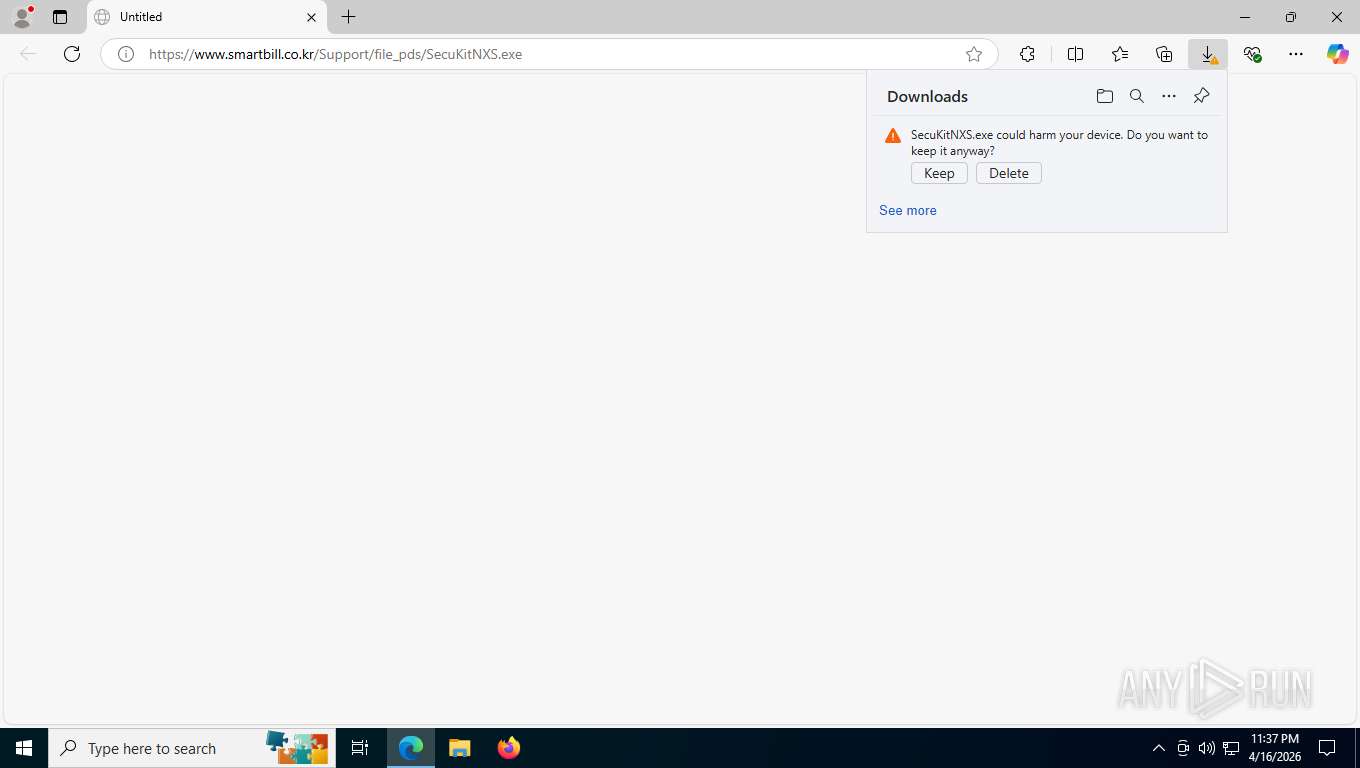
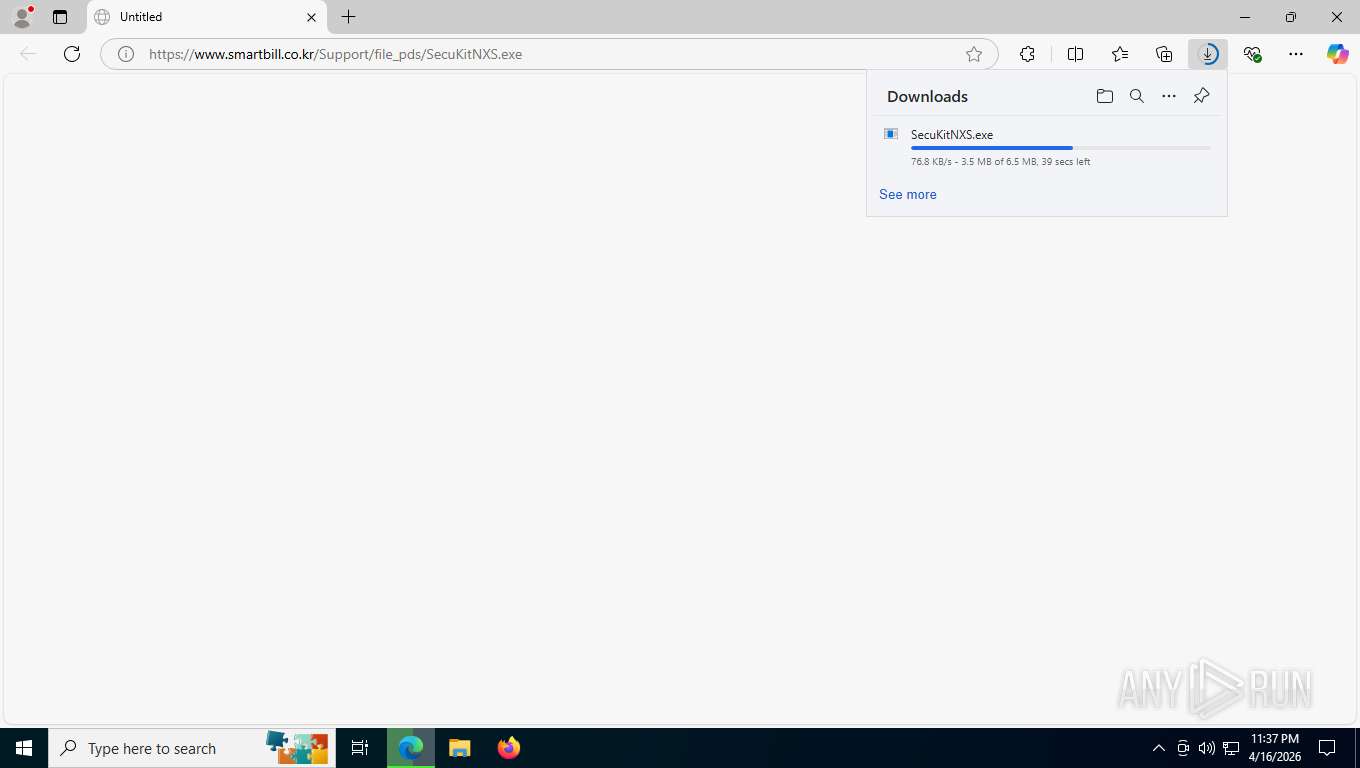
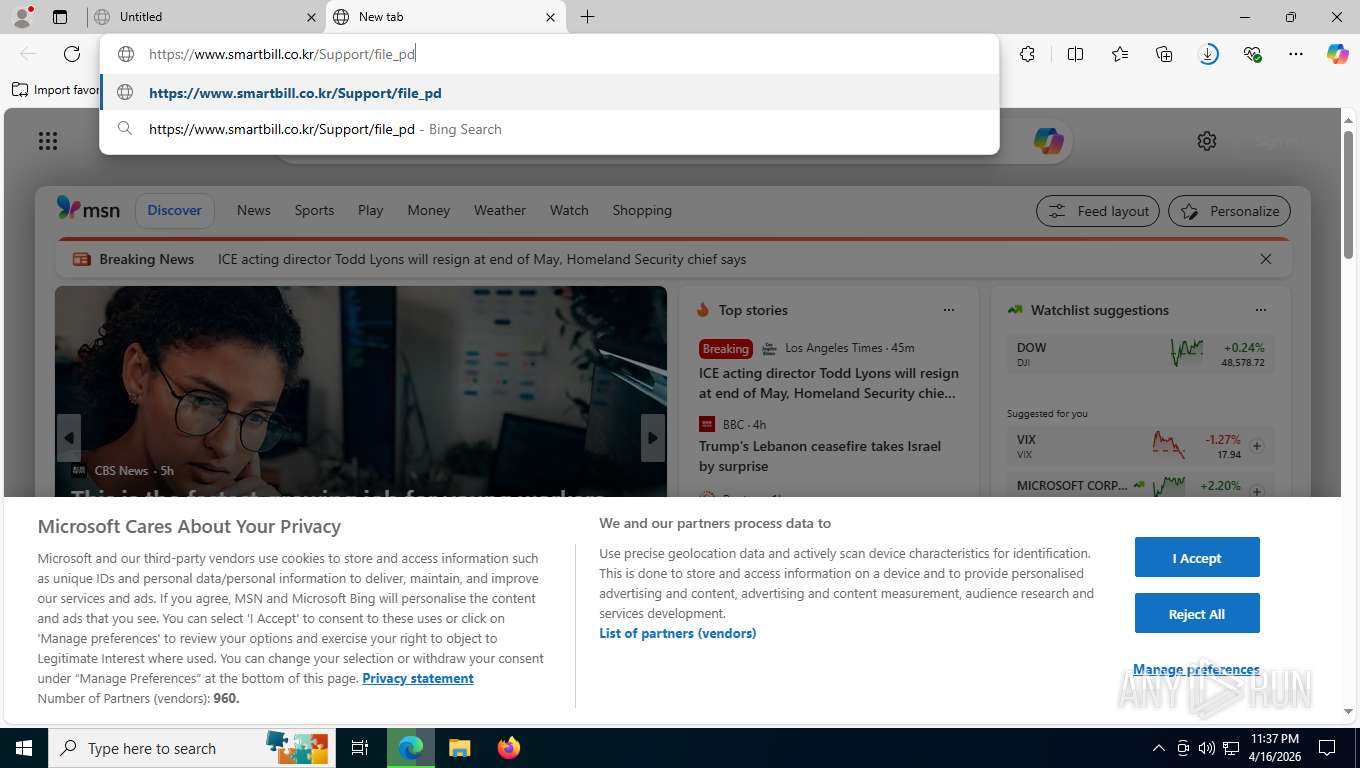
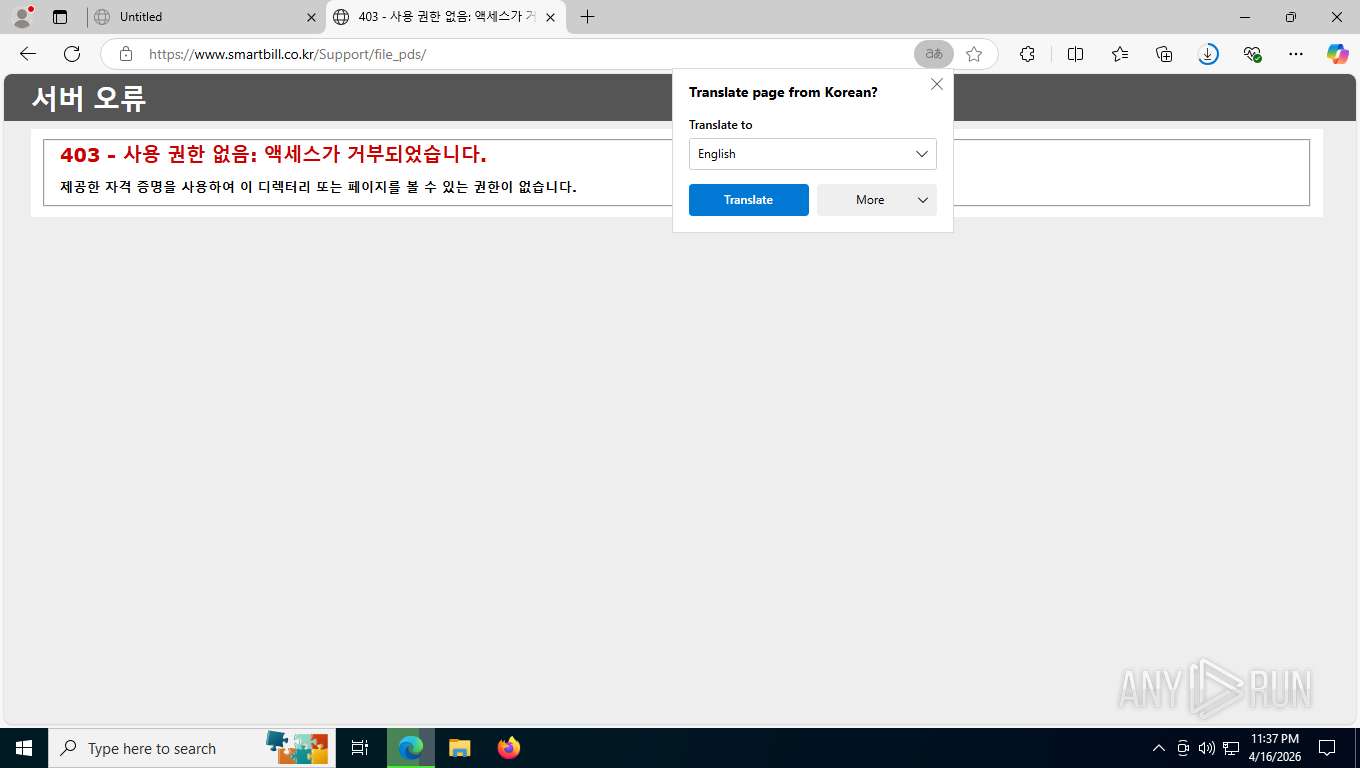
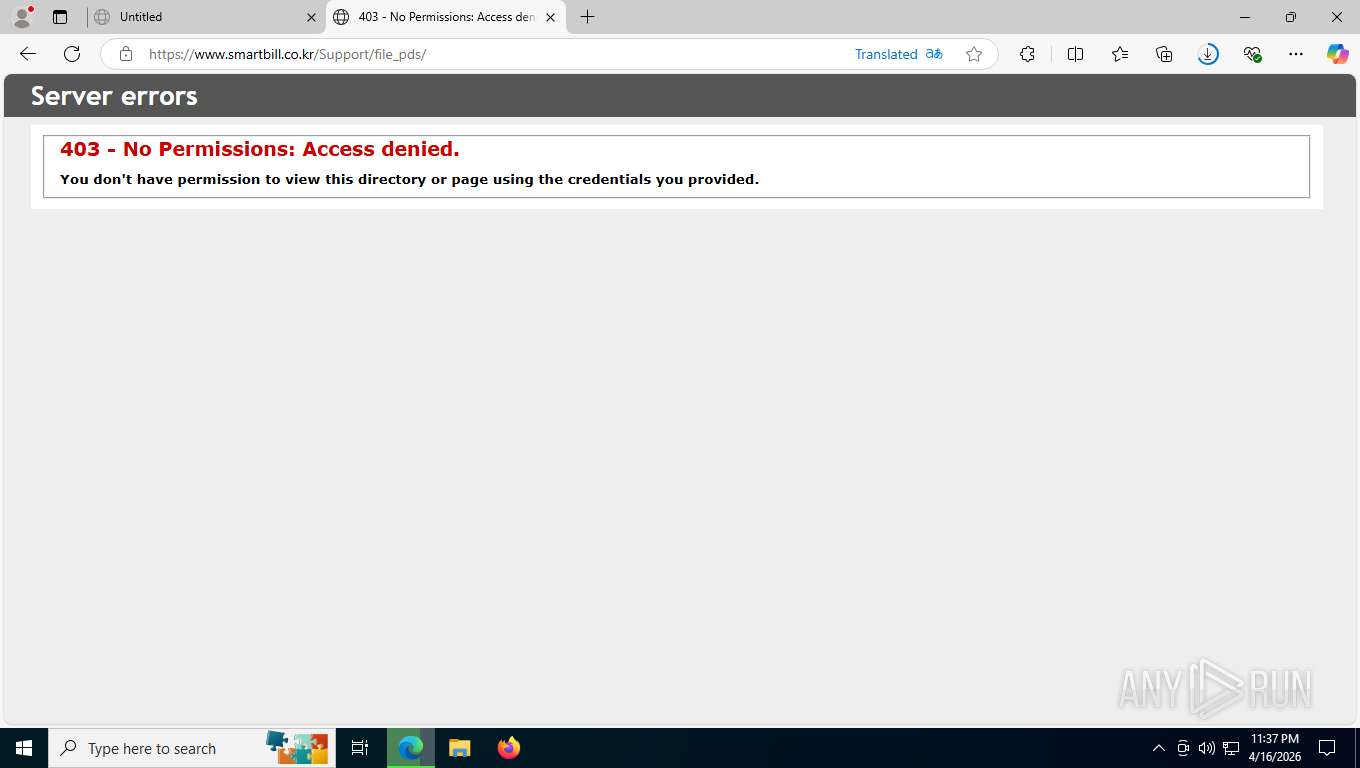
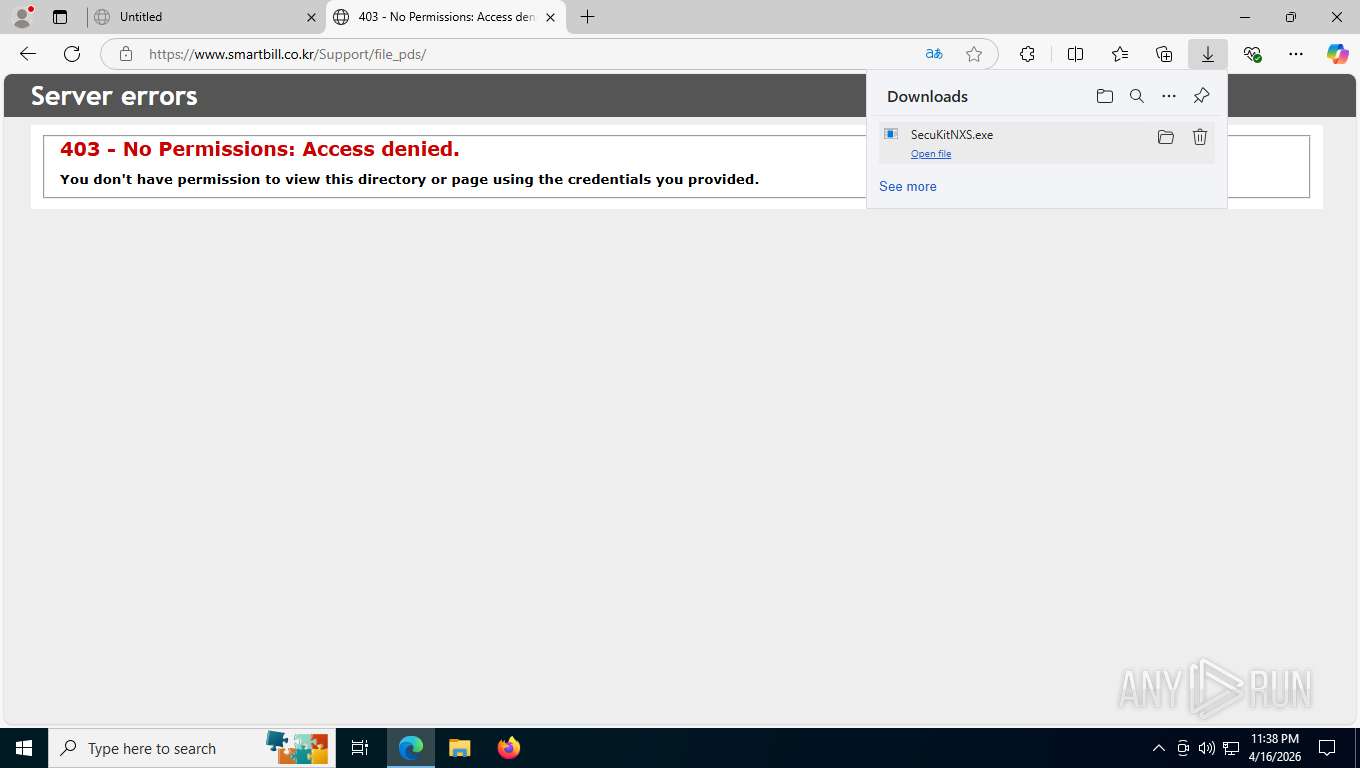
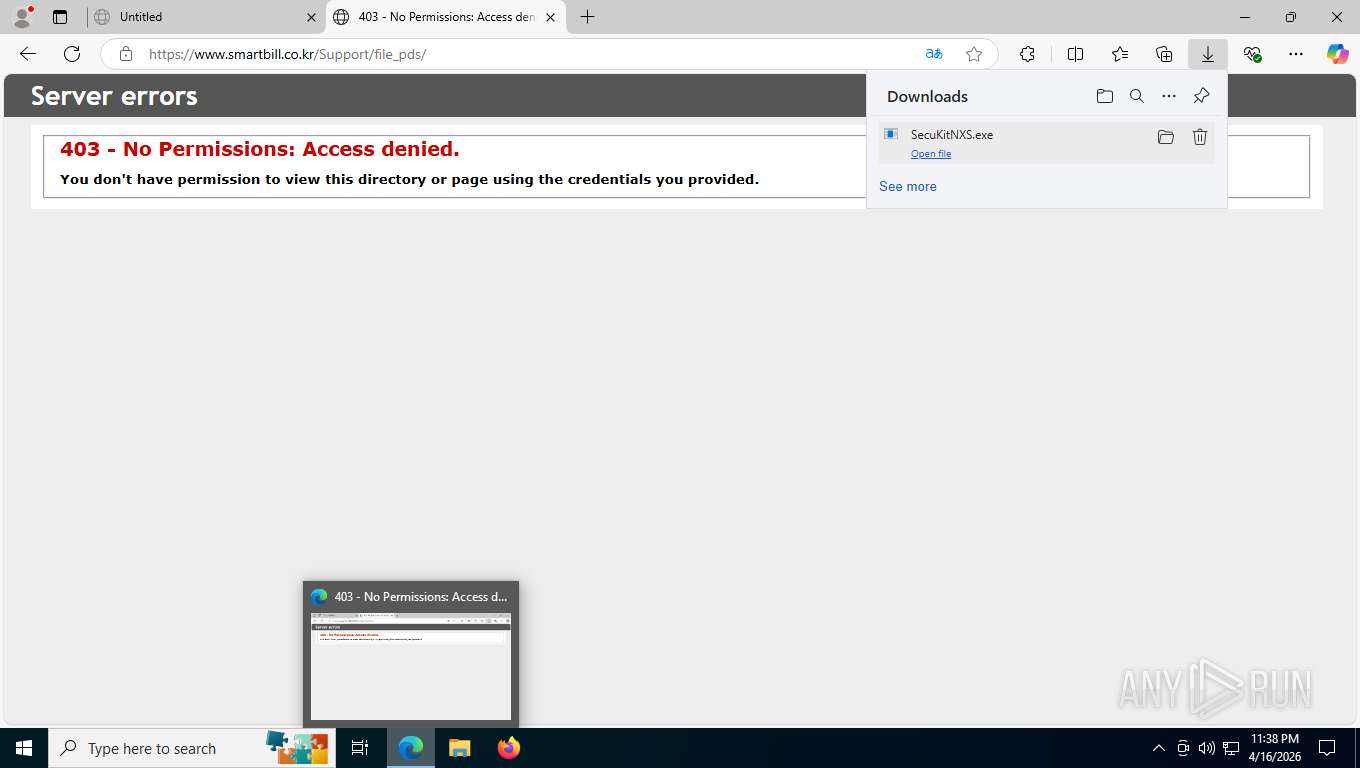
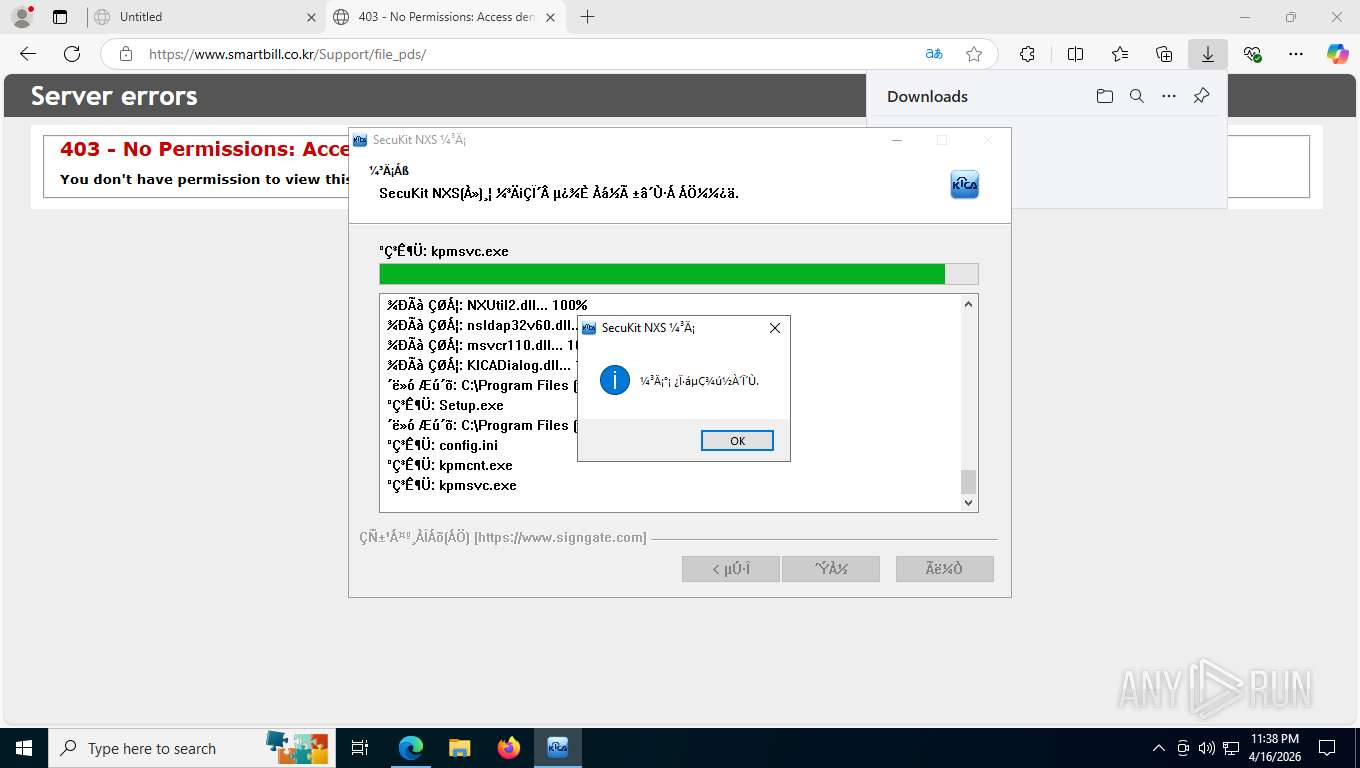
| URL: | https://www.smartbill.co.kr/Support/file_pds/SecuKitNXS.exe |
| Full analysis: | https://app.any.run/tasks/40b10fde-a37c-4eb8-9595-73577df06d18 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2026, 03:36:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 34818E16FCF8218AE1CD6C21F2863226 |
| SHA1: | 6401EACAB41CC2A873DE9A8C393A7A82D4EE47CE |
| SHA256: | 545178235848DCDA1850E5BA868D00EF85E1A0C7C4C2A8B90F846C1C507F6816 |
| SSDEEP: | 3:N8DSLszKlg8cA+eQj0:2OLsig2+e/ |
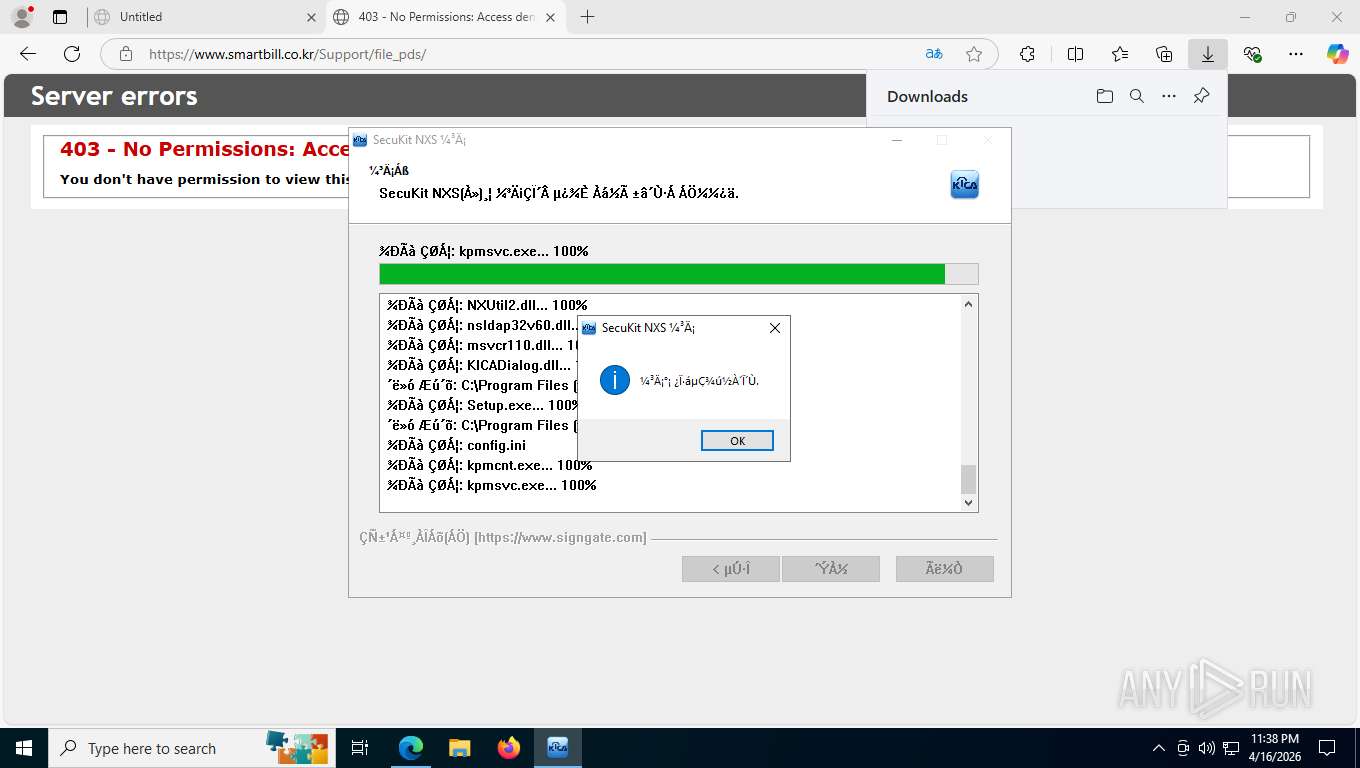
MALICIOUS
Changes settings of System certificates
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Changes the autorun value in the registry
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
The process creates files with name similar to system file names
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Executable content was dropped or overwritten
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
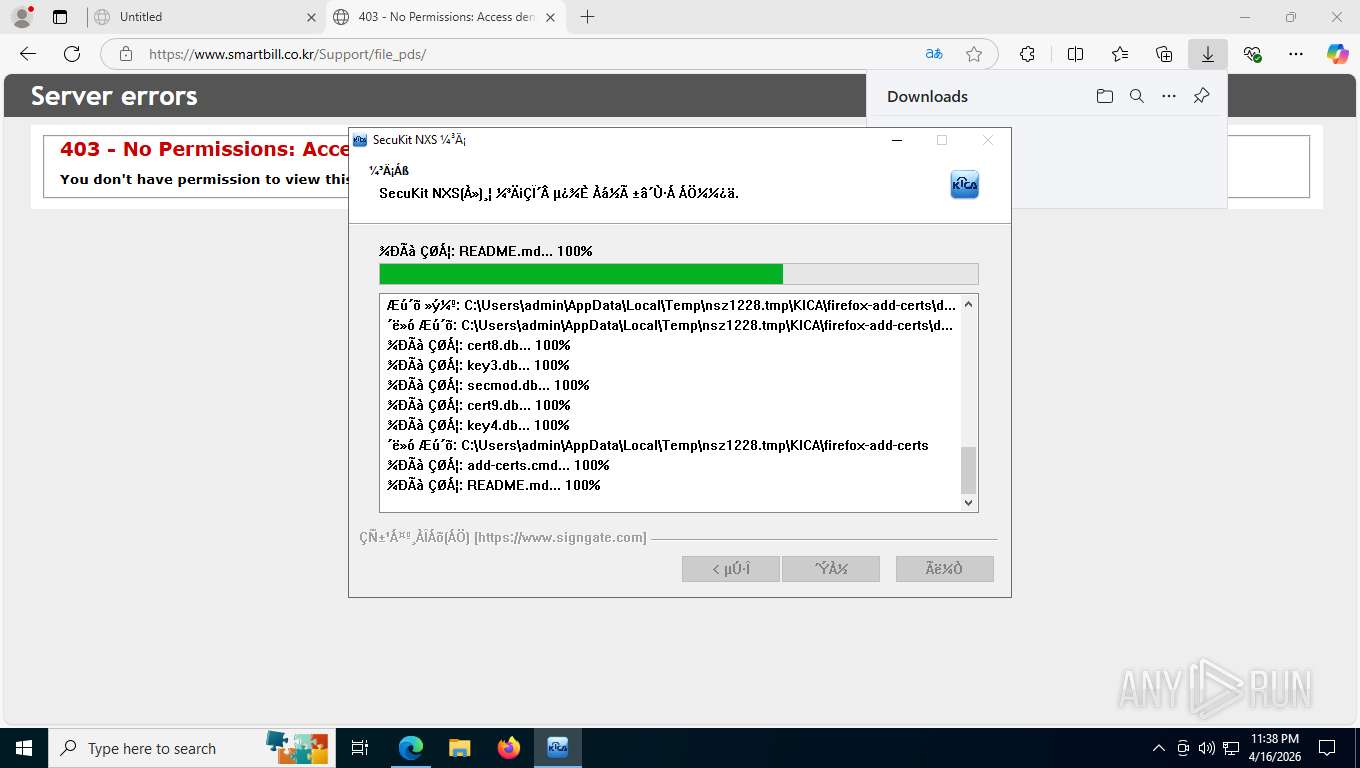
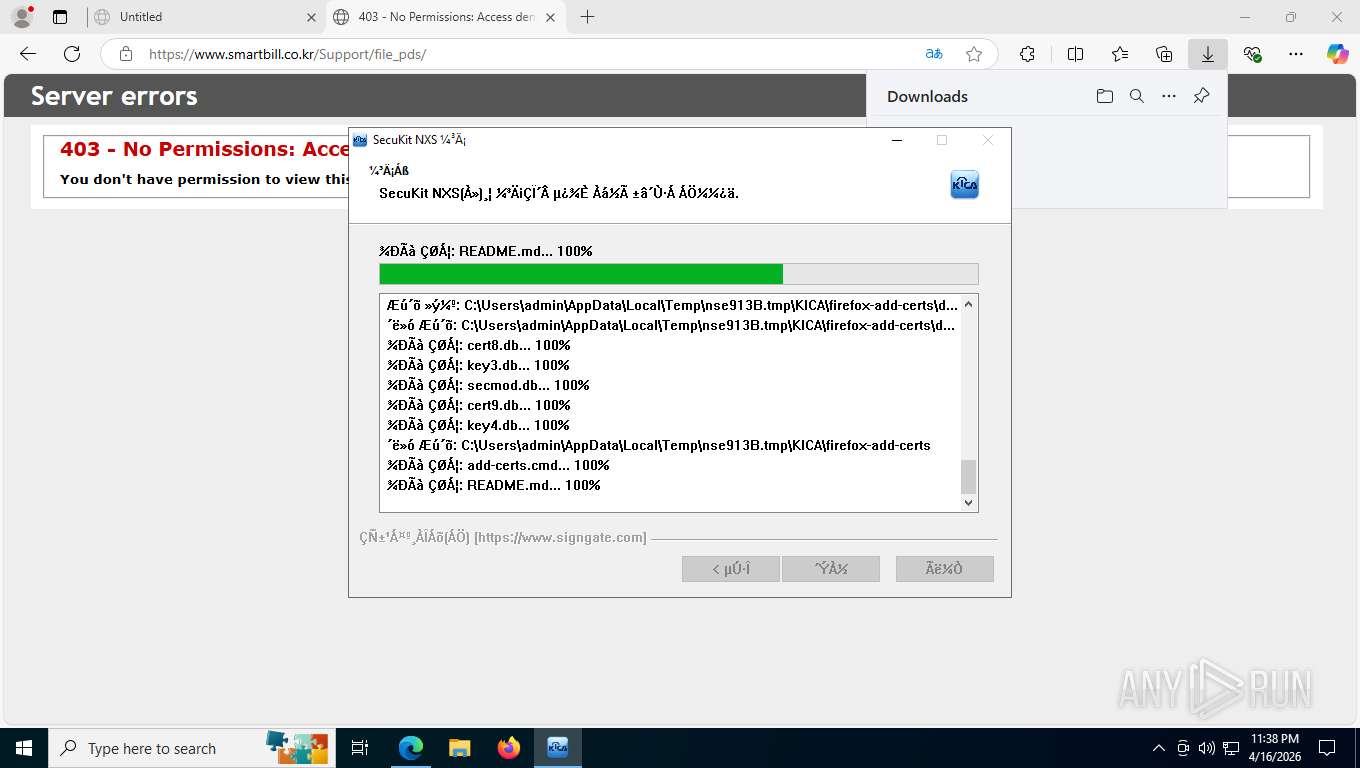
Executing commands from ".cmd" file
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7872)
- cmd.exe (PID: 3324)
The executable file from the user directory is run by the CMD process
- certutil.exe (PID: 6092)
- certutil.exe (PID: 5160)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 684)
- certutil.exe (PID: 6148)
- certutil.exe (PID: 8296)
- certutil.exe (PID: 8392)
- certutil.exe (PID: 7752)
- certutil.exe (PID: 8376)
- certutil.exe (PID: 6816)
- certutil.exe (PID: 7532)
- certutil.exe (PID: 8928)
- certutil.exe (PID: 8804)
- certutil.exe (PID: 8772)
- certutil.exe (PID: 6064)
- certutil.exe (PID: 8612)
- certutil.exe (PID: 8832)
- certutil.exe (PID: 7460)
- certutil.exe (PID: 8860)
- certutil.exe (PID: 2936)
The process executes files with name similar to system file names
- cmd.exe (PID: 7872)
- cmd.exe (PID: 3324)
Adds/modifies Windows certificates
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
The process drops C-runtime libraries
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
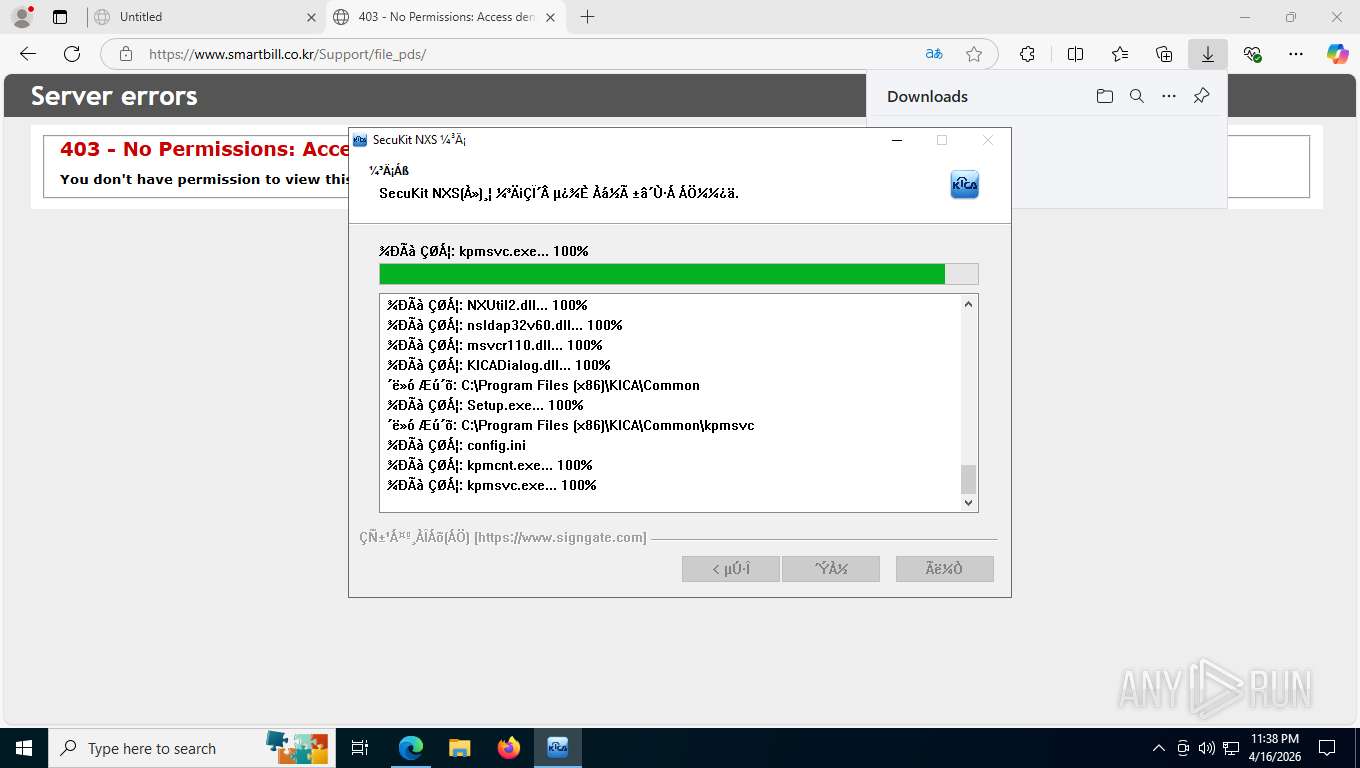
Executes as Windows Service
- kpmsvc.exe (PID: 5852)
- kpmsvc.exe (PID: 4960)
INFO
Application launched itself
- msedge.exe (PID: 7484)
Reads the computer name
- identity_helper.exe (PID: 7924)
- SecuKitNXS.exe (PID: 7404)
- certutil.exe (PID: 5160)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 684)
- certutil.exe (PID: 6148)
- certutil.exe (PID: 8296)
- certutil.exe (PID: 6092)
- certutil.exe (PID: 6816)
- certutil.exe (PID: 7752)
- certutil.exe (PID: 8392)
- certutil.exe (PID: 8376)
- kpmsvc.exe (PID: 5852)
- kpmcnt.exe (PID: 7620)
- SecuKitNXS.exe (PID: 2312)
- certutil.exe (PID: 7532)
- certutil.exe (PID: 8928)
- certutil.exe (PID: 8804)
- certutil.exe (PID: 8772)
- certutil.exe (PID: 6064)
- certutil.exe (PID: 8612)
- certutil.exe (PID: 8832)
- certutil.exe (PID: 7460)
- certutil.exe (PID: 8860)
- certutil.exe (PID: 2936)
- kpmcnt.exe (PID: 3164)
- kpmsvc.exe (PID: 4960)
Executable content was dropped or overwritten
- msedge.exe (PID: 7484)
- msedge.exe (PID: 4304)
Checks supported languages
- SecuKitNXS.exe (PID: 7404)
- identity_helper.exe (PID: 7924)
- certutil.exe (PID: 6092)
- certutil.exe (PID: 5160)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 8296)
- certutil.exe (PID: 684)
- certutil.exe (PID: 6148)
- certutil.exe (PID: 6816)
- certutil.exe (PID: 7752)
- certutil.exe (PID: 8392)
- certutil.exe (PID: 8376)
- kpmcnt.exe (PID: 7600)
- SecuKitNXS.exe (PID: 2312)
- kpmsvc.exe (PID: 5852)
- kpmcnt.exe (PID: 7620)
- certutil.exe (PID: 7532)
- certutil.exe (PID: 8928)
- certutil.exe (PID: 8804)
- certutil.exe (PID: 6064)
- certutil.exe (PID: 8772)
- certutil.exe (PID: 8612)
- certutil.exe (PID: 8832)
- certutil.exe (PID: 8860)
- certutil.exe (PID: 2936)
- kpmcnt.exe (PID: 3164)
- certutil.exe (PID: 7460)
- kpmsvc.exe (PID: 4960)
- kpmcnt.exe (PID: 8468)
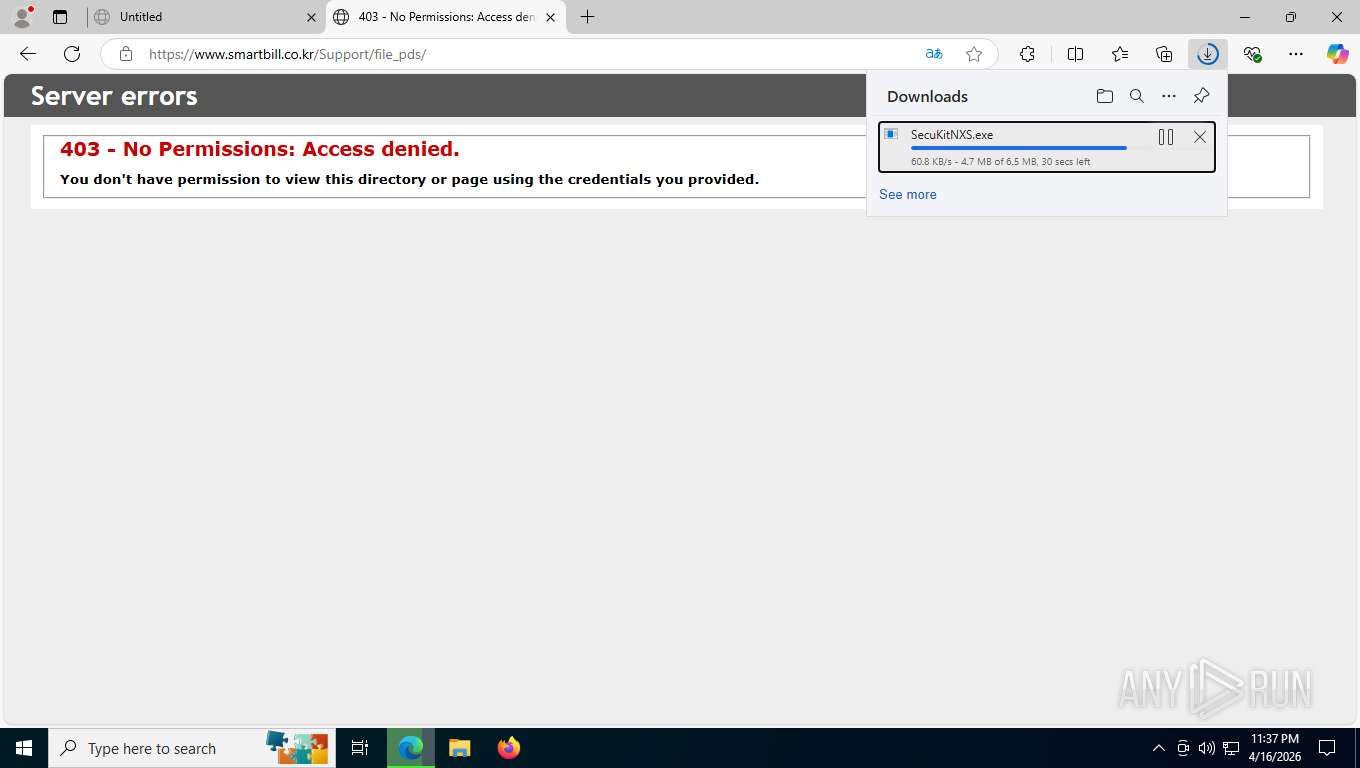
Launching a file from the Downloads directory
- msedge.exe (PID: 7484)
The sample compiled with korean language support
- msedge.exe (PID: 7484)
- msedge.exe (PID: 4304)
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Reads Environment values
- identity_helper.exe (PID: 7924)
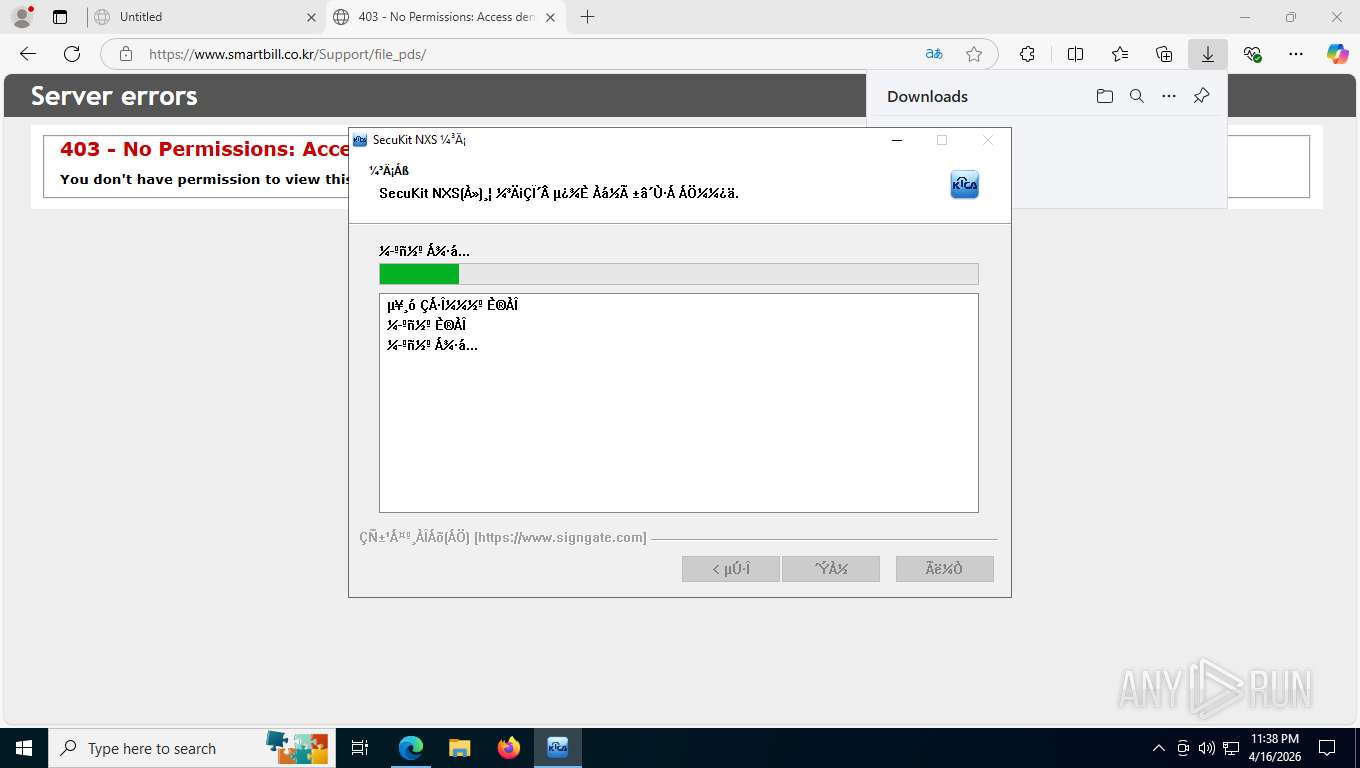
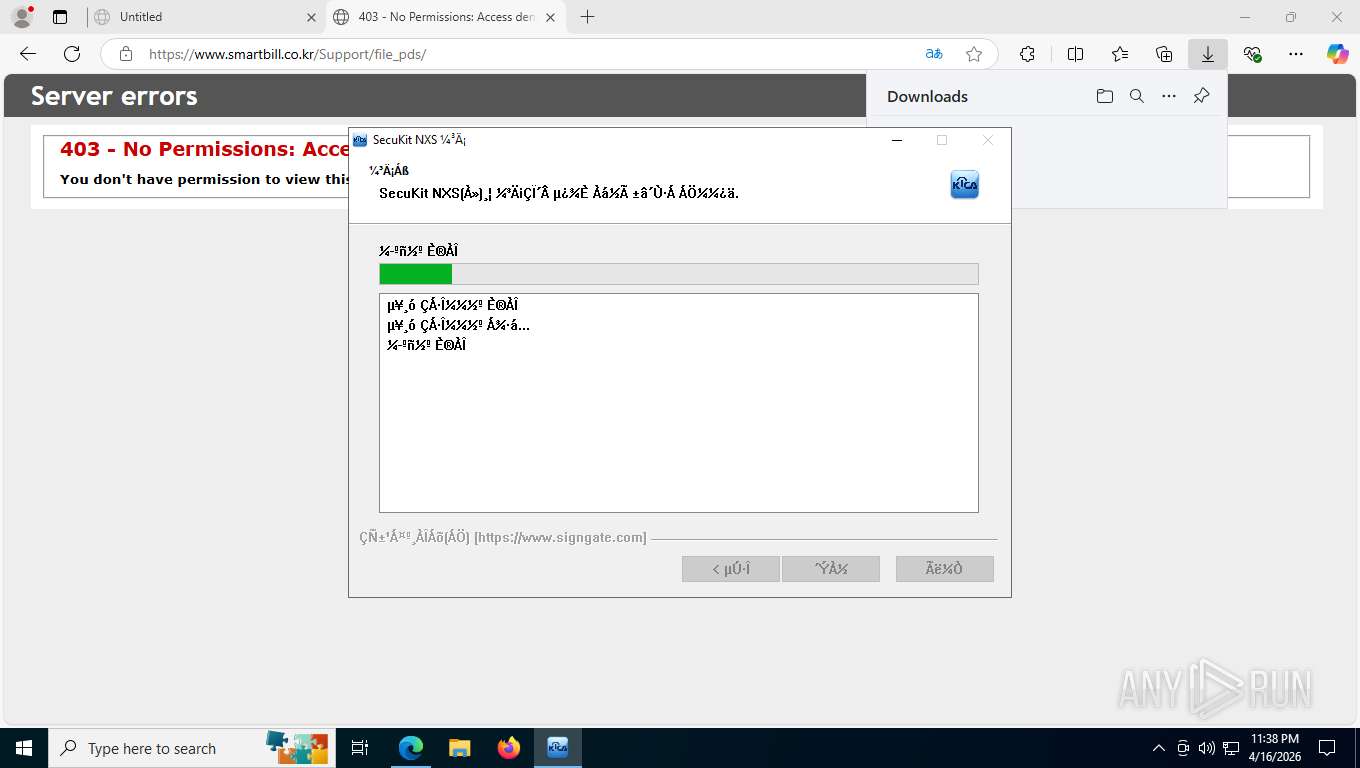
Create files in a temporary directory
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
The sample compiled with english language support
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Creates files or folders in the user directory
- certutil.exe (PID: 6148)
- certutil.exe (PID: 1296)
- certutil.exe (PID: 6816)
- certutil.exe (PID: 8392)
- certutil.exe (PID: 8804)
- certutil.exe (PID: 6064)
- certutil.exe (PID: 8832)
- certutil.exe (PID: 2936)
Reads the machine GUID from the registry
- kpmcnt.exe (PID: 7620)
- kpmcnt.exe (PID: 3164)
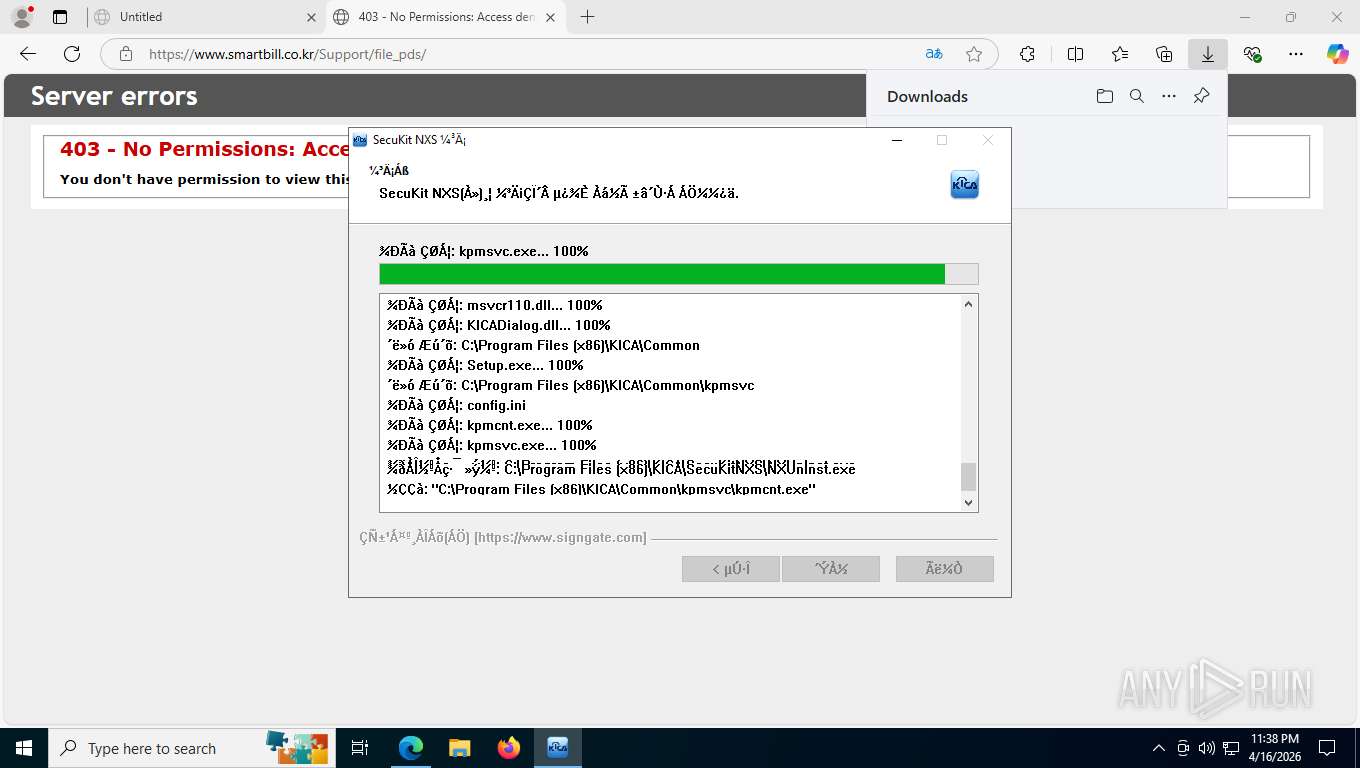
Launching a file from a Registry key
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Creates a software uninstall entry
- SecuKitNXS.exe (PID: 7404)
- SecuKitNXS.exe (PID: 2312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
69
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Users\admin\AppData\Local\Temp\nsz1228.tmp\KICA\firefox-add-certs\bin\certutil.exe" -A -n "AddedByUser RootCA" -i "C:\Users\admin\AppData\Local\Temp\nsz1228.tmp\KICA\firefox-add-certs\cacert\RootCA.pem" -t "cTC,cTC,cTC", -d "dbm:C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\i17fj4h8.default" | C:\Users\admin\AppData\Local\Temp\nsz1228.tmp\KICA\firefox-add-certs\bin\certutil.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Local\Temp\nsz1228.tmp\KICA\firefox-add-certs\bin\certutil.exe" -A -n "AddedByUser RootCA" -i "C:\Users\admin\AppData\Local\Temp\nsz1228.tmp\KICA\firefox-add-certs\cacert\RootCA.pem" -t "cTC,cTC,cTC", -d "sql:C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release" | C:\Users\admin\AppData\Local\Temp\nsz1228.tmp\KICA\firefox-add-certs\bin\certutil.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
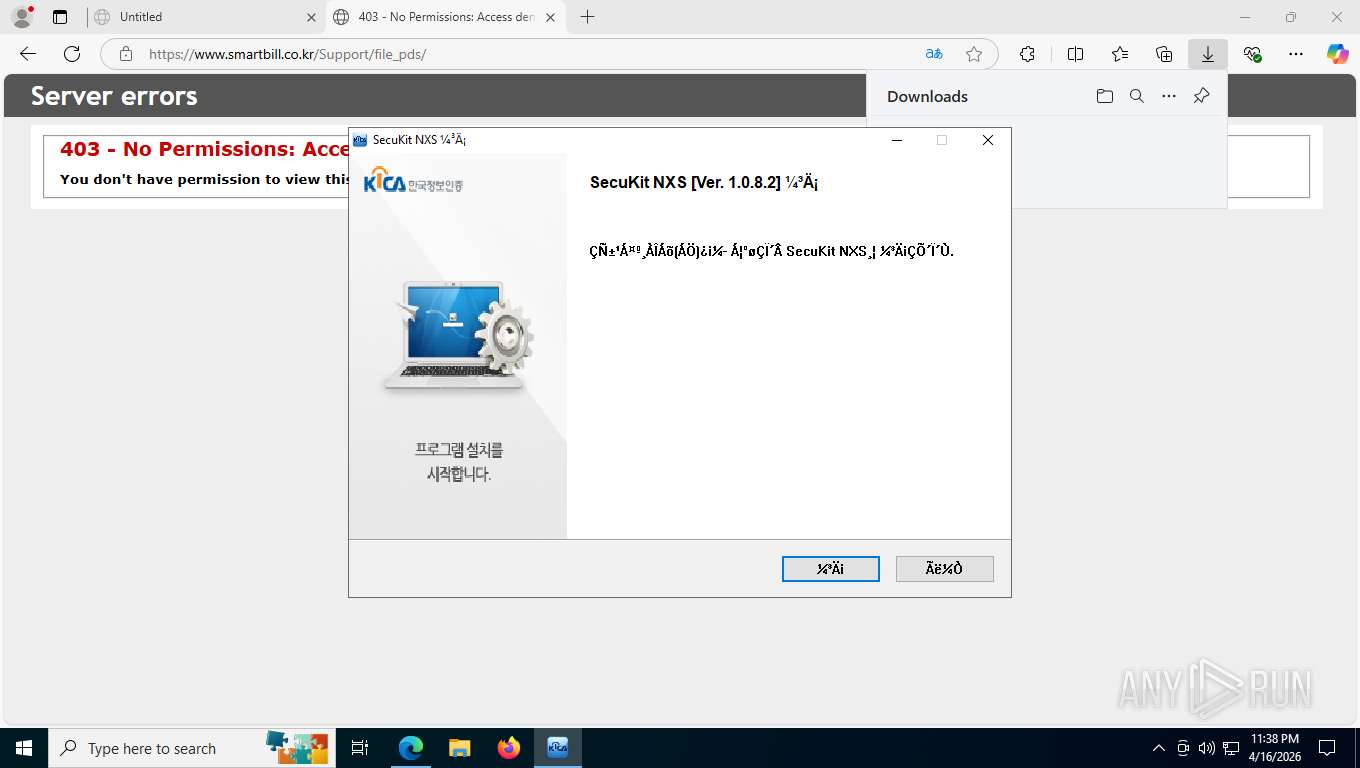
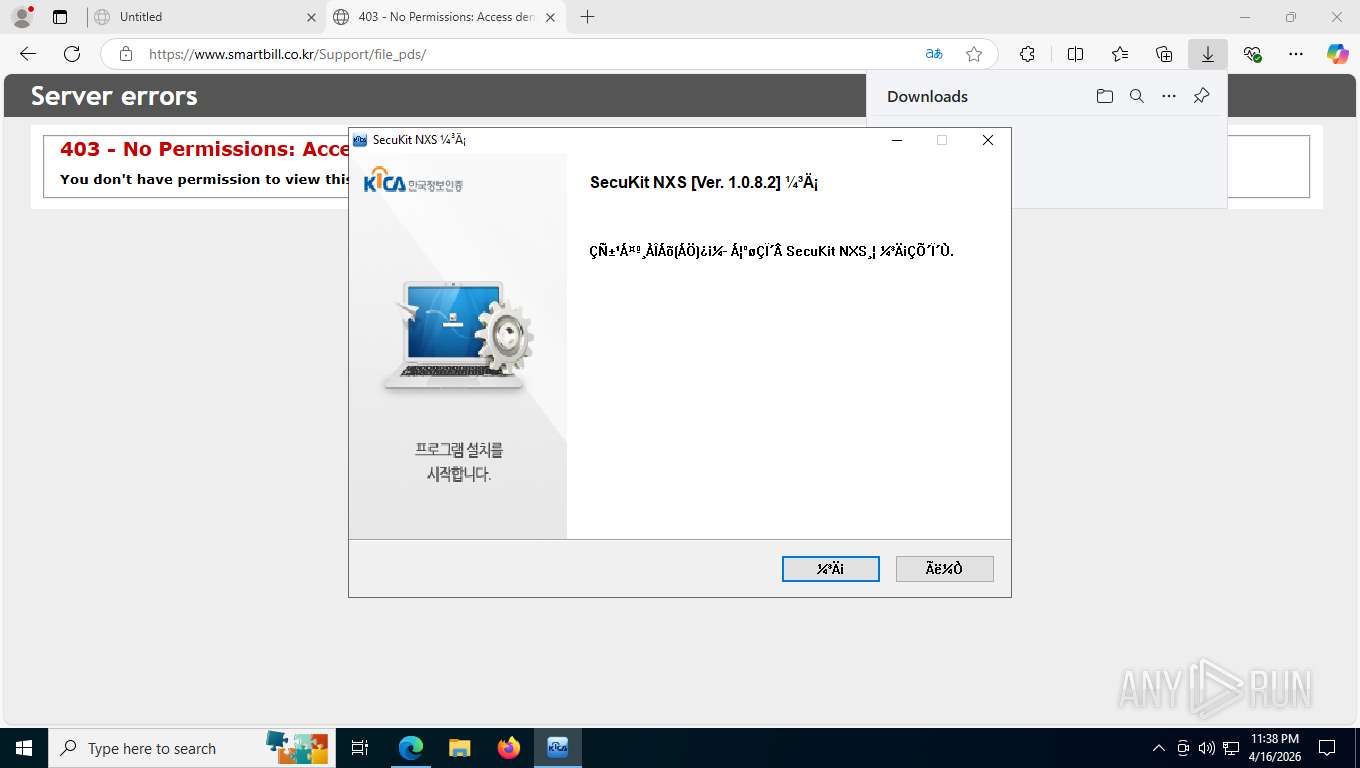
| 2312 | "C:\Users\admin\Downloads\SecuKitNXS.exe" | C:\Users\admin\Downloads\SecuKitNXS.exe | msedge.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SecuKit NXS Setup Exit code: 0 Version: 1.0.8.2 Modules
| |||||||||||||||
| 2324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=5904,i,13701300575910149282,1960042081626496397,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6172 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6776,i,13701300575910149282,1960042081626496397,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6804 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6436,i,13701300575910149282,1960042081626496397,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6468 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2724 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6100,i,13701300575910149282,1960042081626496397,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6136 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\AppData\Local\Temp\nse913B.tmp\KICA\firefox-add-certs\bin\certutil.exe" -A -n "AddedByUser RootCA" -i "C:\Users\admin\AppData\Local\Temp\nse913B.tmp\KICA\firefox-add-certs\cacert\RootCA.pem" -t "cTC,cTC,cTC", -d "sql:C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\i17fj4h8.default" | C:\Users\admin\AppData\Local\Temp\nse913B.tmp\KICA\firefox-add-certs\bin\certutil.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2996 | findstr /i "AddedByUser RootCA" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3164 | "C:\Program Files (x86)\KICA\Common\kpmsvc\kpmcnt.exe" | C:\Program Files (x86)\KICA\Common\kpmsvc\kpmcnt.exe | — | kpmsvc.exe | |||||||||||
User: admin Company: KICA Inc. Integrity Level: HIGH Description: KICA Process Manager Service Version: 1.1.5.11 Modules
| |||||||||||||||
Total events
7 180
Read events
7 164
Write events
14
Delete events
2
Modification events
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 68C232D21D4B44F3403B0A5F8C92ED88E32804D3 |
Value: | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\68C232D21D4B44F3403B0A5F8C92ED88E32804D3 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000068C232D21D4B44F3403B0A5F8C92ED88E32804D320000000010000004C0300003082034830820230A003020102020101300D06092A864886F70D01010B0500303C310B3009060355040613024B5231123010060355040A0C094B49434120496E632E3119301706035504030C104B494341204E585320526F6F74204341301E170D3136303732363036313135335A170D3336303732313036313135335A303C310B3009060355040613024B5231123010060355040A0C094B49434120496E632E3119301706035504030C104B494341204E585320526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100A34806795010E27E7E86CD41442711DC7082903DC0044D50409FA2DF2817FECB6823A030BD731186D5B2947BEAB7555C416E92A36CD3166EDF736ACB5E252F8C0C047223A2C5418542C52E6F329CCB4CFD0B93C49EA20D8DFEB19ADB3415986055E5DED62D761A6C0952C7FD789A8B7902294431682569BE77C2F5FF63BC301B5AD1B8FEF7834A5002FFD65888283F7B92A4DFEAD5F352A5CE9AC7FFB02AA4BB677943CF671A65816194E8967FA2FB94D56A955A96B34976692E9FD20550D3DD40773FFE12F23203C20E21CFE6A3FE7F2CB56C63DE3C5C59FF56A8983DCF699CFA276134F984E8985B374196FB79BDFAAFFCB750F02C93316D23F4FC93AC20230203010001A355305330120603551D130101FF040830060101FF020100301D0603551D0E04160414048CC68BC2DC763BE33BEA388FE64DFA25E9F8AE300B0603551D0F040403020106301106096086480186F8420101040403020007300D06092A864886F70D01010B050003820101006BCD1E8F7F980AEC3E8F8E42A8D9D989541BF7A144AACB9A54E5AA0B47A93BBFC005C9ED2C33195423B1489C9E56F876E4D436B13D3E89C3A5E4D629D0DF811481190783F5F43B74A062B89B23F4E98D16DEA176F3256CBDDB823F9F624764564FF7395BCD63D7223E280370135D0C4F95C2878FD1D45F7D8D94AB756F3D435D50615D2EB63D937C3FDF723689F9B9B8C0642901B16EF9F77526C22204B2C034716F744DE5E3CFF84480B3CCAD619946C424A0B7E710000AE4D29518B62FAD1E0A8A75C0F17EFF723695077EE80D93F9651AC79865885931DA2AC2CCE6B42404B260FB6DE6CD790A812F676AC6AD6A07849E9EDC46E9448F0215797A74371197 | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SecuKit NXS |
| Operation: | write | Name: | DisplayName |
Value: SecuKit NXS | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SecuKit NXS |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\KICA\SecuKitNXS\NXUnInst.exe | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SecuKit NXS |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0.8.2 | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SecuKit NXS |
| Operation: | write | Name: | URLInfoAbout |
Value: https://www.signgate.com | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\SecuKit NXS |
| Operation: | write | Name: | Publisher |
Value: Çѱ¹Á¤º¸ÀÎÁõ(ÁÖ) | |||
| (PID) Process: | (7404) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | kpmcnt.exe |
Value: C:\Program Files (x86)\KICA\Common\kpmsvc\kpmcnt.exe | |||
| (PID) Process: | (2312) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 68C232D21D4B44F3403B0A5F8C92ED88E32804D3 |
Value: | |||
| (PID) Process: | (2312) SecuKitNXS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\68C232D21D4B44F3403B0A5F8C92ED88E32804D3 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000068C232D21D4B44F3403B0A5F8C92ED88E32804D320000000010000004C0300003082034830820230A003020102020101300D06092A864886F70D01010B0500303C310B3009060355040613024B5231123010060355040A0C094B49434120496E632E3119301706035504030C104B494341204E585320526F6F74204341301E170D3136303732363036313135335A170D3336303732313036313135335A303C310B3009060355040613024B5231123010060355040A0C094B49434120496E632E3119301706035504030C104B494341204E585320526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100A34806795010E27E7E86CD41442711DC7082903DC0044D50409FA2DF2817FECB6823A030BD731186D5B2947BEAB7555C416E92A36CD3166EDF736ACB5E252F8C0C047223A2C5418542C52E6F329CCB4CFD0B93C49EA20D8DFEB19ADB3415986055E5DED62D761A6C0952C7FD789A8B7902294431682569BE77C2F5FF63BC301B5AD1B8FEF7834A5002FFD65888283F7B92A4DFEAD5F352A5CE9AC7FFB02AA4BB677943CF671A65816194E8967FA2FB94D56A955A96B34976692E9FD20550D3DD40773FFE12F23203C20E21CFE6A3FE7F2CB56C63DE3C5C59FF56A8983DCF699CFA276134F984E8985B374196FB79BDFAAFFCB750F02C93316D23F4FC93AC20230203010001A355305330120603551D130101FF040830060101FF020100301D0603551D0E04160414048CC68BC2DC763BE33BEA388FE64DFA25E9F8AE300B0603551D0F040403020106301106096086480186F8420101040403020007300D06092A864886F70D01010B050003820101006BCD1E8F7F980AEC3E8F8E42A8D9D989541BF7A144AACB9A54E5AA0B47A93BBFC005C9ED2C33195423B1489C9E56F876E4D436B13D3E89C3A5E4D629D0DF811481190783F5F43B74A062B89B23F4E98D16DEA176F3256CBDDB823F9F624764564FF7395BCD63D7223E280370135D0C4F95C2878FD1D45F7D8D94AB756F3D435D50615D2EB63D937C3FDF723689F9B9B8C0642901B16EF9F77526C22204B2C034716F744DE5E3CFF84480B3CCAD619946C424A0B7E710000AE4D29518B62FAD1E0A8A75C0F17EFF723695077EE80D93F9651AC79865885931DA2AC2CCE6B42404B260FB6DE6CD790A812F676AC6AD6A07849E9EDC46E9448F0215797A74371197 | |||
Executable files
94
Suspicious files
440
Text files
371
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdff5f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdff5f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdff5f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdff6f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFdff7f.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
360
TCP/UDP connections
77
DNS requests
93
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4304 | msedge.exe | GET | 200 | 183.111.188.210:443 | https://www.smartbill.co.kr/Support/file_pds/SecuKitNXS.exe | KR | — | — | unknown |
4304 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
4304 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:txXnZTDs2E00RqChYFbpTpe1iTwTqNE0ZRAoVoqMwAk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 98 b | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
4304 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 132 b | whitelisted |
4304 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
4304 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.37 Kb | whitelisted |
4304 | msedge.exe | GET | 200 | 150.171.109.193:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
4304 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1776397026&lafgdate=0 | US | text | 43.4 Kb | whitelisted |
4304 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=domains_config_gz&version=3.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | text | 267 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7784 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 128.24.231.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 92.123.104.21:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4304 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4304 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.smartbill.co.kr |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7784 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |