| File name: | gets.ps1 |
| Full analysis: | https://app.any.run/tasks/50ca7e4e-4e46-44af-8687-f0235fa017c3 |
| Verdict: | Malicious activity |
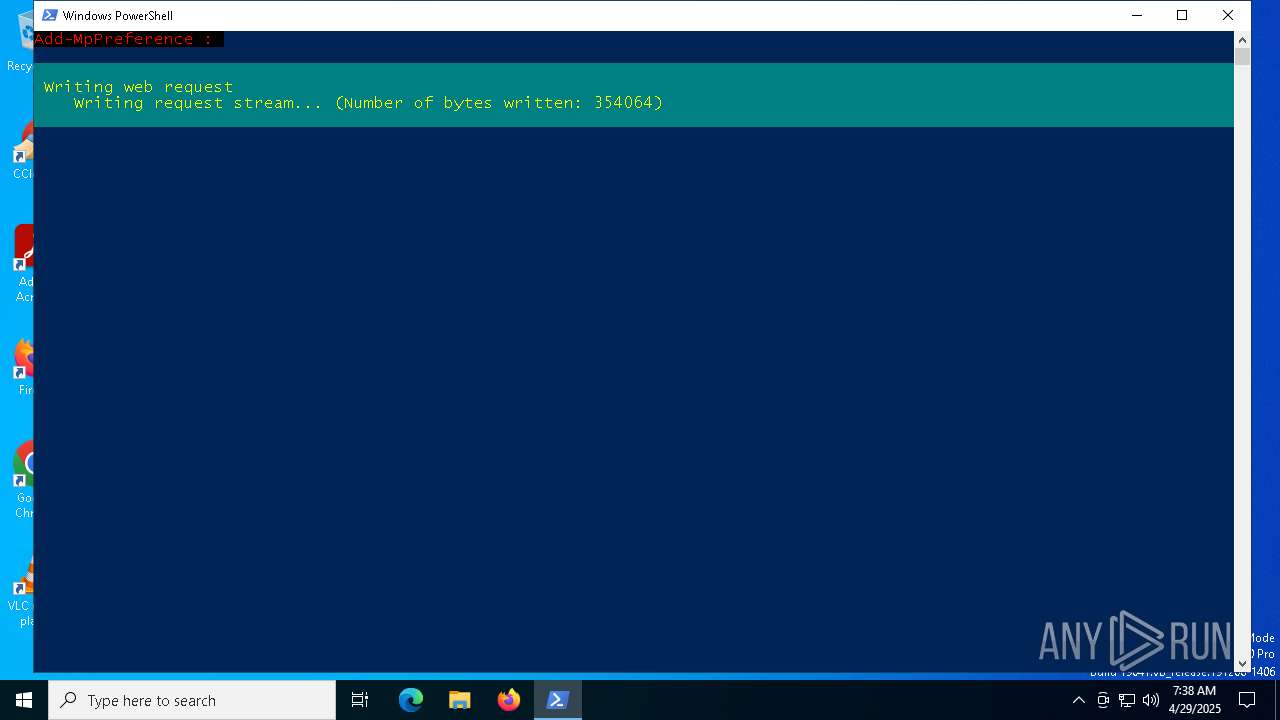
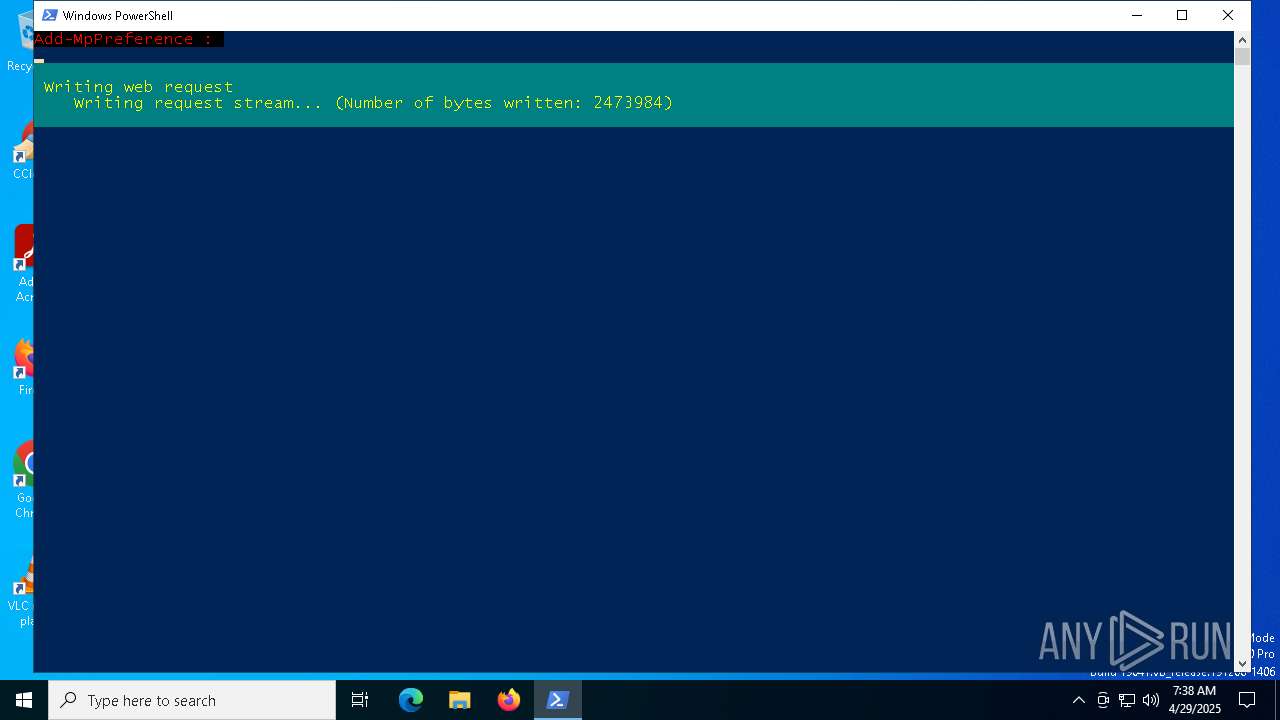
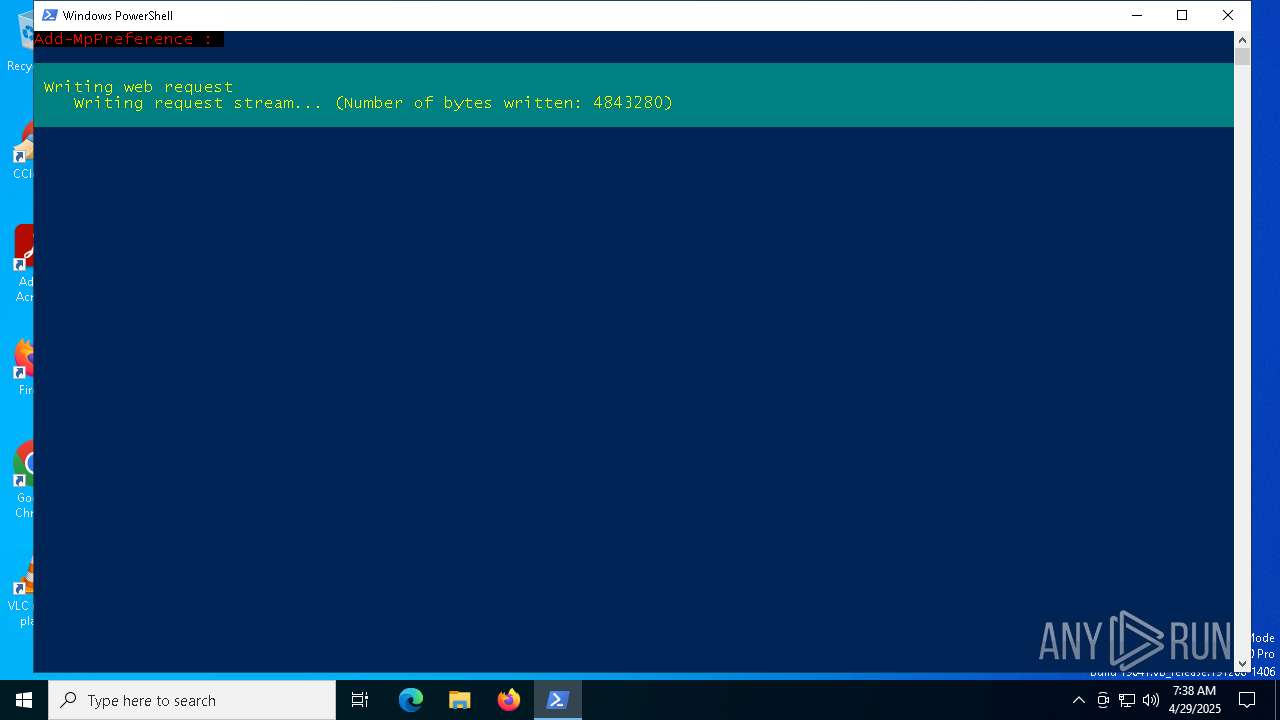
| Analysis date: | April 29, 2025, 07:38:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | 8A30D23A8CD1C0498495447C34BC2989 |
| SHA1: | A0796743D0C9B50C90ECCCE475B3FF8A7D477BEC |
| SHA256: | 54901FAC3345CFB30AE3E9B933025BF52B881813B25D87D64F48BC1AD6AF5385 |
| SSDEEP: | 192:g7yMsnvynOzad4POVk1Gyp/SD2zKDUtXDZABygKlkO7BGTG:MokhKIq |
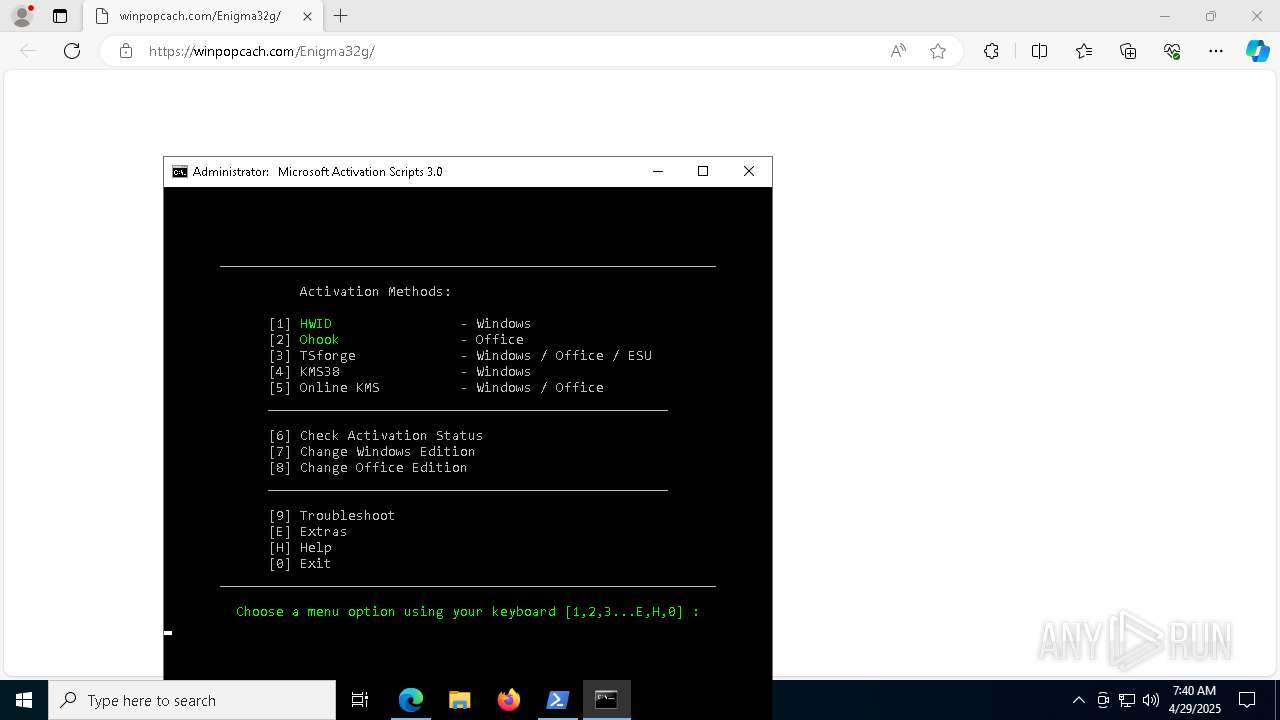
MALICIOUS
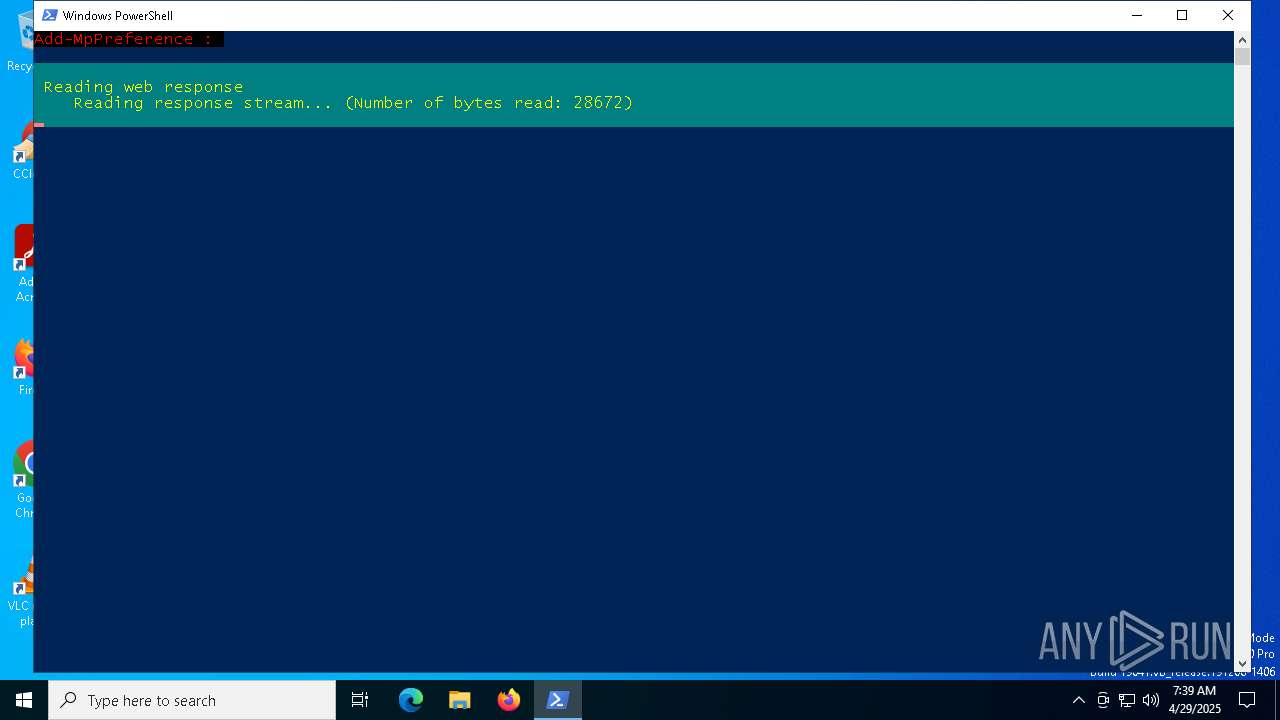
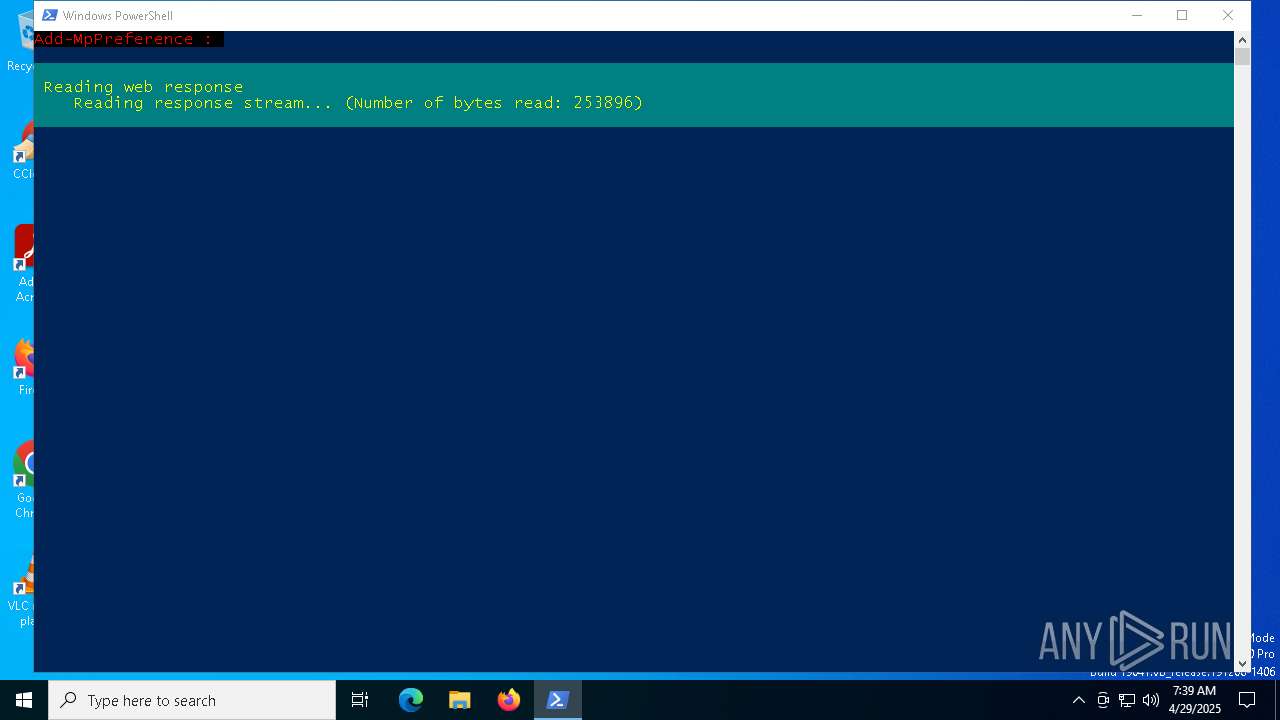
Bypass execution policy to execute commands
- powershell.exe (PID: 4244)
Create files in the Startup directory
- powershell.exe (PID: 4244)
SUSPICIOUS
Gets file extension (POWERSHELL)
- powershell.exe (PID: 4244)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4244)
Reads security settings of Internet Explorer
- Enigma32g.exe (PID: 5728)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4244)
Executable content was dropped or overwritten
- powershell.exe (PID: 4244)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 776)
- powershell.exe (PID: 4244)
- cmd.exe (PID: 5812)
- powershell.exe (PID: 7796)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 8112)
- powershell.exe (PID: 7864)
Executing commands from ".cmd" file
- powershell.exe (PID: 4244)
- cmd.exe (PID: 776)
- powershell.exe (PID: 7796)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8000)
- powershell.exe (PID: 7864)
Starts SC.EXE for service management
- cmd.exe (PID: 776)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8000)
Windows service management via SC.EXE
- sc.exe (PID: 5736)
- sc.exe (PID: 8060)
- sc.exe (PID: 7824)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 776)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8000)
Application launched itself
- cmd.exe (PID: 776)
- cmd.exe (PID: 5812)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 8000)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 776)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 8000)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7232)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7232)
INFO
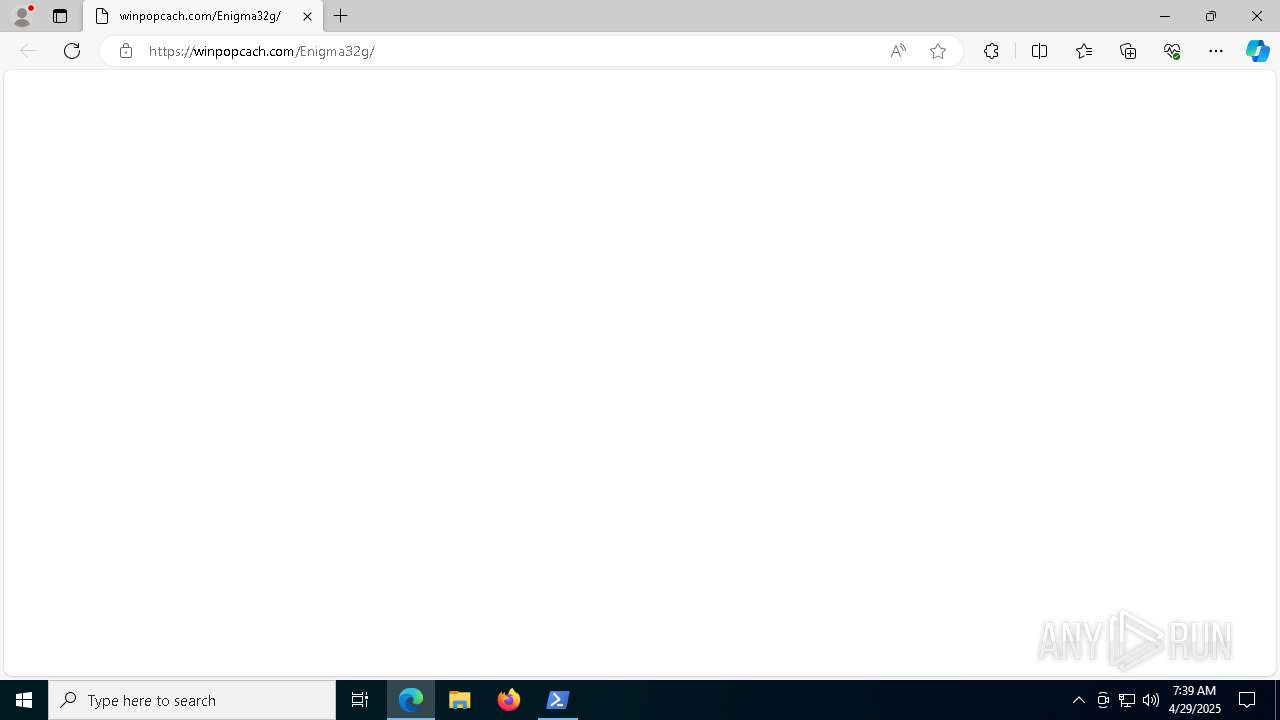
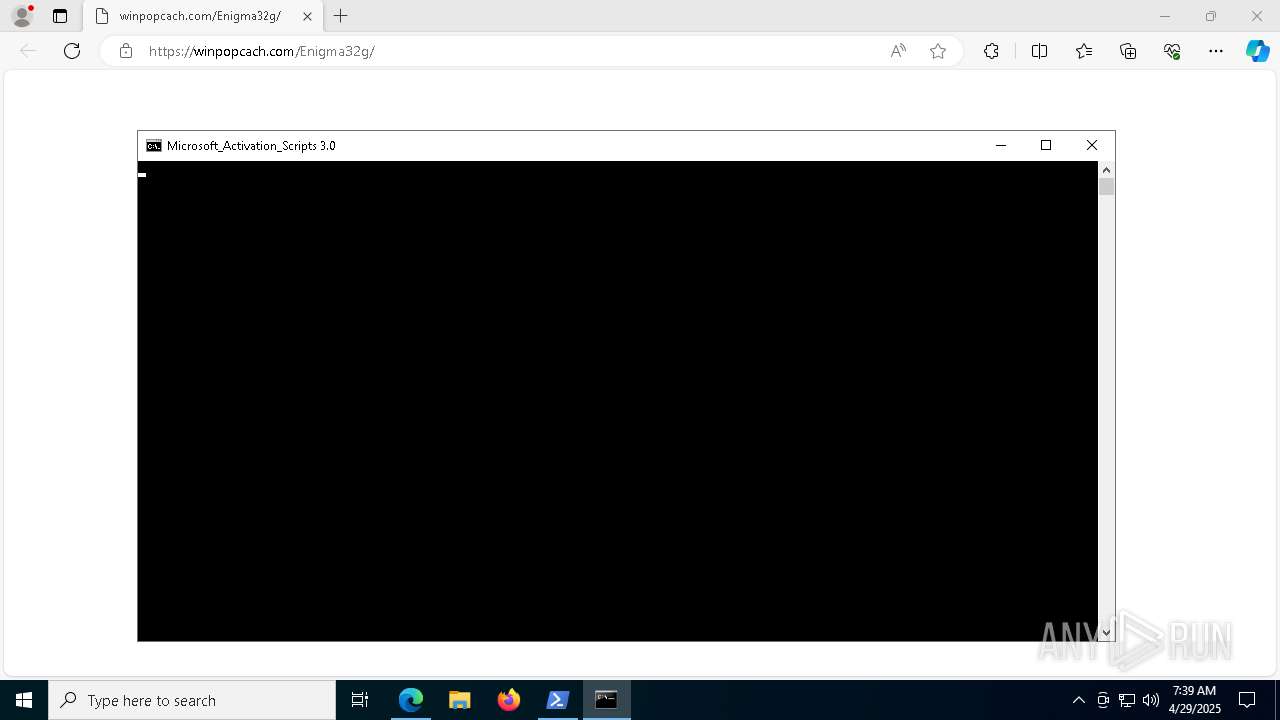
The executable file from the user directory is run by the Powershell process
- Enigma32g.exe (PID: 5728)
Auto-launch of the file from Startup directory
- powershell.exe (PID: 4244)
Reads the software policy settings
- slui.exe (PID: 6488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4244)
Disables trace logs
- powershell.exe (PID: 4244)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Checks proxy server information
- powershell.exe (PID: 4244)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4244)
Reads the computer name
- Enigma32g.exe (PID: 5728)
- identity_helper.exe (PID: 7388)
The sample compiled with english language support
- powershell.exe (PID: 4244)
Checks supported languages
- Enigma32g.exe (PID: 5728)
- identity_helper.exe (PID: 7388)
- mode.com (PID: 7844)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Application launched itself
- msedge.exe (PID: 5988)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Checks operating system version
- cmd.exe (PID: 776)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8000)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5812)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 7228)
Manual execution by a user
- msedge.exe (PID: 7648)
Reads Environment values
- identity_helper.exe (PID: 7388)
Starts MODE.COM to configure console settings
- mode.com (PID: 7844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
244
Monitored processes
111
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2912 --field-trial-handle=2404,i,16938265615607492384,6503580464726757970,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 776 | "C:\WINDOWS\system32\cmd.exe" /c ""C:\Users\admin\AppData\Local\Temp\MAS_14d486fe-4f88-4523-b7cf-0fa0d30b5ada.cmd" " | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\AppData\Local\Temp\MAS_14d486fe-4f88-4523-b7cf-0fa0d30b5ada.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4028 --field-trial-handle=2404,i,16938265615607492384,6503580464726757970,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3016 --field-trial-handle=2404,i,16938265615607492384,6503580464726757970,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3472 --field-trial-handle=2404,i,16938265615607492384,6503580464726757970,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
43 809
Read events
43 789
Write events
20
Delete events
0
Modification events
| (PID) Process: | (5728) Enigma32g.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D1A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5728) Enigma32g.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5728) Enigma32g.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5728) Enigma32g.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5988) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3EF385307C922F00 | |||
| (PID) Process: | (5988) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 79D88F307C922F00 | |||
Executable files
9
Suspicious files
196
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
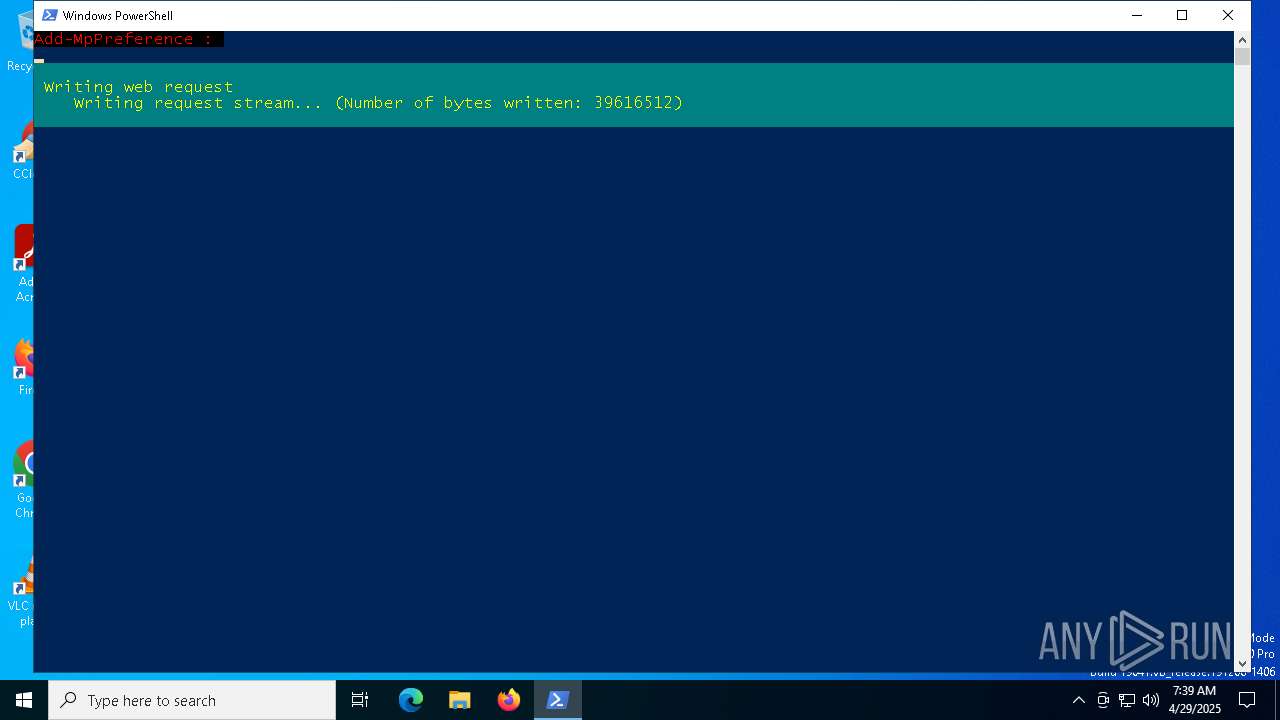
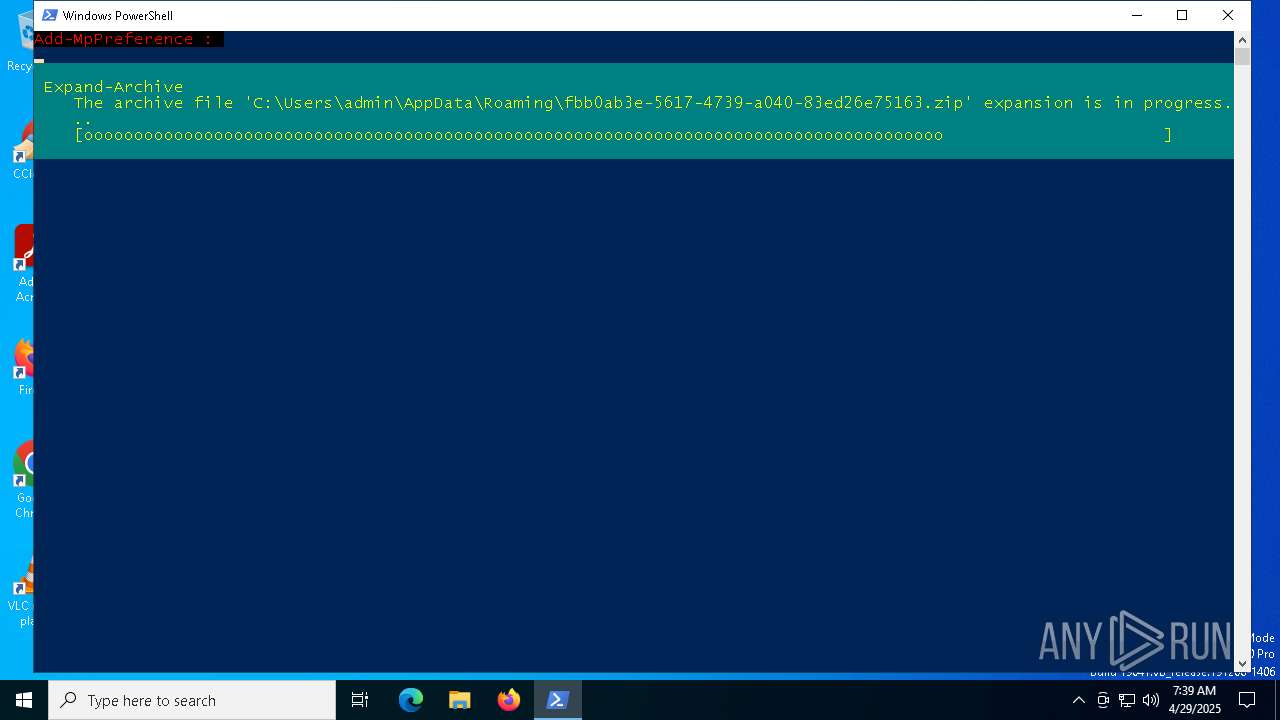
| 4244 | powershell.exe | C:\Users\admin\AppData\Roaming\fbb0ab3e-5617-4739-a040-83ed26e75163.zip | — | |
MD5:— | SHA256:— | |||
| 4244 | powershell.exe | C:\Users\admin\AppData\Roaming\fbb0ab3e-5617-4739-a040-83ed26e75163\Enigma32g.dat | — | |
MD5:— | SHA256:— | |||
| 4244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bb34.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 4244 | powershell.exe | C:\Users\admin\AppData\Roaming\fbb0ab3e-5617-4739-a040-83ed26e75163\libspv.dll | executable | |
MD5:236CB2976CE842B342EDC7CA0B4F9EF2 | SHA256:BD85775CB2BEE6680D700214CAC8ACC325F0080C62A69A8A74B32F7FBA4B1997 | |||
| 5988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:6971E42ED64D2BE125547F021EB852B1 | SHA256:B46CFDC4106DF566F71AA34D6F10B53767C561DFD17DD07A5930A18E67BB344B | |||
| 4244 | powershell.exe | C:\Users\admin\AppData\Roaming\fbb0ab3e-5617-4739-a040-83ed26e75163\libssv.dll | executable | |
MD5:DC88D5AF993F3396F1866516671E1EEB | SHA256:8ACD36A0566C657497419BE076FAF43ACC49F6D169CF5133E9060A3D46E2BD23 | |||
| 5988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11fc2f.TMP | — | |
MD5:— | SHA256:— | |||
| 5988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4244 | powershell.exe | C:\Users\admin\AppData\Roaming\fbb0ab3e-5617-4739-a040-83ed26e75163\libeay32.dll | executable | |
MD5:061DAE89B309A98382DEDC04942BD8A2 | SHA256:B0826835B77EF66964244CB708A58AB8BAFF69F4DFABEFA412E377A86AA20246 | |||
| 5988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11fc20.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
41
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5936 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4244 | powershell.exe | 185.255.122.94:443 | conecwinlab.com | — | GB | unknown |
4244 | powershell.exe | 185.255.122.89:443 | modulowinapp.com | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
conecwinlab.com |
| unknown |
modulowinapp.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |