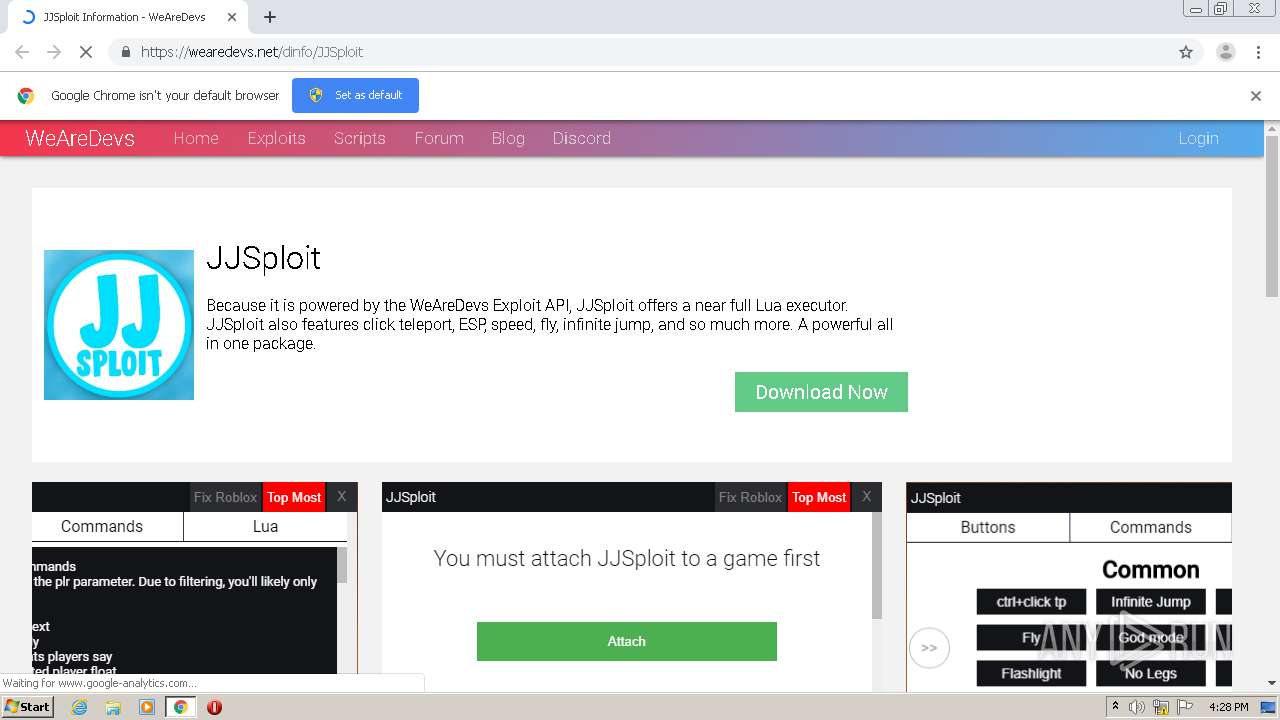
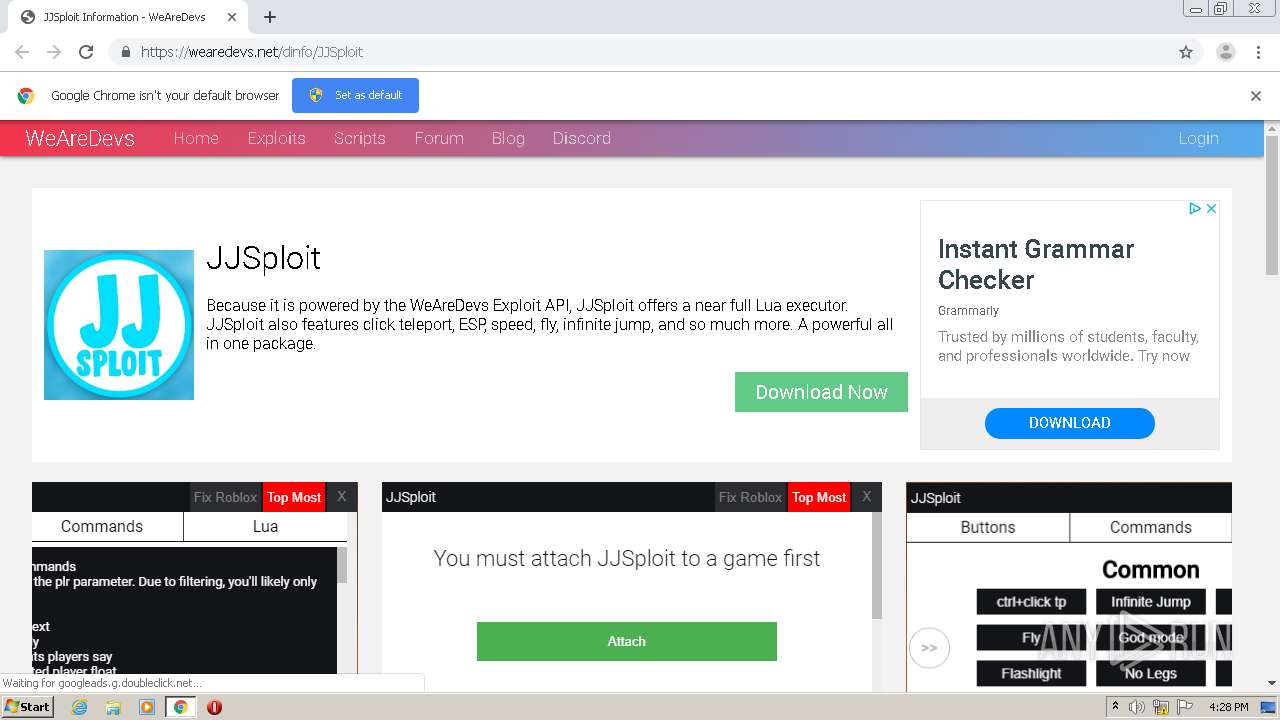
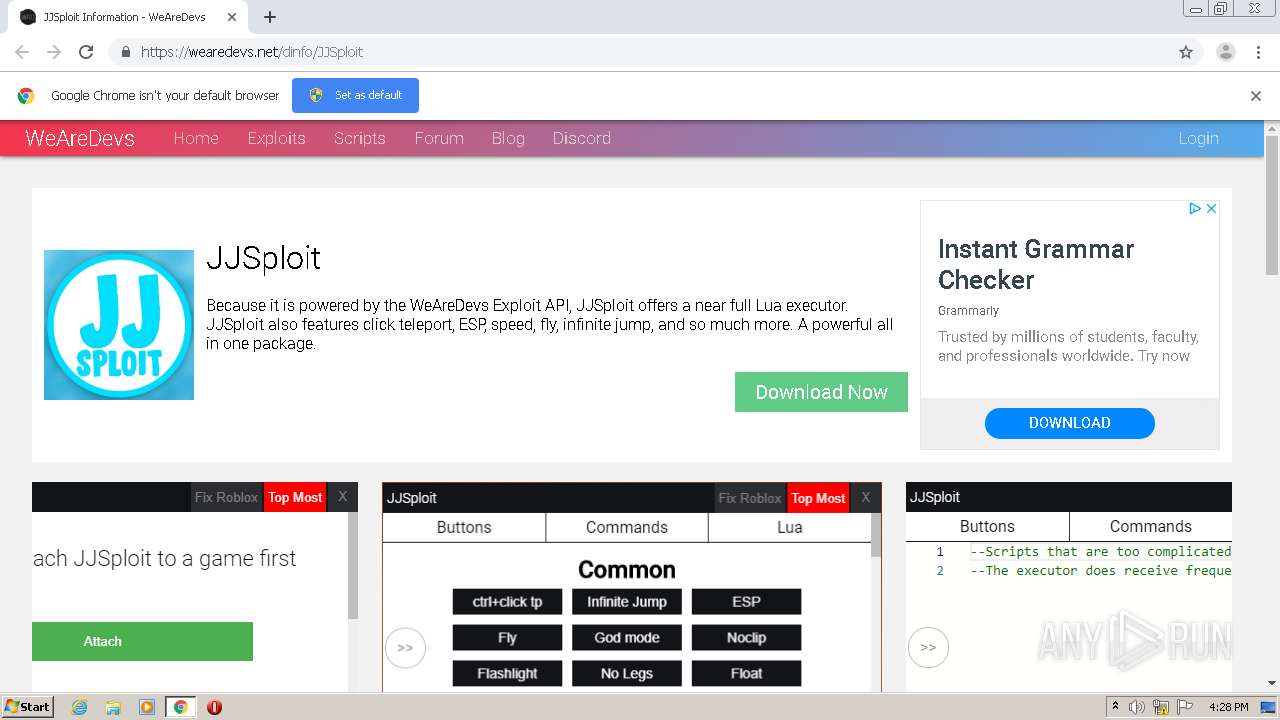
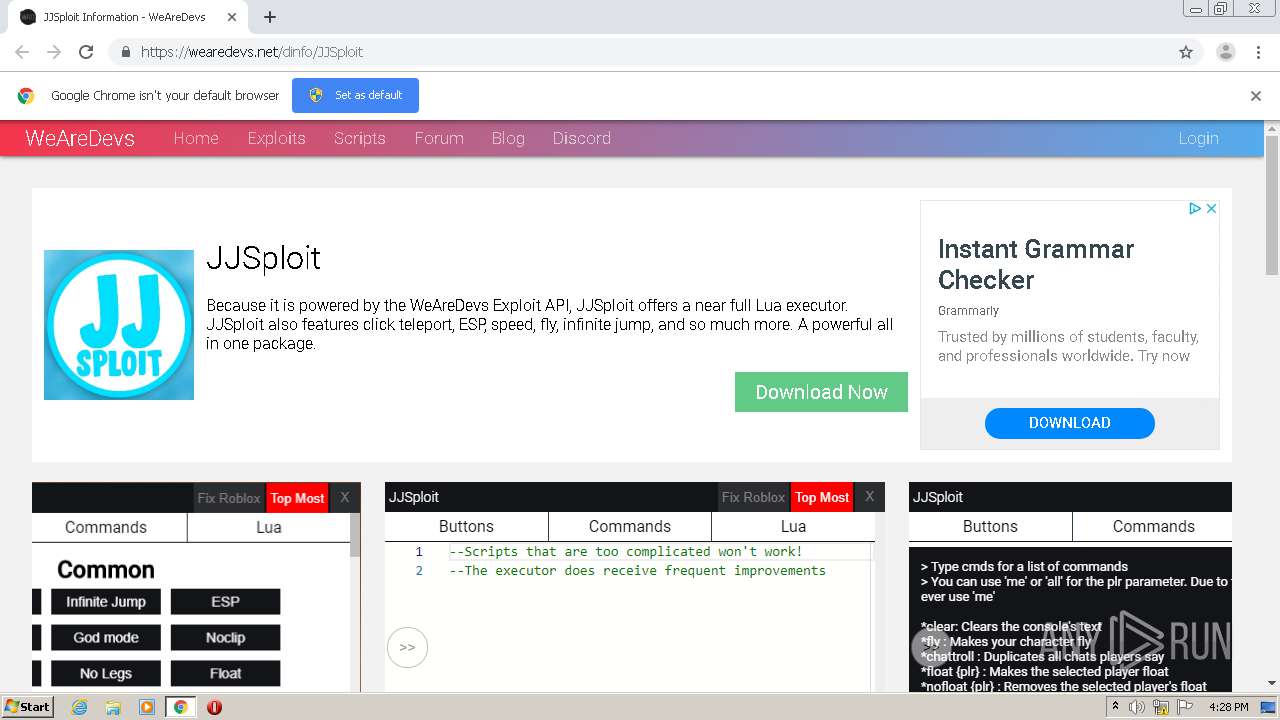
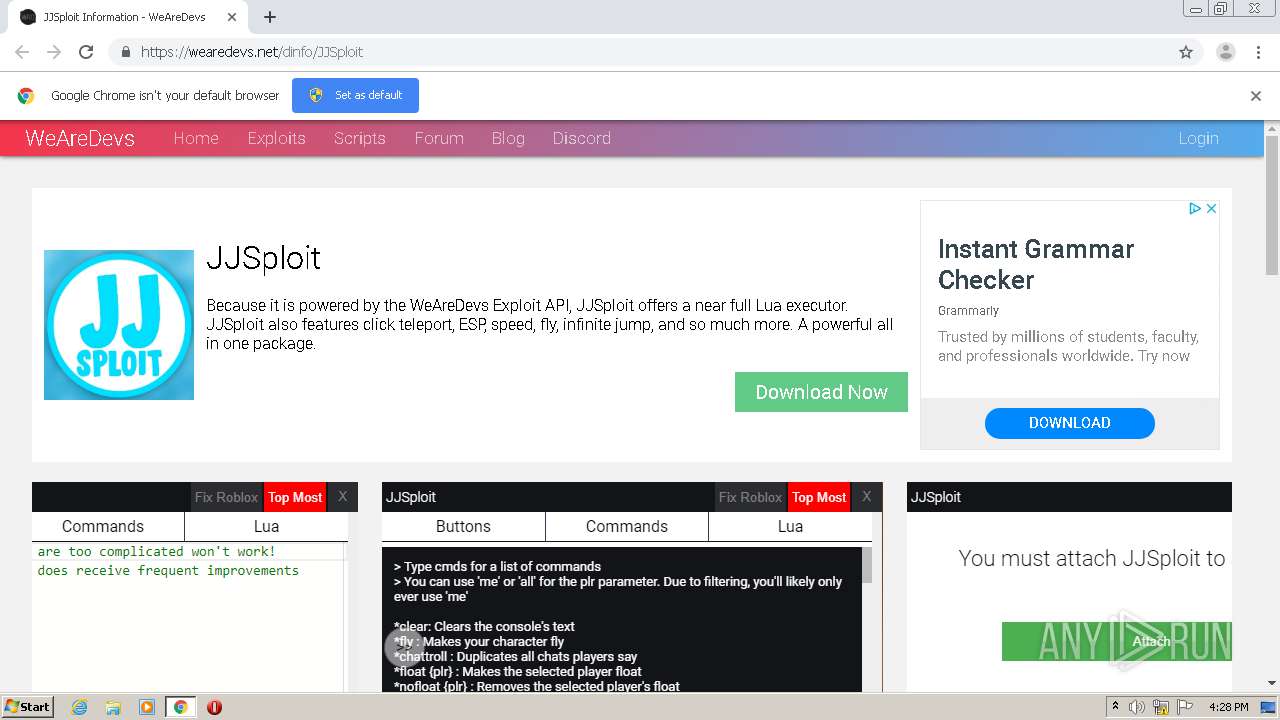
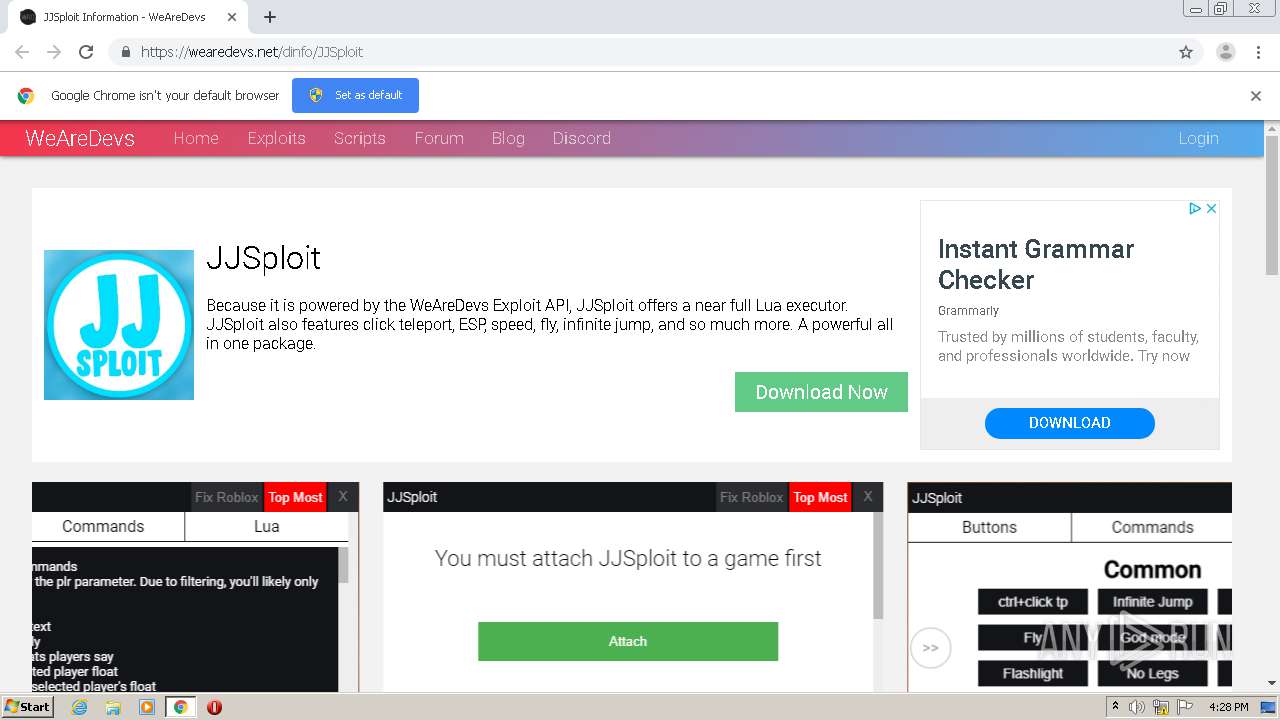
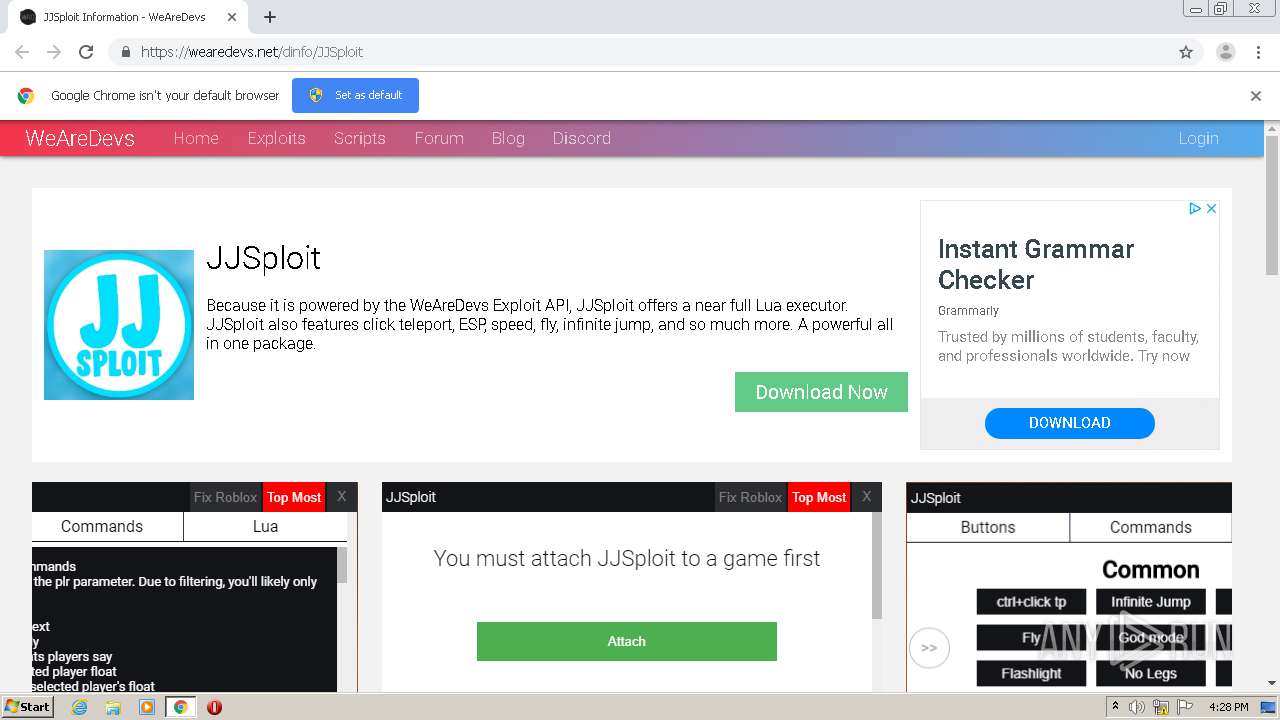
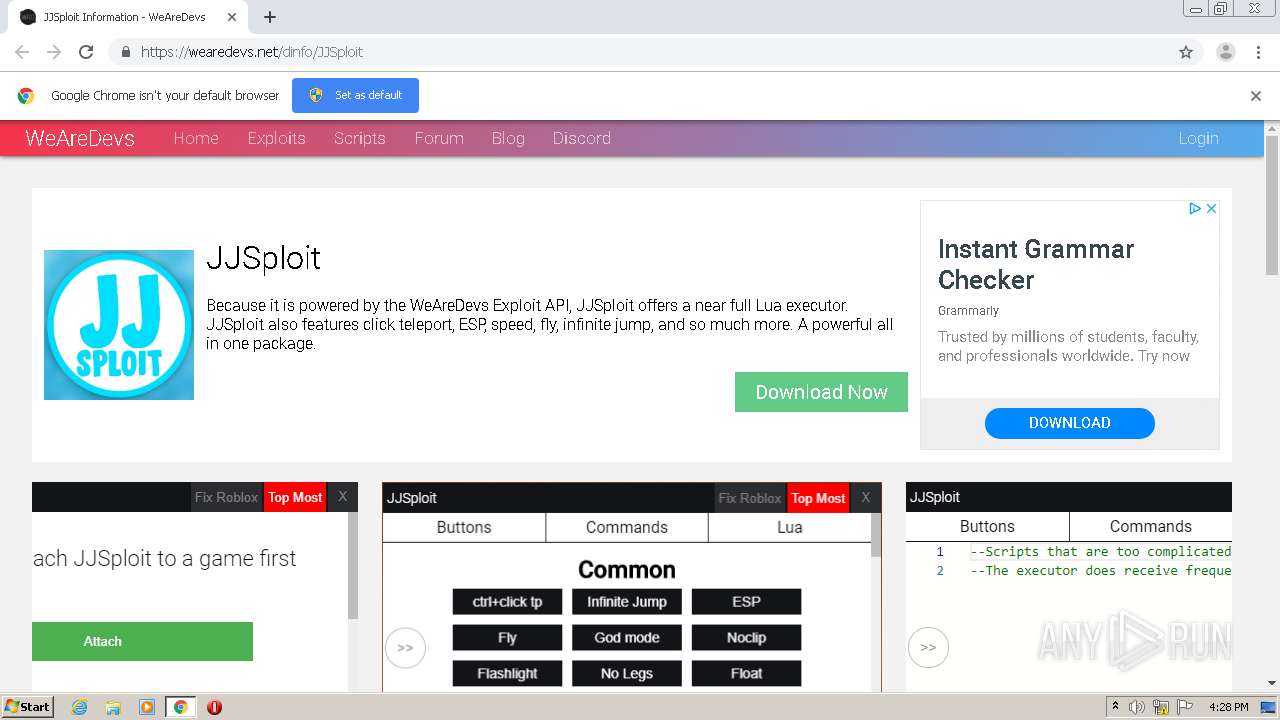
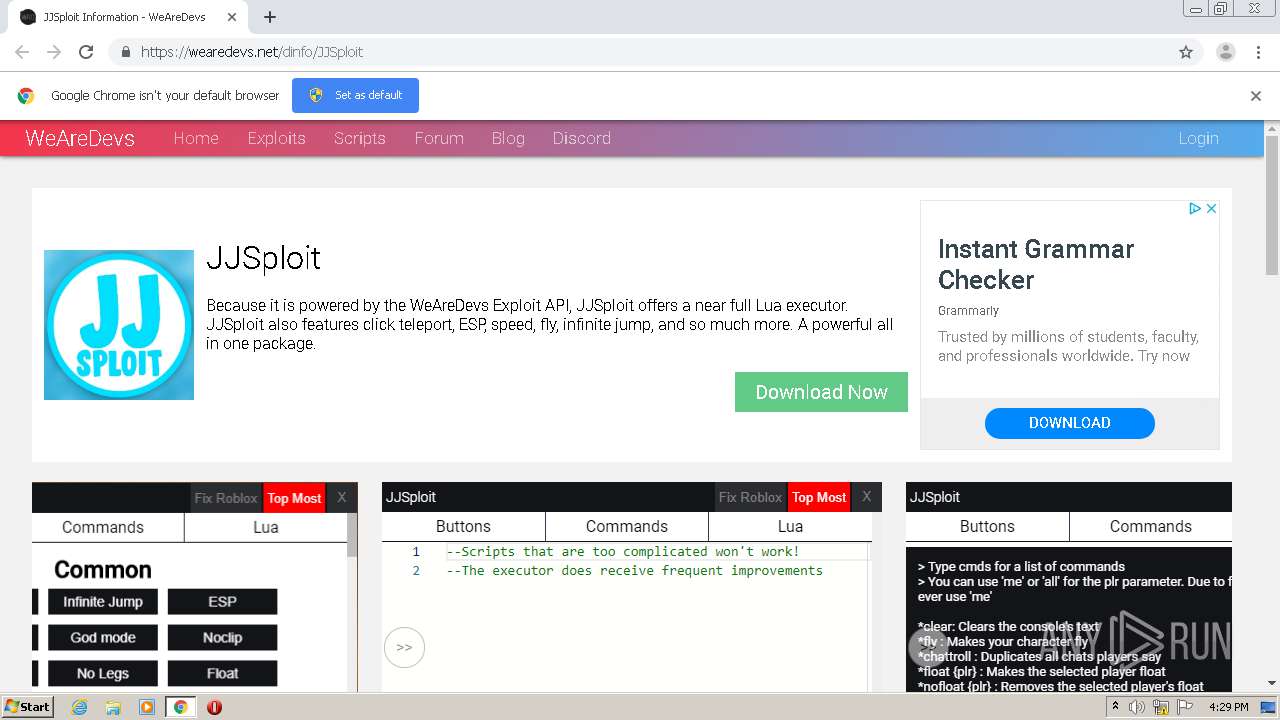
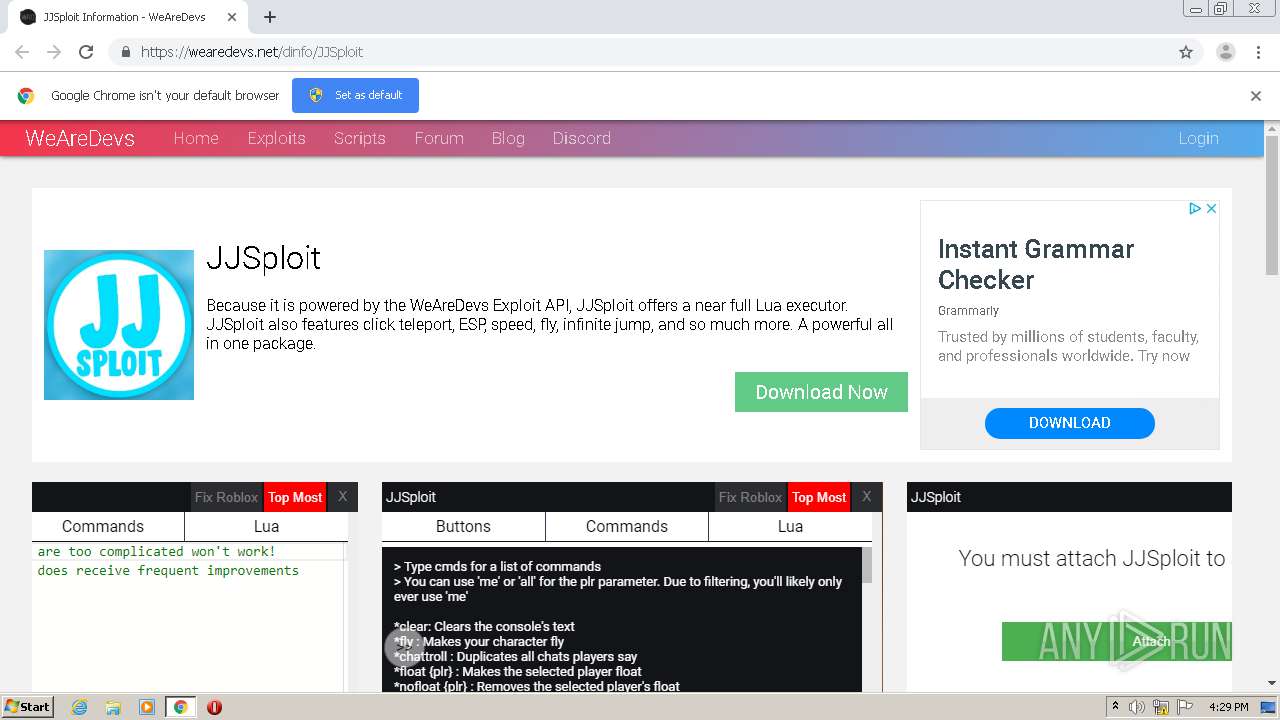
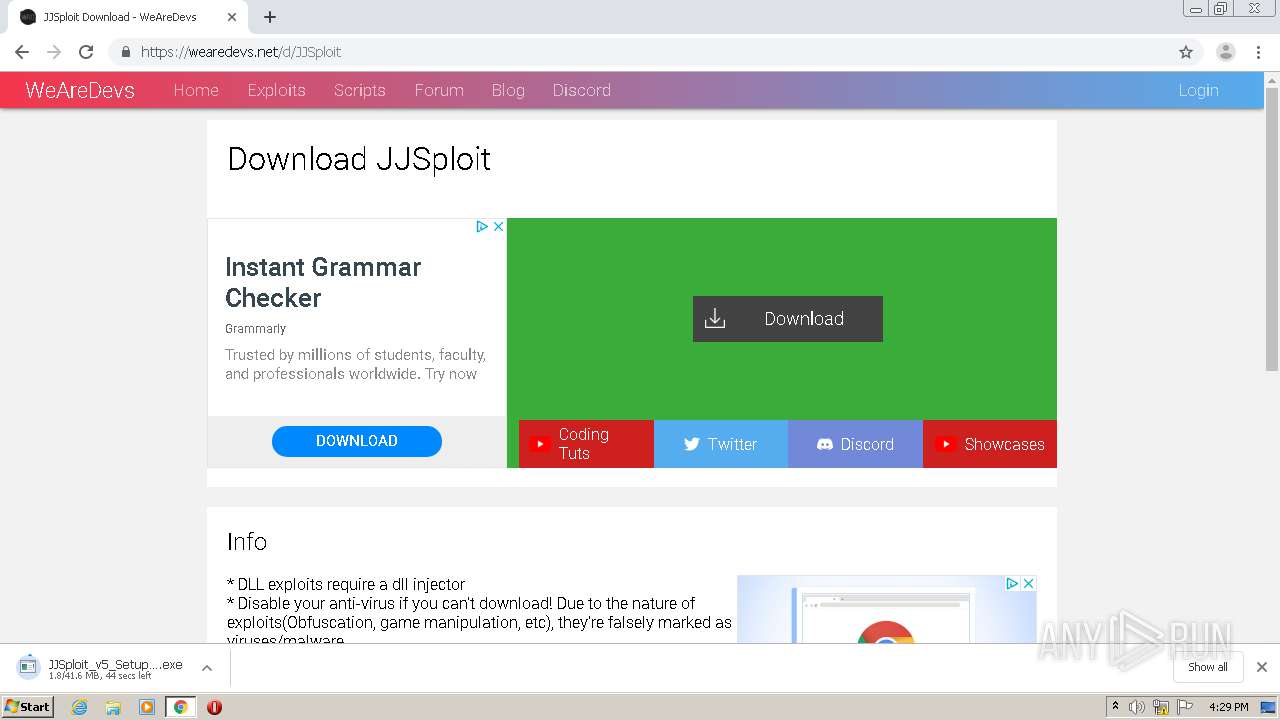
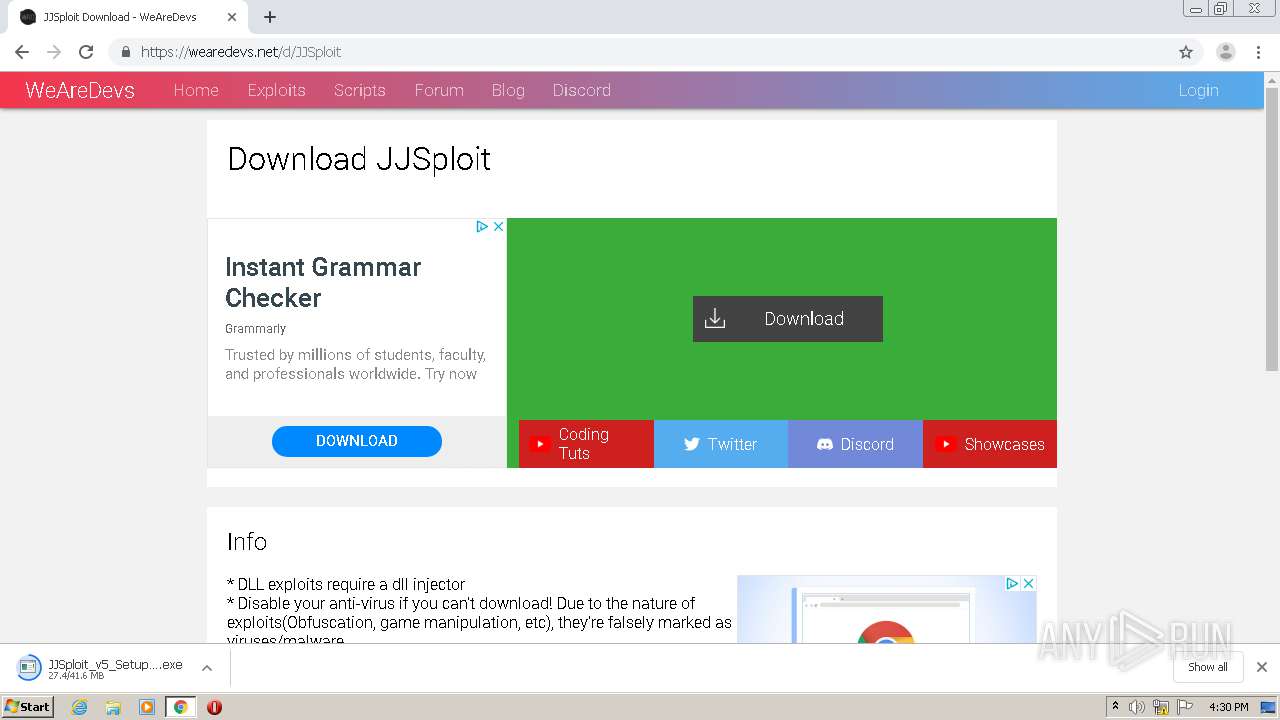
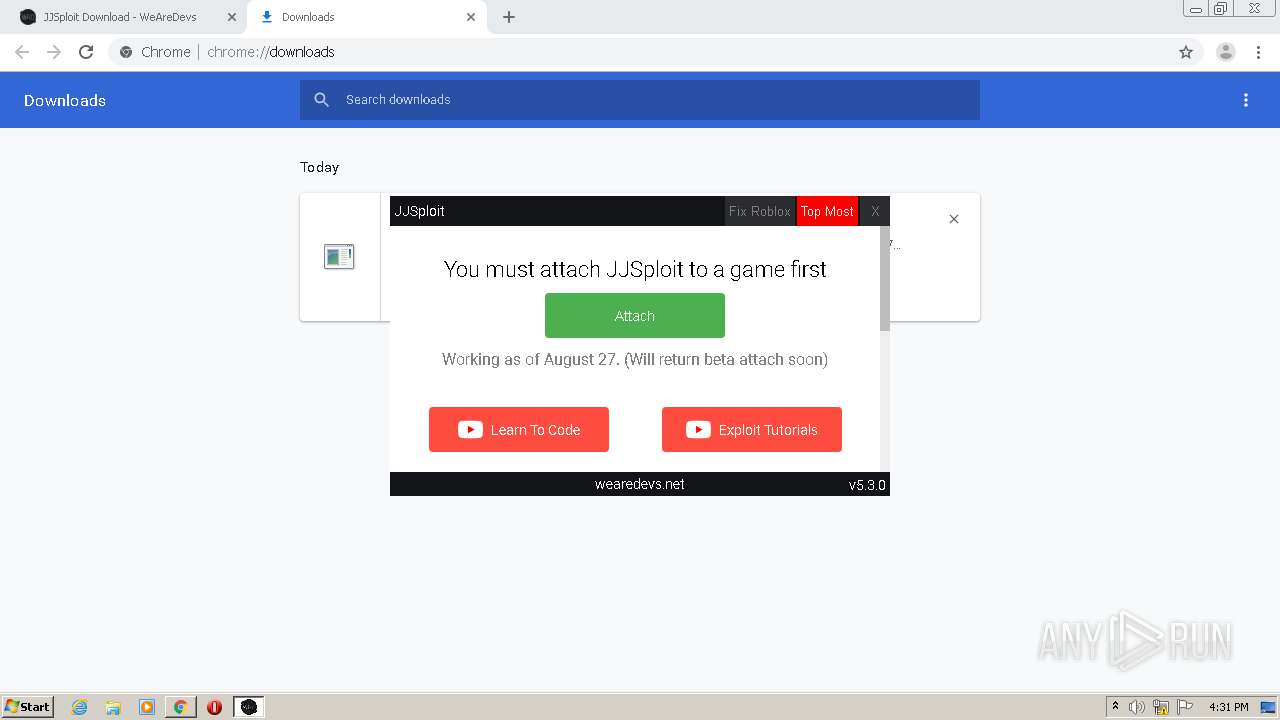
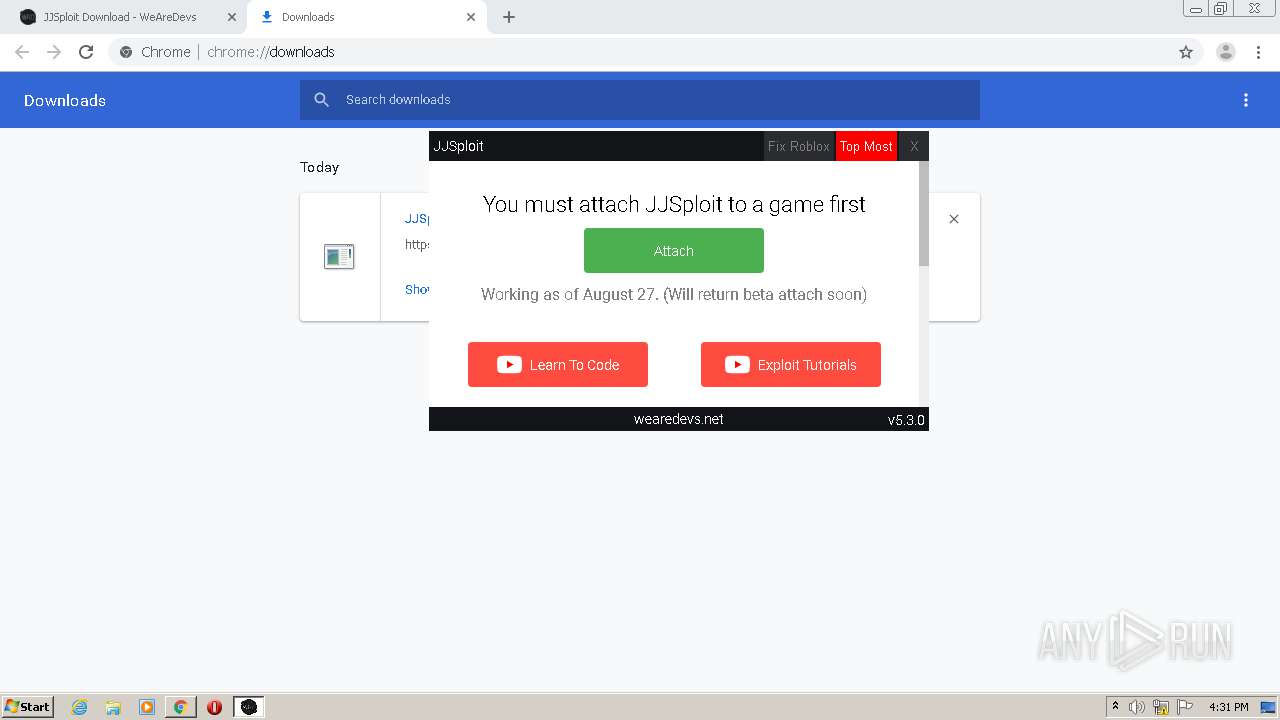
| URL: | https://wearedevs.net/dinfo/JJSploit |
| Full analysis: | https://app.any.run/tasks/fa78ddd7-7d78-4cd4-b9b2-d1feb05aab42 |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2020, 15:28:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 07DDE833BD9948E0F74CBC3EF5FBE58F |
| SHA1: | 7338CB74861EB0C6DC3E29BE77F80EFA4B2199F6 |
| SHA256: | 549F6209F5D22E30628C8B6F453081112CA18F18EB2027019669130352A902B7 |
| SSDEEP: | 3:N8R/BApK6LDKKKKQ:25BuHLWFB |
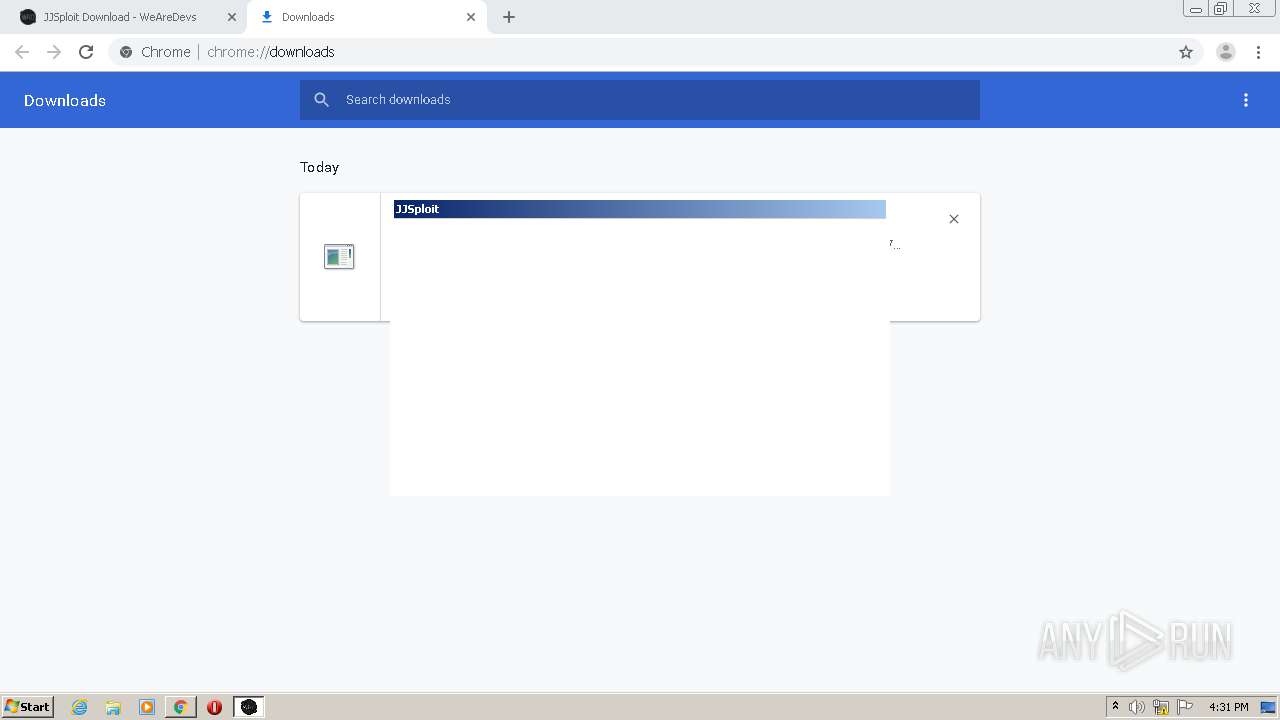
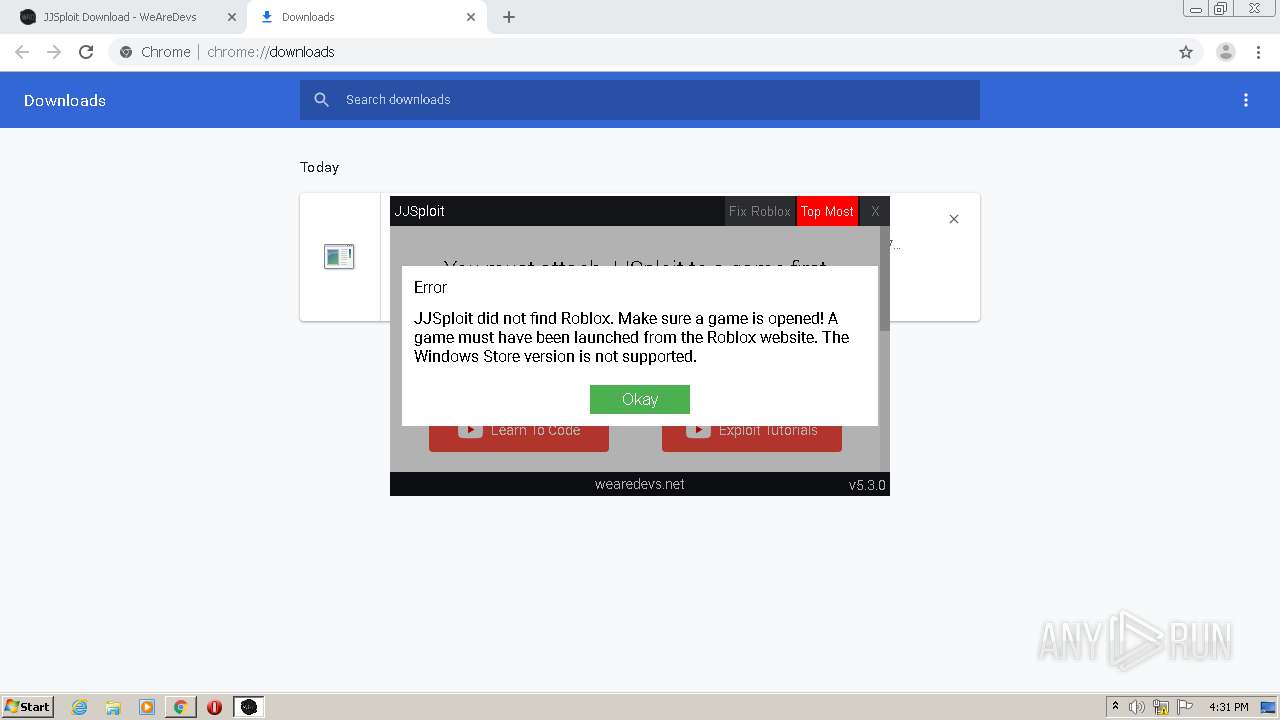
MALICIOUS
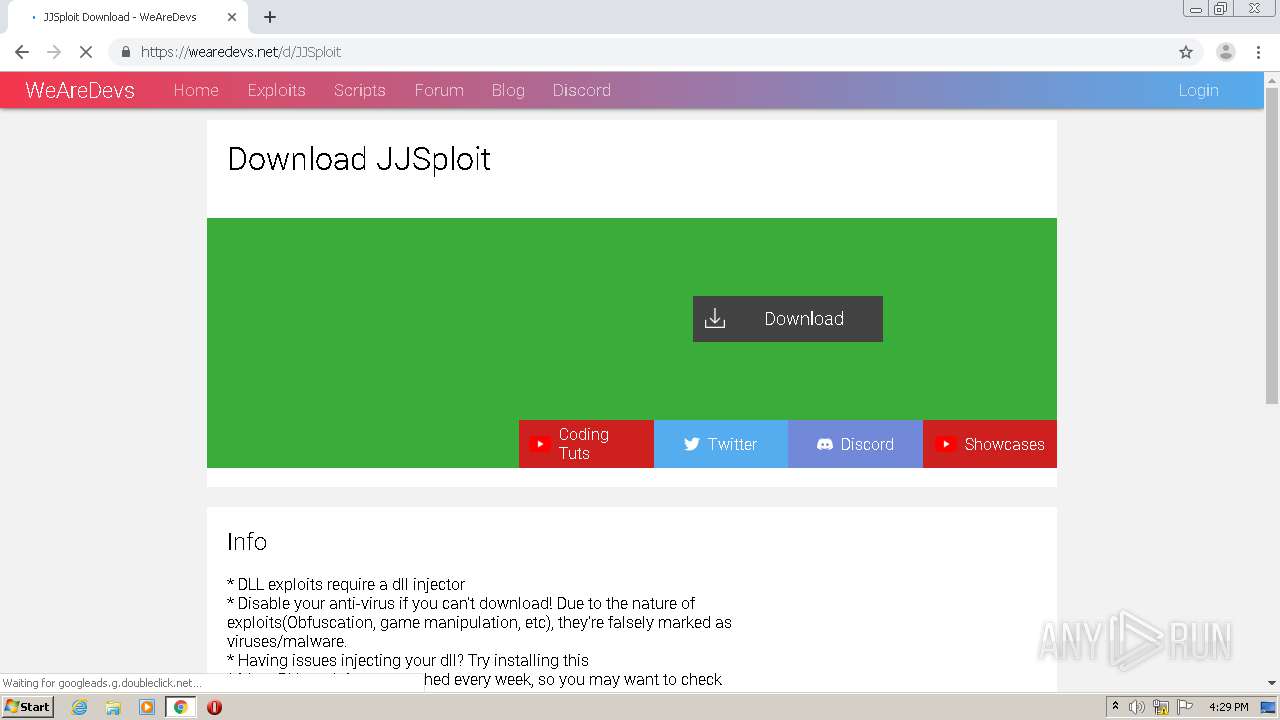
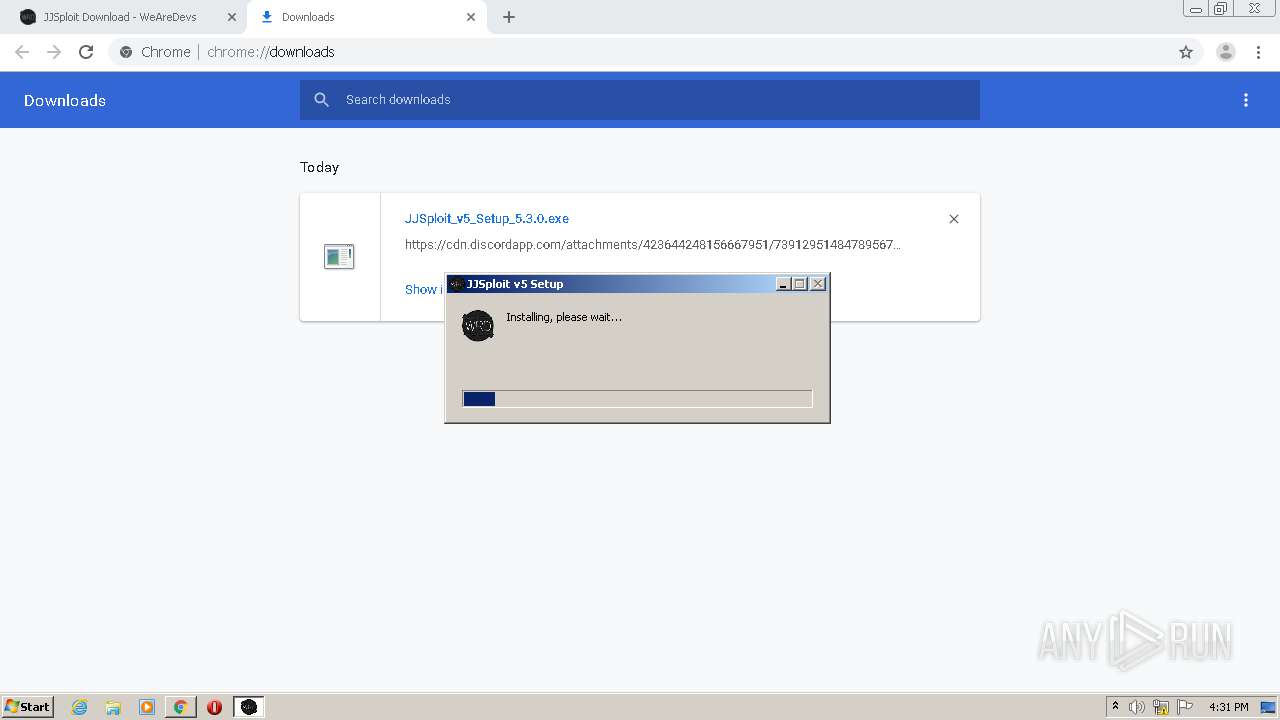
Loads dropped or rewritten executable
- JJSploit v5.exe (PID: 2192)
- JJSploit v5.exe (PID: 2096)
- JJSploit_v5_Setup_5.3.0.exe (PID: 1556)
- JJSploit v5.exe (PID: 3764)
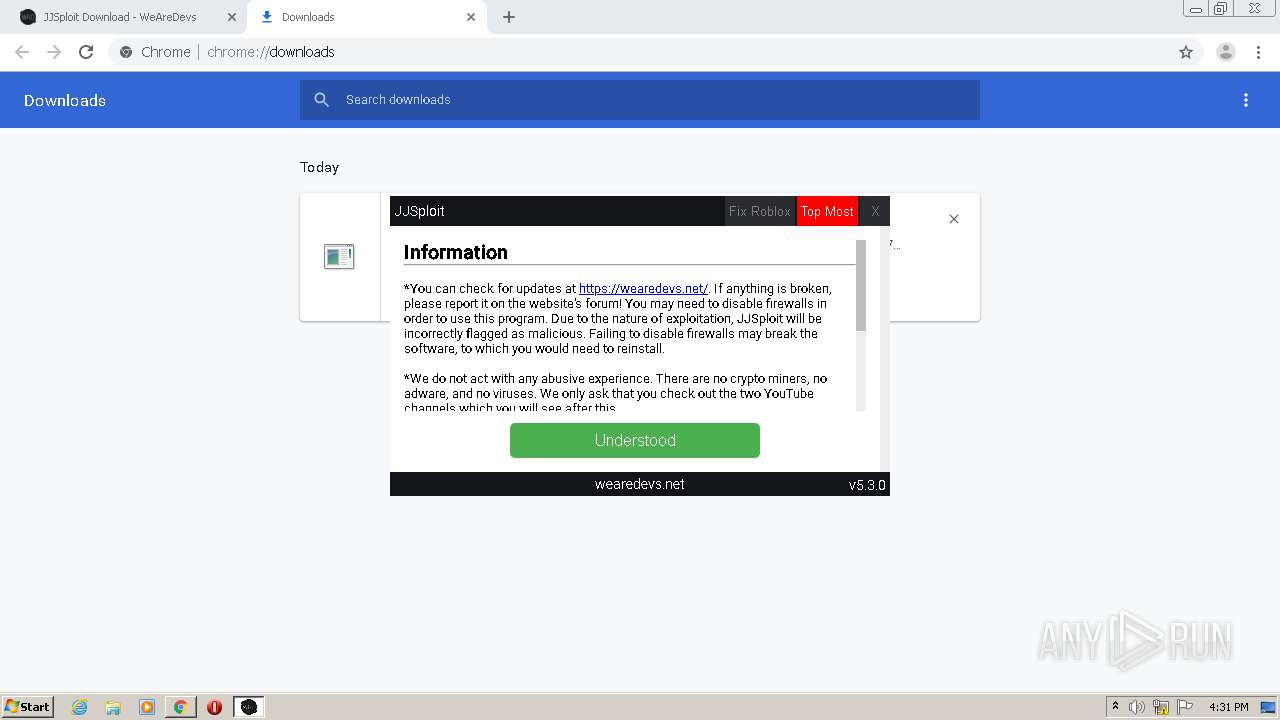
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.3.0.exe (PID: 1556)
SUSPICIOUS
Creates files in the user directory
- JJSploit_v5_Setup_5.3.0.exe (PID: 1556)
- JJSploit v5.exe (PID: 2192)
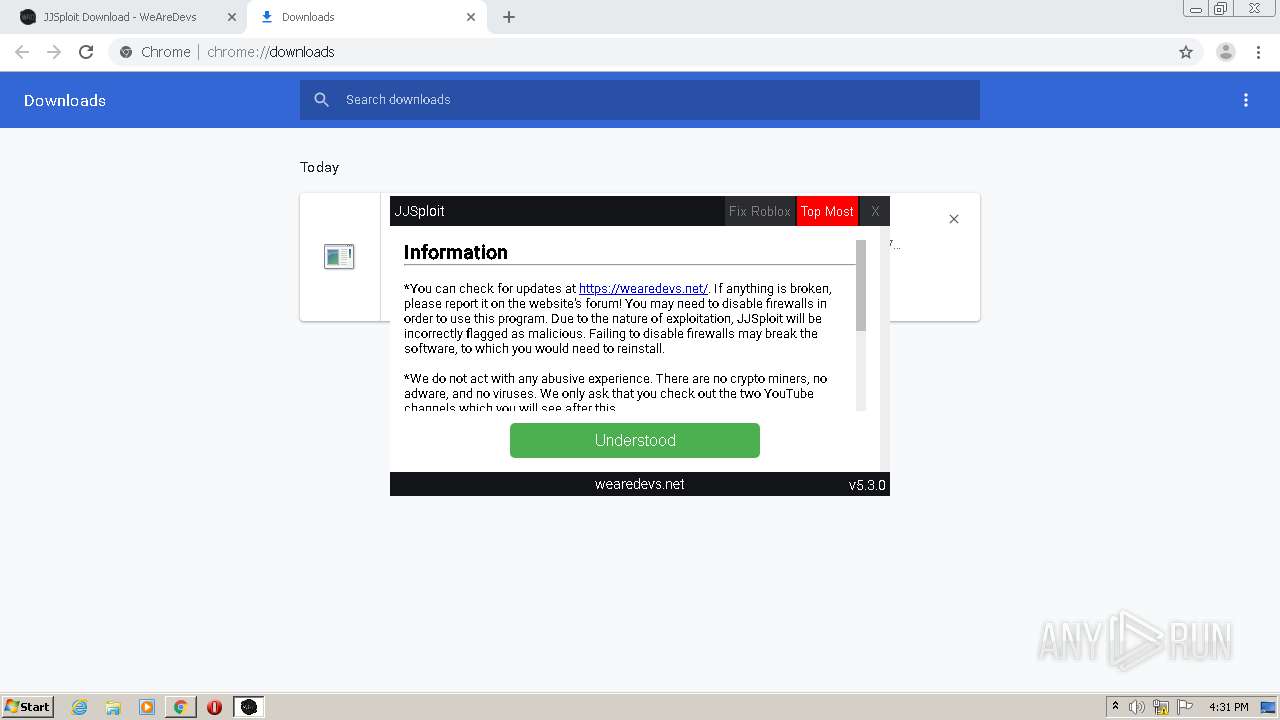
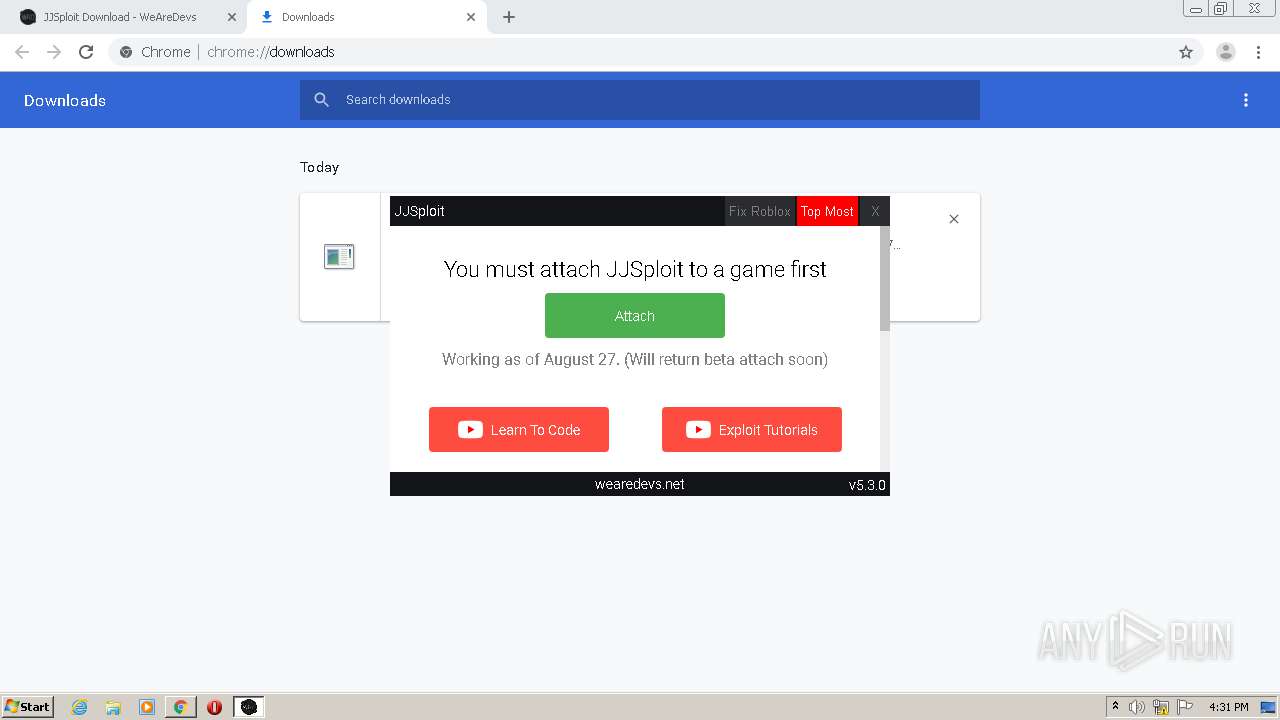
Application launched itself
- JJSploit v5.exe (PID: 2192)
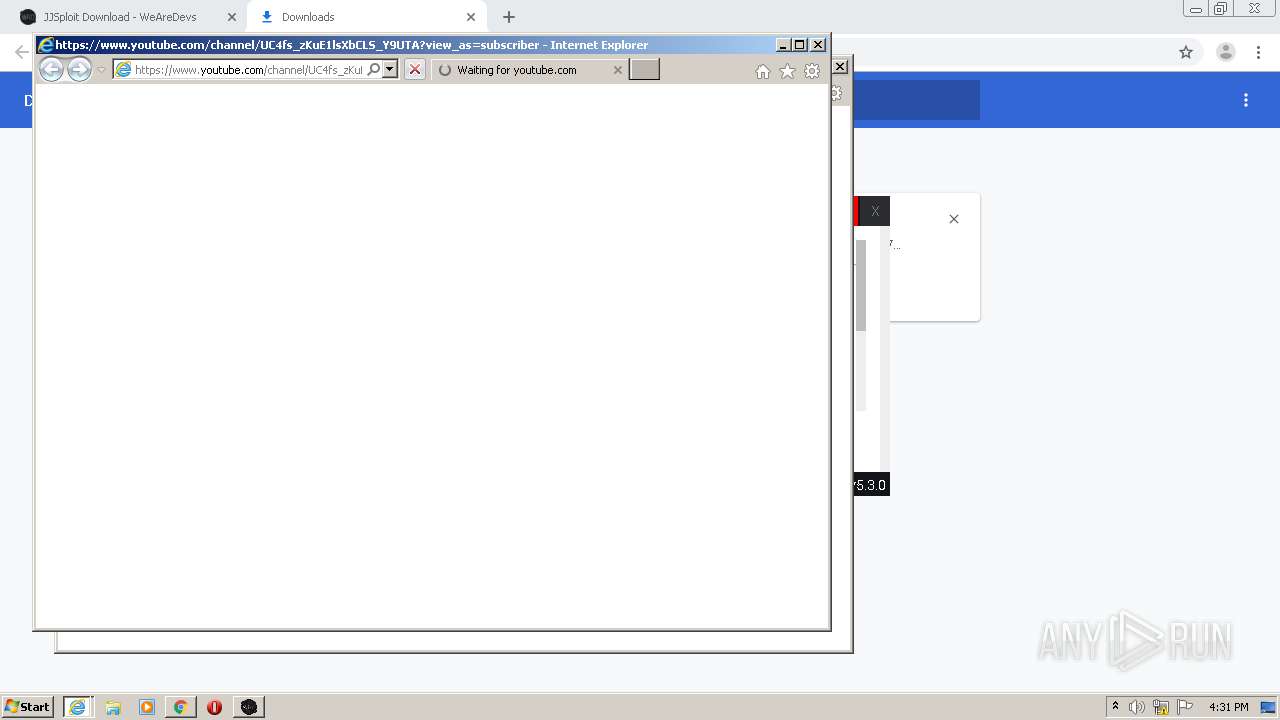
Starts Internet Explorer
- JJSploit v5.exe (PID: 2192)
Executable content was dropped or overwritten
- JJSploit_v5_Setup_5.3.0.exe (PID: 1556)
- chrome.exe (PID: 2780)
- JJSploit v5.exe (PID: 2192)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.0.exe (PID: 1556)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2780)
- iexplore.exe (PID: 2628)
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 1008)
- iexplore.exe (PID: 1804)
Manual execution by user
- JJSploit v5.exe (PID: 2192)
Reads the hosts file
- chrome.exe (PID: 2780)
- chrome.exe (PID: 2484)
- JJSploit v5.exe (PID: 2192)
Application launched itself
- chrome.exe (PID: 2780)
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2628)
Changes internet zones settings
- iexplore.exe (PID: 3332)
- iexplore.exe (PID: 2628)
Reads settings of System Certificates
- iexplore.exe (PID: 1008)
Creates files in the user directory
- iexplore.exe (PID: 1804)
- iexplore.exe (PID: 1008)
Reads internet explorer settings
- iexplore.exe (PID: 1804)
- iexplore.exe (PID: 1008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
28
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2628 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,10660708480992685720,13006712322703370831,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12751148283407960293 --mojo-platform-channel-handle=3496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
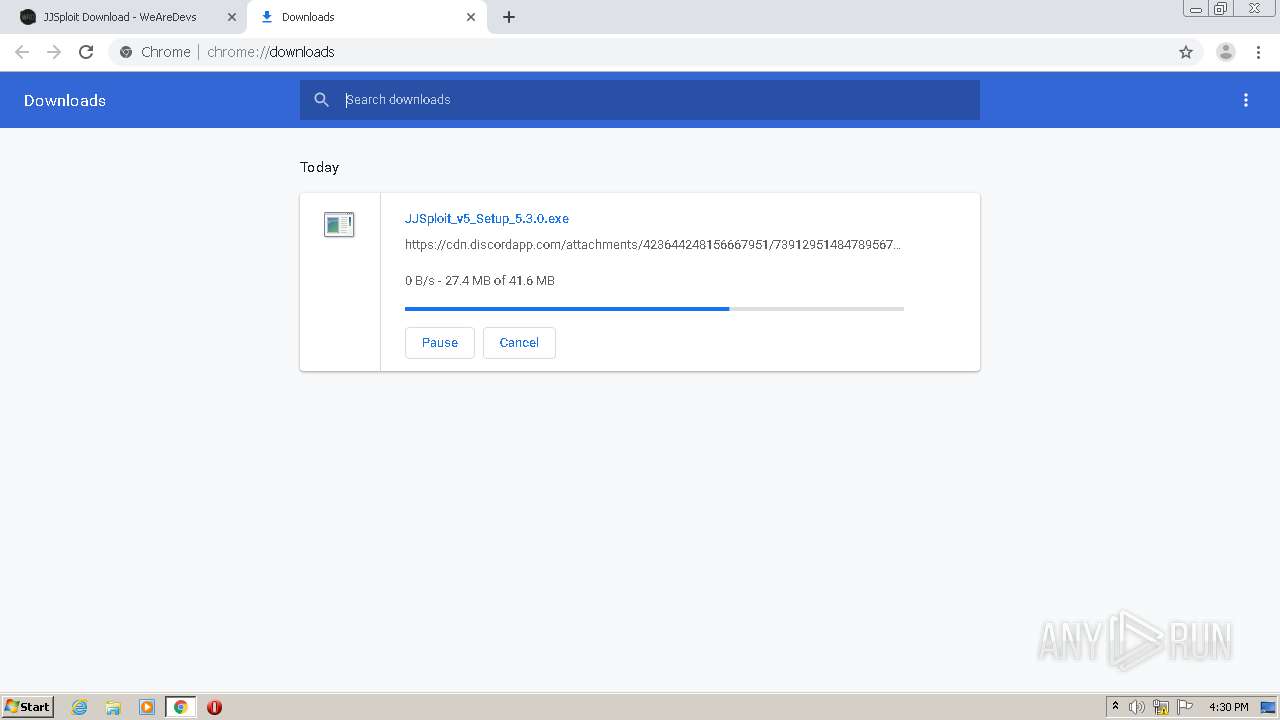
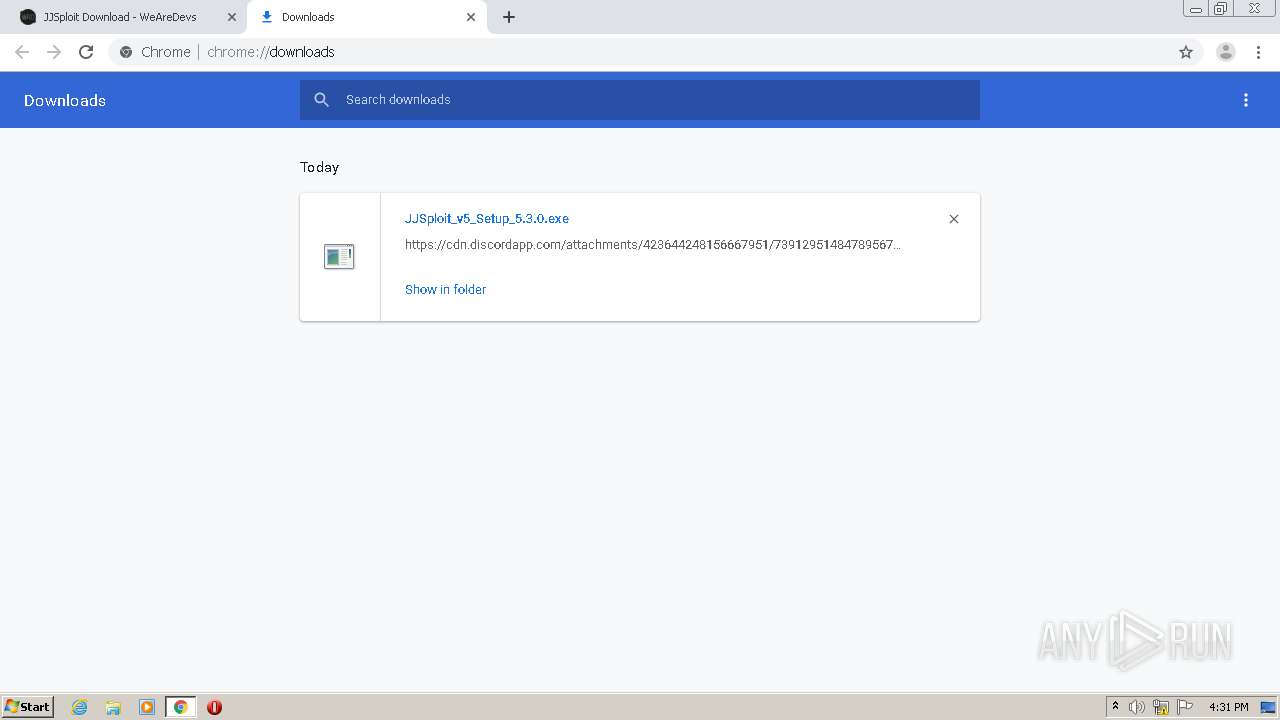
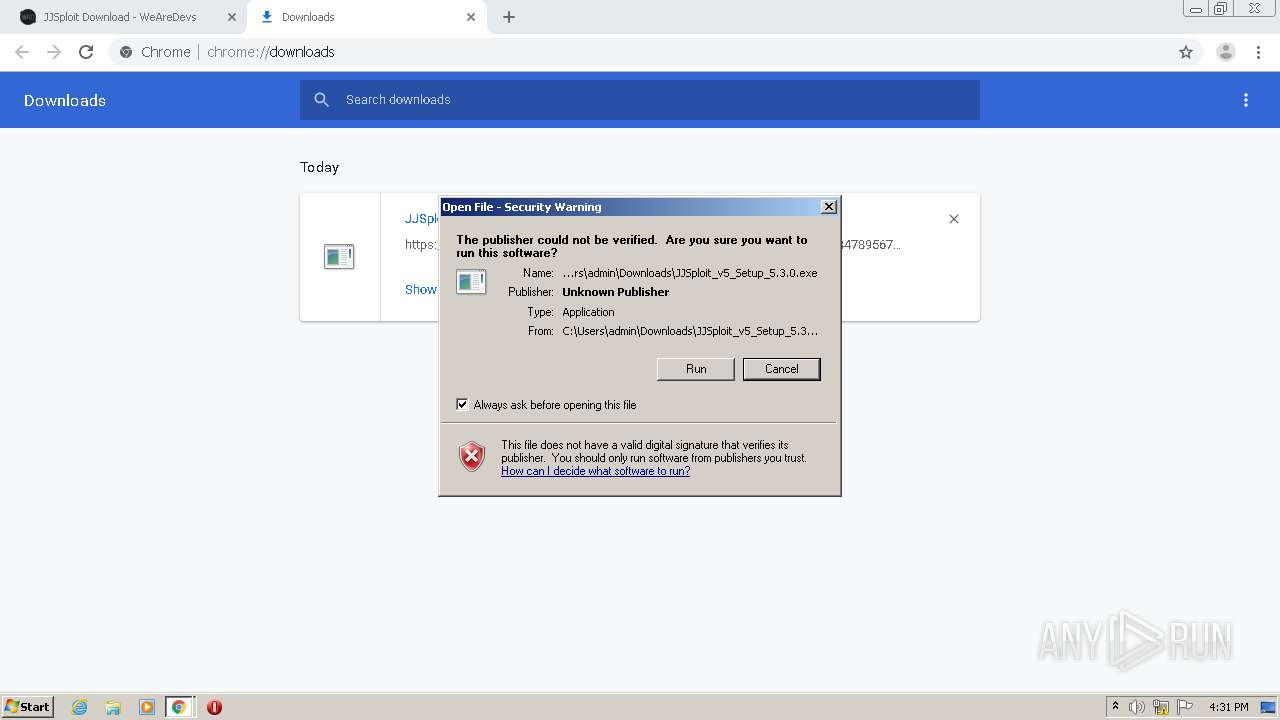
| 1556 | "C:\Users\admin\Downloads\JJSploit_v5_Setup_5.3.0.exe" | C:\Users\admin\Downloads\JJSploit_v5_Setup_5.3.0.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.3.0 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,10660708480992685720,13006712322703370831,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7493314565490416418 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3332 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,10660708480992685720,13006712322703370831,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6718590590473588879 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" --type=gpu-process --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9444727147164103538 --mojo-platform-channel-handle=1152 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | — | JJSploit v5.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJSploit v5 Exit code: 0 Version: 5.3.0 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,10660708480992685720,13006712322703370831,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2760844200254144931 --mojo-platform-channel-handle=3624 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe" | C:\Users\admin\AppData\Local\Programs\jjsploitv5\JJSploit v5.exe | explorer.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit v5 Exit code: 0 Version: 5.3.0 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,10660708480992685720,13006712322703370831,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5181619700575539221 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 196
Read events
1 988
Write events
199
Delete events
9
Modification events
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2780-13243274916625500 |
Value: 259 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2780) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
20
Suspicious files
106
Text files
100
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5728d286-5095-4738-b01c-213b242d3787.tmp | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF150bd1.TMP | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF150c0f.TMP | text | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF150db5.TMP | — | |
MD5:— | SHA256:— | |||
| 2780 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
99
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1008 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQuffJGOa20wgAAAAAUx0t | US | der | 472 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECpjZbLBNjarCAAAAABTG2o%3D | US | der | 471 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQuffJGOa20wgAAAAAUx0t | US | der | 472 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDRSVutUkbqxAgAAAAAUxzi | US | der | 472 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1008 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDQuffJGOa20wgAAAAAUx0t | US | der | 472 b | whitelisted |
1804 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECpjZbLBNjarCAAAAABTG2o%3D | US | der | 471 b | whitelisted |
1008 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDRSVutUkbqxAgAAAAAUxzi | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2484 | chrome.exe | 104.17.79.107:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
2484 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
2484 | chrome.exe | 172.217.16.130:443 | adservice.google.dk | Google Inc. | US | whitelisted |
2484 | chrome.exe | 172.217.18.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
2484 | chrome.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
2484 | chrome.exe | 172.217.23.163:443 | www.google.dk | Google Inc. | US | whitelisted |
2484 | chrome.exe | 172.217.23.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.jsdelivr.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |