| File name: | Synapse X Serial Key Generator.exe |
| Full analysis: | https://app.any.run/tasks/3d5c3dea-ec99-4193-a6f9-abcaae976744 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2020, 14:28:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 768B21C1C518AA0258EBF0C3AF5C5AAA |
| SHA1: | 81BAFF6AAE38F8103457D15313166B571623BE94 |
| SHA256: | 54490440082D4DB95180097552899A6C178D4BB90BBA15390BA668088ADF867B |
| SSDEEP: | 12288:ymkOy/IwEUvC+Q3gwUVN9WCWqsDgpbaN8rO1X3m1PYGapR7pSiha0bKqgqZ6J3N:yfOy0Uq0jiqsEpbVkXgPYFpR7of0bDgl |
MALICIOUS
Loads the Task Scheduler COM API
- schtasks.exe (PID: 4076)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3028)
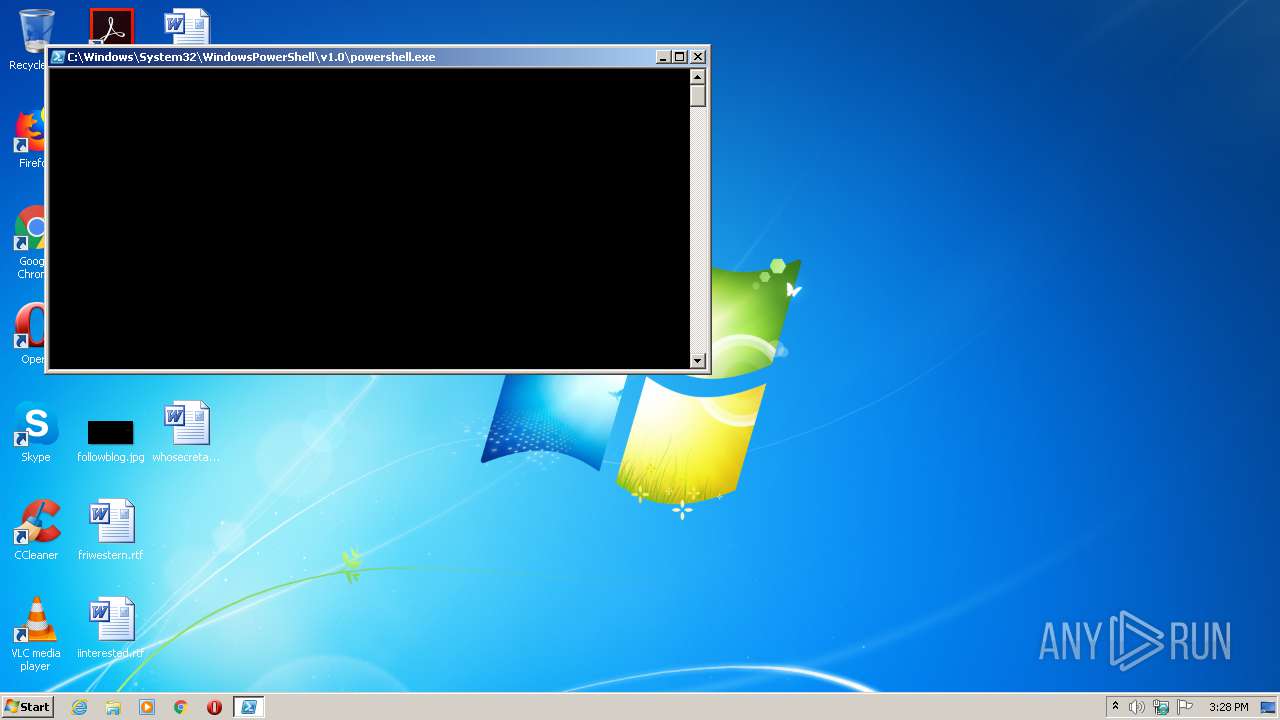
Executes PowerShell scripts
- cmd.exe (PID: 4040)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2368)
- powershell.exe (PID: 2980)
Application launched itself
- powershell.exe (PID: 2368)
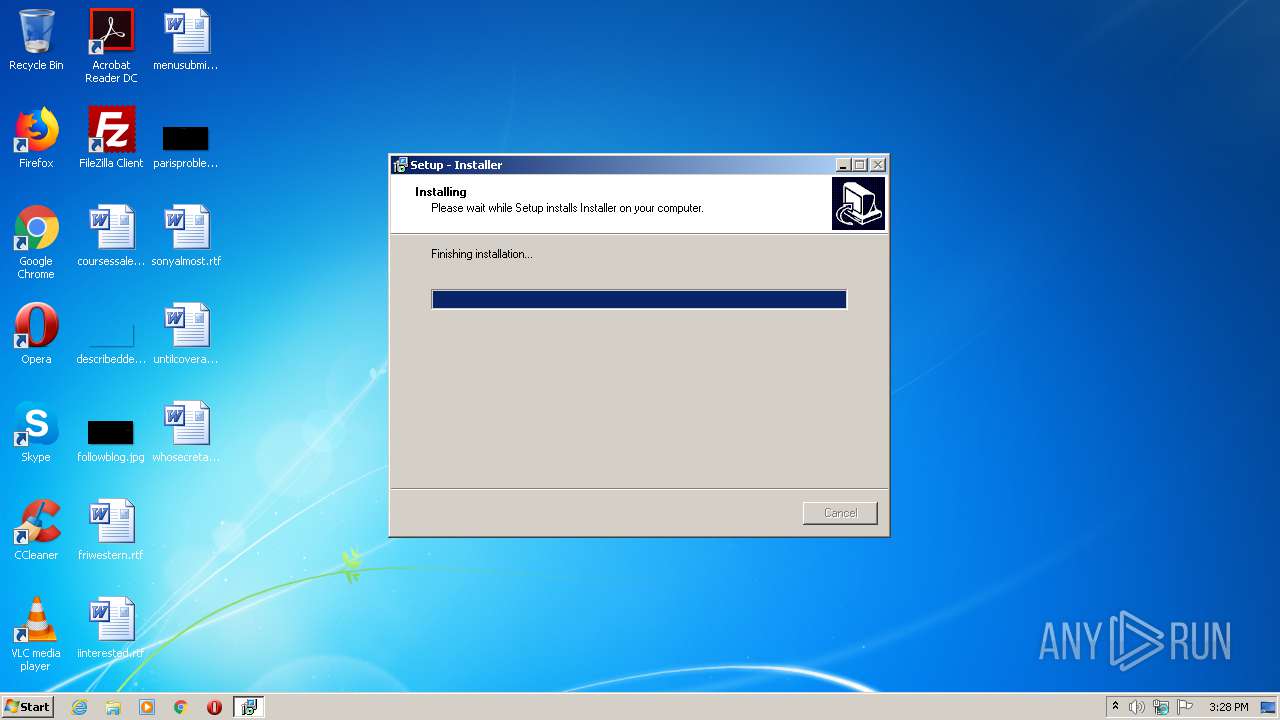
Executable content was dropped or overwritten
- Synapse X Serial Key Generator.exe (PID: 2776)
- is-RE6UV.tmp (PID: 3860)
Executes PowerShell scripts
- powershell.exe (PID: 2368)
Starts CMD.EXE for commands execution
- is-RE6UV.tmp (PID: 3860)
INFO
Creates files in the program directory
- is-RE6UV.tmp (PID: 3860)
Application was dropped or rewritten from another process
- is-RE6UV.tmp (PID: 3860)
Loads dropped or rewritten executable
- is-RE6UV.tmp (PID: 3860)
Creates a software uninstall entry
- is-RE6UV.tmp (PID: 3860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable PowerBASIC/Win 9.x (51.2) |
|---|---|---|
| .exe | | | Inno Setup installer (37.9) |
| .exe | | | Win32 Executable Delphi generic (4.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 36864 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x98d8 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CompanyName: | |
| FileDescription: | Installer Setup |
| FileVersion: | |
| LegalCopyright: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CompanyName: | - |
| FileDescription: | Installer Setup |
| FileVersion: | - |
| LegalCopyright: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00008FFC | 0x00009000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59246 |
DATA | 0x0000A000 | 0x00000248 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.69893 |
BSS | 0x0000B000 | 0x00000E34 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000C000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43127 |
.tls | 0x0000D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x0000F000 | 0x000008A0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00010000 | 0x00002800 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.4698 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87667 | 899 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
49
Monitored processes
10
Malicious processes
3
Suspicious processes
1
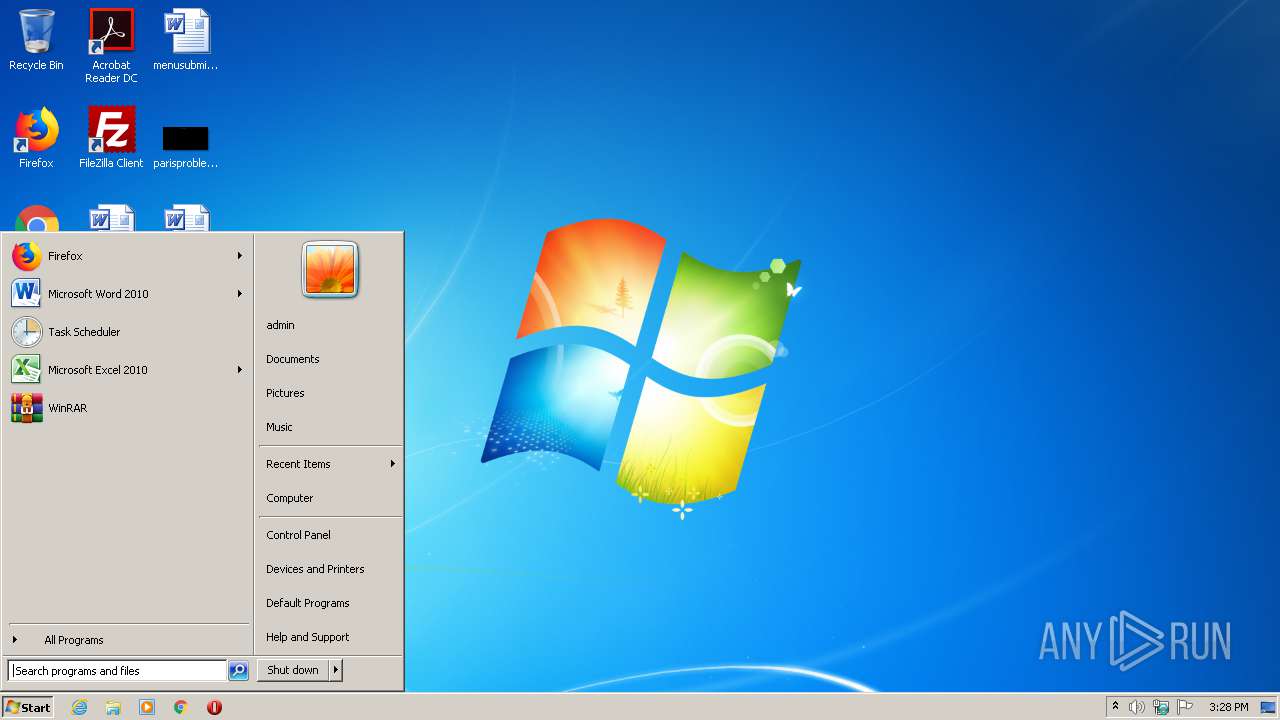
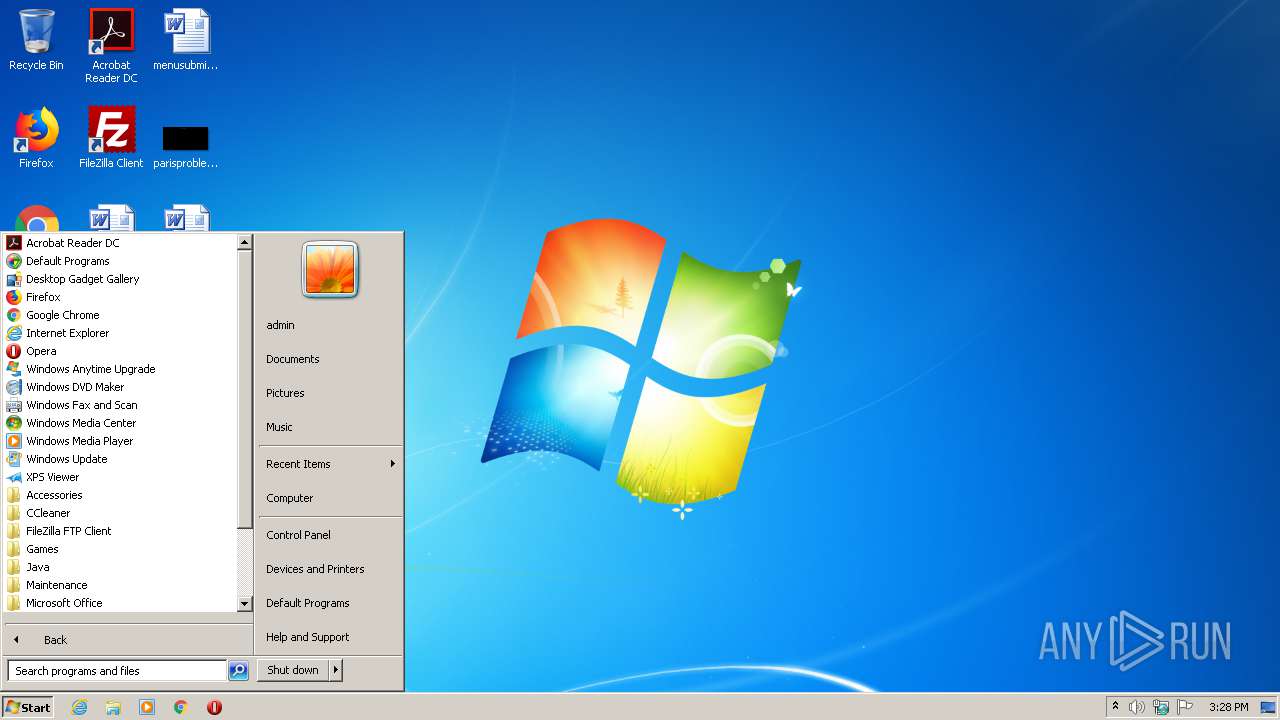
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | xcopy /s /y /k /f "C:\Program Files (x86)\Avira Antivir\Check for updates.bat" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup" | C:\Windows\system32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\AppData\Local\Temp\Synapse X Serial Key Generator.exe" | C:\Users\admin\AppData\Local\Temp\Synapse X Serial Key Generator.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Installer Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 2368 | powershell -Command "Start-Process powershell \"-ExecutionPolicy Bypass -NoProfile -Command `\"cd \`\"C:\Program Files (x86)\Avira Antivir\`\"; & \`\".\Compatibility test.ps1\`\"`\"\" -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\Synapse X Serial Key Generator.exe" | C:\Users\admin\AppData\Local\Temp\Synapse X Serial Key Generator.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Installer Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2812 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\Avira Antivir\check for updates.bat"" | C:\Windows\system32\cmd.exe | — | is-RE6UV.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2980 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -NoProfile -Command "cd \"C:\Program Files (x86)\Avira Antivir\"; & \".\Compatibility test.ps1\"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3028 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\Avira Antivir\avirascan.bat"" | C:\Windows\system32\cmd.exe | — | is-RE6UV.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3860 | "C:\Users\admin\AppData\Local\Temp\is-5DA1R.tmp\is-RE6UV.tmp" /SL4 $30138 "C:\Users\admin\AppData\Local\Temp\Synapse X Serial Key Generator.exe" 380631 52224 | C:\Users\admin\AppData\Local\Temp\is-5DA1R.tmp\is-RE6UV.tmp | Synapse X Serial Key Generator.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.43.0.0 Modules
| |||||||||||||||
| 4040 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\Avira Antivir\Run_Compatibility_test.bat"" | C:\Windows\system32\cmd.exe | — | is-RE6UV.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4076 | Schtasks.exe /create /F /tn "Avira routine scan" /tr "C:\Program Files (x86)\Avira Antivir\Check for updates.bat" /SC DAILY | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
836
Read events
711
Write events
125
Delete events
0
Modification events
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.1.8 | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Avira Antivir | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Avira Antivir\ | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Installer | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Avira Antivir\unins000.exe" | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Avira Antivir\unins000.exe" /SILENT | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (3860) is-RE6UV.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{1485B3A2-4F13-4C2A-8971-658FC8468BC5}_is1 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
7
Suspicious files
4
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-3MBOE.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-6AMCB.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-LM616.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-D60VI.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-V3F6N.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-HL3MP.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-8PL49.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-SJAQ3.tmp | — | |
MD5:— | SHA256:— | |||
| 3860 | is-RE6UV.tmp | C:\Program Files\Avira Antivir\is-KSO2B.tmp | — | |
MD5:— | SHA256:— | |||
| 2368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\D3AZ28LPURE4NWLT86LA.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report