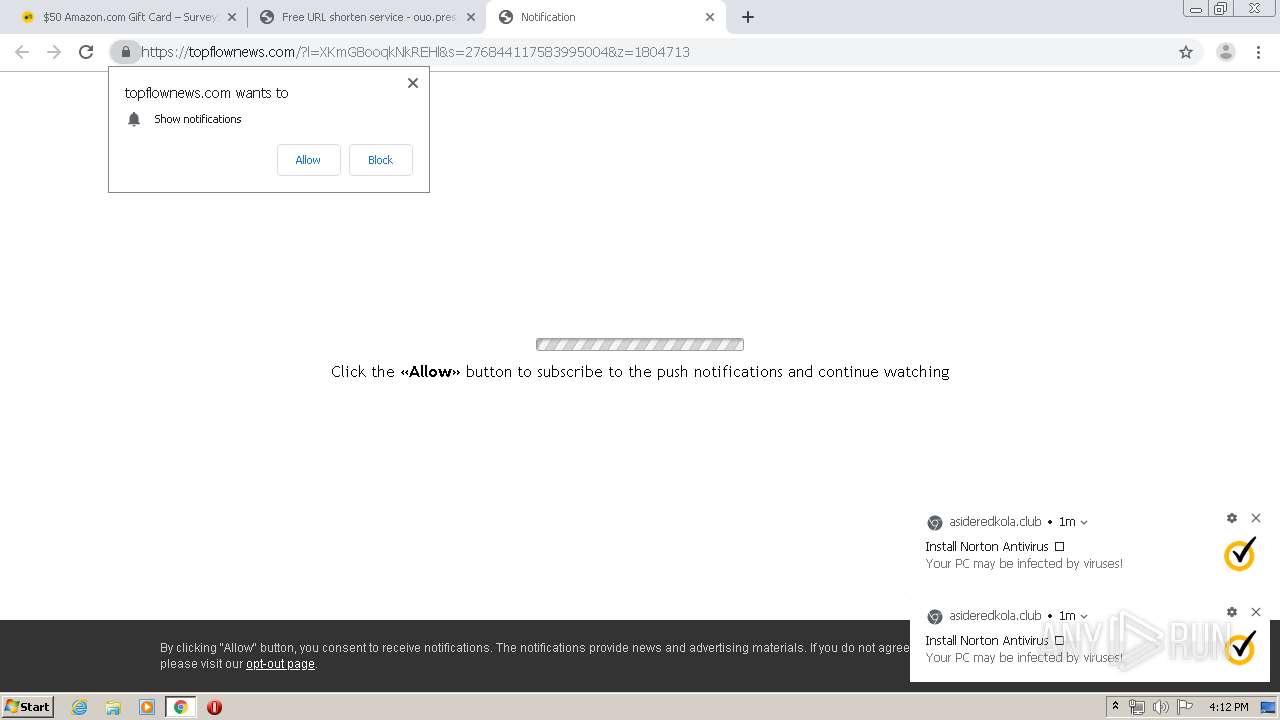
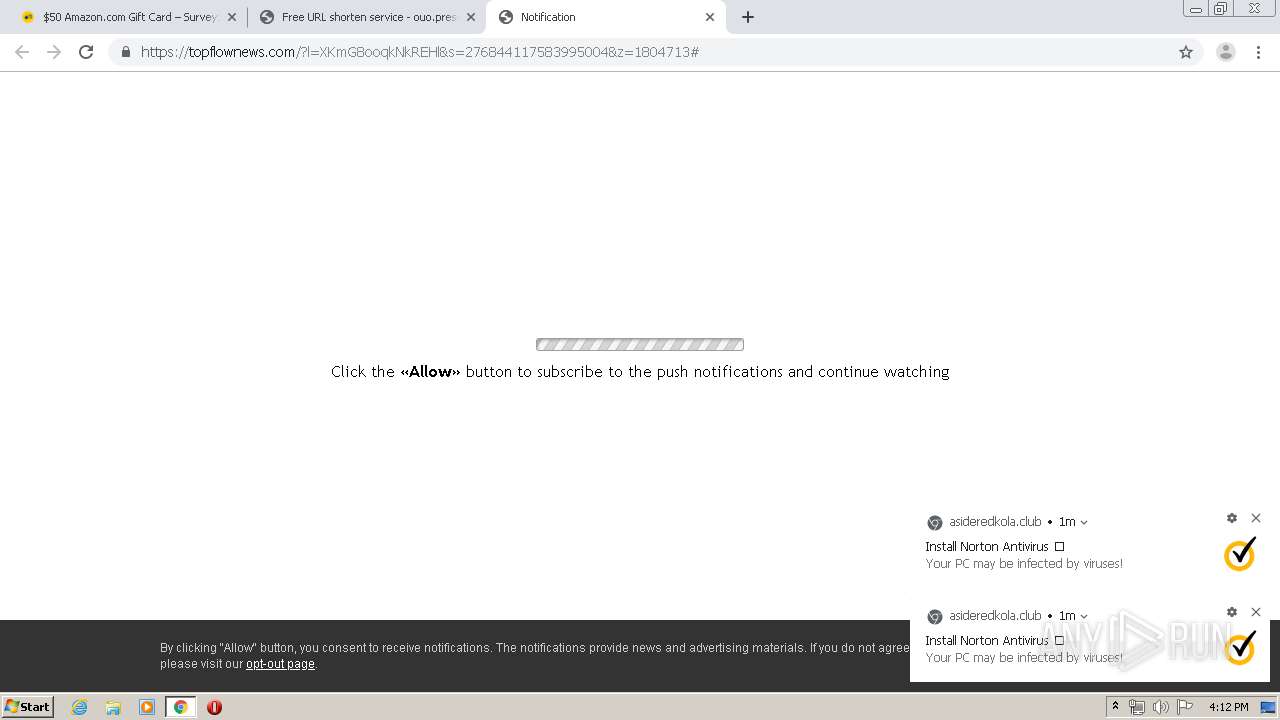
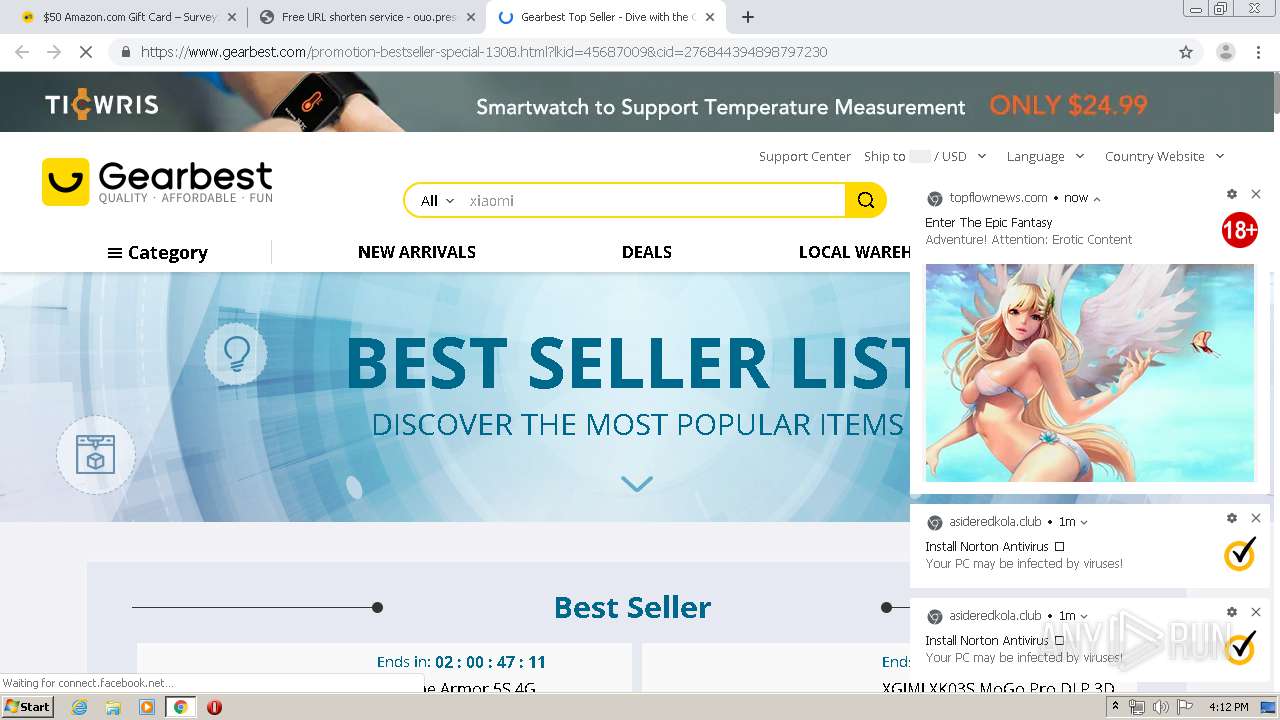
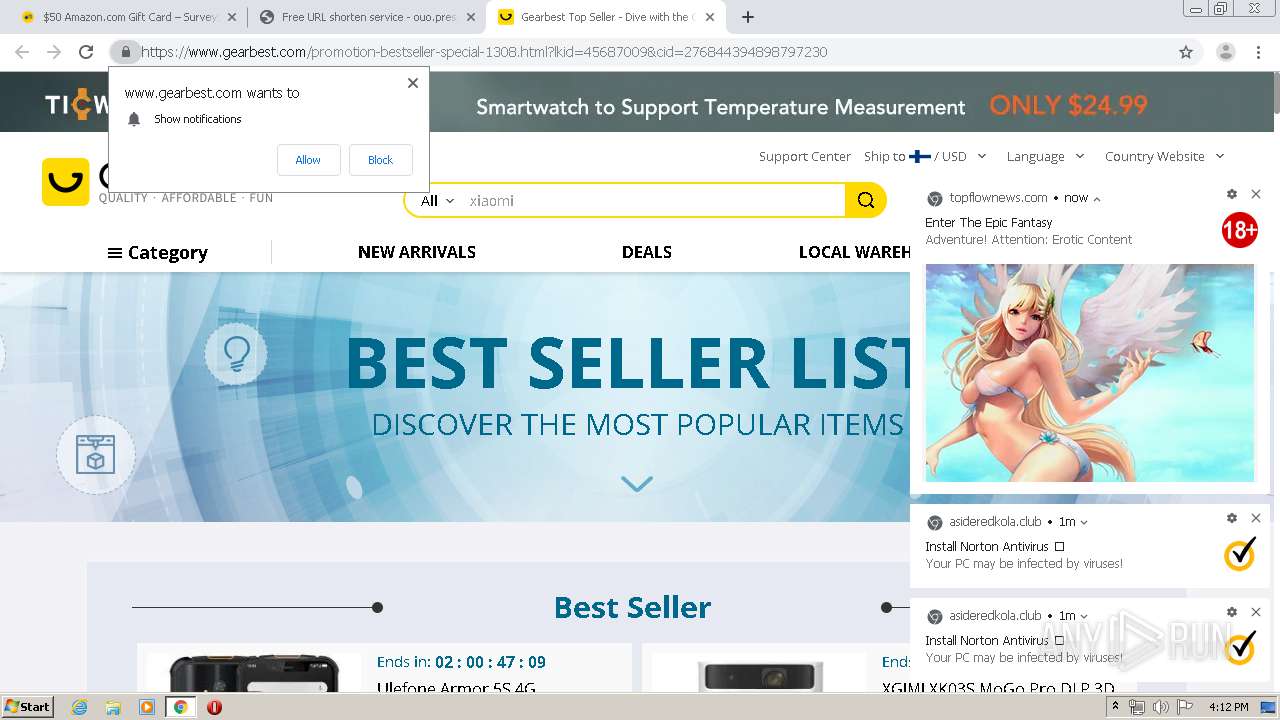
Modifies files in Chrome extension folder
- chrome.exe (PID: 3552)
INFO
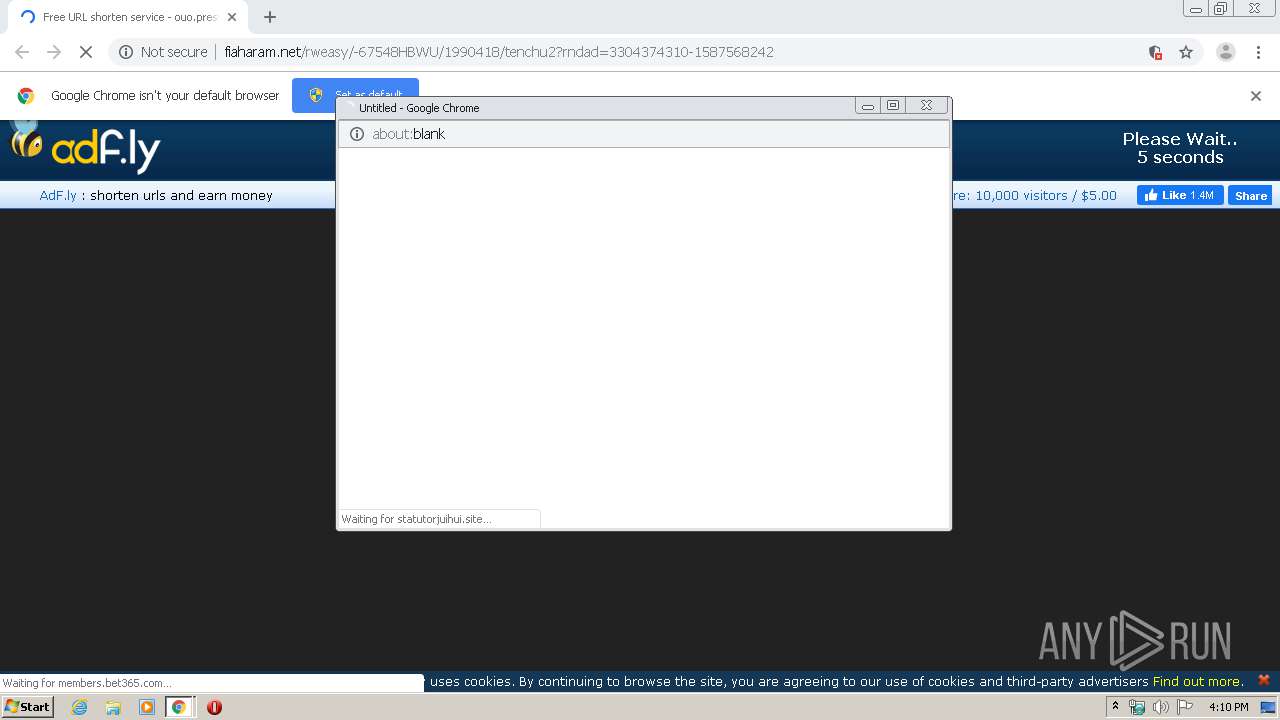
Connects to unusual port
- chrome.exe (PID: 2904)
Reads the hosts file
- chrome.exe (PID: 3552)
- chrome.exe (PID: 2904)
Reads settings of System Certificates
- chrome.exe (PID: 2904)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3552)
Changes settings of System certificates
- chrome.exe (PID: 2904)
Application launched itself
- chrome.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
59
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1206442059759131039 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7758546128685012851 --mojo-platform-channel-handle=3824 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5877341035349737870 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11059271505285721706 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4921379644722664423 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13822749322120480478 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9004612450542969456 --mojo-platform-channel-handle=4620 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4557785521241890529 --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17822802842063200858 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11486703415723209360,221763569963495272,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6044551047244318167 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
933
Read events
813
Write events
115
Delete events
5
Modification events
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3552-13232041837706375 |
Value: 259 | |||
Executable files
0
Suspicious files
335
Text files
269
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EA05E6E-DE0.pma | — | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3a80bfed-02a2-45ac-9c8c-fe1bd30c9d02.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa6e288.TMP | text | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e20b.TMP | text | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e3b1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
243
DNS requests
143
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
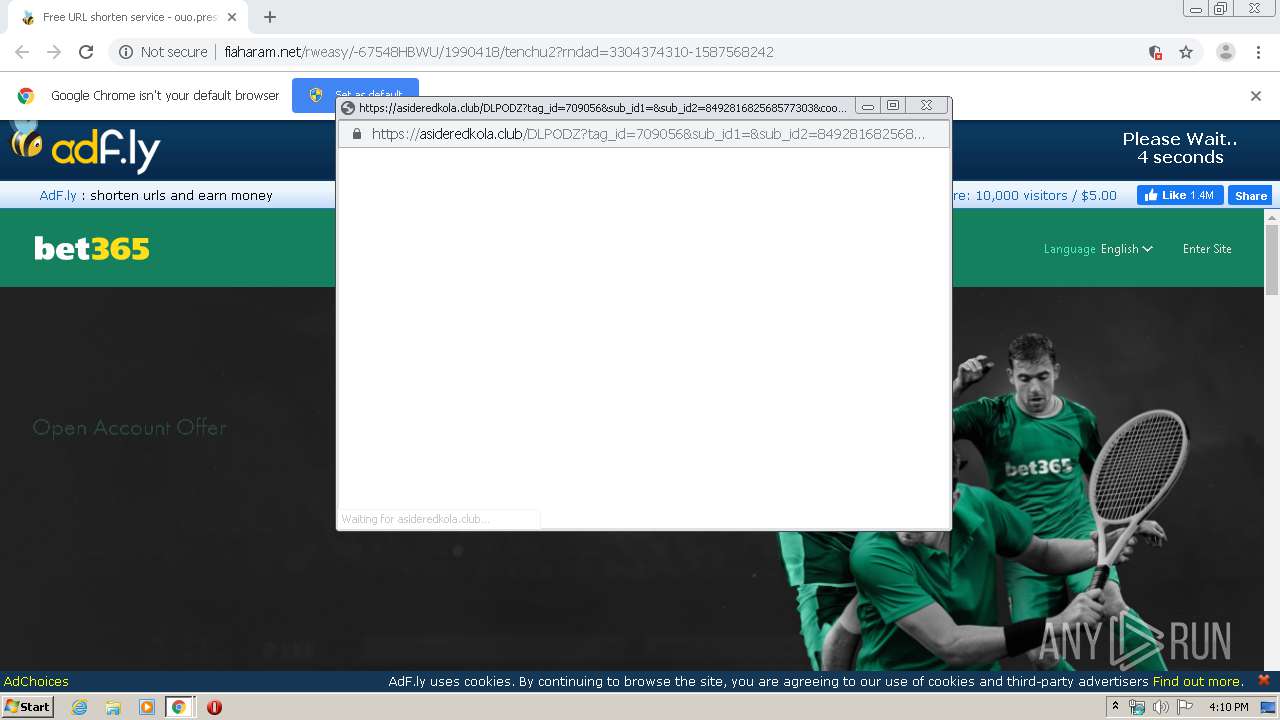
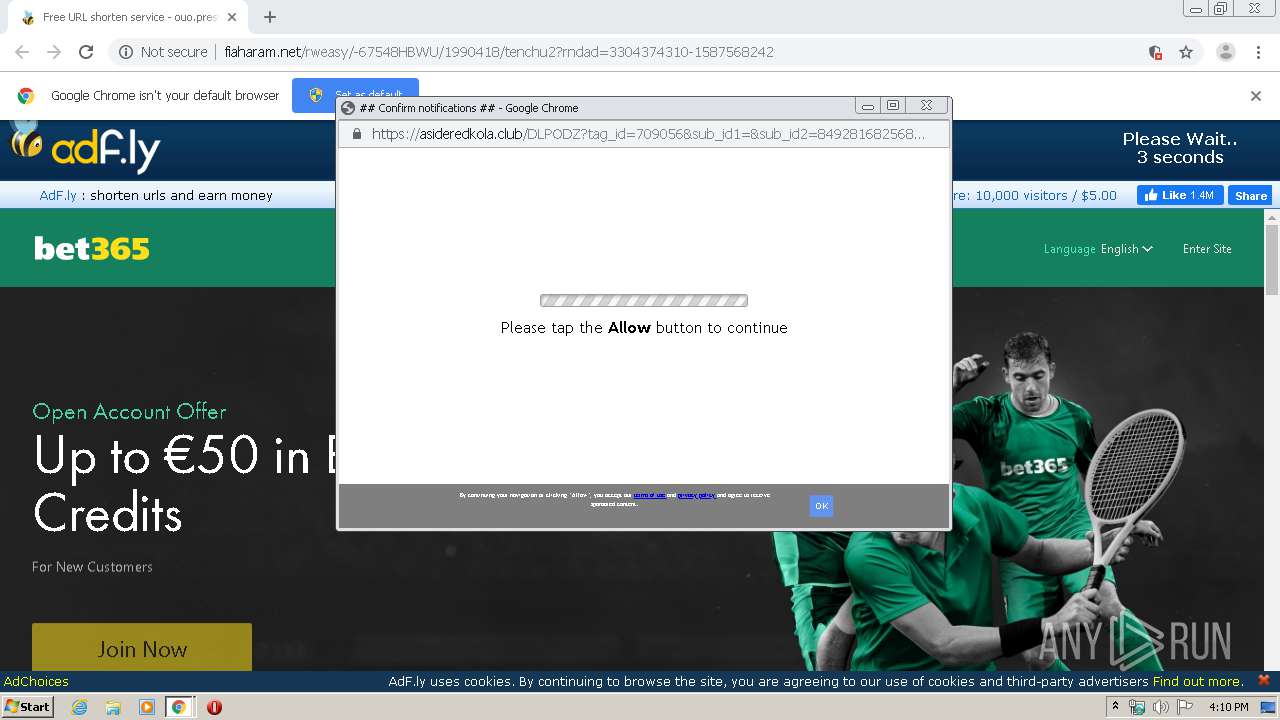
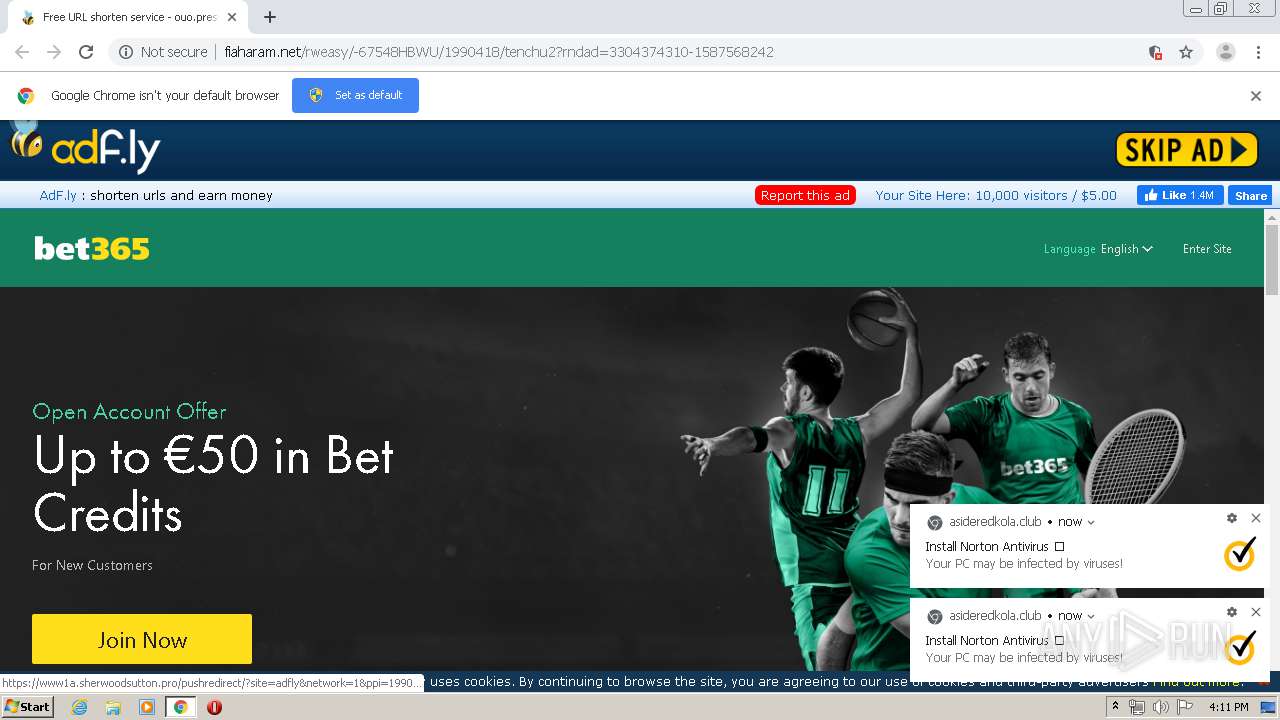
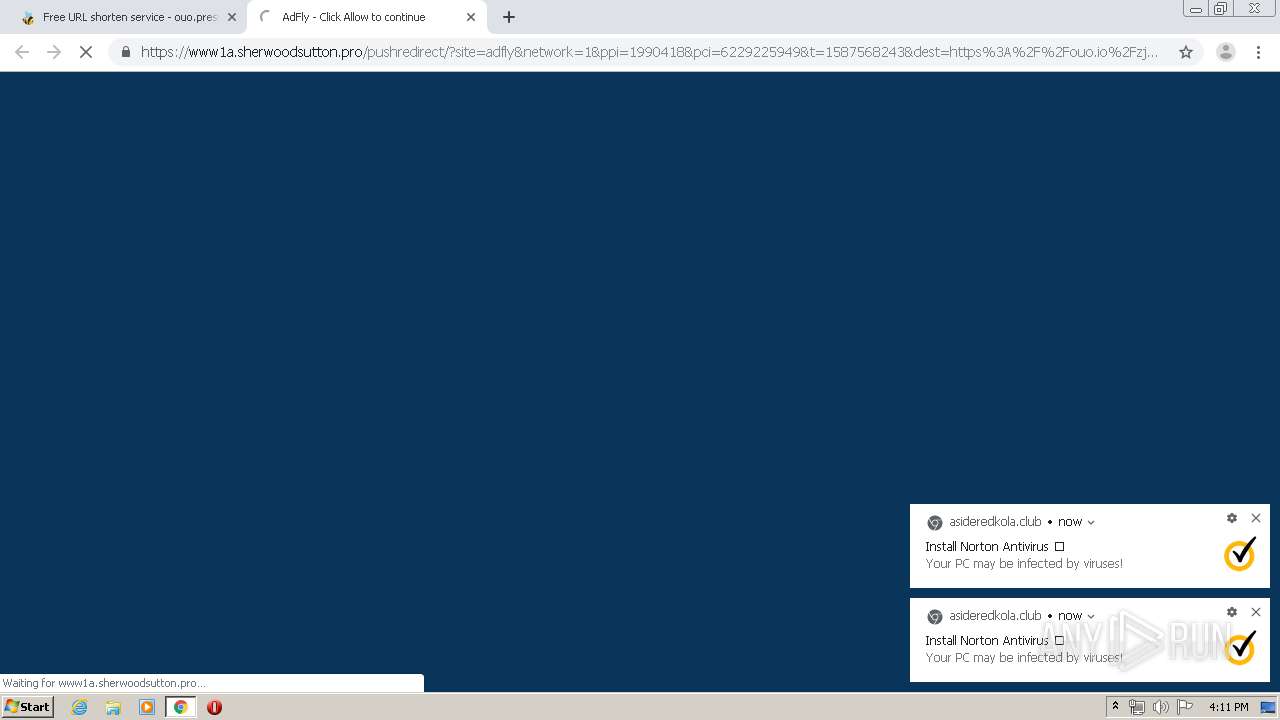
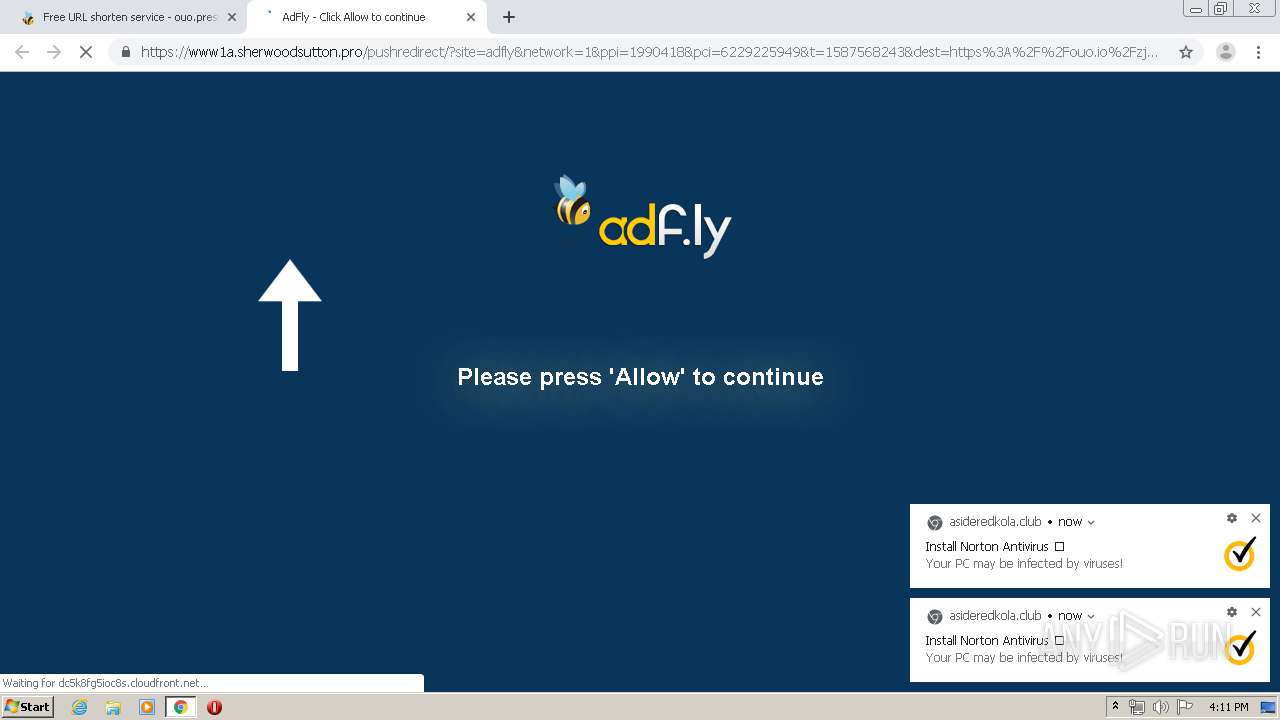
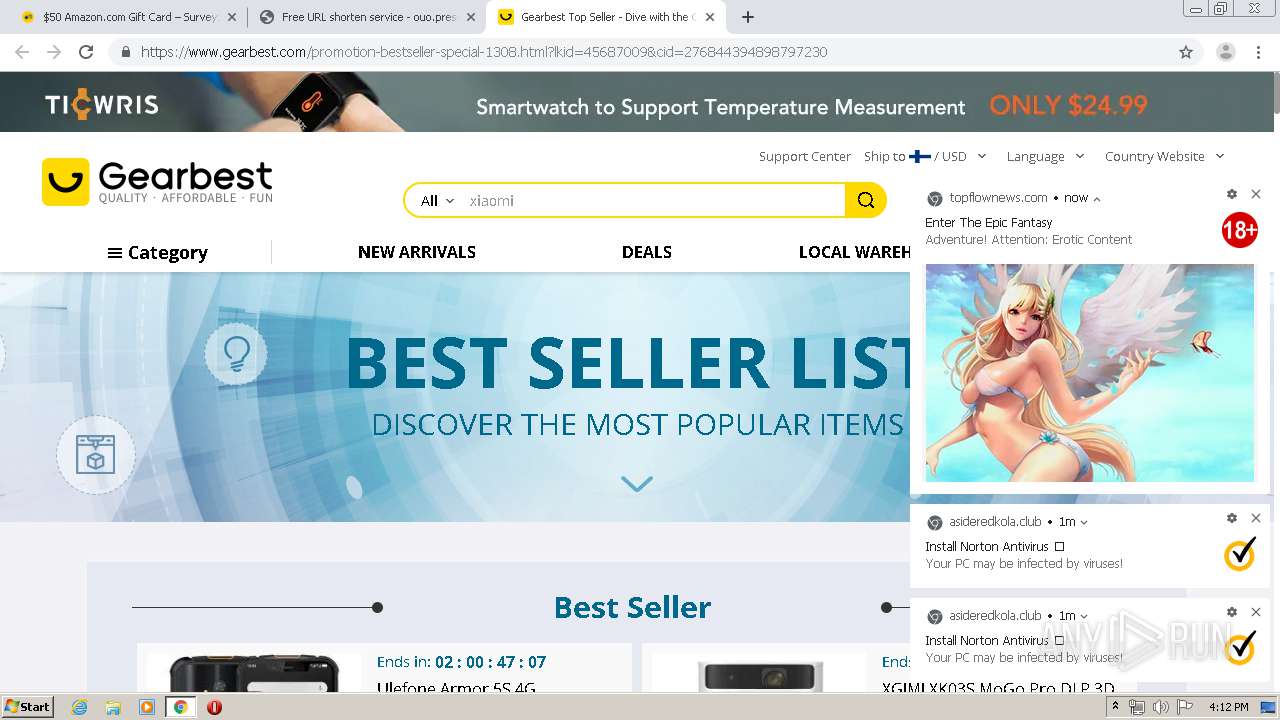
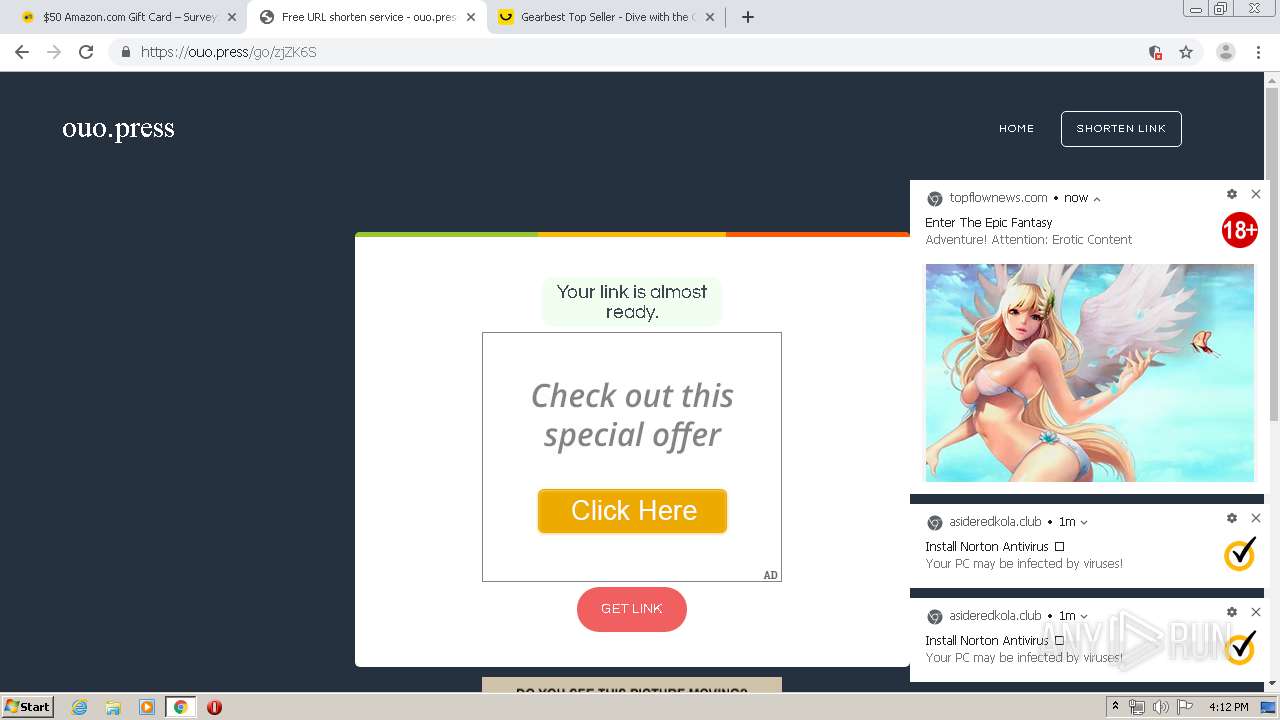
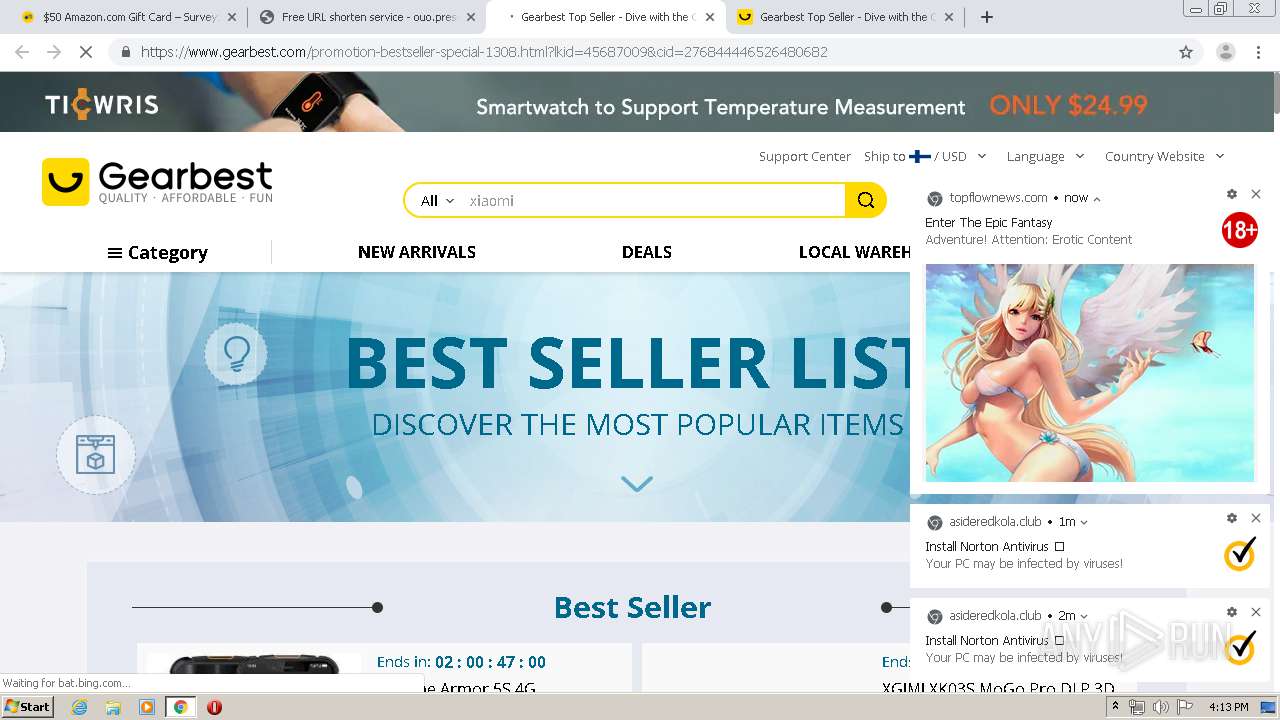
2904 | chrome.exe | GET | 301 | 104.16.108.45:80 | http://demannewcure.site/popunder.gif | US | — | — | suspicious |
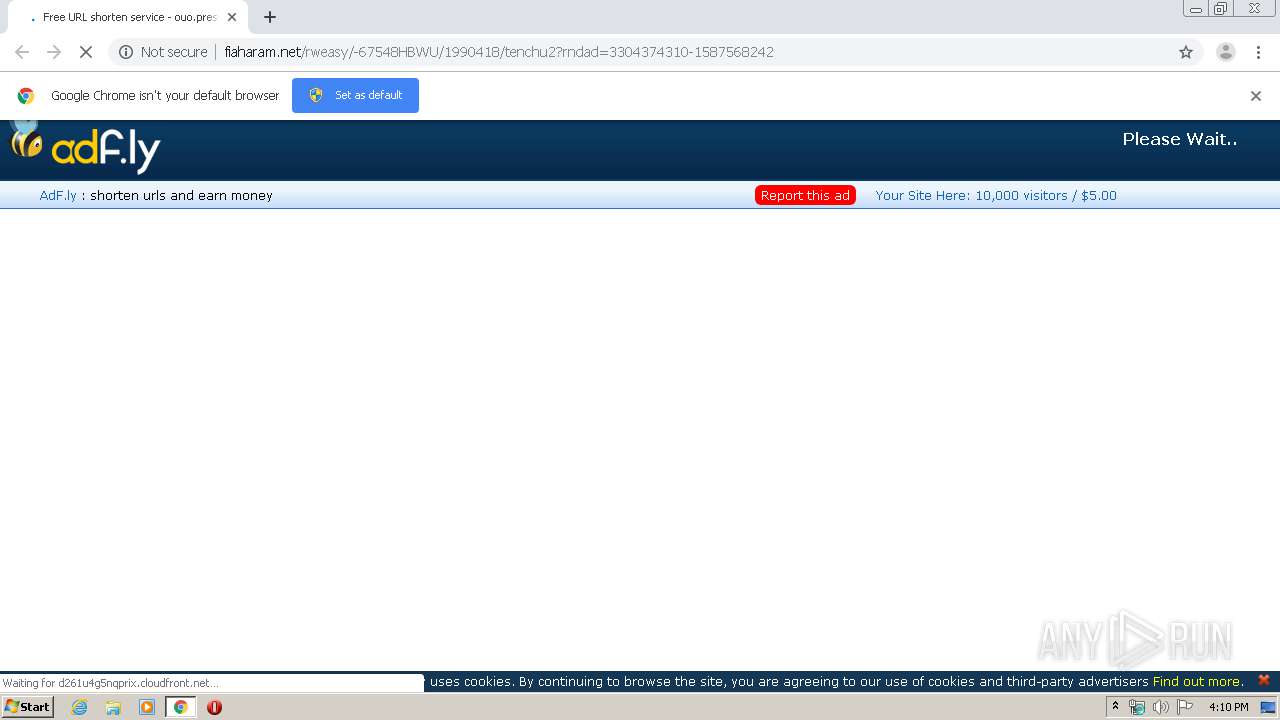
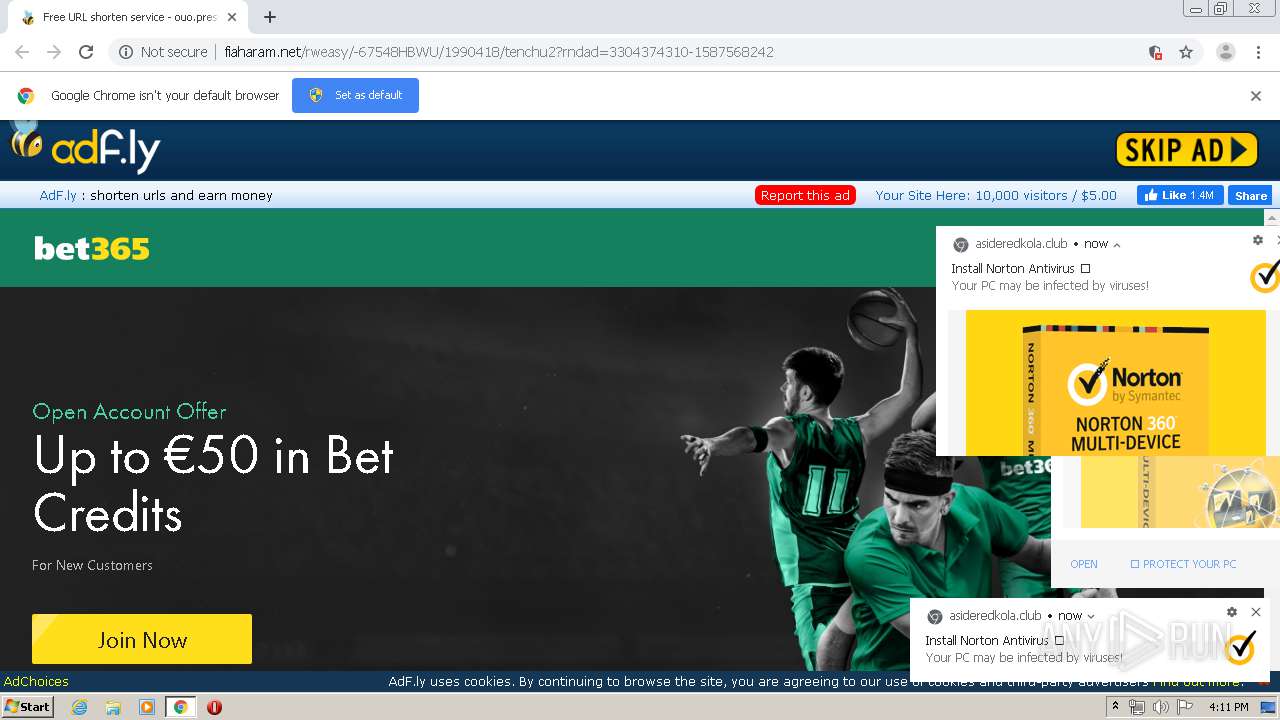
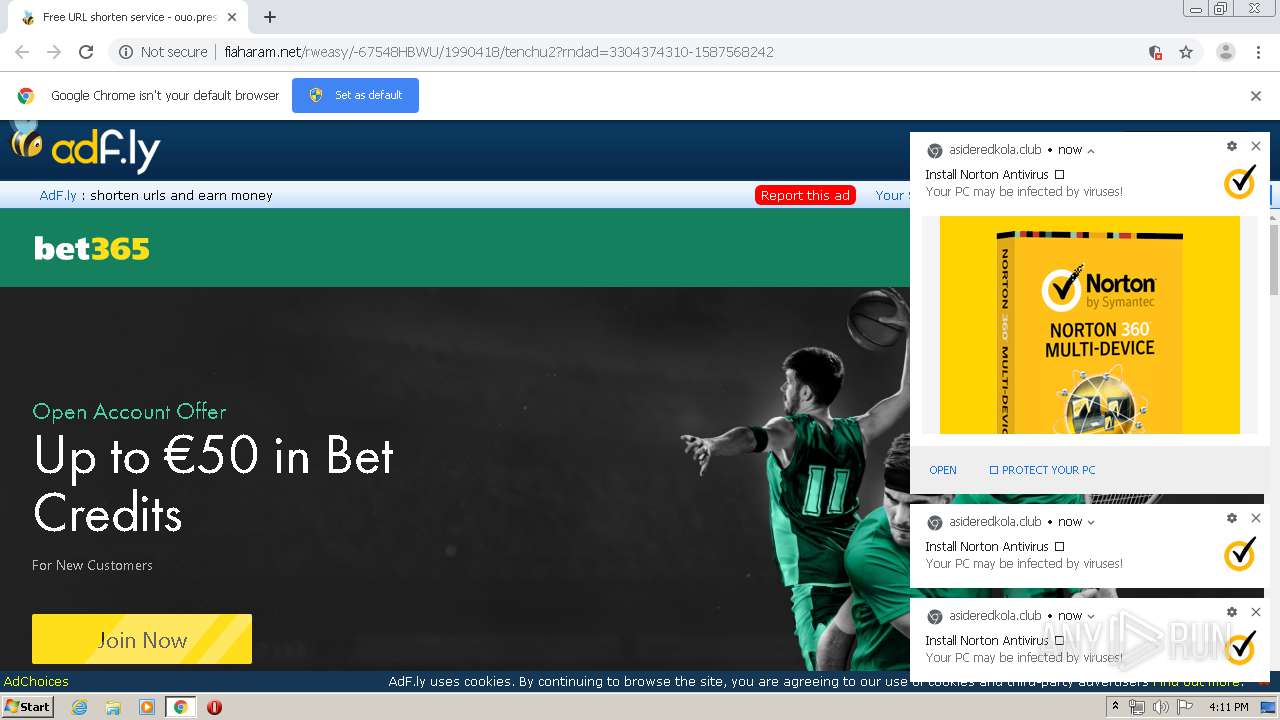
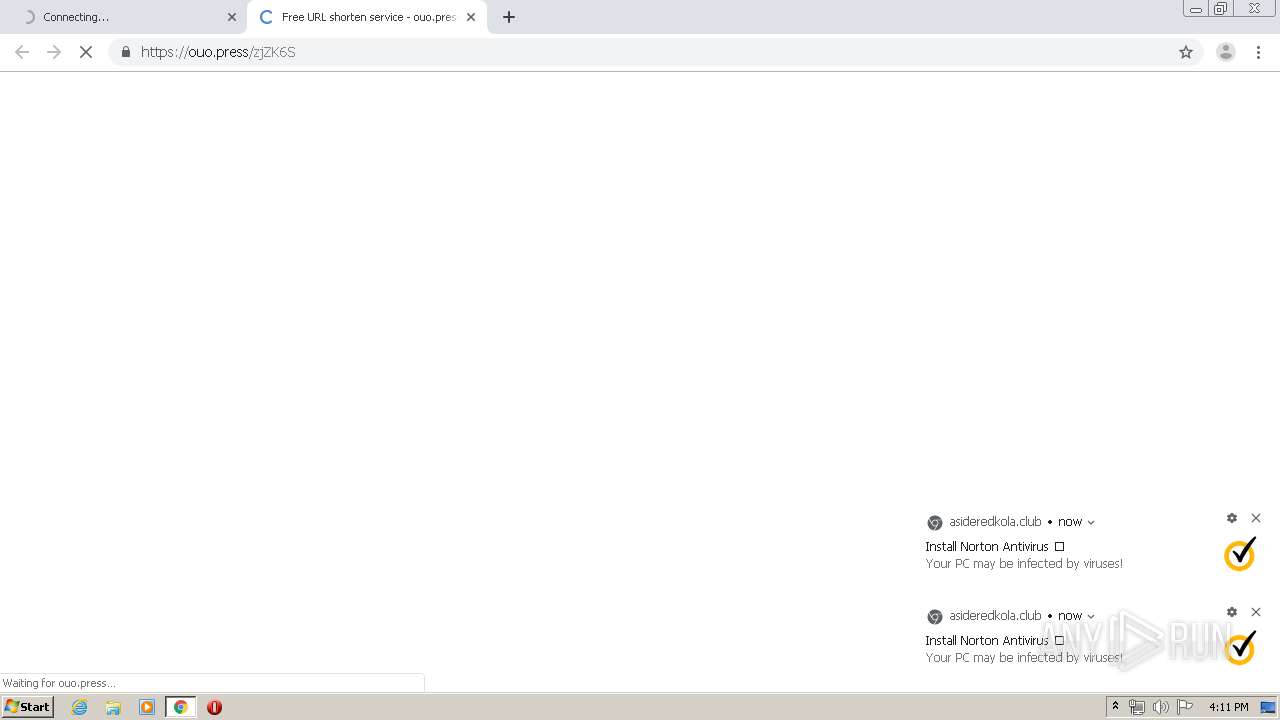
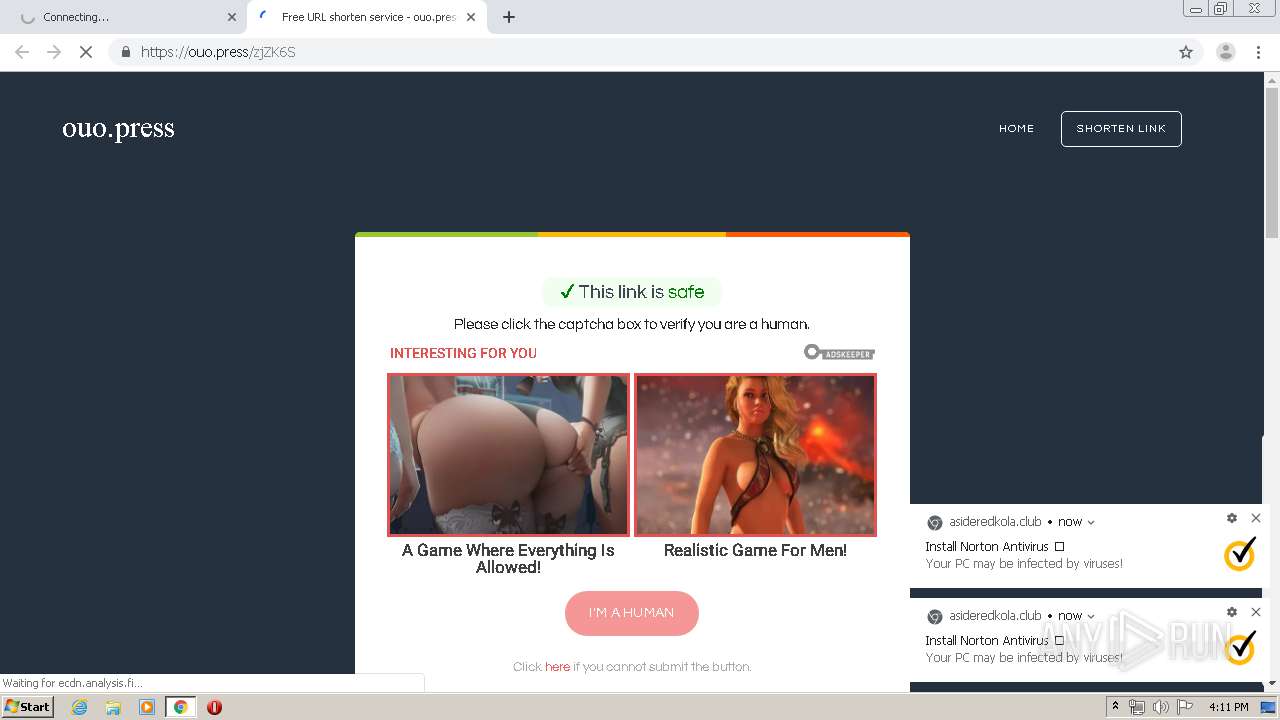
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://fiaharam.net/rweasy/-67548HBWU/1990418/tenchu2?rndad=3304374310-1587568242 | US | html | 5.69 Kb | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://cdn.fiaharam.net/static/js/main.js | US | text | 667 b | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://fiaharam.net/fp.rev11.php?ver=1990418&nocache=280 | US | text | 12.8 Kb | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://cdn.fiaharam.net/static/css/adfly_7.css | US | text | 869 b | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://cdn.fiaharam.net/static/js/b64.js | US | text | 1.07 Kb | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://fiaharam.net/js/display.js | US | text | 13.1 Kb | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://cdn.fiaharam.net/static/js/amvn.js | US | text | 86.2 Kb | whitelisted |
2904 | chrome.exe | GET | 200 | 172.64.164.11:80 | http://cdn.fiaharam.net/static/js/view111.js | US | text | 28.1 Kb | whitelisted |
2904 | chrome.exe | GET | 200 | 52.222.149.7:80 | http://d261u4g5nqprix.cloudfront.net/gQUQyNFkiK1xSZjUtVglvcXABAm1nLkFbNzF5QFE8AwJLA24PCnhhM2cwSFBkcGJeVTcmeRRRNyJ5AxI4JSYPBH81NF1fZDk+VVMpNjNTVTVnMVMJNC4+W1g1IGEAcmxvdBcGaWkzW1o9LjNBEWtxKkYRa3FyHAVwZHYCVSkxKFdDPCMvW0B8cwIHB25vdw-QRa3FsWVwtLCgXBhpkdgJYMCohFwZpJiFRXzZoYQAEOik2XVk8ZHZ0A2xvdBwHbnZ0HAVpcWEABCogIlNGMGR2dAFqdmoBAn80eQECYHgiA1JqJHUCA20kdwpVOid2UAc9cnUAUjgnIQBW | US | text | 397 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2904 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 104.28.25.228:80 | evassmat.com | Cloudflare Inc | US | shared |
2904 | chrome.exe | 172.217.16.170:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 172.64.164.11:80 | fiaharam.net | Cloudflare Inc | US | shared |
2904 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2904 | chrome.exe | 104.16.107.77:443 | statutorjuihui.site | Cloudflare Inc | US | suspicious |
2904 | chrome.exe | 185.33.220.243:443 | secure.adnxs.com | AppNexus, Inc | — | unknown |
2904 | chrome.exe | 104.16.107.113:443 | wordshipopa.club | Cloudflare Inc | US | unknown |
2904 | chrome.exe | 52.222.149.7:80 | d261u4g5nqprix.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
evassmat.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fiaharam.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.fiaharam.net |
| whitelisted |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
www.google.com |
| malicious |
demannewcure.site |
| suspicious |
statutorjuihui.site |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2904 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2904 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2904 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2904 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |