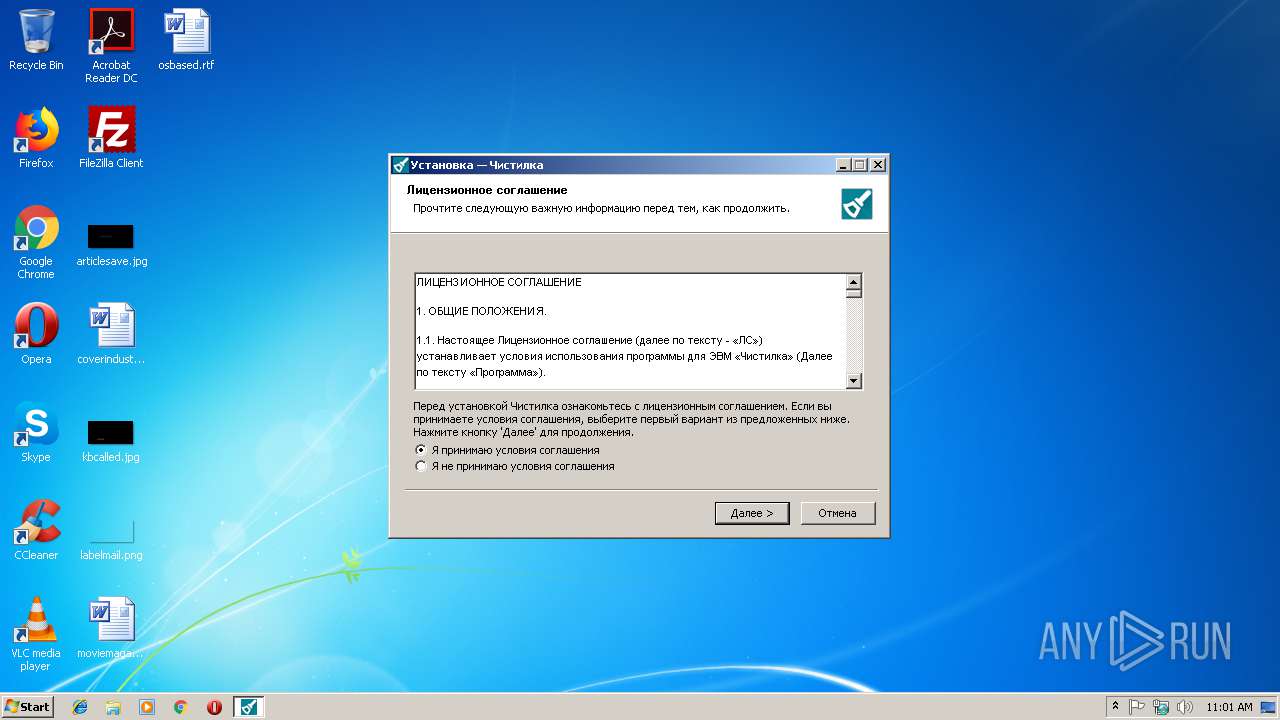
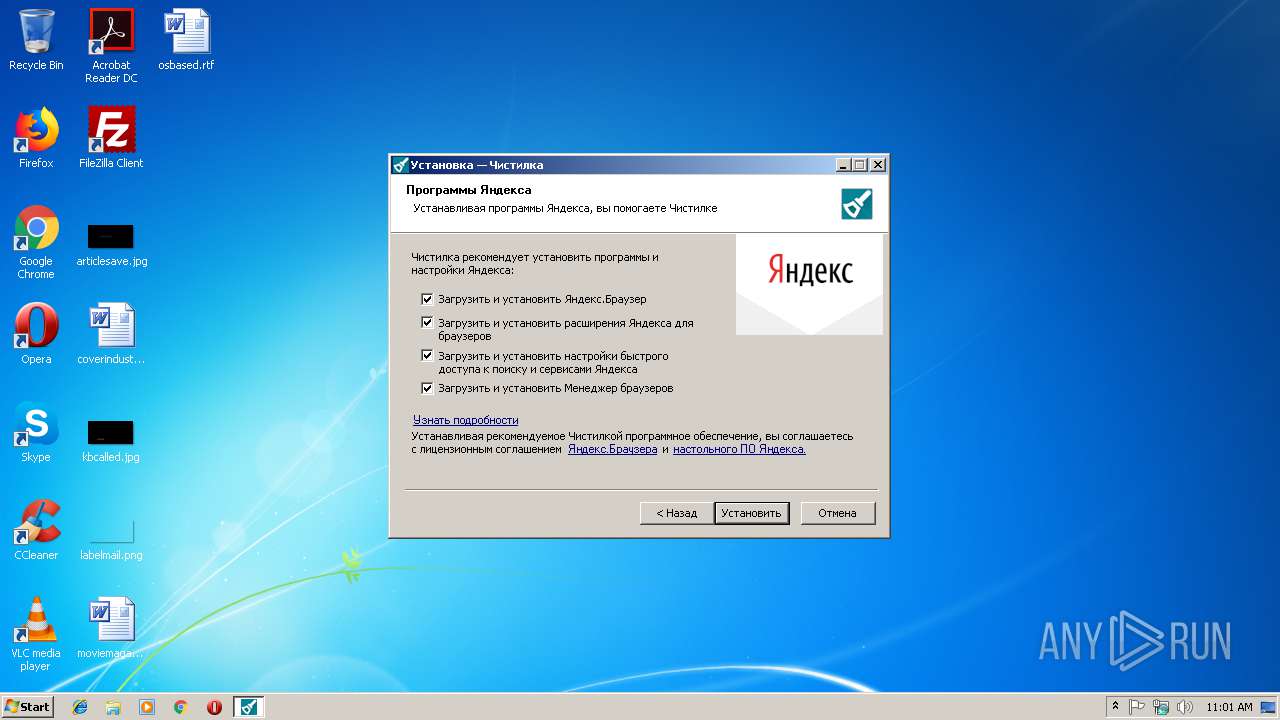
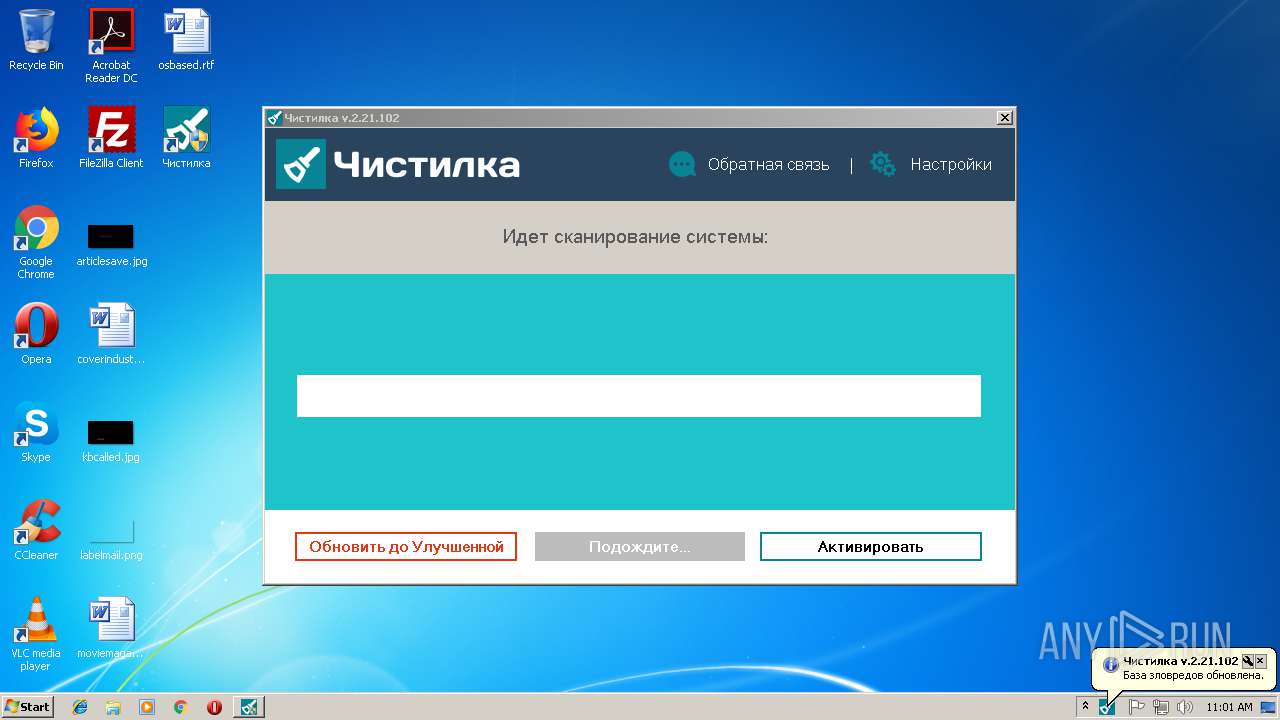
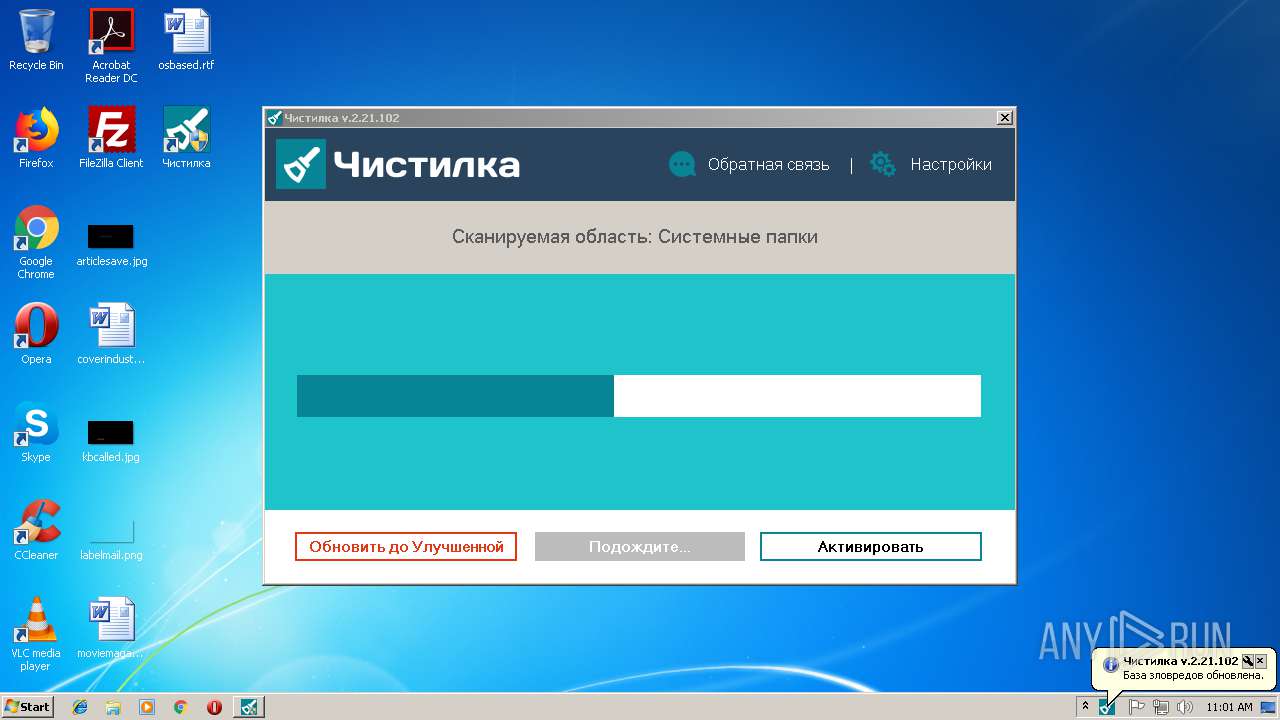
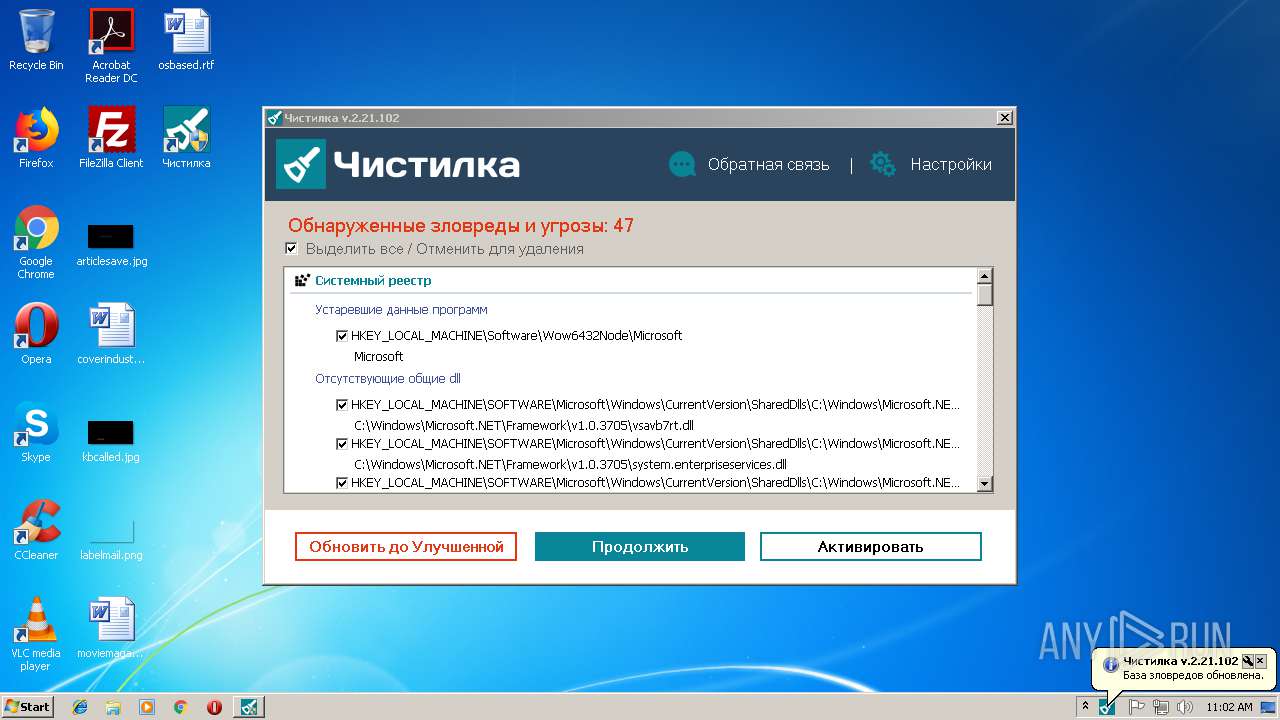
| File name: | chistilka.exe |
| Full analysis: | https://app.any.run/tasks/557dd12d-8296-4682-ac73-98f74afccb23 |
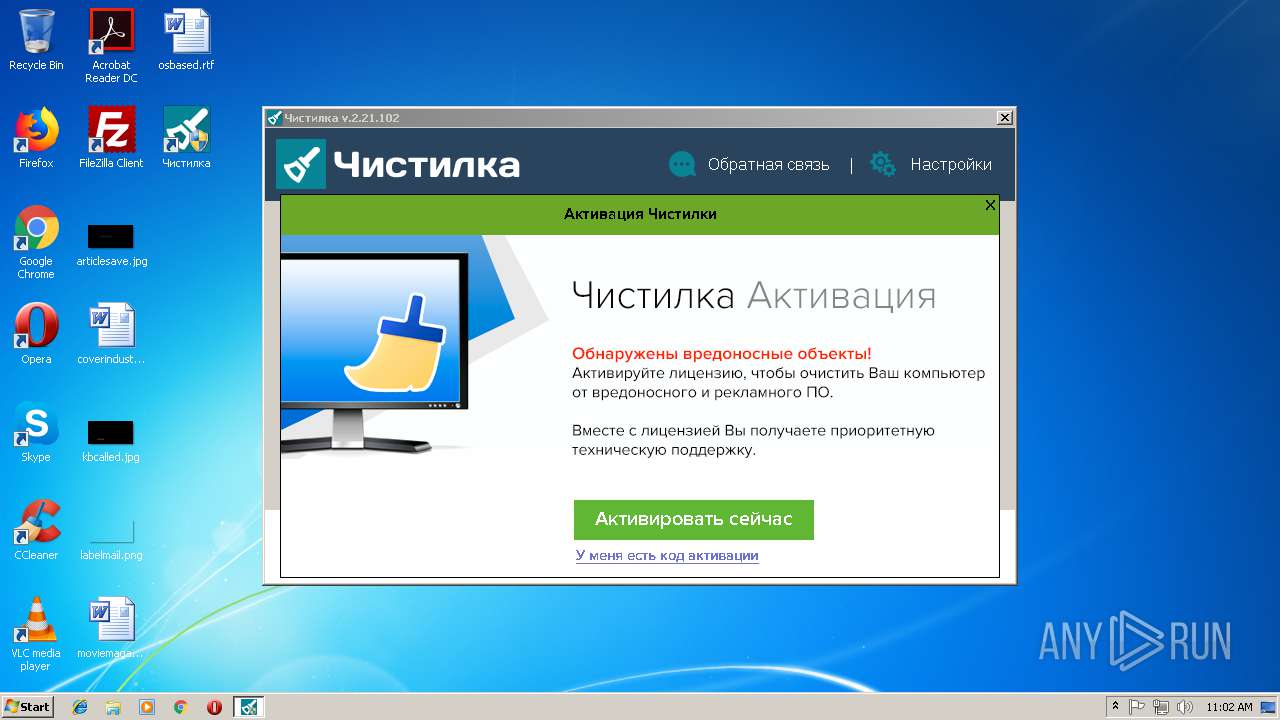
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | February 13, 2019, 11:01:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F7CAC2E61F6E6F559311BB680CDD3EA9 |
| SHA1: | 36A7F424992573649BABD4F2FCF1AC1647DF3EE1 |
| SHA256: | 54E2B31F3269E331335CD748A25A2C0860B4BF035704150D4C6A5F2A84EB39BB |
| SSDEEP: | 49152:cTZcIvjvJgeHqJU9uQNHm3D1jWlwoMr5UJYhZfsZ3rki24hnNgavHuJ:dojRgQqC9FH4Z6eUqjfW3rvbhzuJ |
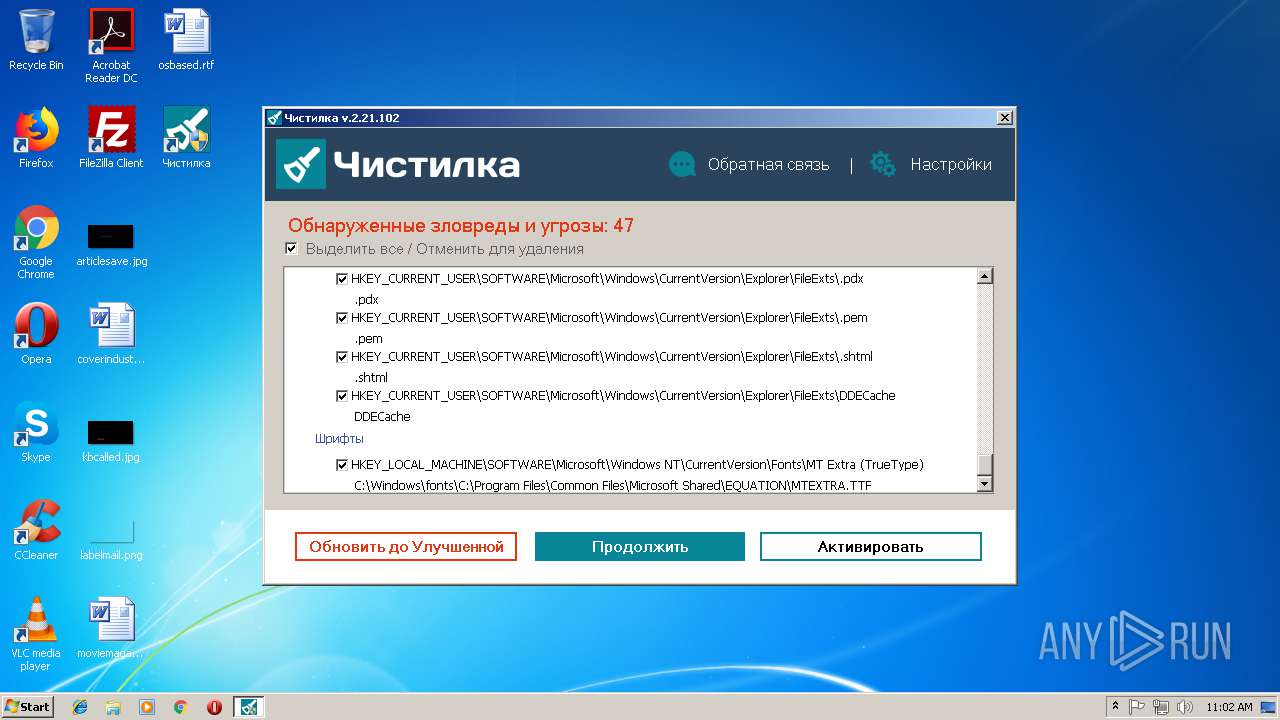
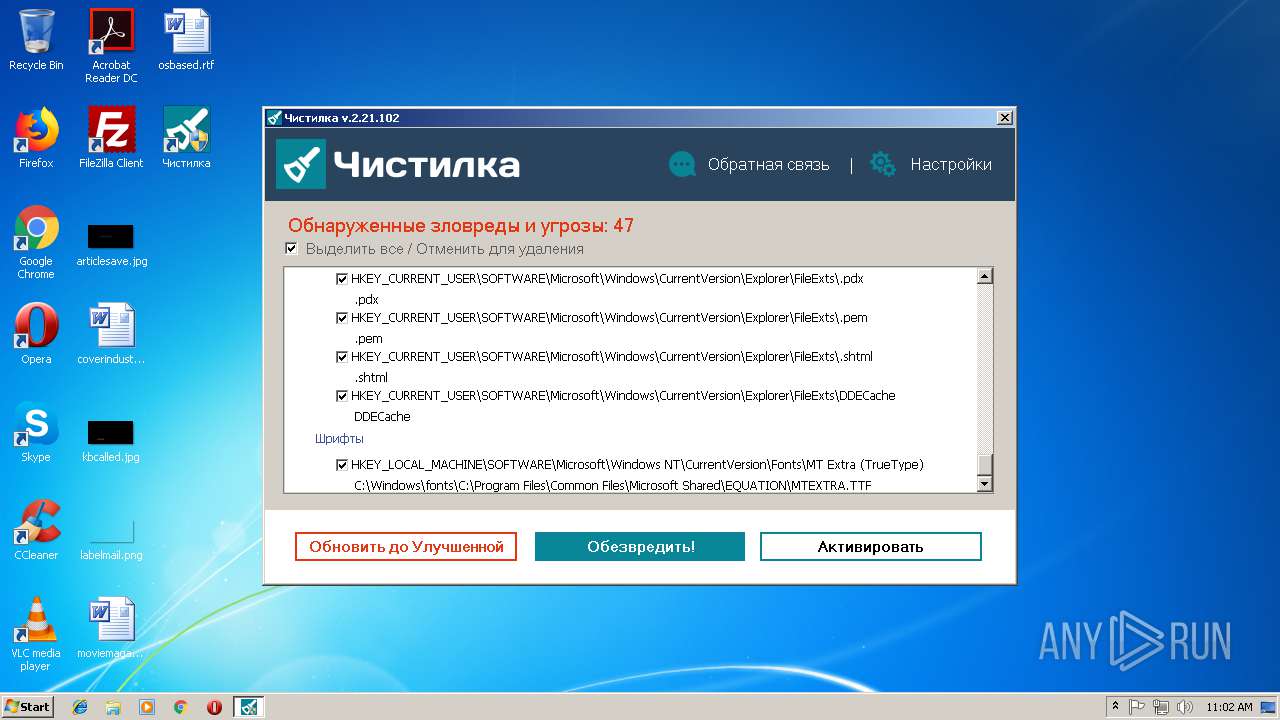
MALICIOUS
Loads dropped or rewritten executable
- chistilka.exe (PID: 2612)
Application was dropped or rewritten from another process
- nsC74F.tmp (PID: 3152)
- Чистилка.exe (PID: 2392)
- uidcreator.exe (PID: 3724)
- downloader.exe (PID: 3420)
- Чистилка.exe (PID: 3728)
- downloader.exe (PID: 3292)
- YandexPackSetup.exe (PID: 3120)
- lite_installer.exe (PID: 2596)
- seederexe.exe (PID: 2472)
- downloader.exe (PID: 4068)
- Yandex.exe (PID: 2784)
- sender.exe (PID: 280)
Loads the Task Scheduler COM API
- Чистилка.exe (PID: 3728)
Changes Windows auto-update feature
- Чистилка.exe (PID: 3728)
Downloads executable files from the Internet
- downloader.exe (PID: 3292)
SUSPICIOUS
Starts application with an unusual extension
- chistilka.exe (PID: 2612)
Executable content was dropped or overwritten
- chistilka.exe (PID: 2612)
- Чистилка.exe (PID: 3728)
- downloader.exe (PID: 3292)
- MsiExec.exe (PID: 2684)
- msiexec.exe (PID: 2128)
- Yandex.exe (PID: 2784)
Creates a software uninstall entry
- chistilka.exe (PID: 2612)
- Yandex.exe (PID: 2784)
Creates files in the program directory
- chistilka.exe (PID: 2612)
- Чистилка.exe (PID: 3728)
- Чистилка.exe (PID: 2392)
Low-level read access rights to disk partition
- Чистилка.exe (PID: 3728)
Reads internet explorer settings
- Чистилка.exe (PID: 3728)
Reads the cookies of Google Chrome
- Чистилка.exe (PID: 3728)
Creates files in the Windows directory
- Чистилка.exe (PID: 3728)
Reads the cookies of Mozilla Firefox
- Чистилка.exe (PID: 3728)
Application launched itself
- Чистилка.exe (PID: 3728)
- downloader.exe (PID: 3292)
Creates files in the user directory
- Чистилка.exe (PID: 3728)
- lite_installer.exe (PID: 2596)
- Yandex.exe (PID: 2784)
- seederexe.exe (PID: 2472)
Reads Internet Cache Settings
- Чистилка.exe (PID: 3728)
Reads Microsoft Outlook installation path
- Чистилка.exe (PID: 3728)
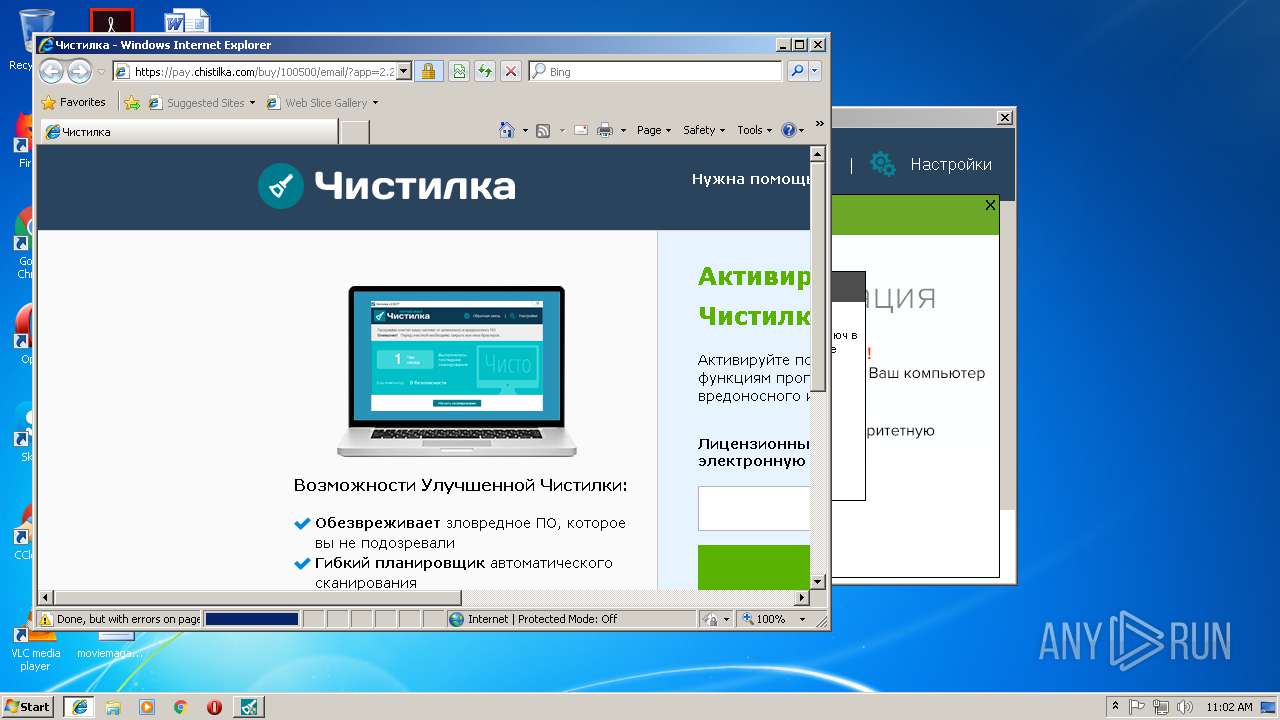
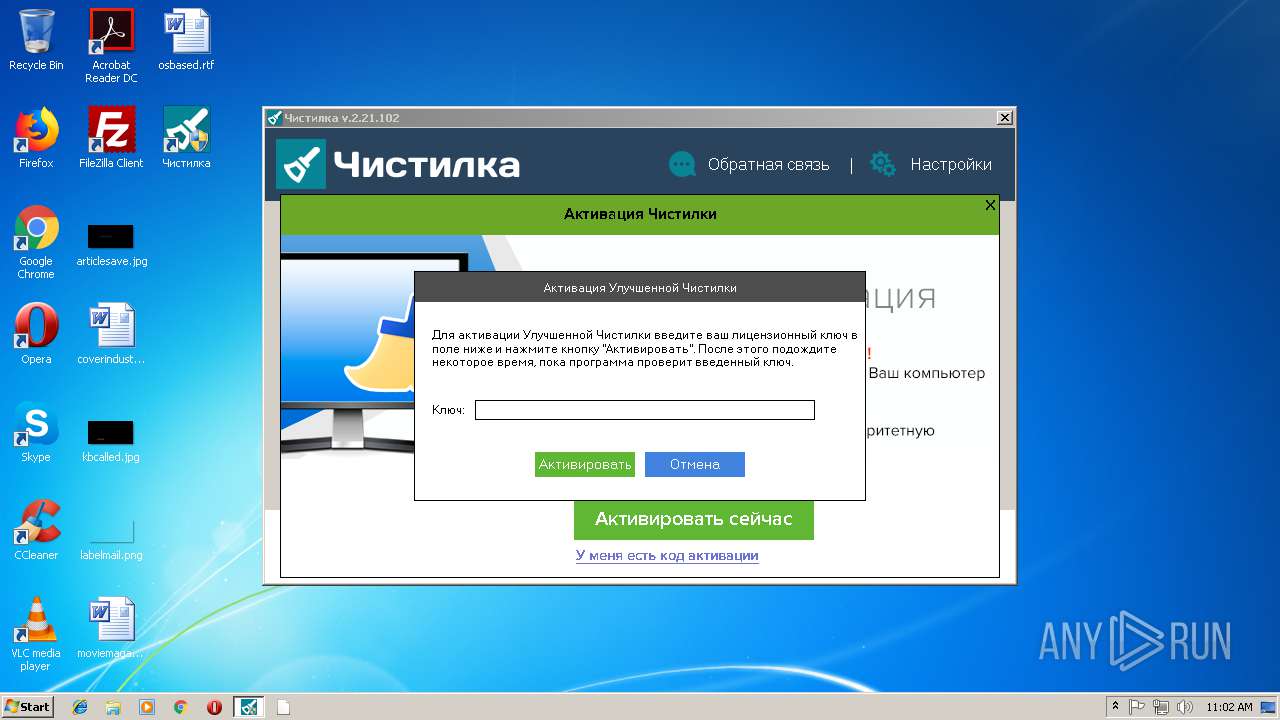
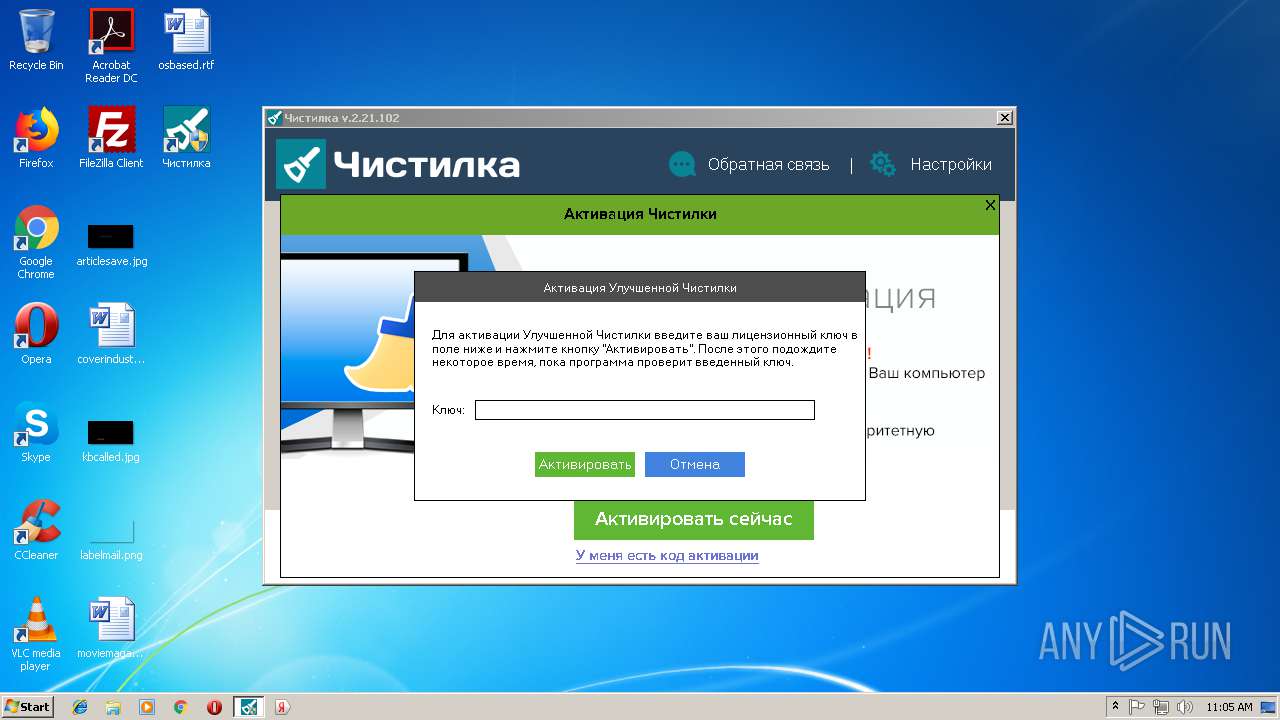
Starts Internet Explorer
- Чистилка.exe (PID: 3728)
Reads Environment values
- MsiExec.exe (PID: 2684)
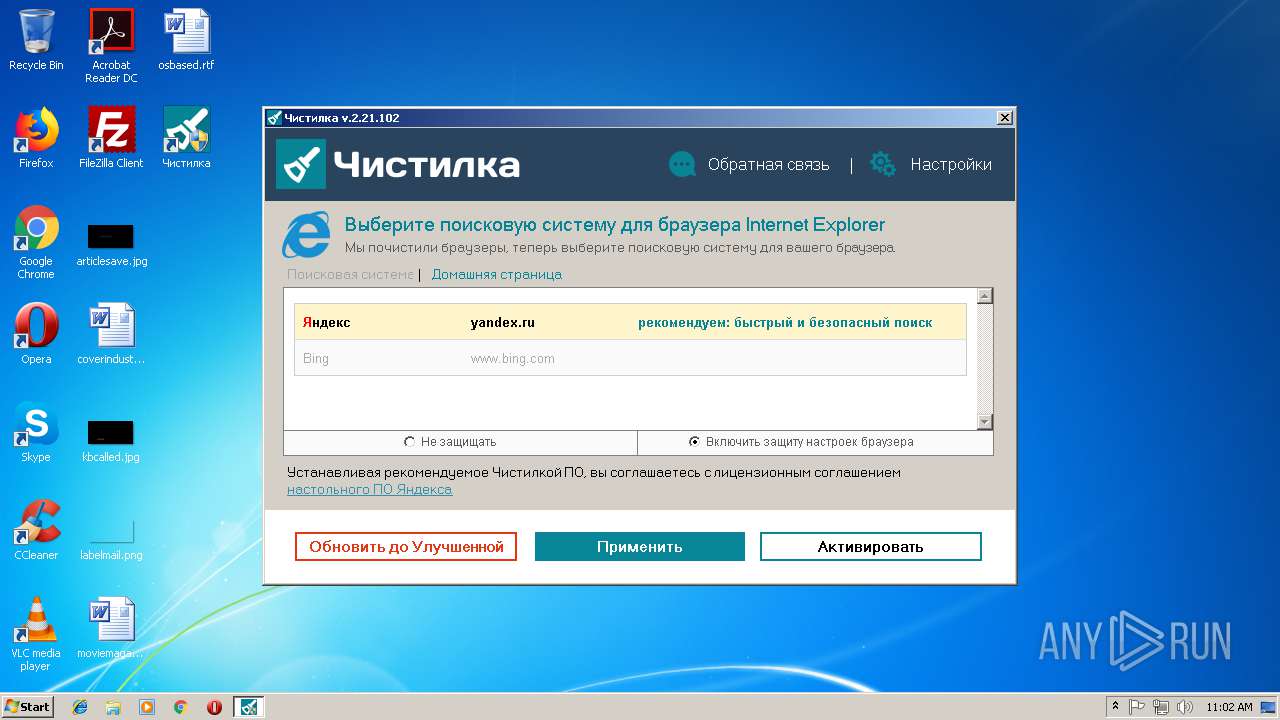
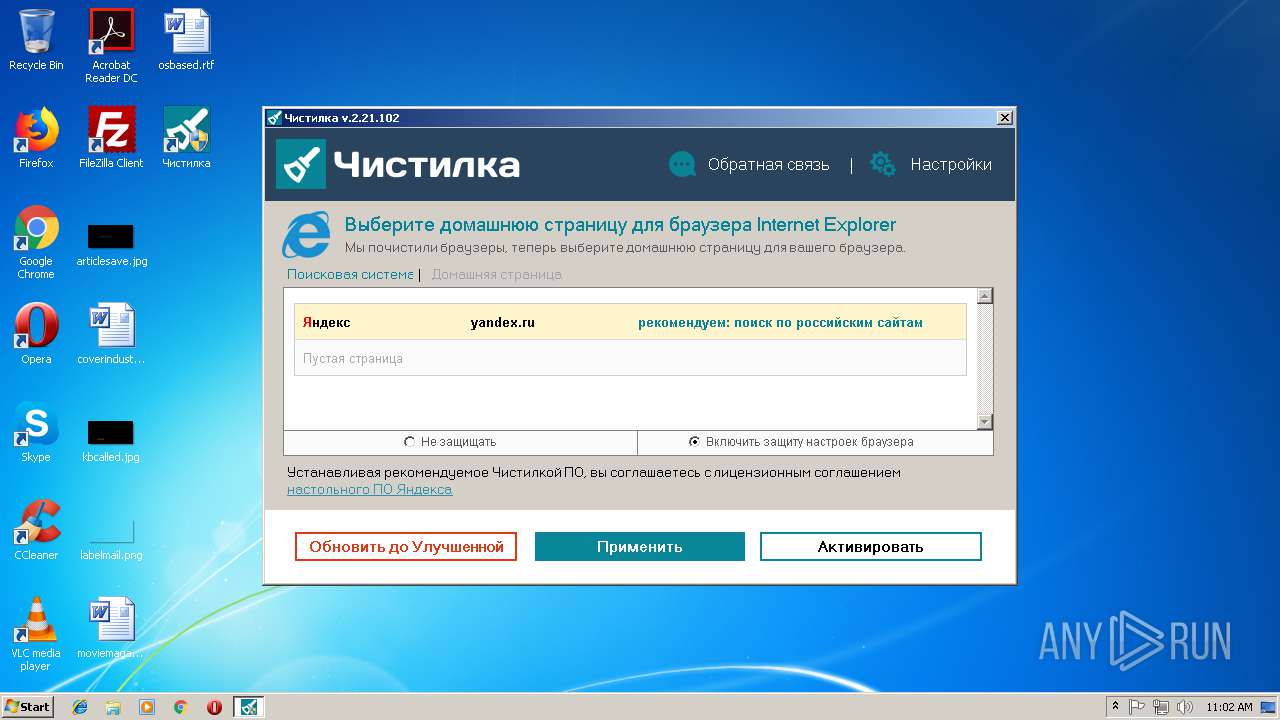
Changes the started page of IE
- seederexe.exe (PID: 2472)
Searches for installed software
- Чистилка.exe (PID: 3728)
INFO
Application launched itself
- iexplore.exe (PID: 2296)
- msiexec.exe (PID: 2128)
Changes internet zones settings
- iexplore.exe (PID: 2296)
Changes settings of System certificates
- iexplore.exe (PID: 3780)
Reads Internet Cache Settings
- iexplore.exe (PID: 3780)
Creates files in the user directory
- iexplore.exe (PID: 3780)
Reads internet explorer settings
- iexplore.exe (PID: 3780)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:01:16 15:07:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 36864 |
| InitializedDataSize: | 40448 |
| UninitializedDataSize: | 462336 |
| EntryPoint: | 0x42ae |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.21.102.0 |
| ProductVersionNumber: | 2.21.102.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 2.21.102.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-2017 14:07:14 |
| Detected languages: |
|
| FileVersion: | 2.21.102.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 16-Jan-2017 14:07:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008F5C | 0x00009000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.06433 |
.data | 0x0000A000 | 0x00000108 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.3581 |
.rdata | 0x0000B000 | 0x00007070 | 0x00007200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.07705 |
.bss | 0x00013000 | 0x00070D40 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00084000 | 0x0000140C | 0x00001600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06767 |
.ndata | 0x00086000 | 0x00134000 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001BA000 | 0x0001BEB0 | 0x0001C000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73433 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29645 | 1066 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.07244 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 7.93337 | 11195 | UNKNOWN | English - United States | RT_ICON |
4 | 4.12089 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.62272 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04001 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.72007 | 574 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.84976 | 260 | UNKNOWN | English - United States | RT_DIALOG |
108 | 2.74782 | 266 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
54
Monitored processes
18
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | C:\Users\admin\AppData\Local\Temp\04A6EE6B-8B87-427C-A662-2AC495481C60\sender.exe --send "/status.xml?clid=2328147-2&uuid=%7B9DE1FFCA-0307-49C4-9150-4E5A9FA83130%7D&vnt=Windows 7x32&file-no=6%0A10%0A11%0A12%0A13%0A15%0A16%0A17%0A18%0A20%0A21%0A22%0A25%0A38%0A40%0A42%0A43%0A45%0A57%0A61%0A89%0A106%0A108%0A111%0A121%0A123%0A124%0A125%0A129%0A" | C:\Users\admin\AppData\Local\Temp\04A6EE6B-8B87-427C-A662-2AC495481C60\sender.exe | seederexe.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Yandex Statistics Exit code: 0 Version: 0.0.2.14 Modules
| |||||||||||||||
| 2128 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Чистилка.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | C:\ProgramData\Чистилка\Чистилка.exe /srvcreate | C:\ProgramData\Чистилка\Чистилка.exe | Чистилка.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\Temp\D4B74118-F056-4117-8E45-0E6FAC321DD0\seederexe.exe" "--yqs=y" "--yhp=y" "--ilight=" "--locale=us" "--browser=n" "--browser_default=" "--yabm=n" "--loglevel=trace" "--ess=" "--clids=C:\Users\admin\AppData\Local\Temp\clids-yasearch.xml" "--sender=C:\Users\admin\AppData\Local\Temp\04A6EE6B-8B87-427C-A662-2AC495481C60\sender.exe" "--is_elevated=yes" "--ui_level=2" "--good_token=1" | C:\Users\admin\AppData\Local\Temp\D4B74118-F056-4117-8E45-0E6FAC321DD0\seederexe.exe | MsiExec.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Browser Integration Module Exit code: 0 Version: 3.5.3.98 Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\AppData\Local\Temp\21706F6E-10DD-4270-BC43-E51AF71D59F1\lite_installer.exe" --use-user-default-locale --silent --cumtom-welcome-page=https://browser.yandex.ru/promo/welcome_com/5/ | C:\Users\admin\AppData\Local\Temp\21706F6E-10DD-4270-BC43-E51AF71D59F1\lite_installer.exe | MsiExec.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: YandexBrowserDownloader Exit code: 0 Version: 1.0.1.88 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\chistilka.exe" | C:\Users\admin\AppData\Local\Temp\chistilka.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2.21.102.0 Modules
| |||||||||||||||
| 2684 | C:\Windows\system32\MsiExec.exe -Embedding 0E5E1547A800CFAAE9DC855CDD49C1BA | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2784 | "C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe" --silent | C:\Users\admin\AppData\Local\Yandex\YaPin\Yandex.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: YandexPin Exit code: 1 Version: 2.0.5.38 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Local\Temp\7F4987FB1A6E43d69E3E94B29EB75926\YandexPackSetup.exe" /quiet /msicl "VID=2 YABROWSER=n YABM=n YAHOMEPAGE=y YAQSEARCH=y" | C:\Users\admin\AppData\Local\Temp\7F4987FB1A6E43d69E3E94B29EB75926\YandexPackSetup.exe | downloader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Software Installer Exit code: 0 Version: 3.0.5419.0 Modules
| |||||||||||||||
Total events
3 719
Read events
3 090
Write events
586
Delete events
43
Modification events
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\chst_installer |
| Operation: | write | Name: | uid |
Value: 28bc55e8-4861-4a0b-9acb-2421fed4d1ed-e983db172eadb6b95adc6cd38fc2ea4e9ee2abc9 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2612) chistilka.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\chistilka_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
20
Suspicious files
20
Text files
126
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2612 | chistilka.exe | C:\Users\admin\AppData\Local\Temp\nsrA81E.tmp\nsDialogs.dll | executable | |
MD5:— | SHA256:— | |||
| 2612 | chistilka.exe | C:\Users\admin\AppData\Local\Temp\nsrA81E.tmp\System.dll | executable | |
MD5:— | SHA256:— | |||
| 3728 | Чистилка.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cookies-journal | — | |
MD5:— | SHA256:— | |||
| 2612 | chistilka.exe | C:\Users\admin\AppData\Local\Temp\nsrA81E.tmp\nsC74F.tmp | executable | |
MD5:— | SHA256:— | |||
| 3728 | Чистилка.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2612 | chistilka.exe | C:\ProgramData\Чистилка\Чистилка.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | chistilka.exe | C:\ProgramData\Чистилка\uidcreator.exe | executable | |
MD5:— | SHA256:— | |||
| 2612 | chistilka.exe | C:\ProgramData\Чистилка\uninstaller.exe | executable | |
MD5:— | SHA256:— | |||
| 3728 | Чистилка.exe | C:\Users\Public\Desktop\Чистилка.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3728 | Чистилка.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Чистилка\Чистилка Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
24
DNS requests
19
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | downloader.exe | GET | 302 | 5.45.205.235:80 | http://downloader.yandex.net/yandex-pack/downloader/info.rss | RU | — | — | whitelisted |
3420 | downloader.exe | GET | — | 87.250.251.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=12/cid=72435/path=noaction/p=8254/* | RU | — | — | whitelisted |
3292 | downloader.exe | GET | 302 | 5.45.205.235:80 | http://downloader.yandex.net/yandex-pack/8254/YandexPackSetup.exe | RU | — | — | whitelisted |
4068 | downloader.exe | GET | — | 87.250.251.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=12/cid=72435/path=dwnldr/p=8254/cnt=0/dt=2/ct=0/rt=6/imp=0/* | RU | — | — | whitelisted |
3292 | downloader.exe | GET | 200 | 37.9.96.18:80 | http://cache-mskstoredata07.cdn.yandex.net/downloader.yandex.net/yandex-pack/8254/YandexPackSetup.exe | RU | executable | 9.24 Mb | whitelisted |
3292 | downloader.exe | GET | 200 | 37.9.96.17:80 | http://cache-mskstoredata06.cdn.yandex.net/downloader.yandex.net/yandex-pack/downloader/info.rss | RU | xml | 267 b | whitelisted |
2596 | lite_installer.exe | GET | — | 87.250.250.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=198/cid=73002/path=0.no_action/ui=%7B9DE1FFCA-0307-49C4-9150-4E5A9FA83130%7D/clid1=-1/dt=0/ds=0/bits=7_5_7601_17514/bver=0_0_0_0/prod_version=1_0_1_88/result=ok/* | RU | — | — | whitelisted |
2472 | seederexe.exe | GET | 200 | 87.250.250.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=198/cid=73068/path=3_5_3_98/anti=0/antiNames=/browser=iexplore/clid=2328147-2/ff=107/gc=229/goodToken=1/googlin=0/ie=142/init=8966/mlru=5/op=14/op64=10/ui=%7B9DE1FFCA-0307-49C4-9150-4E5A9FA83130%7D/yabro=0/%2A | RU | image | 43 b | whitelisted |
3728 | Чистилка.exe | POST | 200 | 172.217.16.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3780 | iexplore.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2612 | chistilka.exe | 172.217.16.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3420 | downloader.exe | 87.250.251.14:80 | clck.yandex.ru | YANDEX LLC | RU | whitelisted |
3728 | Чистилка.exe | 216.239.35.0:123 | time.google.com | Google Inc. | US | unknown |
3728 | Чистилка.exe | 54.37.81.78:443 | stat2.chistilka.com | OVH SAS | FR | malicious |
3728 | Чистилка.exe | 5.135.140.26:443 | update.chistilka.com | OVH SAS | FR | suspicious |
3728 | Чистилка.exe | 172.217.16.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3292 | downloader.exe | 5.45.205.235:80 | downloader.yandex.net | YANDEX LLC | RU | whitelisted |
3292 | downloader.exe | 37.9.96.17:80 | cache-mskstoredata06.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3292 | downloader.exe | 37.9.96.18:80 | cache-mskstoredata07.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3780 | iexplore.exe | 5.135.140.26:443 | update.chistilka.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
clck.yandex.ru |
| whitelisted |
time.google.com |
| whitelisted |
stat2.chistilka.com |
| malicious |
update.chistilka.com |
| suspicious |
downloader.yandex.net |
| whitelisted |
cache-mskstoredata06.cdn.yandex.net |
| whitelisted |
cache-mskstoredata07.cdn.yandex.net |
| whitelisted |
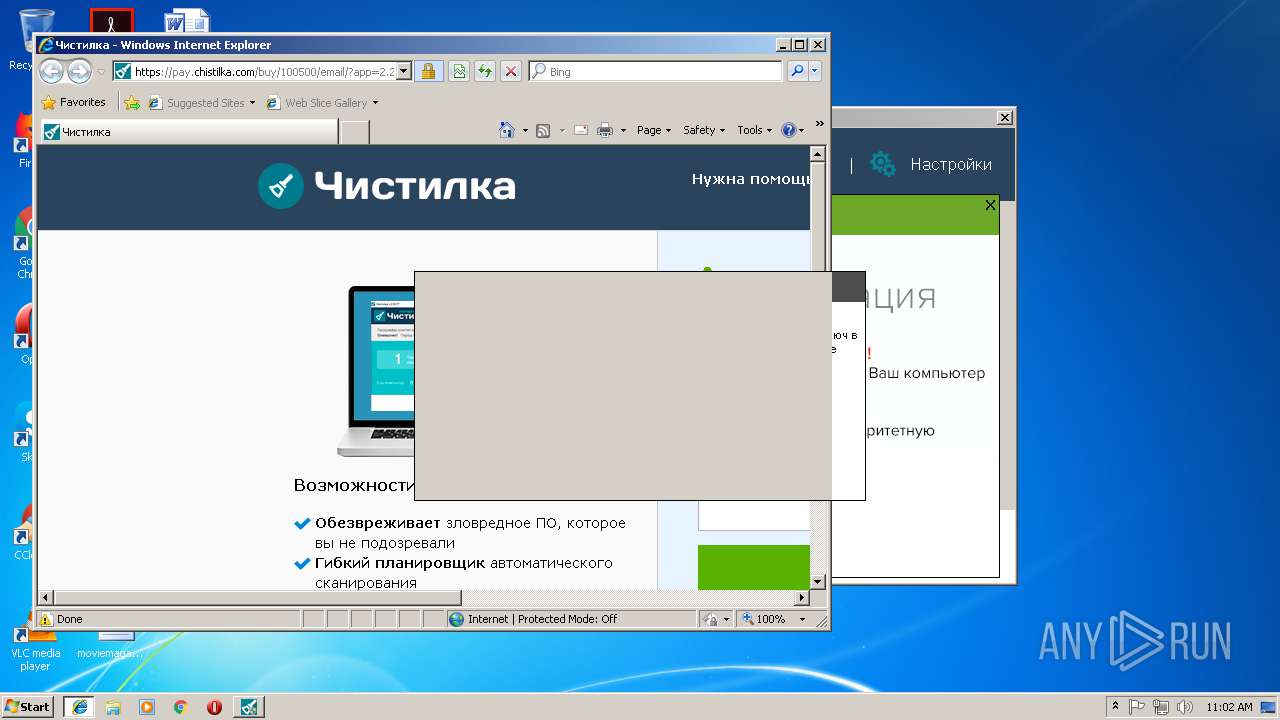
pay.chistilka.com |
| suspicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2612 | chistilka.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
3420 | downloader.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
3292 | downloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4068 | downloader.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
Process | Message |
|---|---|
Чистилка.exe | [2019-02-13 11:01:46] M Log.cpp:110 Logging to C:\ProgramData\????????\logs\TKiller-2-2019-02-13-11-01-46.log
|
Чистилка.exe | [2019-02-13 11:01:46] M main.cpp:13 App started, version 2.21.102, build type 'UTIL', pid 3728, command line '"C:\ProgramData\????????\????????.exe" '
|
Чистилка.exe | [2019-02-13 11:01:46] M Http.cpp:36 WinSock init ok, version 514
|
Чистилка.exe | [2019-02-13 11:01:46] M Config.cpp:282 Partner: 'chistilkacom'
|
Чистилка.exe | [2019-02-13 11:01:46] M Config.cpp:384 Yandex VID: '2'
|
Чистилка.exe | [2019-02-13 11:01:46] M SystemInfo.cpp:62 OS: Windows 7 (6.1-32)
|
Чистилка.exe | [2019-02-13 11:01:46] M SystemInfo.cpp:164 Using uid from installer: 28bc55e8-4861-4a0b-9acb-2421fed4d1ed-e983db172eadb6b95adc6cd38fc2ea4e9ee2abc9
|
Чистилка.exe | [2019-02-13 11:01:46] M SystemInfo.cpp:66 UID: 28bc55e8-4861-4a0b-9acb-2421fed4d1ed-e983db172eadb6b95adc6cd38fc2ea4e9ee2abc9
|
Чистилка.exe | [2019-02-13 11:01:46] M SystemInfo.cpp:70 HWID: 048ea7dadfda4e2e7e4c5da96a4934a6d6c67b7a
|
Чистилка.exe | [2019-02-13 11:01:46] M StatSenderImpl.cpp:46 Got UTC time: 1550055706
|