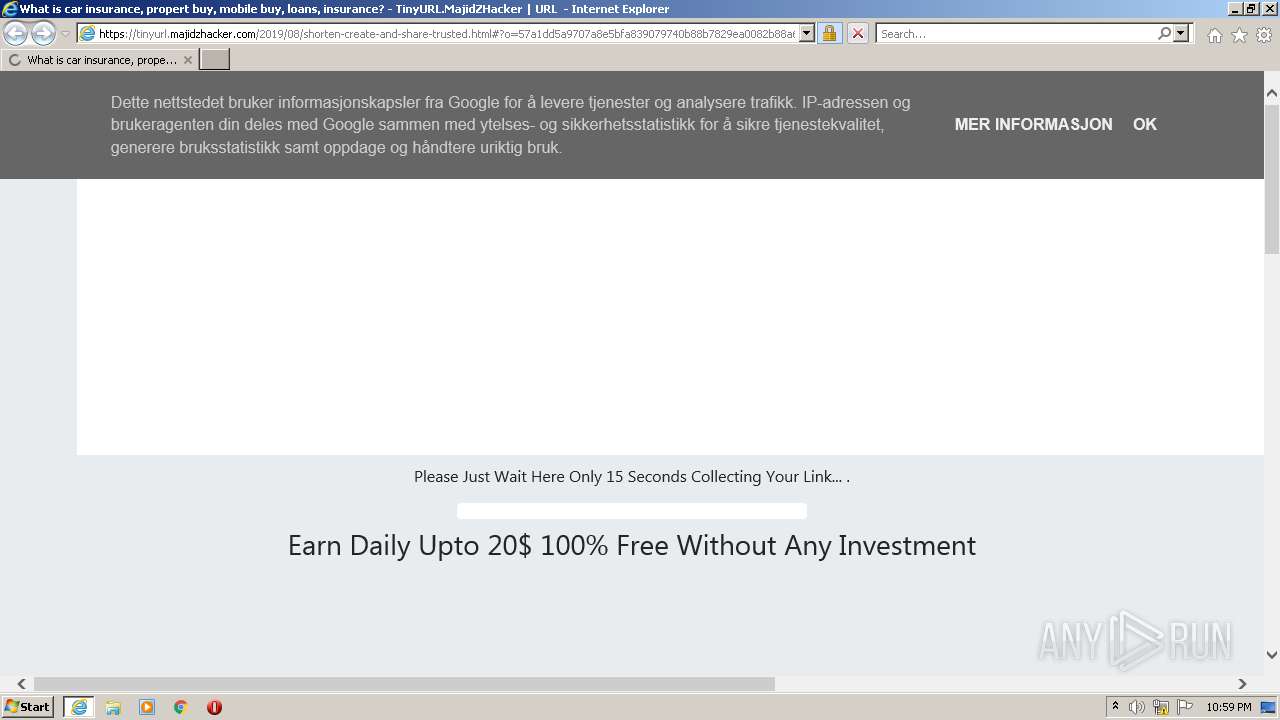
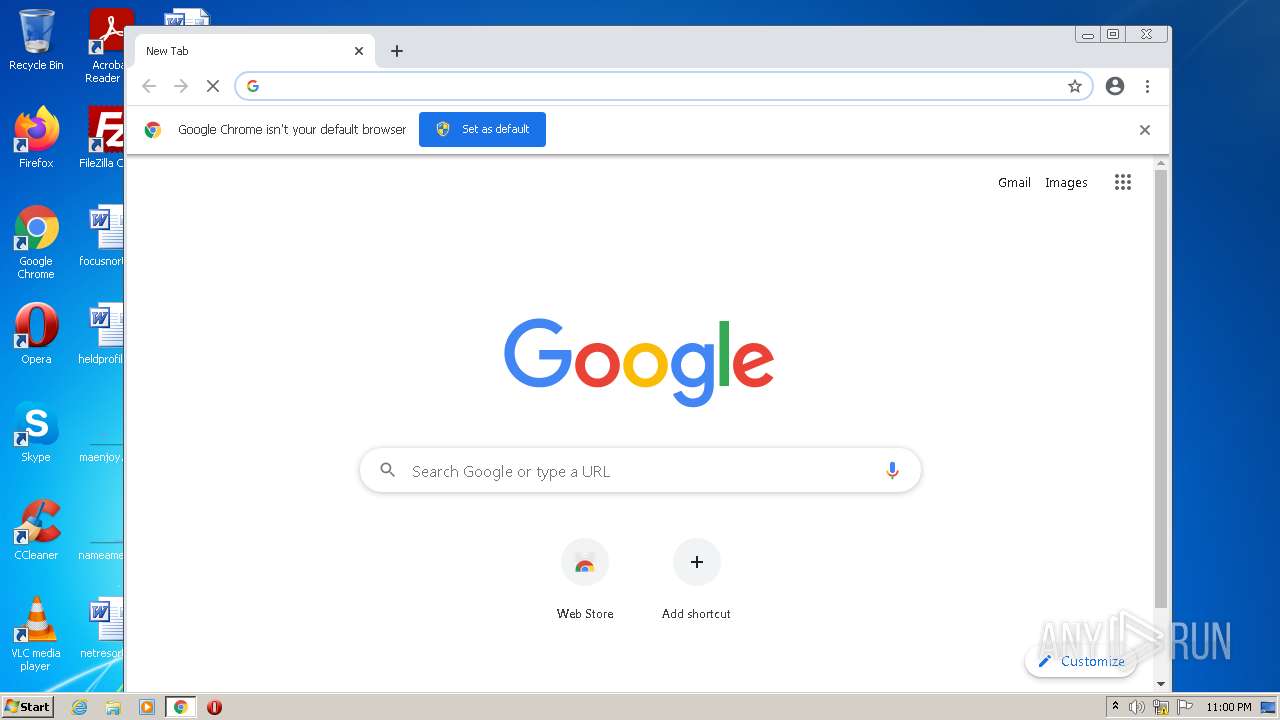
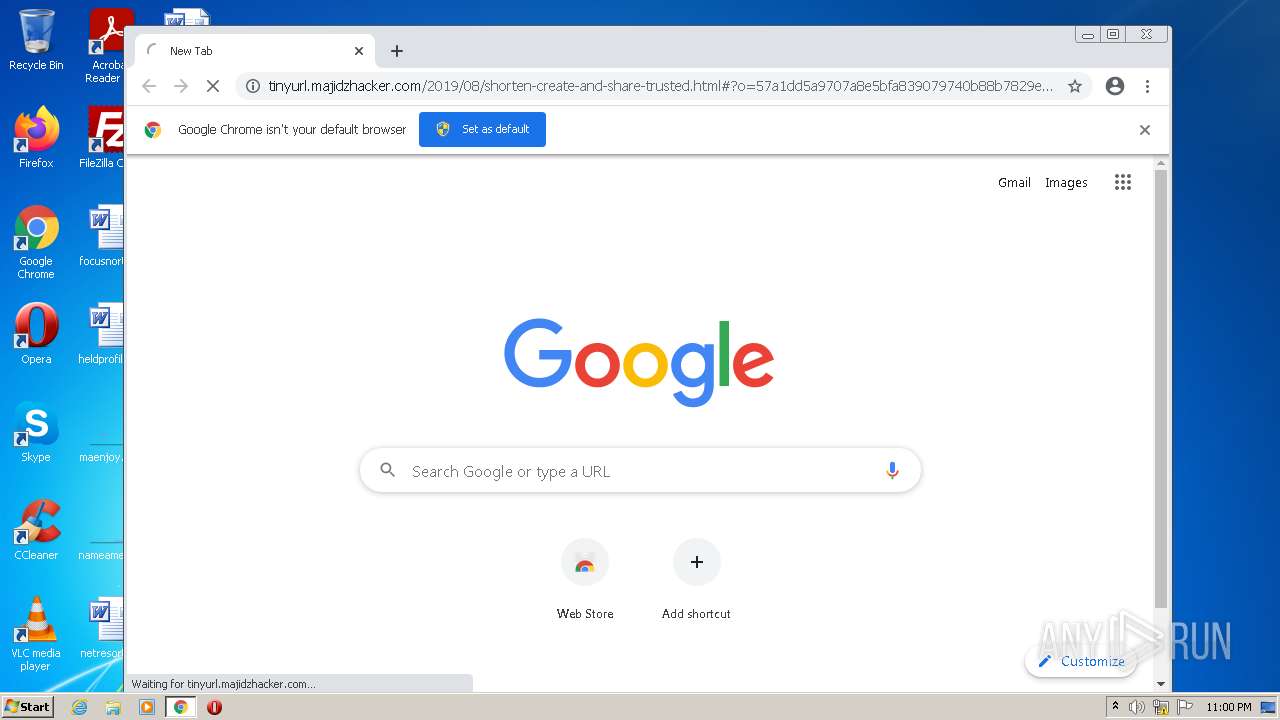
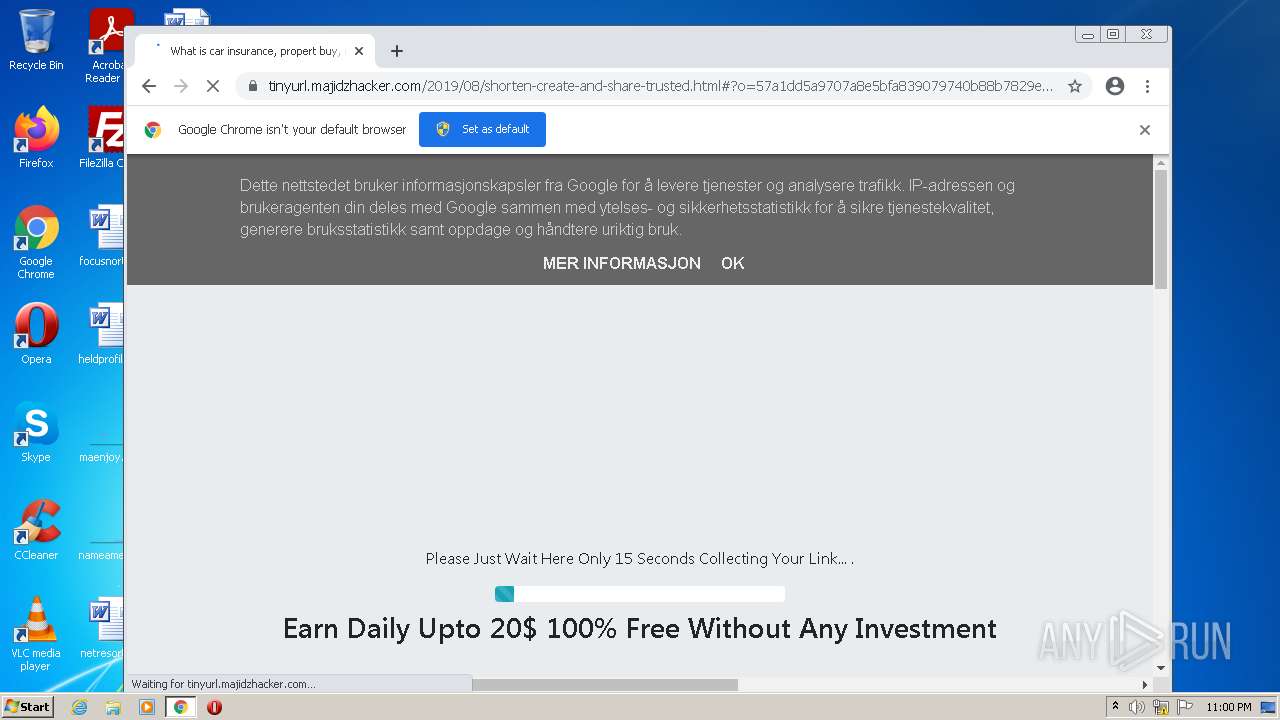
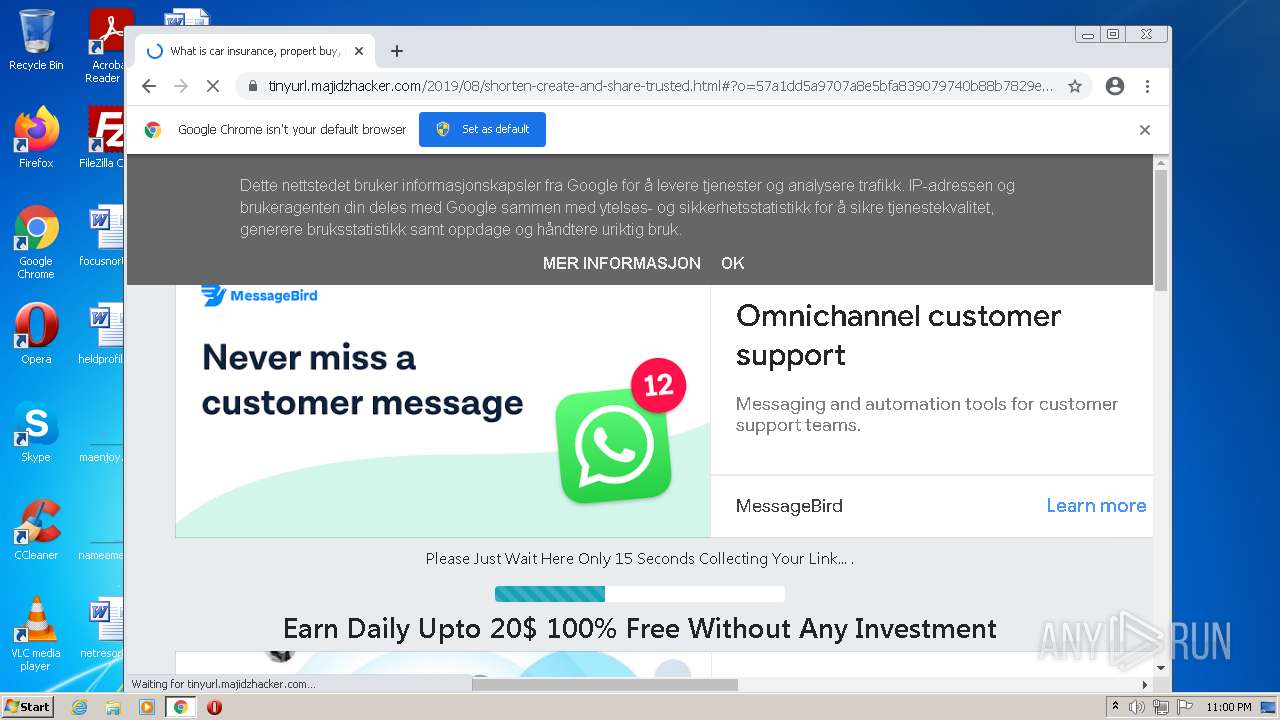
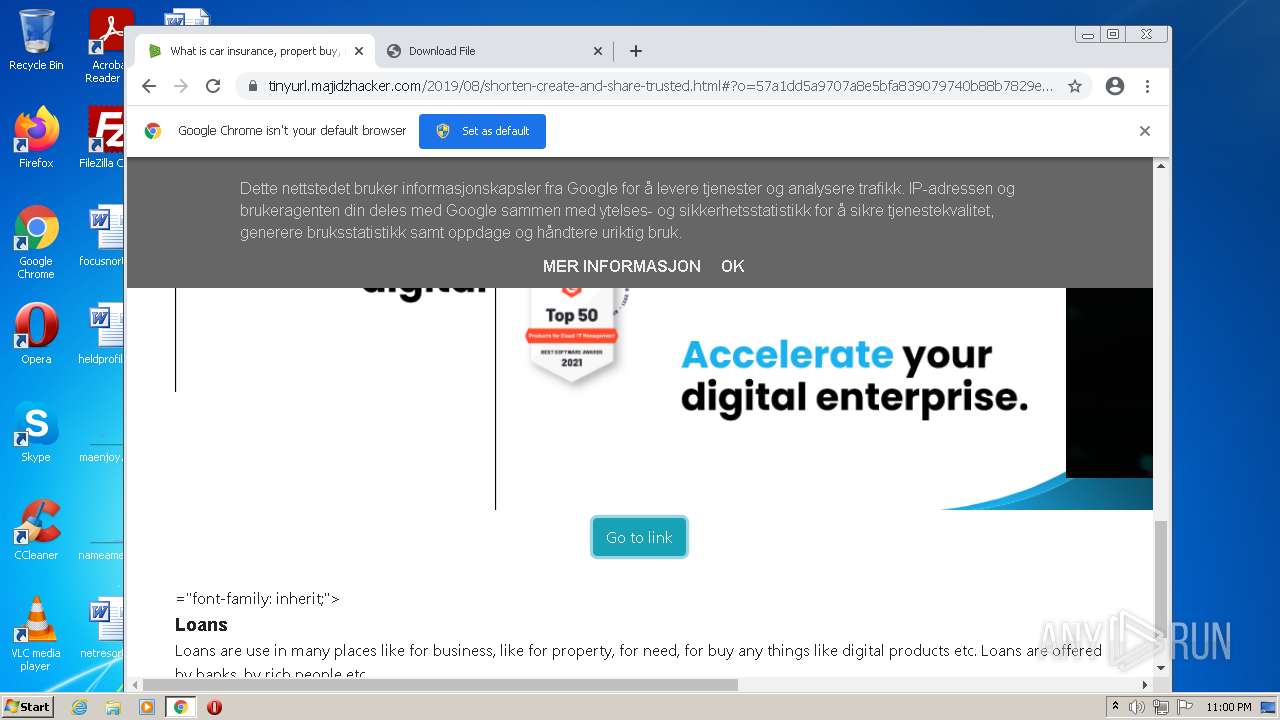
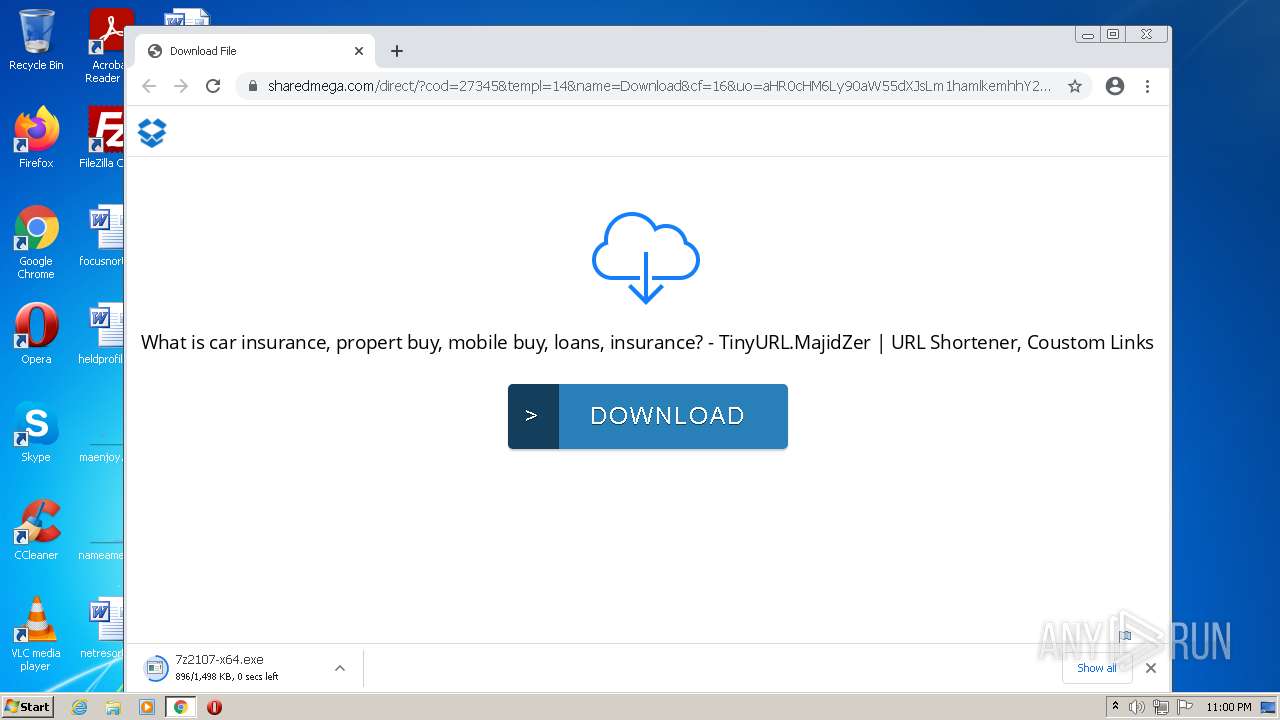
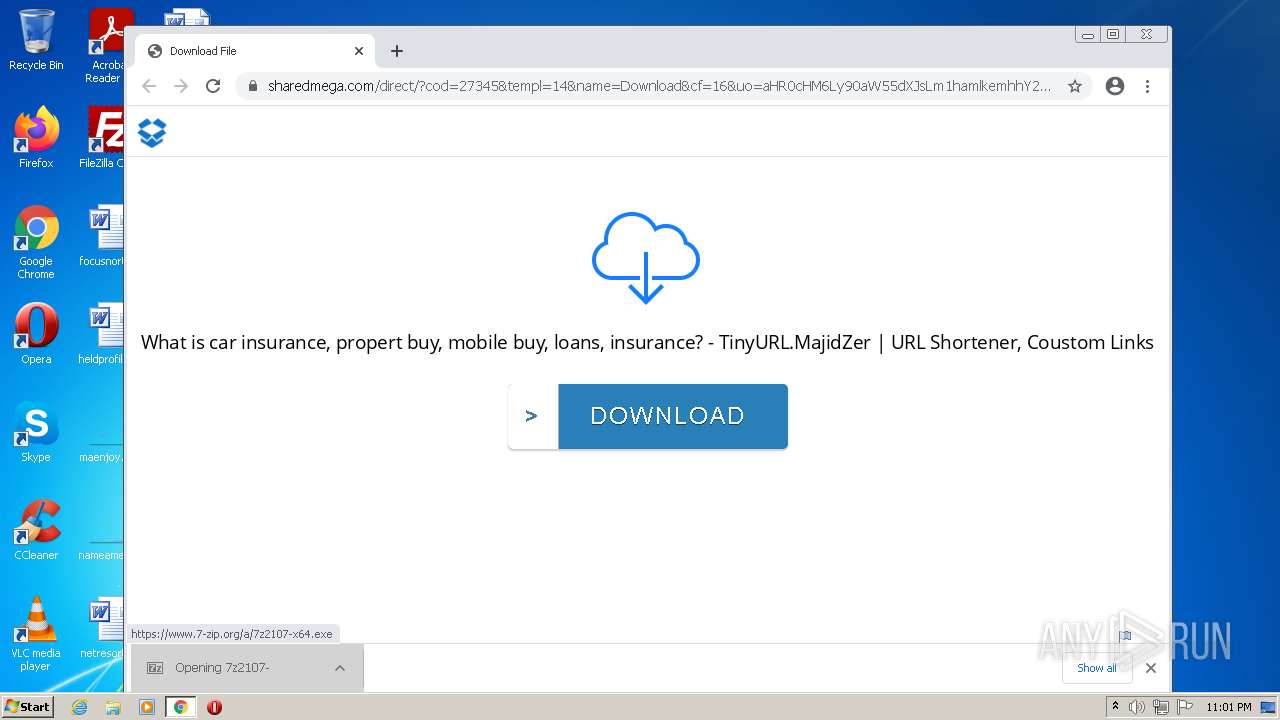
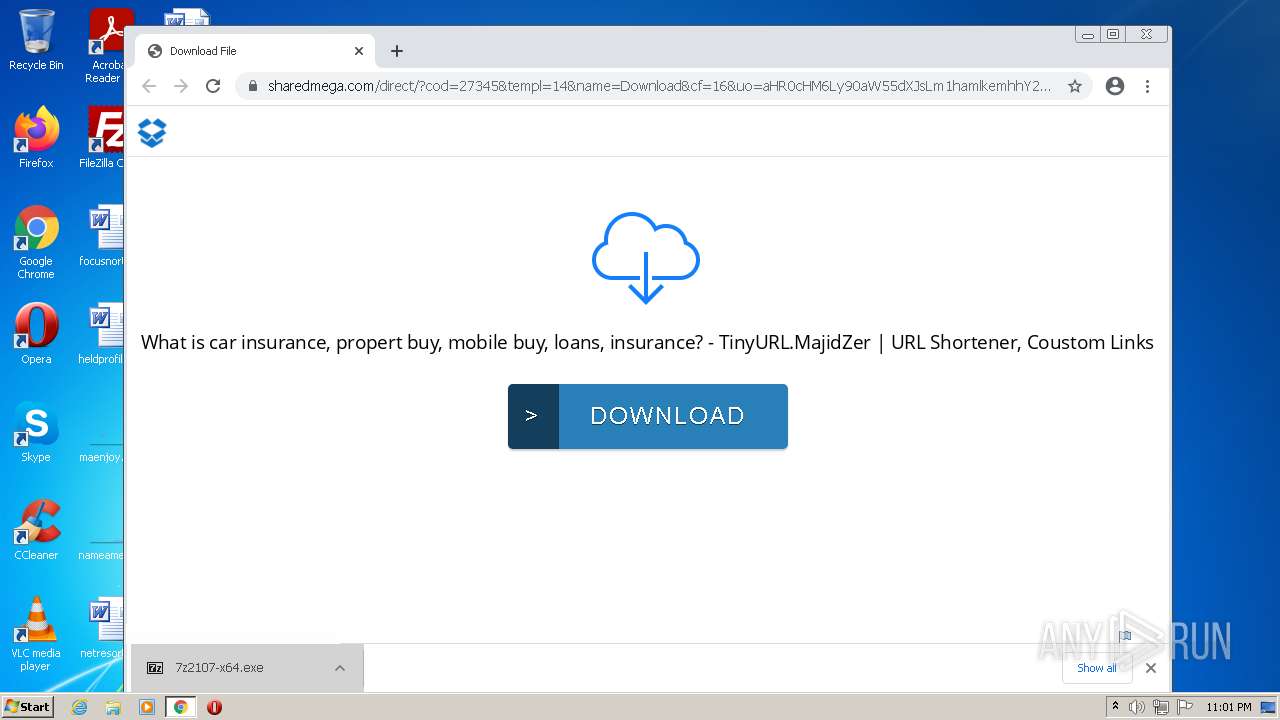
| URL: | https://tinyurl.majidzhacker.com/2019/08/shorten-create-and-share-trusted.html#?o=57a1dd5a9707a8e5bfa839079740b88b7829ea0082b88a6600f8e91641c63717e15b1f85cd54e24c8dd32c9a11fff0ae12336a4e63cbf3c93b1135a87dc8a733c288237ff08b093e5093f3e132fa2863d11056d66162c786 |
| Full analysis: | https://app.any.run/tasks/9151b8bf-c550-434b-aab7-b93e1a66b87d |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 21:59:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
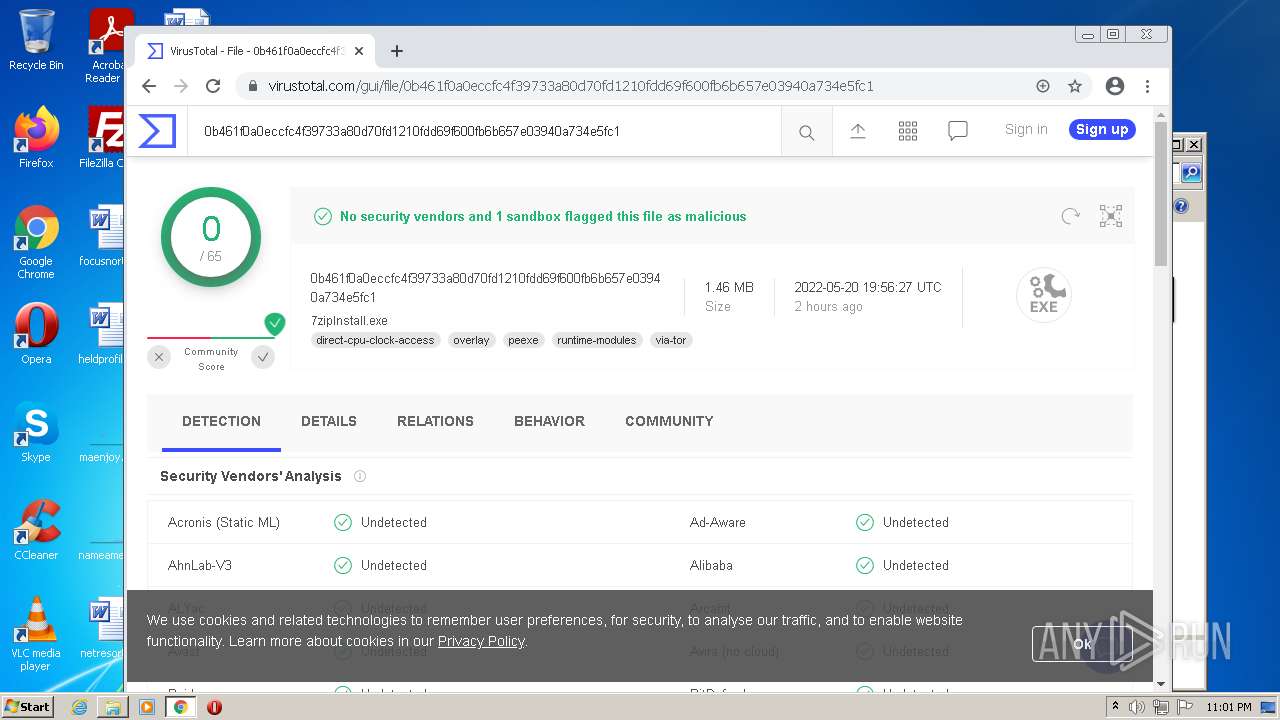
| MD5: | 0E3A47AFDCAE922E9331A03D719F01F0 |
| SHA1: | 04C903107F2DC0F7F147A6B114B0E37BD2F9BC07 |
| SHA256: | 54A6B7C9E51616760225040DAD9ED7AC1D95BB96E2E1DC873EF8302871A7F7E0 |
| SSDEEP: | 6:2EnkvQJMPVIkVKqIM9pC8GZkUmbvyxdcW0jMTH2Jyjn:2EnkvQ0VTIM9pCJECn0jMTH2Ijn |
MALICIOUS
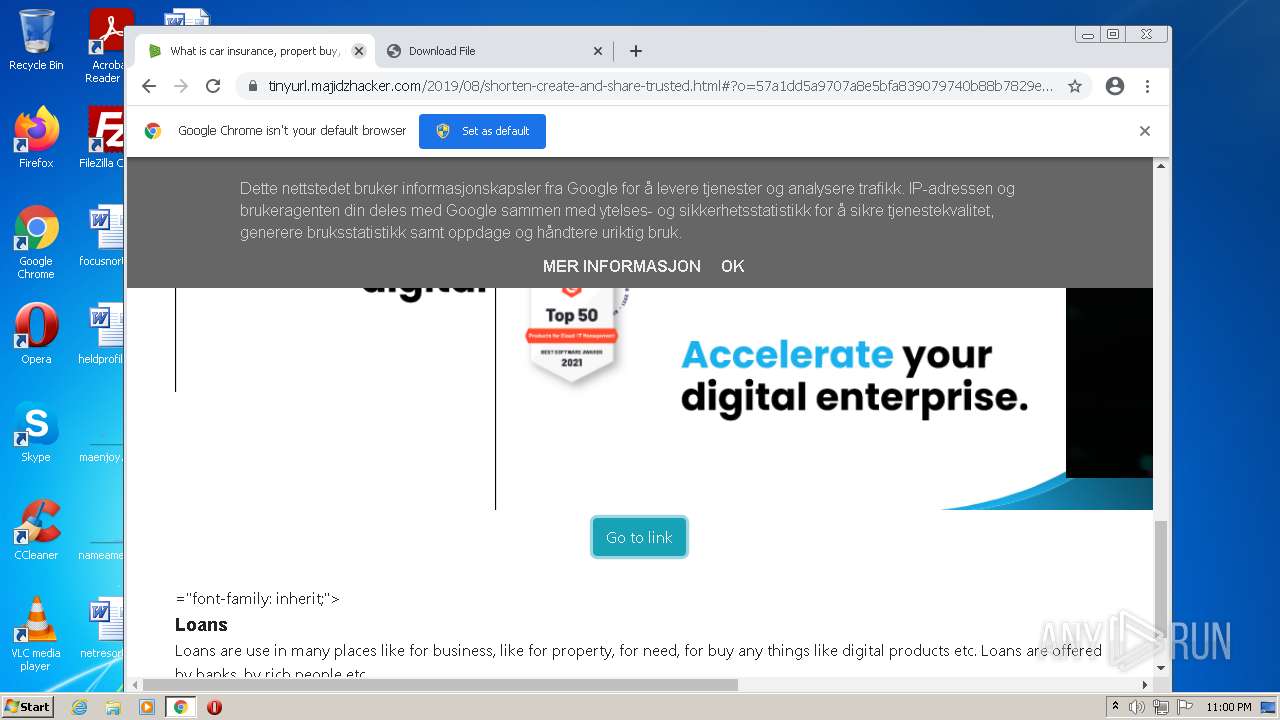
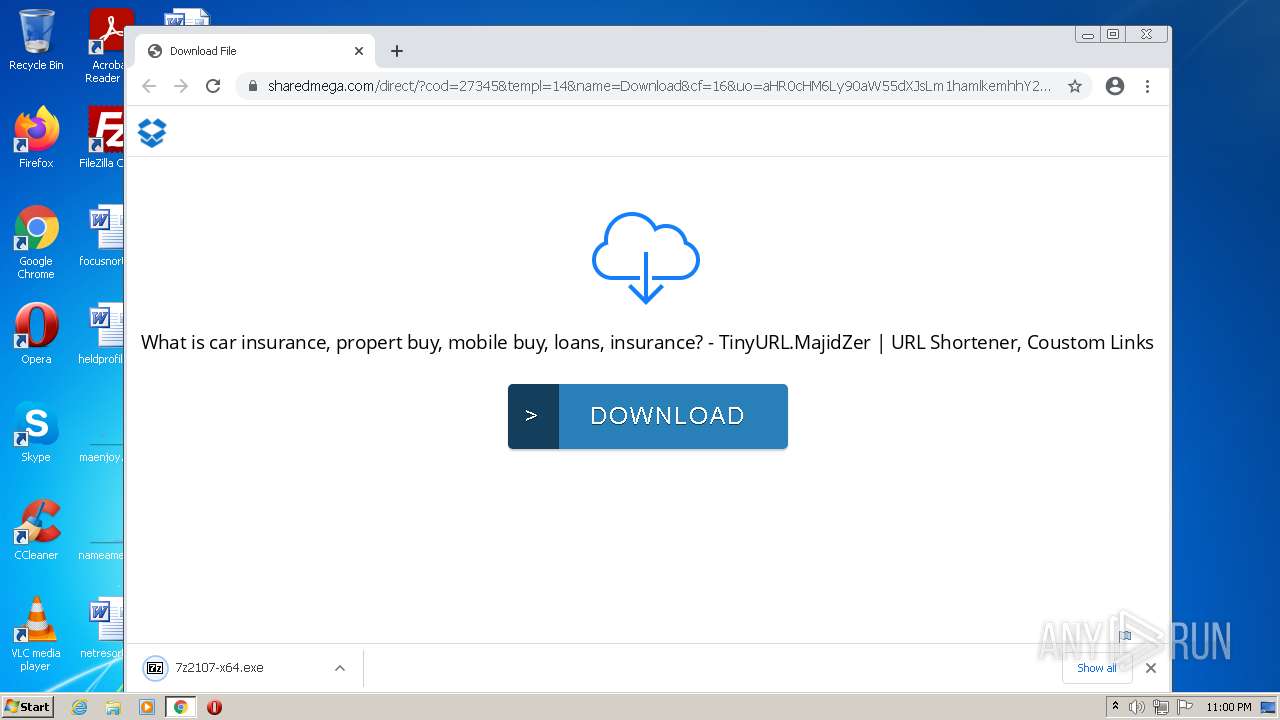
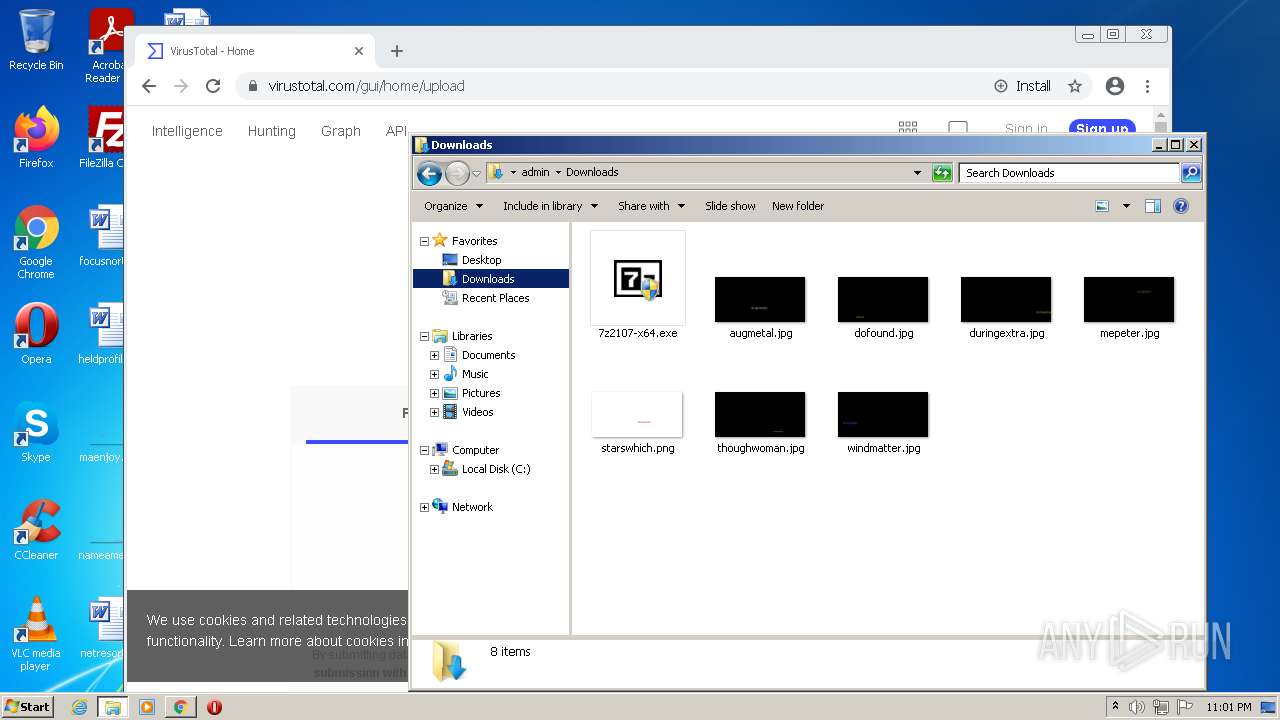
Drops executable file immediately after starts
- chrome.exe (PID: 476)
- chrome.exe (PID: 3560)
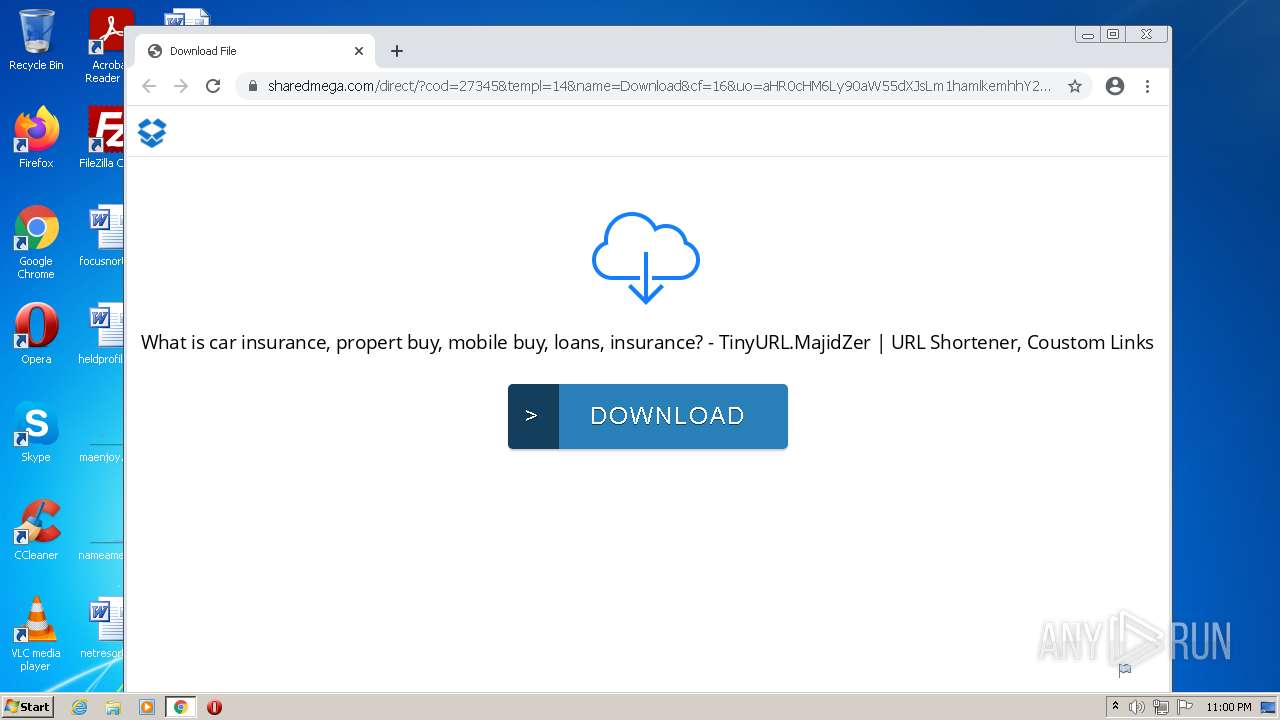
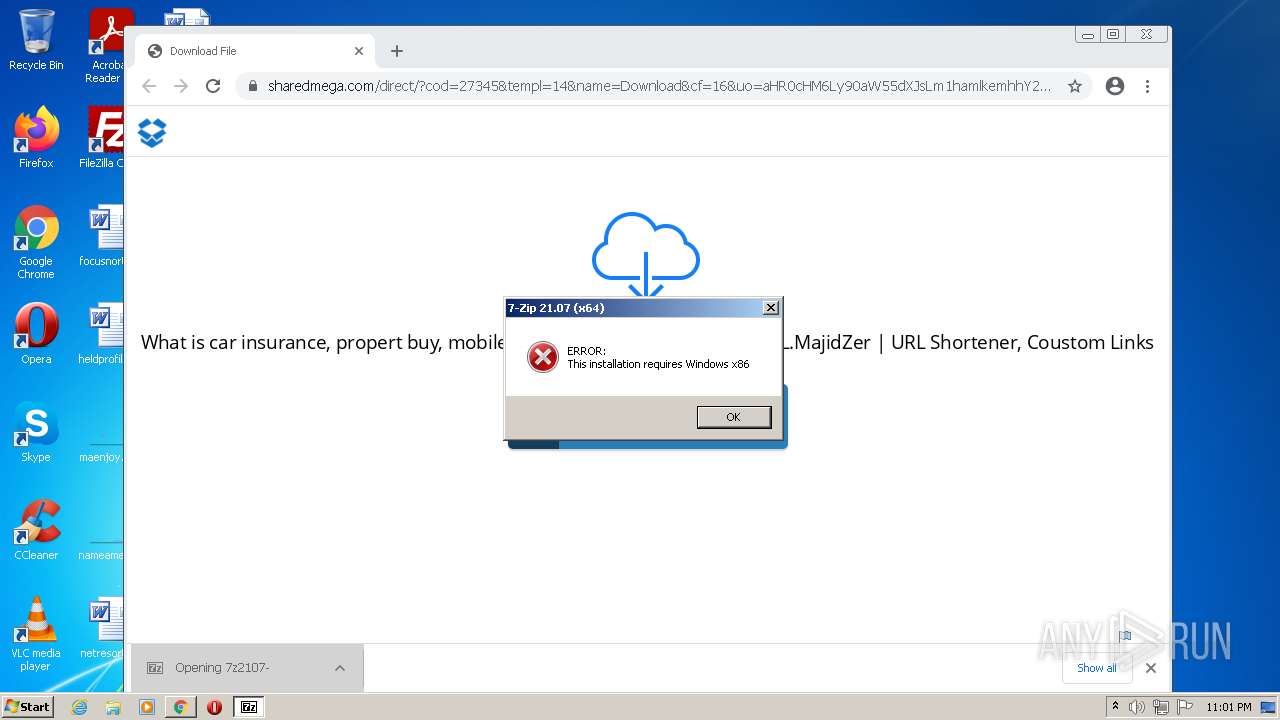
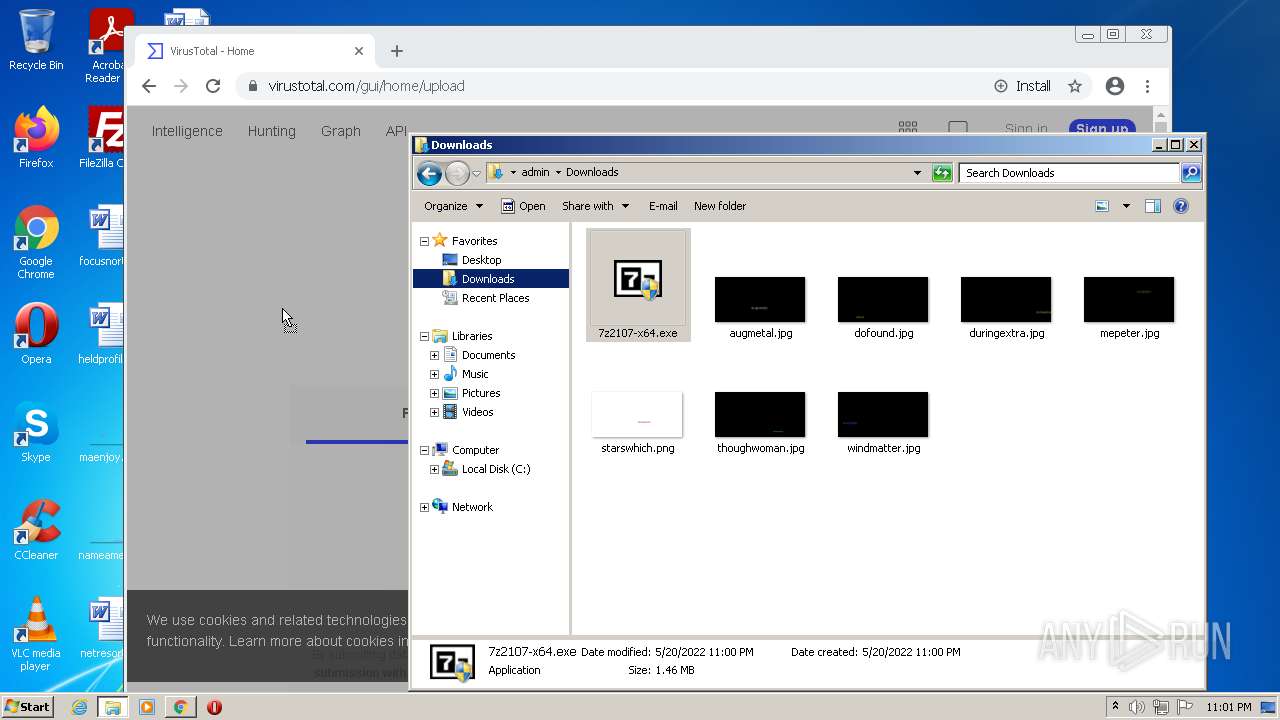
Application was dropped or rewritten from another process
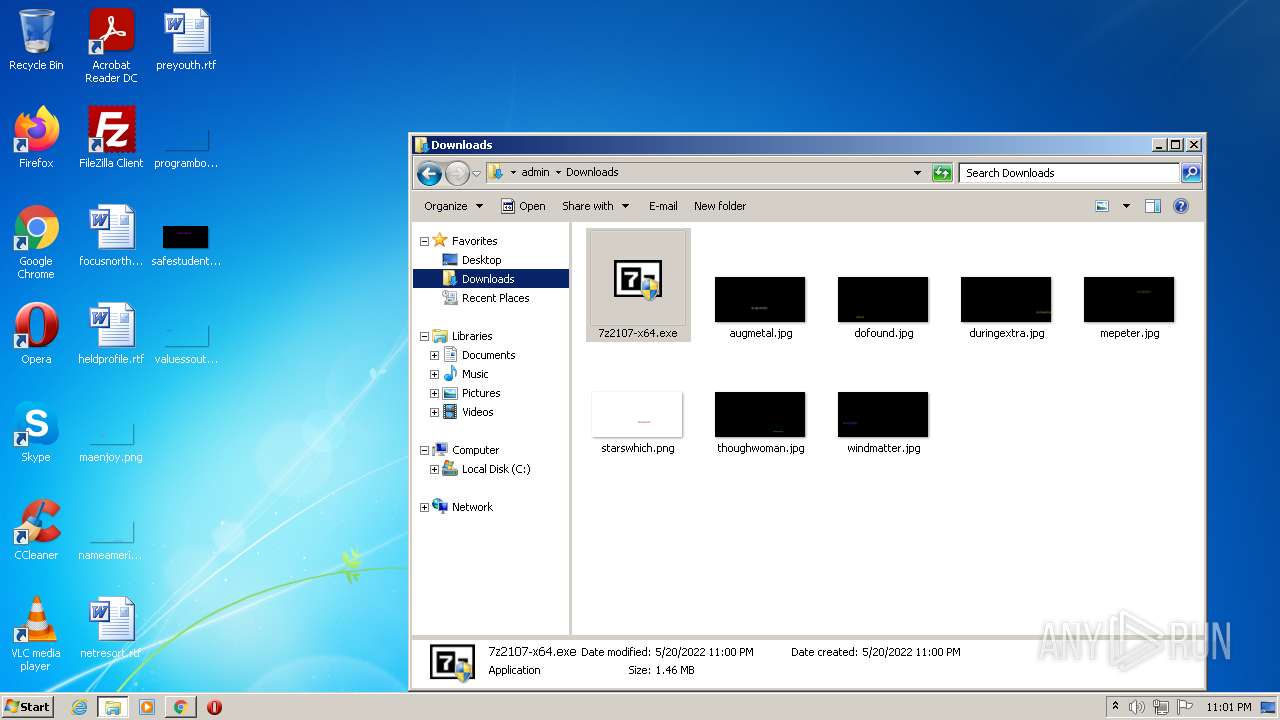
- 7z2107-x64.exe (PID: 912)
- 7z2107-x64.exe (PID: 2604)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1396)
- iexplore.exe (PID: 2868)
Modifies files in Chrome extension folder
- chrome.exe (PID: 476)
Executable content was dropped or overwritten
- chrome.exe (PID: 476)
- chrome.exe (PID: 3560)
Drops a file with a compile date too recent
- chrome.exe (PID: 3560)
- chrome.exe (PID: 476)
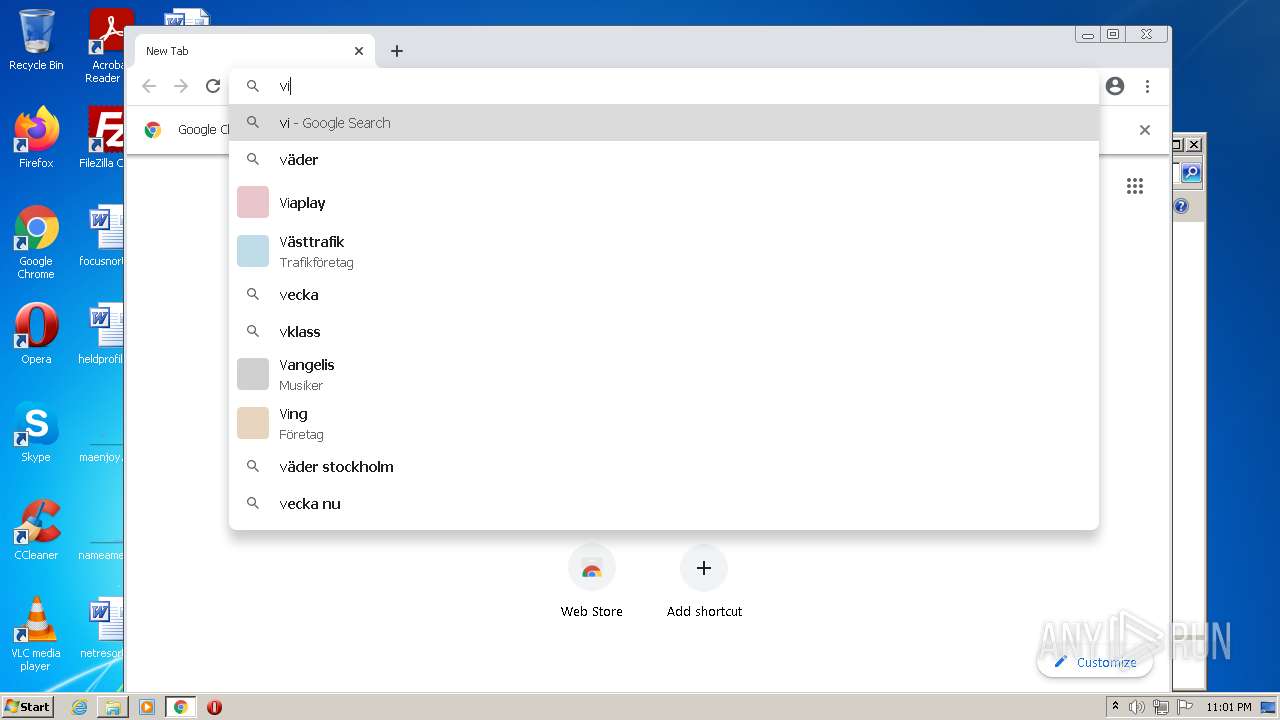
Checks supported languages
- 7z2107-x64.exe (PID: 2604)
INFO
Reads the computer name
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 1396)
- chrome.exe (PID: 476)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 468)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2868)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2656)
- explorer.exe (PID: 4080)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 1596)
Application launched itself
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 476)
- chrome.exe (PID: 2796)
- iexplore.exe (PID: 2760)
Changes internet zones settings
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 2760)
Checks supported languages
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 1396)
- chrome.exe (PID: 476)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 292)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 688)
- chrome.exe (PID: 432)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 468)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2868)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 532)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 3224)
- explorer.exe (PID: 4080)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 364)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 768)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3620)
- chrome.exe (PID: 2868)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 1596)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2156)
Reads settings of System Certificates
- iexplore.exe (PID: 1396)
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 2796)
Checks Windows Trust Settings
- iexplore.exe (PID: 1396)
- iexplore.exe (PID: 2944)
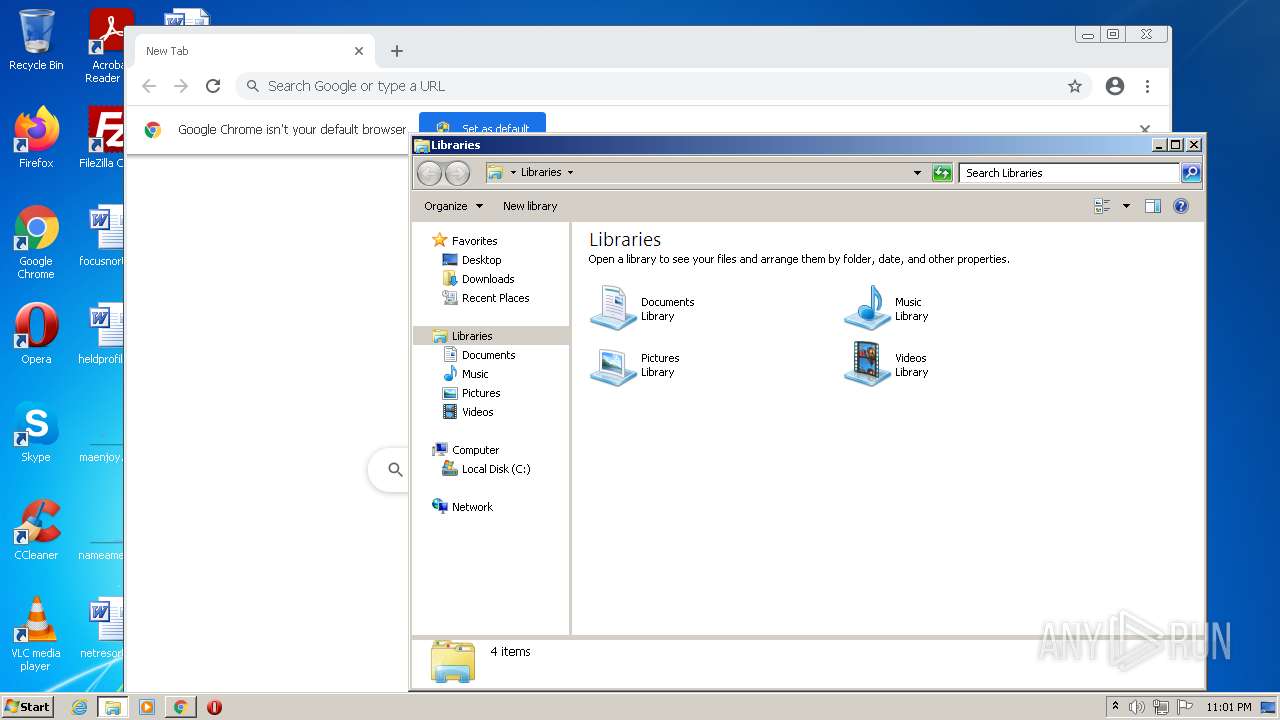
Creates files in the user directory
- iexplore.exe (PID: 1396)
Reads the date of Windows installation
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 3580)
- iexplore.exe (PID: 2760)
- chrome.exe (PID: 1596)
Reads internet explorer settings
- iexplore.exe (PID: 1396)
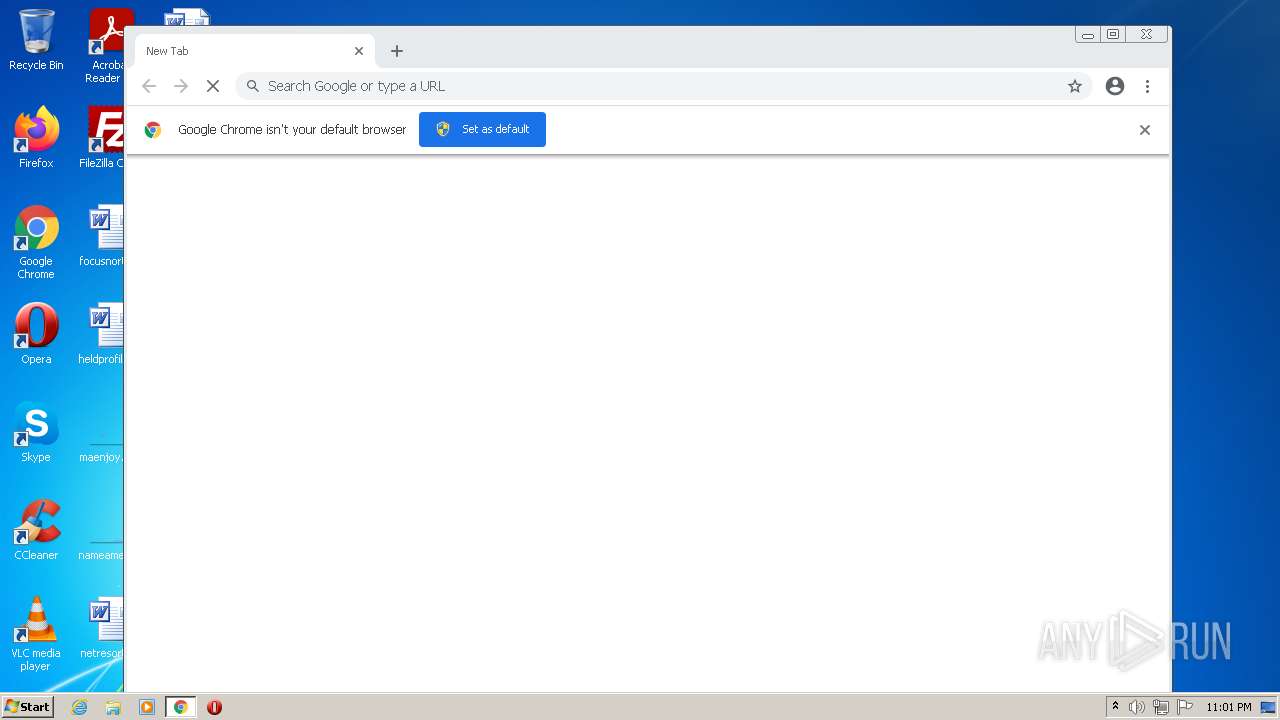
Manual execution by user
- chrome.exe (PID: 476)
- iexplore.exe (PID: 2760)
- chrome.exe (PID: 2796)
- explorer.exe (PID: 4080)
Reads the hosts file
- chrome.exe (PID: 476)
- chrome.exe (PID: 3560)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 3624)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
110
Monitored processes
64
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,10751083063660231314,6794611900855972956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2848 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,7060626784666331197,1394142555881096034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3720 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10751083063660231314,6794611900855972956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,10751083063660231314,6794611900855972956,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --field-trial-handle=1040,7060626784666331197,1394142555881096034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,10751083063660231314,6794611900855972956,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3692 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7060626784666331197,1394142555881096034,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 912 | "C:\Users\admin\Downloads\7z2107-x64.exe" | C:\Users\admin\Downloads\7z2107-x64.exe | — | chrome.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 21.07 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,7060626784666331197,1394142555881096034,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
39 203
Read events
38 615
Write events
583
Delete events
5
Modification events
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960788 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960788 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
287
Text files
262
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\shorten-create-and-share-trusted[1].htm | html | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 1396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E87CE99F124623F95572A696C80EFCAF_609ACDACD474234BBB2272FC20821323 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
162
DNS requests
95
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1396 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFsL8ccV6MRJElibH7RYju4%3D | US | der | 471 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBI3POrj%2FdCwCsU2CxA305s%3D | US | der | 471 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCHXS%2FWwGsOSRJbmAIB8NC3 | US | der | 472 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG3aTvFLTYzNCmxS2fUJutw%3D | US | der | 471 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1396 | iexplore.exe | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1e501821bc2be913 | US | compressed | 60.0 Kb | whitelisted |
1396 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDExSUZ712qmxLhqE9UUaDV | US | der | 472 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDiYhVuiqGgGClac6iAn%2FuM%3D | US | der | 471 b | whitelisted |
1396 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1396 | iexplore.exe | 188.114.97.10:443 | tinyurl.majidzhacker.com | Cloudflare Inc | US | malicious |
1396 | iexplore.exe | 142.250.185.202:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
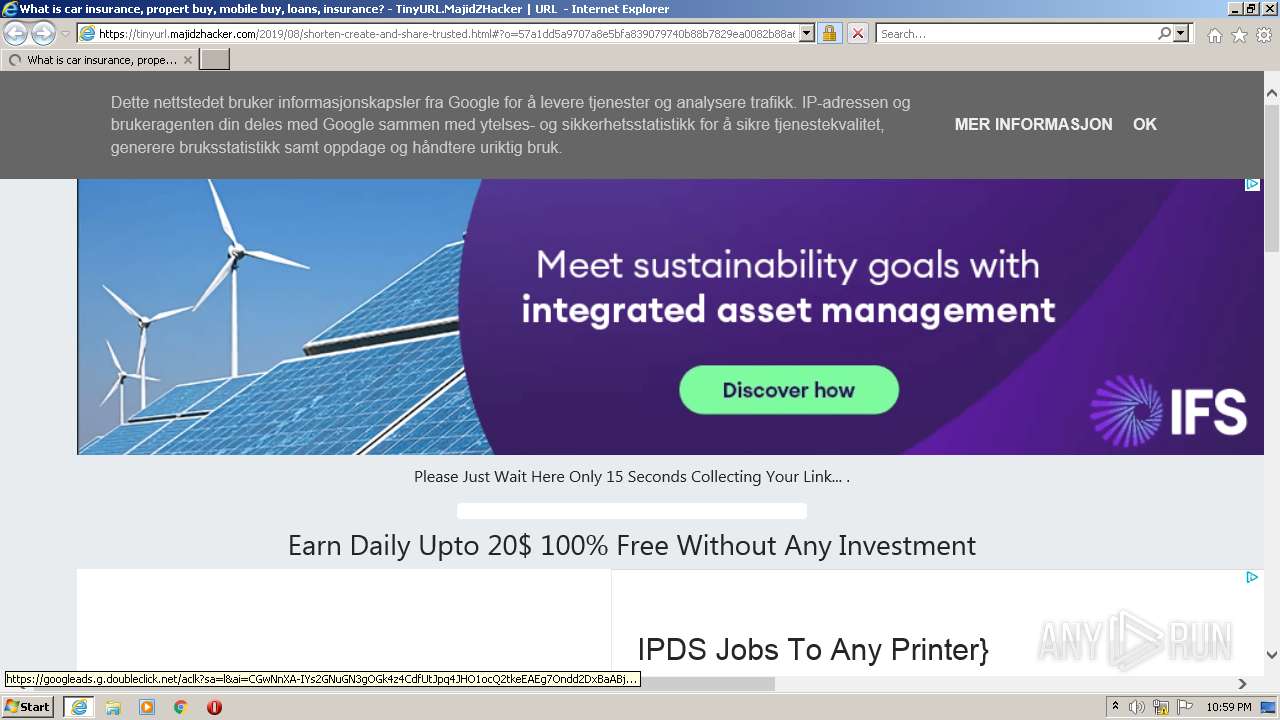
1396 | iexplore.exe | 142.250.186.98:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
2944 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1396 | iexplore.exe | 142.250.184.201:443 | www.blogger.com | Google Inc. | US | unknown |
1396 | iexplore.exe | 199.232.192.134:443 | kamran-jaisak-1.disqus.com | — | US | suspicious |
1396 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2944 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1396 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
1396 | iexplore.exe | 172.217.18.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tinyurl.majidzhacker.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.blogger.com |
| shared |
ocsp.pki.goog |
| whitelisted |