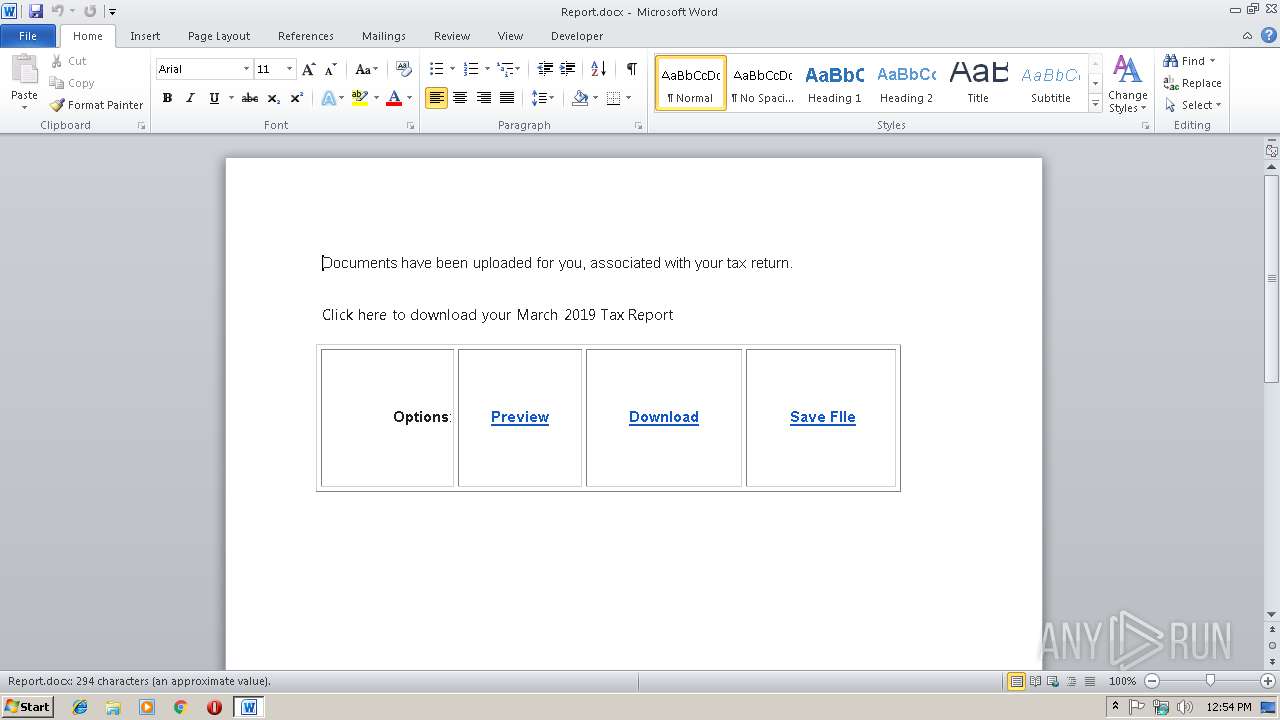
| File name: | Report.docx |
| Full analysis: | https://app.any.run/tasks/6d49b531-ec17-4a66-ab7a-9168987b5fae |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 12:53:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 2AFAD5FF40FBE4B6762615870CE4B459 |
| SHA1: | 0FBC8DECEF21E57BF86F01471625216186ED1864 |
| SHA256: | 5455853B2935E1A2C4E4668BA61D20BF7FFE5F3E2D23204CA90E8A169C15384F |
| SSDEEP: | 384:aSBfbYI9C78Q/m5d6+9vmBFnEnwZStp9P4:LDf28mmq+9YV3Z1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
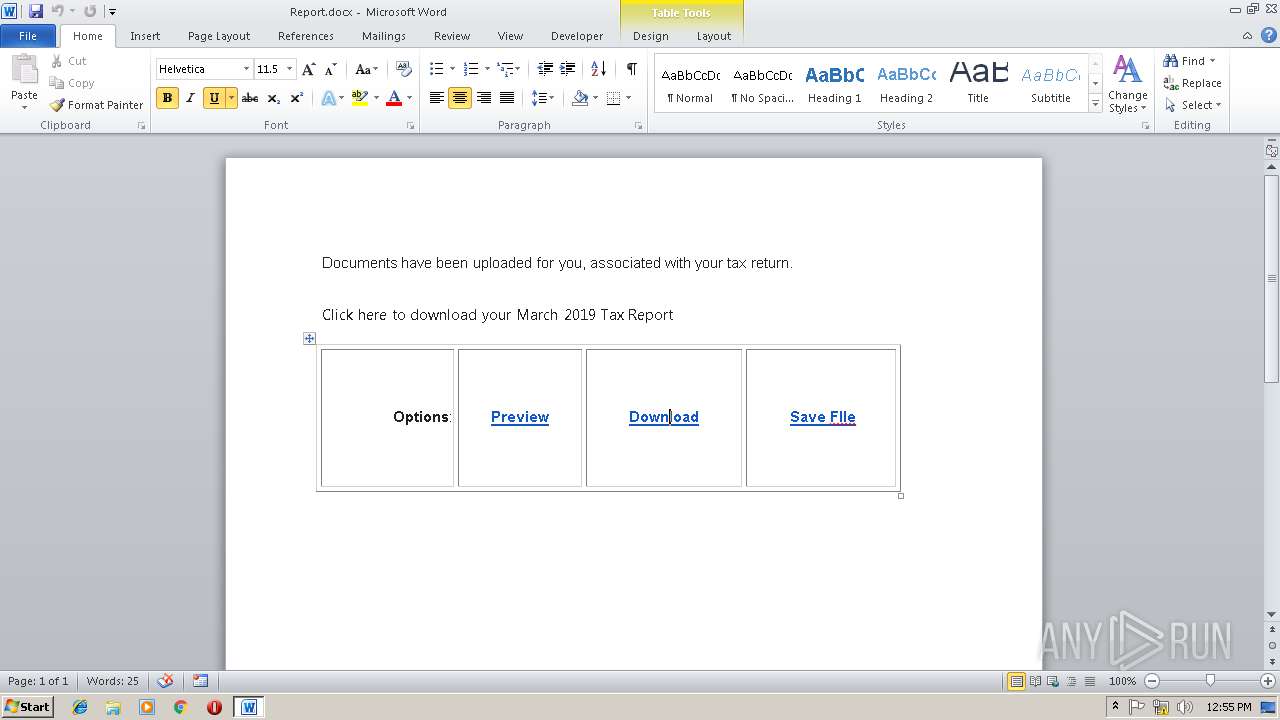
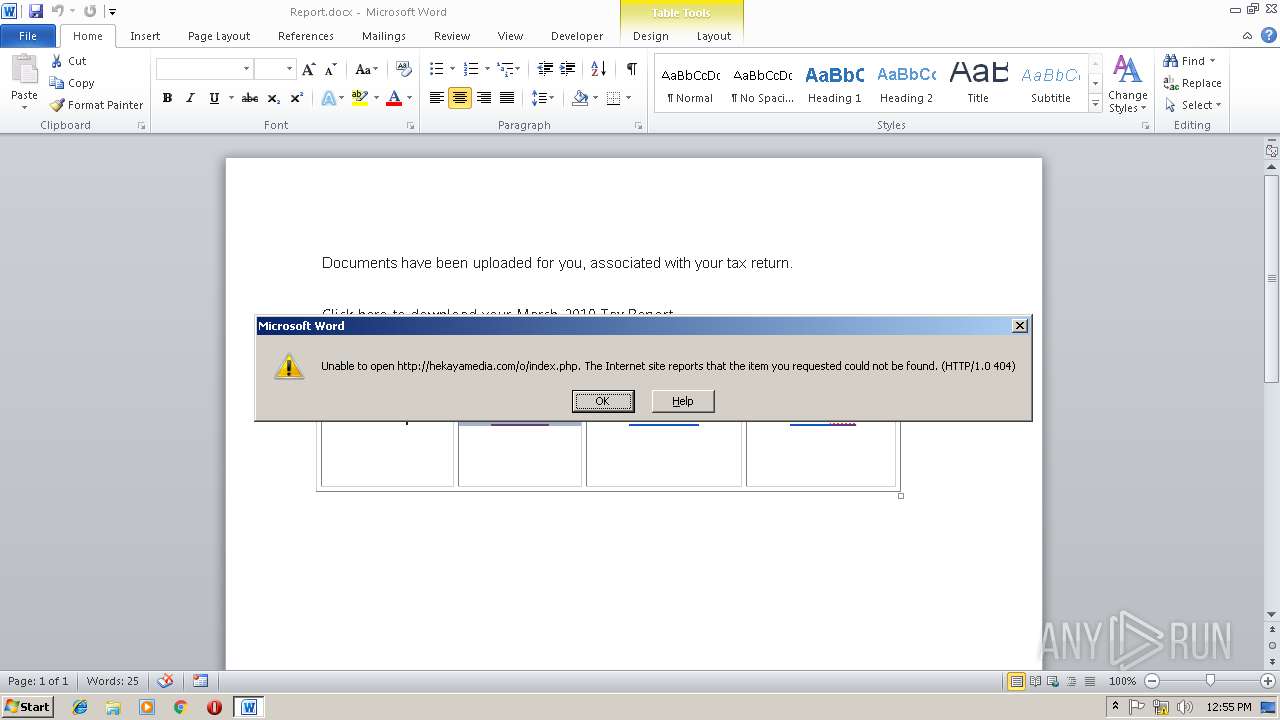
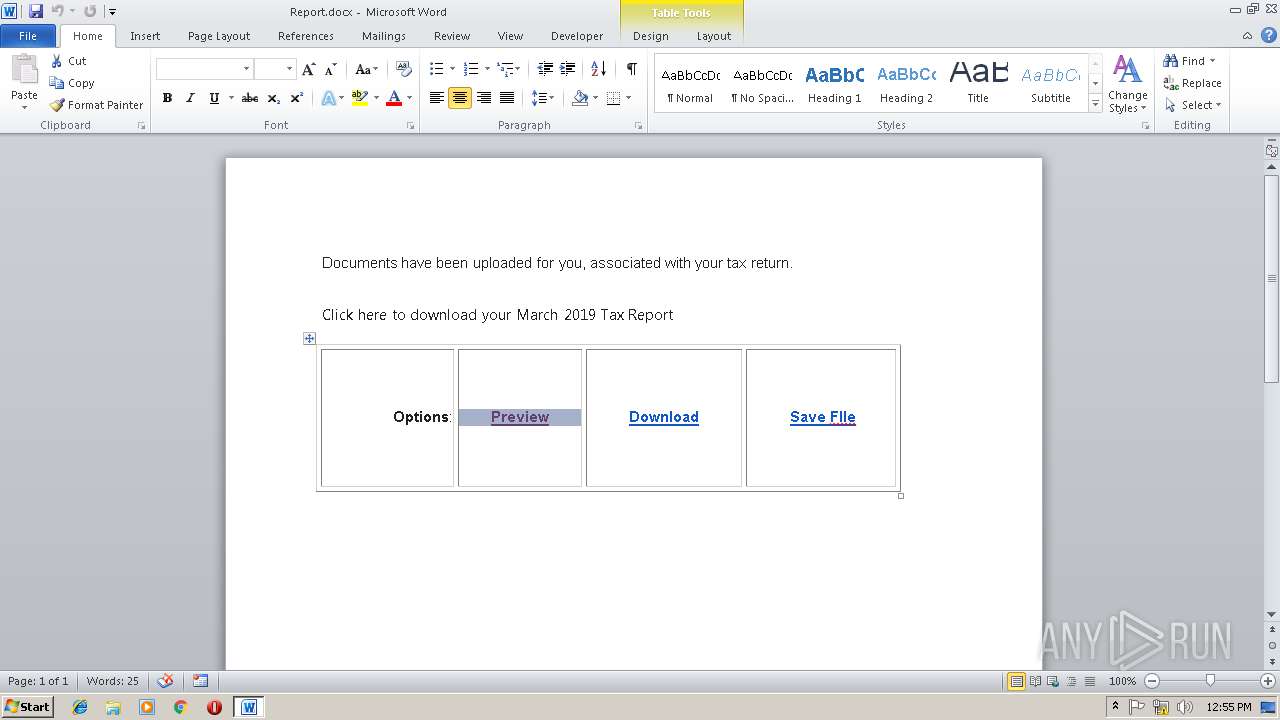
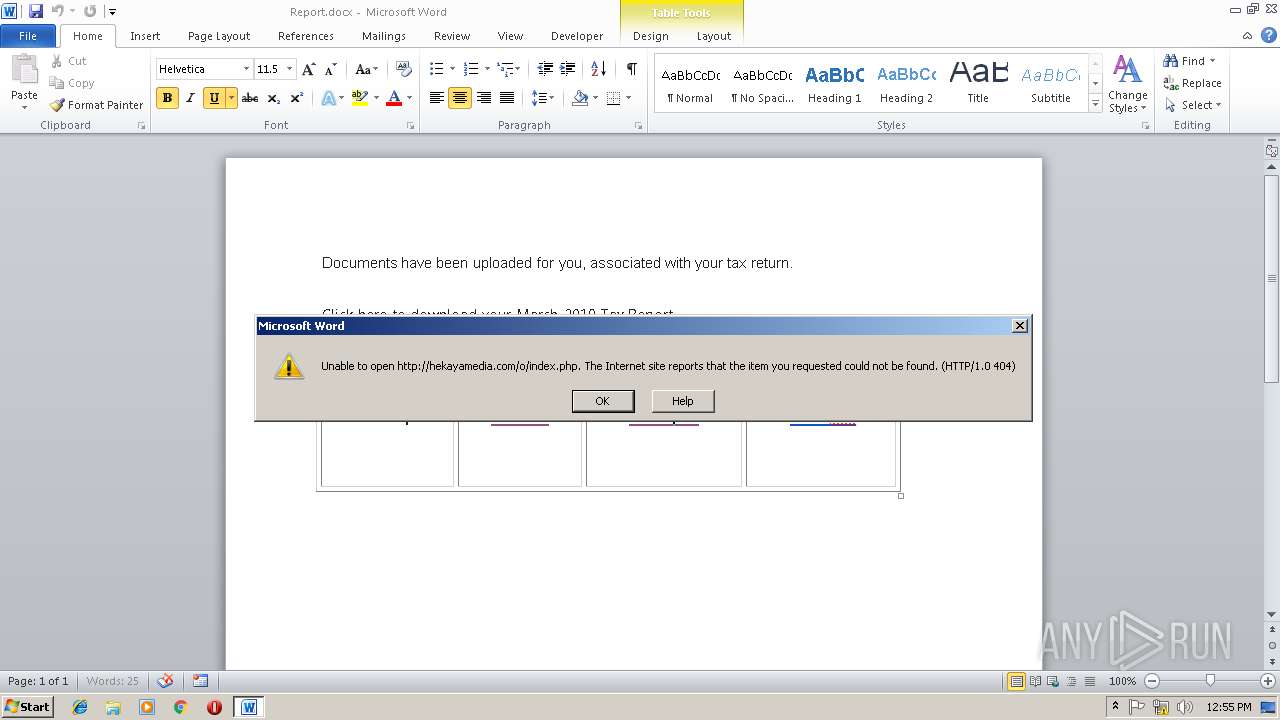
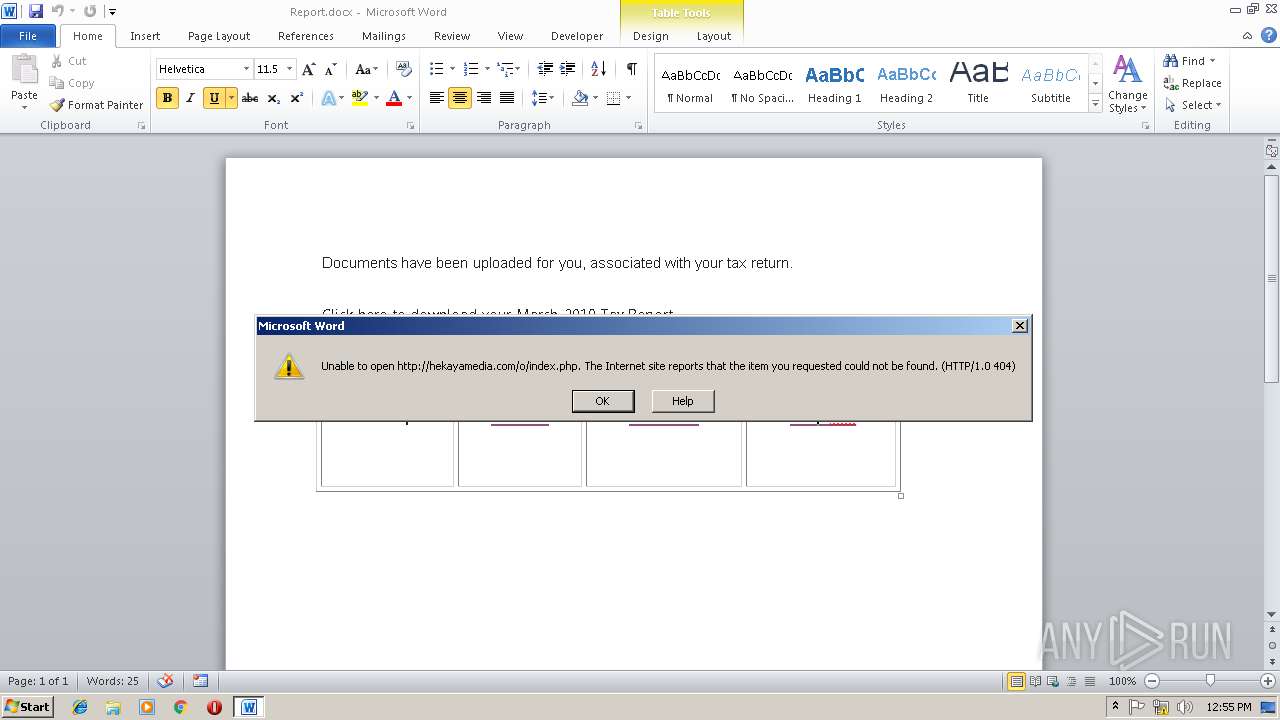
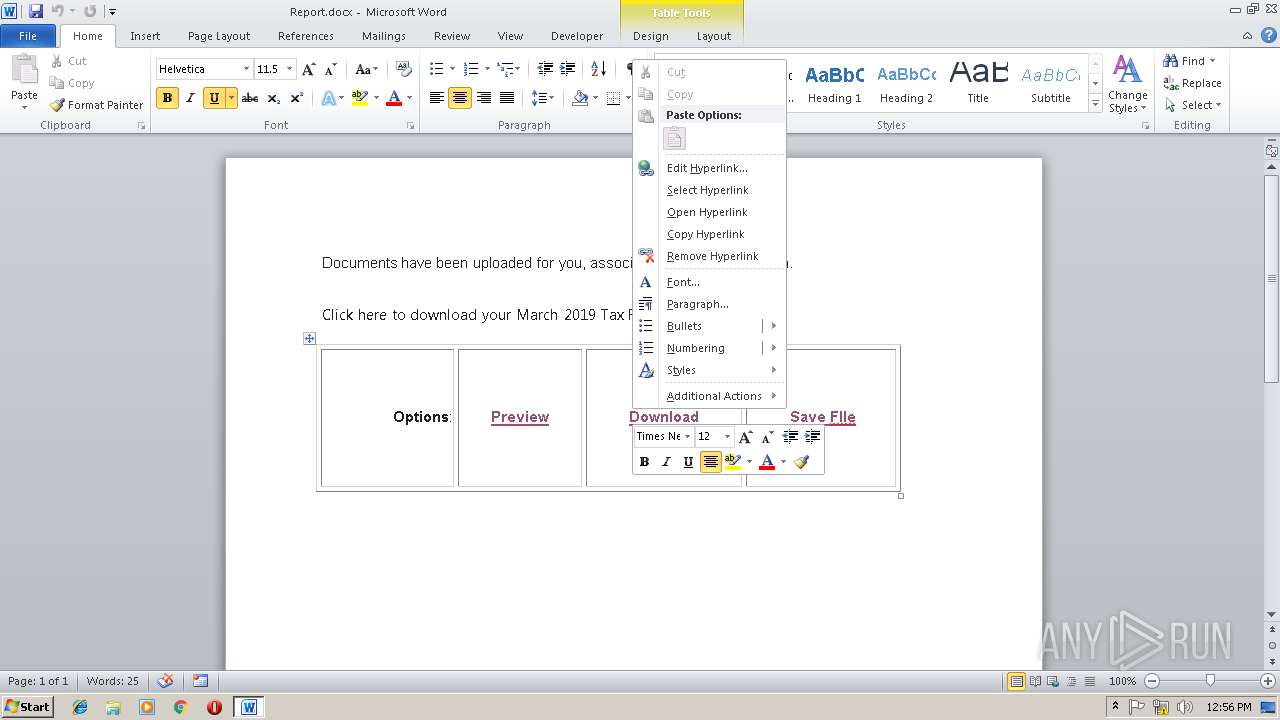
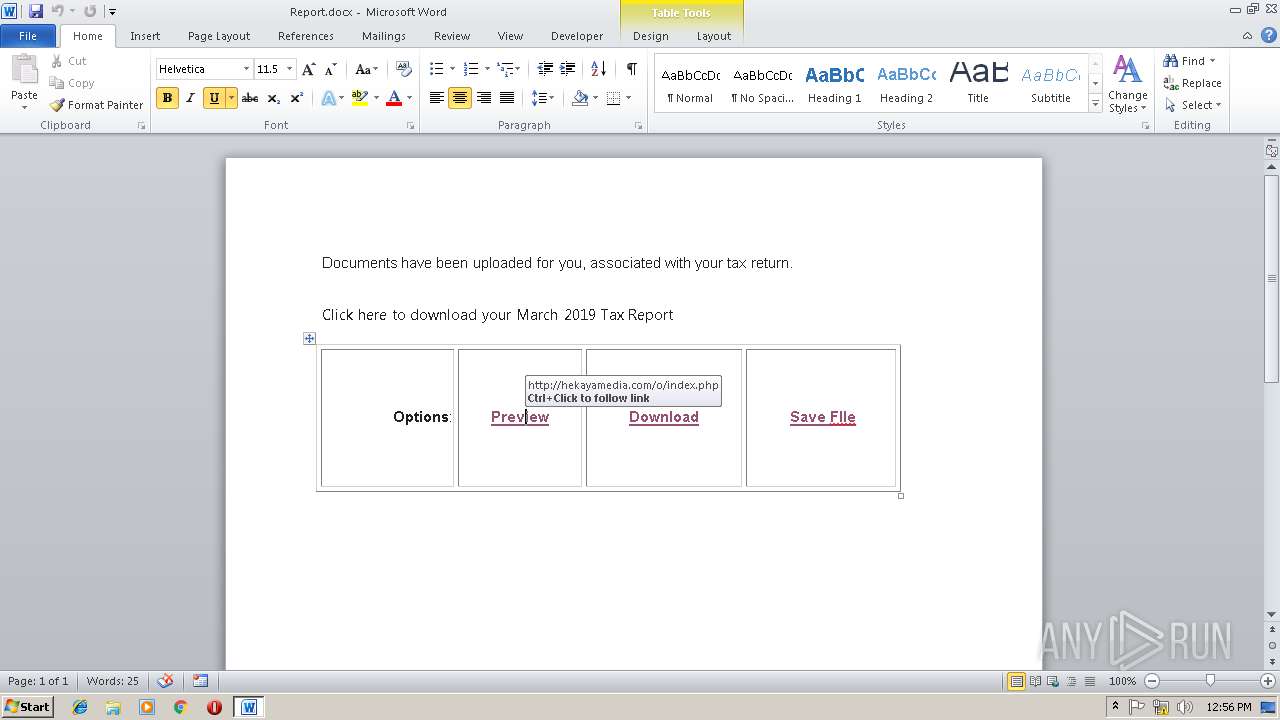
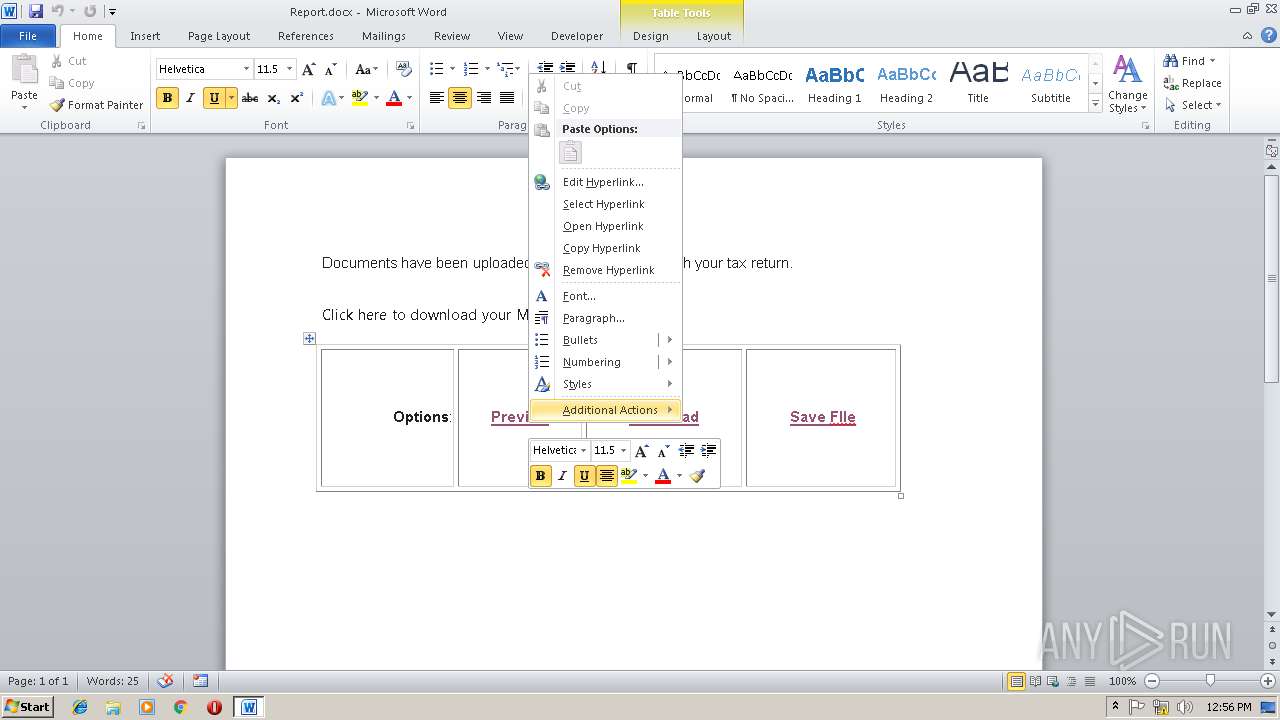
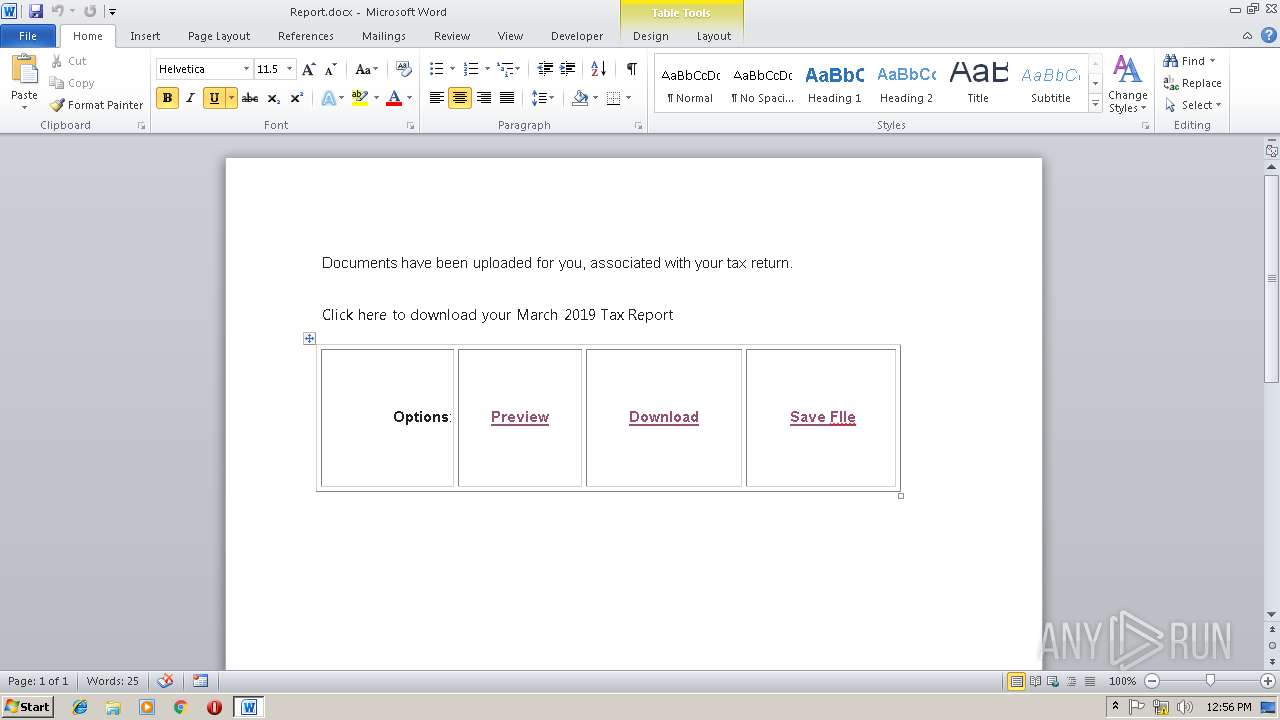
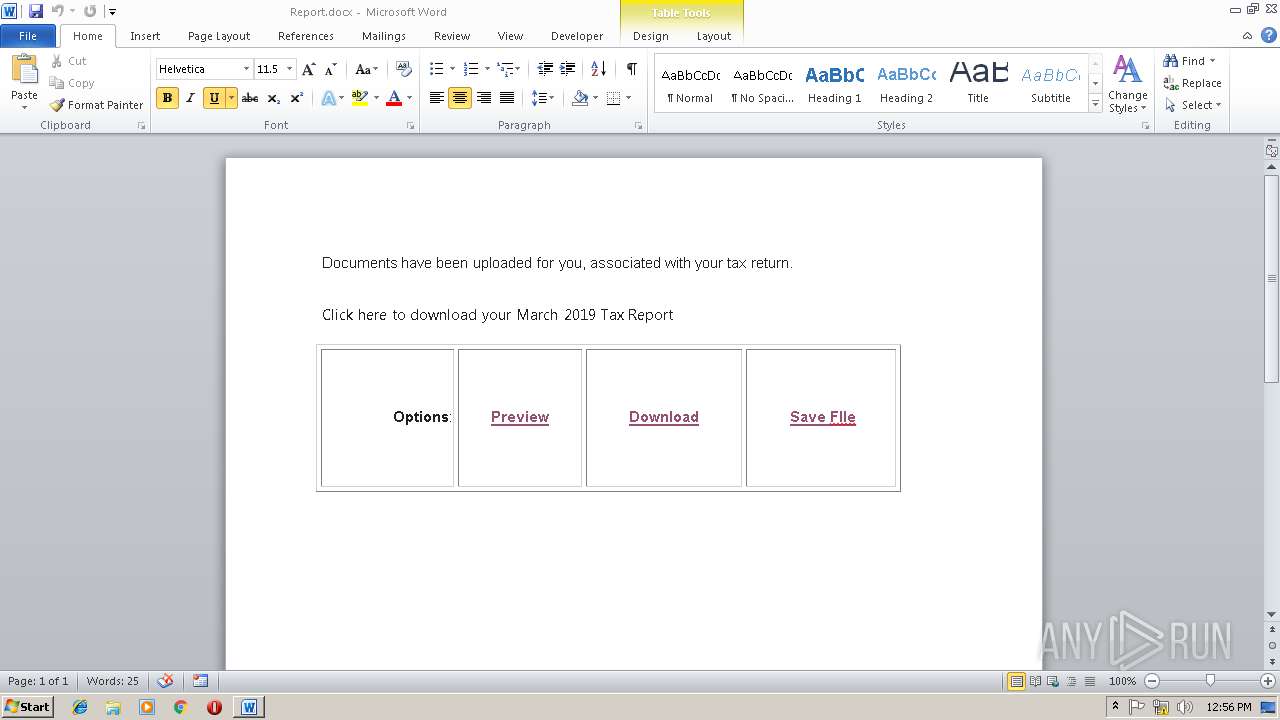
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2872)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2872)
Creates files in the user directory
- WINWORD.EXE (PID: 2872)
Reads settings of System Certificates
- chrome.exe (PID: 3732)
Application launched itself
- chrome.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x6cd2a4df |
| ZipCompressedSize: | 346 |
| ZipUncompressedSize: | 1312 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | 58 minutes |
| Pages: | 1 |
| Words: | 53 |
| Characters: | 304 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 2 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 356 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | OG |
| RevisionNumber: | 7 |
| CreateDate: | 2019:03:11 12:50:00Z |
| ModifyDate: | 2019:03:13 18:09:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | OG |
| Description: | - |
Total processes
46
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C2E3263E80B8A104961F3F8433F7A8E3 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C2E3263E80B8A104961F3F8433F7A8E3 --renderer-client-id=10 --mojo-platform-channel-handle=4228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=49A35C6380F37D0CCC5F808CA7D6B57D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=49A35C6380F37D0CCC5F808CA7D6B57D --renderer-client-id=11 --mojo-platform-channel-handle=4044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6b7500b0,0x6b7500c0,0x6b7500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=9917E3BFB186AF09F2D24E9D5A99F4A0 --mojo-platform-channel-handle=936 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Report.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2E644BF409732590A4C594AF5523353E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2E644BF409732590A4C594AF5523353E --renderer-client-id=7 --mojo-platform-channel-handle=3800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --service-pipe-token=8F767D079B65AC32A1E9067074D3F0A6 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8F767D079B65AC32A1E9067074D3F0A6 --renderer-client-id=5 --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=D77602A0663B99111FAEBEC7C1AAD7C9 --mojo-platform-channel-handle=3604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8328CE63EC04252AFA87D4F925E40762 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8328CE63EC04252AFA87D4F925E40762 --renderer-client-id=6 --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=856,5447787342929307212,6825040669527197026,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8B9F4012FD452C82E9550D88B1AAEB1F --mojo-platform-channel-handle=2172 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 457
Read events
796
Write events
651
Delete events
10
Modification events
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | w.% |
Value: 772E2500380B0000010000000000000000000000 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831838 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831952 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831953 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 380B0000FAE8771665DAD40100000000 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | s1% |
Value: 73312500380B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | s1% |
Value: 73312500380B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2872) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
57
Text files
71
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD2D7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dba85212-04cf-4306-b585-fdb5a646090a.tmp | — | |
MD5:— | SHA256:— | |||
| 3732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2872 | WINWORD.EXE | C:\Users\admin\Desktop\~$Report.docx | pgc | |
MD5:— | SHA256:— | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Report.docx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\55ee231e-bae4-428a-8b93-316d4a4a053f.tmp | — | |
MD5:— | SHA256:— | |||
| 3732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
29
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
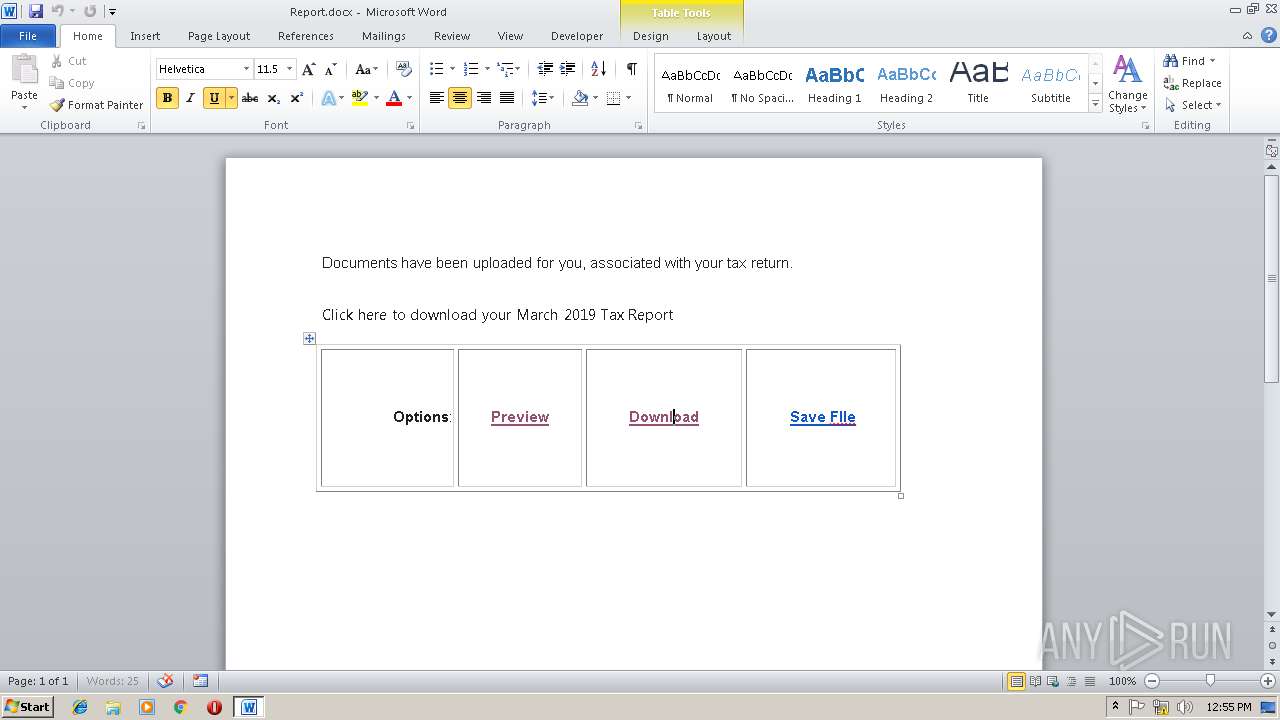
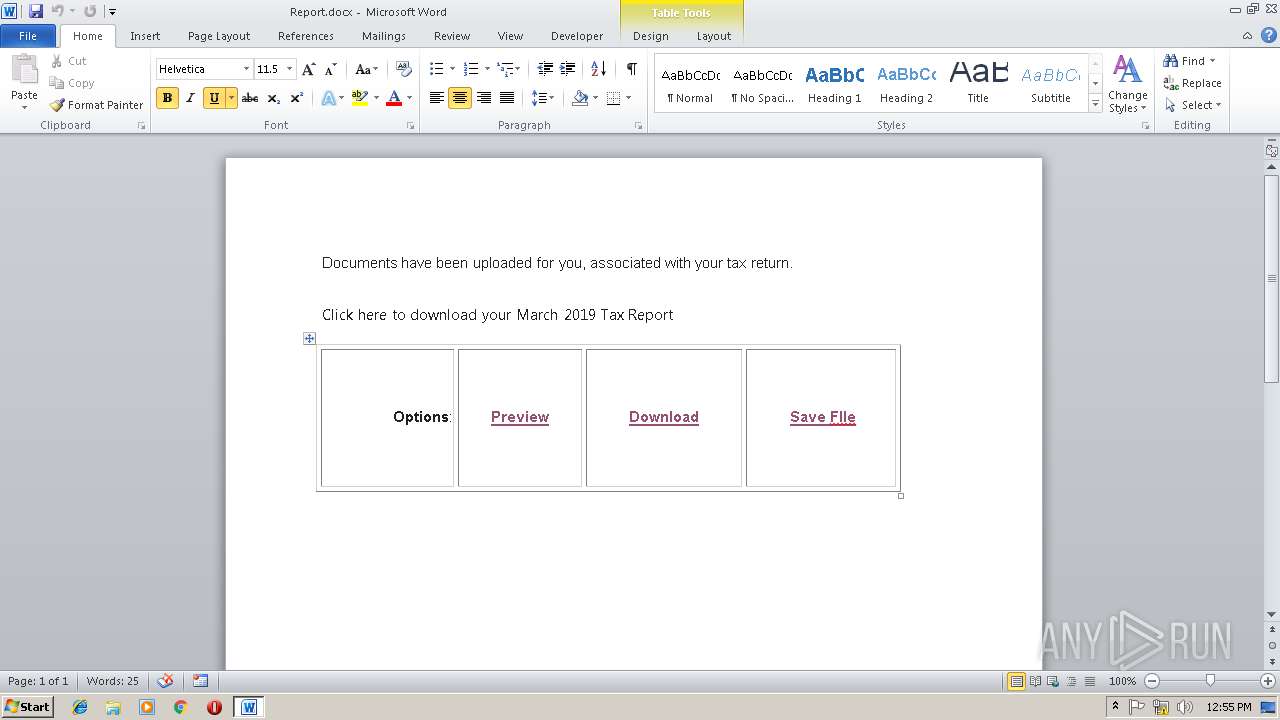
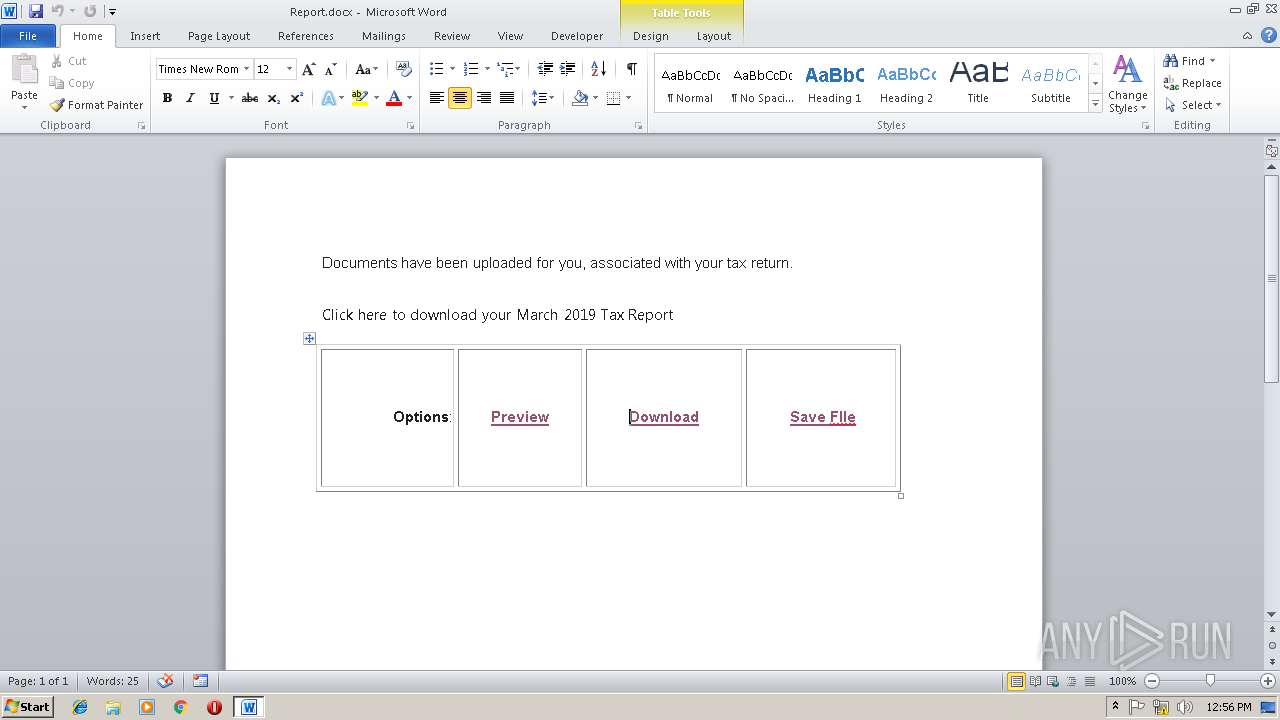
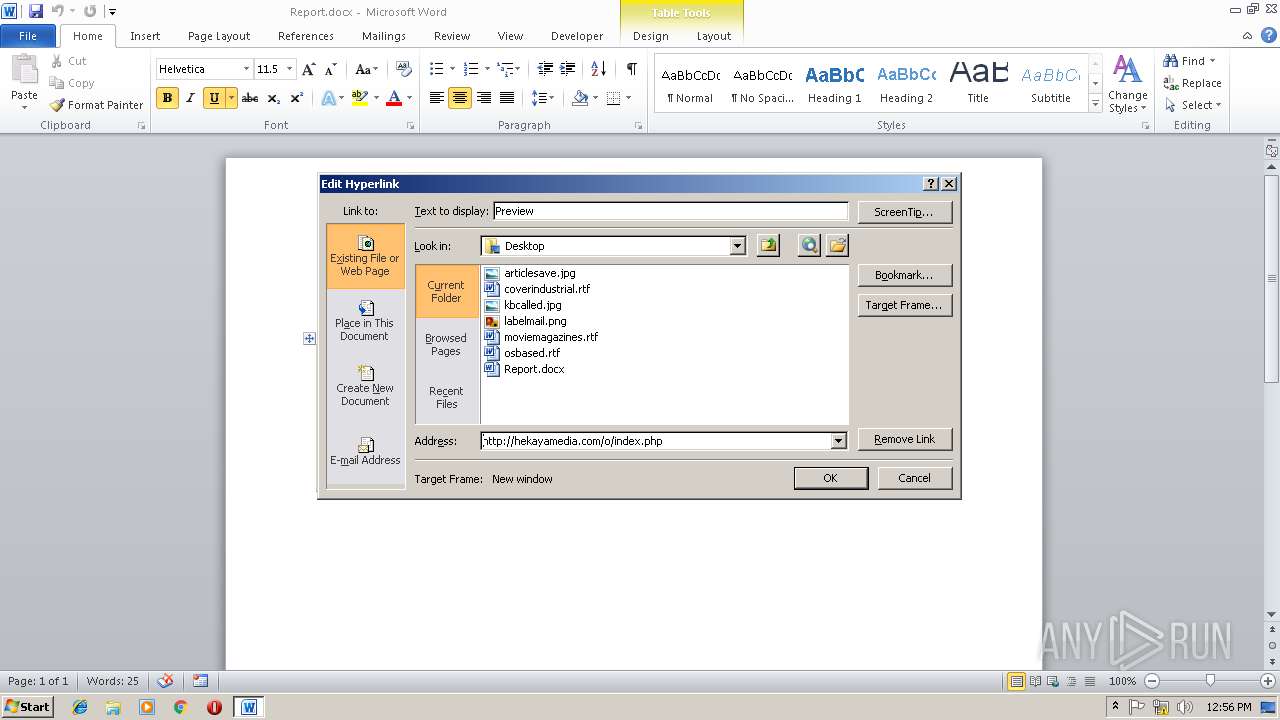
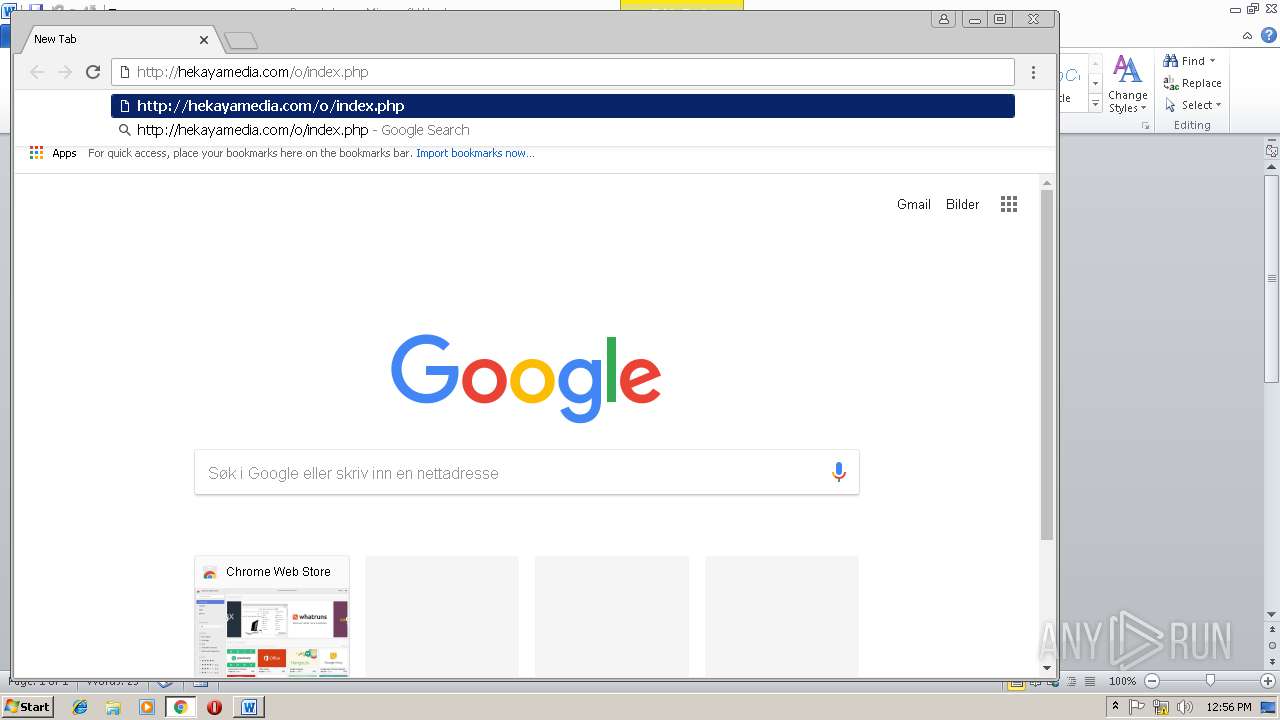
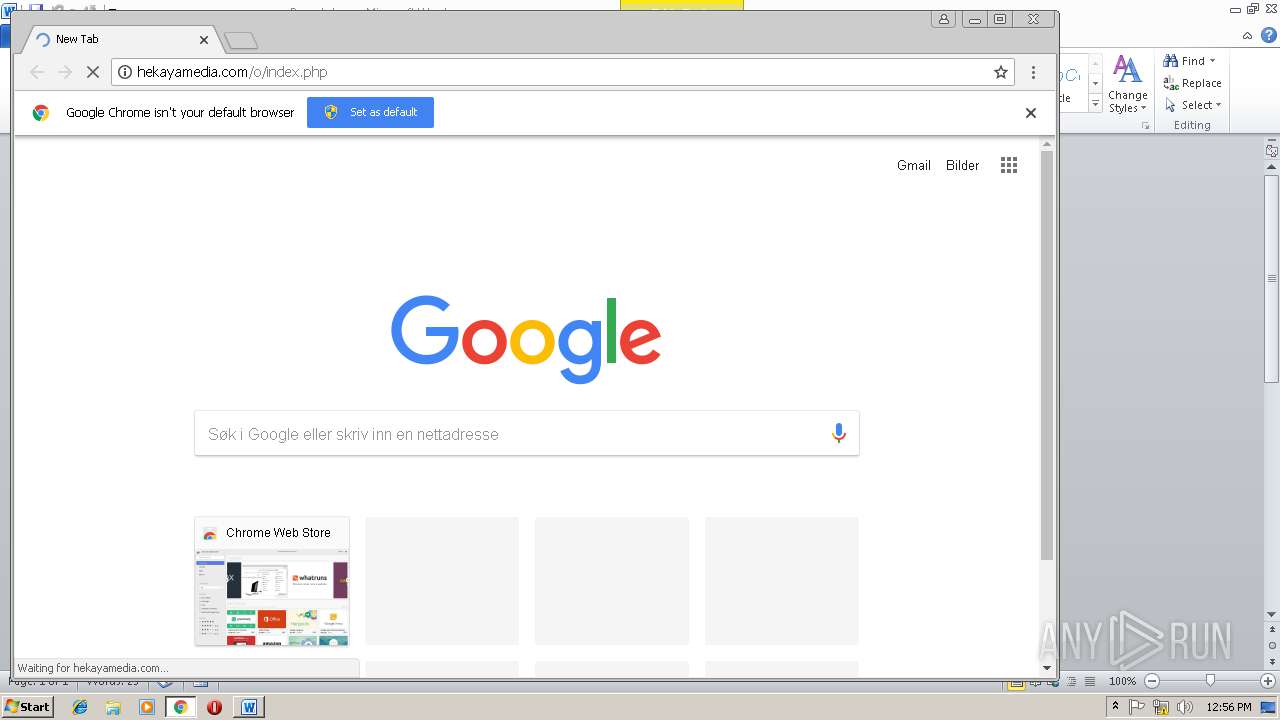
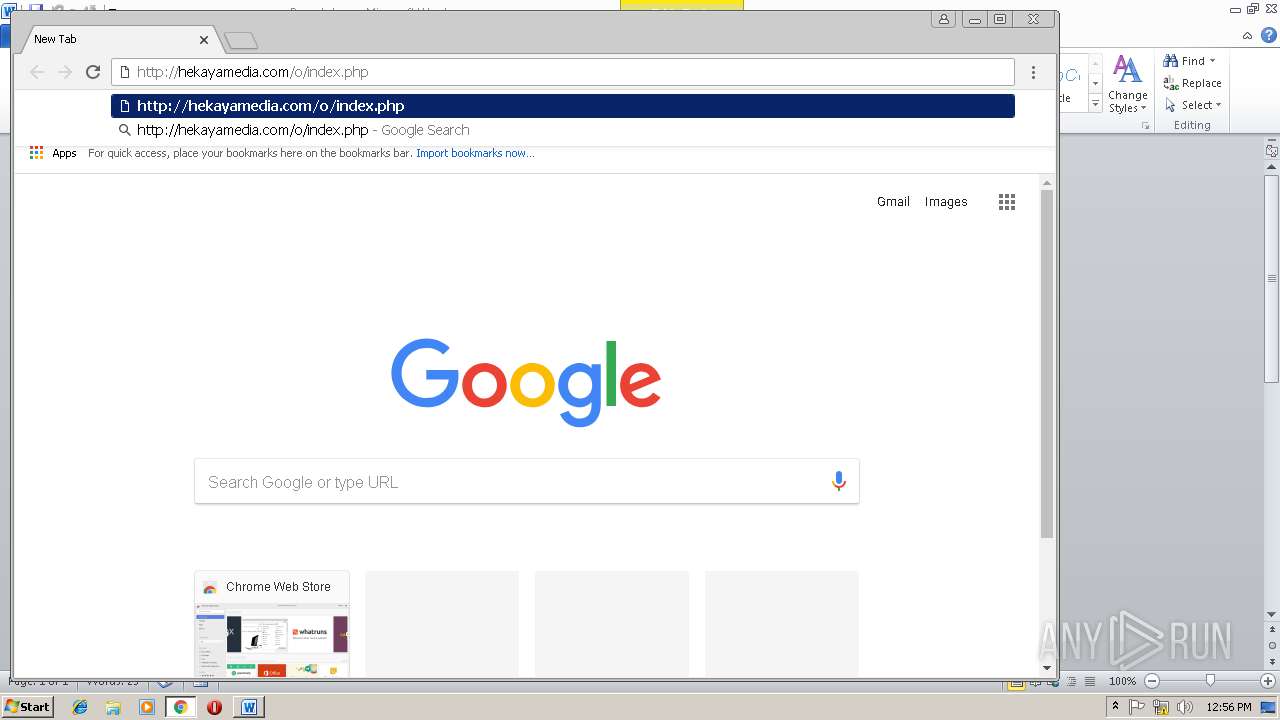
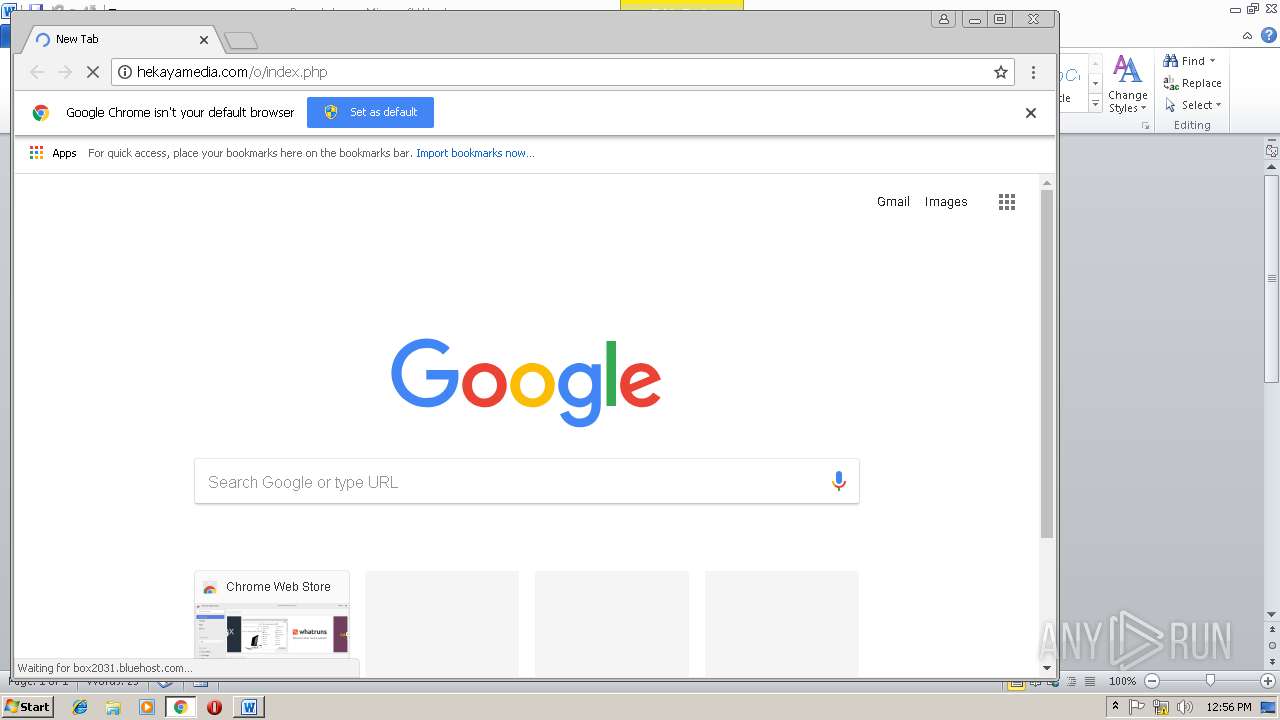
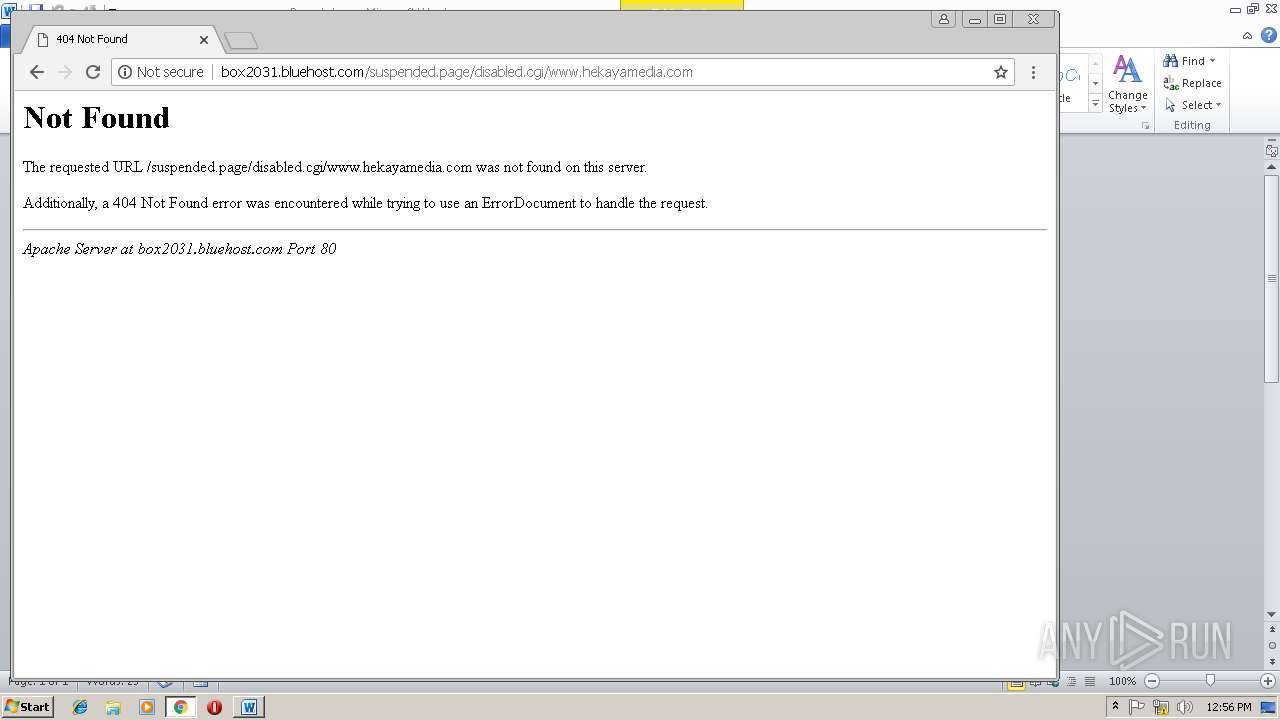
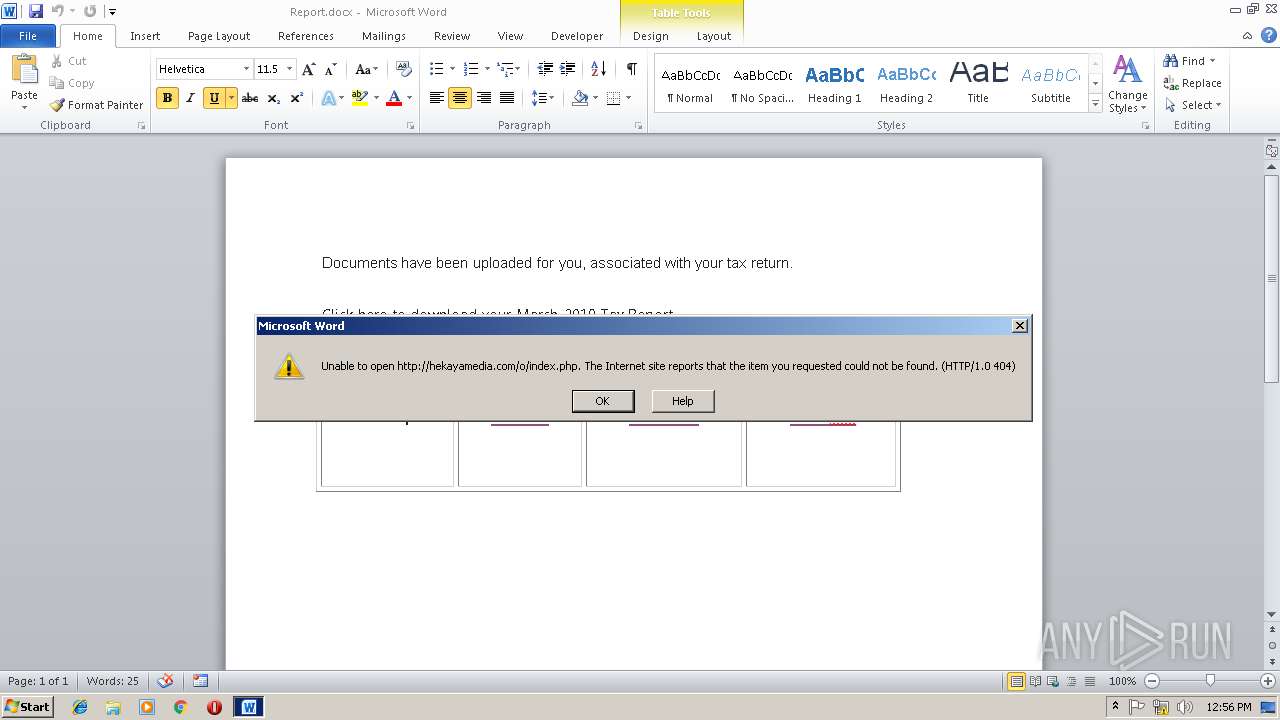
2872 | WINWORD.EXE | GET | — | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | — | — | suspicious |
2872 | WINWORD.EXE | GET | — | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | — | — | suspicious |
2872 | WINWORD.EXE | GET | — | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | — | — | suspicious |
2872 | WINWORD.EXE | GET | — | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | — | — | suspicious |
3732 | chrome.exe | GET | — | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | — | — | suspicious |
3732 | chrome.exe | GET | — | 74.220.219.225:80 | http://box2031.bluehost.com/404.html | US | — | — | suspicious |
2872 | WINWORD.EXE | GET | — | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | — | — | suspicious |
2872 | WINWORD.EXE | GET | 302 | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | html | 324 b | suspicious |
2872 | WINWORD.EXE | GET | 302 | 74.220.219.225:80 | http://hekayamedia.com/o/index.php | US | html | 324 b | suspicious |
2872 | WINWORD.EXE | GET | 404 | 74.220.219.225:80 | http://box2031.bluehost.com/suspended.page/disabled.cgi/www.hekayamedia.com | US | html | 320 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3732 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2872 | WINWORD.EXE | 74.220.219.225:80 | hekayamedia.com | Unified Layer | US | suspicious |
3732 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3732 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3732 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
3732 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3732 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3732 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3732 | chrome.exe | 74.220.219.225:80 | hekayamedia.com | Unified Layer | US | suspicious |
3732 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hekayamedia.com |
| suspicious |
box2031.bluehost.com |
| suspicious |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients4.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |