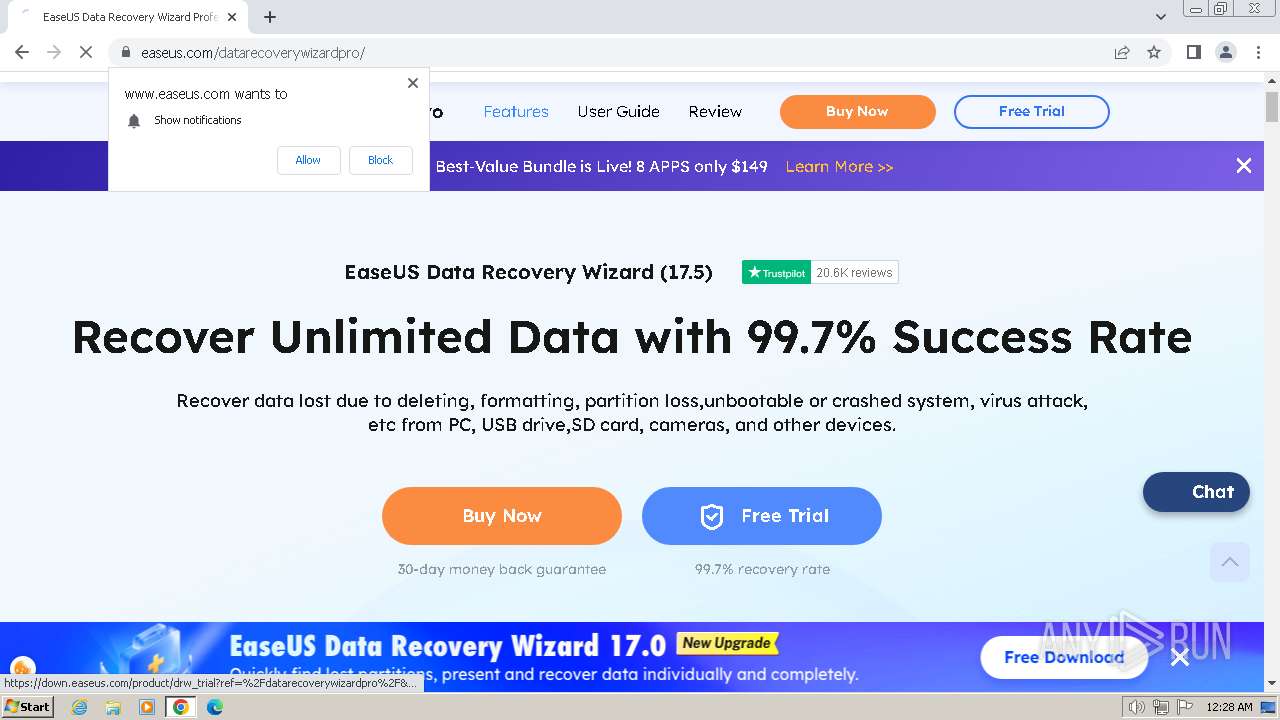
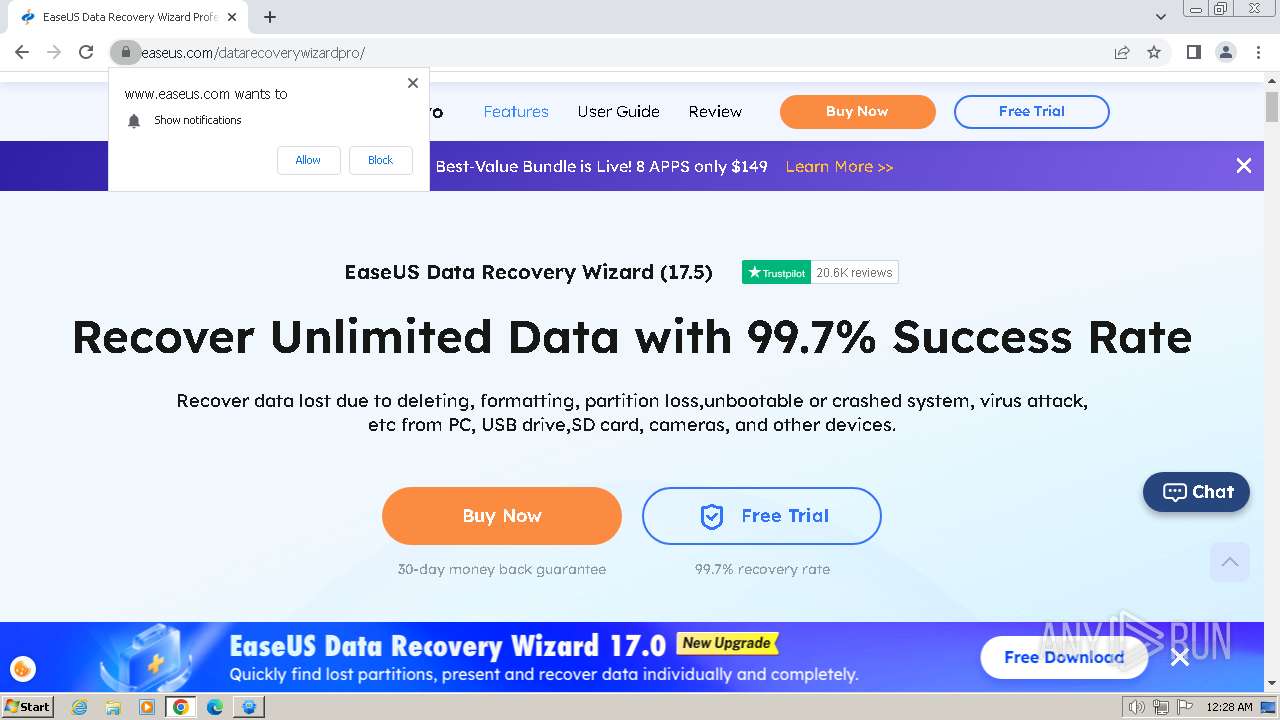
| URL: | https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwi_s6G__NaFAxVA7jgGHYD_AvwQFnoECAcQAQ&url=https%3A%2F%2Fwww.easeus.com%2F&usg=AOvVaw3twRFJ9PTMaw6bhrwvqfeR&opi=89978449 |
| Full analysis: | https://app.any.run/tasks/7bef365b-be13-40c1-b33e-30fc54b70fa6 |
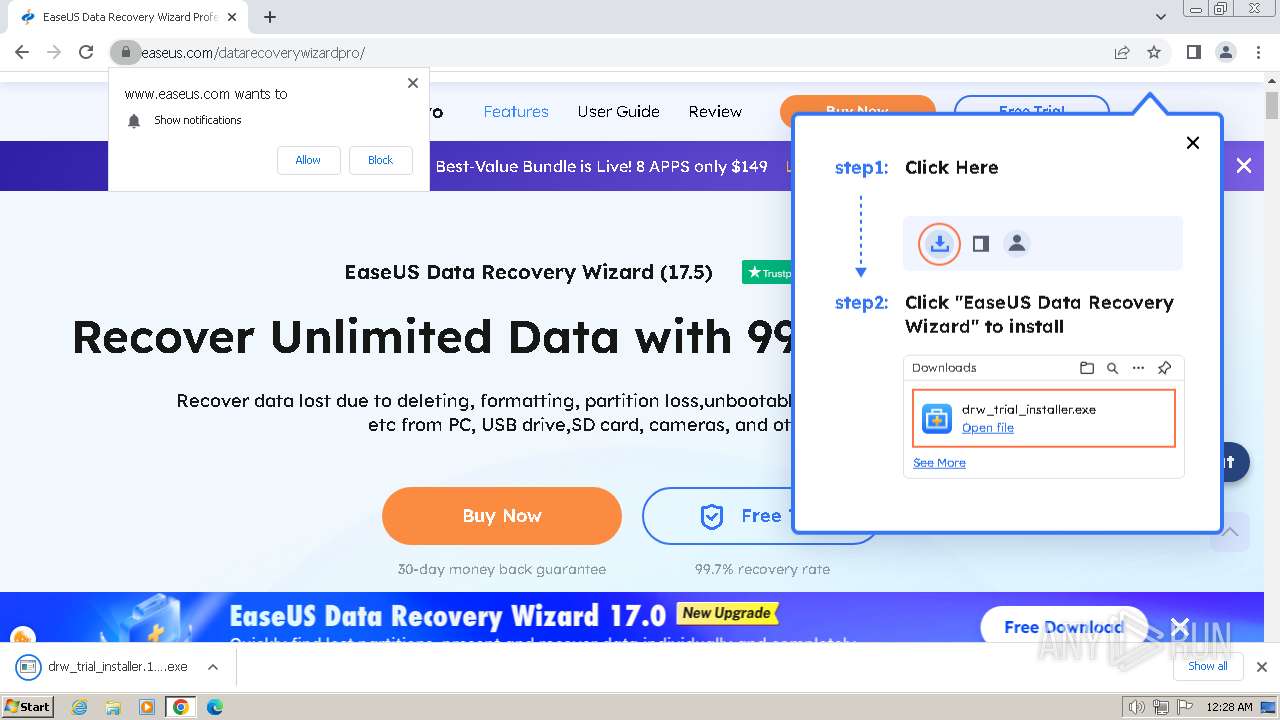
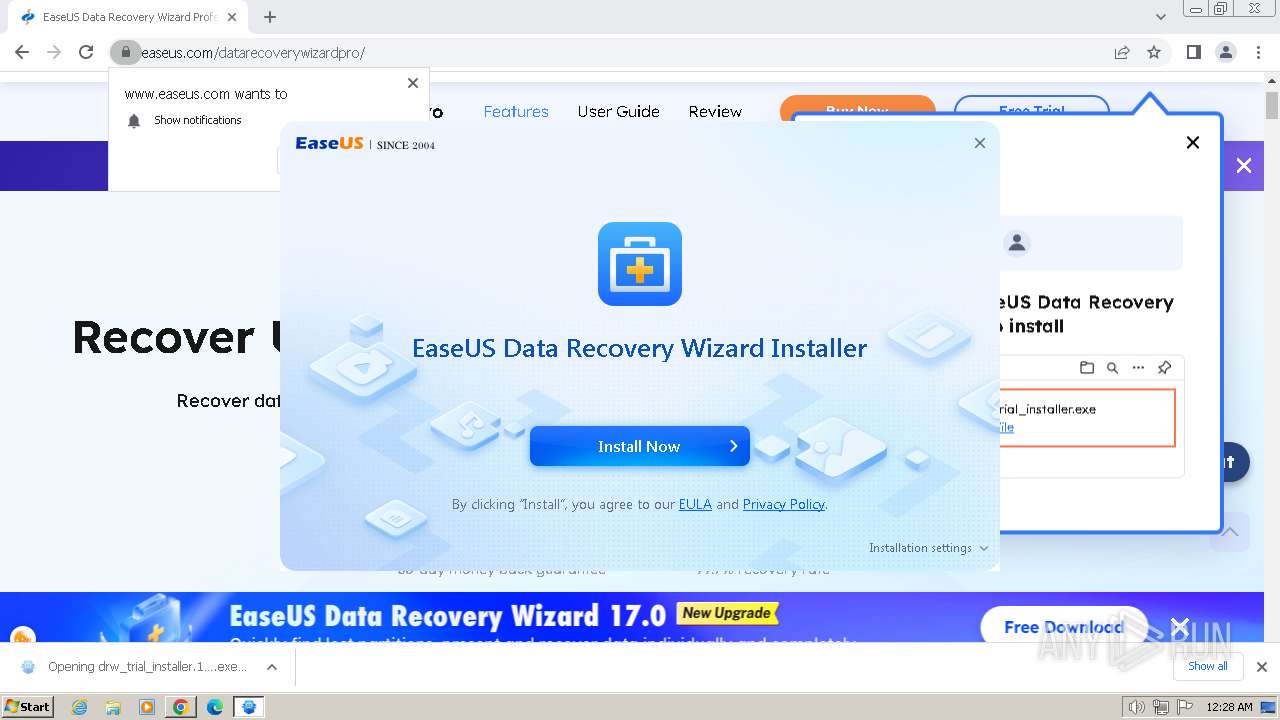
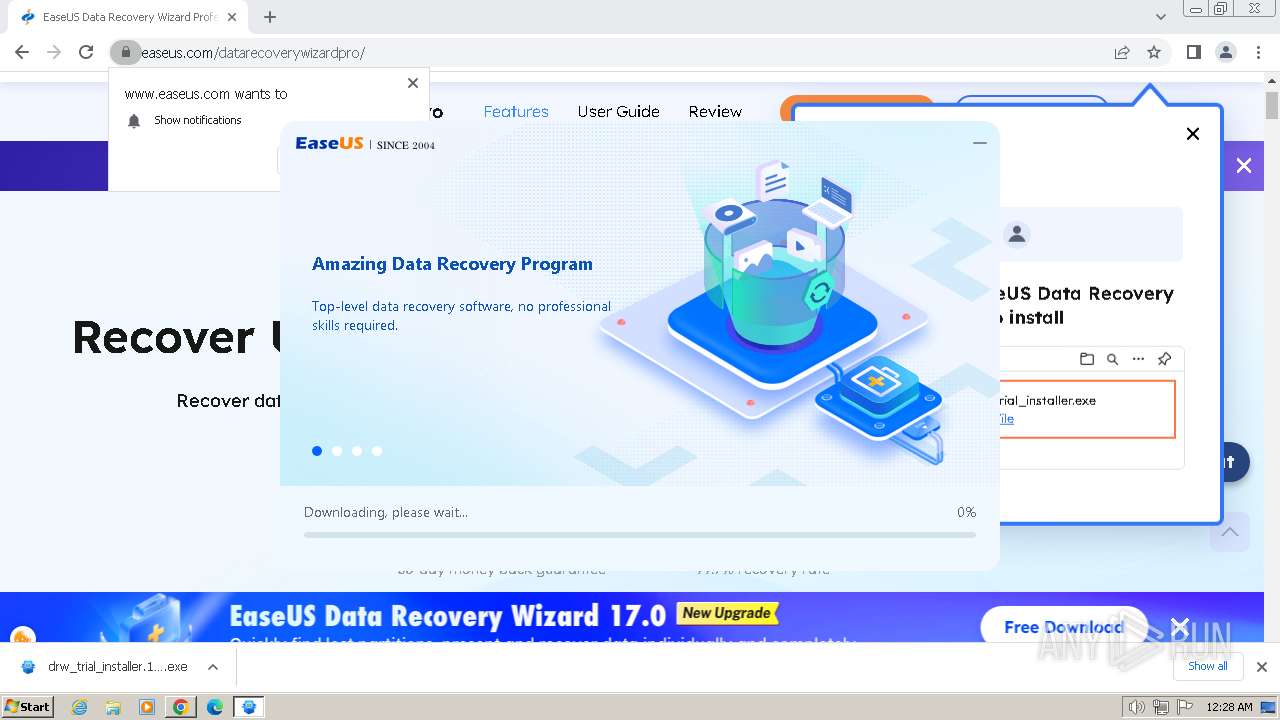
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2024, 23:27:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 80FED78E92919A8C9DCA23DE8067761F |
| SHA1: | AD46FA37C8244378D1D9F6F0E236A2DE4785485B |
| SHA256: | 54AEFAAF1A009AC02C895CB4047C6A7E9E985571C9F5DA541D68E28E26383D0B |
| SSDEEP: | 6:2OLI2sq+wp1w4pNbR2FCXJYNRR3zbFSdj7Rya:2V2JnNlRJY5Fo |
MALICIOUS
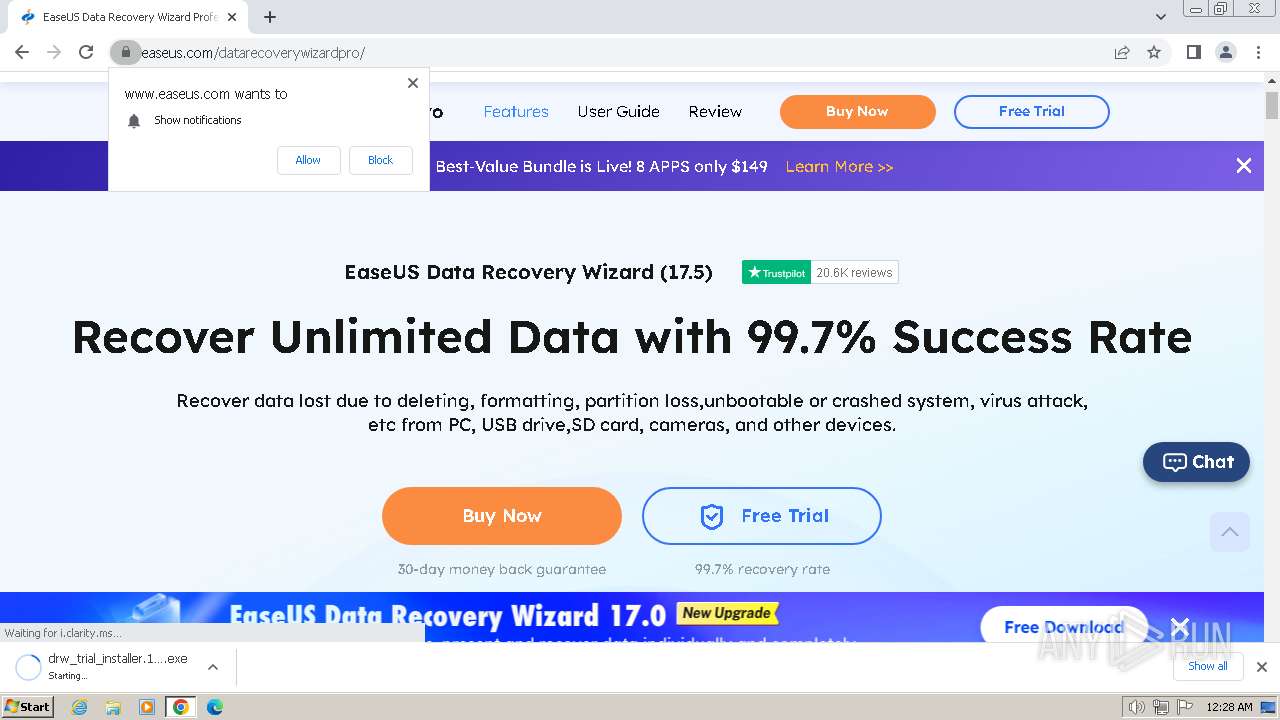
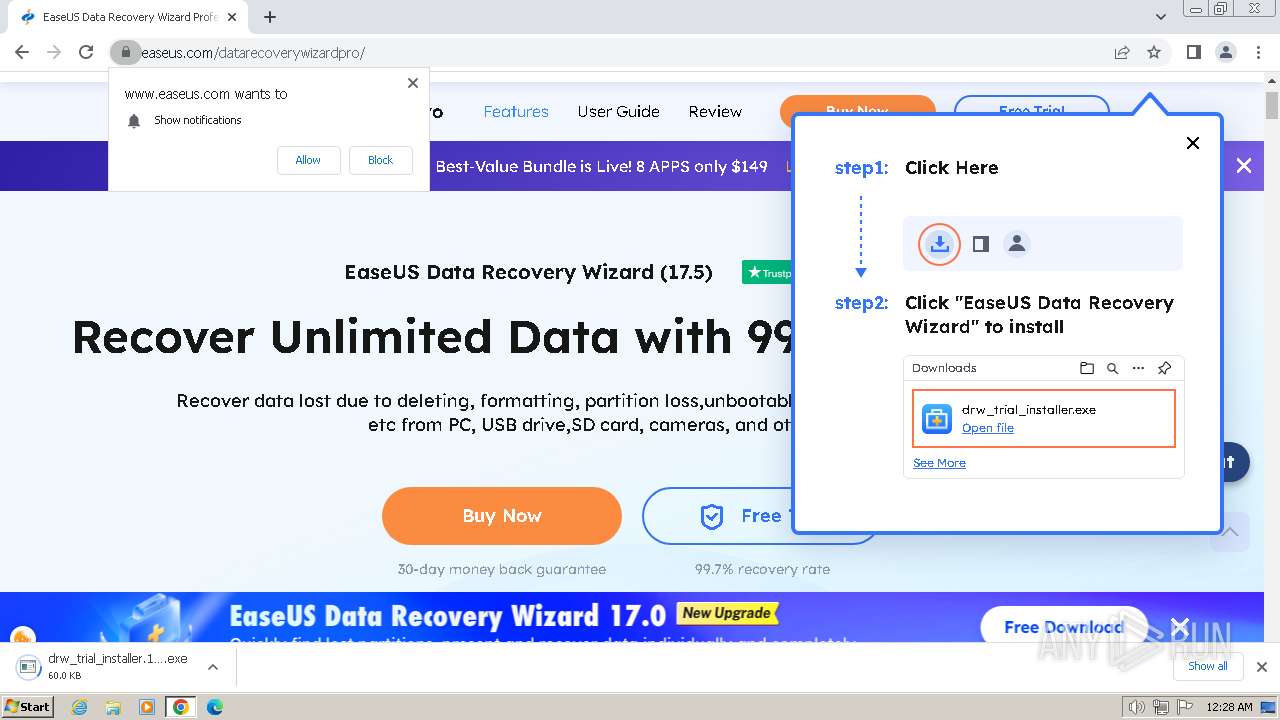
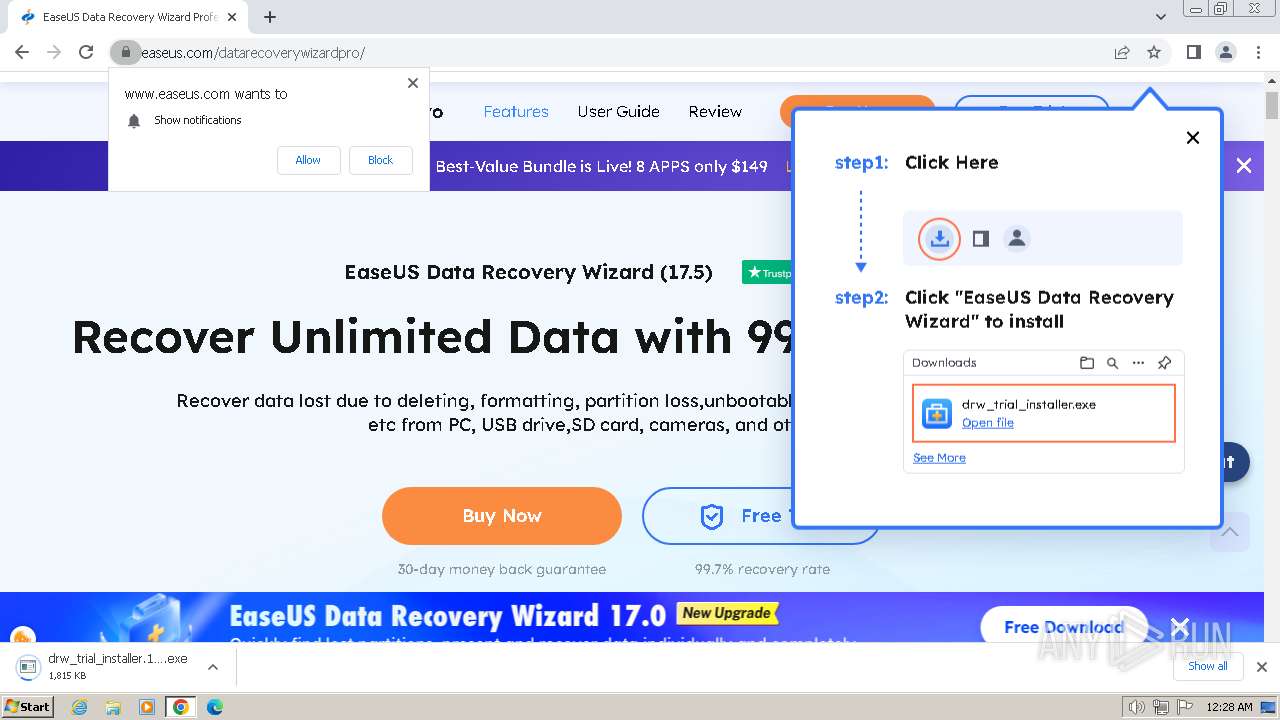
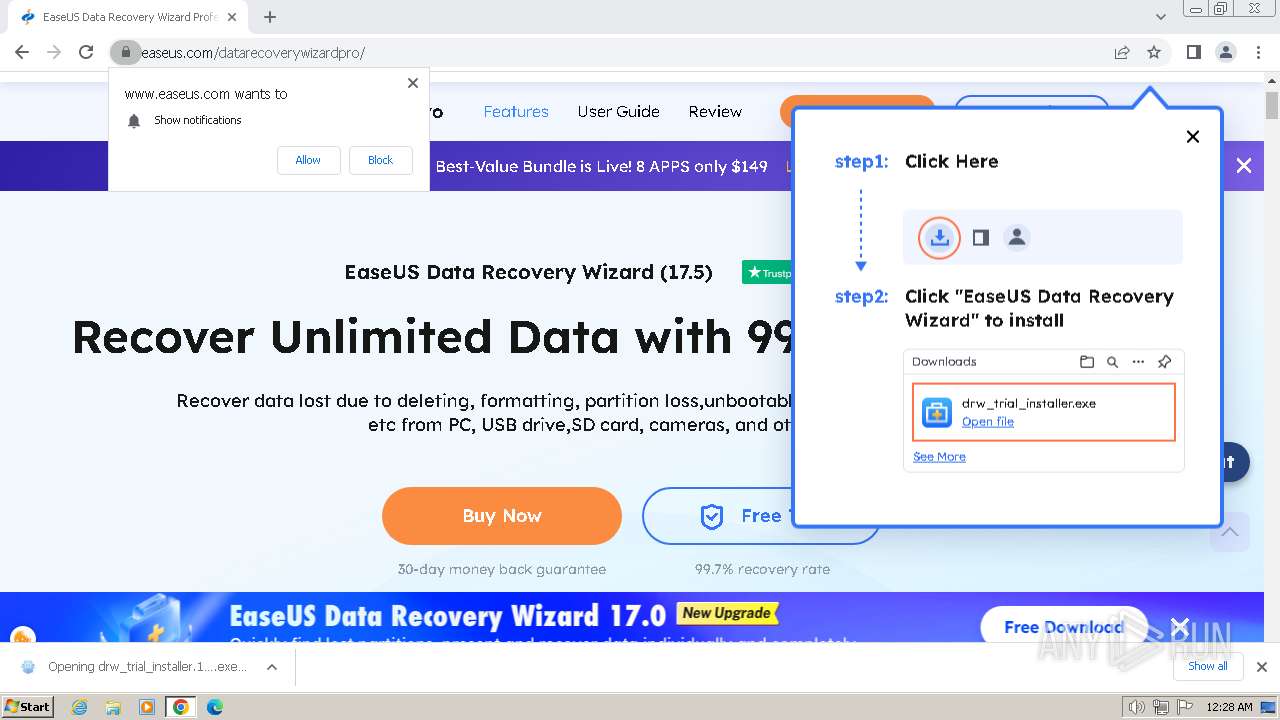
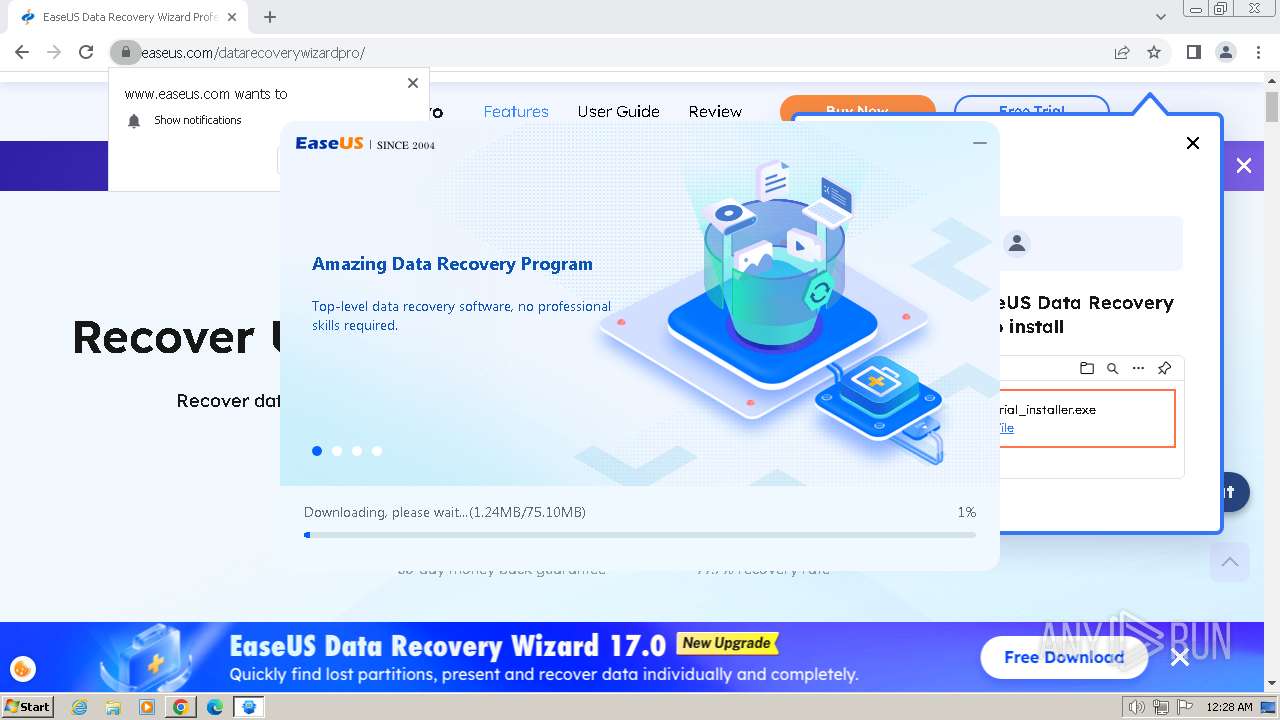
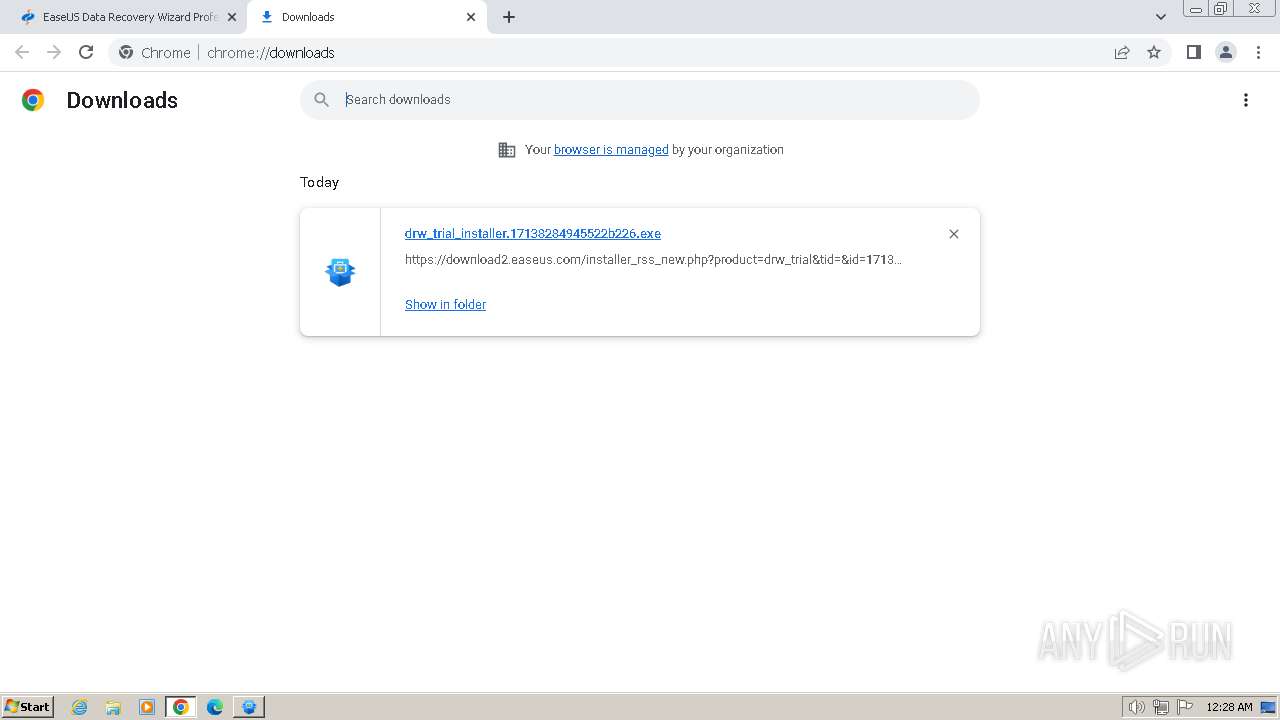
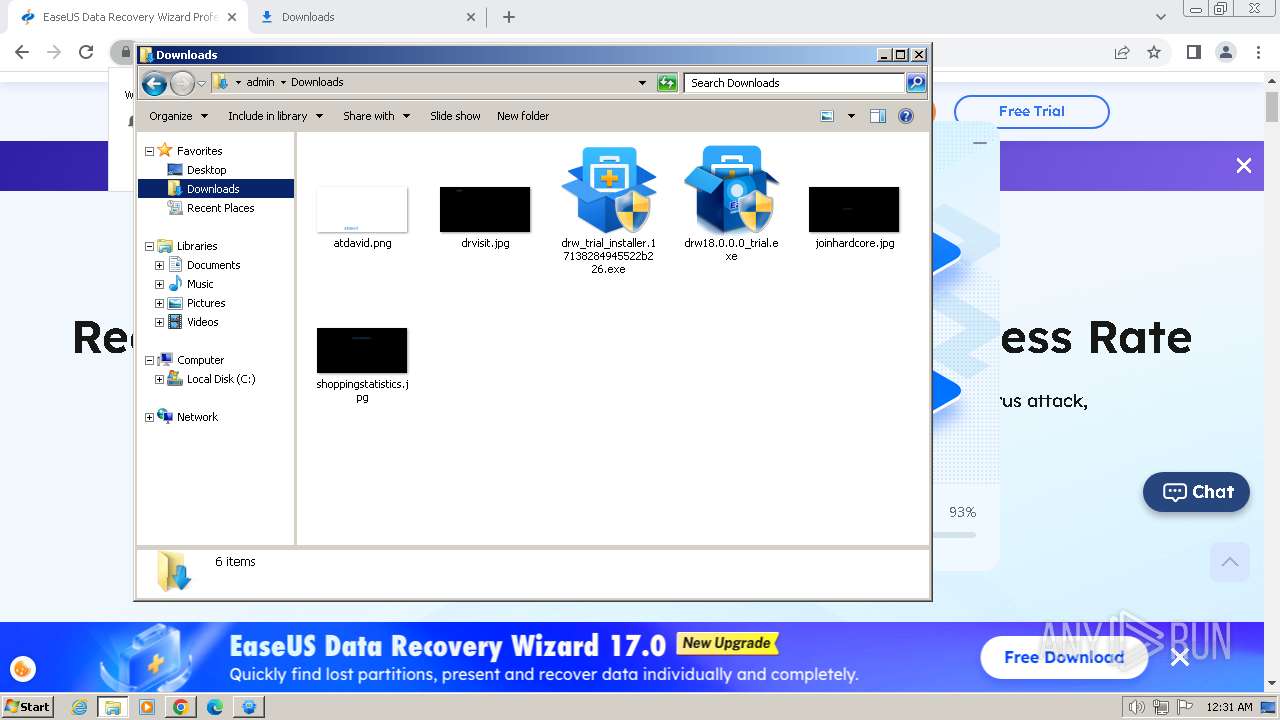
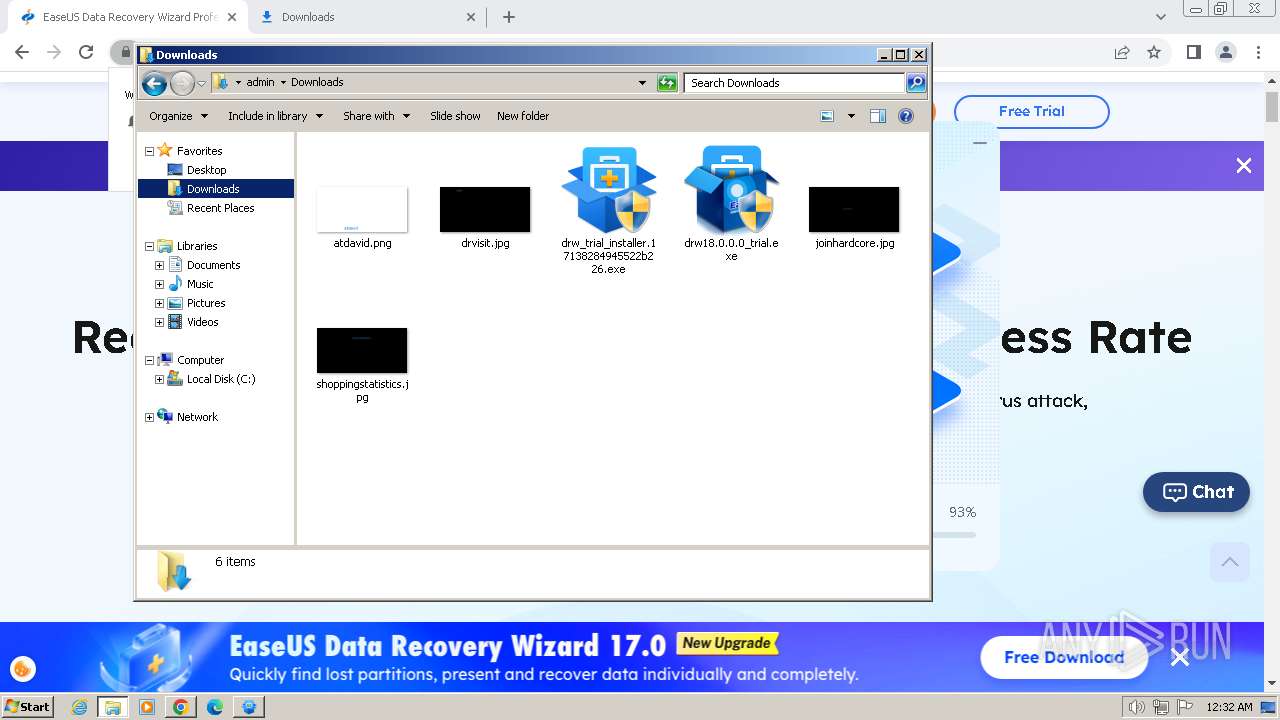
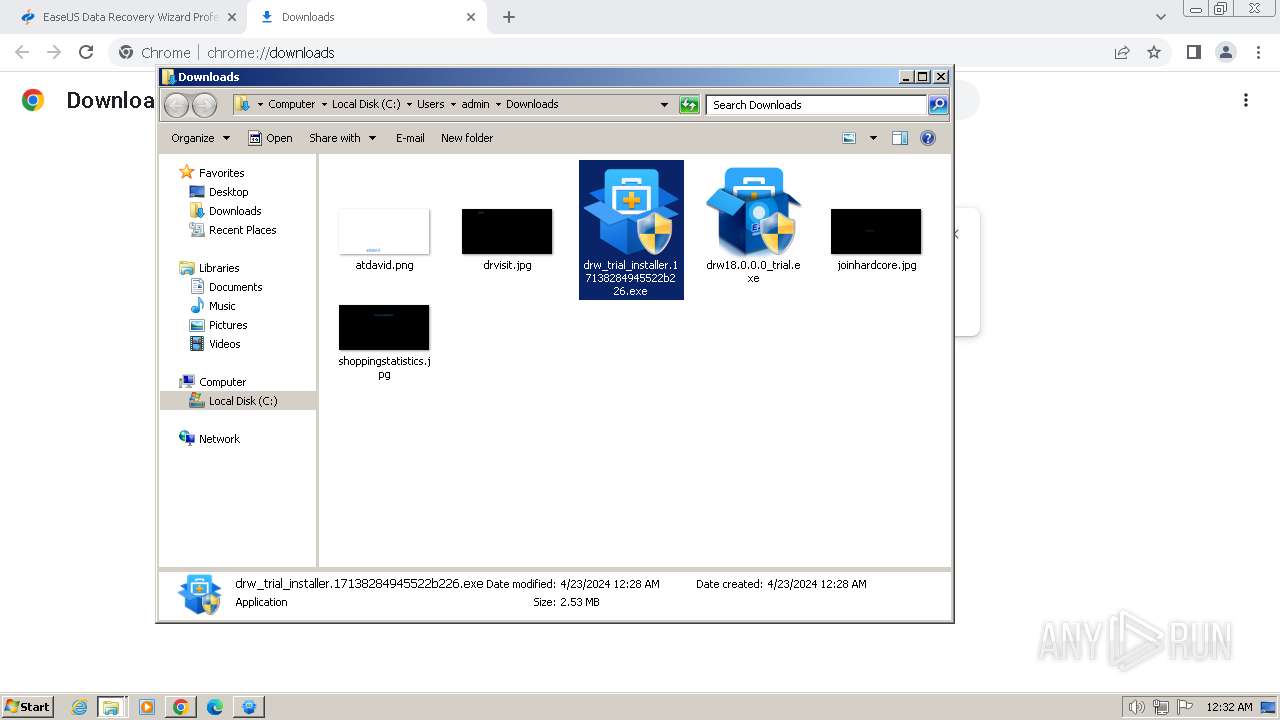
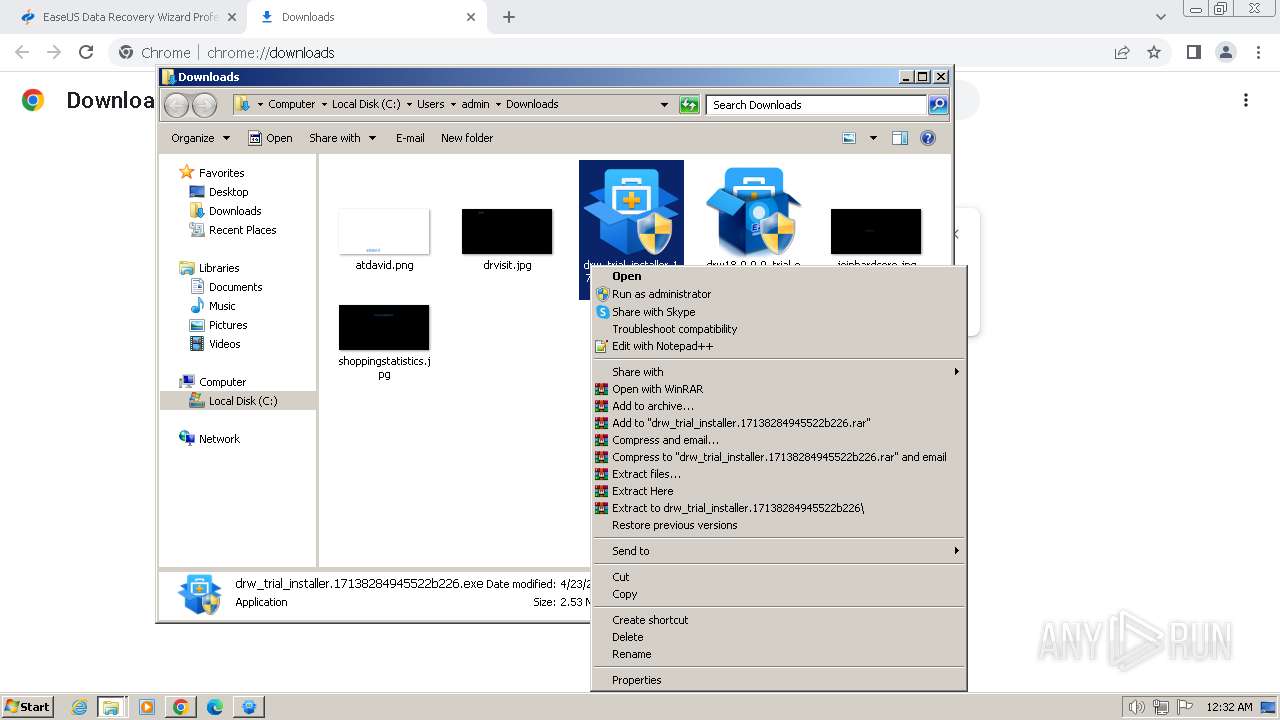
Drops the executable file immediately after the start
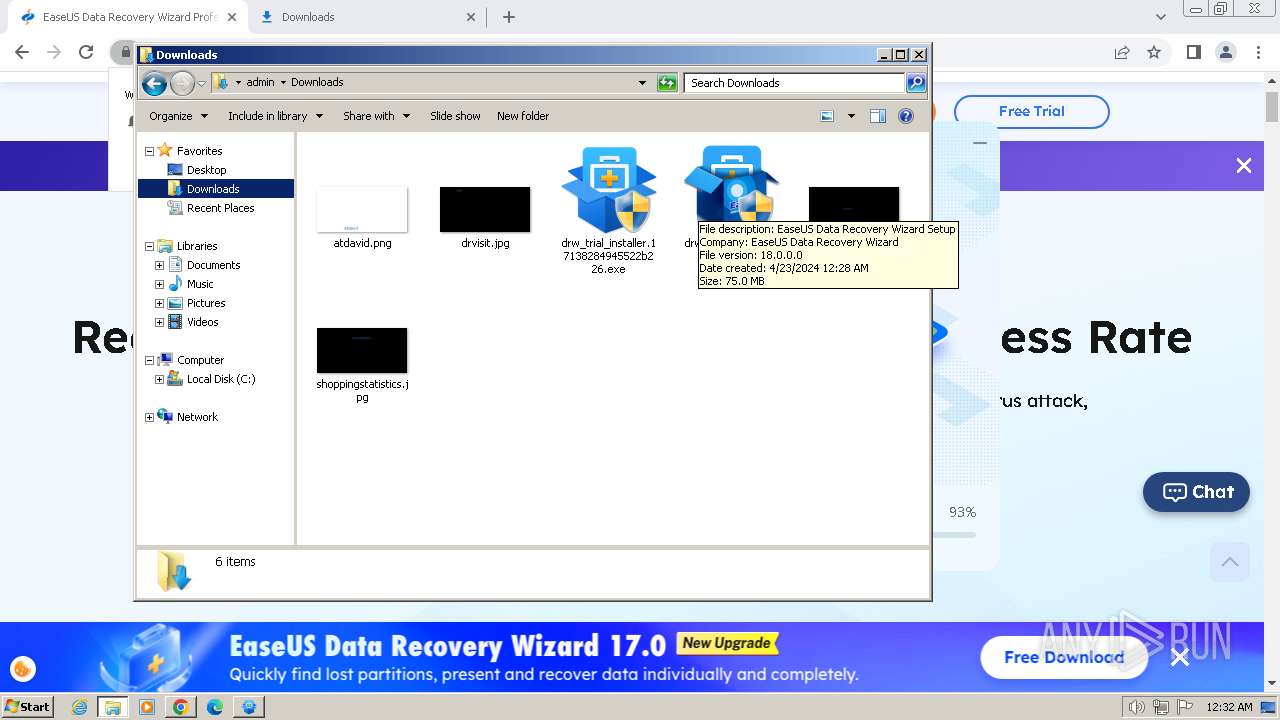
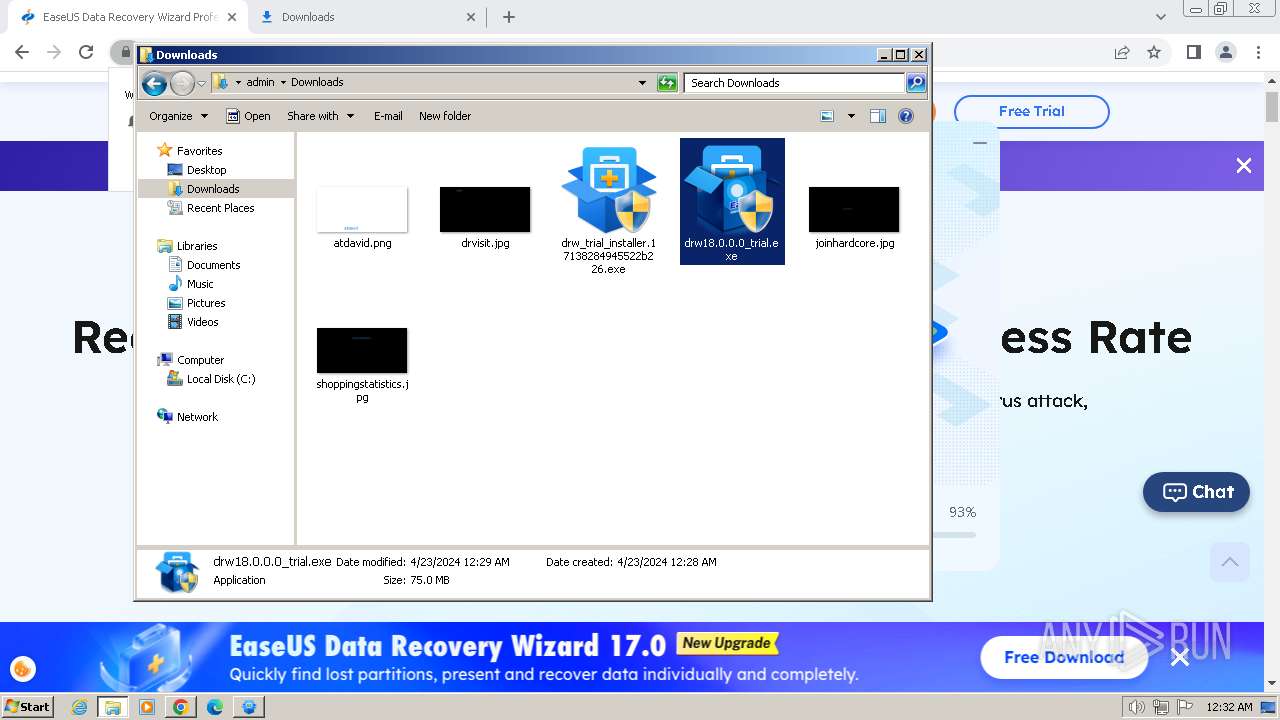
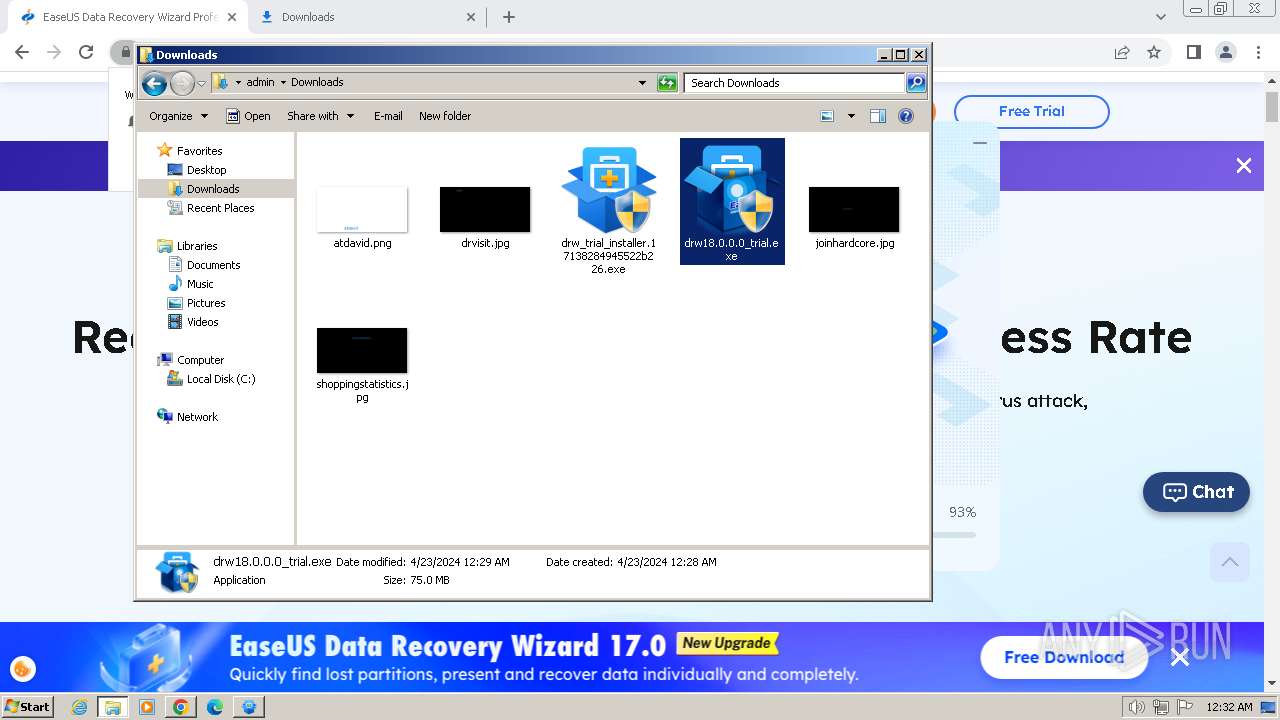
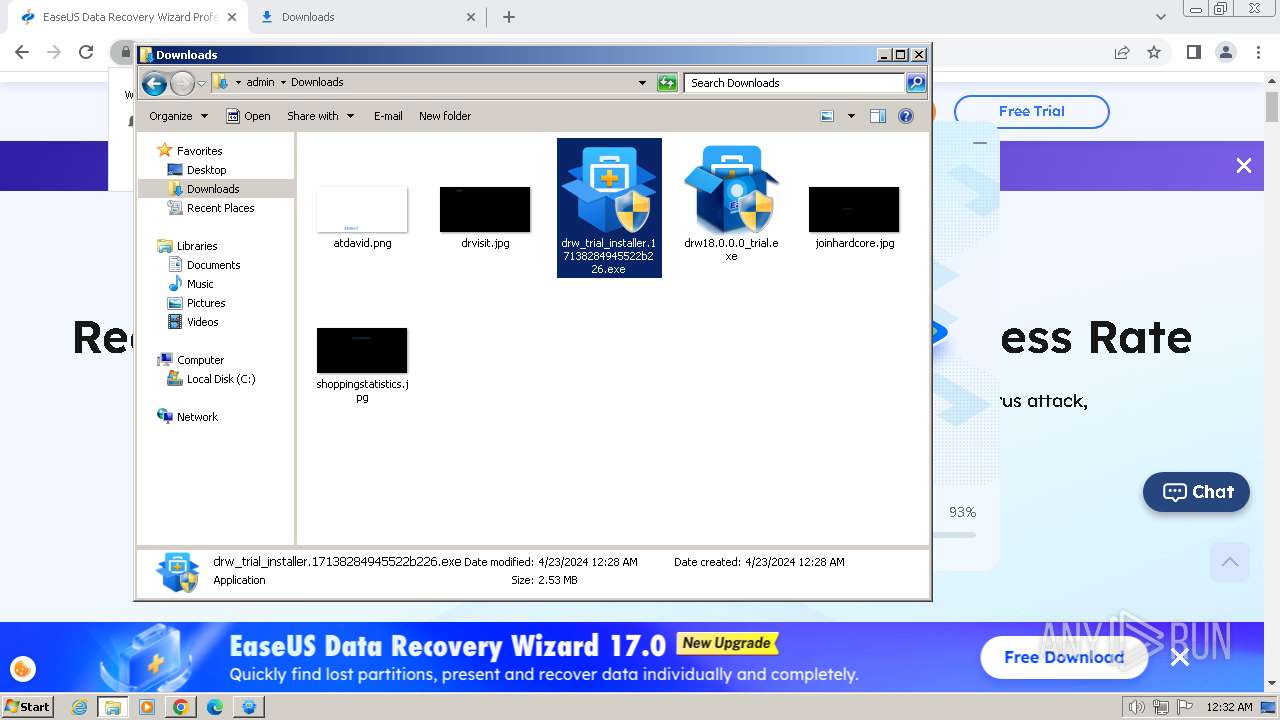
- drw_trial_installer.17138284945522b226.exe (PID: 1336)
- drw18.0.0.0_trial.exe (PID: 1832)
- drw18.0.0.0_trial.tmp (PID: 2488)
SUSPICIOUS
Executable content was dropped or overwritten
- drw_trial_installer.17138284945522b226.exe (PID: 1336)
- drw18.0.0.0_trial.exe (PID: 1832)
- drw18.0.0.0_trial.tmp (PID: 2488)
Reads the Internet Settings
- AliyunWrapExe.Exe (PID: 2860)
- EDownloader.exe (PID: 3980)
- AliyunWrapExe.Exe (PID: 3852)
Reads security settings of Internet Explorer
- AliyunWrapExe.Exe (PID: 2860)
- EDownloader.exe (PID: 3980)
- AliyunWrapExe.Exe (PID: 3852)
Reads Microsoft Outlook installation path
- EDownloader.exe (PID: 3980)
Reads Internet Explorer settings
- EDownloader.exe (PID: 3980)
Reads the Windows owner or organization settings
- drw18.0.0.0_trial.tmp (PID: 2488)
Process drops legitimate windows executable
- drw18.0.0.0_trial.tmp (PID: 2488)
The process drops C-runtime libraries
- drw18.0.0.0_trial.tmp (PID: 2488)
INFO
Drops the executable file immediately after the start
- chrome.exe (PID: 1288)
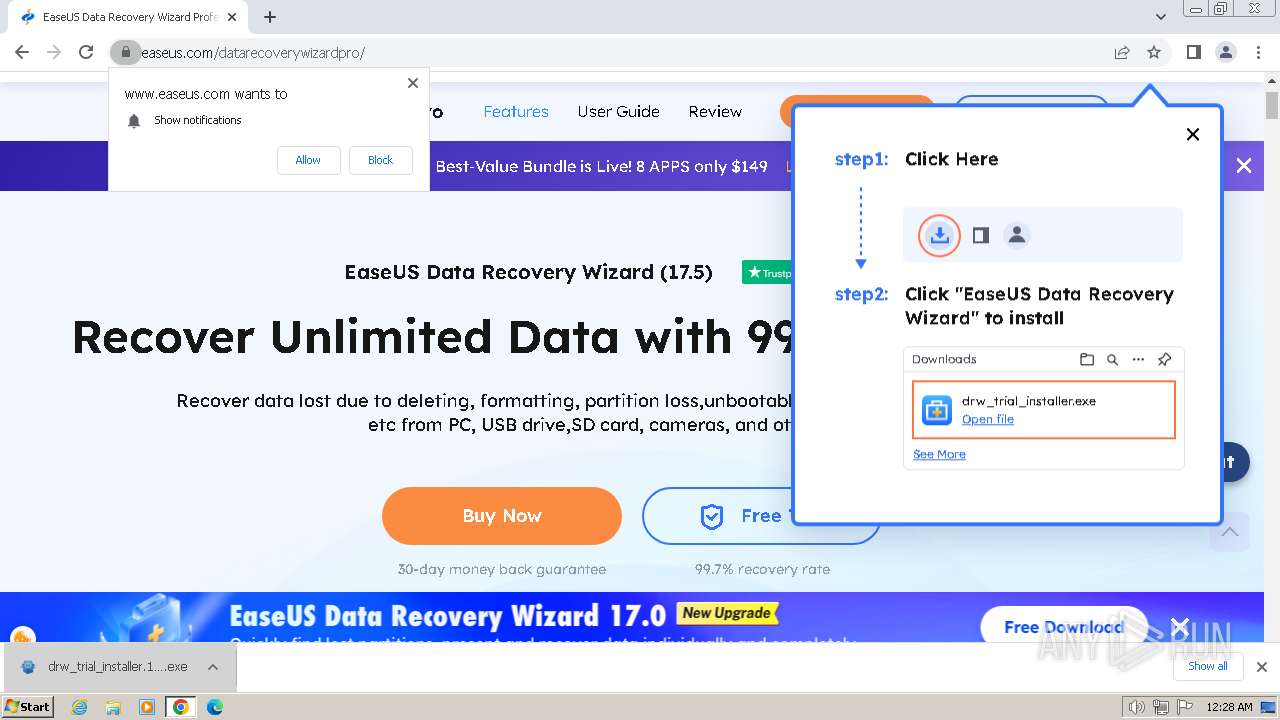
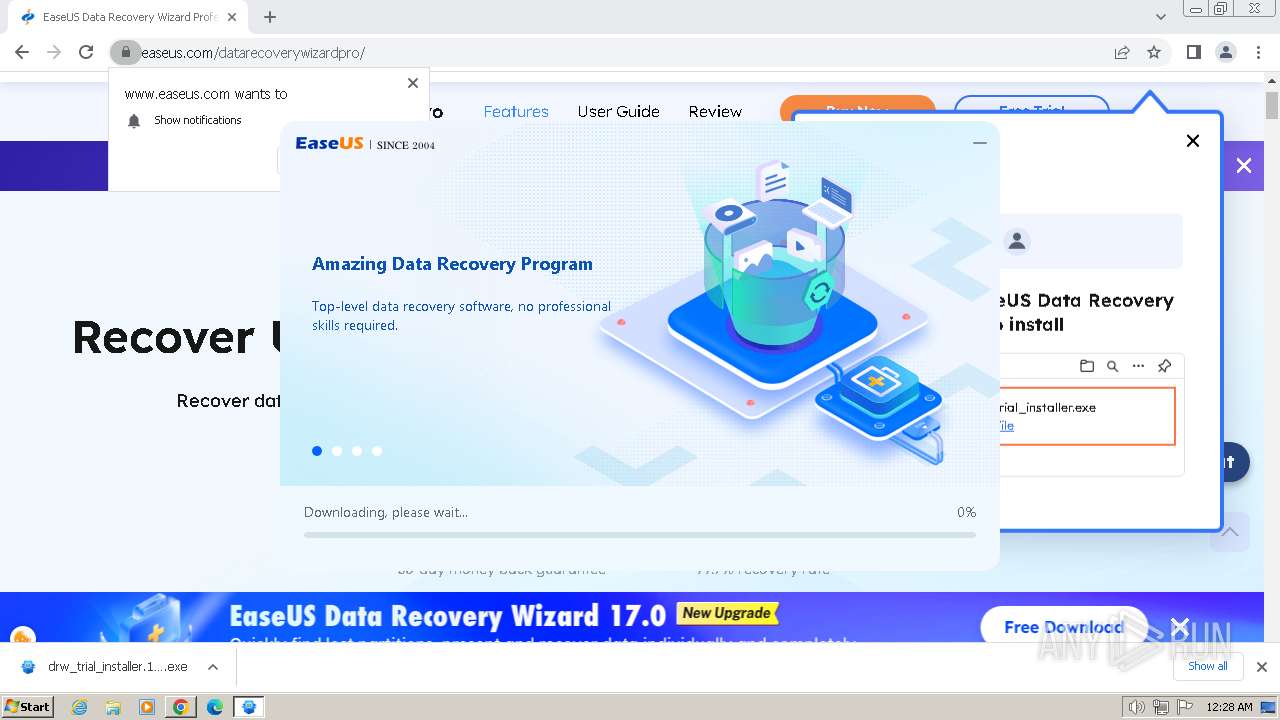
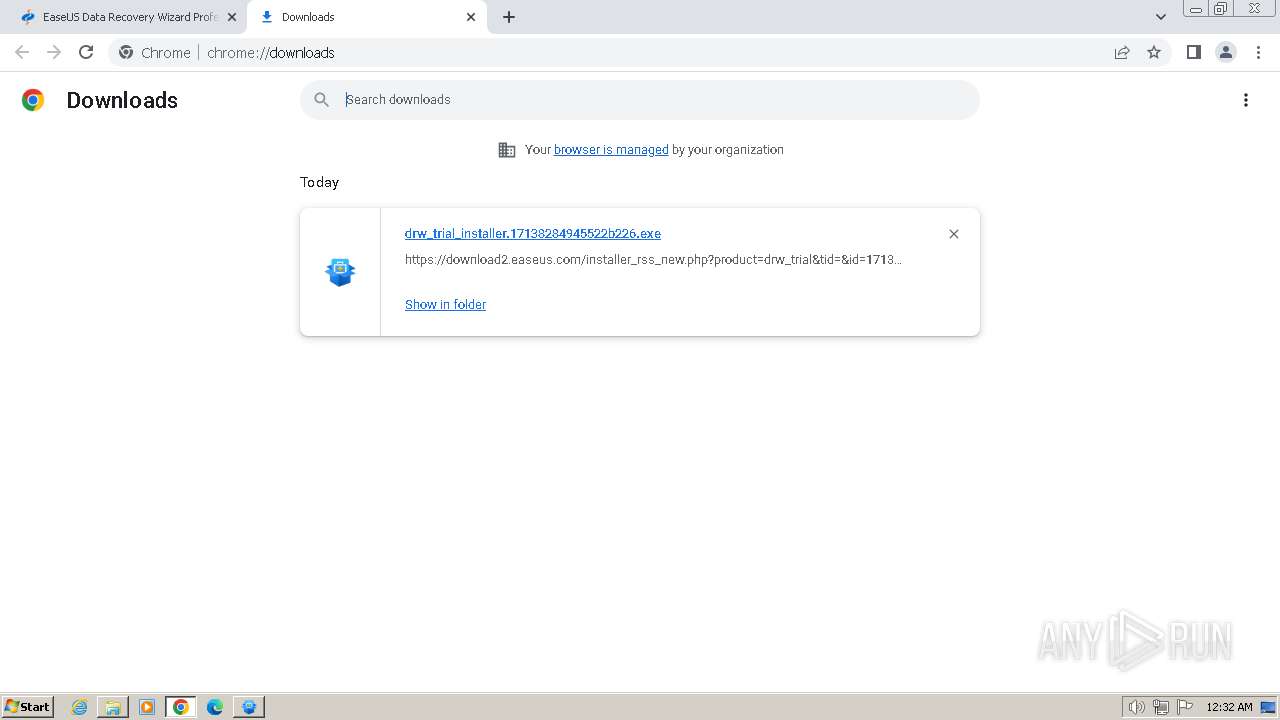
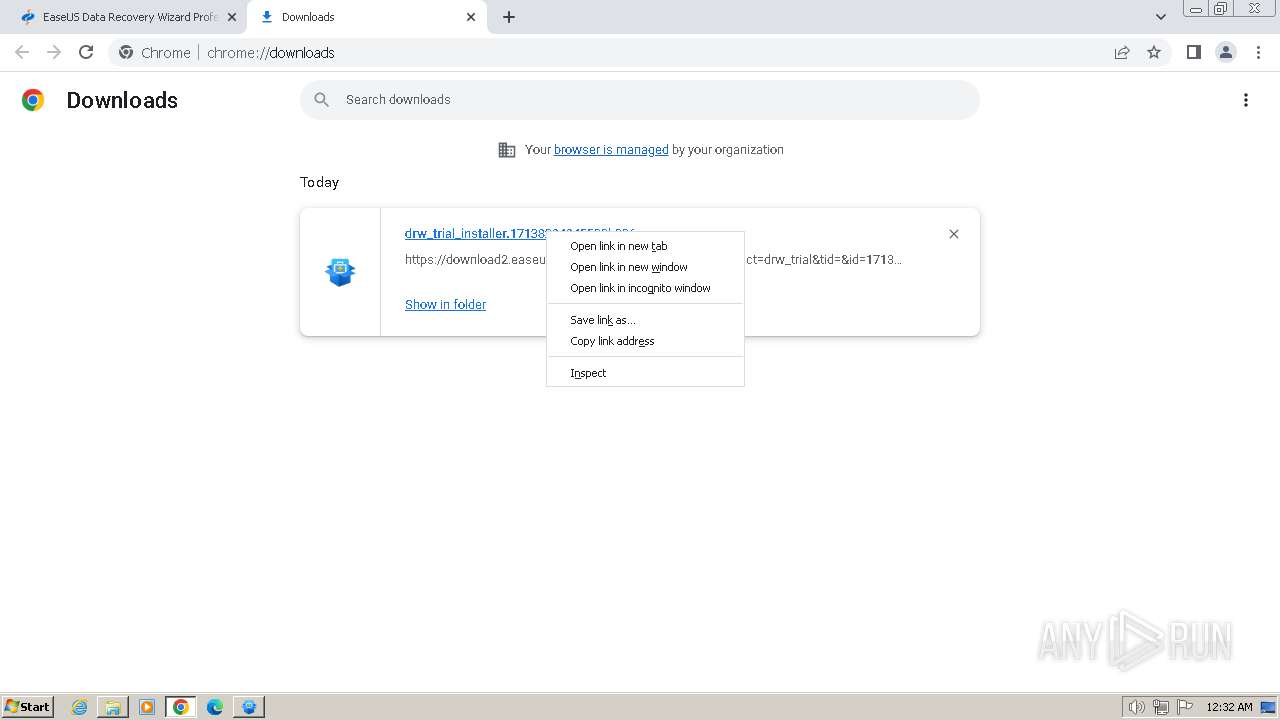
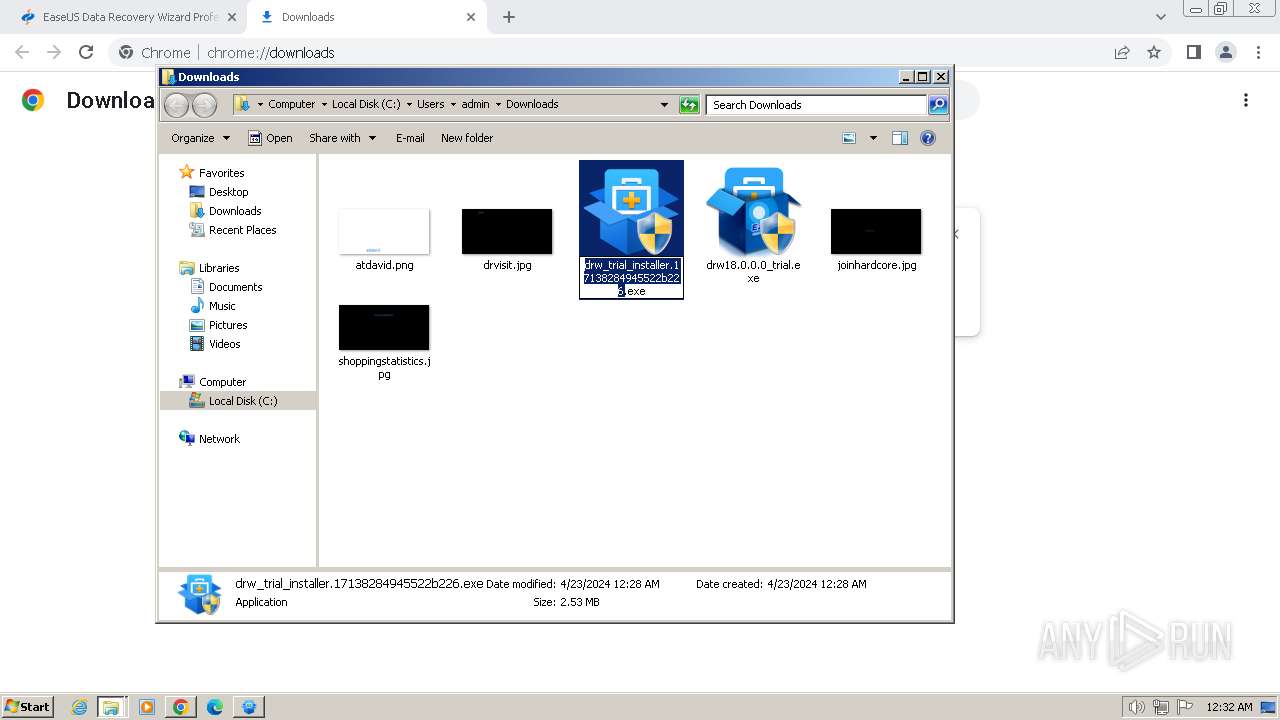
The process uses the downloaded file
- chrome.exe (PID: 1956)
- chrome.exe (PID: 1288)
Reads the computer name
- drw_trial_installer.17138284945522b226.exe (PID: 1336)
- EDownloader.exe (PID: 3980)
- AliyunWrapExe.Exe (PID: 2860)
- drw18.0.0.0_trial.tmp (PID: 2488)
- AliyunWrapExe.Exe (PID: 3852)
Checks supported languages
- InfoForSetup.exe (PID: 1972)
- AliyunWrapExe.Exe (PID: 2860)
- drw_trial_installer.17138284945522b226.exe (PID: 1336)
- EDownloader.exe (PID: 3980)
- InfoForSetup.exe (PID: 3680)
- InfoForSetup.exe (PID: 4052)
- InfoForSetup.exe (PID: 1848)
- InfoForSetup.exe (PID: 3432)
- InfoForSetup.exe (PID: 2056)
- InfoForSetup.exe (PID: 1124)
- InfoForSetup.exe (PID: 3300)
- drw18.0.0.0_trial.exe (PID: 1832)
- drw18.0.0.0_trial.tmp (PID: 2488)
- AliyunWrapExe.Exe (PID: 3852)
- InfoForSetup.exe (PID: 3668)
- InfoForSetup.exe (PID: 2000)
- InfoForSetup.exe (PID: 1232)
- InfoForSetup.exe (PID: 4060)
Executable content was dropped or overwritten
- chrome.exe (PID: 1288)
Create files in a temporary directory
- drw_trial_installer.17138284945522b226.exe (PID: 1336)
- EDownloader.exe (PID: 3980)
- InfoForSetup.exe (PID: 1972)
- AliyunWrapExe.Exe (PID: 2860)
- drw18.0.0.0_trial.exe (PID: 1832)
- drw18.0.0.0_trial.tmp (PID: 2488)
- AliyunWrapExe.Exe (PID: 3852)
Checks proxy server information
- AliyunWrapExe.Exe (PID: 2860)
- EDownloader.exe (PID: 3980)
- AliyunWrapExe.Exe (PID: 3852)
Application launched itself
- chrome.exe (PID: 1288)
Reads the machine GUID from the registry
- AliyunWrapExe.Exe (PID: 2860)
- EDownloader.exe (PID: 3980)
- AliyunWrapExe.Exe (PID: 3852)
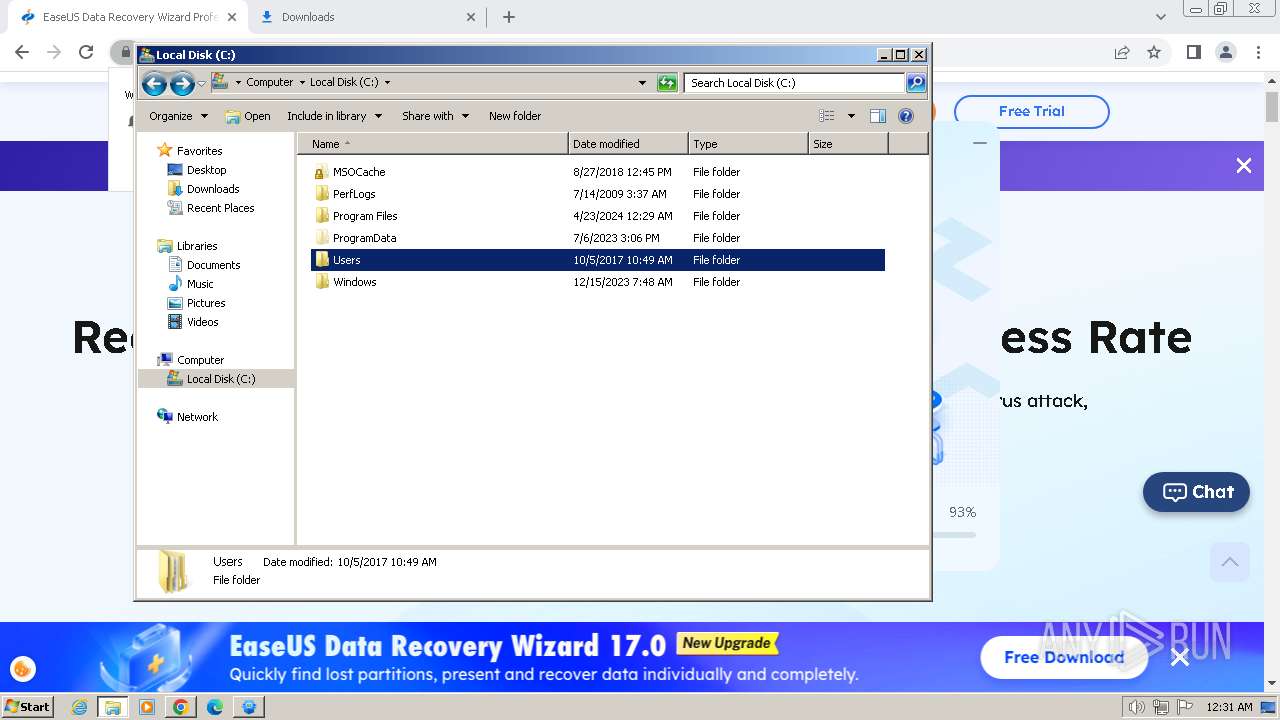
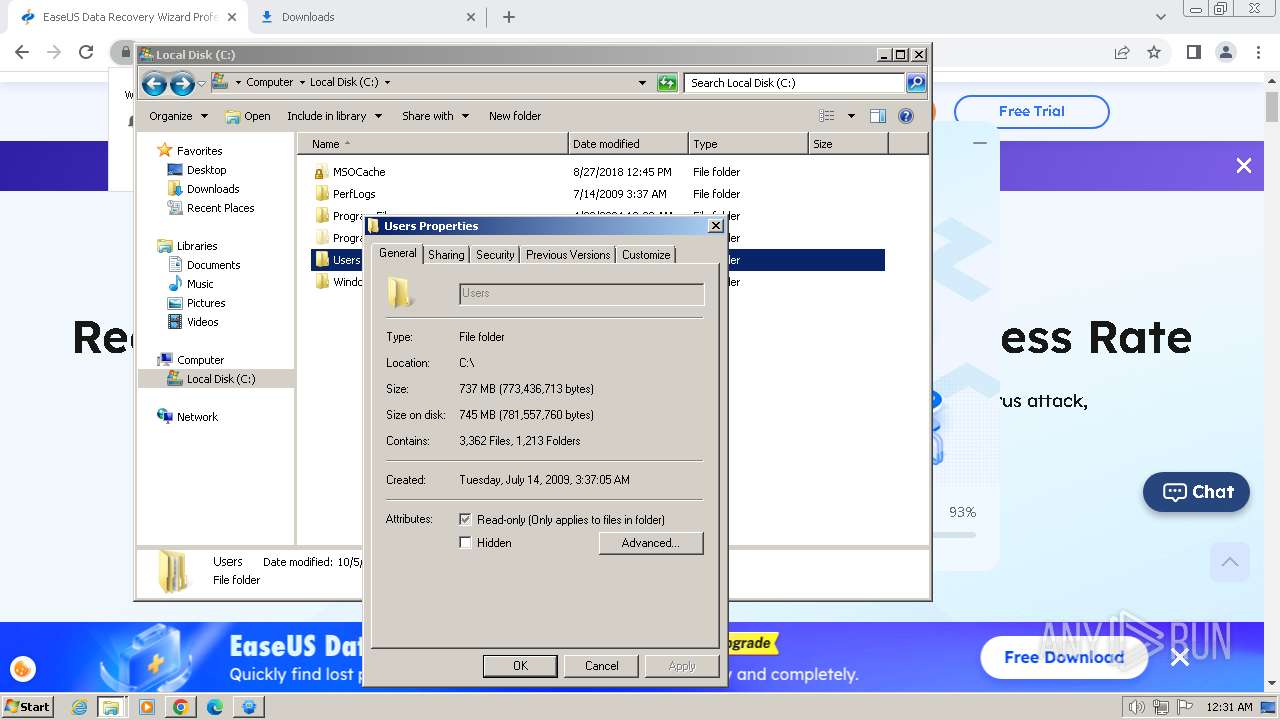
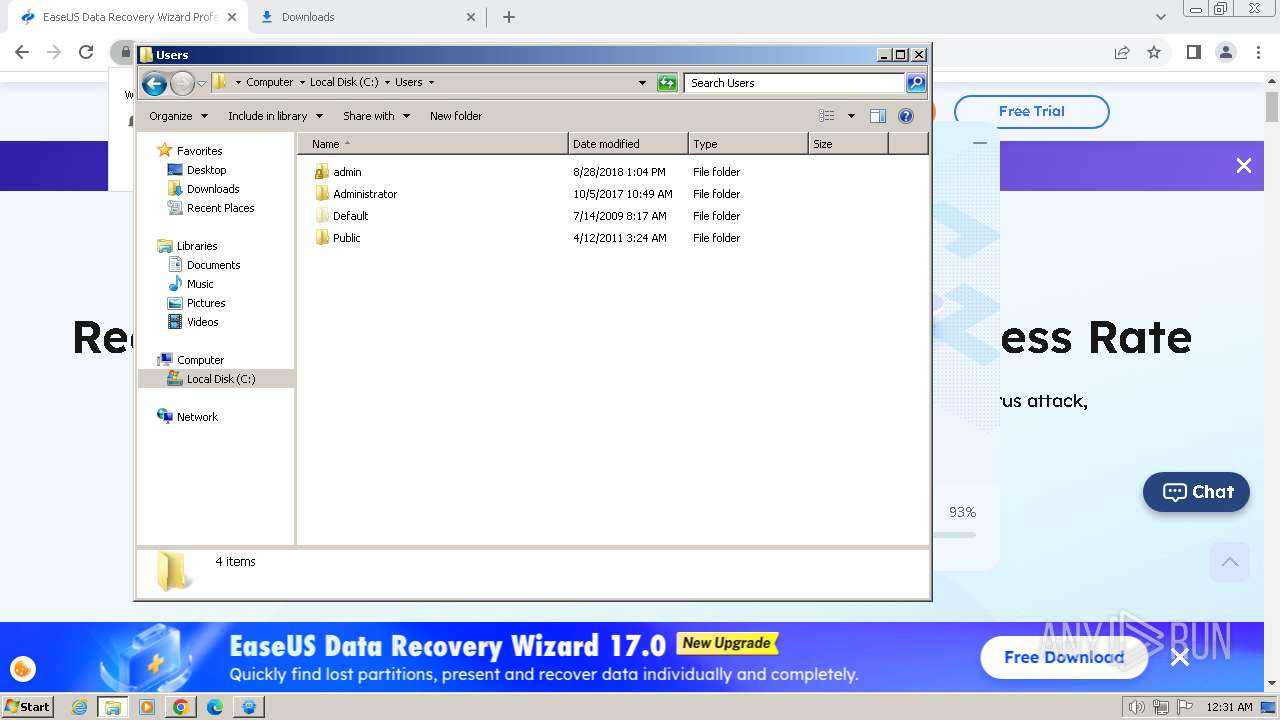
Creates files or folders in the user directory
- AliyunWrapExe.Exe (PID: 2860)
- AliyunWrapExe.Exe (PID: 3852)
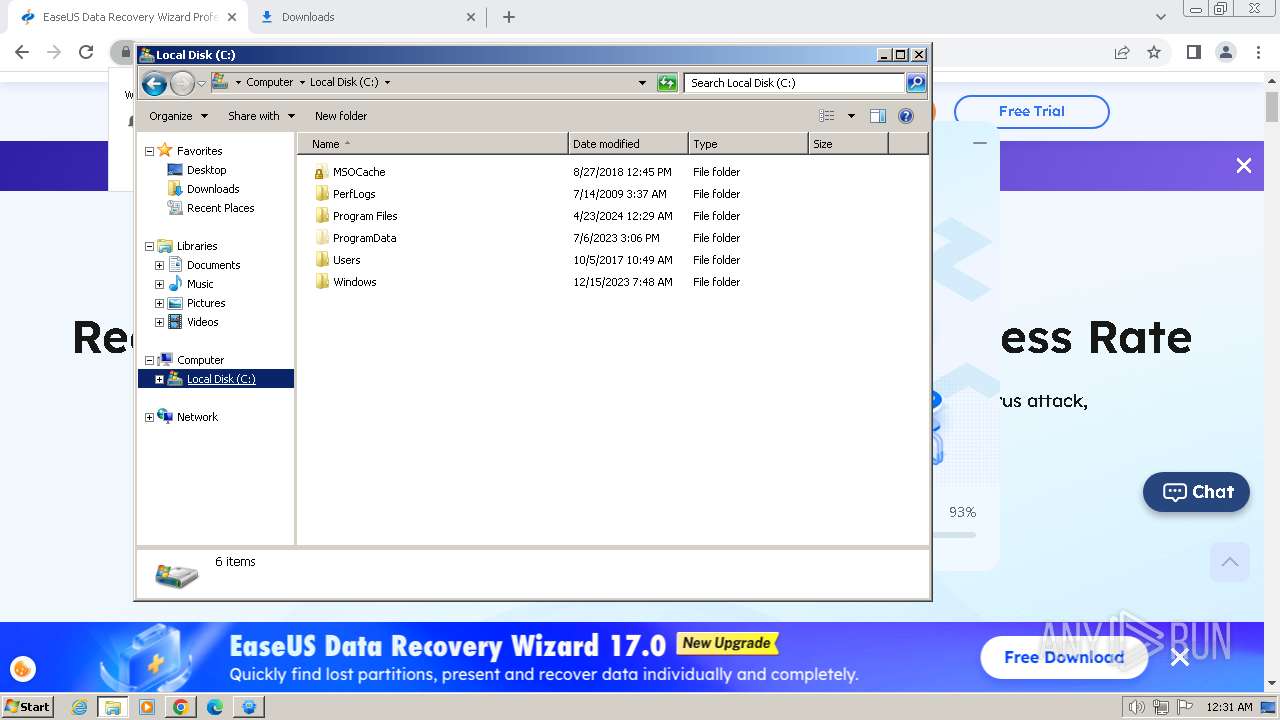
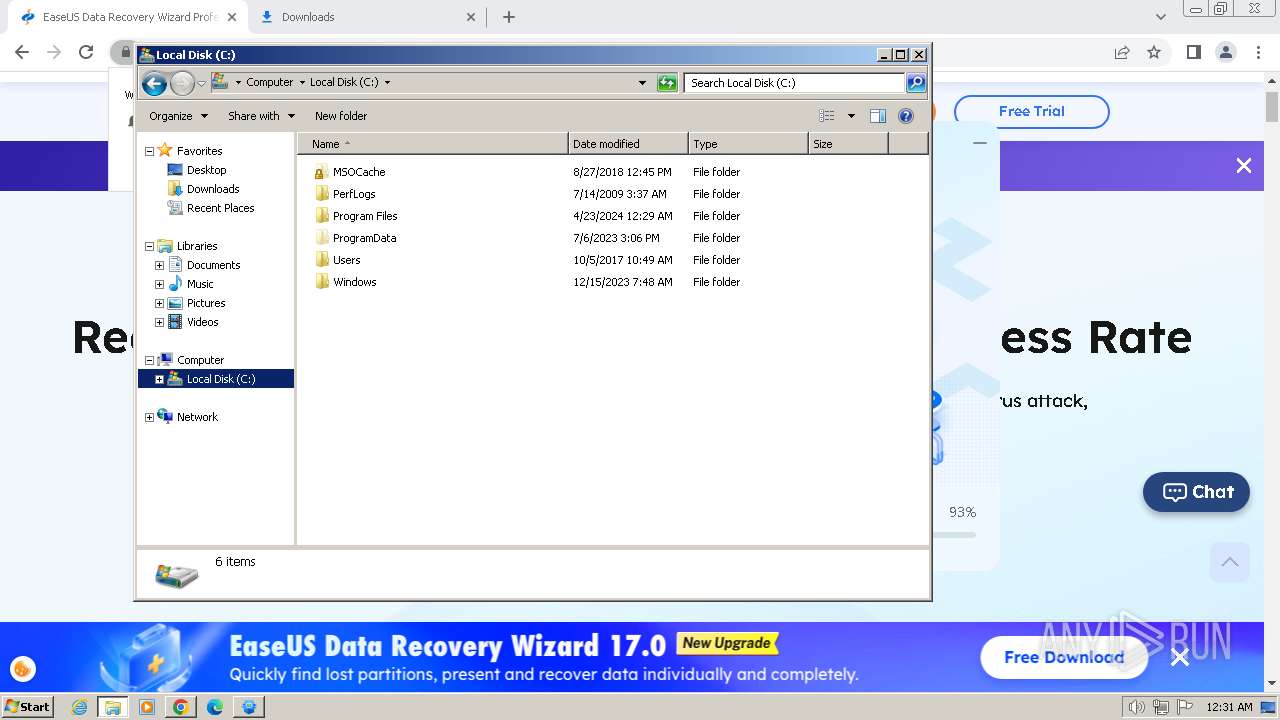
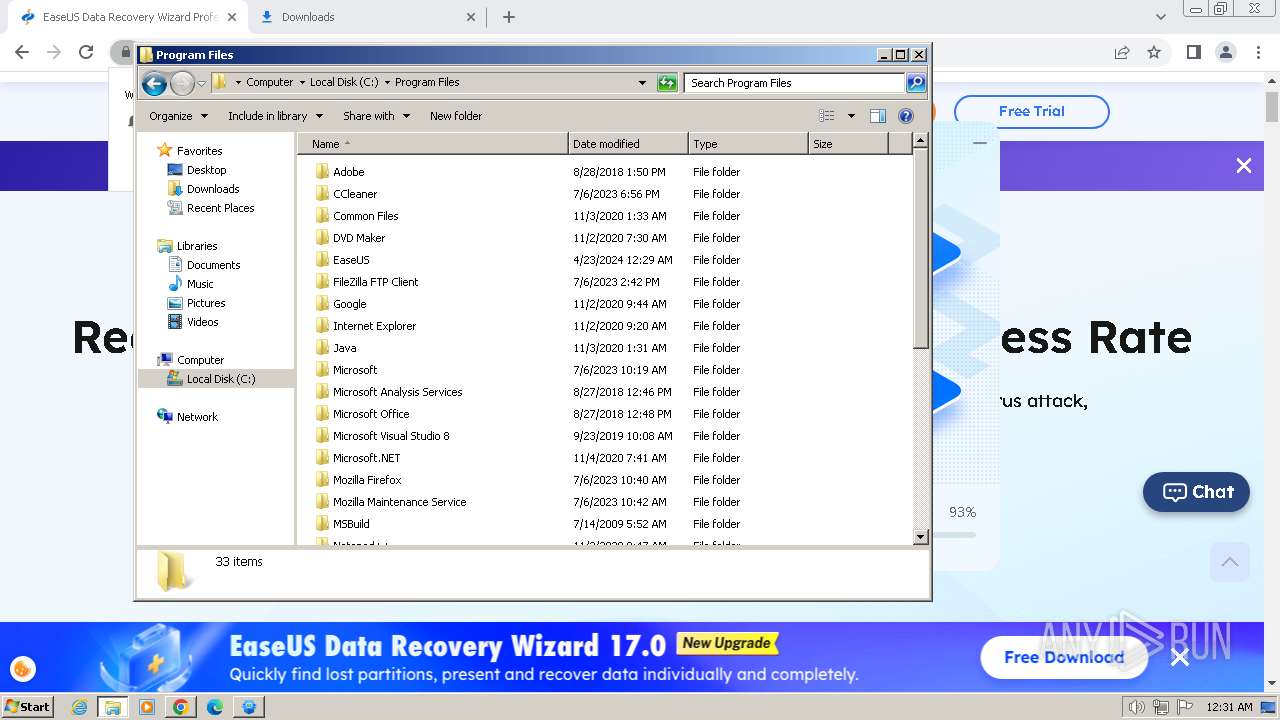
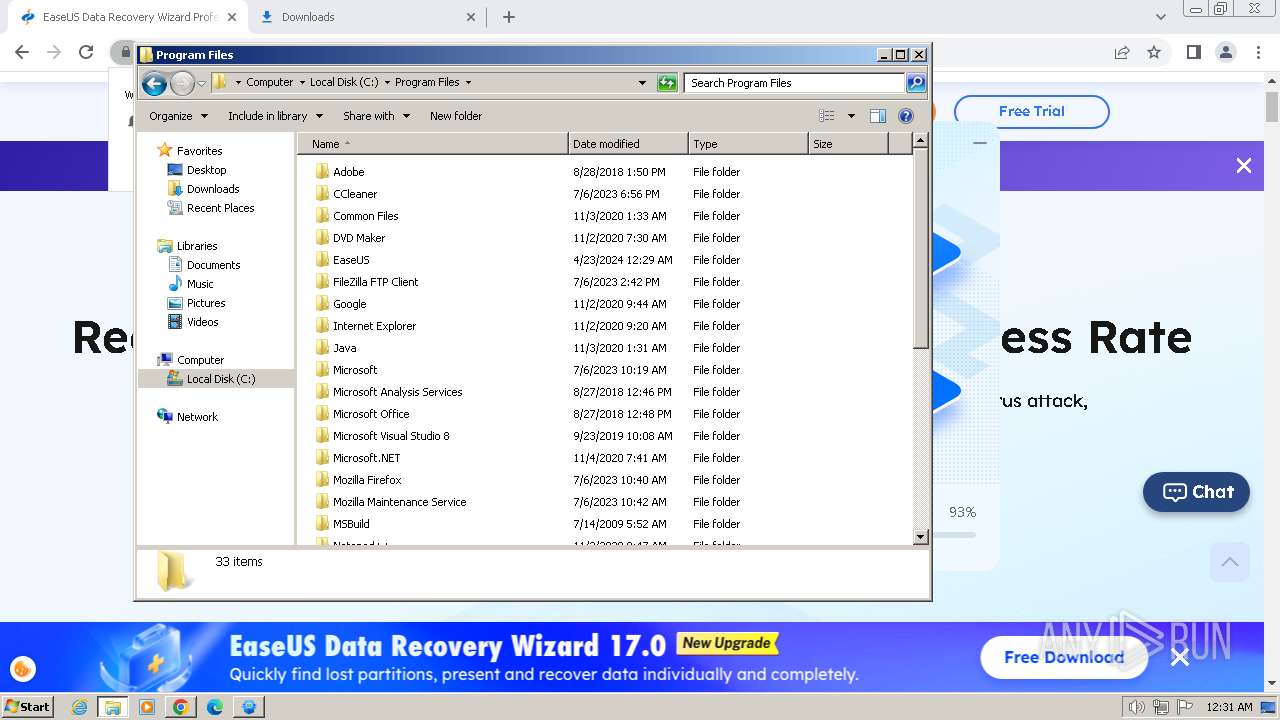
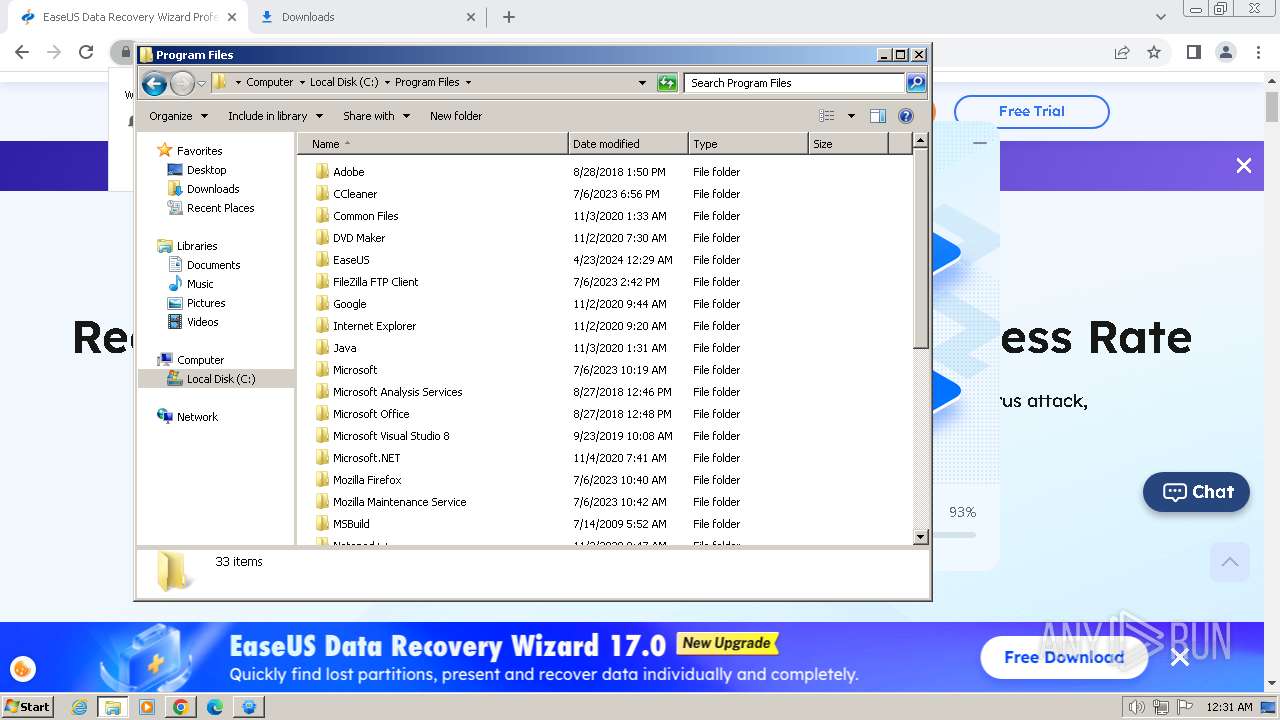
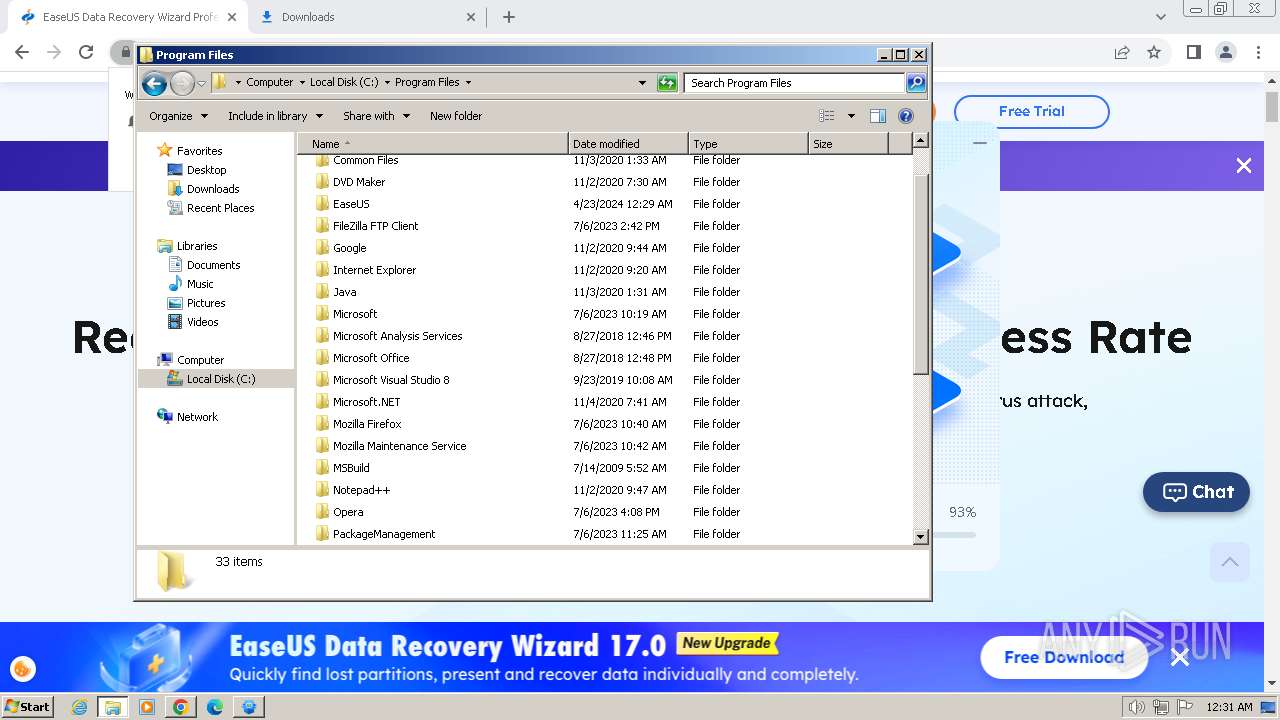
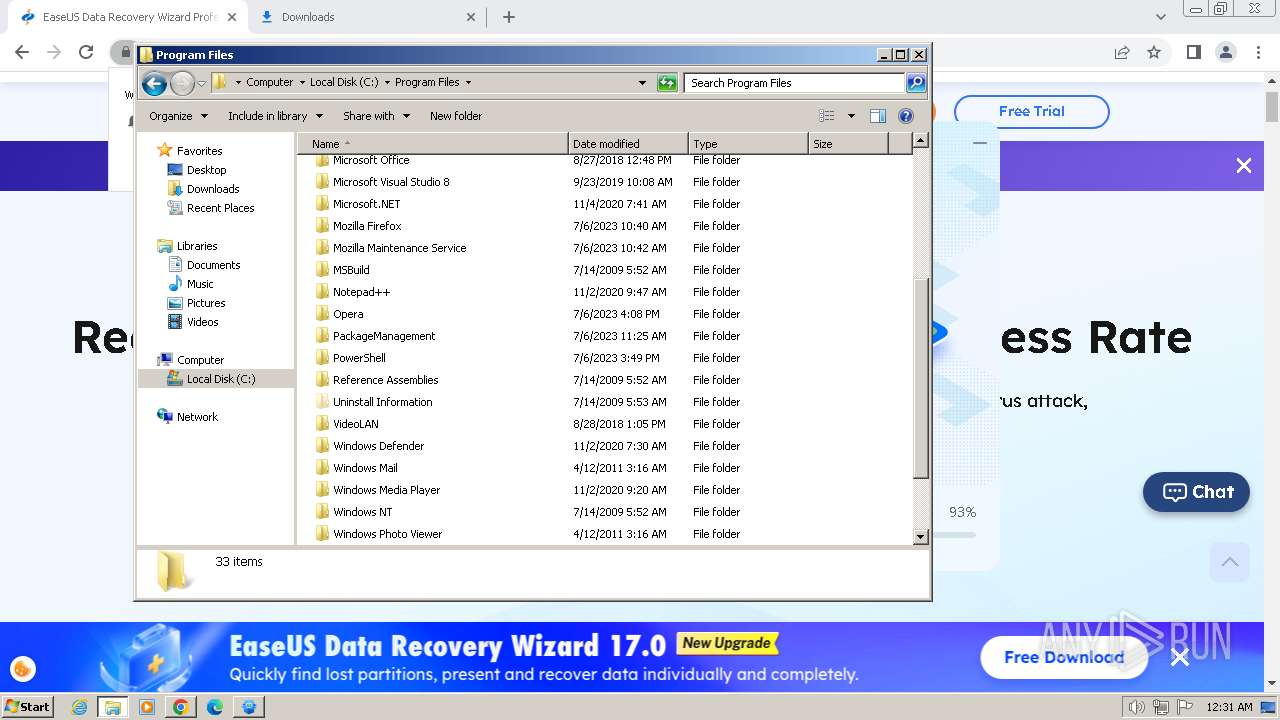
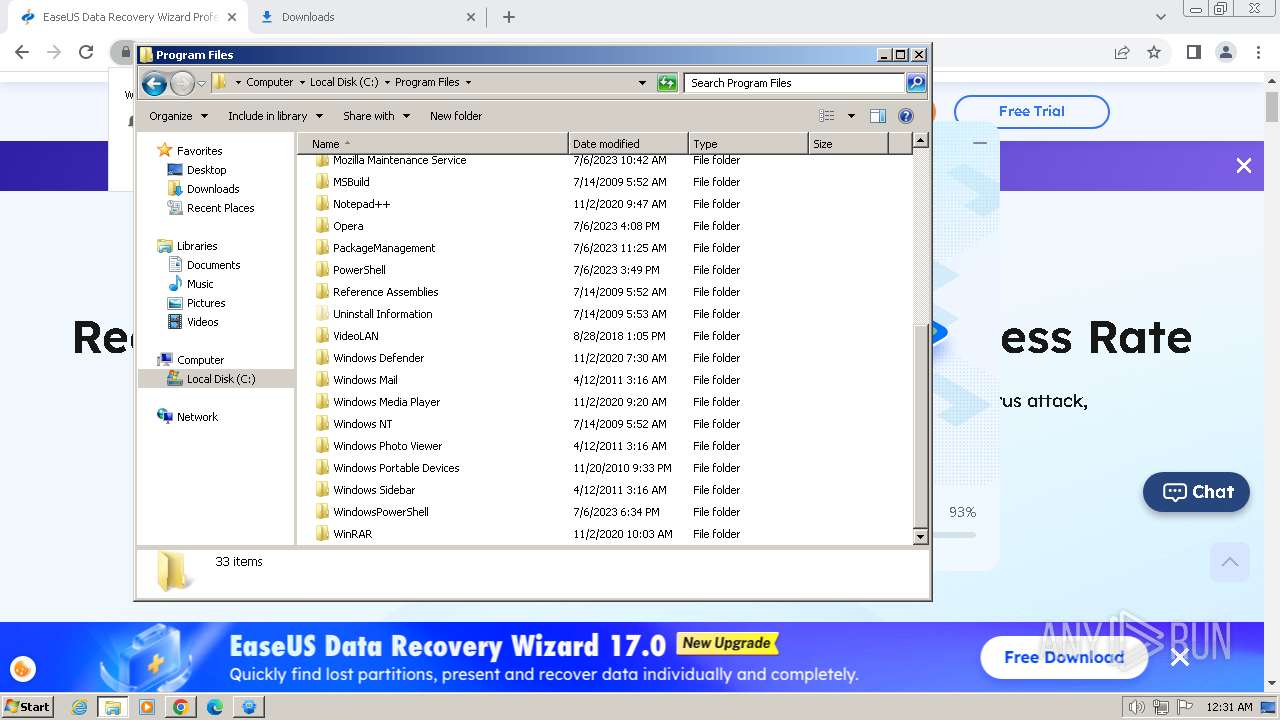
Creates files in the program directory
- drw18.0.0.0_trial.tmp (PID: 2488)
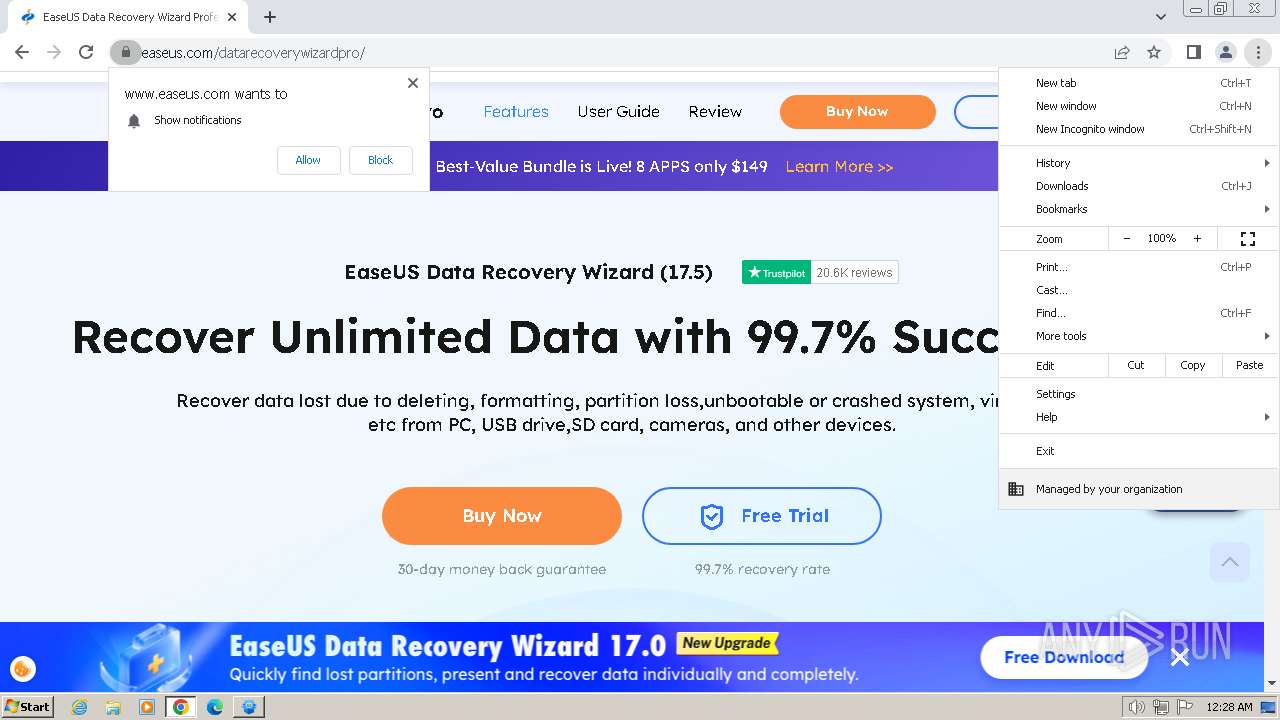
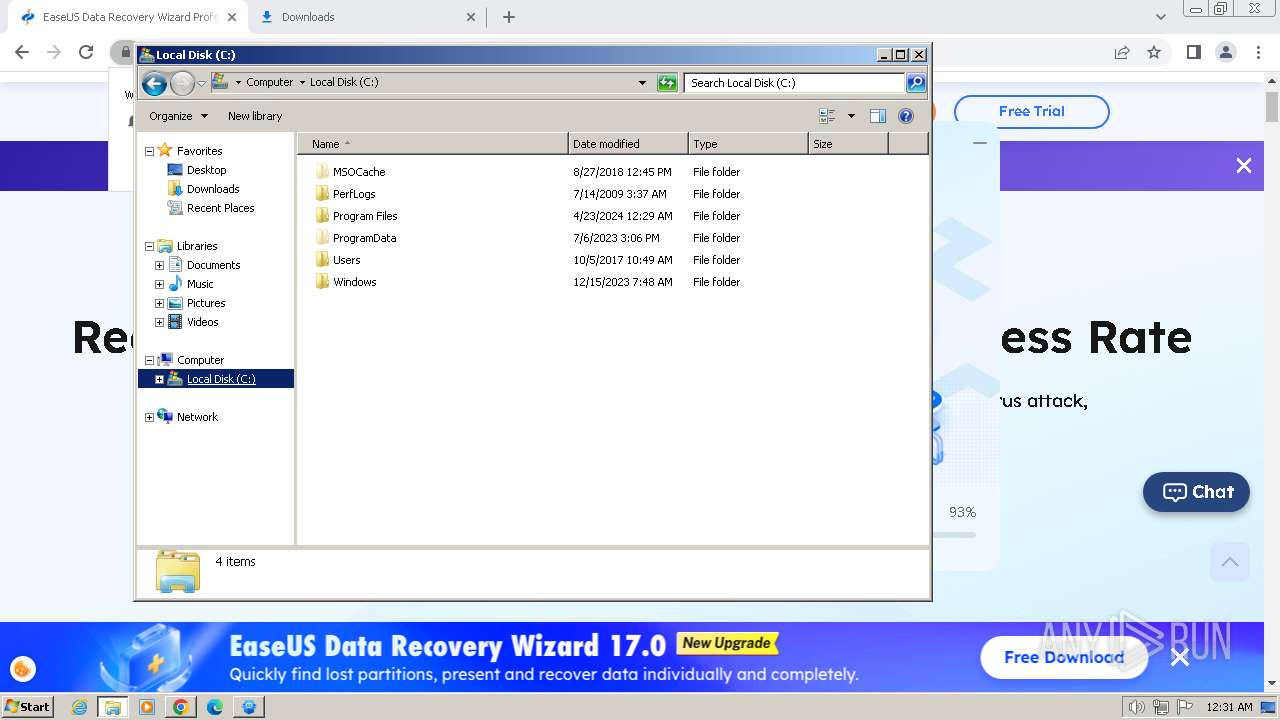
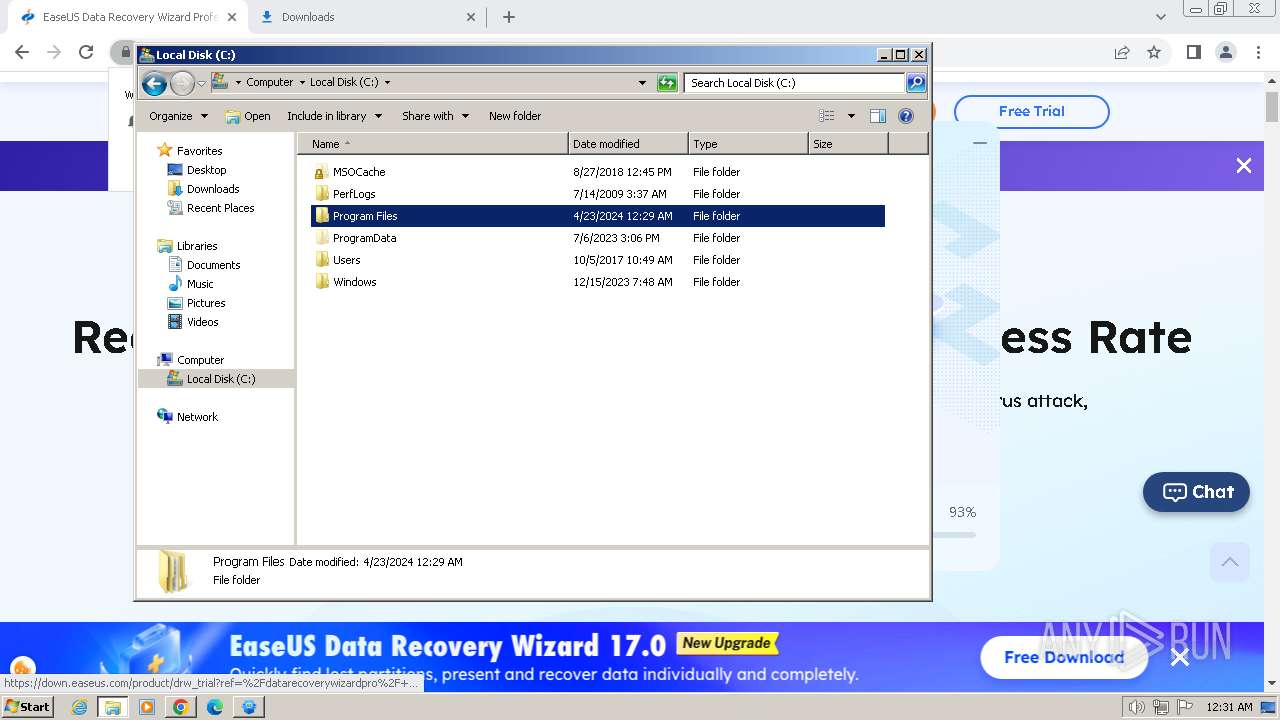
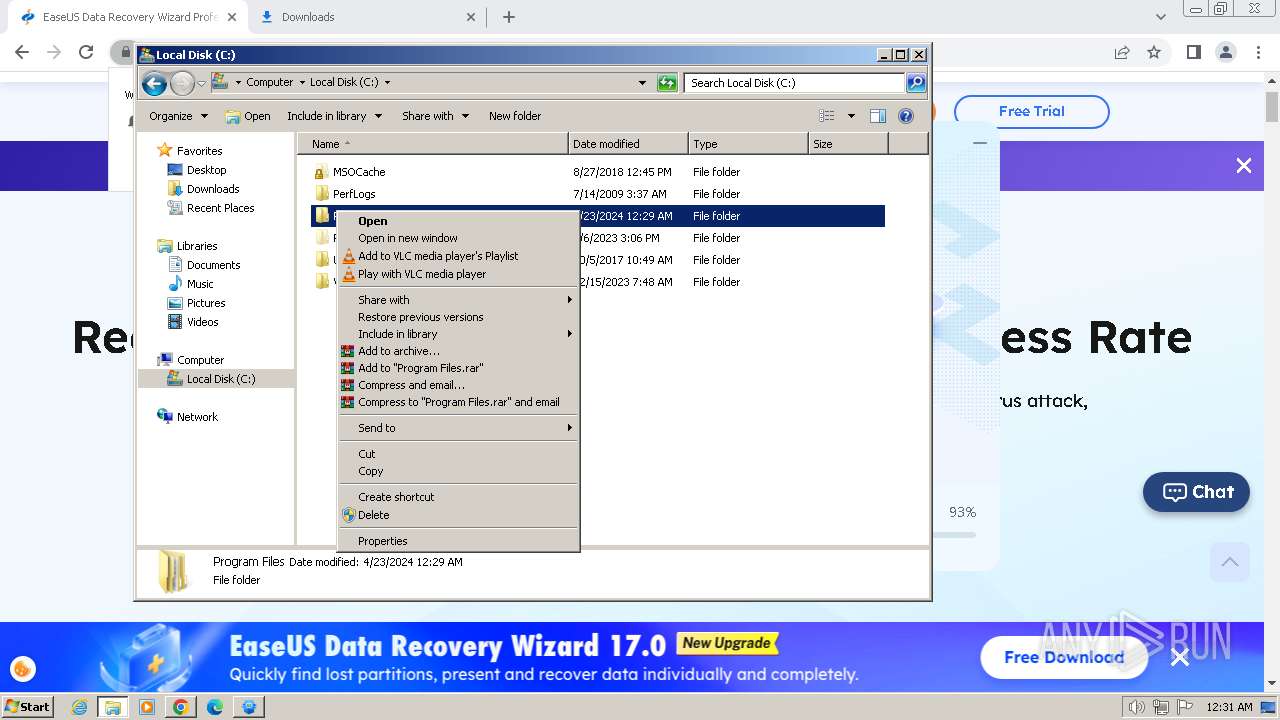
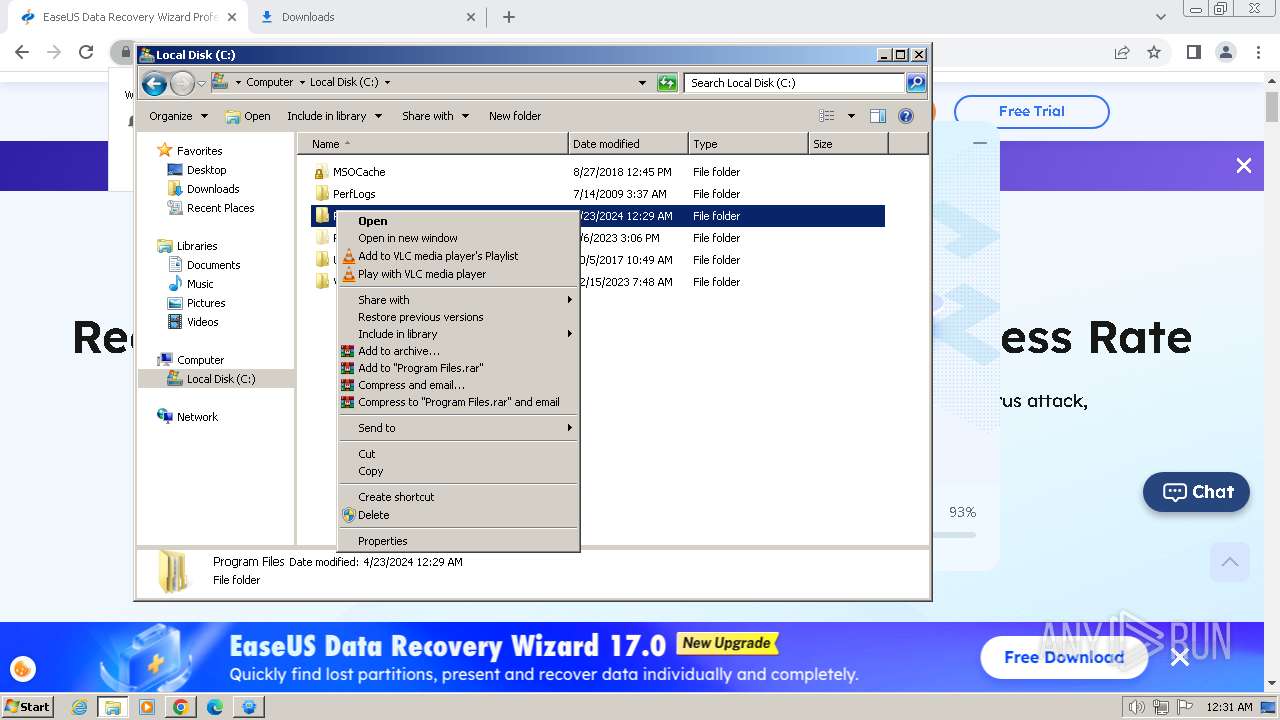
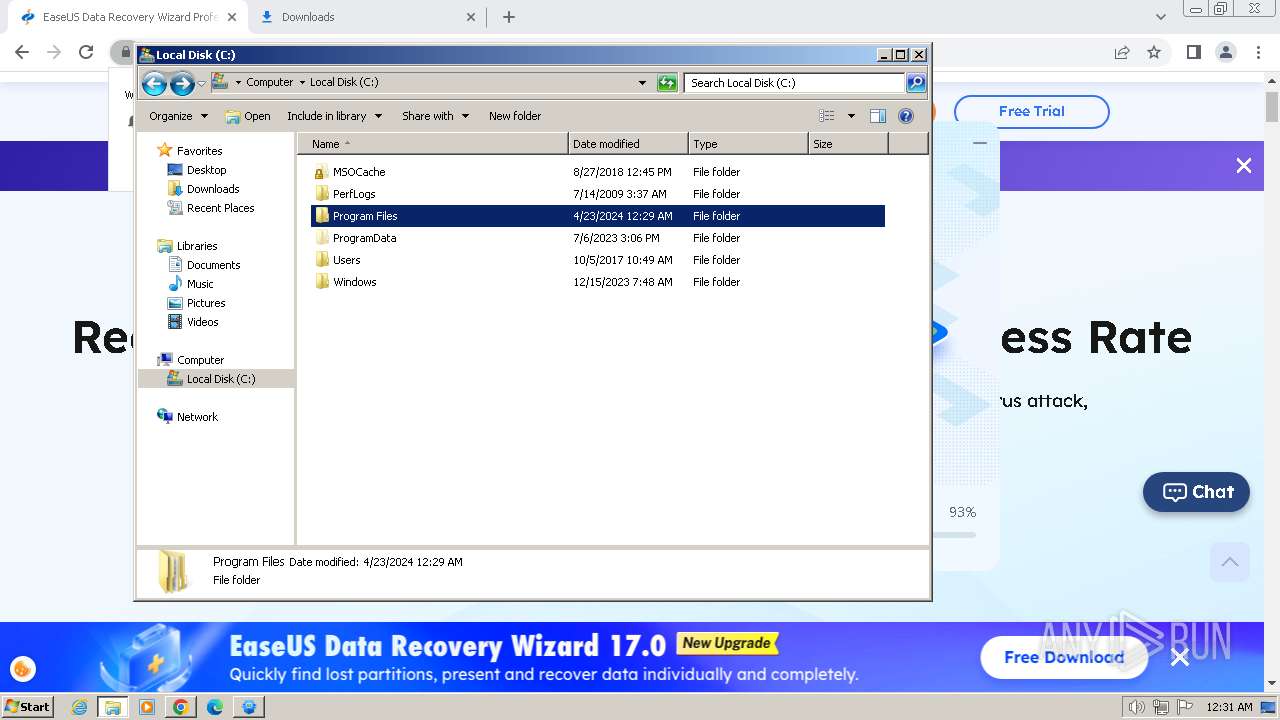
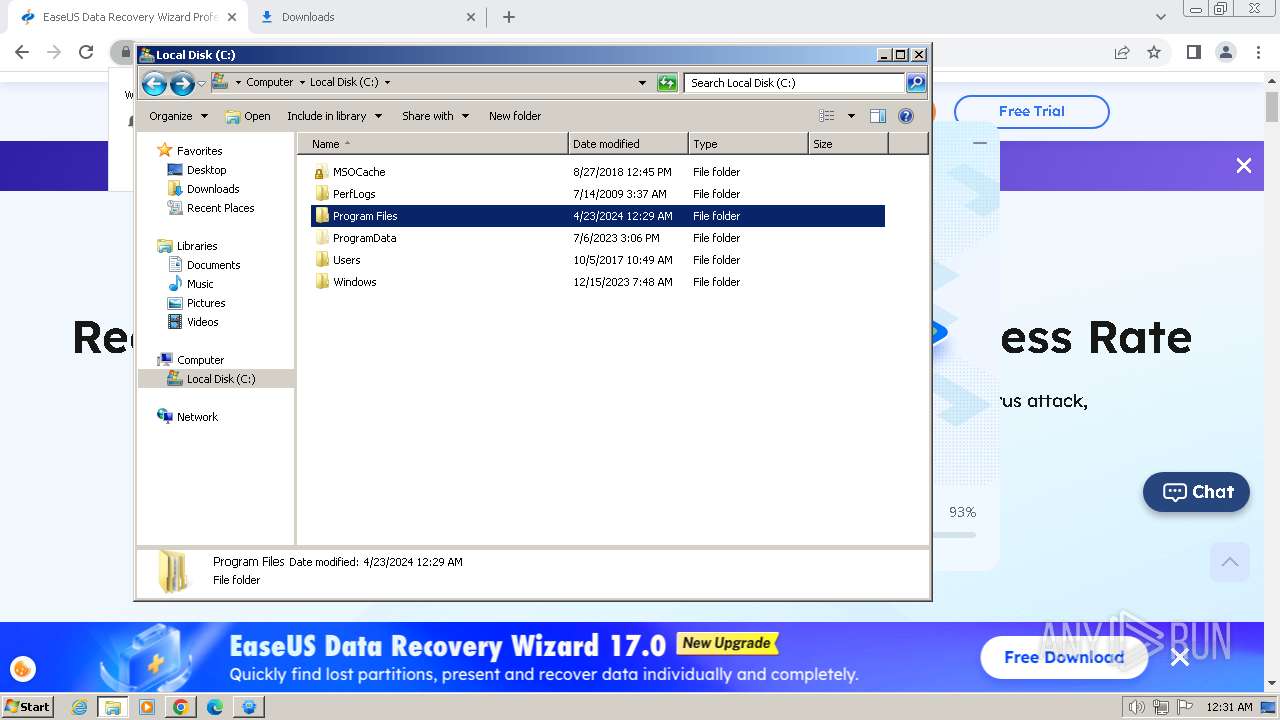
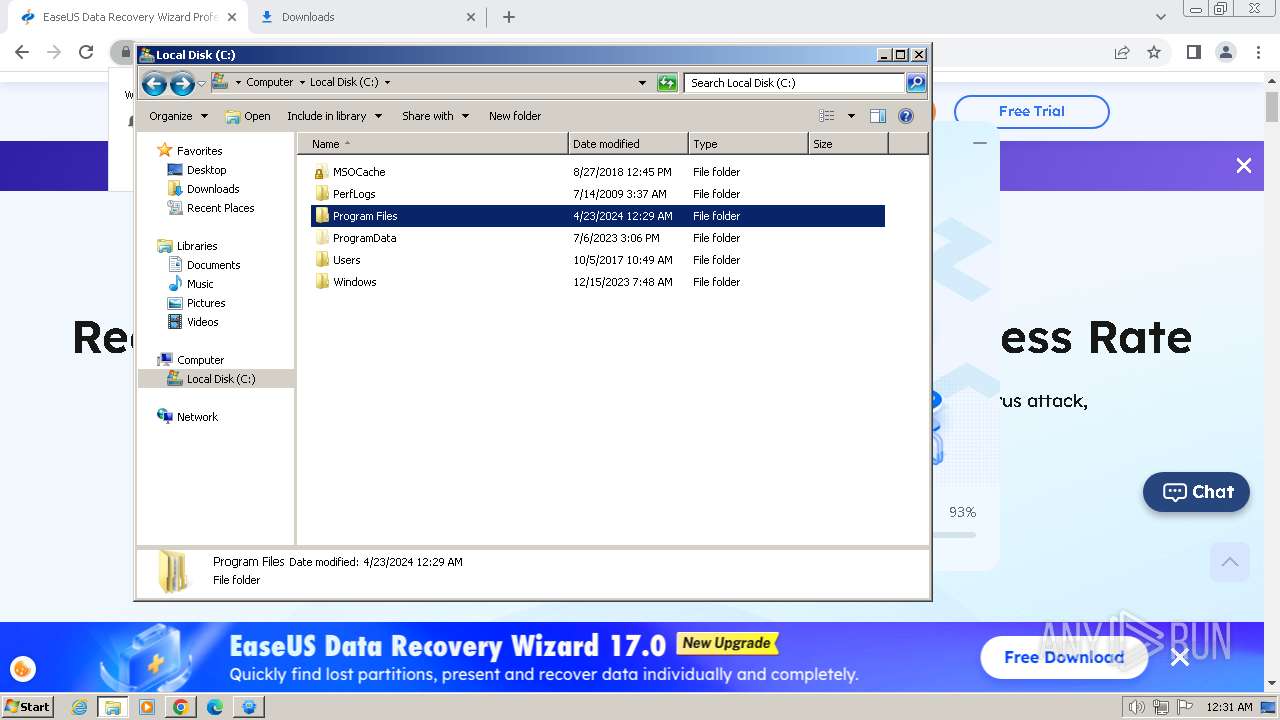
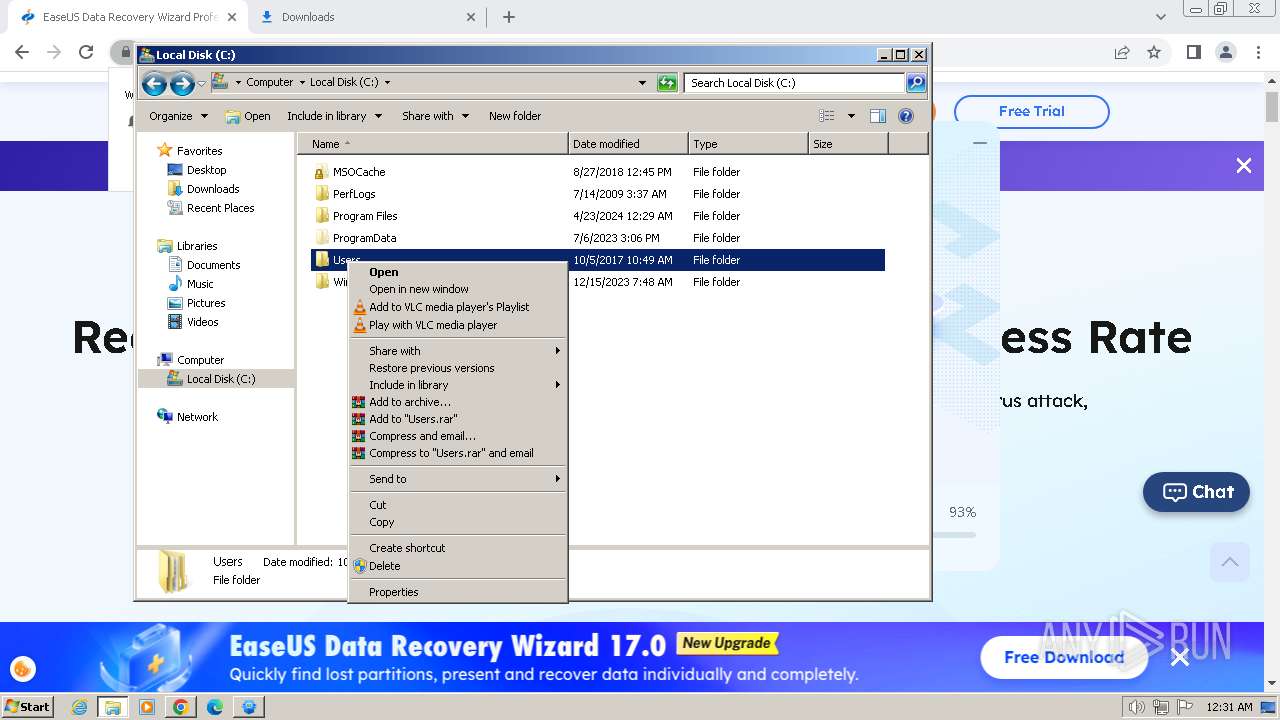
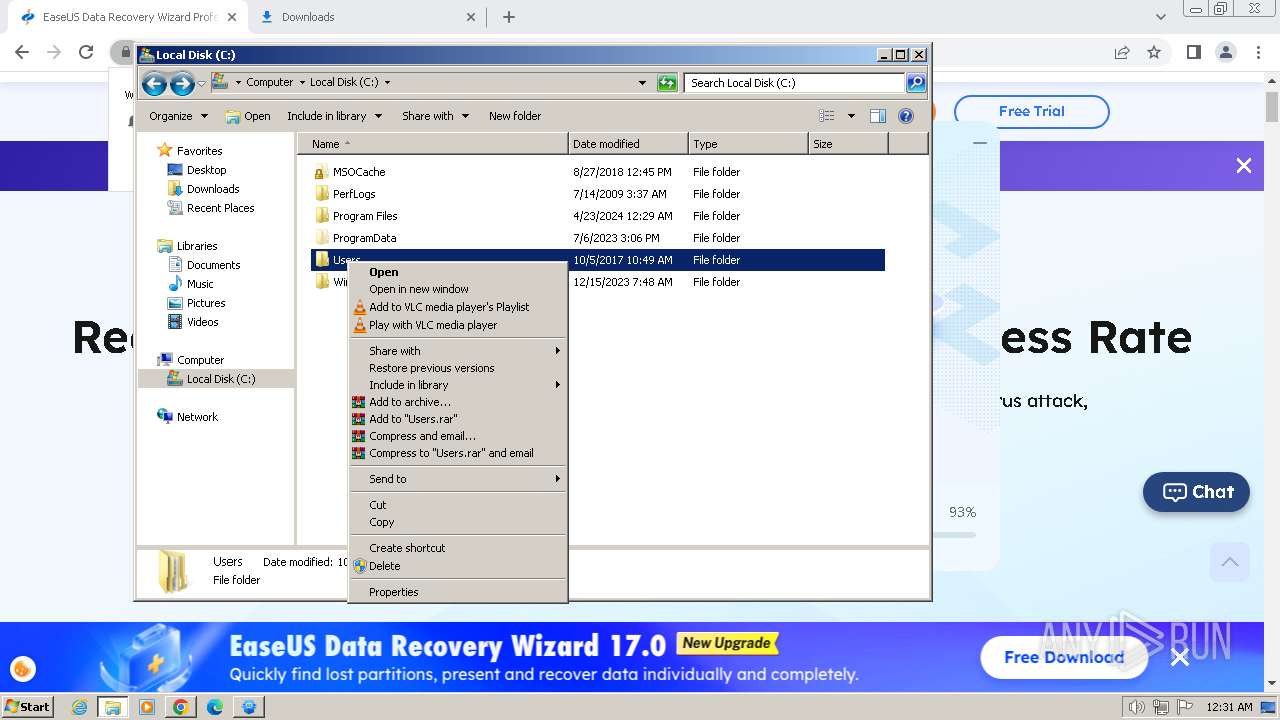
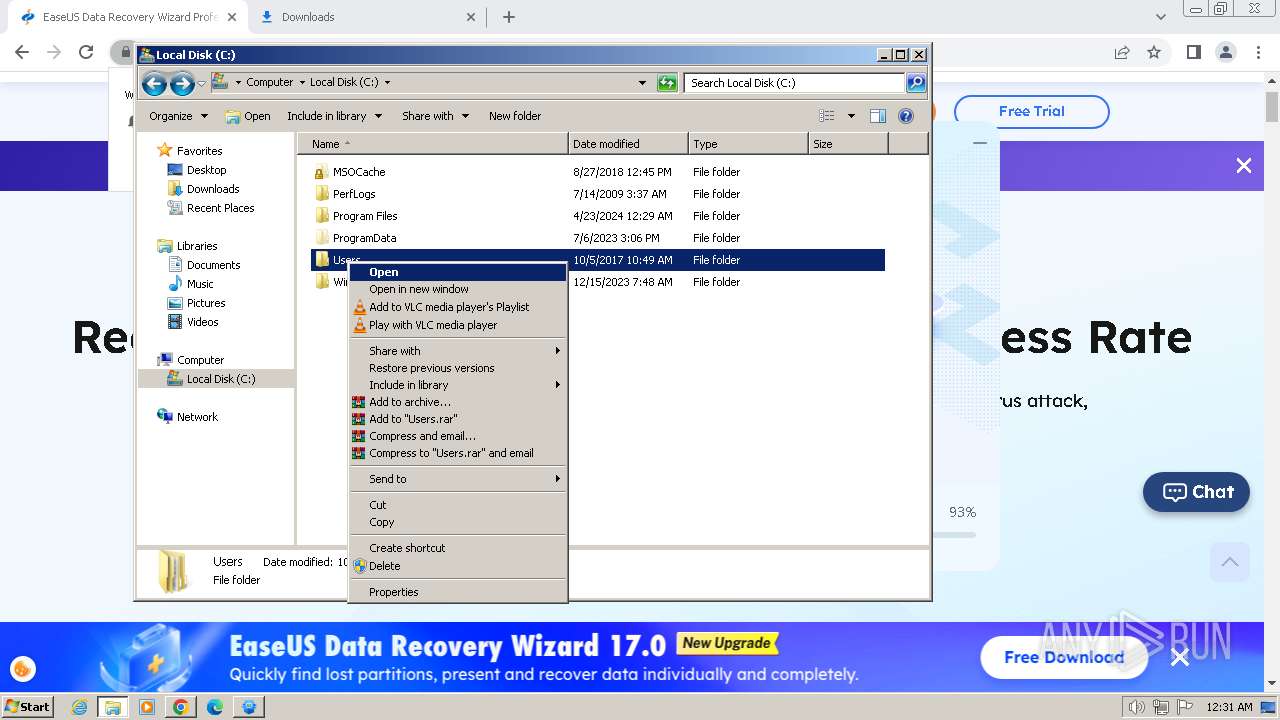
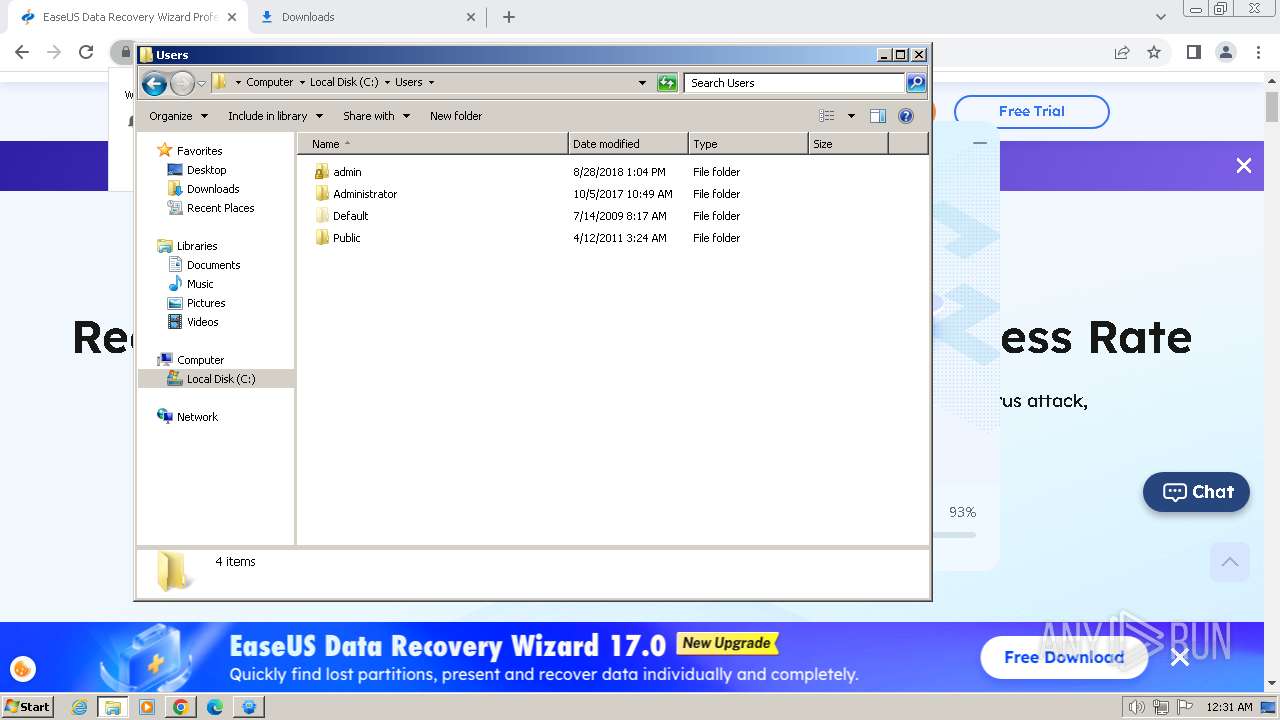
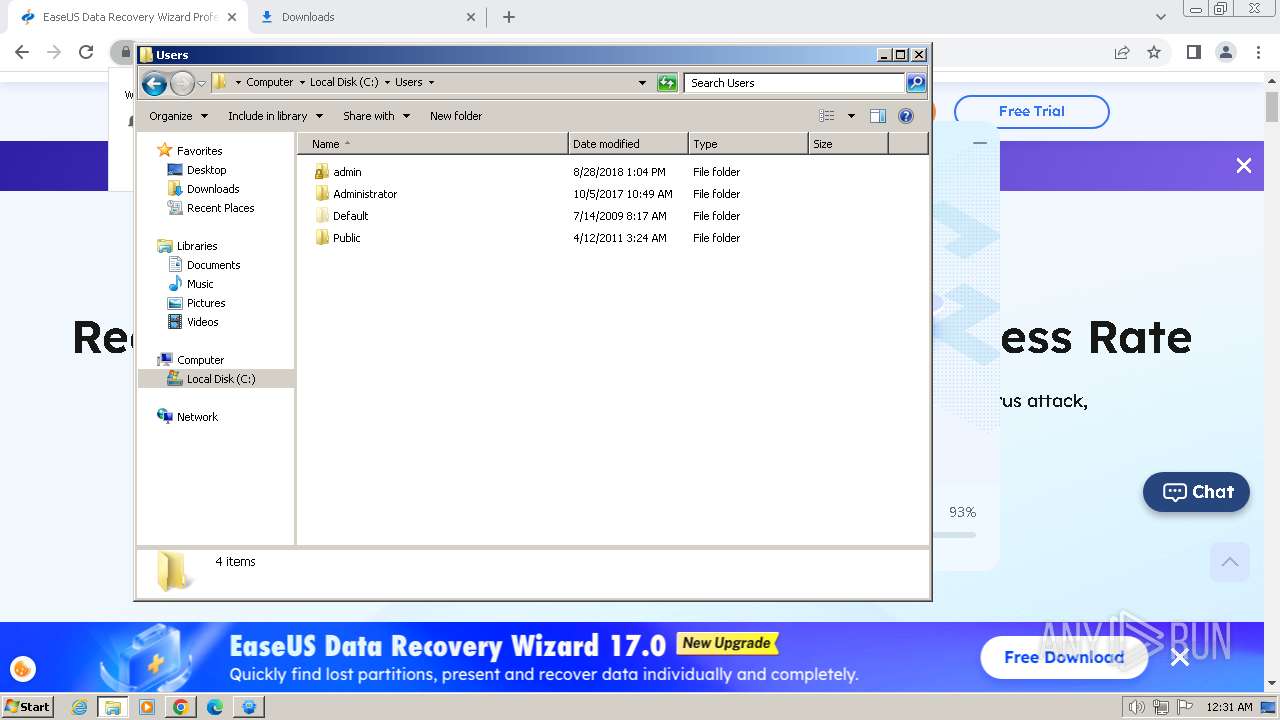
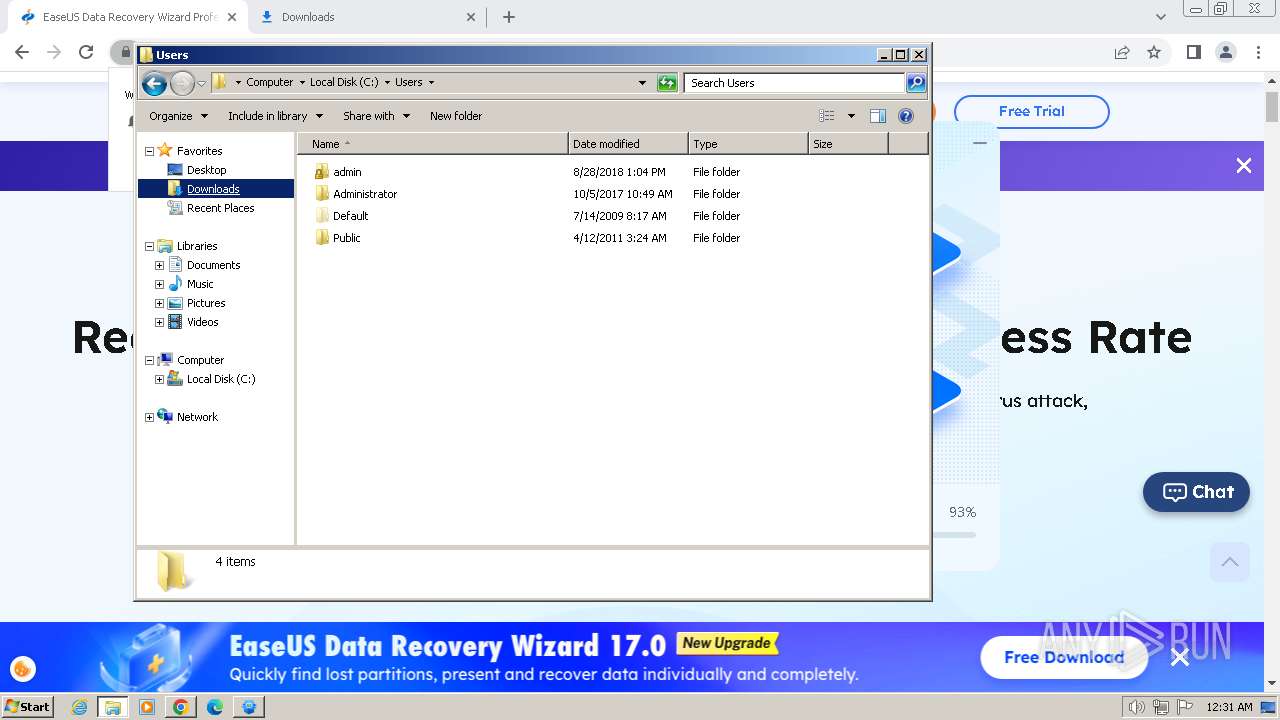
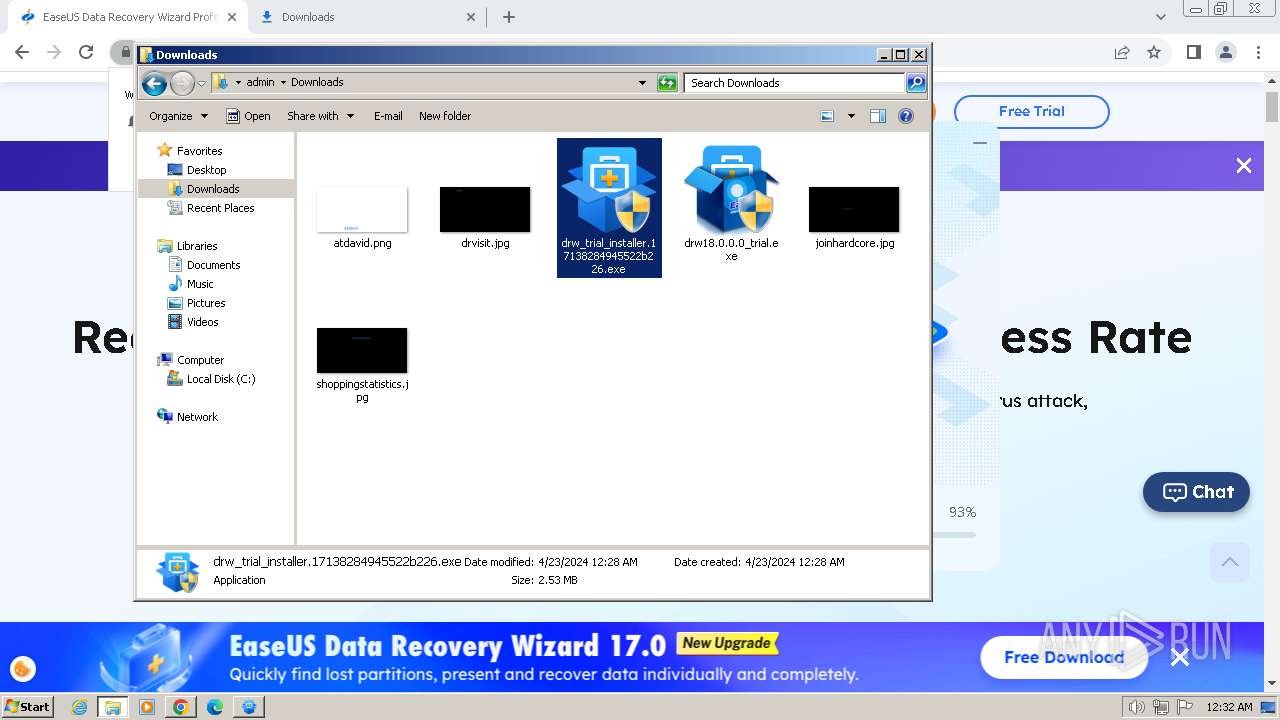
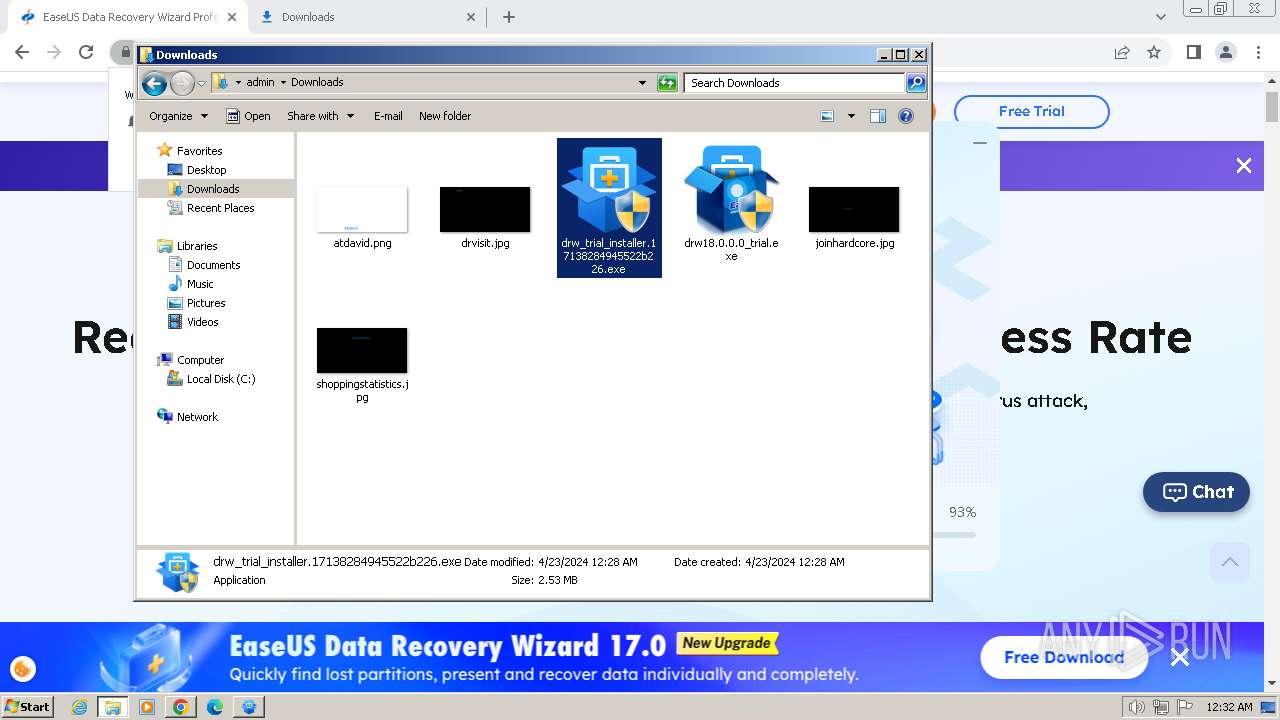
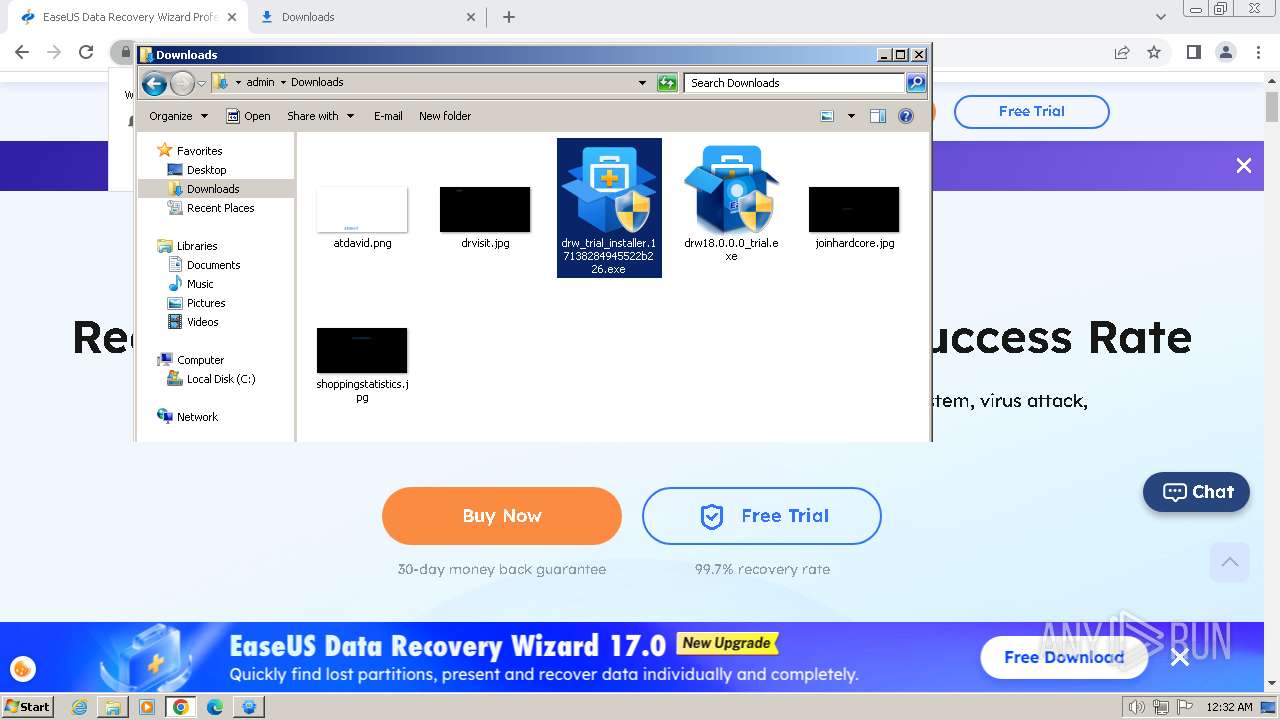
Manual execution by a user
- explorer.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
55
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=652 --field-trial-handle=1124,i,568723281828174398,1850206024895249388,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=1888 --field-trial-handle=1124,i,568723281828174398,1850206024895249388,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1328 --field-trial-handle=1124,i,568723281828174398,1850206024895249388,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | /SendInfo Window "Installing" Activity "Info_Start_Install_Program" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\2.0.0\2trial\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
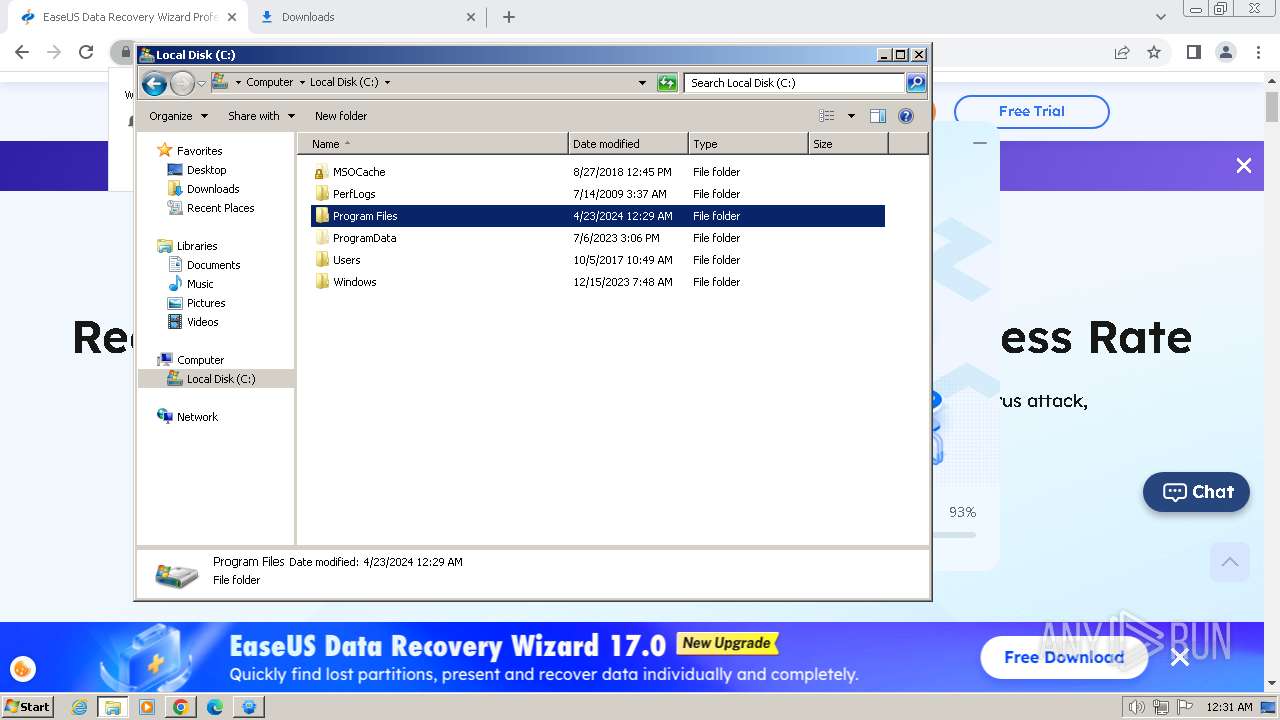
| 1232 | "C:\Users\admin\AppData\Local\Temp\is-U4VIB.tmp\InfoForSetup.exe" /SendInfo "Window" "Selectdestinationlocation" "Activity" "Click_Confirm" "Attribute" "{\"Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\"}" | C:\Users\admin\AppData\Local\Temp\is-U4VIB.tmp\InfoForSetup.exe | — | drw18.0.0.0_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwi_s6G__NaFAxVA7jgGHYD_AvwQFnoECAcQAQ&url=https%3A%2F%2Fwww.easeus.com%2F&usg=AOvVaw3twRFJ9PTMaw6bhrwvqfeR&opi=89978449" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ba18b38,0x6ba18b48,0x6ba18b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\Downloads\drw_trial_installer.17138284945522b226.exe" | C:\Users\admin\Downloads\drw_trial_installer.17138284945522b226.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3088 --field-trial-handle=1124,i,568723281828174398,1850206024895249388,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=4308 --field-trial-handle=1124,i,568723281828174398,1850206024895249388,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
24 400
Read events
24 195
Write events
187
Delete events
18
Modification events
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1288) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
151
Suspicious files
161
Text files
4 067
Unknown types
202
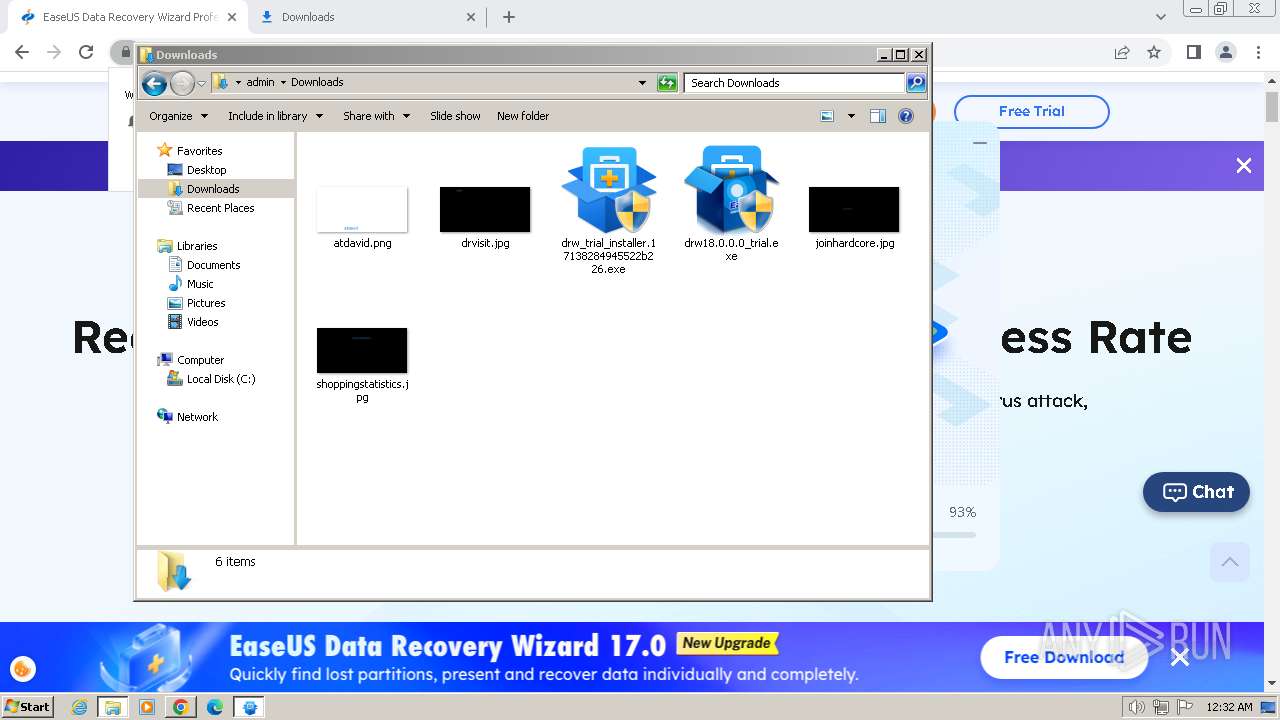
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bd9f1.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1bd9e2.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1bdc62.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF1bdafb.TMP | text | |
MD5:BF244CDEBD39A0D20444C1578C0200BE | SHA256:CC7E247D7764DA50D4137E894838F918281D4915FE0823B4FC0CB763BF582F4D | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1be125.TMP | — | |
MD5:— | SHA256:— | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF1bdabc.TMP | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 1288 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4e9d0376-6d8f-471b-95dc-7b41c7ab0e7d.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
131
DNS requests
324
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2860 | AliyunWrapExe.Exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=2 | unknown | — | — | unknown |
2860 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ae2w3fv2vmc6qxhudcjhxeiny4_932/efniojlnjndmcbiieegkicadnoecjjef_932_all_l7yekqs5sh3zcwwvk5emxjy25a.crx3 | unknown | — | — | unknown |
3852 | AliyunWrapExe.Exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=2 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ae2w3fv2vmc6qxhudcjhxeiny4_932/efniojlnjndmcbiieegkicadnoecjjef_932_all_l7yekqs5sh3zcwwvk5emxjy25a.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ae2w3fv2vmc6qxhudcjhxeiny4_932/efniojlnjndmcbiieegkicadnoecjjef_932_all_l7yekqs5sh3zcwwvk5emxjy25a.crx3 | unknown | — | — | unknown |
3852 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.8:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_windrw_ip/shards/lb | unknown | — | — | unknown |
2860 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
2860 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
2860 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.12:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
2880 | chrome.exe | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1288 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2880 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
2880 | chrome.exe | 104.18.6.90:443 | www.easeus.com | CLOUDFLARENET | — | unknown |
2880 | chrome.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
2880 | chrome.exe | 142.250.186.130:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.easeus.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
static.hotjar.com |
| whitelisted |
mail.easeus.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
cdn.consentmanager.net |
| malicious |
Threats
Process | Message |
|---|---|
EDownloader.exe | [1576]-00:28:25:708 ParseCmdLine param=EXEDIR=C:\Users\admin\Downloads ||| EXENAME=drw_trial_installer.17138284945522b226.exe ||| DOWNLOAD_VERSION=trial ||| PRODUCT_VERSION=2.0.0 ||| INSTALL_TYPE=0
|
EDownloader.exe | [1576]-00:28:25:741 Install recomand return=259
|
EDownloader.exe | [1576]-00:28:26:250 Install recomand return=259
|
EDownloader.exe | [1576]-00:28:28:608 Install recomand return=259
|
EDownloader.exe | [1576]-00:28:28:617 Install recomand return=259
|
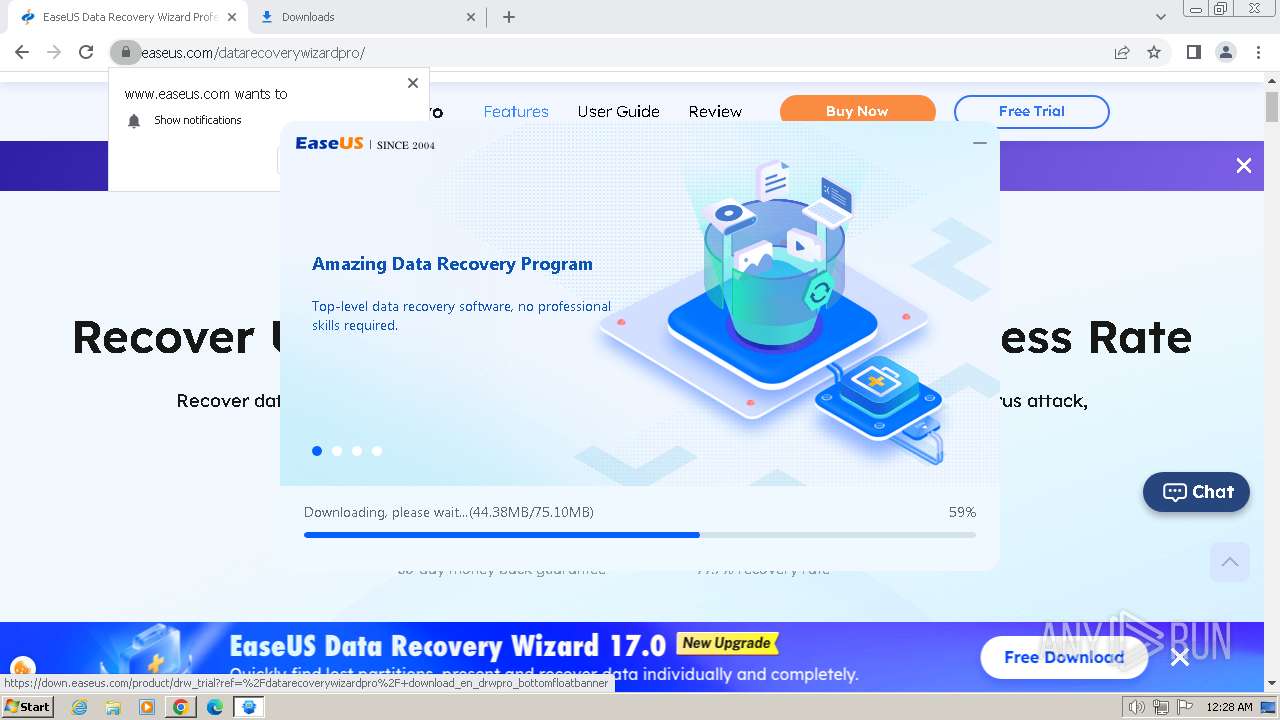
EDownloader.exe | [3908]-00:28:28:625 PostData Start download url=http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/?exeNumber=17138284945522b226&lang=English&pcVersion=home&pid=2&tid=1&version=trial
|
EDownloader.exe | [1576]-00:28:30:209 CHttpHelper::GetDownloadInfo 45 download info code:0
|
EDownloader.exe | [3908]-00:28:30:209 Json parse Data end
|
EDownloader.exe | [3908]-00:28:30:193 Json parse Data Start
|
EDownloader.exe | [3908]-00:28:30:193 PostData end
|