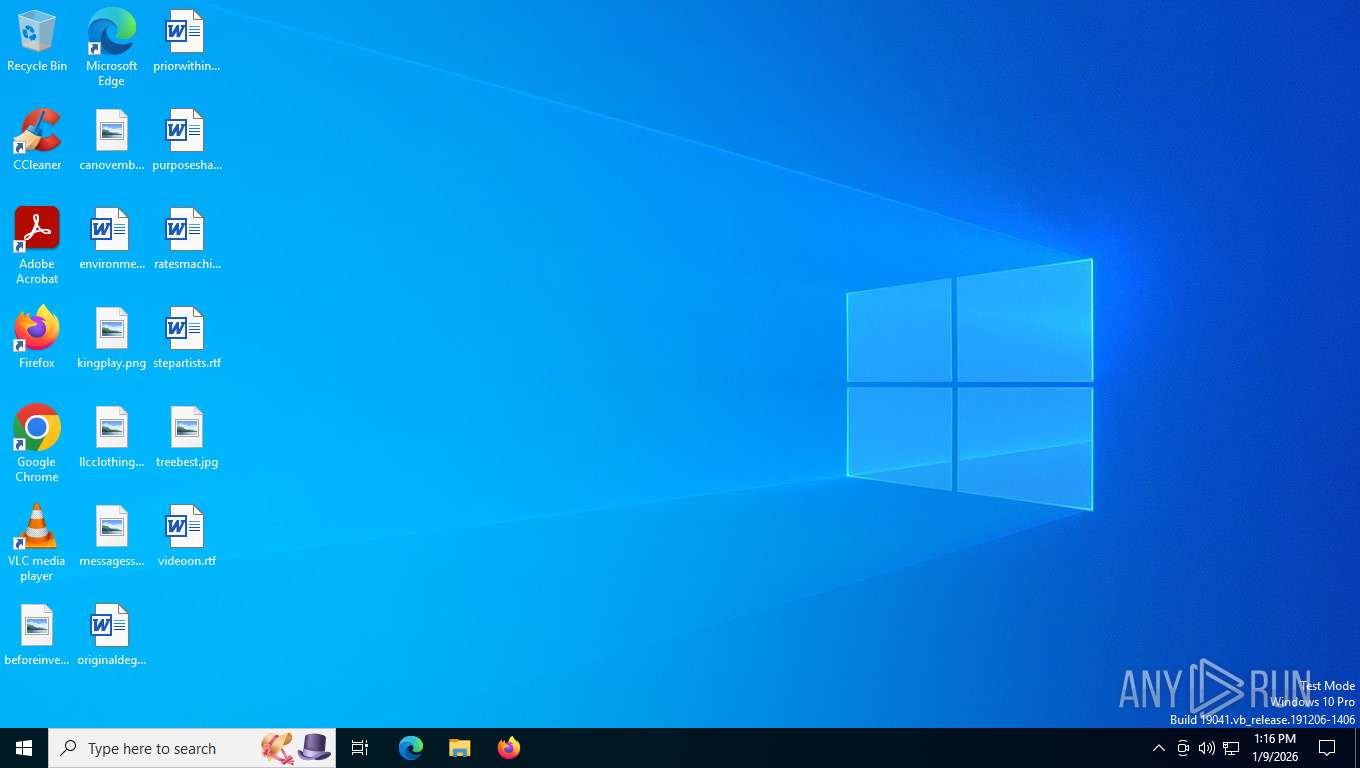
| File name: | Game.exe |
| Full analysis: | https://app.any.run/tasks/17b32ef9-4f29-47ed-a61c-b76139e6dbaf |
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2026, 18:15:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | CA4069130468D93AC7C719BF89F792C8 |
| SHA1: | 7F6AE8F83B6D4CF9D1494221C14437942B9E9152 |
| SHA256: | 54D788B1AF6BA0343256E528AADFAAE30E2AD214E7A6915DC08F0DDDC23B2F2C |
| SSDEEP: | 98304:TiTj4vyYw+Qt/WSYJ33a4aBpClP1ewmJOIJGL57x5cyz6EF1HiDSnNRPDKTl57OC:OlN4vGfpoEL |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7900)
- powershell.exe (PID: 5628)
Bypass execution policy to execute commands
- powershell.exe (PID: 7900)
- powershell.exe (PID: 5628)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7988)
SUSPICIOUS
Executable content was dropped or overwritten
- Game.exe (PID: 7680)
- Game_patch-run.exe (PID: 7724)
Starts itself from another location
- Game.exe (PID: 7680)
Reads security settings of Internet Explorer
- Game.exe (PID: 7680)
- Game_patch-run.exe (PID: 7724)
The process creates files with name similar to system file names
- Game_patch-run.exe (PID: 7724)
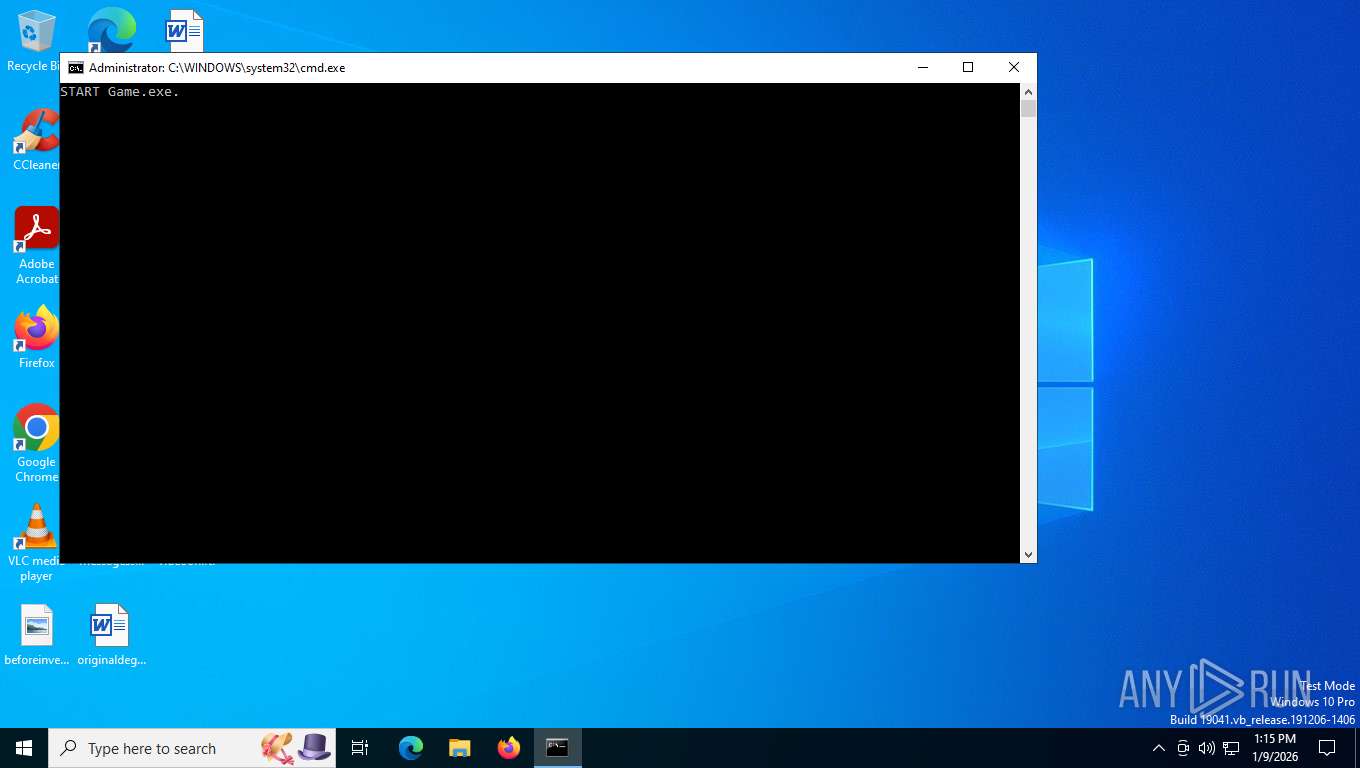
Starts CMD.EXE for commands execution
- Game_patch-run.exe (PID: 7724)
- cmd.exe (PID: 7988)
Executing commands from a ".bat" file
- Game_patch-run.exe (PID: 7724)
Application launched itself
- cmd.exe (PID: 7988)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7988)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7988)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7988)
Executes application which crashes
- Game.exe (PID: 7764)
Malware-specific behavior (creating "System.dll" in Temp)
- Game_patch-run.exe (PID: 7724)
Manipulates environment variables
- powershell.exe (PID: 4636)
- powershell.exe (PID: 7272)
- powershell.exe (PID: 7712)
- powershell.exe (PID: 7900)
Removes files via Powershell
- powershell.exe (PID: 4636)
The process executes Powershell scripts
- cmd.exe (PID: 7988)
Base64-obfuscated command line is found
- cmd.exe (PID: 7988)
Reads binary file using Get-Content
- powershell.exe (PID: 7712)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7272)
- powershell.exe (PID: 7900)
Renames file via Powershell
- powershell.exe (PID: 7272)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7988)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7988)
INFO
Reads the computer name
- Game.exe (PID: 7680)
- Game_patch-run.exe (PID: 7724)
- Game.exe (PID: 7764)
- identity_helper.exe (PID: 7528)
Checks supported languages
- Game.exe (PID: 7680)
- Game_patch-run.exe (PID: 7724)
- Game.exe (PID: 7764)
- identity_helper.exe (PID: 7528)
Create files in a temporary directory
- Game.exe (PID: 7680)
- Game_patch-run.exe (PID: 7724)
Process checks computer location settings
- Game.exe (PID: 7680)
- Game_patch-run.exe (PID: 7724)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8072)
Reads the machine GUID from the registry
- Game.exe (PID: 7764)
Checks proxy server information
- WerFault.exe (PID: 7864)
Creates files or folders in the user directory
- WerFault.exe (PID: 7864)
Creates files in the program directory
- Game_patch-run.exe (PID: 7724)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4220)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7440)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7900)
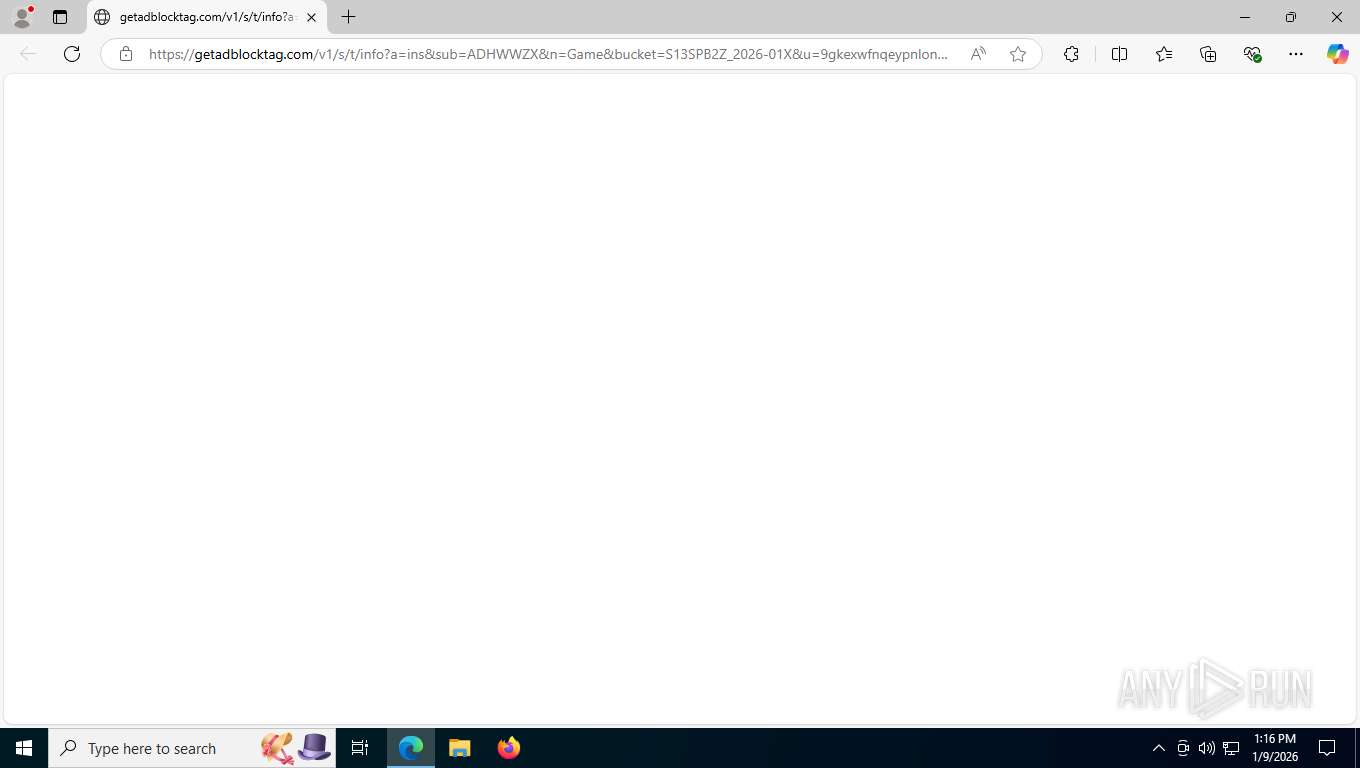
Application launched itself
- msedge.exe (PID: 7184)
- msedge.exe (PID: 7316)
- msedge.exe (PID: 1772)
Manual execution by a user
- msedge.exe (PID: 1772)
Reads Environment values
- identity_helper.exe (PID: 7528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3645 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
191
Monitored processes
42
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2728,i,10055735262416441812,13796709086459051872,262144 --variations-seed-version --mojo-platform-channel-handle=2936 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2120,i,10055735262416441812,13796709086459051872,262144 --variations-seed-version --mojo-platform-channel-handle=2112 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate --single-argument https://getadblocktag.com/v1/s/t/info?a=ins&sub=ADHWWZX&n=Game&bucket=S13SPB2Z_2026-01X&u=9gkexwfnqeypnlonnftxdlsupbxczpcx | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2256 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3844,i,10055735262416441812,13796709086459051872,262144 --variations-seed-version --mojo-platform-channel-handle=4788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2688 | reg.exe import C:\Users\admin\AppData\Local\Temp\temp_cleanup.ico /reg:64 | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3796 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5464,i,10055735262416441812,13796709086459051872,262144 --variations-seed-version --mojo-platform-channel-handle=6076 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4220 | powershell -command "gp 'HKCU:\Control Panel\International\Geo\' | select -exp Name" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4636 | powershell -NoProfile -Command "foreach ($item in @(\"$env:PROGRAMDATA\DiagnosticsNET\configuration.ps1\", \"$env:PROGRAMDATA\DiagnosticsNET\update.vbs\", \"$env:PROGRAMDATA\DiagnosticsNET\updater.vbs\", \"$env:PROGRAMDATA\DiagnosticsNET\cache.ps1\", \"$env:PROGRAMDATA\Features\update.ps1\", \"$env:PROGRAMDATA\UpdatesWin\update.ps1\", \"$env:PROGRAMDATA\UpdatesWin\updater.ps1\", \"$env:PROGRAMDATA\SdkWin\update.ps1\", \"$env:PROGRAMDATA\SdkWin\updater.vbs\", \"$env:PROGRAMDATA\GameSavings\Windows\win_libraries\updater.ps1\", \"$env:PROGRAMDATA\GameSavings\Windows\win_libraries\update.vbs\")) { if (Test-Path -LiteralPath $item) { Remove-Item -LiteralPath $item -Force } }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5628 | powershell -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -File "C:\ProgramData\Features\update.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4292,i,10055735262416441812,13796709086459051872,262144 --variations-seed-version --mojo-platform-channel-handle=4312 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
41 892
Read events
41 862
Write events
27
Delete events
3
Modification events
| (PID) Process: | (7864) WerFault.exe | Key: | \REGISTRY\A\{7d4162bf-d5c2-7a04-4159-8124e97c980e}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (7864) WerFault.exe | Key: | \REGISTRY\A\{7d4162bf-d5c2-7a04-4159-8124e97c980e}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7864) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | ClockTimeSeconds |
Value: D845616900000000 | |||
| (PID) Process: | (7864) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | TickCount |
Value: B2E00F0000000000 | |||
| (PID) Process: | (2688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Provisioning\OMADM\Accounts\FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF |
| Operation: | write | Name: | Flags |
Value: 14089087 | |||
| (PID) Process: | (2688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Provisioning\OMADM\Accounts\FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF |
| Operation: | write | Name: | AcctUId |
Value: 0x000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Provisioning\OMADM\Accounts\FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF |
| Operation: | write | Name: | RoamingCount |
Value: 0 | |||
| (PID) Process: | (2688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Provisioning\OMADM\Accounts\FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF |
| Operation: | write | Name: | SslClientCertReference |
Value: MY;User;0000000000000000000000000000000000000000 | |||
| (PID) Process: | (2688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Provisioning\OMADM\Accounts\FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF |
| Operation: | write | Name: | ProtoVer |
Value: 1.2 | |||
| (PID) Process: | (2688) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Enrollments\FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF |
| Operation: | write | Name: | EnrollmentState |
Value: 1 | |||
Executable files
10
Suspicious files
109
Text files
353
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7864 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Game.exe_e6159ebf926c70ee51b3becda91393bfb8c3a_ec47739b_286b9ea1-9ac1-468c-8fd8-824eb045deb1\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7864 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Game.exe.7764.dmp | — | |
MD5:— | SHA256:— | |||
| 7680 | Game.exe | C:\Users\admin\AppData\Local\Temp\Game_patch-run.exe | executable | |
MD5:CA4069130468D93AC7C719BF89F792C8 | SHA256:54D788B1AF6BA0343256E528AADFAAE30E2AD214E7A6915DC08F0DDDC23B2F2C | |||
| 7680 | Game.exe | C:\Users\admin\AppData\Local\Temp\nsyD99F.tmp | binary | |
MD5:820164D4CDBD8BE368E87292FF9D398D | SHA256:107B4BA5CE9EC284D7CEC1ECF22EF9C489F33E738F72B5A59F46767663C2321B | |||
| 7724 | Game_patch-run.exe | C:\Users\admin\AppData\Local\Temp\Game.exe | executable | |
MD5:C2F26DCF03CE79D120884CB0EC4B8090 | SHA256:8A191BE25D13DDC8EDB54BA5FBD8D19B9F2CC6D7EE6471190C8E641C88189C2B | |||
| 7864 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:C1F26312267DEA40606400FA6885B253 | SHA256:7C140BF547D0F668A34674105144CAE4033E2A722CA8E3047C2DC67700C86098 | |||
| 7864 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDFA9.tmp.WERInternalMetadata.xml | xml | |
MD5:E70A6120A2BF83DABFF6A68FFB204068 | SHA256:C93718A8DF60E531297D0E5856CDC8A01BC5A942007C6FA68744DC41E31178F5 | |||
| 7864 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDF1C.tmp.dmp | binary | |
MD5:65E1EB3FA2158173FED5CF1B089CA813 | SHA256:AC0AEF179E9C3B2D9FB3D462D88CFDF642ED025A7CDA563F125A24A5DBC779F2 | |||
| 7864 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERDFCA.tmp.xml | xml | |
MD5:3E5E9BBBF954BC06BCD39BB10963F78A | SHA256:4B3CDB460B09519CA9E2AF94EEDCE4736C2F2562A31DCB39CEE7B8F254CD8EBD | |||
| 7864 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:05DDF56FC804F432398703E32AF90A79 | SHA256:7193D01CF9580401784B76B581FABC0D63B97D49977EDD15370DF6967EF2F443 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
122
TCP/UDP connections
77
DNS requests
66
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=1&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
7864 | WerFault.exe | POST | 200 | 135.233.45.221:443 | https://watson.events.data.microsoft.com/Telemetry.Request | unknown | xml | 685 b | whitelisted |
4344 | svchost.exe | POST | 200 | 20.190.159.0:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
816 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 29.1 Kb | whitelisted |
816 | SIHClient.exe | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
4344 | svchost.exe | POST | 200 | 20.190.159.0:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
3368 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=1&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | text | 1.43 Kb | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | text | 34.1 Kb | whitelisted |
816 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3796 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7864 | WerFault.exe | 135.233.45.221:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7864 | WerFault.exe | 2.16.168.124:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7864 | WerFault.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4344 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
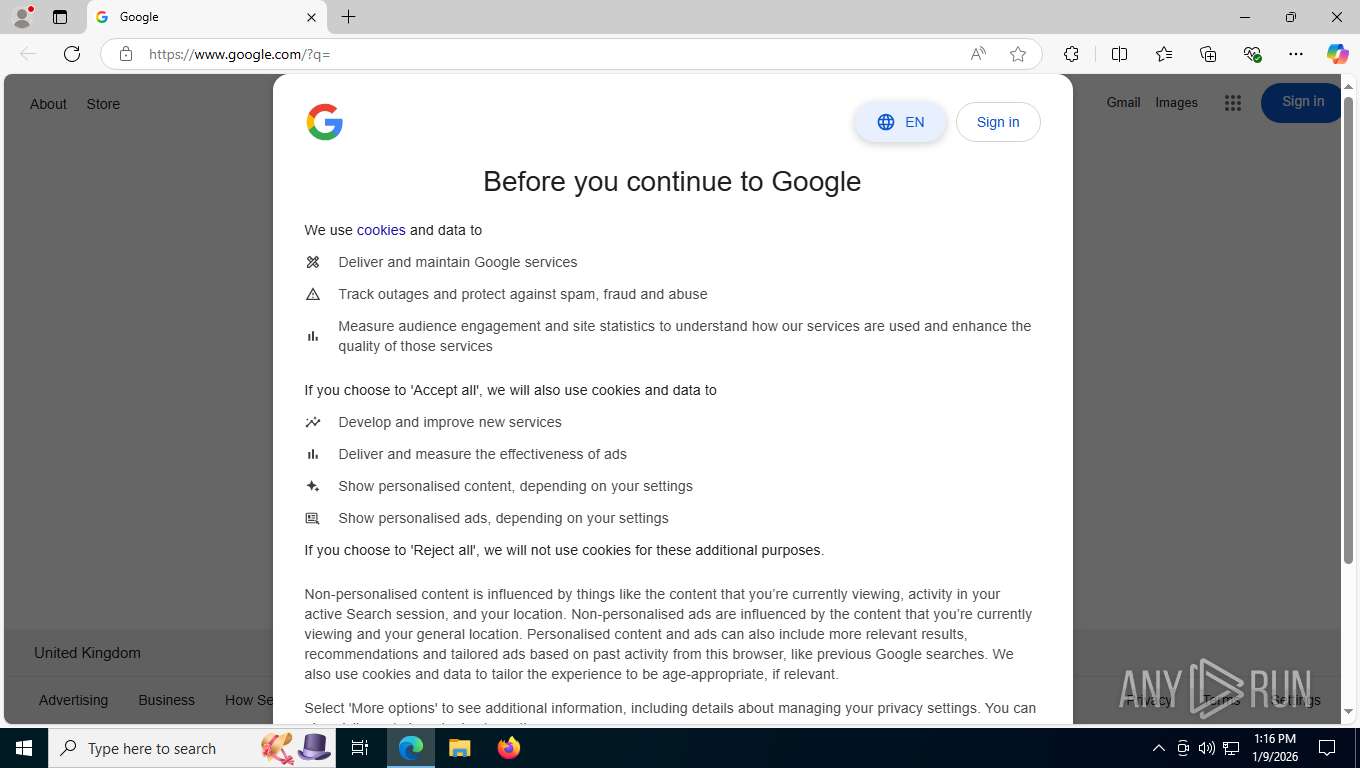
google.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |