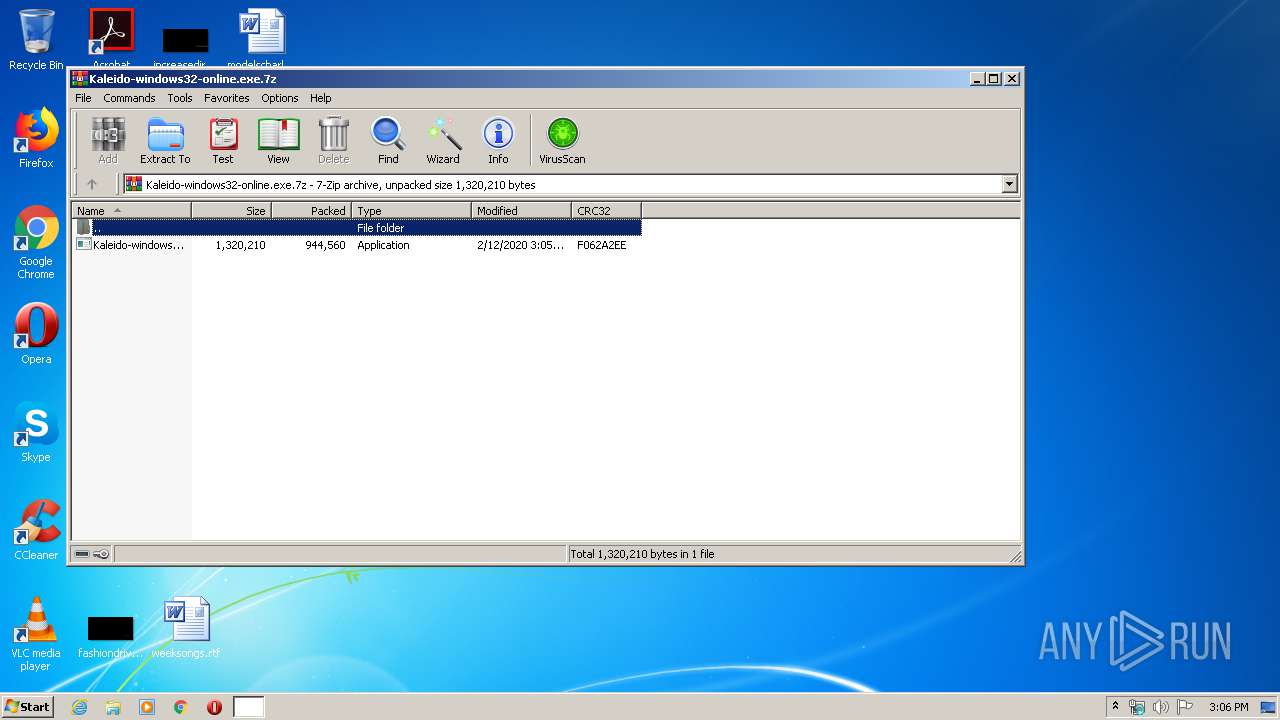
| File name: | Kaleido-windows32-online.exe.7z |
| Full analysis: | https://app.any.run/tasks/e2b0de7d-9e3a-4e7f-9ba4-b81a05dc0321 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2020, 15:06:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.3 |
| MD5: | 44C648D1FF516F64F30A92C0DD9911AB |
| SHA1: | BCA0E4D0707338B8D6C3A91670D5B2C737B84DD9 |
| SHA256: | 545D9E2C4DEF4A0F57E6374220F4419919EFDB5FF9308EAFD0B620E56C5E8D1B |
| SSDEEP: | 24576:9/O9t+LTr3xYecp1y7enwcsg9/3+aBr+W8R2Hpl0UfiojbrO:9/CmxYecp1y7Lct9/ZU2H8ChjPO |
MALICIOUS
Application was dropped or rewritten from another process
- Kaleido-windows32-online.exe (PID: 3492)
SUSPICIOUS
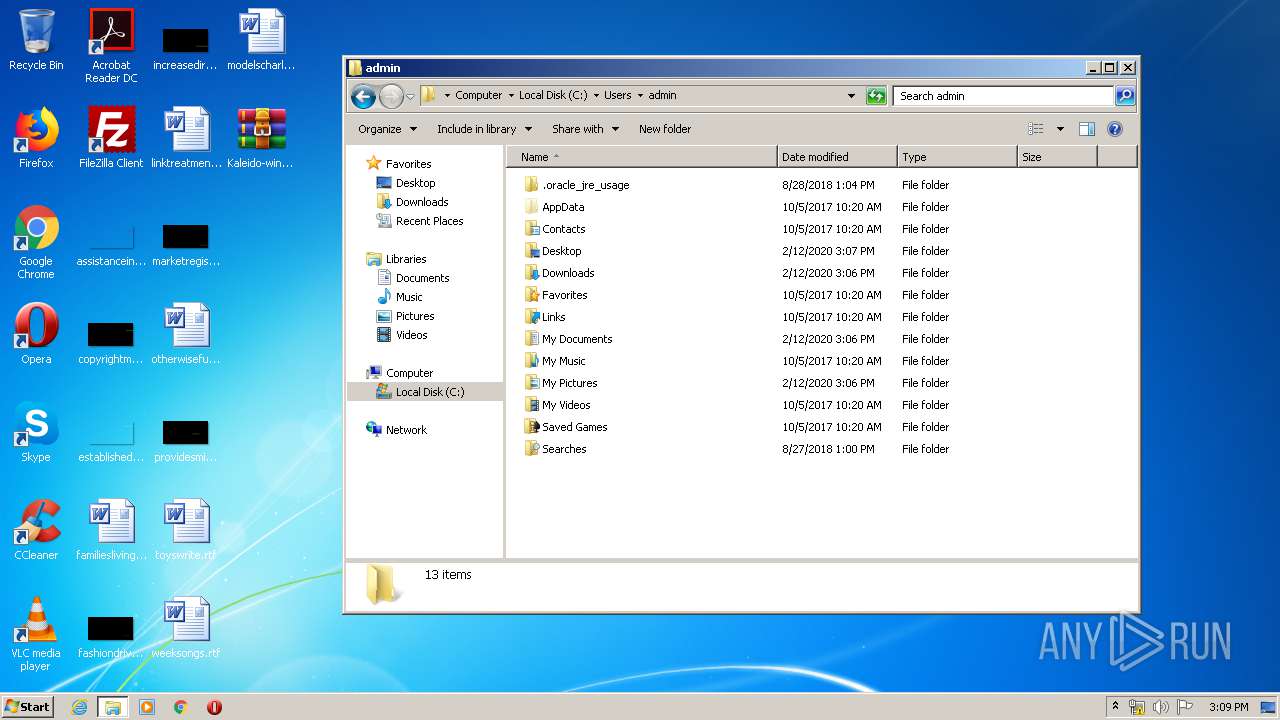
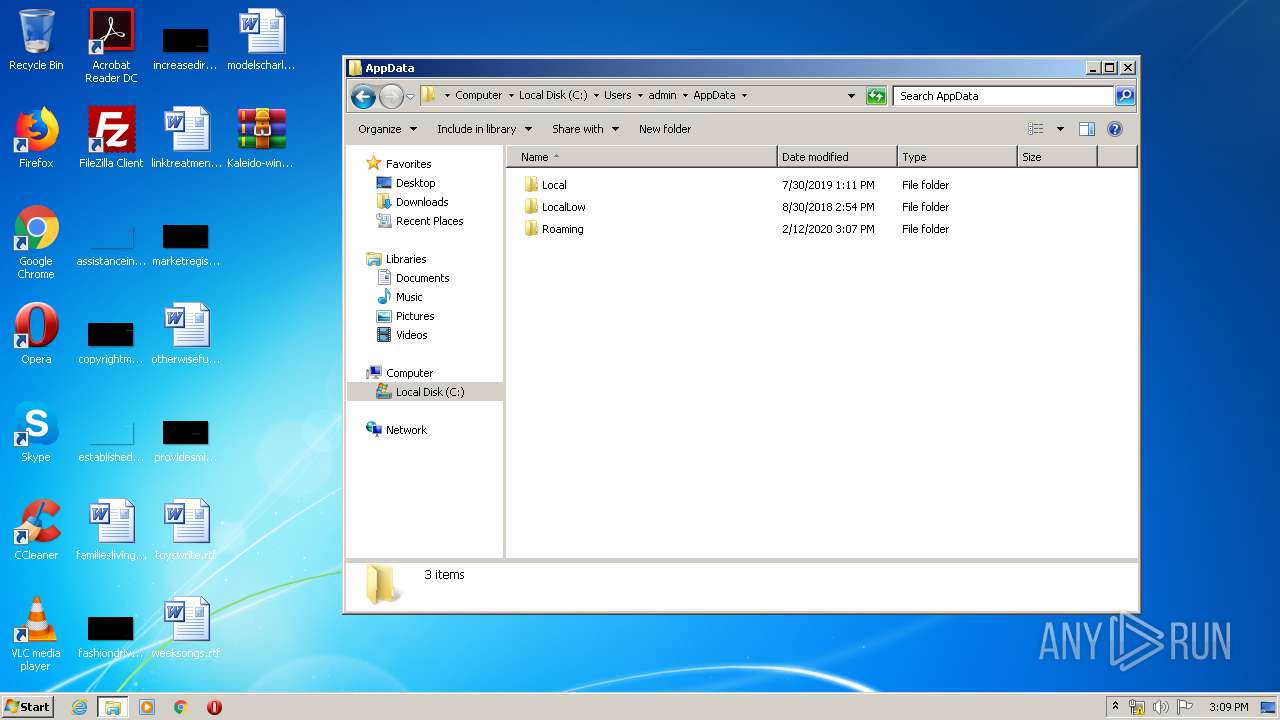
Creates files in the user directory
- lzma.exe (PID: 3796)
- Kaleido-windows32-online.exe (PID: 3492)
Reads Internet Cache Settings
- Kaleido-windows32-online.exe (PID: 3492)
INFO
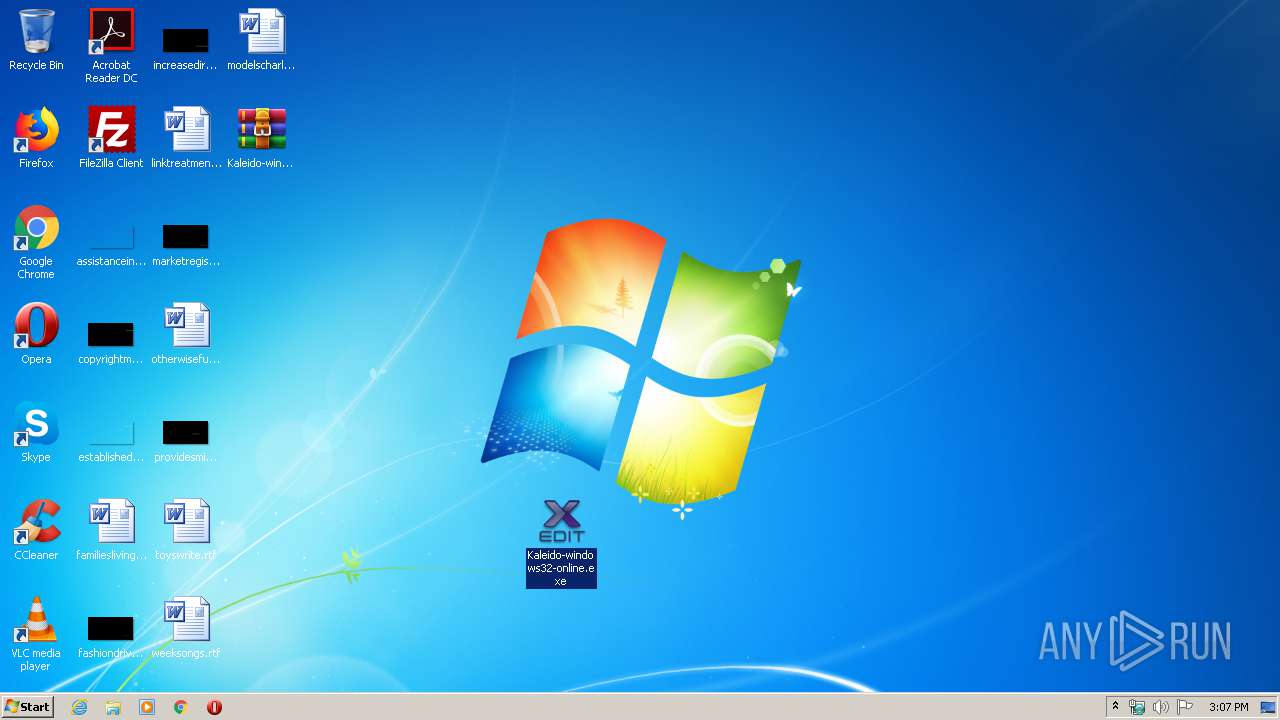
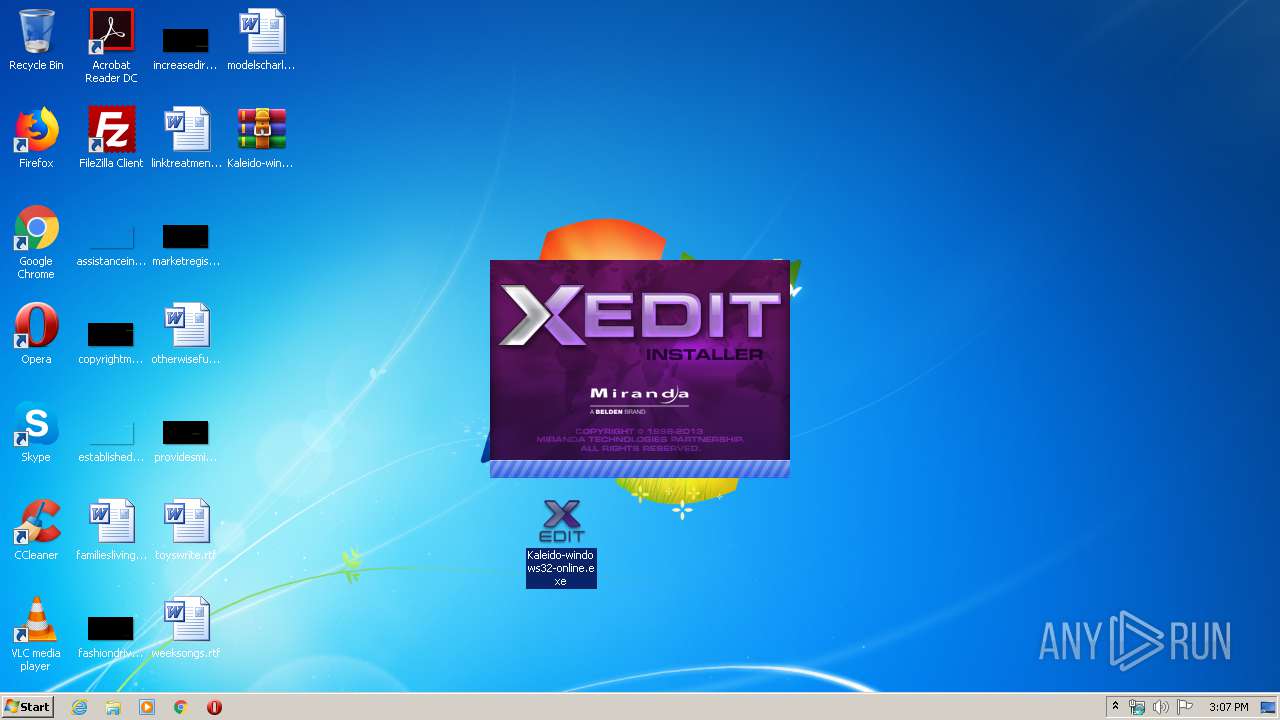
Manual execution by user
- Kaleido-windows32-online.exe (PID: 3492)
- explorer.exe (PID: 3664)
- iexplore.exe (PID: 680)
Reads Internet Cache Settings
- iexplore.exe (PID: 680)
- iexplore.exe (PID: 3308)
Changes internet zones settings
- iexplore.exe (PID: 680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (gen) (100) |
|---|
Total processes
46
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.bing.com/search?q=Create+folders+%2F+append+data&src=IE-TopResult&FORM=IE11TR&conversationid= | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1744 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Kaleido-windows32-online.exe.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:680 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\Desktop\Kaleido-windows32-online.exe" | C:\Users\admin\Desktop\Kaleido-windows32-online.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3664 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
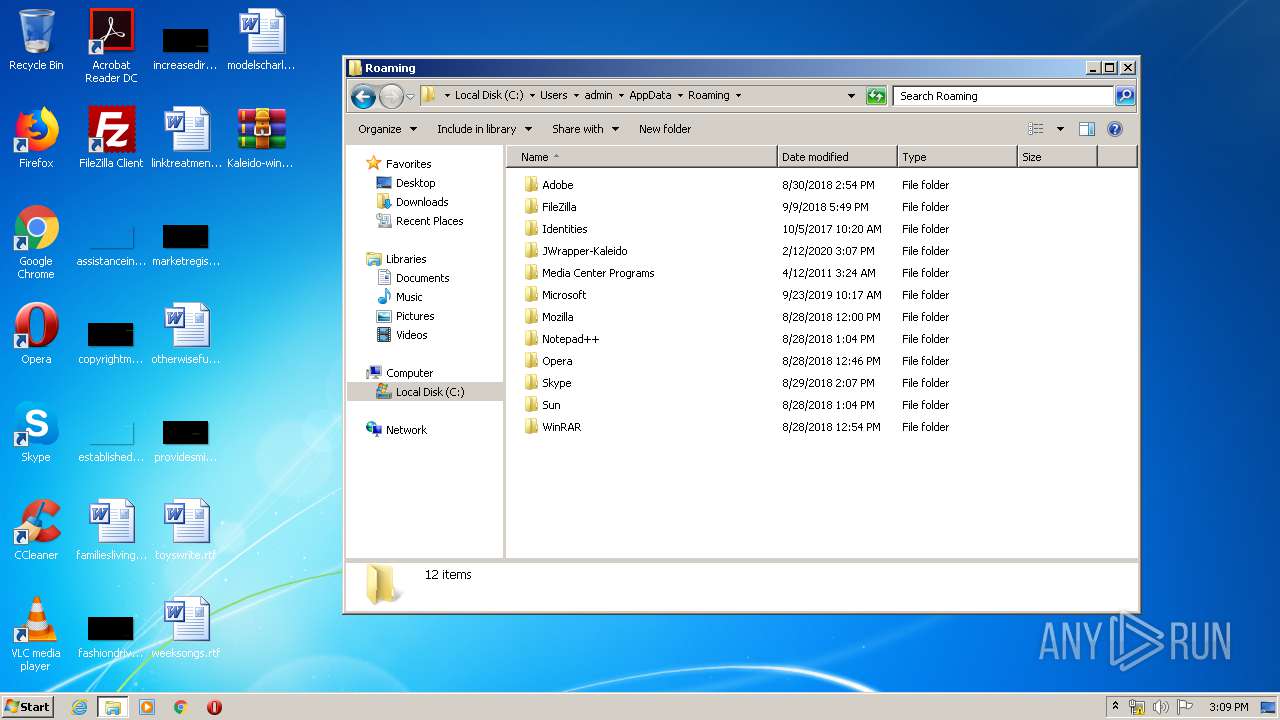
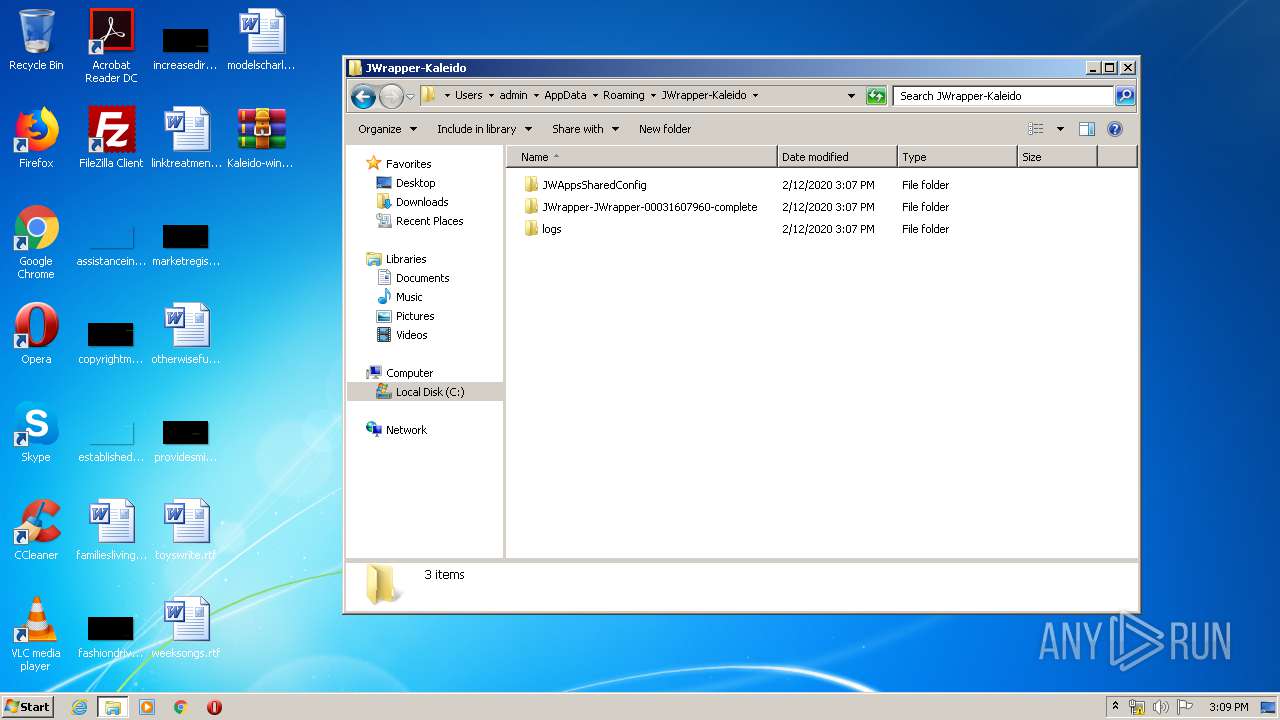
| 3796 | "C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\lzma.exe" "d" "C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\JWrapper-JWrapper-00031607960-archive.p2.l2" "C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\JWrapper-JWrapper-00031607960-archive.p2" | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\lzma.exe | — | Kaleido-windows32-online.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
562
Read events
489
Write events
69
Delete events
4
Modification events
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Kaleido-windows32-online.exe.7z | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
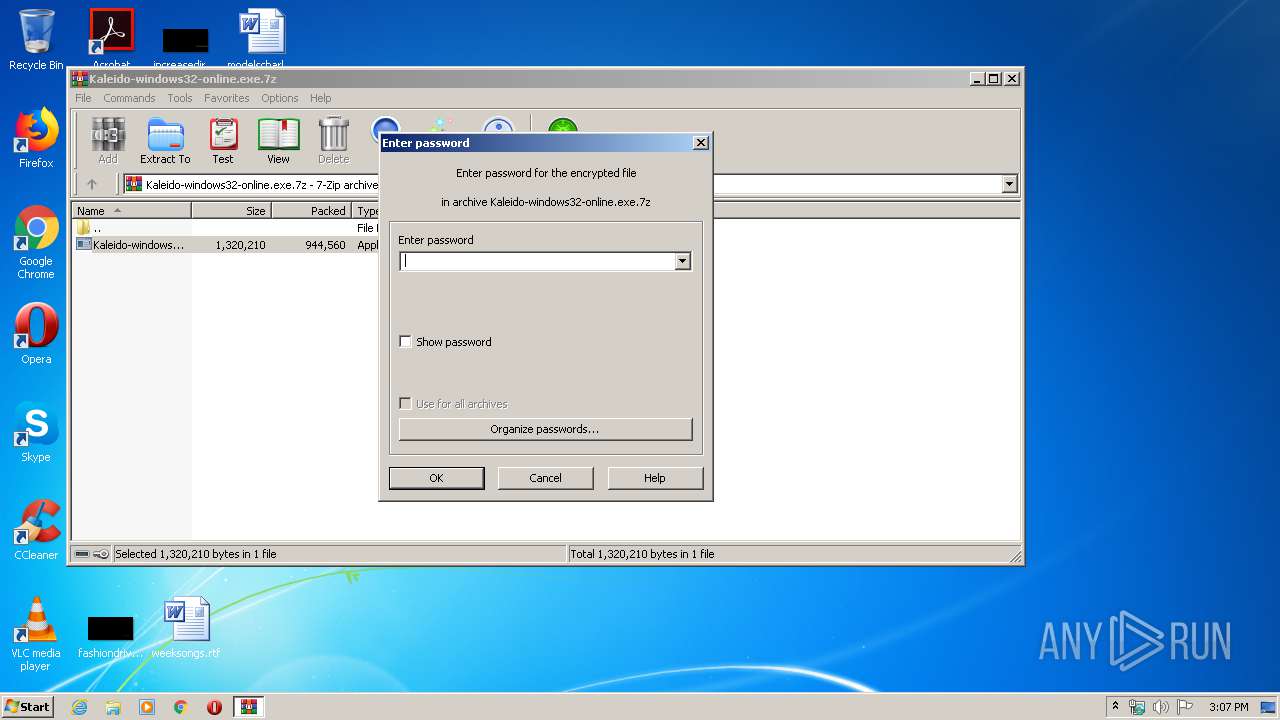
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1744) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
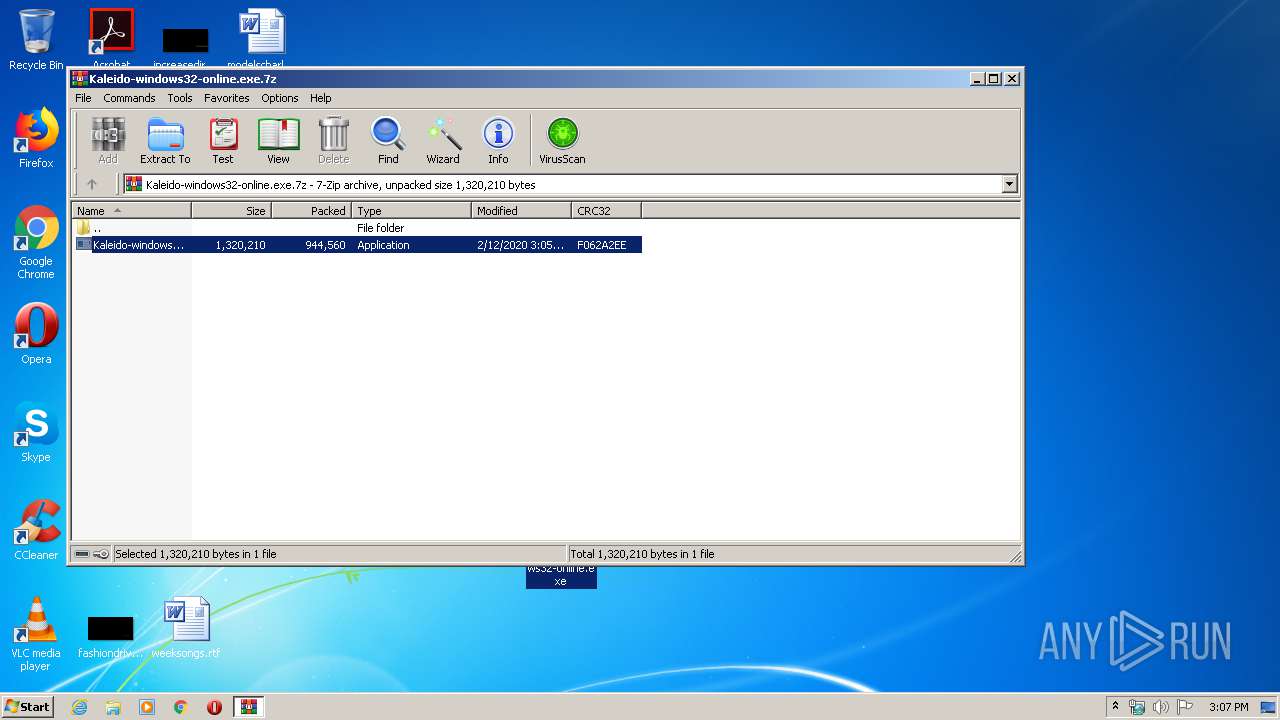
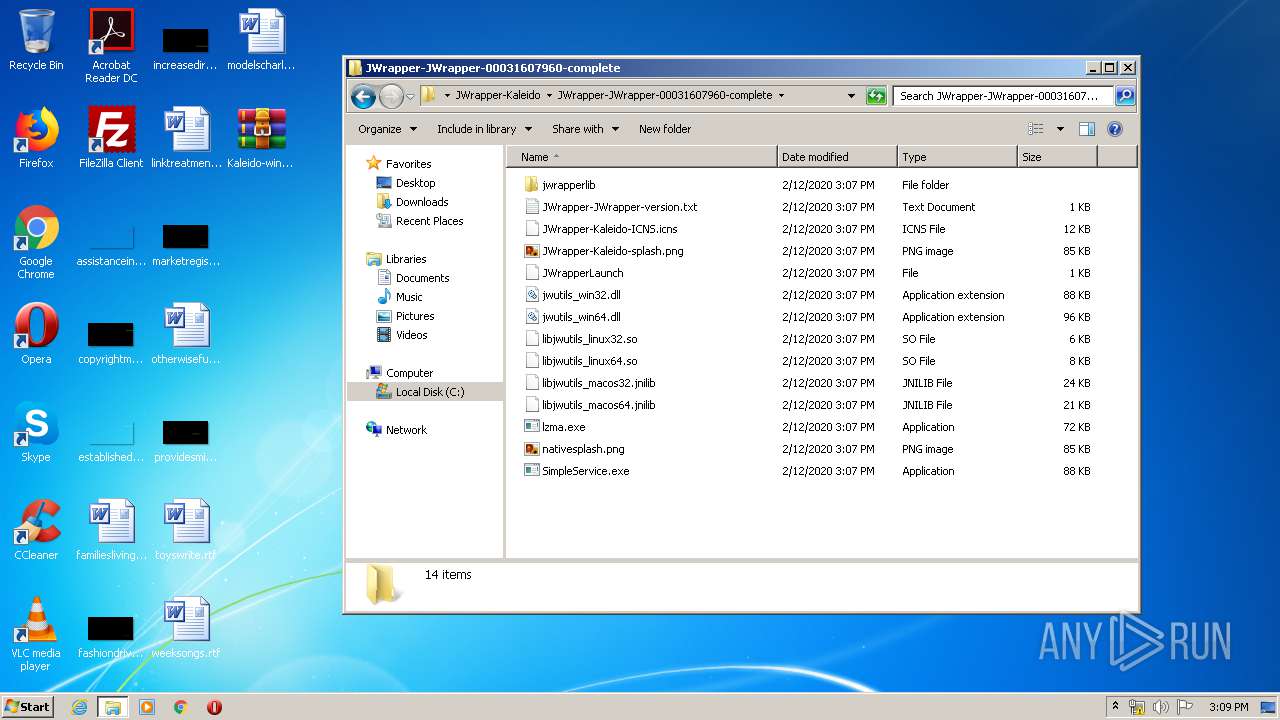
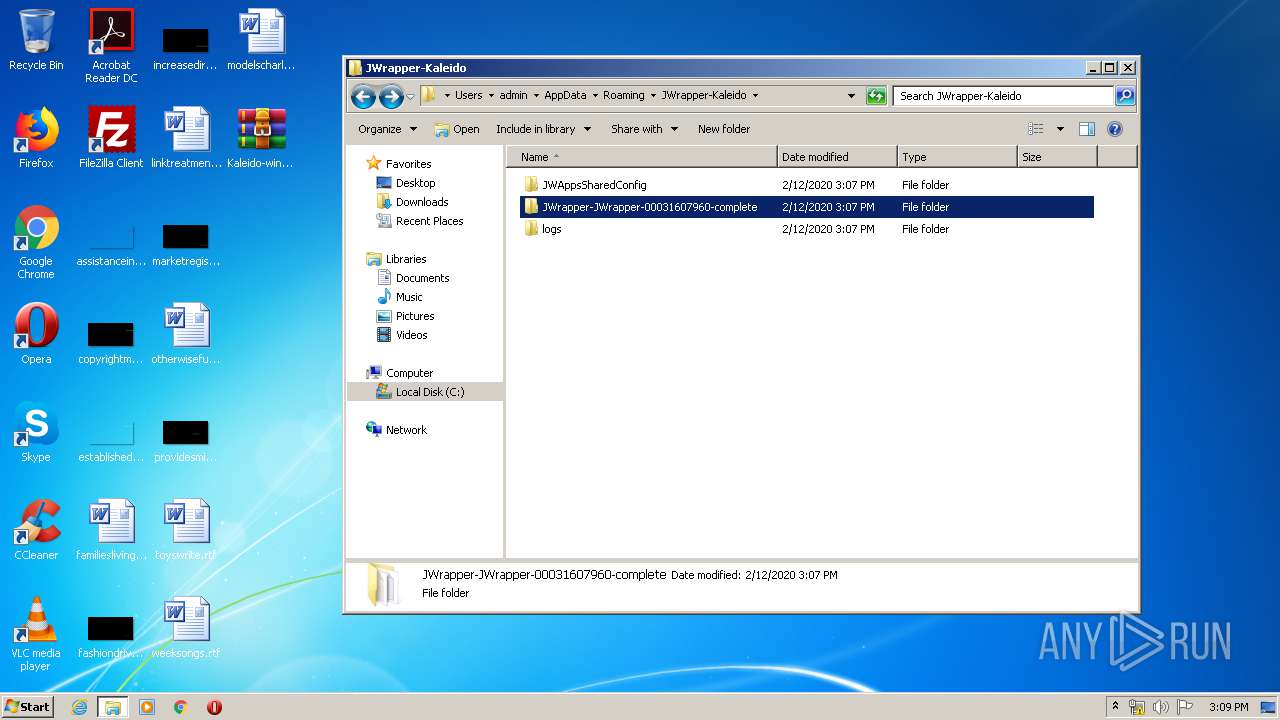
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1744.2413\Kaleido-windows32-online.exe | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\lzma.exe | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\nativesplash.png | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\JWrapper-JWrapper-00031607960-archive.p2.l2 | — | |
MD5:— | SHA256:— | |||
| 3796 | lzma.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\JWrapper-JWrapper-00031607960-archive.p2 | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\jwrapperlib\jwstandalonelaunch.jar | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\jwrapperlib\jwstandalone.jar | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\jwrapperlib\sevenzip.jar | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\JWrapper-Kaleido-splash.png | — | |
MD5:— | SHA256:— | |||
| 3492 | Kaleido-windows32-online.exe | C:\Users\admin\AppData\Roaming\JWrapper-Kaleido\JWrapperTemp-1581520028-0-app\JWrapper-Kaleido-ICNS.icns | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3492 | Kaleido-windows32-online.exe | GET | — | 172.30.16.94:80 | http://172.30.16.94/installers/xedit/JWrapper-Windows32JRE-version.txt | unknown | — | — | unknown |
3492 | Kaleido-windows32-online.exe | GET | — | 172.30.16.94:80 | http://172.30.16.94/installers/xedit/JWrapper-Windows32JRE-version.txt | unknown | — | — | unknown |
3492 | Kaleido-windows32-online.exe | GET | — | 172.30.16.94:80 | http://172.30.16.94/installers/xedit/JWrapper-Windows32JRE-version.txt | unknown | — | — | unknown |
3308 | iexplore.exe | GET | — | 13.107.21.200:80 | http://www.bing.com/search?q=Create+folders+%2F+append+data&src=IE-TopResult&FORM=IE11TR&conversationid= | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3492 | Kaleido-windows32-online.exe | 172.30.16.94:80 | — | — | — | unknown |
3308 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |