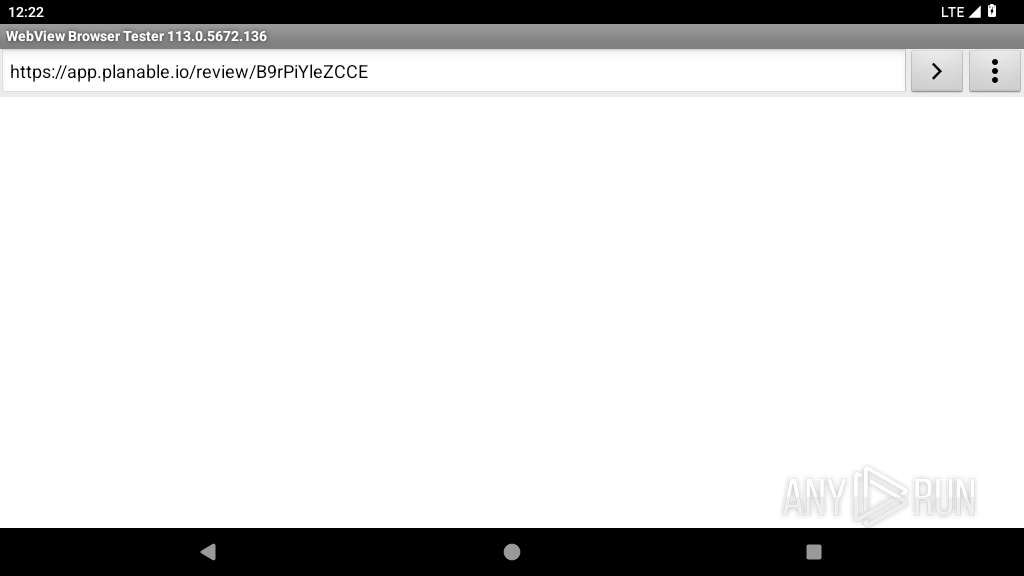
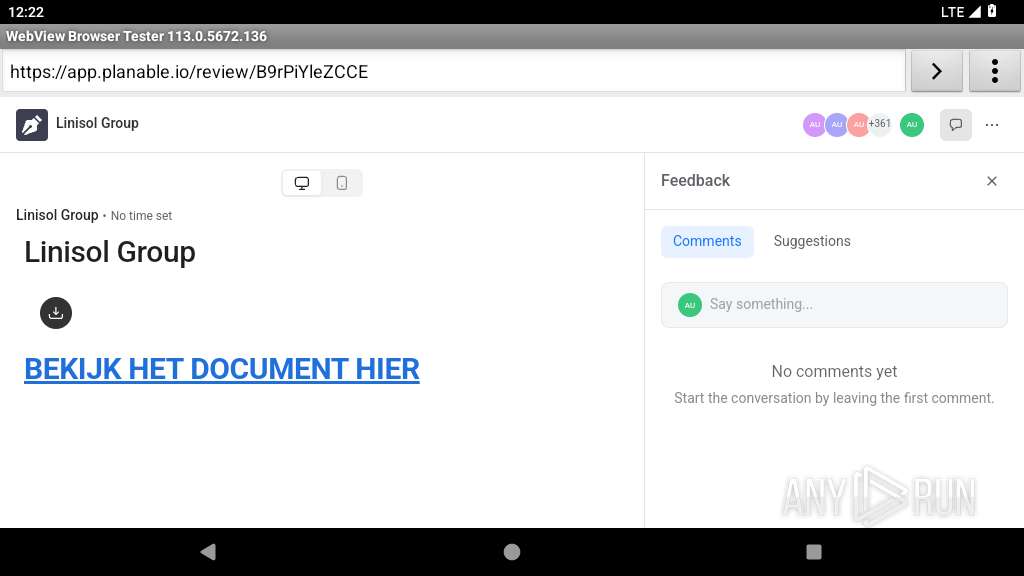
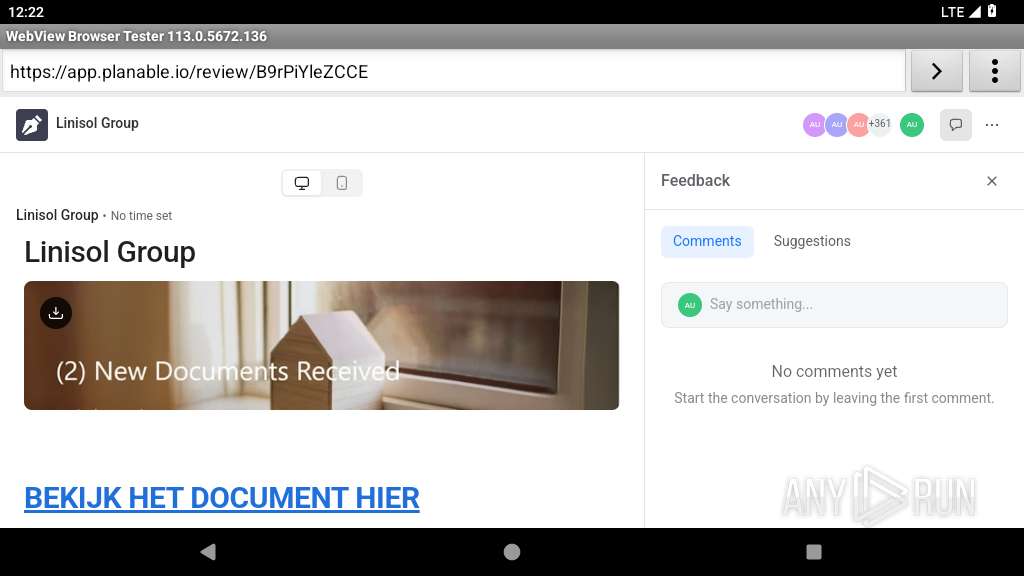
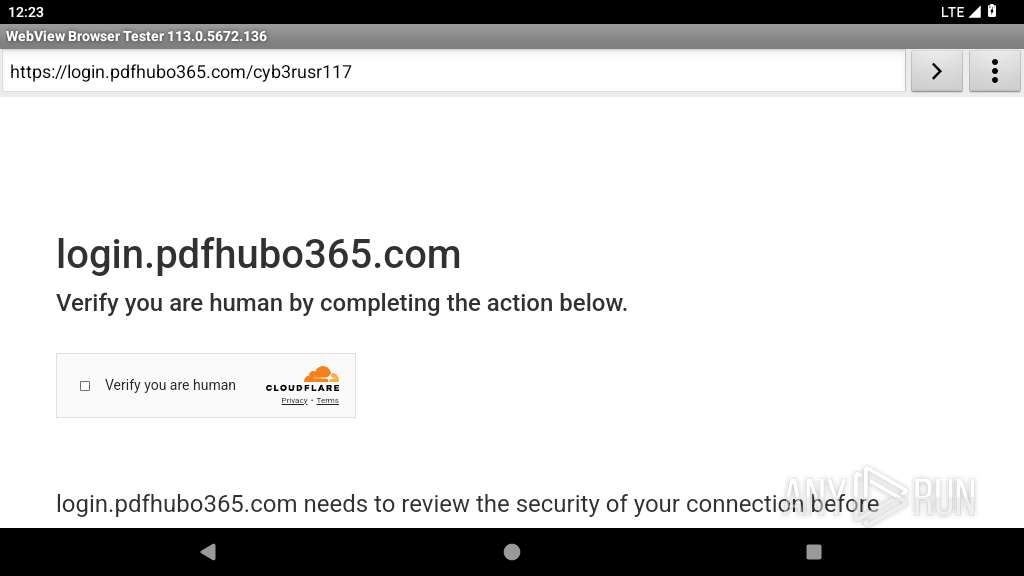
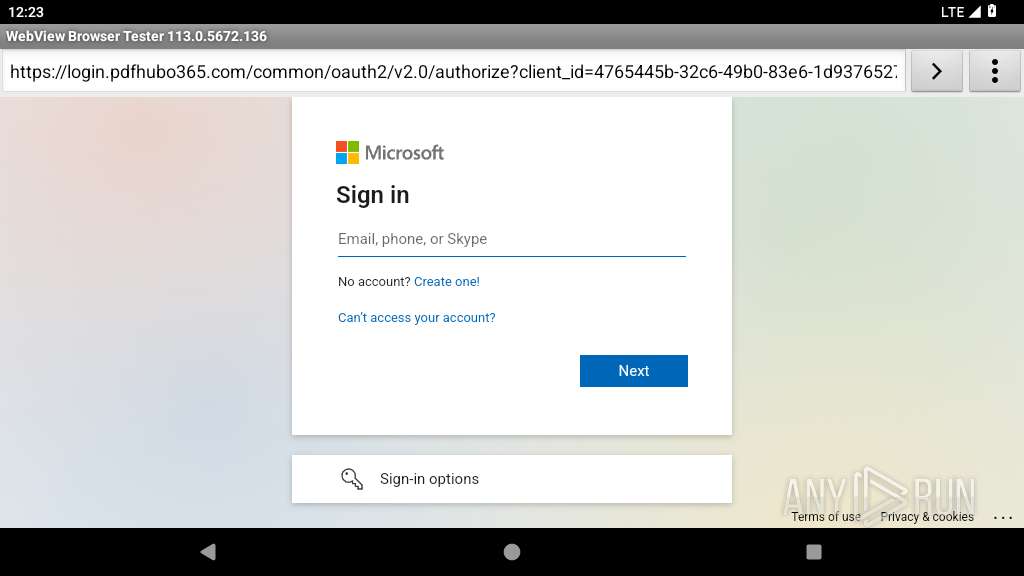
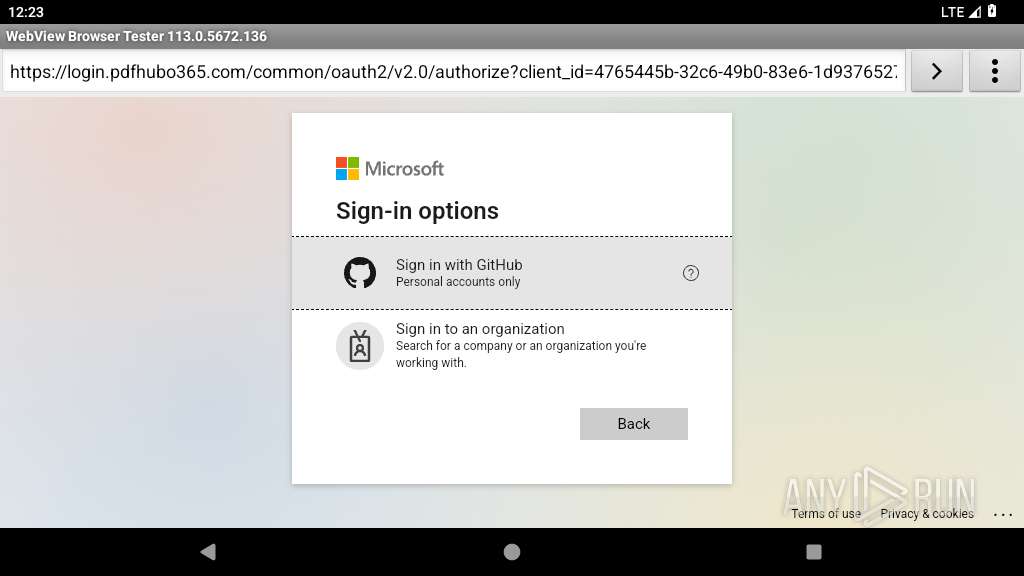
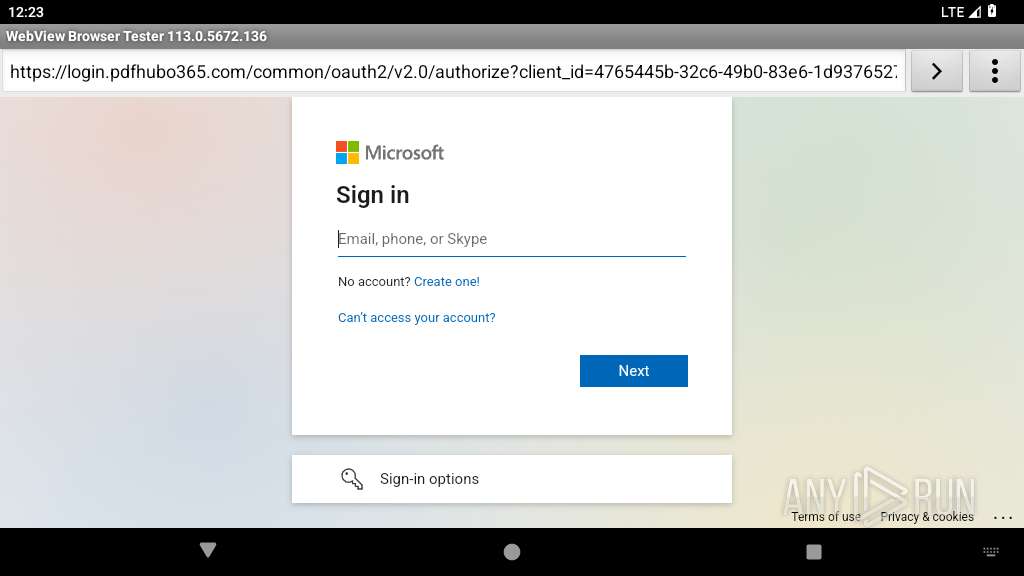
| URL: | http://plnbl.io/review/B9rPiYleZCCE |
| Full analysis: | https://app.any.run/tasks/4ad8c2bc-81b5-4a04-b66e-dec105b97f48 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2025, 12:22:30 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | B68C3ABCAC2C61A0902E1A6D4699827F |
| SHA1: | 96BD66CBD753E0FF867BB65F7CDB92D35E894826 |
| SHA256: | 5490C6895F2620100CE871F7613D29BB98C95EF692B9E3684584EF14ECEB5A5B |
| SSDEEP: | 3:N1KOJSMI:COJSMI |
MALICIOUS
PHISHING has been detected (SURICATA)
- app_process64 (PID: 2224)
- netd (PID: 345)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
127
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 345 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2224 | org.chromium.webview_shell | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2249 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2269 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2301 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
104
DNS requests
68
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2224 | app_process64 | GET | 301 | 188.114.97.3:80 | http://plnbl.io/review/B9rPiYleZCCE | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 64.233.167.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
449 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
2224 | app_process64 | 188.114.97.3:80 | plnbl.io | CLOUDFLARENET | NL | unknown |
2249 | app_process32 | 142.250.185.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2301 | app_process32 | 142.250.185.163:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2301 | app_process32 | 142.250.186.142:443 | dl.google.com | GOOGLE | US | whitelisted |
2224 | app_process64 | 52.208.194.84:443 | app.planable.io | AMAZON-02 | IE | unknown |
2224 | app_process64 | 142.250.185.174:443 | apis.google.com | GOOGLE | US | whitelisted |
2224 | app_process64 | 18.66.137.195:443 | do9efv5u6nwa8.cloudfront.net | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
plnbl.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
app.planable.io |
| unknown |
do9efv5u6nwa8.cloudfront.net |
| whitelisted |
d2wxi5827r392t.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
345 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
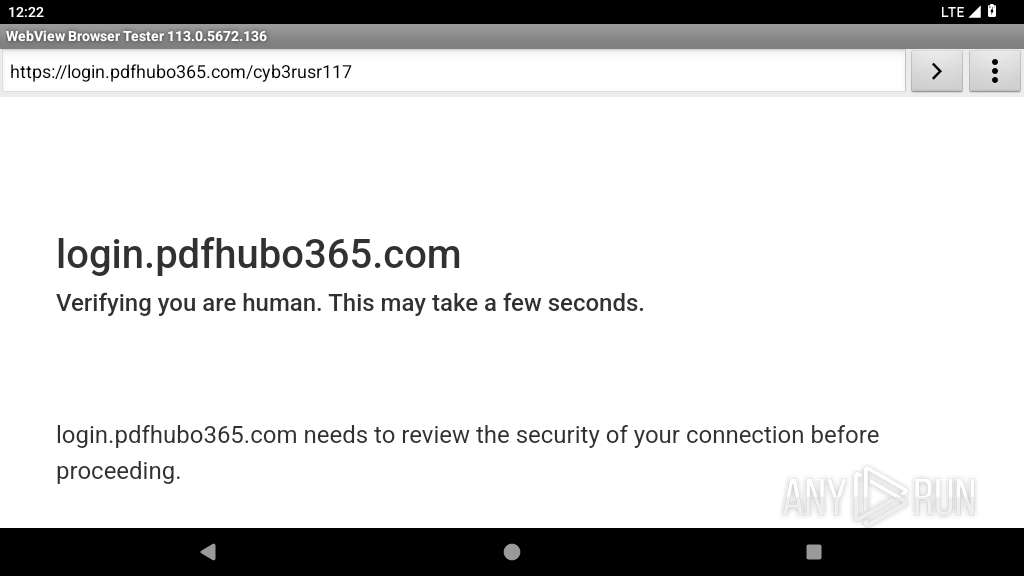
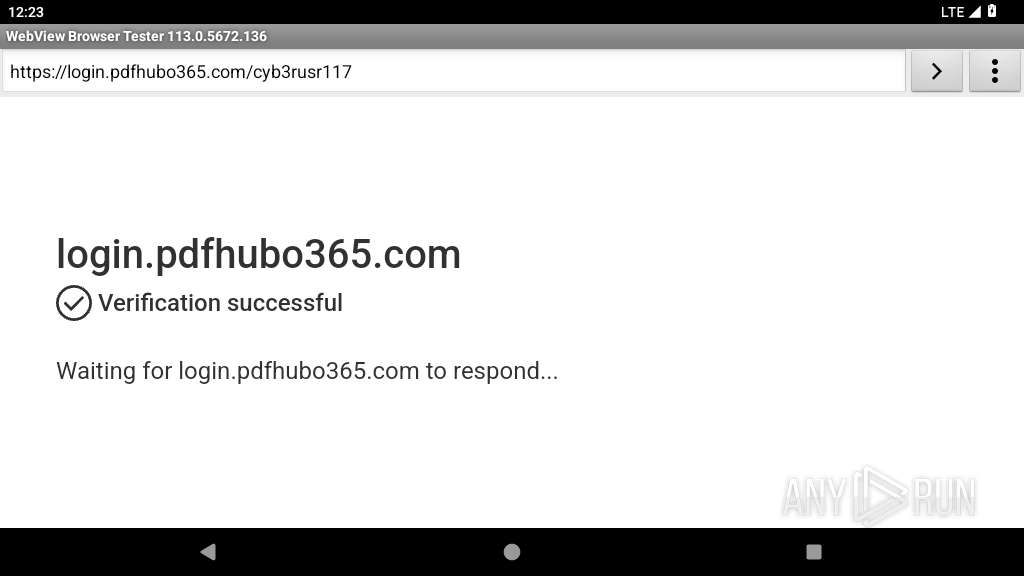
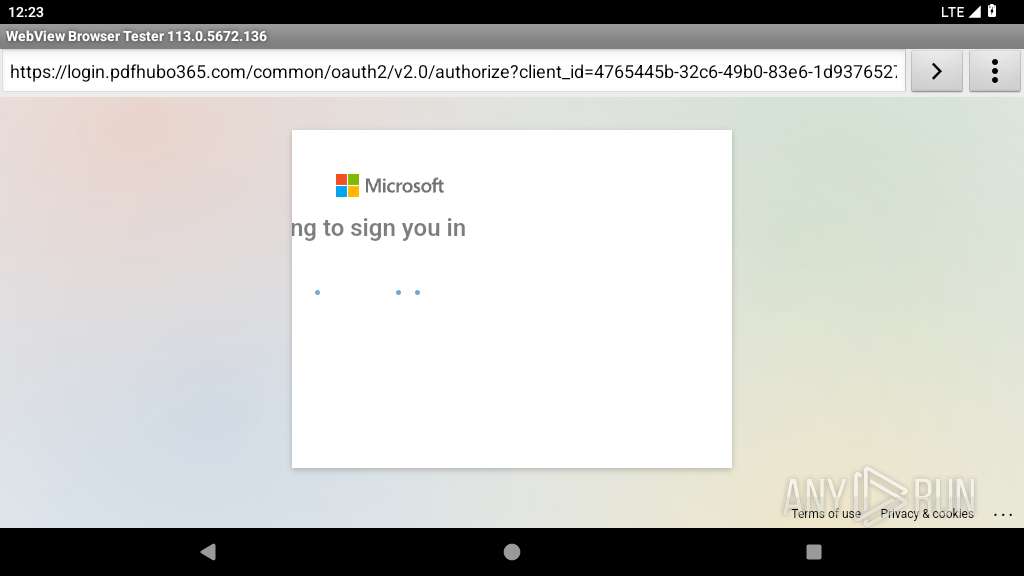
345 | netd | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain Pattern (login. 365) |
345 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
345 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
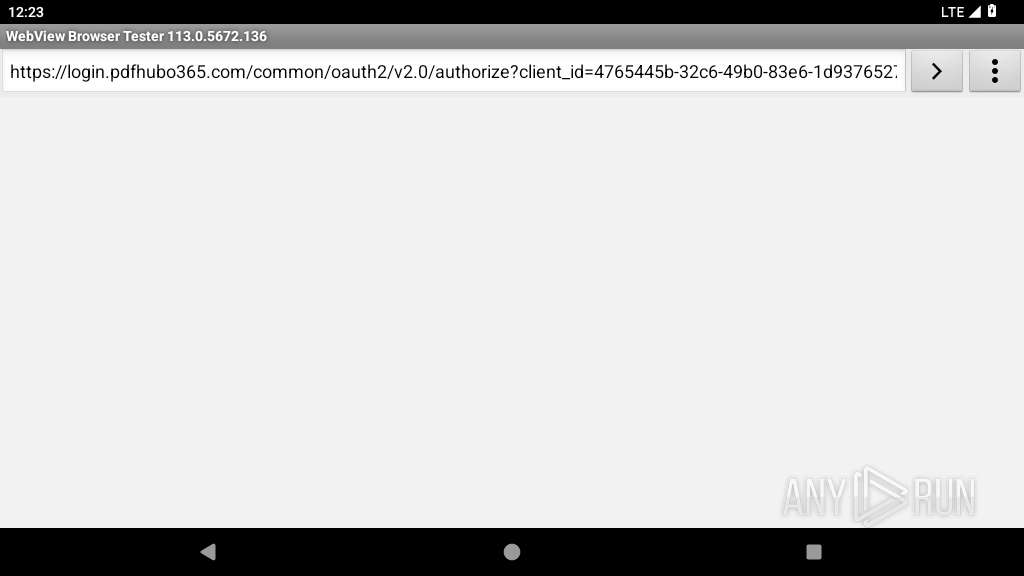
2224 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (aadchallenge) |
2224 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Domain chain identified as Phishing (authisnotlogin) |
2224 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (aadzone) |
2224 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (aadchallenge) |
2224 | app_process64 | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Possible Domain chain identified as Phishing (authisnotlogin) |