| File name: | svchost-windows.exe |
| Full analysis: | https://app.any.run/tasks/ff0a90d6-61fc-48da-8ce9-260bd42c60d2 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 01:46:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 8DDB8C870A5E4CD2F1061A6F63D8FE03 |
| SHA1: | 56098D15264AA3A0452F03E57ED72617A878A7CA |
| SHA256: | 54958740506205B7BA8594DBEBEC7BB9BDD0105527C3EB8AA0F25AD6A3F3C9C4 |
| SSDEEP: | 3072:edw8ZZ39WUw8i8ksBAxZlt+lp19+2gOZA3hHcJkp91p4z/aSu9Vgb4GV+TW3dCGs:ed3ZKUw8vAxZlt+lpG2gOZYhHcJkr4Ze |
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 7484)
- net.exe (PID: 7464)
- svchost-windows.exe (PID: 7420)
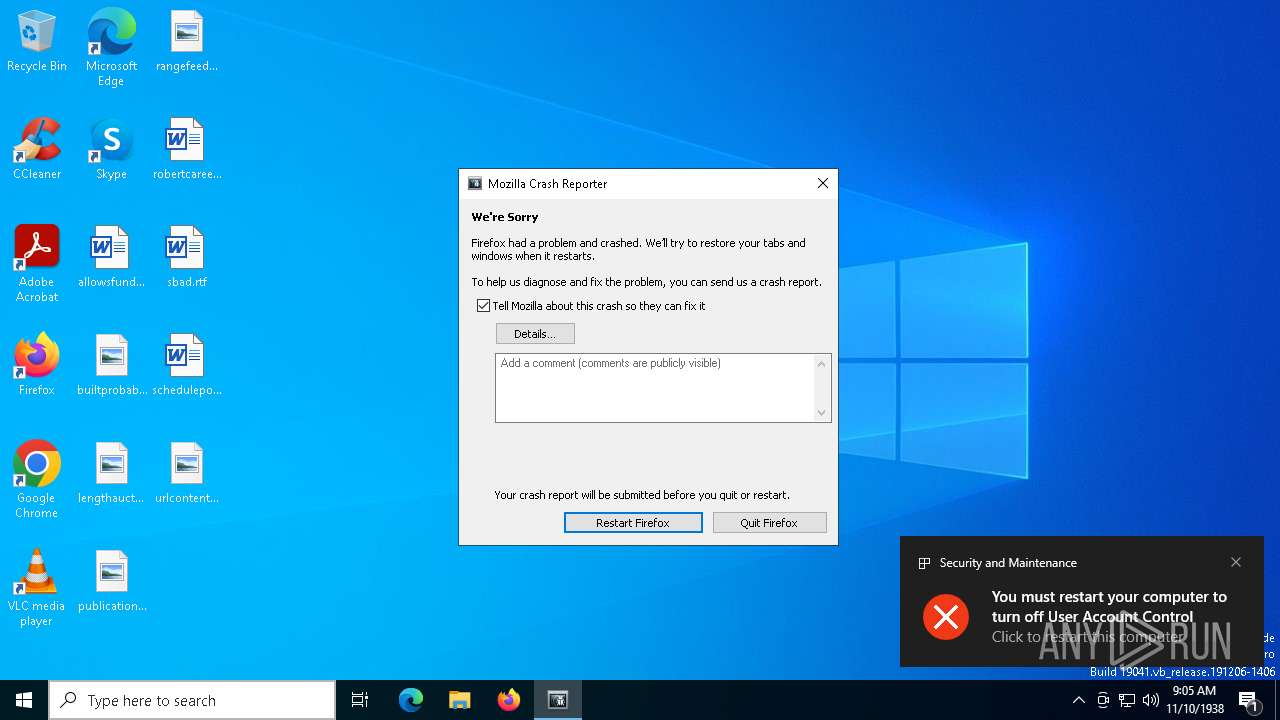
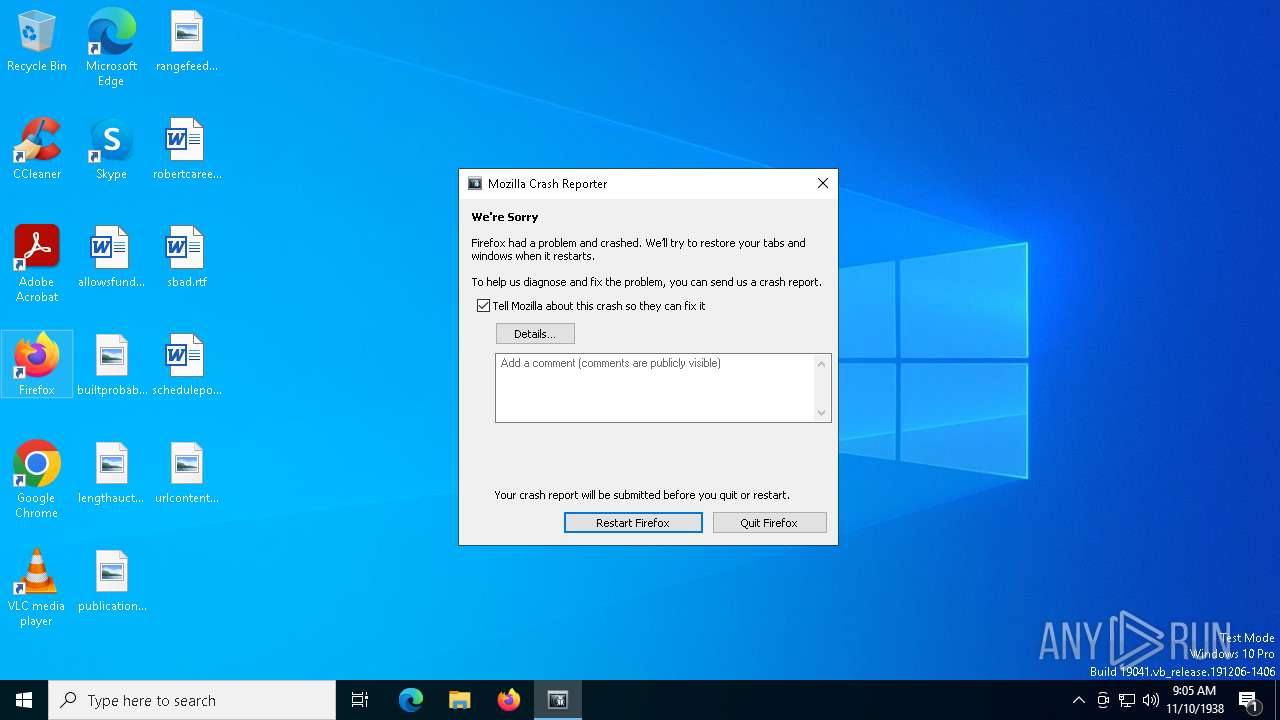
UAC/LUA settings modification
- svchost-windows.exe (PID: 7420)
Changes the autorun value in the registry
- svchost-windows.exe (PID: 7420)
SUSPICIOUS
Process drops legitimate windows executable
- svchost-windows.exe (PID: 7420)
Starts a Microsoft application from unusual location
- svchost-windows.exe (PID: 7420)
- svchost-windows.exe (PID: 7316)
Uses NETSH.EXE to change the status of the firewall
- svchost-windows.exe (PID: 7420)
The process creates files with name similar to system file names
- svchost-windows.exe (PID: 7420)
Executable content was dropped or overwritten
- svchost-windows.exe (PID: 7420)
INFO
The sample compiled with english language support
- svchost-windows.exe (PID: 7420)
Checks supported languages
- svchost-windows.exe (PID: 7420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (63.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (24.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.1) |
| .exe | | | Win32 Executable (generic) (3.5) |
| .exe | | | Generic Win/DOS Executable (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:18 14:54:37+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 110592 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x200c |
| OSVersion: | 4 |
| ImageVersion: | 15 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.7600.16385 |
| ProductVersionNumber: | 6.1.7600.16385 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Host Process for Windows Services |
| FileVersion: | 6.1.7600.16385 (win7_rtm.090713-1255) |
| InternalName: | svchost.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | svchost.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.1.7600.16385 |
Total processes
142
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7316 | "C:\Users\admin\AppData\Local\Temp\svchost-windows.exe" | C:\Users\admin\AppData\Local\Temp\svchost-windows.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 7420 | "C:\Users\admin\AppData\Local\Temp\svchost-windows.exe" | C:\Users\admin\AppData\Local\Temp\svchost-windows.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 7448 | netsh firewall set opmode disable | C:\Windows\SysWOW64\netsh.exe | — | svchost-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7464 | net stop security center | C:\Windows\SysWOW64\net.exe | — | svchost-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7484 | net stop WinDefend | C:\Windows\SysWOW64\net.exe | — | svchost-windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7620 | C:\WINDOWS\system32\net1 stop security center | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7624 | C:\WINDOWS\system32\net1 stop WinDefend | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
56
Read events
53
Write events
3
Delete events
0
Modification events
| (PID) Process: | (7420) svchost-windows.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Security Center |
| Operation: | write | Name: | UACDisableNotify |
Value: 0 | |||
| (PID) Process: | (7420) svchost-windows.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (7420) svchost-windows.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | svchost |
Value: C:\WINDOWS\svchost.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7420 | svchost-windows.exe | C:\Windows\svchost.exe | executable | |
MD5:8DDB8C870A5E4CD2F1061A6F63D8FE03 | SHA256:54958740506205B7BA8594DBEBEC7BB9BDD0105527C3EB8AA0F25AD6A3F3C9C4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
24
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2292 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3812 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |