| File name: | soft.zip |
| Full analysis: | https://app.any.run/tasks/9322a8f9-baf5-4e35-b261-be585a9719e4 |
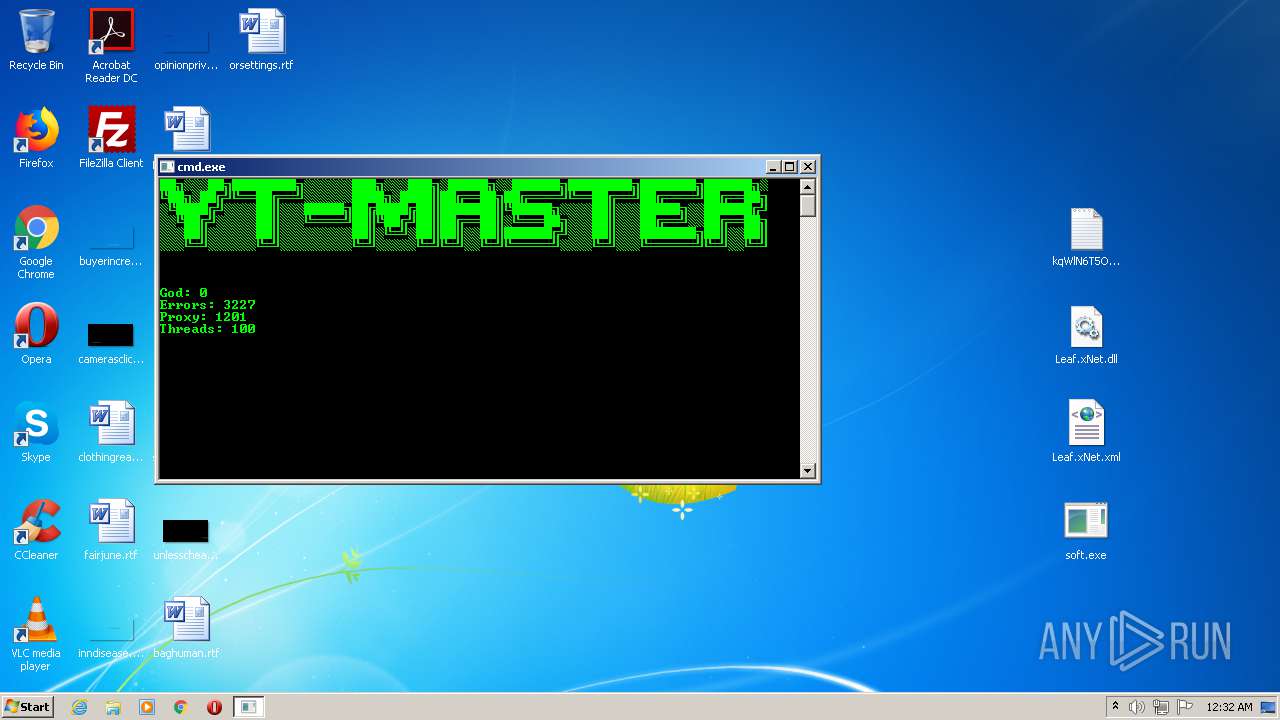
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 00:28:03 |
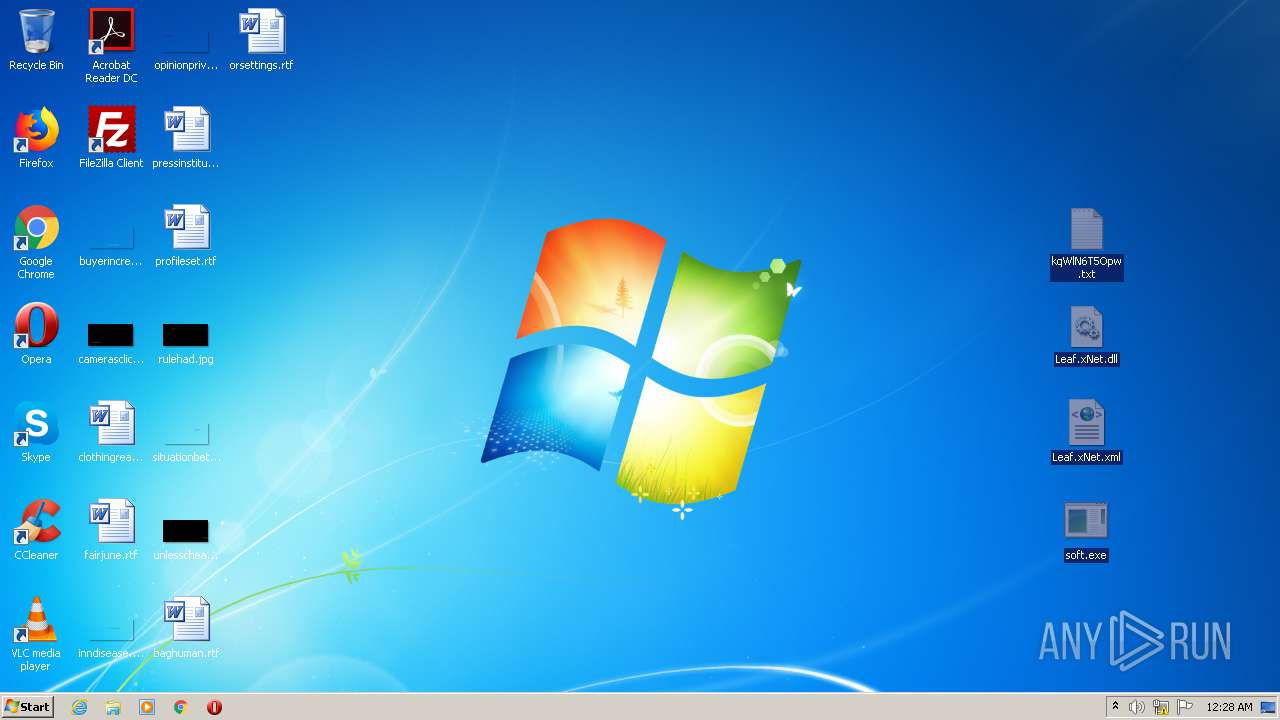
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
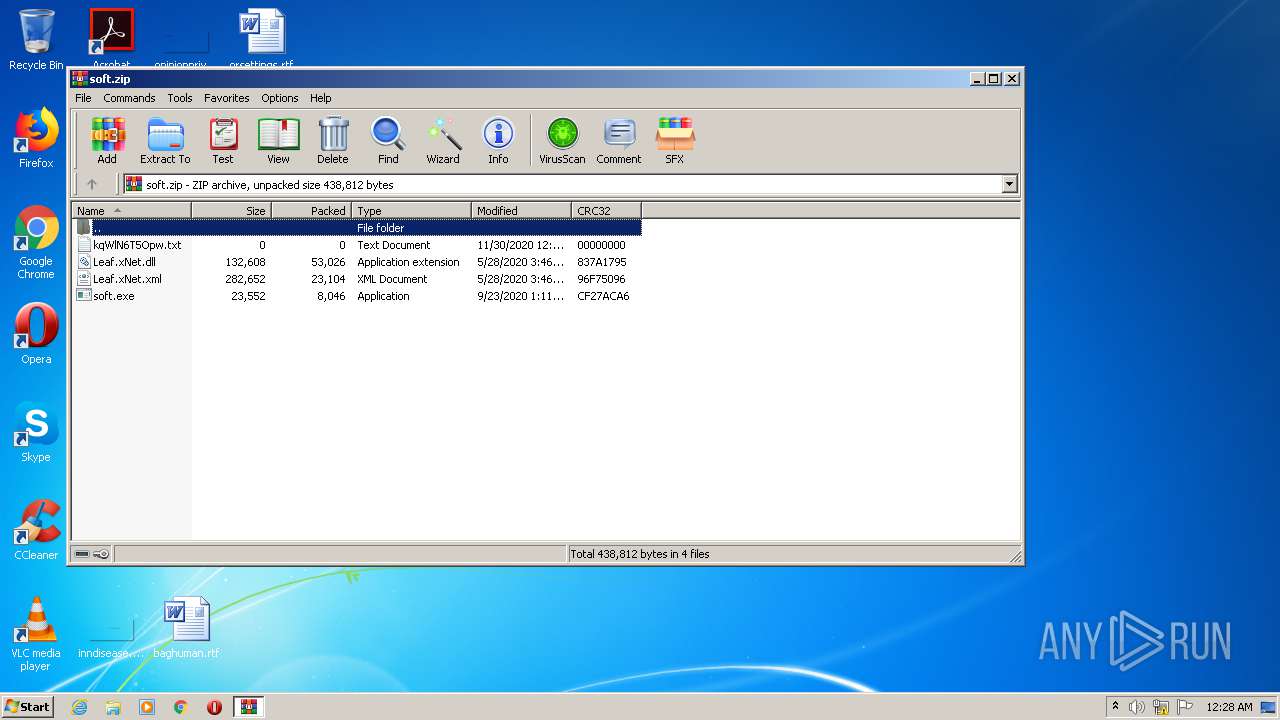
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 7D630C79BF128CB0A72260120BB8AD16 |
| SHA1: | 26DAC3DA10E8377564CAFAADC075C0B245B86258 |
| SHA256: | 5463CCDD9239F5B7B733F8135BEDB59810FFD7356EB591344B7E81846638E24D |
| SSDEEP: | 1536:0DTpSMaVrmUvOJCZqdat2l+J4y+ev2+rVThJk5y1JH66XSCGukx1yf1t+69yZ:YdSMaVrZvTEA+eVrVTzk5Ya7FY59yZ |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3448)
- soft.exe (PID: 3148)
Application was dropped or rewritten from another process
- soft.exe (PID: 3148)
SUSPICIOUS
No suspicious indicators.INFO
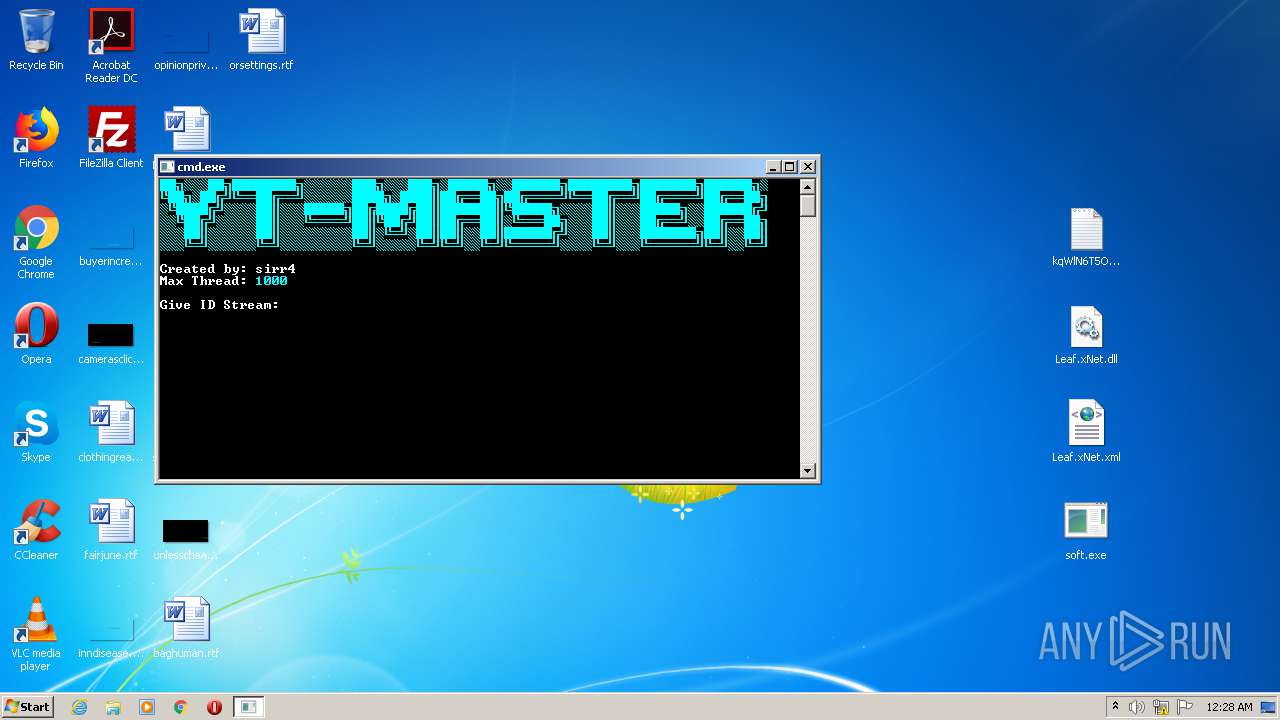
Manual execution by user
- soft.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2020:11:30 09:27:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | kqWlN6T5Opw.txt |
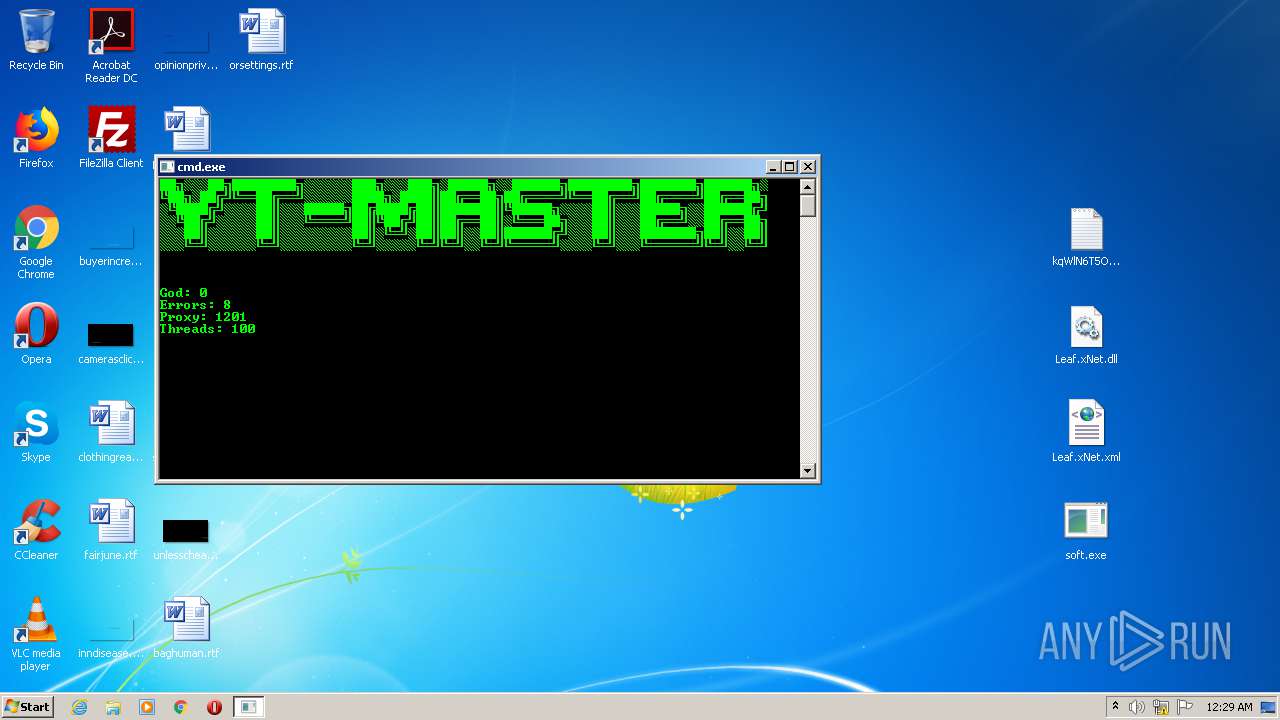
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
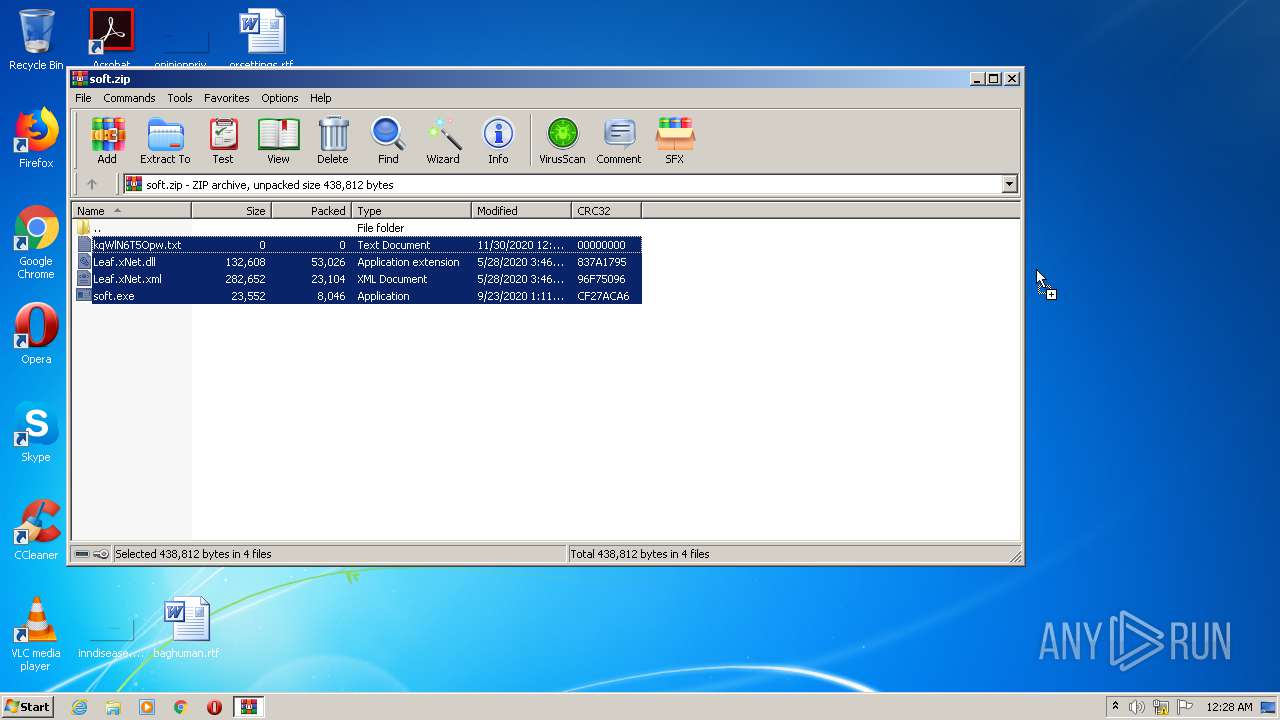
| 620 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\soft.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
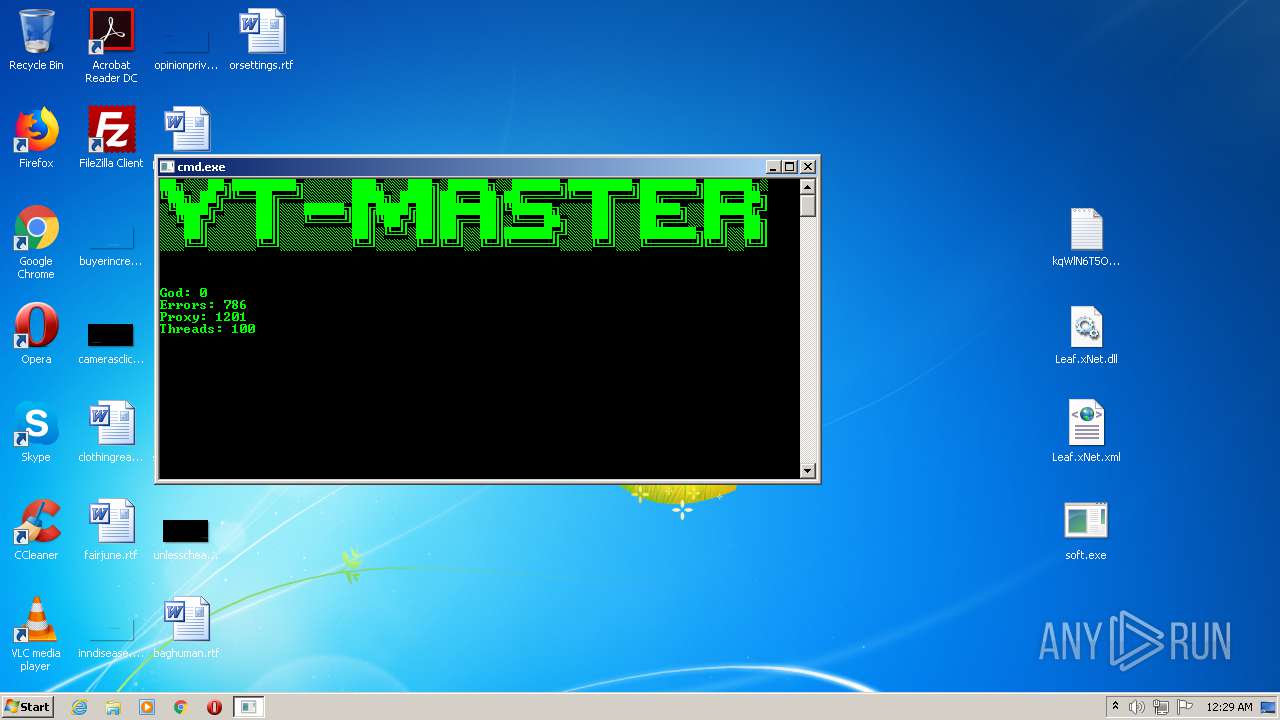
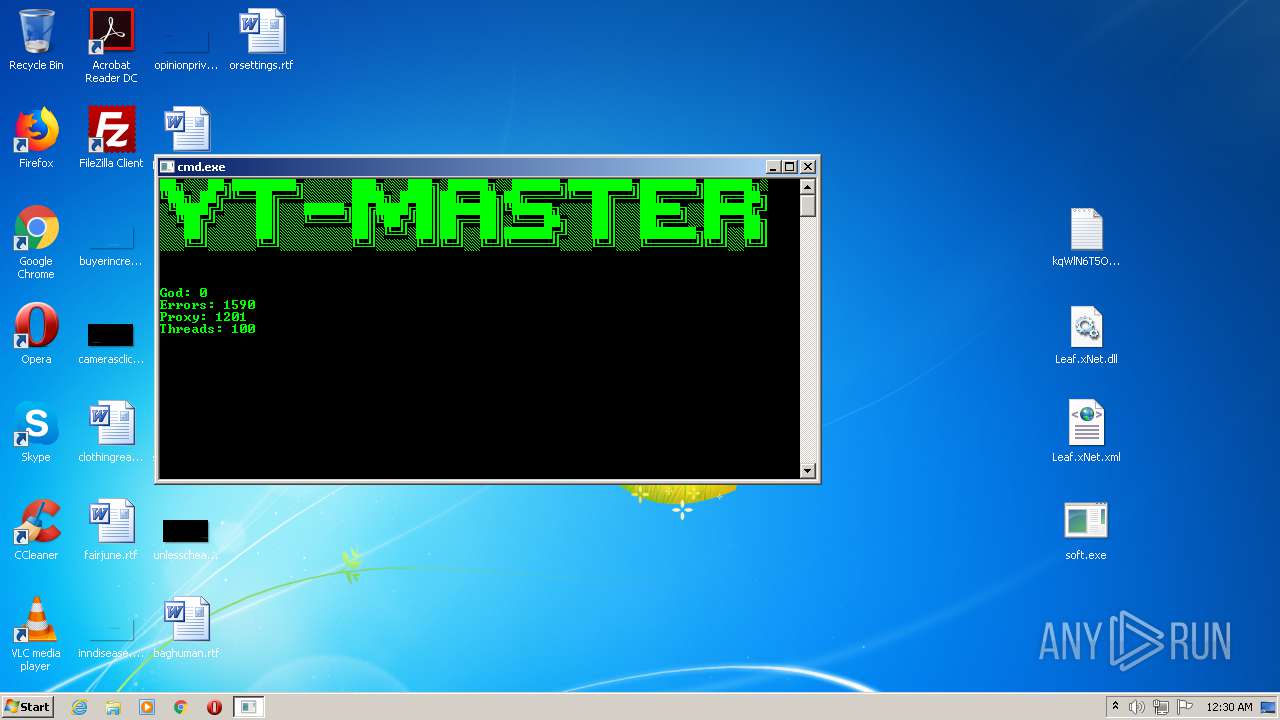
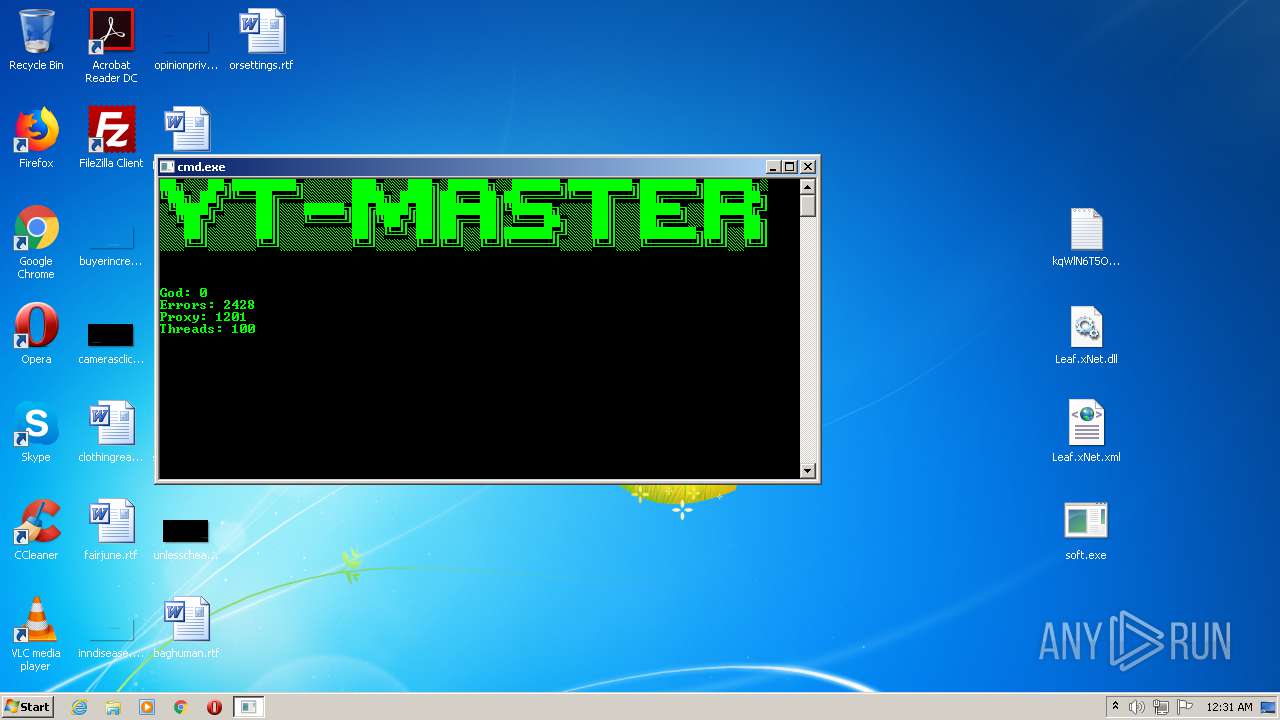
| 3148 | "C:\Users\admin\Desktop\soft.exe" | C:\Users\admin\Desktop\soft.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Youtube-Viewers Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3448 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
486
Read events
450
Write events
36
Delete events
0
Modification events
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\soft.zip | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (620) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
| (PID) Process: | (3448) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
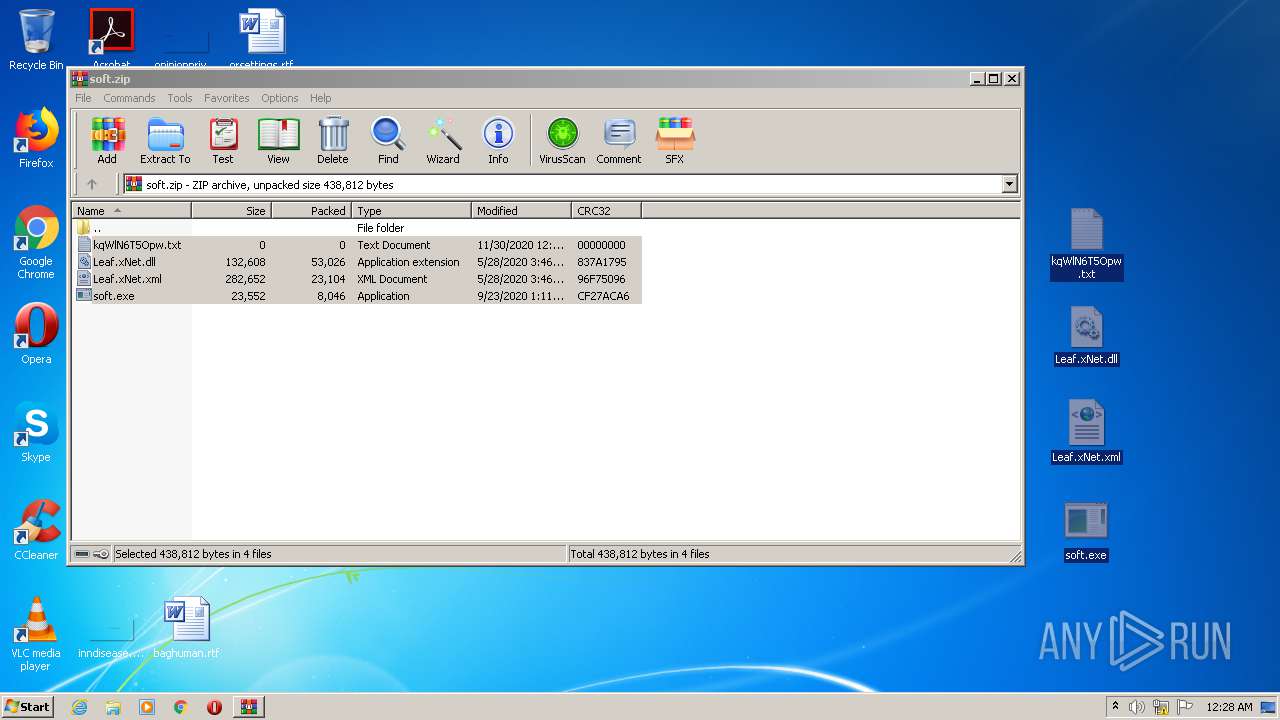
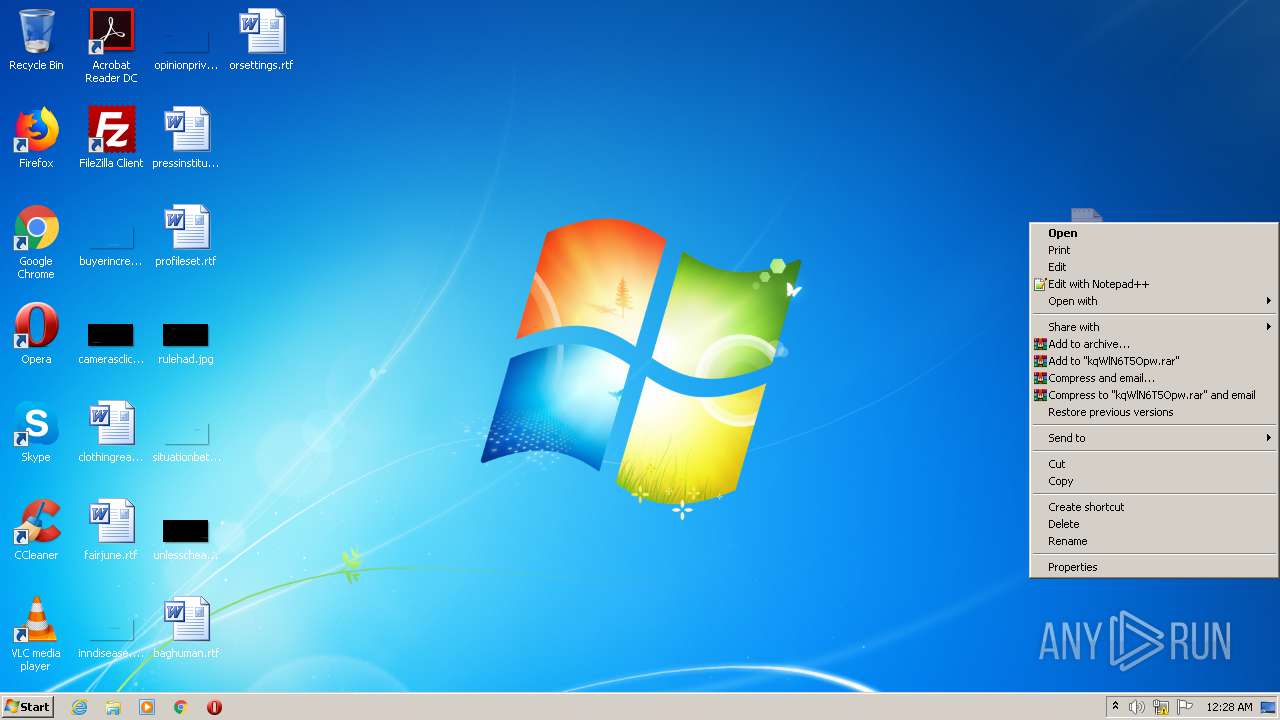
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa620.43665\Leaf.xNet.dll | — | |
MD5:— | SHA256:— | |||
| 620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa620.43665\Leaf.xNet.xml | — | |
MD5:— | SHA256:— | |||
| 620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa620.43665\soft.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4 125
DNS requests
10
Threats
2 437
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | soft.exe | 104.31.74.183:443 | www.proxy-list.download | Cloudflare Inc | US | unknown |
3148 | soft.exe | 114.95.233.11:4145 | — | China Telecom (Group) | CN | suspicious |
3148 | soft.exe | 1.179.148.9:36476 | — | TOT Public Company Limited | TH | suspicious |
3148 | soft.exe | 183.6.130.21:41212 | — | No.31,Jin-rong Street | CN | suspicious |
3148 | soft.exe | 114.250.149.214:36608 | — | China Unicom Beijing Province Network | CN | suspicious |
3148 | soft.exe | 183.182.101.32:44267 | — | PO box T511 Phonexay road - Xaysettha district | LA | suspicious |
3148 | soft.exe | 37.205.81.41:4145 | — | JSC Zap-Sib TransTeleCom, Novosibirsk | RU | suspicious |
3148 | soft.exe | 183.87.69.233:36185 | — | Syscon Infoway Pvt. Ltd. | IN | suspicious |
3148 | soft.exe | 37.228.65.107:51032 | — | JSC Kaztranscom | KZ | suspicious |
3148 | soft.exe | 37.235.220.140:4145 | — | LANTA Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.proxy-list.download |
| malicious |
m.youtube.com |
| whitelisted |
www.google.com |
| malicious |
www.youtube.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |
3148 | soft.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Socks4 Connection |